Juli Cha Cha jl A cryptographically secure pseudorandom

- Slides: 17
Juli. Cha (Cha. jl): A cryptographically secure pseudorandom number generator for Julia Adam Sealfon
Random numbers in computing • Modeling and simulation • Optimization • Randomized algorithms • Approximation algorithms • Primality testing • Games, e. g. poker • Cryptography
Pseudorandom number generators (PRNGs) • True randomness is expensive or limited • PRNGs take a short random seed and expand it to produce a long sequence of bits that “look random” • Programs can use this instead of true randomness • The sequence should have the same statistical properties as a random sequence, e. g. : • • • Roughly equal number of 0 s and 1 s Short substrings are repeated with the expected probability Ascending and descending sequences should occur in the right pattern Random binary matrices should have high rank etc.
The need for better pseudorandomness • For some applications it’s not enough for PRNG output to have the same statistical properties as a random string • We want it to be impossible to distinguish from true randomness • E. g. Poker, cryptography • Poor design or buggy implementations of PRNGs has led to cryptographic breaks
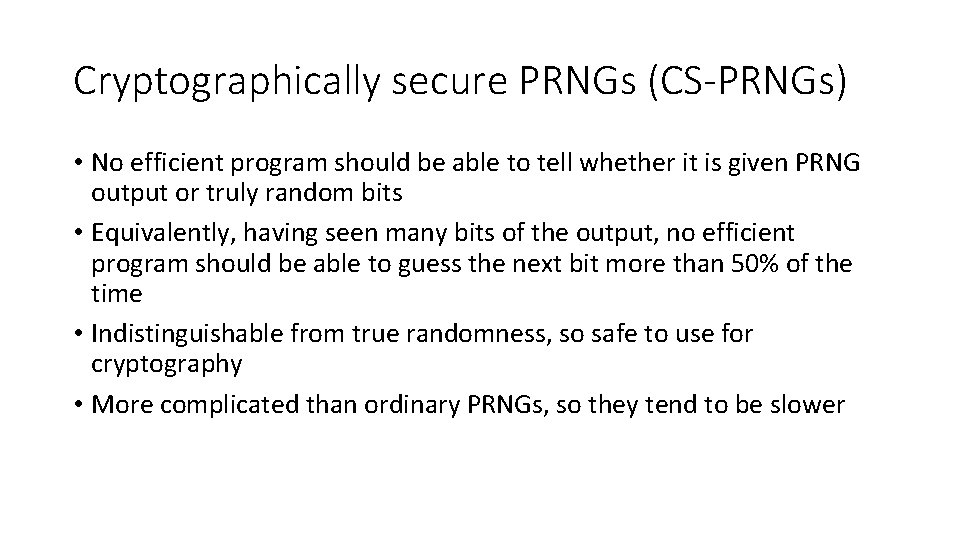
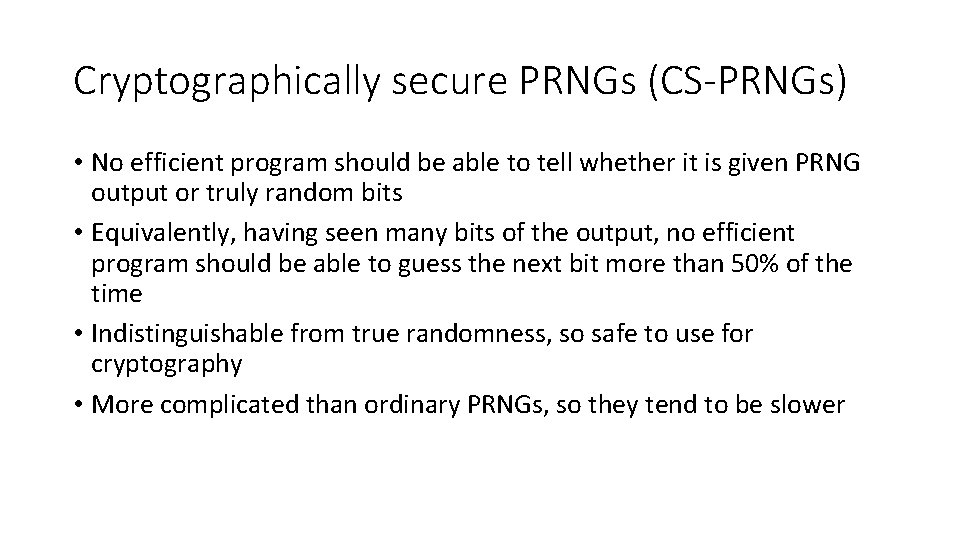
Cryptographically secure PRNGs (CS-PRNGs) • No efficient program should be able to tell whether it is given PRNG output or truly random bits • Equivalently, having seen many bits of the output, no efficient program should be able to guess the next bit more than 50% of the time • Indistinguishable from true randomness, so safe to use for cryptography • More complicated than ordinary PRNGs, so they tend to be slower
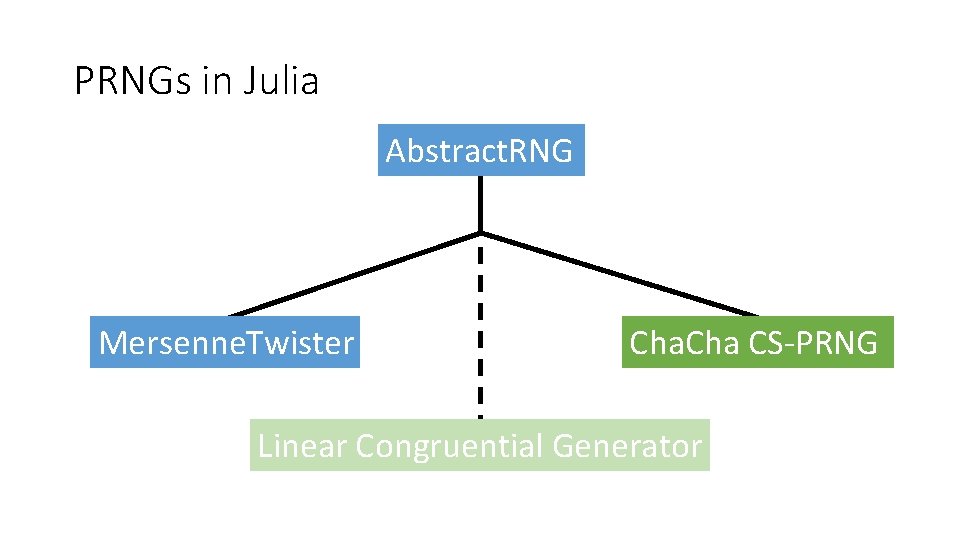
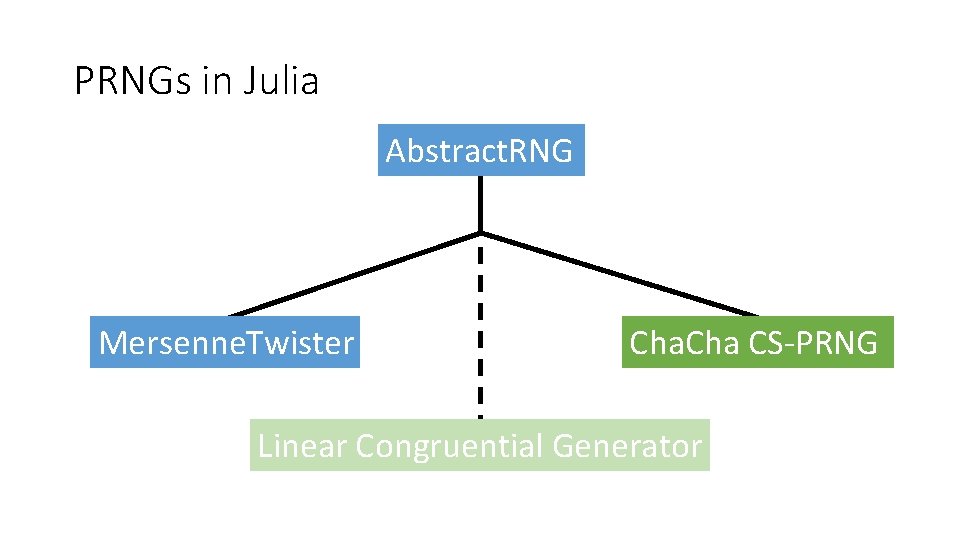
PRNGs in Julia Abstract. RNG Mersenne. Twister Cha CS-PRNG Linear Congruential Generator
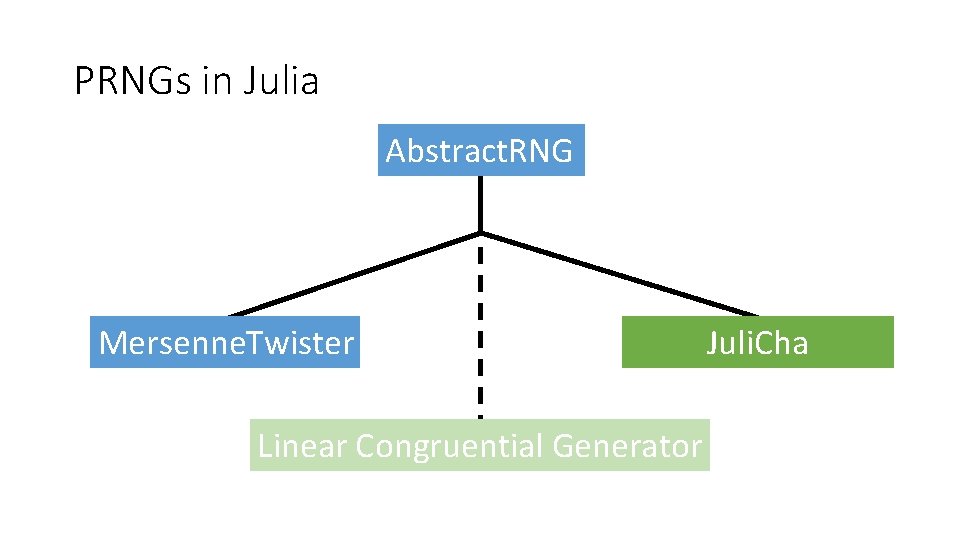
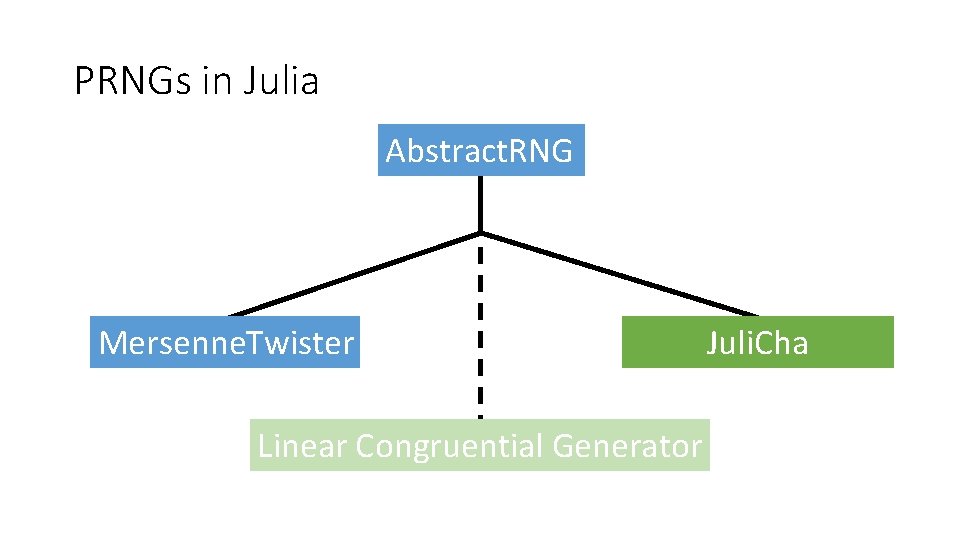
PRNGs in Julia Abstract. RNG Mersenne. Twister Linear Congruential Generator Juli. Cha
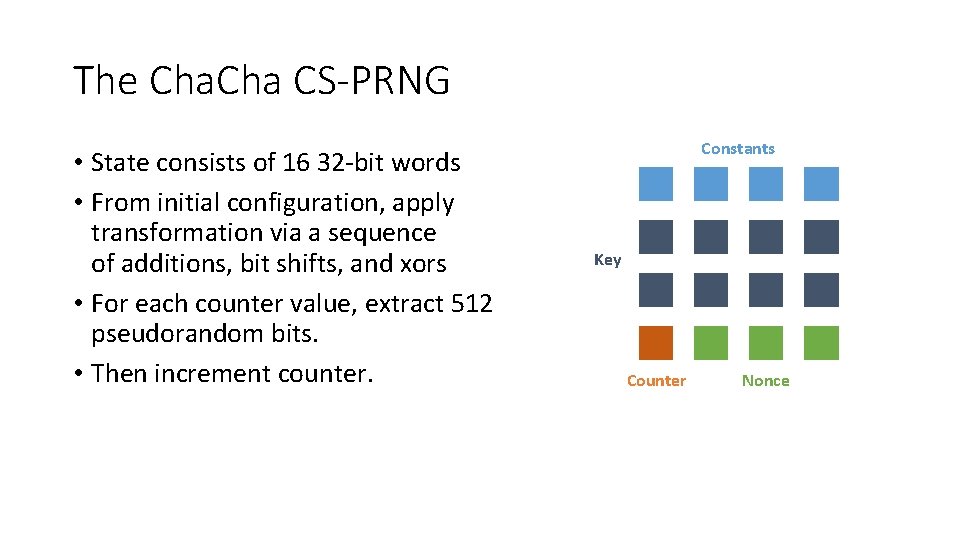
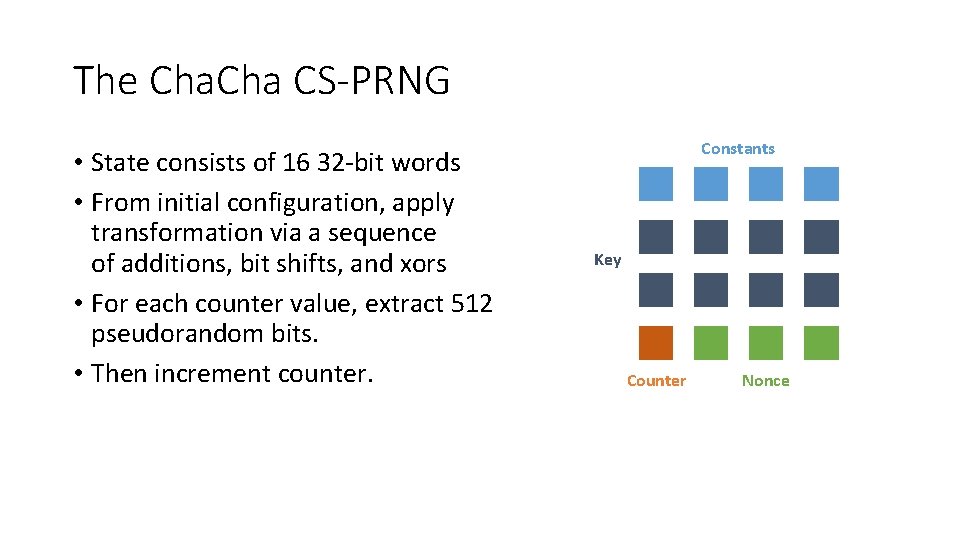
The Cha CS-PRNG • State consists of 16 32 -bit words • From initial configuration, apply transformation via a sequence of additions, bit shifts, and xors • For each counter value, extract 512 pseudorandom bits. • Then increment counter. Constants Key Counter Nonce
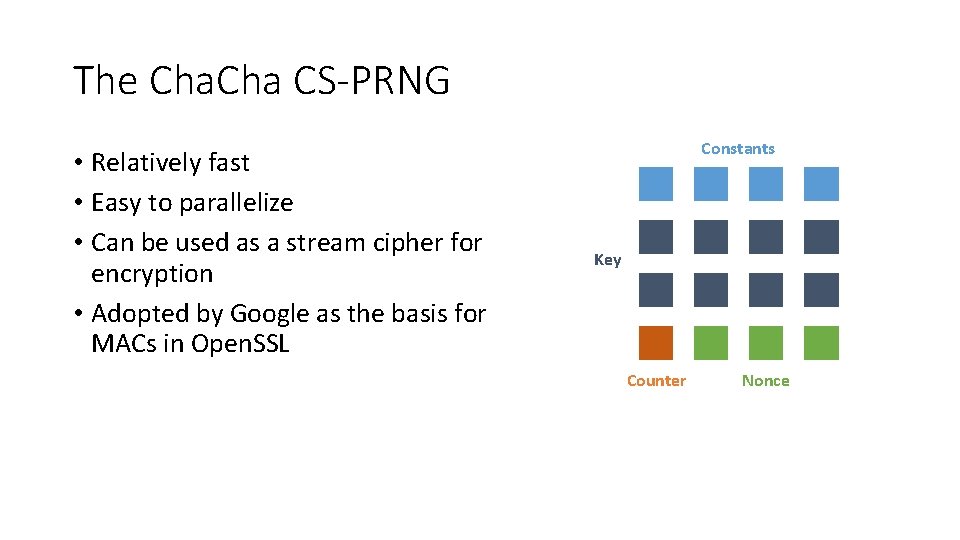
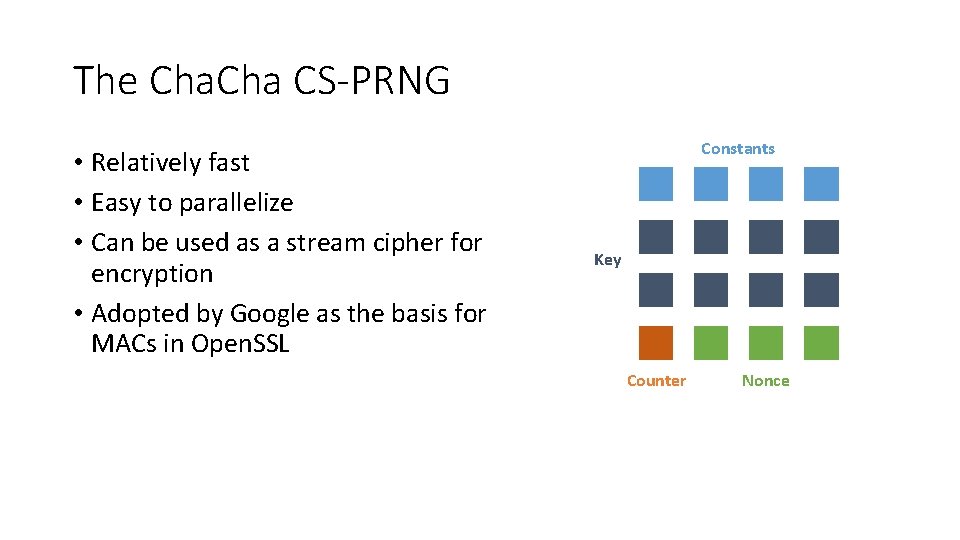
The Cha CS-PRNG • Relatively fast • Easy to parallelize • Can be used as a stream cipher for encryption • Adopted by Google as the basis for MACs in Open. SSL Constants Key Counter Nonce
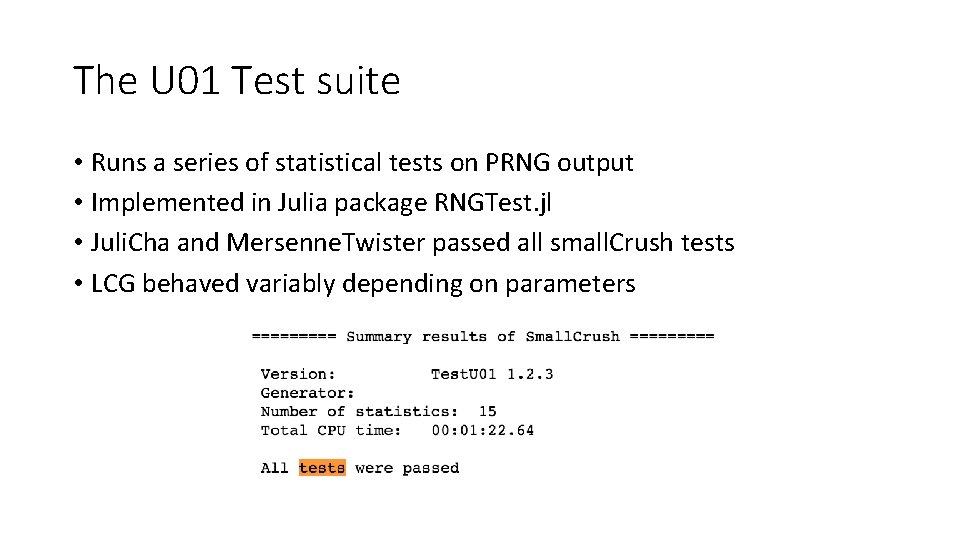
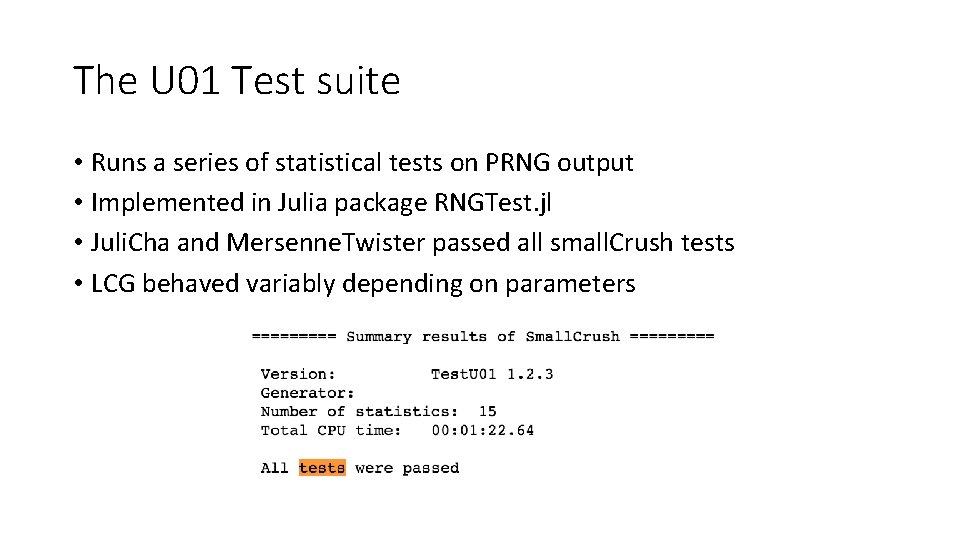
The U 01 Test suite • Runs a series of statistical tests on PRNG output • Implemented in Julia package RNGTest. jl • Juli. Cha and Mersenne. Twister passed all small. Crush tests • LCG behaved variably depending on parameters
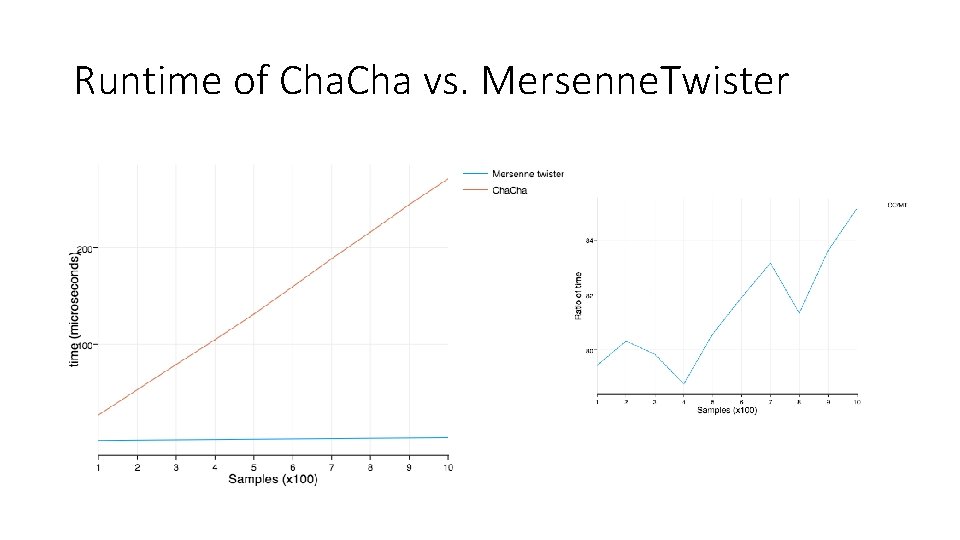
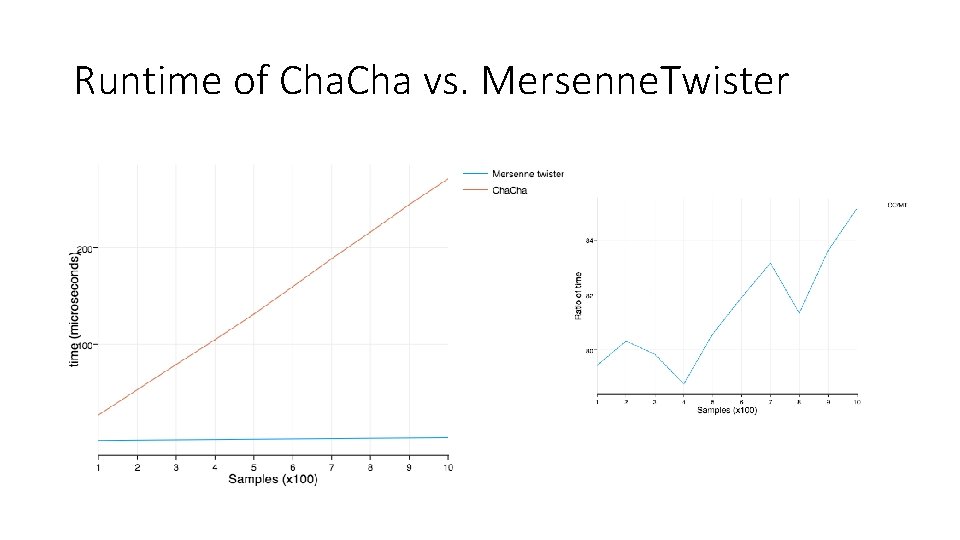
Runtime of Cha vs. Mersenne. Twister
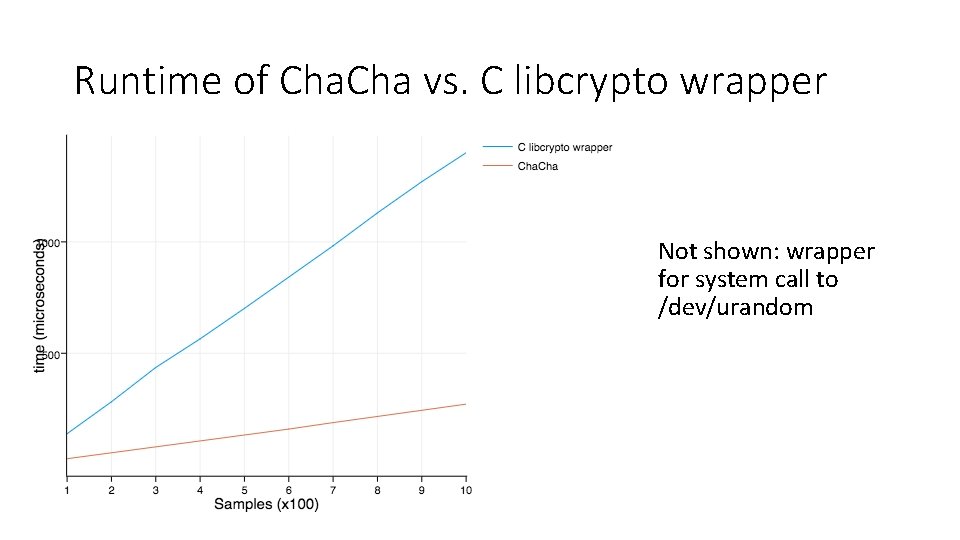
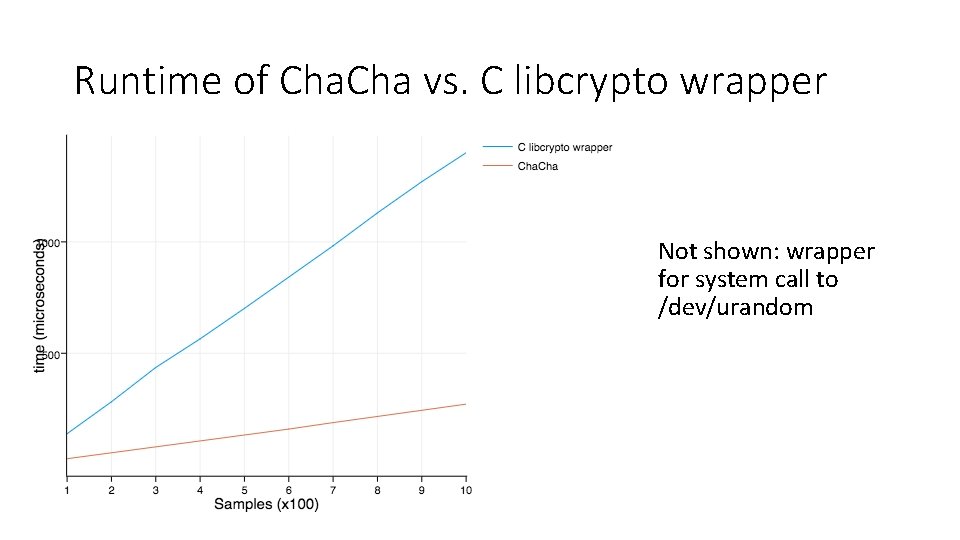
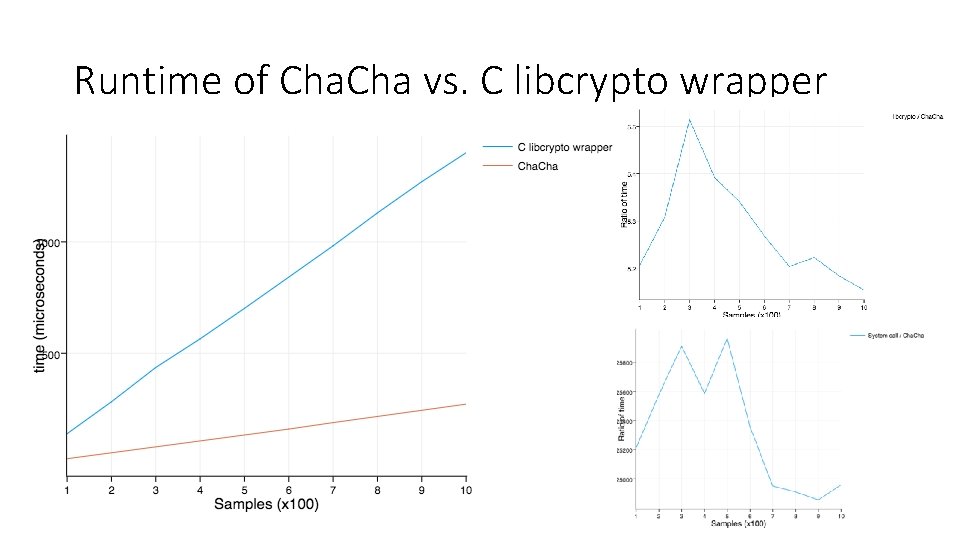
Runtime of Cha vs. C libcrypto wrapper Not shown: wrapper for system call to /dev/urandom
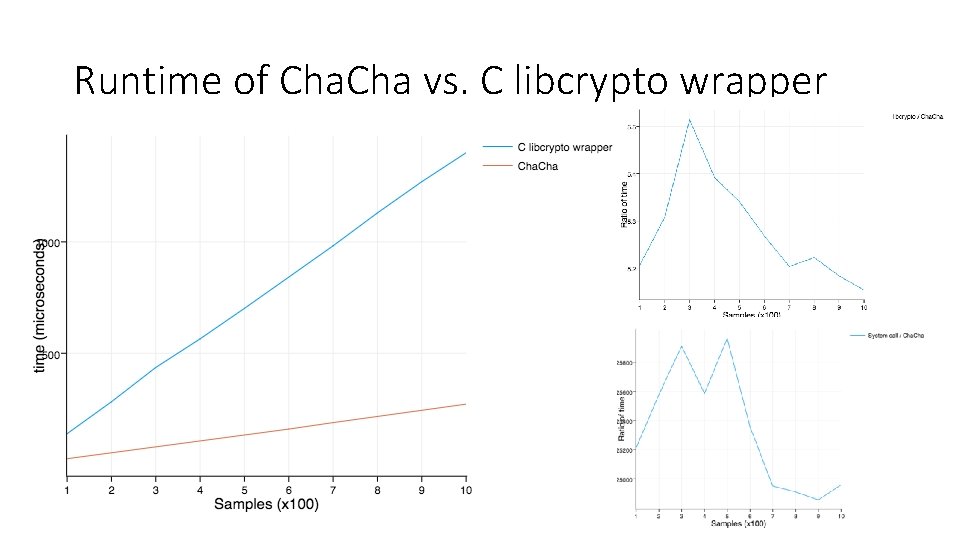
Runtime of Cha vs. C libcrypto wrapper
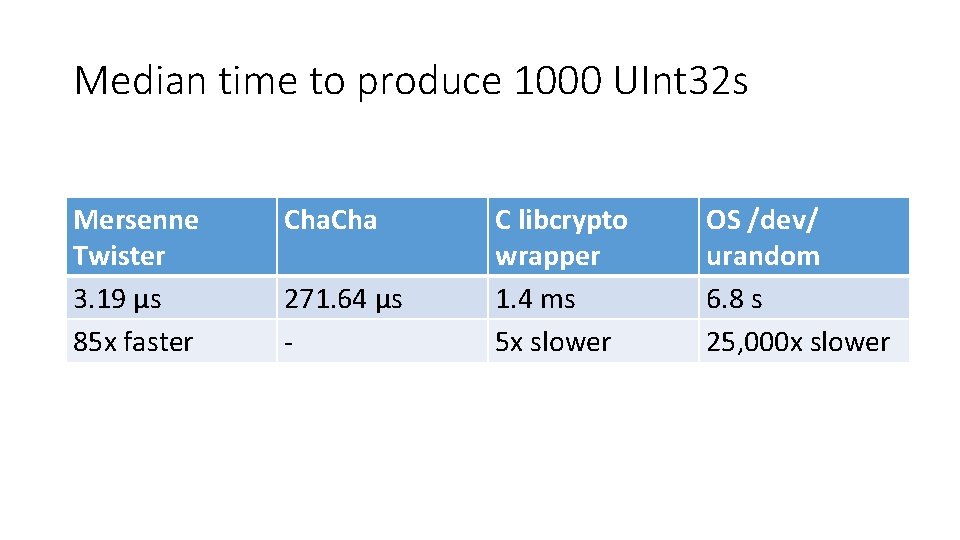
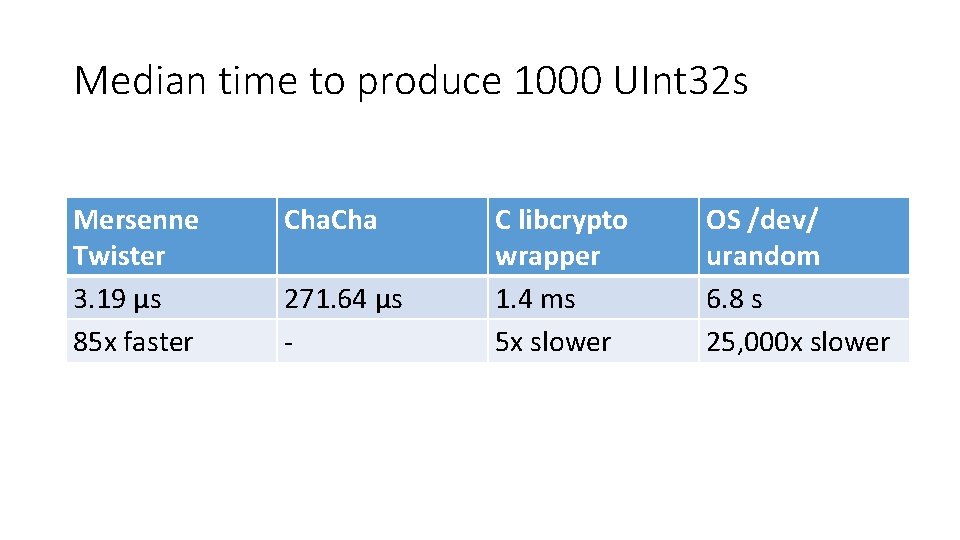
Median time to produce 1000 UInt 32 s Mersenne Twister 3. 19 μs 85 x faster Cha 271. 64 μs - C libcrypto wrapper 1. 4 ms 5 x slower OS /dev/ urandom 6. 8 s 25, 000 x slower

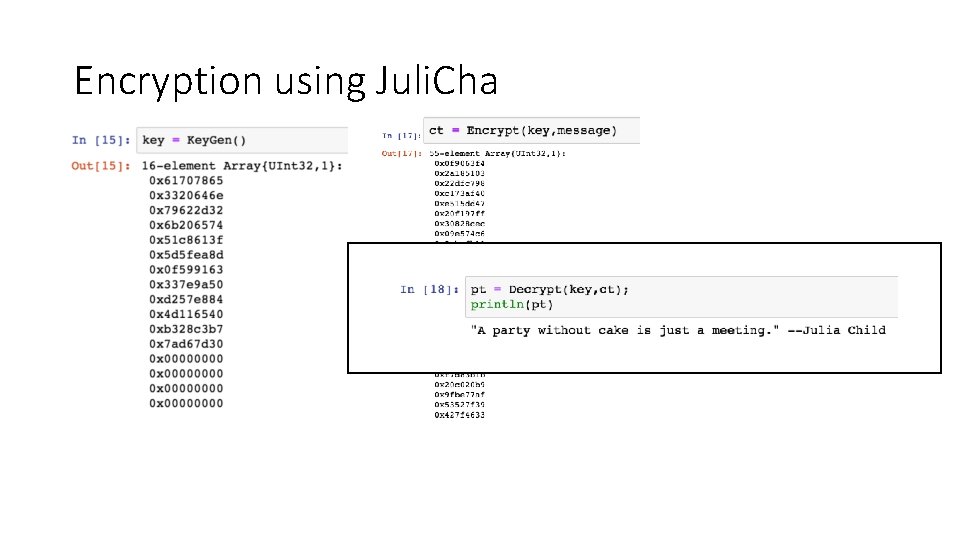
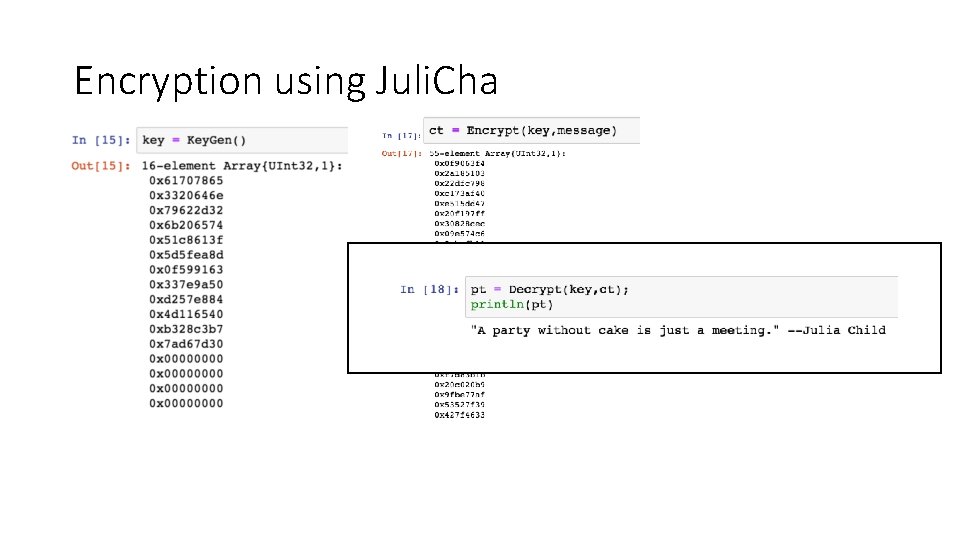
Encryption using Juli. Cha