Java Code Obfuscation Neerja Bhatnagar Reverse Engineering n
Java Code Obfuscation Neerja Bhatnagar
Reverse Engineering n n n Figuring out source code corresponding to a given byte code Source code intellectual property, needs protection Money, intelligence, hard work, time put to work to develop code
Problem of Reverse Engineering n Java code especially prone to reverse engineering, because n Java byte code well documented and well structured (freely available in JVM specs) n Most of the information contained in source code also present in byte code. n Software engineers have little control over distribution of Java applications and their source code because most Java applications distributed over the Internet (easy downloads)
Code Obfuscation n n n Technique to discourage and deter reverse engineering Scrambles byte code to make it unintelligible, difficult to understand Alters structure and appearance of code Attempts to make in uneconomical for an attacker to reverse engineer code Does not affect function of original program Does not alter source code, alters byte code
Code Obfuscation Techniques n n Low-Level n Layout Obfuscations n Control Obfuscations n Data Obfuscations High-Level or Design Obfuscations n Class Coalescing Obfuscation n Class Splitting Obfuscation n Type Hiding
Design Obfuscations n n n Low-level obfuscation techniques not sufficient because they do not hide design information Design information can facilitate an attacker from gaining general understanding of code and what it does Design obfuscations aim at hiding valuable high-level design information
Class Coalescing Obfuscation n n Combines two or more classes into a single class If the classes to be coalesced n have attributes with same name, these are renamed to distinguish among them n have non-constructor methods with same signature, except for one non-constructor methods, all others are renamed and altered
Class Coalescing Obfuscation Example
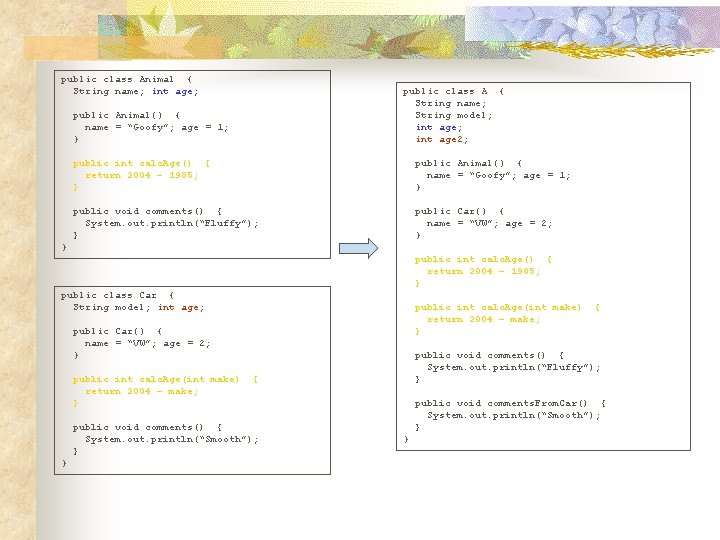
public class Animal { String name; int age; public class A { String name; String model; int age 2; public Animal() { name = “Goofy”; age = 1; } public int calc. Age() { return 2004 – 1985; } public Animal() { name = “Goofy”; age = 1; } public void comments() { System. out. println(“Fluffy”); } public Car() { name = “VW”; age = 2; } } public int calc. Age() { return 2004 – 1985; } public class Car { String model; int age; public int calc. Age(int make) return 2004 – make; } public Car() { name = “VW”; age = 2; } public int calc. Age(int make) return 2004 – make; } } public void comments() { System. out. println(“Fluffy”); } { public void comments() { System. out. println(“Smooth”); } { public void comments. From. Car() { System. out. println(“Smooth”); } }
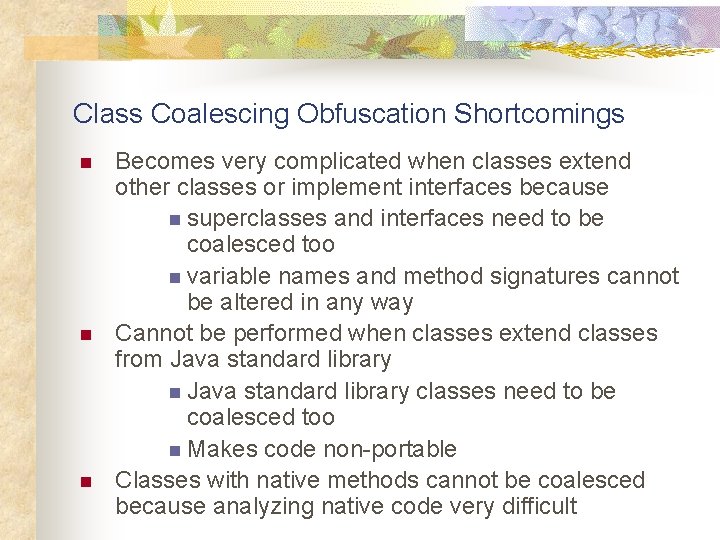
Class Coalescing Obfuscation Shortcomings n n n Becomes very complicated when classes extend other classes or implement interfaces because n superclasses and interfaces need to be coalesced too n variable names and method signatures cannot be altered in any way Cannot be performed when classes extend classes from Java standard library n Java standard library classes need to be coalesced too n Makes code non-portable Classes with native methods cannot be coalesced because analyzing native code very difficult
Class Splitting Obfuscation n n Splits a class into multiple classes Several ways to split a class Valid split function preserves dependencies among class’s methods and fields Valid split functions include n n Split class A into classes A 1 and A 2, where A 2 extends A 1 Split methods defined in class A between classes A 1 and A 2
Class Splitting Obfuscation Example
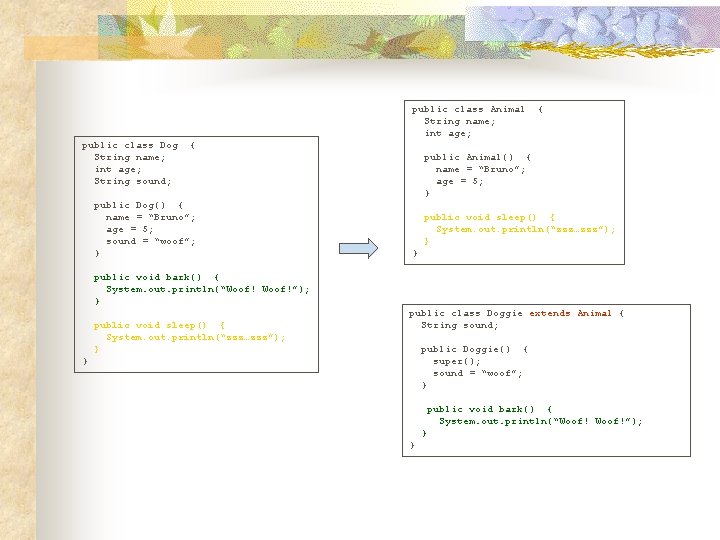
public class Animal String name; int age; public class Dog String name; int age; String sound; { { public Dog() { name = “Bruno”; age = 5; sound = “woof”; } public Animal() { name = “Bruno”; age = 5; } public void sleep() { System. out. println(“zzz…zzz”); } } public void bark() { System. out. println(“Woof!”); } public void sleep() { System. out. println(“zzz…zzz”); } public class Doggie extends Animal { String sound; public Doggie() { super(); sound = “woof”; } } public void bark() { System. out. println(“Woof!”); } }
Class Splitting Obfuscation Shortcomings n n Splitting a class very difficult unless initial design faulty May have reverse effect n Splitting a class may improve overall code design, and get rid of spaghetti code! n Might actually help the attacker, rather than deter him
Type Hiding n n Uses the concept of Java interface Transforms a concrete class into several interfaces Each interface contains a random subset of the concrete class’s methods and fields Obscures by declaring a concrete class that implements those interfaces
Type Hiding Example
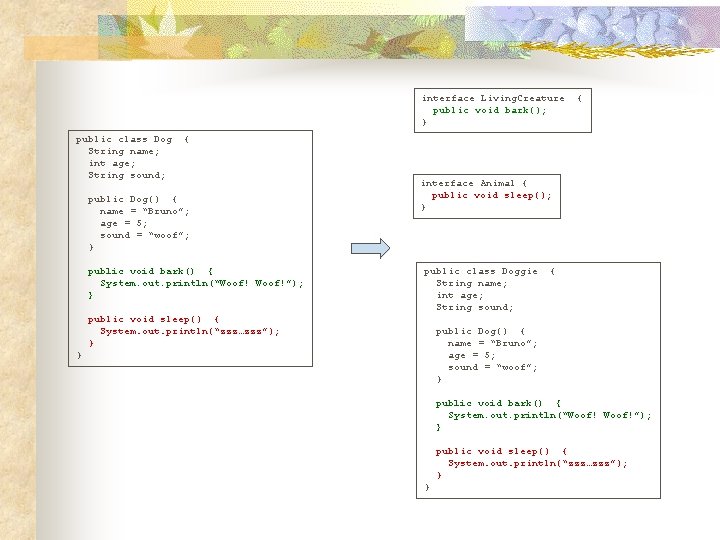
interface Living. Creature public void bark(); } public class Dog String name; int age; String sound; { { public Dog() { name = “Bruno”; age = 5; sound = “woof”; } public void bark() { System. out. println(“Woof!”); } interface Animal { public void sleep(); } public class Doggie String name; int age; String sound; public void sleep() { System. out. println(“zzz…zzz”); } { public Dog() { name = “Bruno”; age = 5; sound = “woof”; } } public void bark() { System. out. println(“Woof!”); } public void sleep() { System. out. println(“zzz…zzz”); } }
Type Hiding Shortcomings n n n Type hiding done the way described in previous slide especially vulnerable to reverse engineering More effective when combined with low -level obfuscation techniques Can be made stronger when randomly selected classes go through type hiding, instead of all classes
Obfuscation Products n n Retro. Guard by Retrologic Systems Klassmaster by Zelix JObfuscator by Duckware Semantic Designs
Conclusion n n n None of the obfuscation techniques sufficient by themselves A combination of these techniques might provide strong resistance to reverse engineering Some claim code obfuscation slows down an application Impact on performance depends on a particular technique Impact usually minimal or none at all Decision to obfuscate or not is a trade-off between protecting code or taking a slight performance hit
- Slides: 20