JMU Gen Cyber Boot Camp Summer 2016 Goals
JMU Gen. Cyber Boot Camp Summer, 2016
Goals • Have fun! • Teach you about Cyber Defense so that you can: –Interest your students in Cyber Defense –Teach your students about Cyber Defense • Cyber Defense Clubs • Cyber. Patriot Program (http: //www. uscyberpatriot. org/)
Exercises • Virtual machines (VMs) are great for hands-on Cyber Defense exercises • You can create and use VMs with your students using free software: –Virtual. Box (https: //www. virtualbox. org/) –VMWare Player (http: //www. vmware. com/products/player/)
Why You (and Your Students) Should Not Be Attackers • It is illegal: –United States Code, Title 18, Section 1030 (and others) –USA Patriot Act, Homeland Security Act, PROTECT Act –www. cybercrime. gov • Basically: –Unauthorized access or use of a computer or network system is illegal –Unintentional attacks are illegal too
Understanding the Systems You are Defending • You cannot effectively defend what you don't understand • Think about what needs to be defended (security triad)
Understanding Your Adversaries • Can evaluate systems you defend as attackers will • Can implement countermeasures designed to thwart attackers • Better understand the implications of certain decisions
Understanding Tools and Techniques at Your Disposal • What security policies and mechanisms you will employ? • What are your goals? • Prevention • Detection • Recovery • What policies and mechanisms are justified?
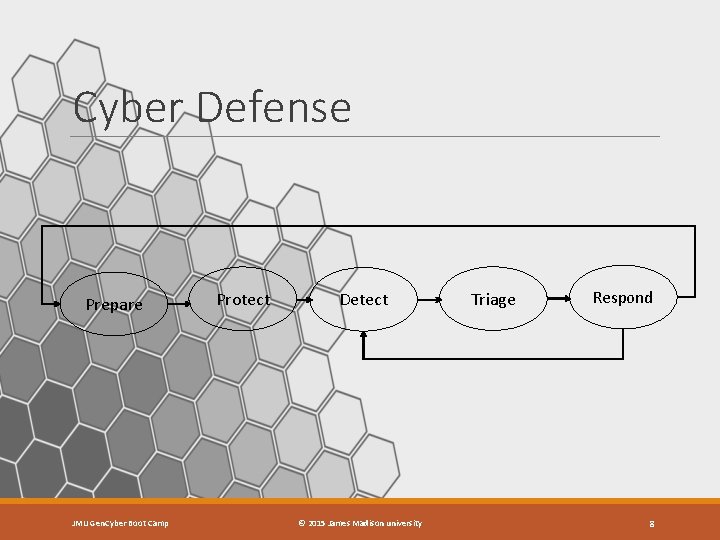
Cyber Defense Prepare JMU Gen. Cyber Boot Camp Protect Detect © 2015 James Madison university Triage Respond 8
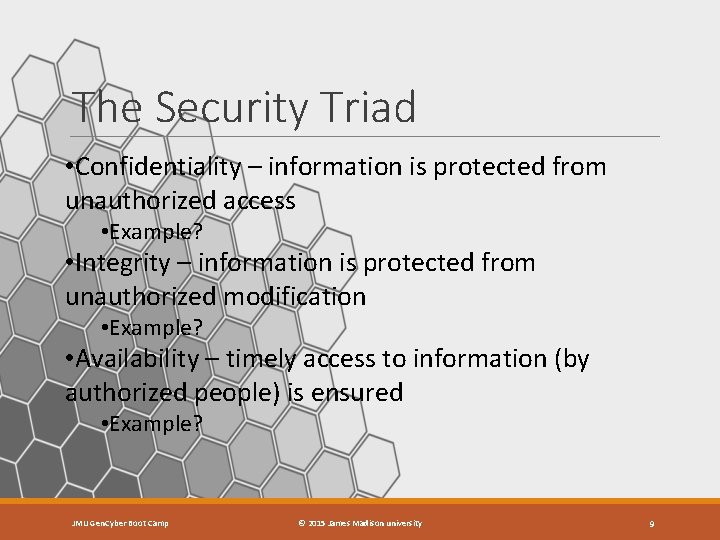
The Security Triad • Confidentiality – information is protected from unauthorized access • Example? • Integrity – information is protected from unauthorized modification • Example? • Availability – timely access to information (by authorized people) is ensured • Example? JMU Gen. Cyber Boot Camp © 2015 James Madison university 9
Gen. Cybersecurity First Principles • Domain Separation • Process Isolation • Resource Encapsulation • Modularity • Least Privilege • Abstraction • Data Hiding • Layering • Conceptually Simple JMU Gen. Cyber Boot Camp © 2015 James Madison university 10
Useful Links csrc. nist. gov/nice/ - NICE is a national campaign designed to improve the cyber behavior, skills, and knowledge of every segment of the population, enabling a safer cyberspace. securingourecity. org/- Securing Our e. City organization provides awareness of potential issues and offers free cybersecurity information and education. www. onguardonline. gov/ - On. Guard. Online. gov is the federal government’s website to help you be safe, secure and responsible online. www. mysecurecyberspace. com - A Free Educational Resource Created by Carnegie Mellon University to Empower You to Secure Your Part of Cyberspace http: //www. carnegiecyberacademy. com/ - At the Carnegie Cyber Academy, cadets complete several training missions in Cyberspace that equip them with the skills they need to be good cybercitizens and Cyber Defenders of the Internet.
Useful Links (cont) http: //www. netsupportschool. com/ - Net. Support School is the class-leading training software solution, providing teachers with the ability to instruct and visually/audibly monitor, as well as interact with their students, individually, as a pre-defined group or to the whole class. http: //www. consumer. ftc. gov/features/feature-0014 -identity-theft - Federal trade commission provides several resources in identity theft, file sharing, and others. http: //www. us-cert. gov/ - US-CERT’s mission is to improve the nation's cybersecurity posture, coordinate cyber information sharing, and proactively manage cyber risks to the nation while protecting the constitutional rights of Americans. http: //www. sans. org/ - The SANS Institute was established in 1989 as a cooperative research and education organization. Its programs now reach more than 165, 000 security professionals around the world. https: //www. issa. org/ - The Information Systems Security Association's official website. http: //www. nationalcyberwatch. org/ - Cyber security resources and certification information.
Final Thoughts • Thank you for your participation! • We hope you can use what we have learned to interest your students in Cyber Defense • If we can be of assistance in the future, just ask • Things to do before you leave: • I 9 forms for stipends • Final Exam
- Slides: 13