ITLegal Guide to EDiscovery and ERecords GOVTECH November
IT-Legal Guide to E-Discovery and E-Records GOVTECH November 6, 2008 Jack Hupper, CIO, NYC Law Department
Our session today l What is electronic discovery? l What impact does it have on IT (whether private or governmental)? l What are e-records? And what are eretention policies? ?
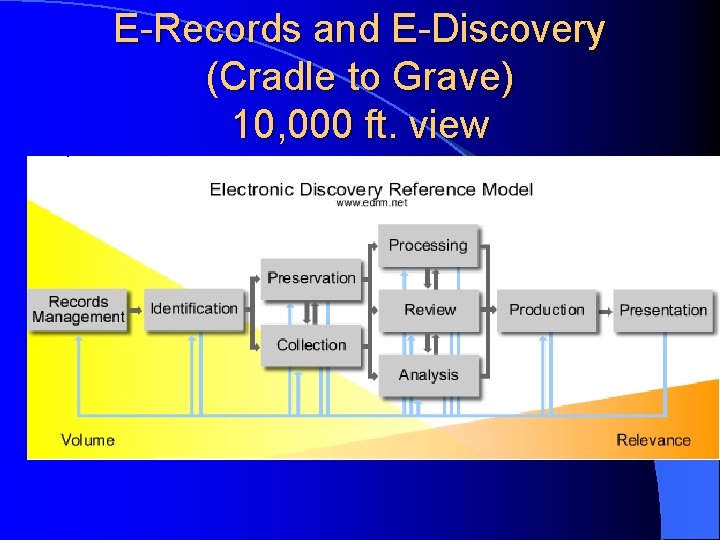
E-Records and E-Discovery (Cradle to Grave) 10, 000 ft. view
Legal Primer: Discovery l Discovery: in litigation, the exchange between adversaries of non-privileged documents relevant to the subject matter of the dispute – Common privileges: attorney-client, confidential attorney work product l FOIL (Freedom of Information Law) requests are from members of the public; litigation not necessary
Legal Primer: E-Discovery l Rules governing litigation in federal court (Fed. Rules of Civ. Pro. , or “FRCP”) changed in Dec. 2006 and made discovery of electronically stored evidence (“ESI”) far more common – Some similar trend in NYS courts l FOIL’d documents can also be electronic
FRCP Primer: IT witnesses l Because ESI is discoverable, it becomes more possible that IT staff will become witnesses (e. g. pursuant to FRCP 30(b)(6))
FRCP Primer: Initial Disclosures l Initial Disclosures & Early Meeting of Parties – ESI issues must be discussed at meet-and- confer: preservation of discoverable information; discovery of ESI, including the form(s) of production; and protection of claims of privilege or trial-preparation materials. Rule 26(f) l At least 21 days before Rule 16(b) scheduling conf. Rule 26(f)
FRCP Primer: Preservation l Initial Disclosures & Early Meeting of Parties – “preservation”: duty to preserve relevant evidence arises when a party should have known that the evidence may be relevant to future litigation. Fujitsu Ltd. v. Federal Express Corp. , 247 F. 3 d 423, 435 (2 d Cir. 2001). l l l Defendant has notice of foreseeable litigation at time of complaint and sometimes earlier Plaintiff foresees litigation well before service of complaint Preservation (“litigation hold”) notice – – – To whom (besides IT)? Who are custodians? Preserve what? PSTs on custodians’ hard drives; is PC slated for reformatting? Stop overwriting backup tapes? Any particularly ephemeral ESI? VM? ? Employee deleting email/files of work computer?
FRCP Primer: Extent of Production l Extent of Production – Rules 26(b)(2)(B) and 45(d)(1)(D) – “Undue burden”: “A party need not provide discovery of [ESI] from sources that the party identifies as not reasonably accessible because of undue burden or cost…. If [such] showing is made, the court may nonetheless order discovery from such sources if the requesting party shows good cause … The court may specify conditions for the discovery. ’ Rule 26(b)(2)(B) l “Good cause” to order production of inaccessible information: Advisory Committee factors: “(1) the specificity of the discovery request; (2) the quantity of information available for other and more easily accessed sources; (3) the failure to produce relevant information that seems likely to have existed but is no longer available on more easily accessed sources; (4) the likelihood of finding relevant, responsive information that cannot be obtained from other, more easily accessed sources; (5) predictions as to the importance and usefulness of the further information; (6) the importance of the issues at stake in the litigation; and (7) the parties’ resources. ” – Re parties resources: note “deep pocket” defendants
FRCP Primer: Sanctions
FRCP Primer: Sanctions – Sanctions can be severe; e. g adverse inference jury instruction; i. e. that the jury may infer that the lost ESI would have been unfavorable to the sanctioned party. (Zubulake) – Sanctions can be on counsel: failure to oversee client, who (even as an apparent power user) did not realize there were parts of the file server other than his network share. (Phoenix Four v. Strategic Resources Corp. , 2006 U. S. Dist. Lexis 32211 (SDNY 2006))
FRCP Primer: Sanctions l Rule 37(f)’s “safe harbor”: “Absent exceptional circumstances, a court may not impose sanctions under these rules on a party for failing to provide [ESI] lost as a result of the routine, good faith operation of an electronic information system. ”
![FRCP Primer: Sanctions l “[ESI] lost as a result of the routine, good-faith operation” FRCP Primer: Sanctions l “[ESI] lost as a result of the routine, good-faith operation”](http://slidetodoc.com/presentation_image_h2/4c7340923b862df79379f47c63cc8af5/image-14.jpg)
FRCP Primer: Sanctions l “[ESI] lost as a result of the routine, good-faith operation” – Committee Notes cite as factors: Steps taken to implement litigation hold; accessibility of system; whether party should have known of loss; and whether unavailable from any other source. – High-value case: set aside backup tape, forensic copy, etc. ? l Set aside all backup tapes? ? – “Whether good faith would call for steps to prevent the loss of information on sources that the party believes are not reasonably accessible under Rule 26(b)(2) depends on the circumstances of each case. One factor is whether the party reasonably believes that the information on such sources is likely to be discoverable and not available from reasonably accessible sources. ” Committee Note on Rule 37(f).
Basic e-records problem: how to organize e-documents of all kinds in a way that: l helps users get their work done; l is supportable by IT; l yet allows automated destruction at end of scheduled period (unless interrupted by a litigation hold), to take advantage of FRCP 37(f)’s safe harbor; l and allows for economical review and production in the litigation
Basic e-records problem: how to organize electronic documents of all kinds (con’t) l It’s VERY hard
Basic e-records problem: how to organize electronic documents of all kinds (con’t) l Holy grail: all docs re particular subject go in a particular bucket – Users find easily (KM happy) – RM age out – Litigators can effectively hold & review/produce; could save HUGE amount of money
Basic e-records problem: how to organize electronic documents of all kinds (con’t) l BUT: – Email Inboxes are an undifferentiated mess l Email not a record “type” – Email folders differently defined & generally not shared – Files: same – Different people see subjects differently (operational vs. HR vs. contract)
Worst problem: E-mail retention “… the management of email is sometimes characterized as the single biggest records management problem in the USA. ” Sedona Guidelines, Best Practice Guidelines & Commentary for Managing Information & Records in the Electronic Age
Sample Retention Policies NYS Archives Schedule MI-1 l “General” retention schedule, broadly applicable, has 37 different series, many with subparts l IT Division records (e. g. help desk records) have about 42 different series, many with subparts l Widely varying periods (0 to permanent) l Varying kinds of dates to start period running (creation date; completion of contract performance; grievance resolution date)
Sample retention policies (con’t): Email “Managing Email Effectively”, NYS Archives, 2002 l Generally appears to contemplate treating email with same retention series as paper (“media neutrality”) -- i. e. by subject – “Generally, specific e-mail records will have the same retention periods as records in other formats that are related to the same program function or activity. Before you can identify the retention period of a particular set of e-mail messages, you must identify what type of record the e-mail actually is and which records series it falls under. ”
Sample retention policies (con’t): Email “Managing Email Effectively”, NYS Archives, 2002 l Distinguish email which is non-record – Most received email (they’re duplicates of Sender’s original) – Sent email when not related to official business: social/party; jokes – Drafts since not “final record” l Some record email can be deleted while still on email server (e. g. Exchange); short useful lifetime of “Internal Information Records” – calendars of appointments, office and travel schedule, memoranda and routing slips, routine internal reports, reviews and plans, used solely to disseminate information or for similar administrative purposes
Sample retention policies (con’t): Email Nevertheless leaves high volume of Sent email (and incoming email from outside your organization) which are records and which have retention periods long enough that they can’t be kept on email server. l Query: Will users comply with a policy that they manually classify all that email by subject, even assuming they would have complied at 2002’s email volume? l Query: Are users going to understand the differences among dozens of record series, and thus be able to choose the correct record series “bucket”? l Query: Where do users store the email outside mailboxes for the extended periods? l Query: What IT system determines that particular emails are of a particular record series, that the retention period has elapsed, and thus the emails are ready for deletion?
Email retention policy strategy #1: retain by email subject This is the method “Managing Email Effectively” contemplates. But, over short run, where to retain email outside Exchange mailbox? l Print to paper? l Save as. MSG files in directories corresponding to record series on shared drives? – User concerns re confidentiality l Save to Exchange public folders, corresponding to record series? – Security rights set to allow just author to view – Public folder periodically PST’d to portable drive. At end of retention period, drive wiped or destroyed.
Email retention policy strategy #2: retain by role of mailbox owner l Example: Enterprise Vault (“KVS”) from Symantec/Veritas – Archive (e. g. to reduce size of Exchange db) – Competitors include: Zantaz; Mimosa; Email. Xtender (EMC Legato); EAS (Exchange Archive Solution); Comm. Vault l Set archive to retain email of HR staff X years, Procurement staff Y years, etc. – Little/no user work required – Very rough classification scheme
Email retention policy strategy #3: retain by format of record (i. e. email) l Example: All email deleted from mailbox after 180 days – Little/no user work required – Very rough classification scheme – Still have problem of saving email somewhere outside mailbox if need for particular emails exceeds 180 days
Email retention policy strategies: recommendations? l Very little case law guidance l Gartner: any reasonable policy as long as you stick with it l Sedona: appears to recommend by contentbased policy (as with paper; “media neutral”), but also says you can take IT environment into account
Email and Document Retention Policies: Long Run Best long run solution may be DMS/RMS combination l DMS adds value to user l – Can collaborate more easily – Google-like searching for own and others’ documents; foundation of KM l DMS containers can be foundation for retention policies managed by RMS – At end of container’s retention period, RMS deletes container and documents within it l Exchange 2007 managed folders
Let’s be friends l Lawyers and IT should make friends well in advance Very different cultures Both concerned with fire-fighting, but very different kinds of fires Many litigators don’t understand difficulty of running an enterprise IT doesn’t always understand need to support litigation; still new Lawyers should ask (nicely) to see network diagrams, data centers, understand architecture – IT should learn more about e-discovery obligations – – –
Resources l l l l Gartner: “What IT Managers Should Do About Compliance”, May 16, 2007 (G 00147735) Gartner: “What Every CIO Needs to Know about E-Discovery”, December 1, 2005 (G 00131055) Gartner: “How to Formulate an E-Mail Retention Strategy”, May 15, 2006 (G 00138146) Sedona Guidelines, Best Practice Guidelines & Commentary for Managing Information & Records in the Electronic Age (Sept. 2005; at www. The. Sedona. Conference. org) E-Discovery Road Map, at http: //www. law. com/jsp/legaltechnology/e. Discovery. Roadmap. jsp “Managing Email Effectively”, at http: //www. archives. nysed. gov/a/nysaservices/ns_mgr_pub 62. shtml NYS Archives Schedule MI-1, at http: //www. archives. nysed. gov/a/nysaservices/ns_mgr_pub_mi 1_part 2. shtml
Questions? l Opinions my own l Thank you! Jack Hupper CIO New York City Law Department jhupper@law. nyc. gov
- Slides: 31