Jihadist Web Postings and Popular Social Media A
Jihadist Web Postings and Popular Social Media: A Forensic Psychological Analysis Ronn Johnson, Ph. D, ABPP* Jessica Mueller, Psy. D Student** Christine Collins, Psy. D Student** David B. Ross, Ed. D. *** Rande Matteson, Ph. D. **** *University of San Diego **Alliant International University ***Nova Southeastern University ****St. Leo University.
Overview ● ● ● ● Importance of this research Analyses Theories Forensic Implications Use of the Internet Forums Types of social media Future directions
Importance of Social Media Research ● The Internet has revolutionized the way terrorists communicate. ● Terrorists have two primary goals: o Demonstrate their strength and make authorities feel vulnerable by inducing fear. ● According to Pew Research (2014), 74% of adults, with 89% of individuals ages 18 -29 using social media extensively. o This statistic is particularly important as it is estimated approximately 70% of the individuals recruited to engage in terrorism are age 18 -23 (Lennings et al. , 2010; Pew Research, 2014)
Analyses ● Automated Web Harvesting ● Systematic scans using keywords o Locating sites and mirrors ● Descriptive content analysis o High and low attribute levels o Members, topics, and posts ● Link Analysis o Similarities based on topic o Terrorist group links (Abdulla, 2011; Salem et al. , 2008; Torres-Soriano, 2013; Weimann)
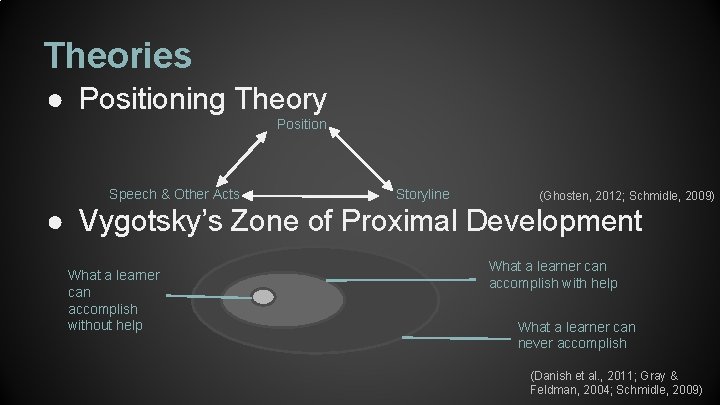
Theories ● Positioning Theory Position Speech & Other Acts Storyline (Ghosten, 2012; Schmidle, 2009) ● Vygotsky’s Zone of Proximal Development What a learner can accomplish without help What a learner can accomplish with help What a learner can never accomplish (Danish et al. , 2011; Gray & Feldman, 2004; Schmidle, 2009)
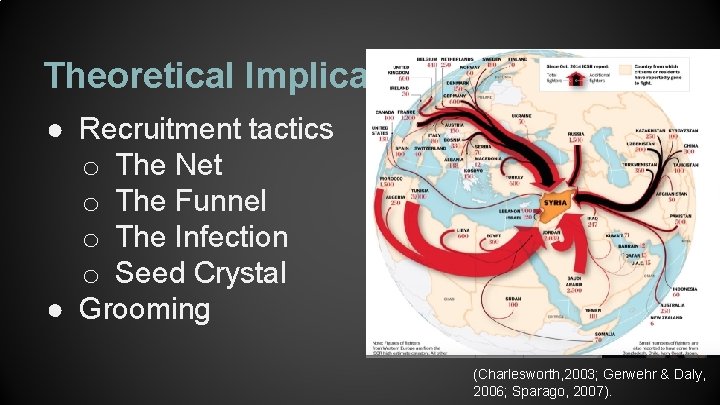
Theoretical Implications in Forensics ● Recruitment tactics o The Net o The Funnel o The Infection o Seed Crystal ● Grooming (Charlesworth, 2003; Gerwehr & Daly, 2006; Sparago, 2007).
Use of Internet ● ● ● Spread propaganda Recruitment Incitement Fundraising Create virtual friendships Virtual Training (Gwinn, 2006; Lethbridge, 1995; Lennings 2010)
Internet Forums ● Formation and design o Host sites and mirrors o Sections ● Utility of Internet forums o Gain followers o Regulate conversation and ideals (Abdulla, 2011; Amble, 2012; Salem, Reid, & Chen, 2008; Torres-Soriano, 2013)
Types of Social Media ● ● Twitter Facebook Youtube Second Life (Altman, 2014; Department of Homeland Secruity, 2010; Klausen et al. , 2012; Weimann, 2010)
Future Directions ● Deterrence o Snort o Network Mapper (Nmap) ● Stricter policies towards national and international security o Israel o The United States and Homeland Security (Dawson, 2015)
Future Directions ● Continuing to monitor forums and social media ● Infiltrate forums and social media o Creation of “honey pot” websites o Hacktivists (Theohary & Rollins, 2011; Weimann, 2004)
References Abdulla, R. A. (2007). Islam, Jihad, and terrorism in post-9/11 Arabic discussion boards. Journal Computer-Mediated Communication, 12, 1063 -1081. doi: 10. 111/j. 1083 -6101. 2007. 00363. x Altman, A. (2014). Why terrorists love twitter. Retrieved from http: //time. com/3319278/isis-isil-twitter/ Danish, J. A. , Peppler, K. , Phelps, D. , & Washington, D. (2011). Life in the hive: Supporting inquiry into complexity within the Zone of Proximal Development. Journal of Science Education Technology, 20, 454 -467. doi: 10. 1007/s 10956 -011 -9313 -4 Department of Homeland Security (2010). Terrorist Use of Social Networking Sites: Facebook Case Study. Retrieved from https: //publicintelligence. net/ufouoles-dhs-terrorist-use-of-social-networking-facebook-case-study/ Gerwehr, S. & Daly, S. (2006). Al- Qaida: Terrorist selection and recruitment. Mc. Graw-Hill Homeland Security Handbook: Chapter 5, 73 -89 Ghosten, C. D. (2012). Analyzing conflict in organizations with positioning theory: A narrative inquiry. (Dissertation). University of Tennessee, Knoxville. Gray, P. , & Feldman, J. (2004). Playing in the Zone of Proximal Development: Qualities of self-directed age mixing between adolescents and young children at a democratic school. American Journal of Education, 110, 108 -145. Lennings, C. J. , Amon, K. L. , Brummert, H. , & Lennings, N. J. (2010). Grooming for terror: The Internet and young people. Psychiatry, Psychology, and Law, 17(3), 424 -437.
References Pew. Research (2014). Social networking fact sheet. Retrieved from http: //www. pewinternet. org/fact-sheets/social-networking-factsheet/ Rivers, D. (2013). How terror can breed through social media. Retrieved from http: //www. cnn. com/2013/04/27/world/rivers-socialmedia-terror/index. html Rogers, M. (2003) “The Psychology of Cyber-terrorism, ” in Terrorist, Victims and Society, ed. Andrew Silke, Chichester: John Wiley & Sons. Salem, A. , Reid, E. , & Chen, H. (2008). Multimedia content coding analysis: Unraveling the content of Jihadi extremist groups’ videos. Studies in Conflict & Terrorism, 31, 605 -626. doi: 10. 1080/105761008021440072 Schmidle, R. E. (2009). Positioning theory and terrorist networks. Journal for the Theory of Social Behaviour, 40(1), 65 -78. Torres-Soriano, M. R. (2013). The dynamics of the creation, evolution, and disappearance of terrorist internet forums. International Journal of Computer Vision, 7(1), 164 -178. Weimann, G. (2006). Terror on the Internet, United States Institute of Peace, Washington D. C. : USIP Press Books, http: //bookstore. usip. org/books/Book. Detail. aspx? product. ID=134280 Weimann, G. (2010). Terror on Facebook, Twitter, and Youtube. Brown Journal of World Affairs, 16(2), 45 -54.
- Slides: 13