IW A CLOUD BASED AND CONVENTIONAL APPROACH by
IW - A CLOUD BASED AND CONVENTIONAL APPROACH by Manu Zacharia MVP (Enterprise Security), ISLA-2010 (ISC)² C|HFI , C|EH, CCNA, MCP, AFCEH, Certified ISO 27001: 2005 Lead Auditor Director – Information Security Millennium Consultants “Aut viam inveniam aut faciam ” Hannibal Barca
#whoami • I am an Information Security Evangelist • For paying my bills – I work as Director – Information Security – US Based Consultants. • Awards • Information Security Leadership Achievement Award from International Information Systems Security Certification Consortium - (ISC)² • Microsoft Most Valuable Professional (Enterprise Security) • Author of a Book – Intrusion Alert – An Ethical Hacker’s Guide to Intrusion Detection Systems
#whoami • Developed an Operating System from Linux kernel – Matriux – (www. matriux. com) - Asia’s First OS for Hacking, Forensics and Security testing – Open Source & Free • Some certifications: • Certified Ethical Hacker (C|EH) C|EH • Certified Hacking Forensics Investigator (C|HFI) C|HFI • Cisco Certified Network Associate • Microsoft Certified Professional • Certified ISO 27001: 2005 Information Security Management Systems Lead Auditor • Extend service to police force as Cyber Forensics Consultant
#whoami • Teaching? ? – no!!!!! – I don’t teach, I just train and preach: preach • Indian Navy - Signal School , Centre for Defense Communication and Electronic and Information / Cyber Warfare • Centre for Police Research, Research Pune • Institute of Management Technology (IMT) IMT – Ghaziabad • IGNOU M-Tech (Information Systems Security) – and also an Expert Member – Curriculum Review Committee • C-DAC, ACTS (DISCS (the tiger team) & DSSD (hard core guys)) • Other International Assignments & Hacking Conferences
Disclaimer(s) • The opinion here represented are my personal ones and do not necessary reflect my employers views. • Registered brands belong to their legitimate owners. • The information contained in this presentation does not break any intellectual property, nor does it provide detailed information that may be in conflict with actual Indian laws (hopefully. . . ) : )
Question • So what is Cloud Computing? • Do you know what is EC 2 and S 3? • How these services could be exploited?
contents INTRODUCTION UNDERSTANDING IW EXPLOITING THE CLOUD FORENSICS CONCLUSION
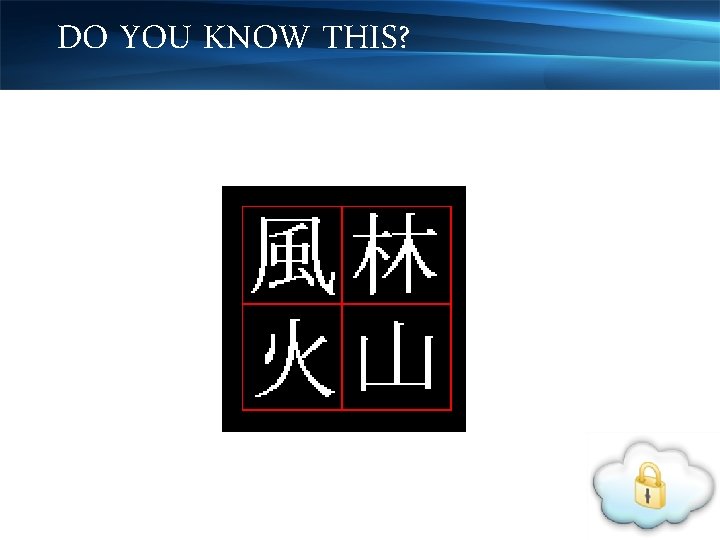
DO YOU KNOW THIS?
INFORMATION WARFARE • Clue: • Kendo (kumdo in korean)
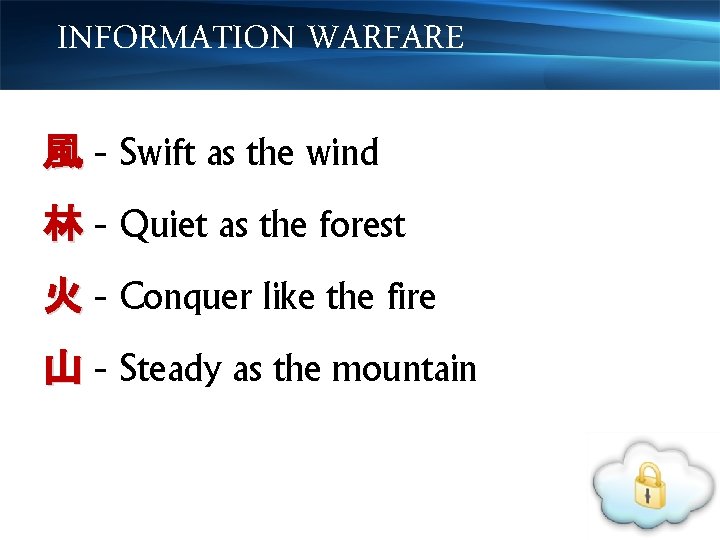
INFORMATION WARFARE 風 - Swift as the wind 林 - Quiet as the forest 火 - Conquer like the fire 山 - Steady as the mountain
INFORMATION WARFARE Battle strategy and motto of Japanese feudal lord Takeda Shingen ( 武田信玄 ) (1521– 1573 A. D. ). • • Twenty-Four Generals - famous groupings of battle commanders • (Takeda Nijūshi-shō ) 武田二十四将
INFORMATION WARFARE • Came from the Art of War by Chinese strategist and tactician Sun Tzu (Sunzi) • A sort of abbreviation to remind officers and troops how to conduct battle
INFORMATION WARFARE • This is what we need in information warfare
INFORMATION WARFARE • “actions taken to achieve information superiority by affecting adversary information, information-based processes, information systems, and computer based networks while defending one's own” • The U. S. Joint Chiefs of Staff
INFORMATION WARFARE “ Information warfare is the use and management of information in pursuit of a competitive advantage over an opponent. ” WIKIPEDIA
TWO SCHOOLS • Two schools of thoughts exists: • Military business • By some other agencies with the involvement of military

FORMS OF IW • Bringing down of financial infrastructure like banks and stock exchange • Enemy communication network spoofing and disabling • Jamming of TV / Radio • Hijacking of TV / radio for disinformation campaign
TYPES OF PLAYERS • State sponsored agencies / groups • Terrorists • Underground war-lords and groups • Individuals ‘n’ script kiddies
What’s the latest happening? • What’s happening in the Indian Web Space – last 45 days? • 14 Aug–Independence day of Pakistan • Underground cracking groups • http: //www. pakcyberarmy. net/ • http: //www. pakhaxors. com/forum. php
What’s the latest happening? • The Two Pakistani Cracker Groups reportedly attacked & defaced a dozen of Indian Websites including: • http: //mallyainparliament. in/ and • http: //malegaonkahero. com/
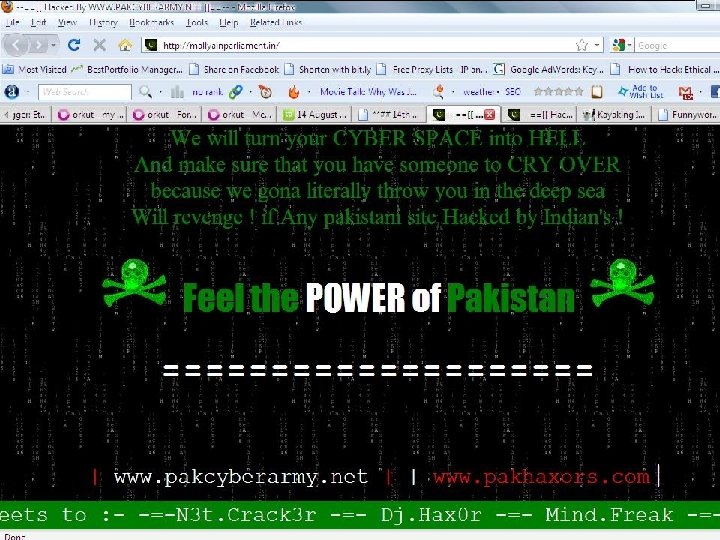
What’s the latest happening?
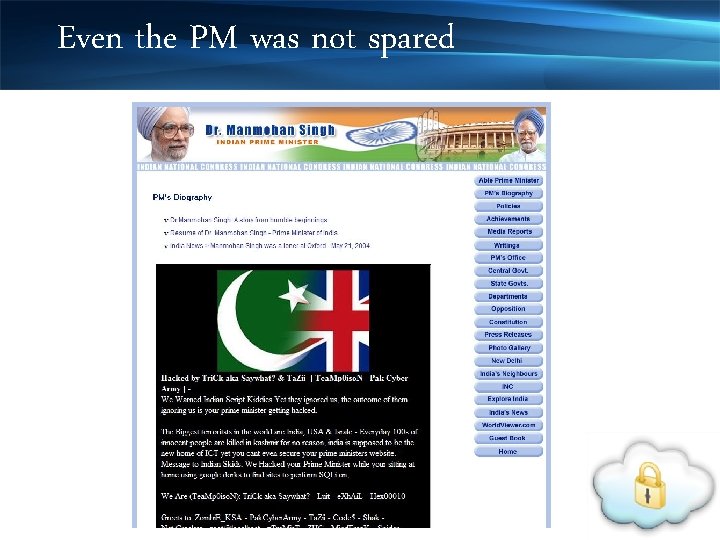
Even the PM was not spared
What’s the latest happening? • On 15 Aug – In return an Indian underground group called as Indian Cyber Army (http: //indishell. in) attacked & defaced around 1226 websites of Pakistan.
MISSION STATEMENT Mission Statement - IN • “Naval orientation and training of recruits to enable accomplishment of their immediate task with self-assurance”.
MISSION STATEMENT Mission statement – IAF • “The mission of the Flight Safety organization of the IAF is to ensure operational capability by conserving human and material resources through prevention of aircraft accidents. ”
mission
LOOK AROUND? • UK Cyber. Safe Command • PLA – Chinese PLA • What happened last December – Jan?
MANCHURIAN ATTACK
what is cloud computing? • Cloud computing is Internet-based computing, whereby shared resources, software and information are provided to computers and other devices on-demand, like a public utility.
cloud in simple terms • Uses the internet and central remote servers to maintain data and applications. • Allows consumers and businesses to use applications without installation and access their personal files at any computer with internet access.
3 types of cloud services • Iaa. S - Infrastructure-as-a-Service • Paa. S - Platform-as-a-Service • Saa. S - Software-as-a-Service
THE CLOUD Five essential characteristics: • on-demand self-service, • broad network access, • resource pooling, • rapid elasticity, and • measured service
EC 2 • Amazon Elastic Compute Cloud (Amazon EC 2) • A web service that provides resizable compute capacity in the cloud
EC 2 - wikipedia • Allows users to rent computers on which to run their own computer applications. • A user can boot an Amazon Machine Image (AMI) to create a virtual machine, which Amazon calls an "instance", containing any software desired.
EC 2 - wikipedia • A user can create, launch, and terminate server instances as needed, paying by the hour for active servers, hence the term "elastic".

S 3 • Amazon S 3 (Simple Storage Service) is an online storage web service offered by Amazon Web Services. • Provides unlimited storage through a simple web services interface
S 3 • $0. 15 per gigabyte-month • 102 billion objects as of March 2010
POWER OF CLOUD • The New York Times used Amazon EC 2 and S 3 to create PDF's of 15 M scanned news articles. • NASDAQ uses Amazon S 3 to deliver historical stock information.
EXPLOITING CLOUD • Sample Task • Break PGP passphrases • Solution • Brute forcing PGP passphrases
EXPLOITING CLOUD • Try – Elcom. Soft Distributed Password Recovery (with some patches to handle PGP ZIP) • Two elements - EDPR Managers & EDPR Agents
EXPLOITING CLOUD • On a fast dual core Win 7 box - 2100 days for a complex passphrase. • Not acceptable – too long • Lets exploit the cloud.
EXPLOITING CLOUD • First things first – Create an Account on Amazon. Credit Card Required • Install Amazon EC 2 API Tools on your linux box. sudo apt-get install ec 2 -api-tools
EXPLOITING CLOUD • Select an AMI (Amazon Machine Image) • Example - use a 32 bit Windows AMI ami-df 20 c 3 b 6 -g
EXPLOITING CLOUD • Start an instance from the Linux shell as follows: ec 2 -run-instances -k ssh-keypair amidf 20 c 3 b 6 -g default
EXPLOITING CLOUD • Once the instance is up and running, we enumerated the instance ID and public IP address of the running instance with the command ec 2 -describe-instances
EXPLOITING CLOUD • Wait for the instance status has to change from “pending” to “running” • Extract the admin password for the instance ec 2 -get-password -k ssh-keypair. pem $instance. ID
EXPLOITING CLOUD • Configure EC 2 firewall to permit inbound RDP traffic to the instance. ec 2 -authorize default -p 3389 -s $trusted_ip_address/32
EXPLOITING CLOUD • Configure the firewall in front of the EDPR manager system to permit TCP/12121 from anywhere. • RDP into the instance & configure EDPR
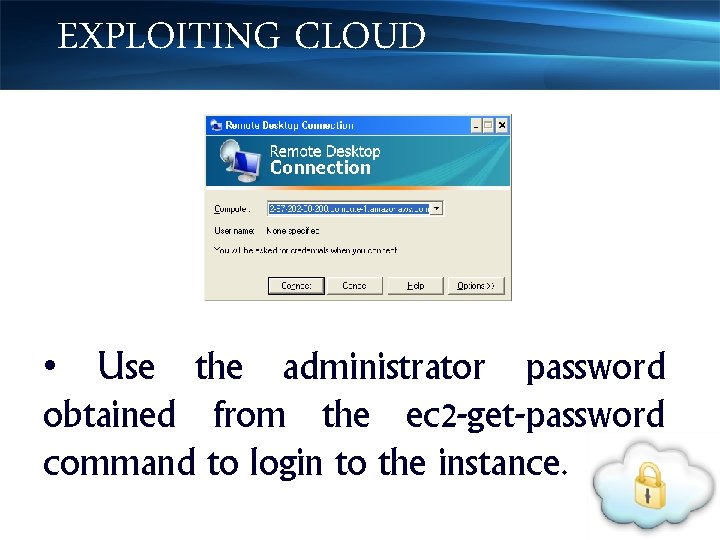
EXPLOITING CLOUD • Use the administrator password obtained from the ec 2 -get-password command to login to the instance.
EXPLOITING CLOUD • Install EDPR Agent, • Configure the Agent to connect to the Manager. • 3 points to configure mainly
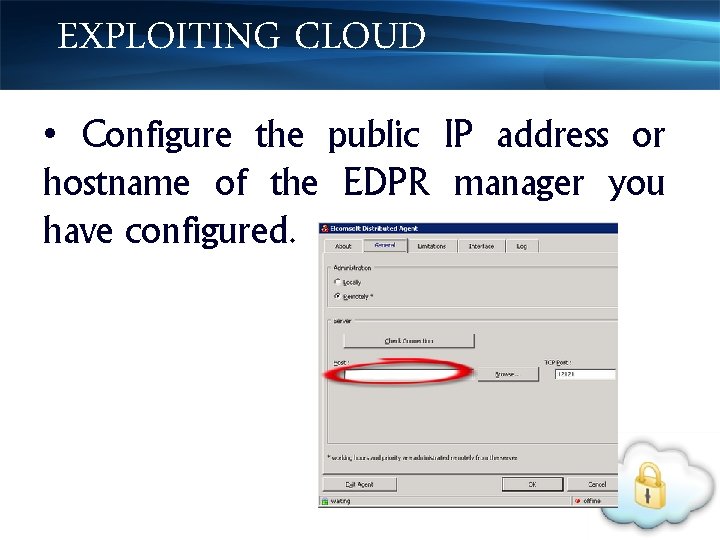
EXPLOITING CLOUD • Configure the public IP address or hostname of the EDPR manager you have configured.
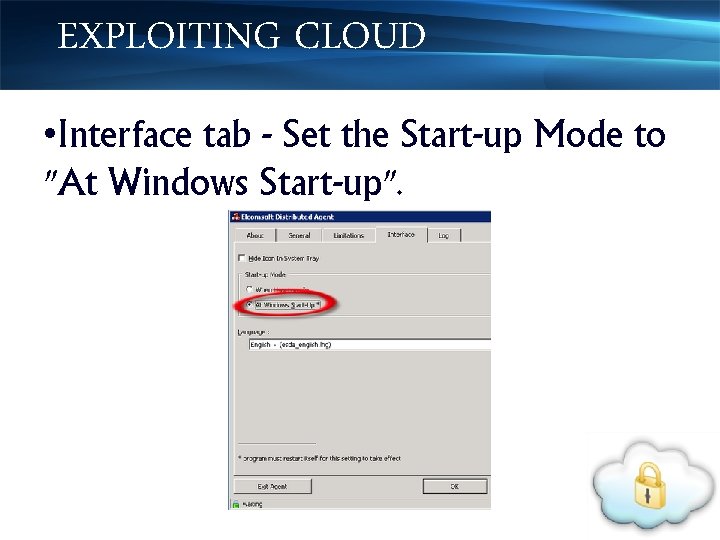
EXPLOITING CLOUD • Interface tab - Set the Start-up Mode to "At Windows Start-up".
EXPLOITING CLOUD • Registry hack • EDPR creates a pair of registry values which are used to uniquely identify the agent when connecting to the manager. • We need to scrub these values – why?
EXPLOITING CLOUD • If we do not edit, every single instance we spawn / initiate will appear to be the same agent to the manager, and the job handling will be totally corrupted.
EXPLOITING CLOUD HKEY_LOCAL_MACHINESoftwareEl com. SoftDistributed AgentUID • Set the value of the UID key to null, but DO NOT DELETE THE KEY
EXPLOITING CLOUD • Let’s bundle the EC 2 instance. • Remember in cloud, bundle is similar to creating a terminology. ‘template’ in VMware
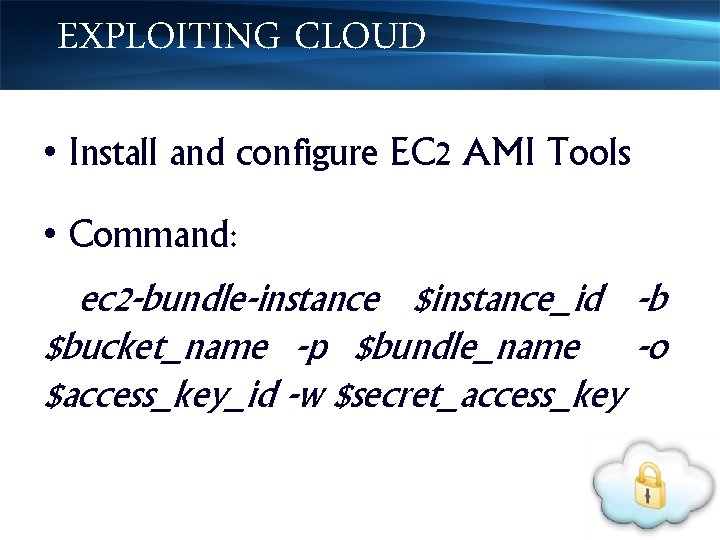
EXPLOITING CLOUD • Install and configure EC 2 AMI Tools • Command: ec 2 -bundle-instance $instance_id -b $bucket_name -p $bundle_name -o $access_key_id -w $secret_access_key
EXPLOITING CLOUD • Remember the values - we need it later to register the bundled AMI. • Bundling process runs sysprep on the Windows instance, compress and copies the instance to S 3.
EXPLOITING CLOUD • To check the progress of the bundle task, use the command: ec 2 -describe-bundle-tasks
EXPLOITING CLOUD • Register the bundled AMI, which allows it to be used to run instances: ec 2 -register $bucket_name/$bundle_name. manifest. x ml
EXPLOITING CLOUD • The register command will return an AMI ID, which we will use to spawn instances of the EDPR agent. Example: IMAGE ami-54 f 3103 d
ACTION TIME • Start the EDPR manager, and configure the task. • to brute an password composed of uppercase letters, lowercase letters, and the numbers 0 -9, with a length of between 1 to 8 characters against a PGP ZIP file.
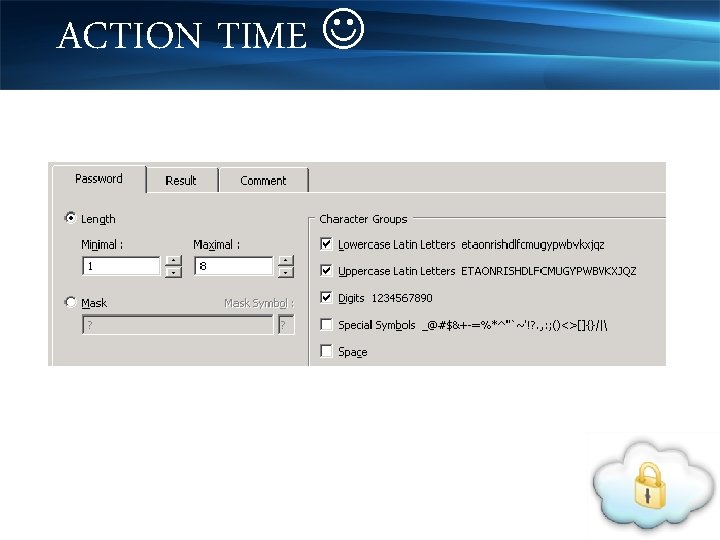
ACTION TIME
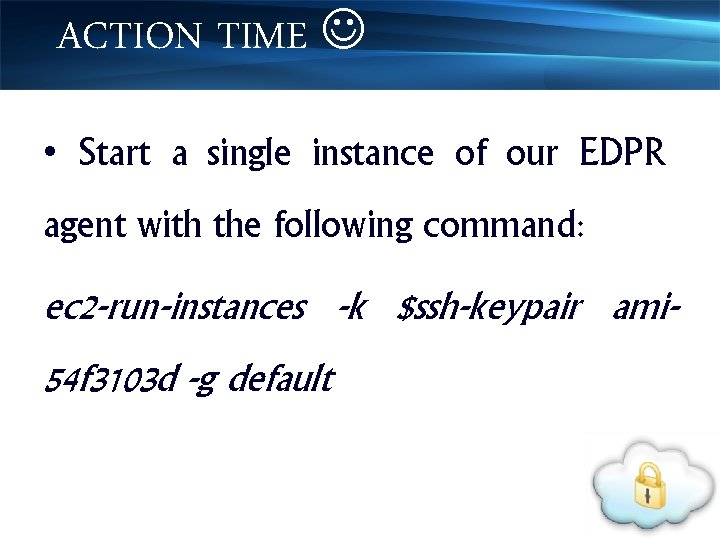
ACTION TIME • Start a single instance of our EDPR agent with the following command: ec 2 -run-instances -k $ssh-keypair ami 54 f 3103 d -g default
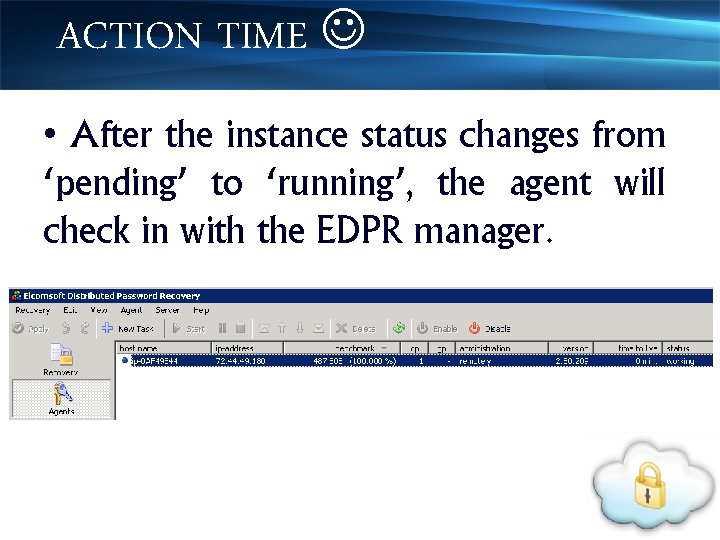
ACTION TIME • After the instance status changes from ‘pending’ to ‘running’, the agent will check in with the EDPR manager.
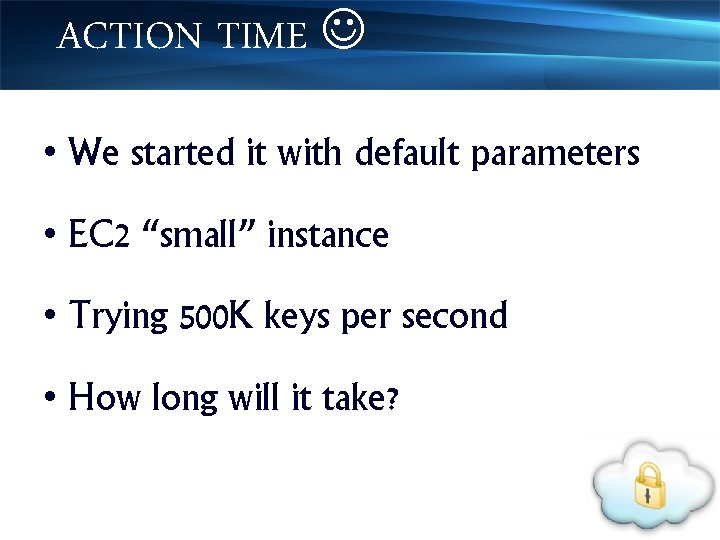
ACTION TIME • We started it with default parameters • EC 2 “small” instance • Trying 500 K keys per second • How long will it take?
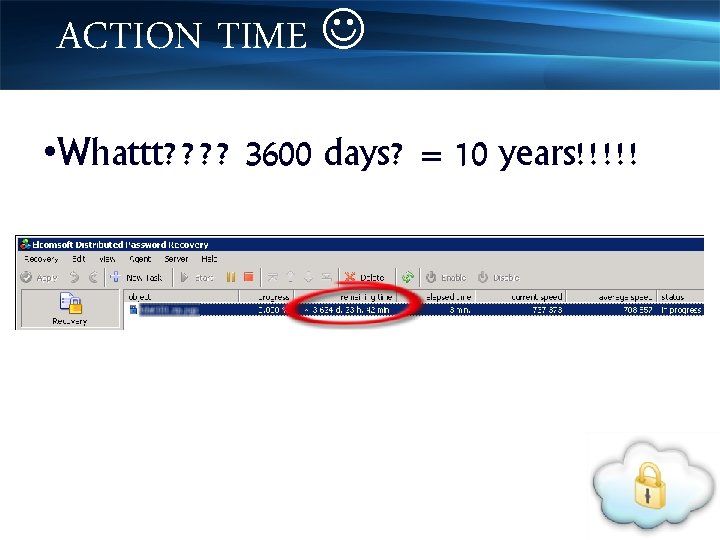
ACTION TIME • Whattt? ? 3600 days? = 10 years!!!!!
ACTION TIME • Let’s scale up – deploy 10 additional instances: ec 2 -run-instances -n 10 -k ssh-keypair ami -54 f 3103 d -g default -t c 1. medium
ACTION TIME • The -n 10 parameter tells EC 2 to launch 10 instances. • c 1. medium instance = “High CPU" instance
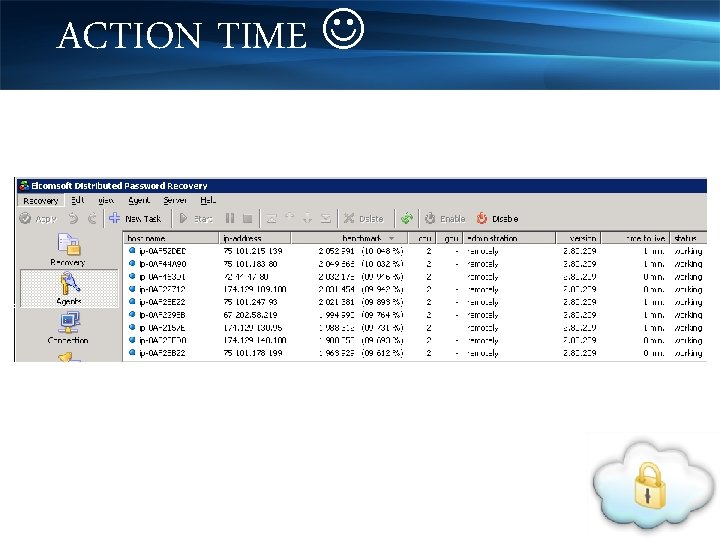
ACTION TIME
ACTION TIME • Now we have more cracking agents in the party!!! • 2+M keys/second • So what's the time required now? ? ?
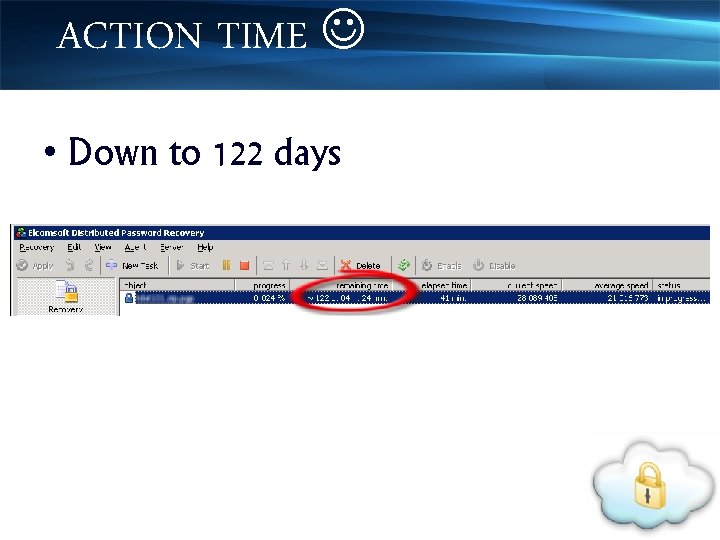
ACTION TIME • Down to 122 days
ACTION TIME • Kickoff another 89 to hit a century. ec 2 -run-instances -n 89 -k ssh-keypair ami -54 f 3103 d -g default -t c 1. medium Note: Check your EDPR License.
ACTION TIME • Error: Client. Instance. Limit. Exceeded: Your quota allows for 9 more instance(s). You requested at least 89
ACTION TIME • Option 1 • Request to instance amazon EC 2 Instance Limit http: //aws. amazon. com/contact-us/ec 2 request/ -
ACTION TIME • Option 2 • Amazon spot instances - allows us to bid on unused Amazon EC 2 capacity and run those instances.
ACTION TIME • Option 3 • Create custom python script to bypass this limitation
ACTION TIME • With a couple more of instances, we can reduce it to hours • A successful cloud based distributed cracking system.
CLOUD FORENSICS • Mixed Responses • Bad guys have started using cloud based services and infrastructure for launching attacks • Cloud do provide a good platform for incidence response and forensics investigations
CLOUD FORENSICS • By utilizing the inherent features of cloud computing, computer forensic can become an on-demand service under certain circumstances.
CLOUD FORENSICS • Regular business and operations are not affected when a cloud environment needs to be forensically examined. • Not the case with the traditional infrastructure where the equipments are seized. • Cloud Example – Amazon EBS
CLOUD FORENSICS • Cloud based forensics took a new turn when Amazon introduced Elastic Block Store (EBS) volumes • Enables the user to launch an instance with an Amazon EBS volume that will serve as the root device.
CLOUD FORENSICS • When there is a need to preserve a cloud environment, EBS can create an exact replica of the cloud instance & put it on the same cloud forensics evaluation and examination. • Since the forensic investigators will be working with another instance of the environment, the regular operations is not affected in any way.
CLOUD FORENSICS • Replication process achieved in few minutes. • Forensic evidences are invalid if they are not cryptographically hashed. • This can be easily achieved using the ondemand feature of cloud.
CLOUD FORENSICS • Replication process achieved in few minutes. • Forensic evidences are invalid if they are not cryptographically hashed. • This can be easily achieved using the ondemand feature of cloud.
CLOUD FORENSICS • The cloud based hashing takes less time and is much faster when you compare it with the traditional cryptographic hashing process. • Amazon Web Services is already providing a good forensic feature where it can provide a MD 5 hash of every file that is on the cloud system.
CLOUD FORENSICS • What this practically means is that when a bit by bit copy is initiated (forensic duplication), you have systems in place which can ensure that you made the exact replica and not even a bit has changed during the replication and copying process.
CLOUD FORENSICS • Even though you have all the above services available, cloud forensics is still challenging. • Virtualization of various entities like the applications and host systems, which once used to be in-house is now scattered on the cloud.
CLOUD FORENSICS • Makes evidence gathering a challenging task • Since we are acquiring data from a virtual environment, the forensic investigator should have a clear and precise understanding of how they work and what files are interesting and required to acquire.
CLOUD FORENSICS • Near to impossible to acquire the complete hard disk due to various reasons including but not limited to: • multiple data owners on the same disk, • remote geographical location, • jurisdictional difficulties, • RAID configurations etc
And finally • Questions also arise on the compatibility and reliability of the tools used for investigating cloud forensics - because most of the tools are meant for real time systems and not for virtualized environments. • A collaborative and collective effort is required to address what we discussed.
# forum http: //chat. theadmins. info or irc: //irc. chat 4 all. org/#theadmis 92
# contact me Manu Zacharia thank you! m@matriux. com or 93

thank you !
- Slides: 94