Java Vs Dot Net Security Presented By Naveen
Java Vs Dot Net Security Presented By, Naveen Kumar Ratkal
Outline CLR VS JVM Java Byte Code and MSIL Comparing the stacks Major security vulnerabilities reported Code Access Security Policy Tool Java Authentication and Authorization service (JAAS) Class file and Cs file Summary Choosing between Java and. Net
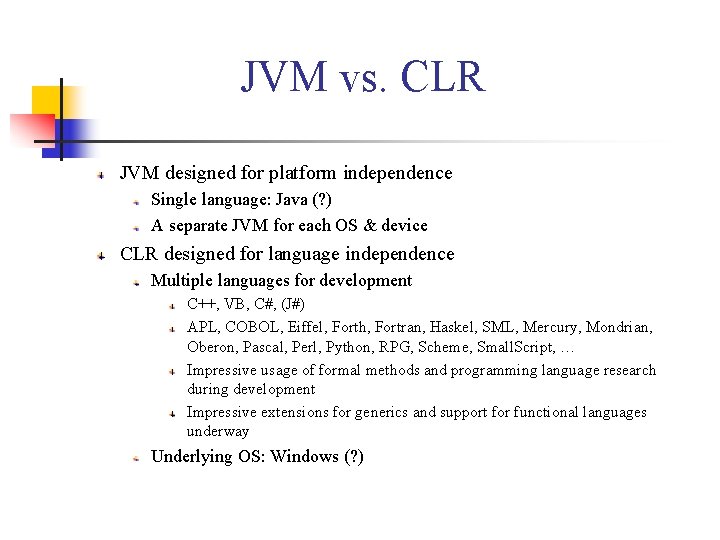
JVM vs. CLR JVM designed for platform independence Single language: Java (? ) A separate JVM for each OS & device CLR designed for language independence Multiple languages for development C++, VB, C#, (J#) APL, COBOL, Eiffel, Forth, Fortran, Haskel, SML, Mercury, Mondrian, Oberon, Pascal, Perl, Python, RPG, Scheme, Small. Script, … Impressive usage of formal methods and programming language research during development Impressive extensions for generics and support for functional languages underway Underlying OS: Windows (? )
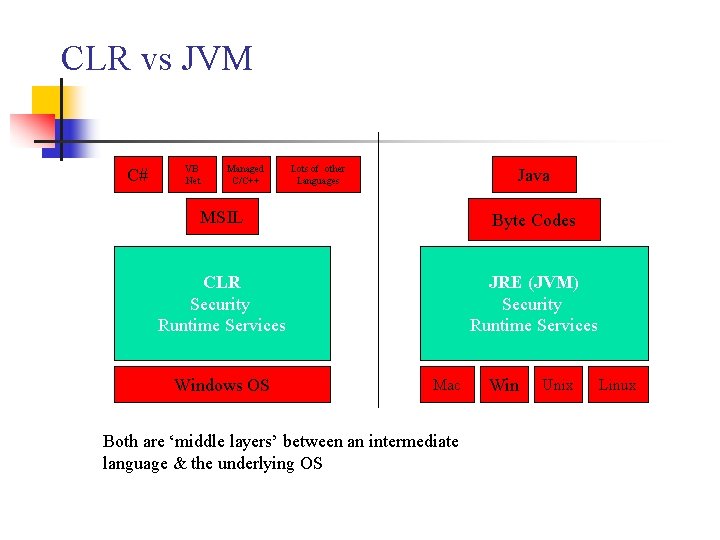
CLR vs JVM C# VB. Net Managed C/C++ Lots of other Languages Java MSIL Byte Codes CLR Security Runtime Services JRE (JVM) Security Runtime Services Windows OS Mac Both are ‘middle layers’ between an intermediate language & the underlying OS Win Unix Linux
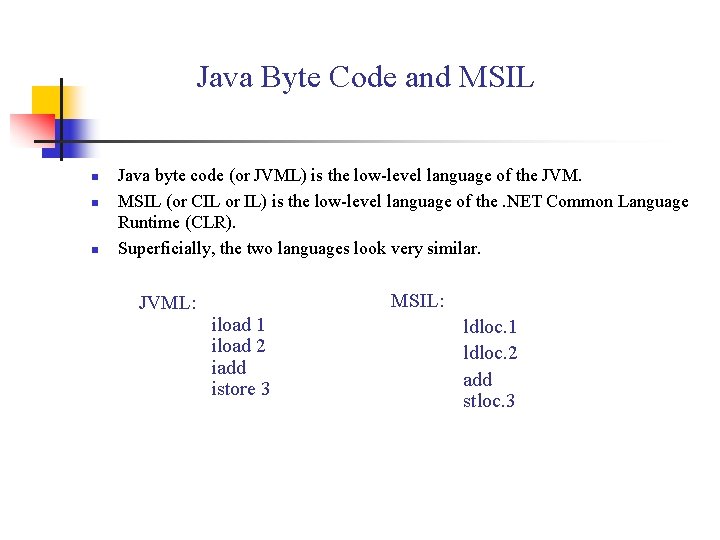
Java Byte Code and MSIL n n n Java byte code (or JVML) is the low-level language of the JVM. MSIL (or CIL or IL) is the low-level language of the. NET Common Language Runtime (CLR). Superficially, the two languages look very similar. JVML: MSIL: iload 1 iload 2 iadd istore 3 ldloc. 1 ldloc. 2 add stloc. 3
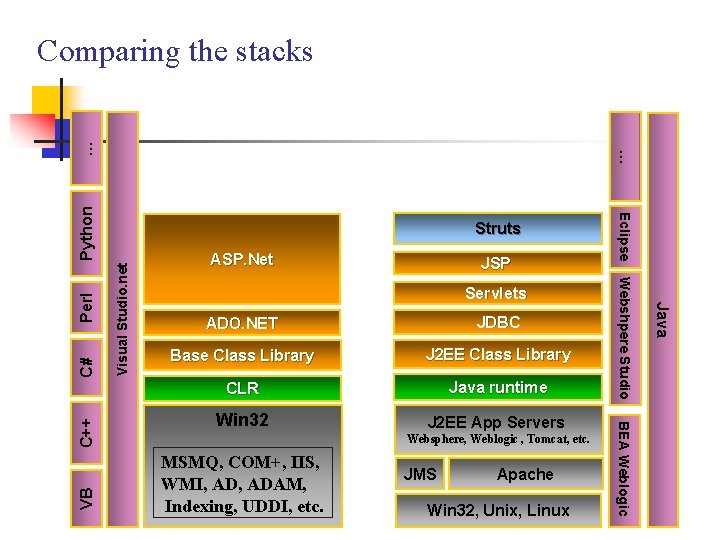
Visual Studio. net Perl Servlets ADO. NET JDBC Base Class Library J 2 EE Class Library CLR Java runtime Win 32 J 2 EE App Servers Websphere, Weblogic , Tomcat, etc. MSMQ, COM+, IIS, WMI, ADAM, Indexing, UDDI, etc. JMS Apache Win 32, Unix, Linux Java C# JSP BEA Weblogic C++ ASP. Net Webshpere Studio VB Struts Eclipse Python … … Comparing the stacks
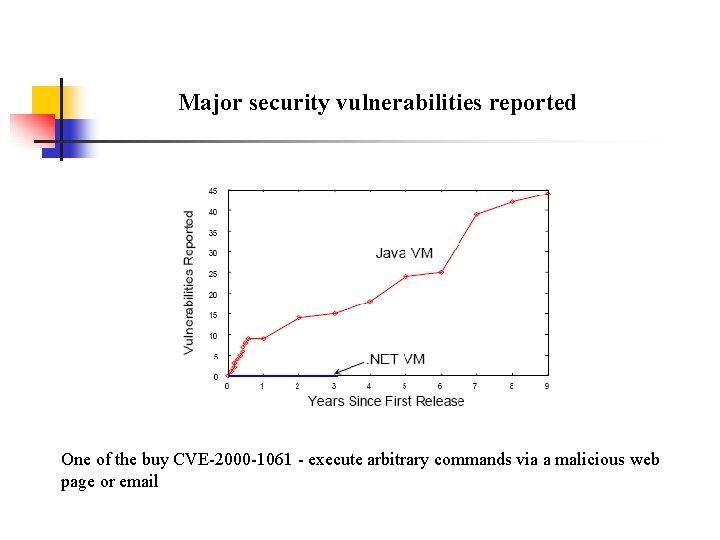
Major security vulnerabilities reported One of the buy CVE-2000 -1061 - execute arbitrary commands via a malicious web page or email
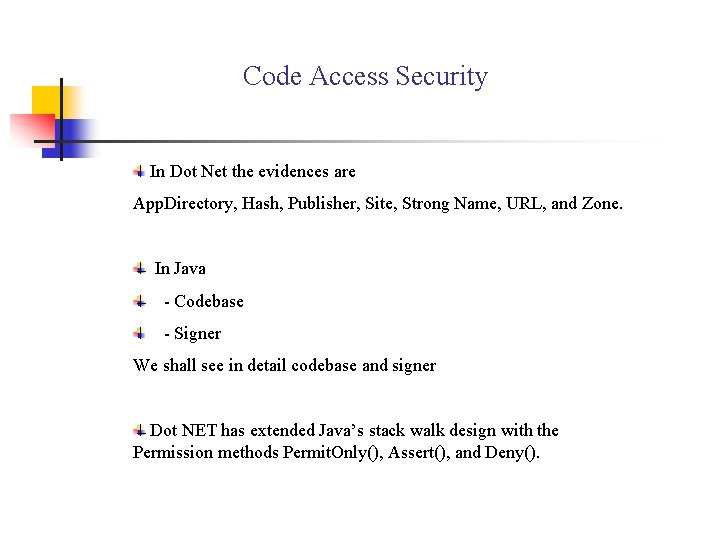
Code Access Security In Dot Net the evidences are App. Directory, Hash, Publisher, Site, Strong Name, URL, and Zone. In Java - Codebase - Signer We shall see in detail codebase and signer Dot NET has extended Java’s stack walk design with the Permission methods Permit. Only(), Assert(), and Deny().
Ctnd. . Code base evidence can be URL, either web or local, from where it is accessed. Signer (effectively, the publisher of the code). Specify the permission in the policy file. Sign the jar files, if the policy file specifies the permission only for signed jar files. One can check the Manifest folder to see the signatures.
Demo Process…. . java -classpath "%EXEC_CLASSPATH%" -Djava. security. manager Djava. security. policy=="access. policy" Permission. Check access Without permissions java -classpath "%EXEC_CLASSPATH%" -Djava. security. manager Djava. security. policy=="access. policy" Permission. Check delete Accessing with permissions by signer jarsigner -verbose -keystore Demo. Pub. keystore -storepass changeit Permission. Check. jar Demo. Publisher java -classpath "%EXEC_CLASSPATH%" -Djava. security. manager Djava. security. policy=="access. policy" Permission. Check delete pause
Policy Tool What is a policy tool ? Uses Freeware Provided by Sun
Java Authentication and Authorization service (JAAS) To verify that a user is a subject and granting the user certain principals; "who you are. " The JAAS authentication component provides the ability to check who is currently executing Java code, regardless of whether the code is running as an application, an applet, a bean, or a servlet.
Login Module The login module receives information about the user and authenticates the user, thereby verifying that he or she is a valid subject. These login modules are identified by a name in a configuration file and then called by a Login. Context class that JAAS provides. Most of these modules expect to be run from an application or on the command line, and thus to be able to interact directly with a user.
Class file and Cs file With almost every form we write a cs file which handles the events. dot class files does same thing in java’s web application which is places in the WEB-INF classes folder.
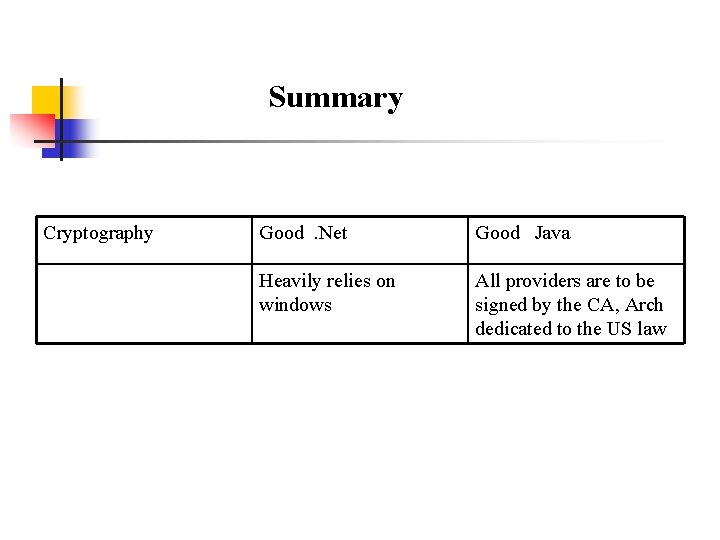
Summary Cryptography Good. Net Good Java Heavily relies on windows All providers are to be signed by the CA, Arch dedicated to the US law
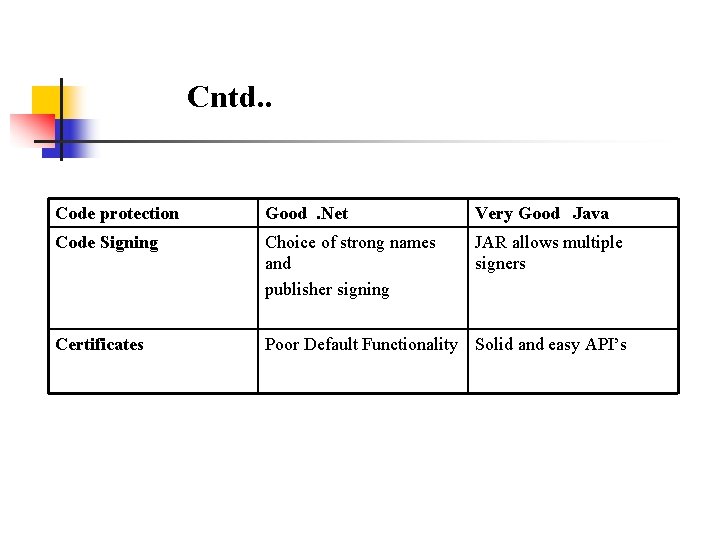
Cntd. . Code protection Good. Net Very Good Java Code Signing Choice of strong names and publisher signing JAR allows multiple signers Certificates Poor Default Functionality Solid and easy API’s
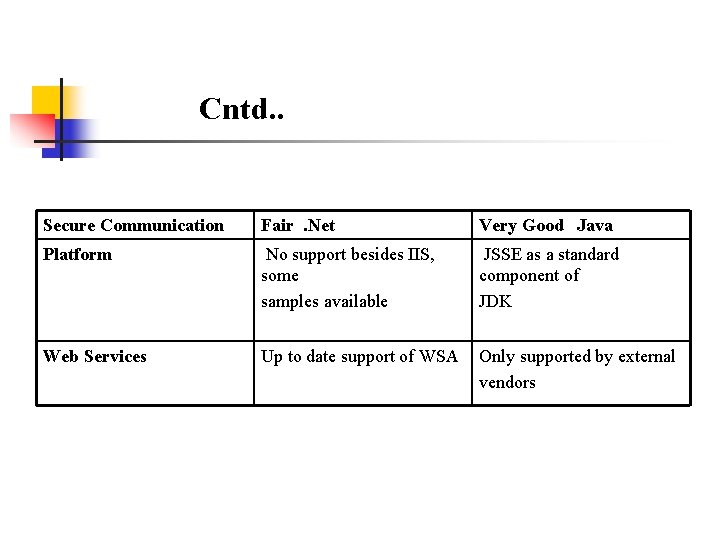
Cntd. . Secure Communication Fair. Net Very Good Java Platform No support besides IIS, some samples available JSSE as a standard component of JDK Web Services Up to date support of WSA Only supported by external vendors
Choosing between Java and. Net The ultimate choice usually depends not on technical superiority, but on: n n cultural/”religious”/political preferences Skill set of your developers Customer preference Vendor relations
References Websites : http: //vsbabu. org/mt/archives/2003/09/05/slashdot_java_vs_net. html http: //www. cgisecurity. com/lib/J 2 EEand. Dot. Netsecurity. By. Ger. Mulcahy. pdf http: //diuf. unifr. ch/softeng/seminars/SE 2003/buchmann/htmlpaper/index. html Book : Java Security - By oaks
Any Questions ? ? ?
- Slides: 20