ITU Workshop on Countering and Combating Spam Rethinking
ITU Workshop on “Countering and Combating Spam” Rethinking Spam The Evolution of A Threat Vector Myla V. Pilao Director of Core Technology Marketing Trend Micro, Inc.

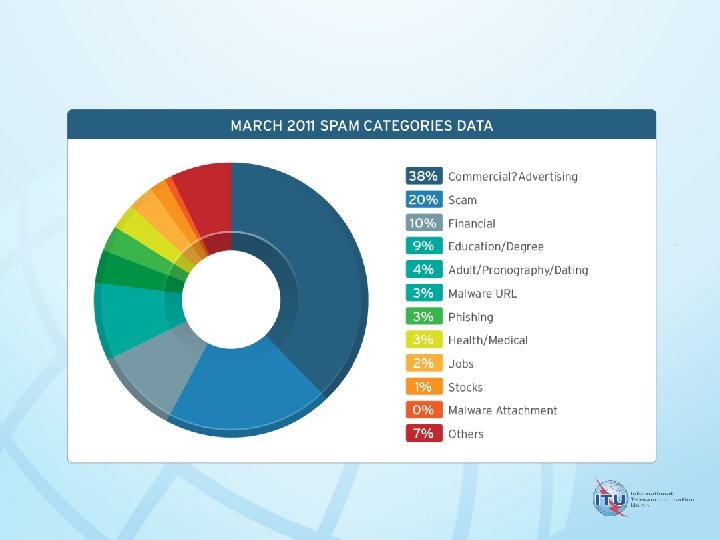
SPAM AT A GLANCE
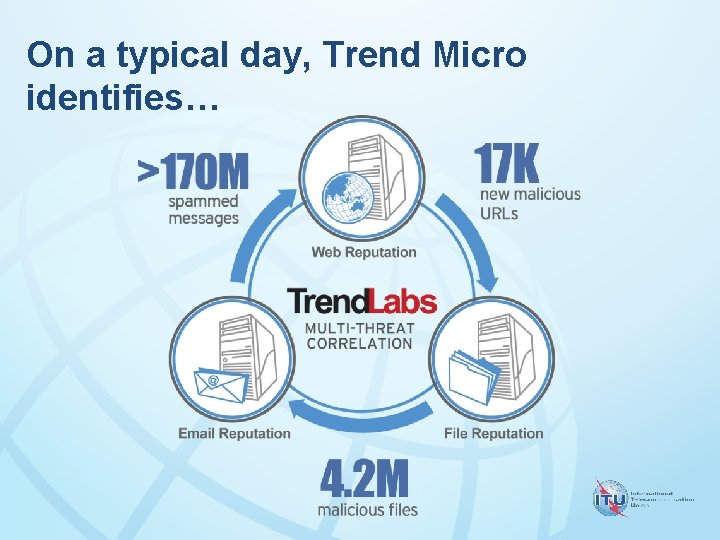
On a typical day, Trend Micro identifies…
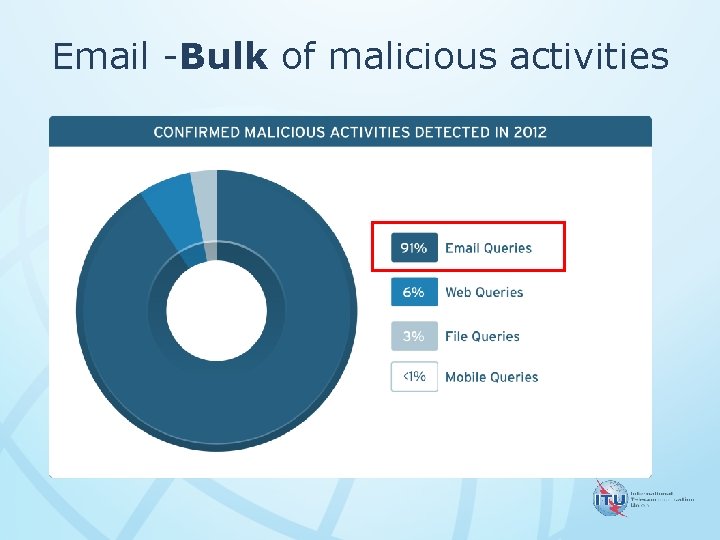
Email -Bulk of malicious activities
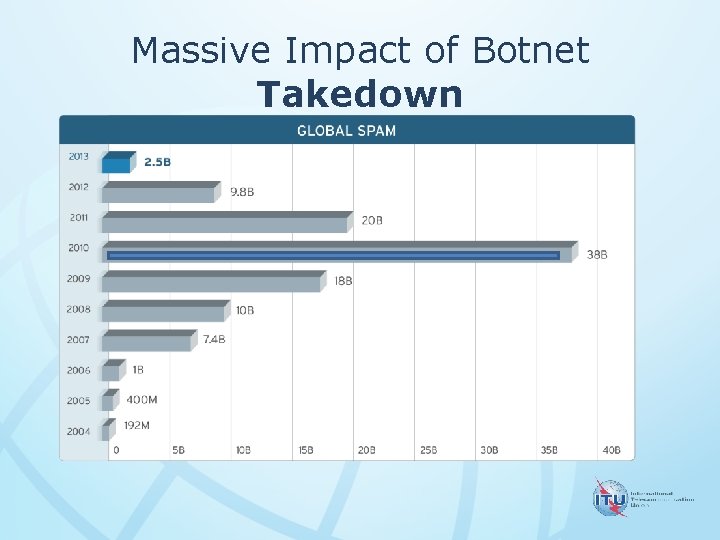
Massive Impact of Botnet Takedown
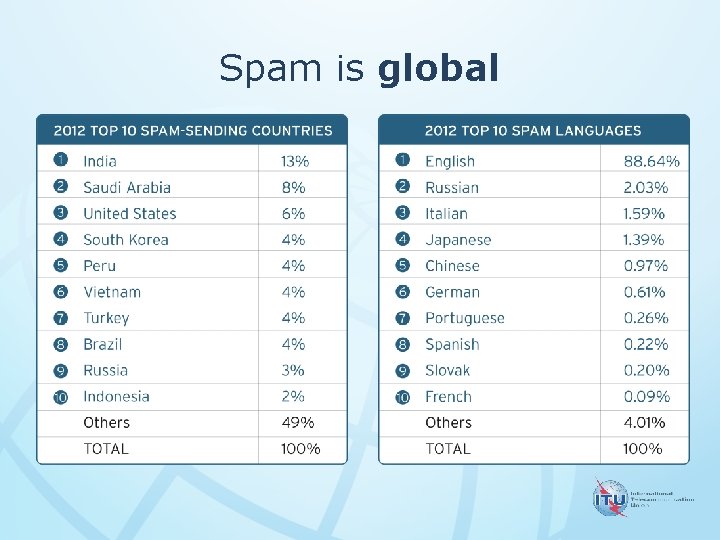
Spam is global

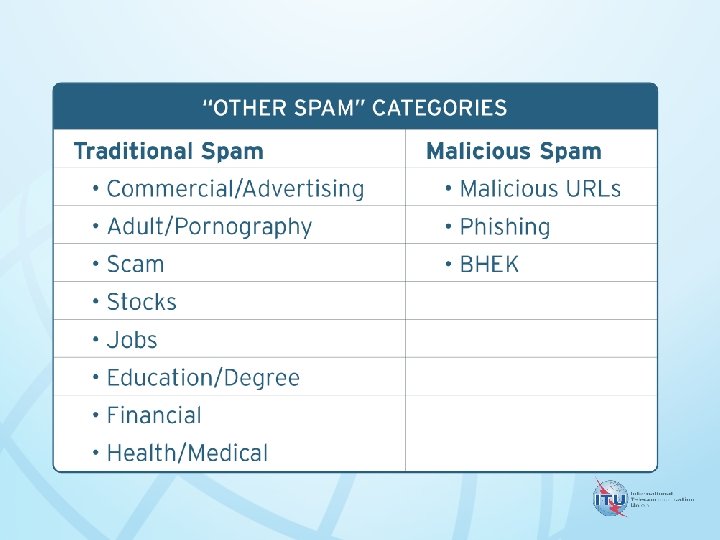
Traditional Method dominates the market

SOUTH AFRICAN THREAT LANDSCAPE
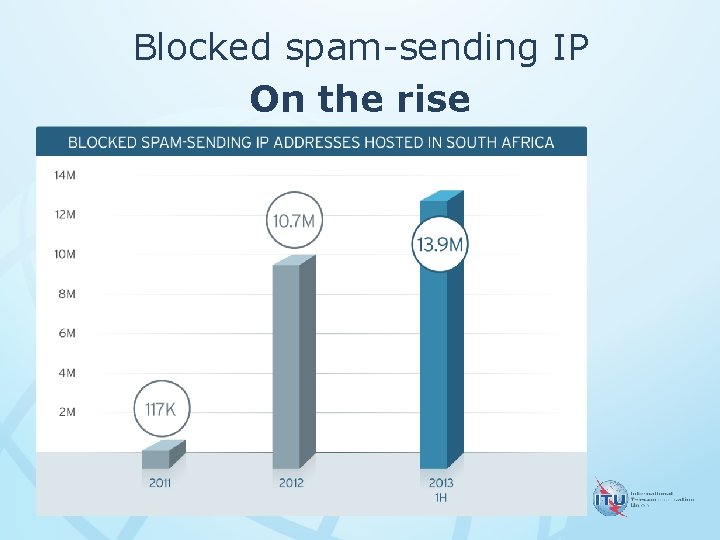
Blocked spam-sending IP On the rise
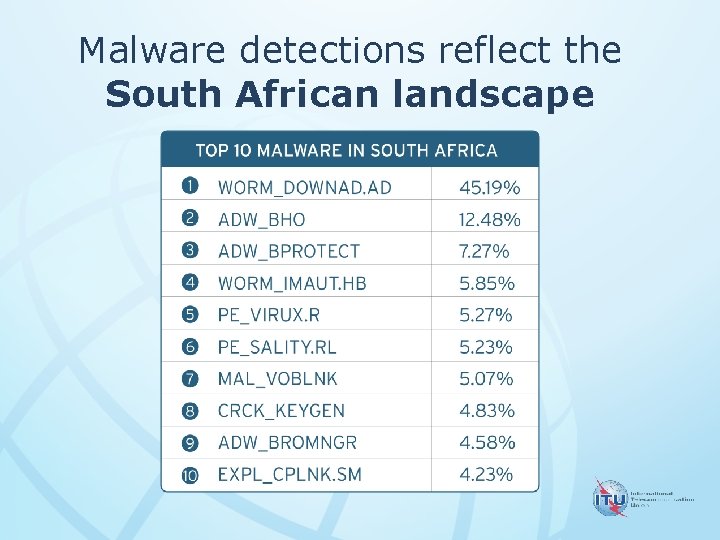
Malware detections reflect the South African landscape
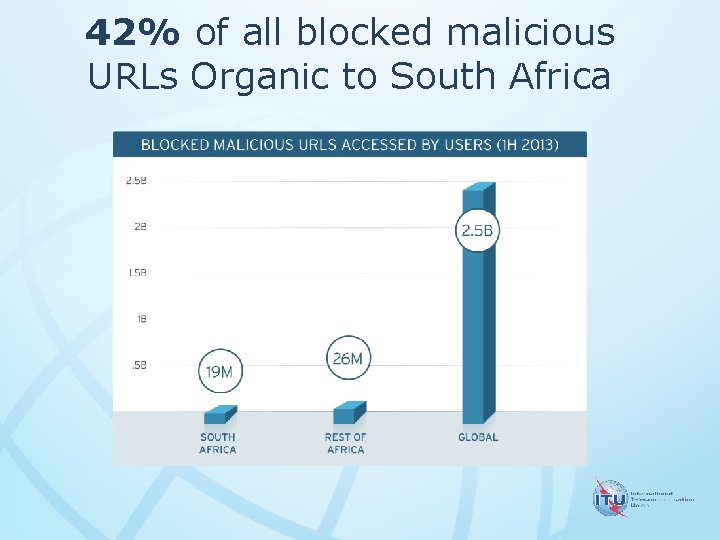
42% of all blocked malicious URLs Organic to South Africa
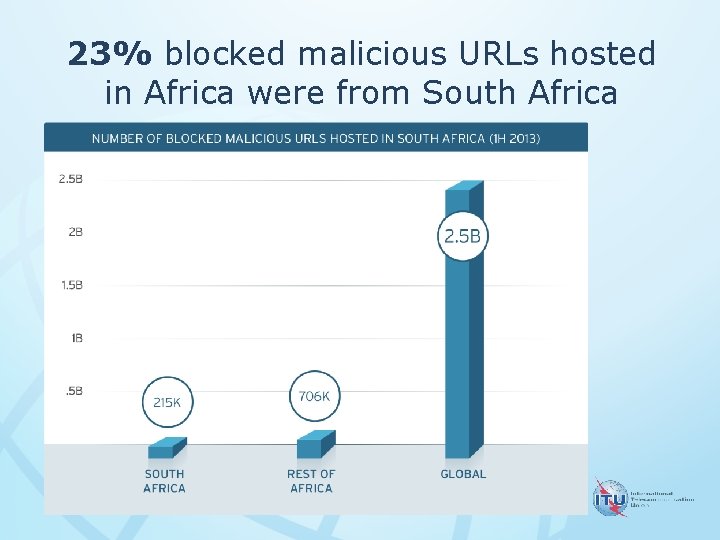
23% blocked malicious URLs hosted in Africa were from South Africa

TECHNIQUES & TRENDS
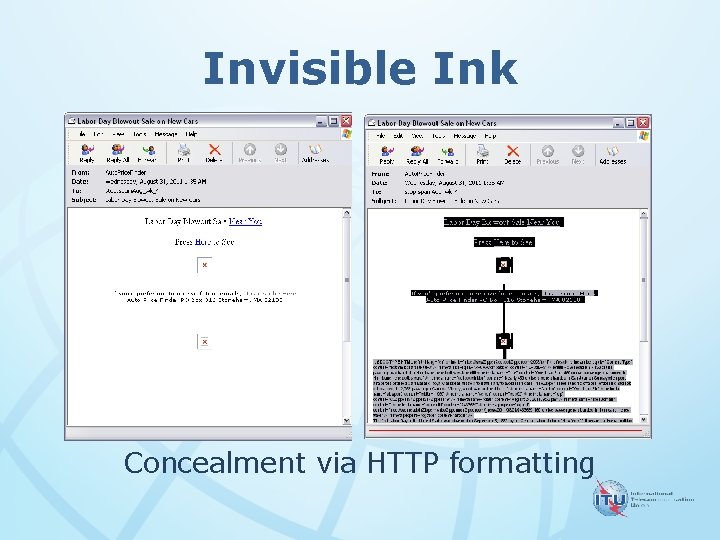
Invisible Ink Concealment via HTTP formatting
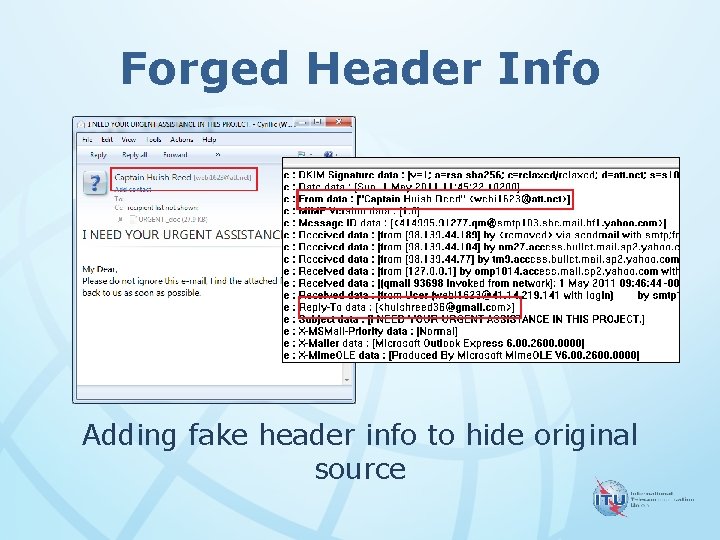
Forged Header Info Adding fake header info to hide original source
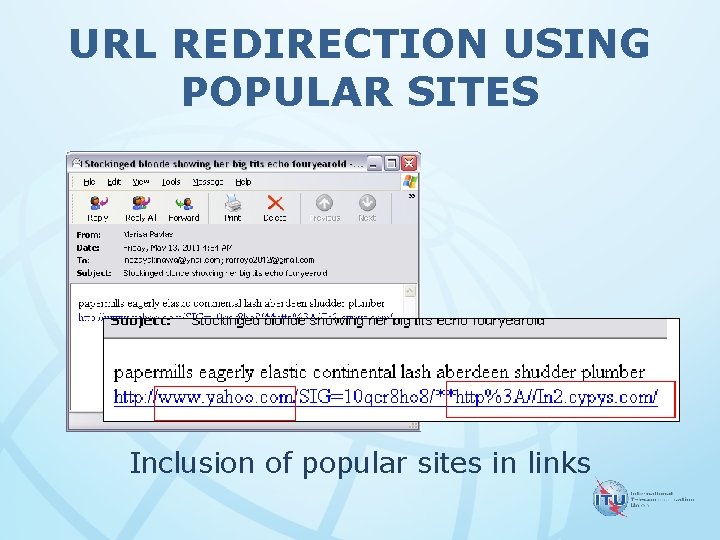
URL REDIRECTION USING POPULAR SITES Inclusion of popular sites in links
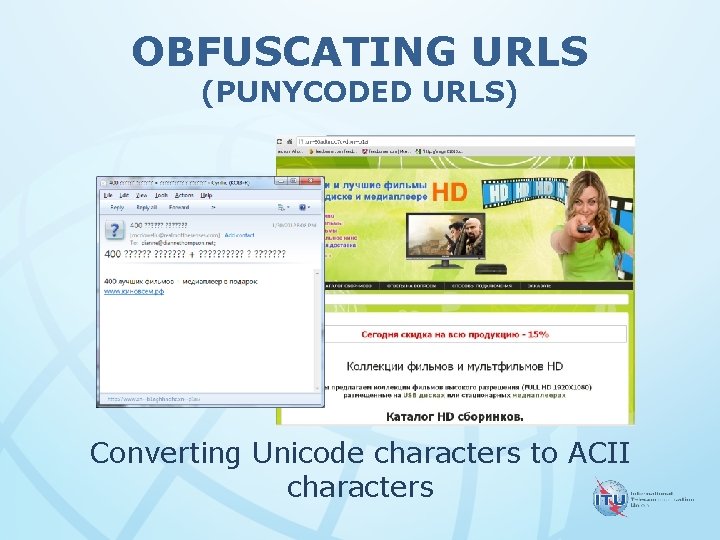
OBFUSCATING URLS (PUNYCODED URLS) Converting Unicode characters to ACII characters
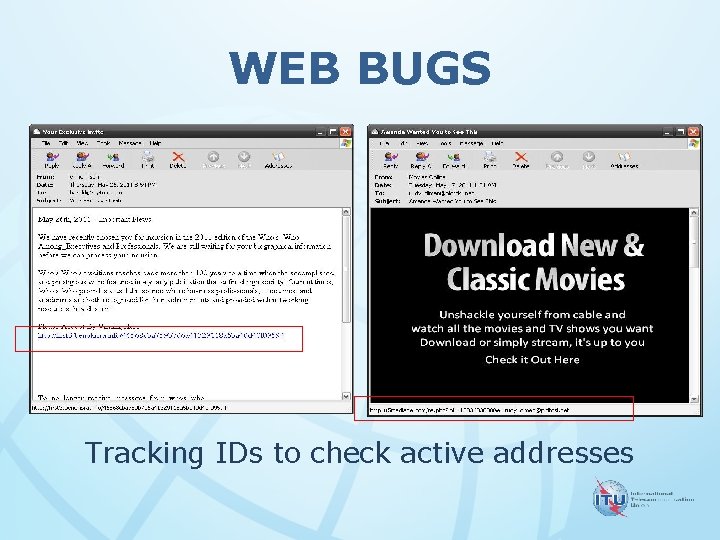
WEB BUGS Tracking IDs to check active addresses
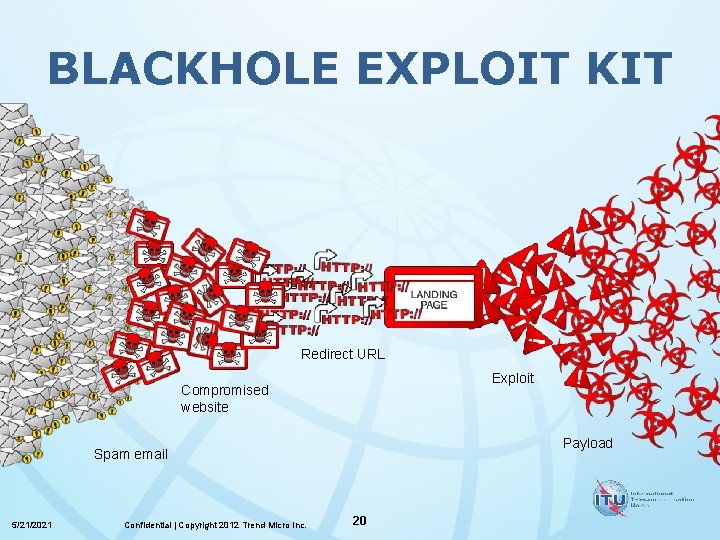
BLACKHOLE EXPLOIT KIT Redirect URL Exploit Compromised website Payload Spam email 5/21/2021 Confidential | Copyright 2012 Trend Micro Inc. 20
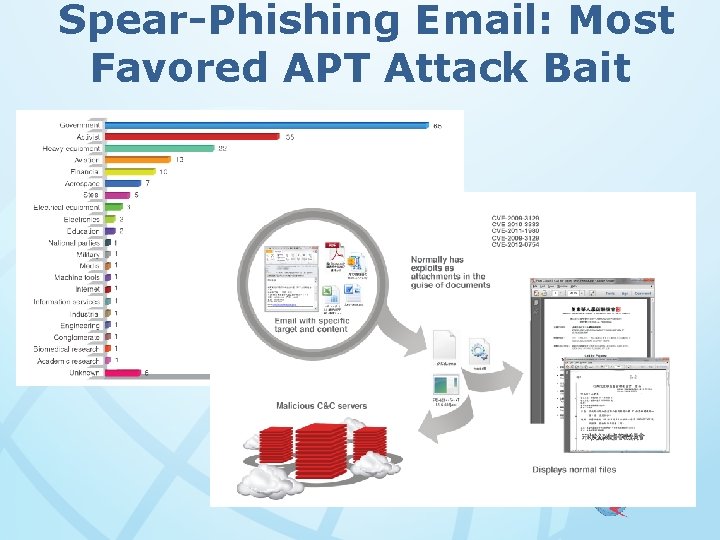
Spear-Phishing Email: Most Favored APT Attack Bait
THE CYBERCRIMINAL UNDERGROUND LINK
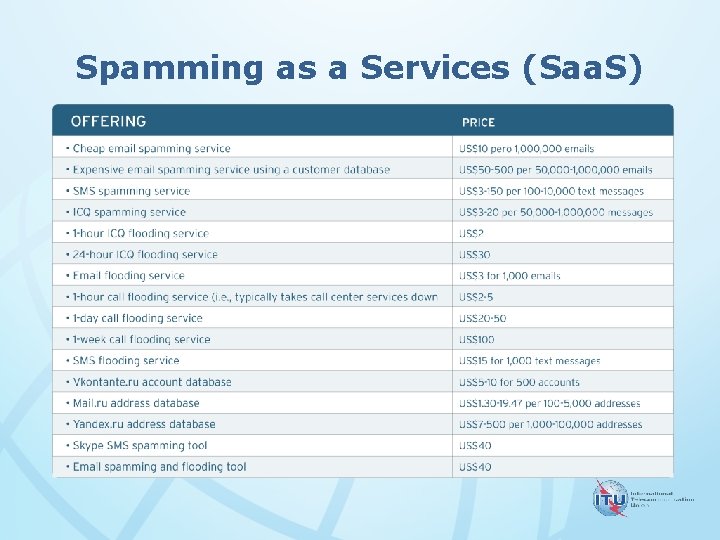
Spamming as a Services (Saa. S)

THE FUTURE OF SPAM

Africa, Security Challenges 5/21/2021 25 | Copyright 2012 Trend Micro Inc.
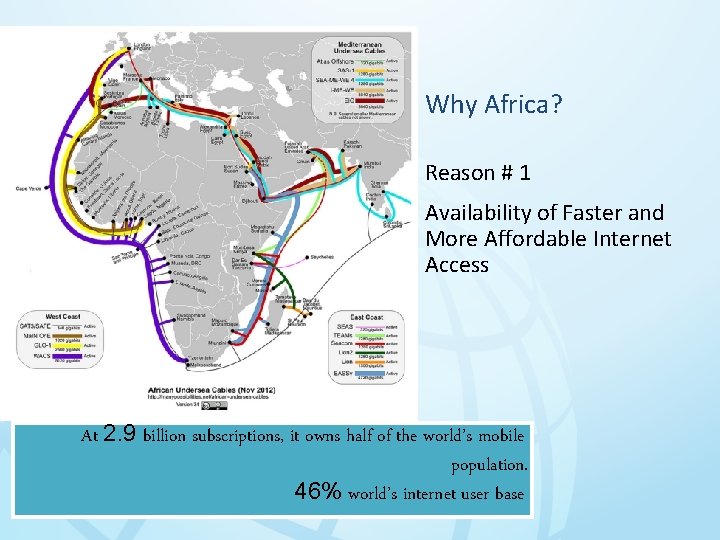
Why Africa? Reason # 1 Availability of Faster and More Affordable Internet Access At 2. 9 billion subscriptions, it owns half of the world’s mobile population. 46% world’s internet user base 26
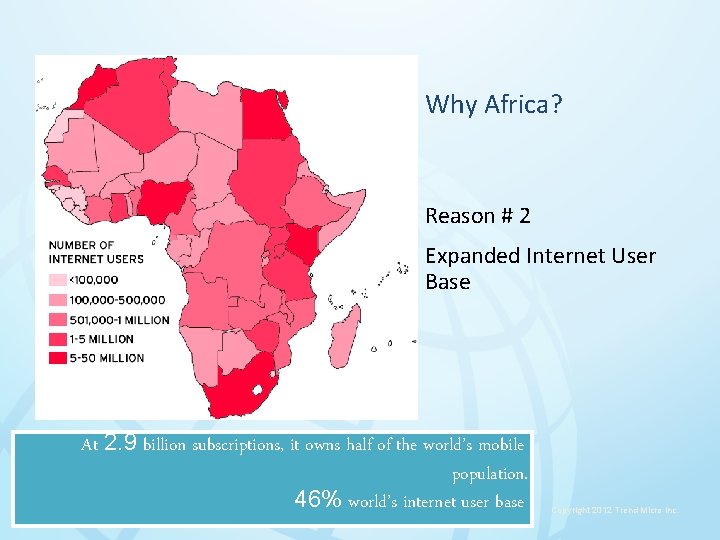
Why Africa? Reason # 2 Expanded Internet User Base At 2. 9 billion subscriptions, it owns half of the world’s mobile population. 46% world’s internet user base 27 5/21/2021 Copyright 2012 Trend Micro Inc.
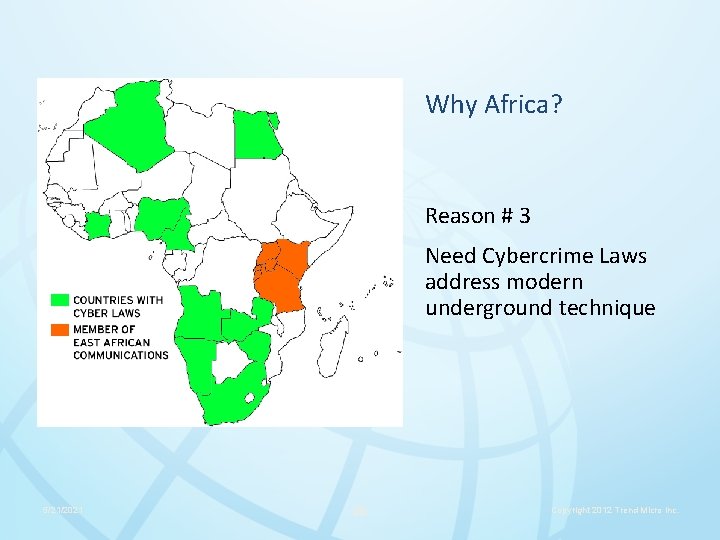
Why Africa? Reason # 3 Need Cybercrime Laws address modern underground technique 5/21/2021 28 Copyright 2012 Trend Micro Inc.
• The number of spam will continue to decrease as solution becomes basic • The number of traditional spam will decrease because of new vectors • Criminals will design highly targeted attack using customize spam • Spam will be still be “sexy” for cybercriminals

BACKUP SLIDES
- Slides: 32