ITIS 61678167 Network and Information Security Weichao Wang





- Slides: 41
ITIS 6167/8167: Network and Information Security Weichao Wang
Contents • ARP protocol and ARP poisoning – How ARP works – ARP poisoning – Security impacts – Mitigation mechanisms • IP fragmentation and attacks – IP fragmentation – Attacks – Mitigation mechanisms 2

3
Ethernet address • Layered model of Internet • Separation of IP address and physical address • How does IP routing works – Example 4
• IP address – 32 bits (IPv 4) • Ethernet address – 48 bits – Different hardware vendors get different chunk of addresses – Can be broadcast or unicast address – Mapping b/w IP and Ethernet address can change 5
• IP routing needs the mapping b/w IP addresses and physical addresses – Static mapping (pro. NET or token ring) • Physical address = f (IP address) – Dynamic binding • More flexible • Needs a protocol to accomplish this task – Address Resolution Protocol (ARP) 6
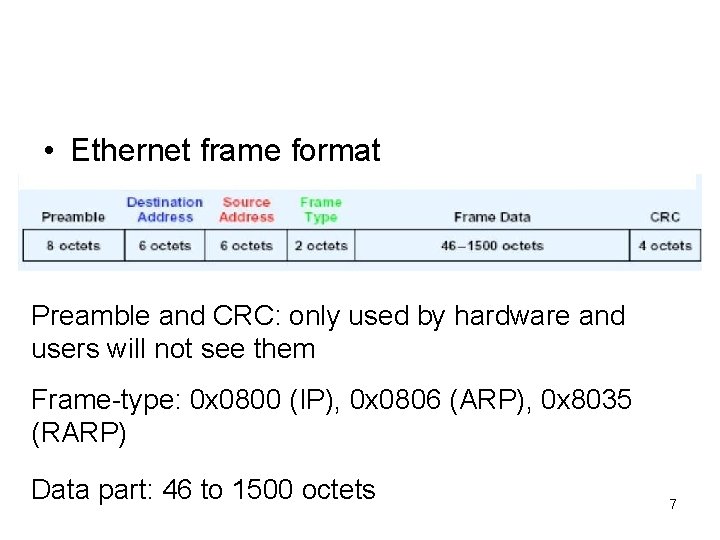
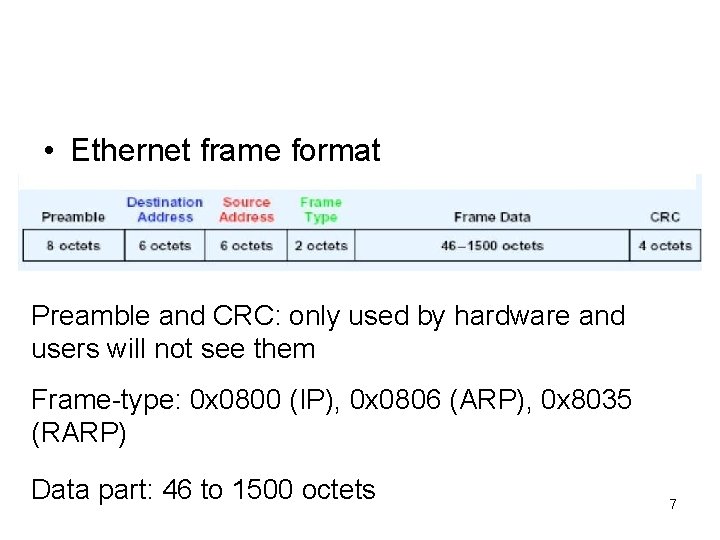
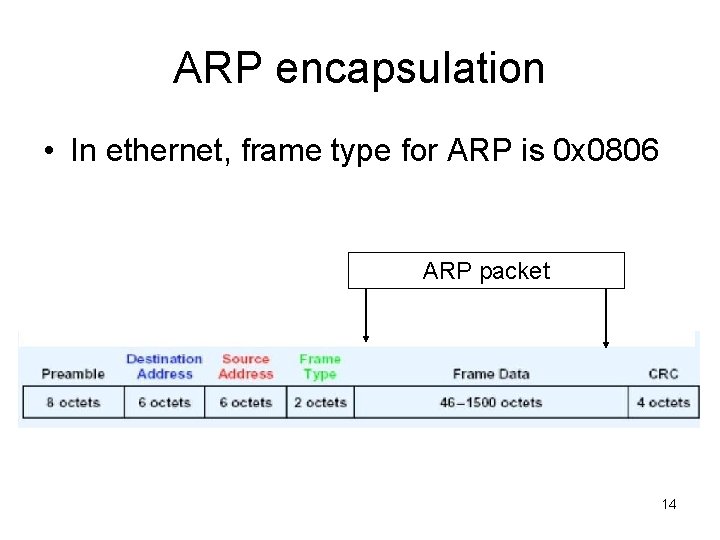
• Ethernet frame format Preamble and CRC: only used by hardware and users will not see them Frame-type: 0 x 0800 (IP), 0 x 0806 (ARP), 0 x 8035 (RARP) Data part: 46 to 1500 octets 7
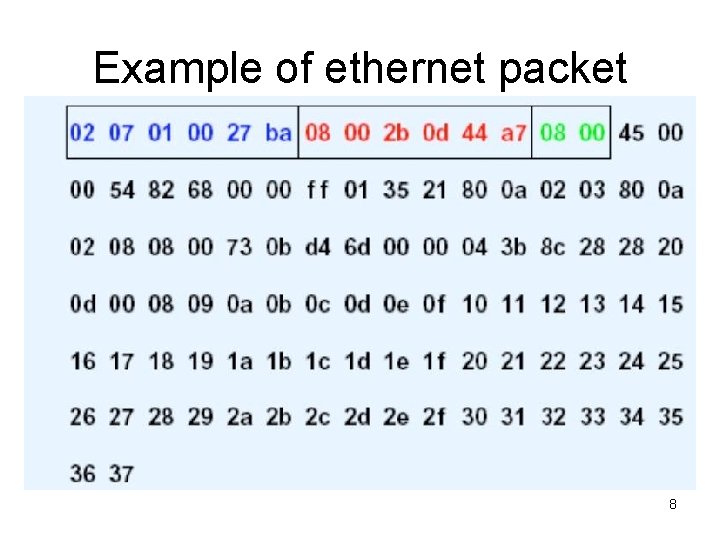
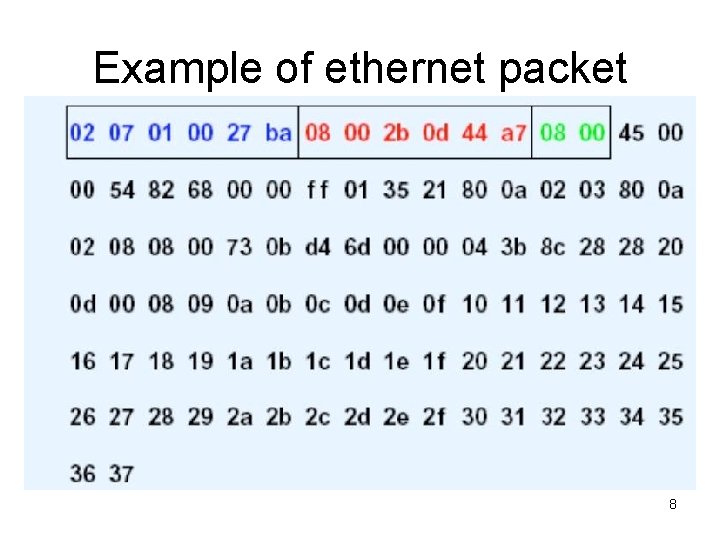
Example of ethernet packet 8
• Destination physical address: 02 07 01 00 27 ba • Source physical address 08 00 2 b 0 d 44 a 7 • Protocol type: 0800 (IP) • More details of the packet: this is an ICMP packet 9

10
ARP protocol • Motivation – Ethernet card only needs to recognize ethernet address – Upper layer (IP) only knows IP address – Routing table entry – The user have to map the IP address to physical address 11
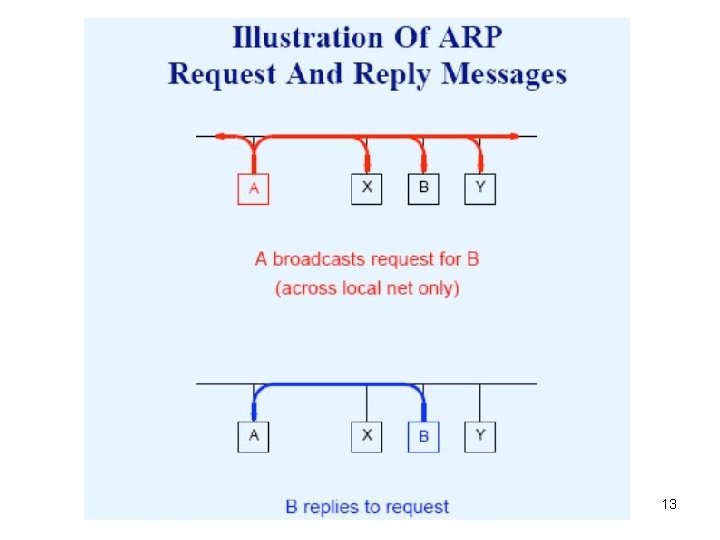
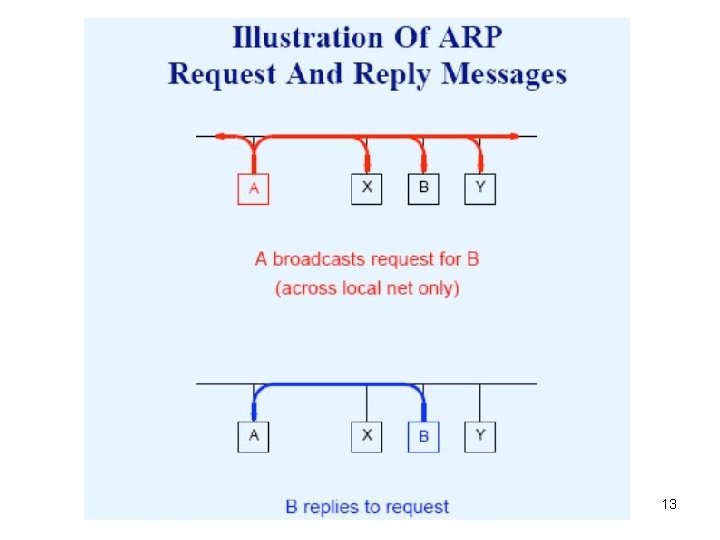
• ARP protocol – Machine A want to send a packet to B, but only know B’s IP address – Machine A broadcast an ARP request with B’s IP address (using broadcast physical address) – All nodes receive the request – B replies with its physical address – Machine A adds the address into its ARP cache – A sends packets to B 12
13
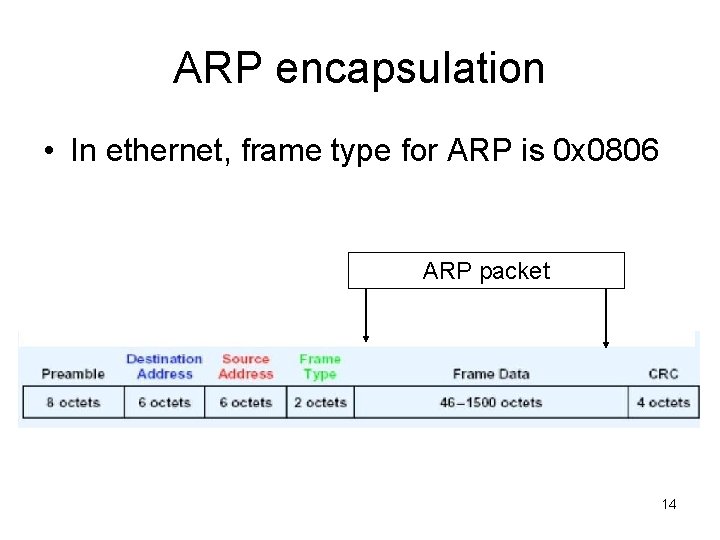
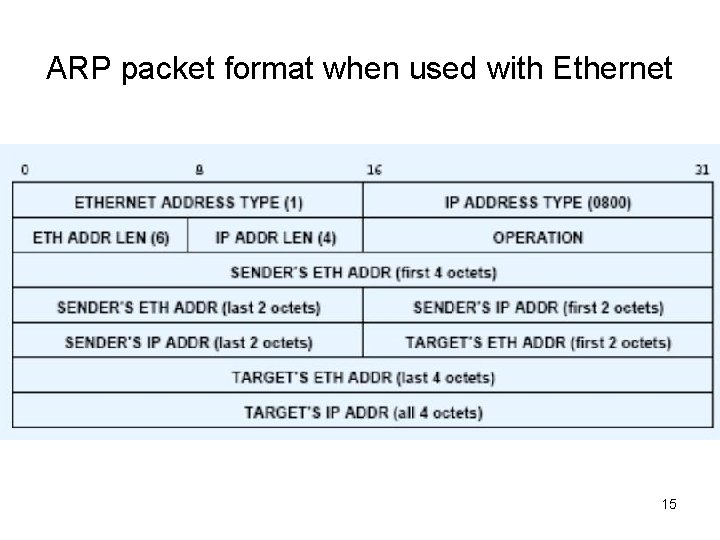
ARP encapsulation • In ethernet, frame type for ARP is 0 x 0806 ARP packet 14
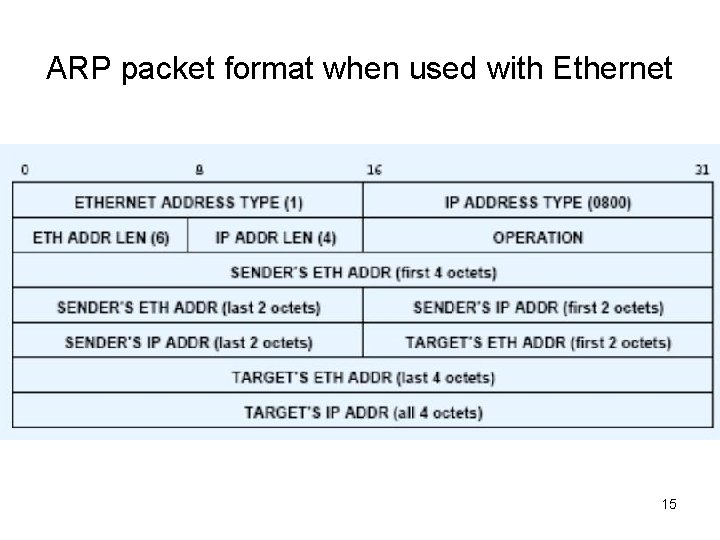
ARP packet format when used with Ethernet 15
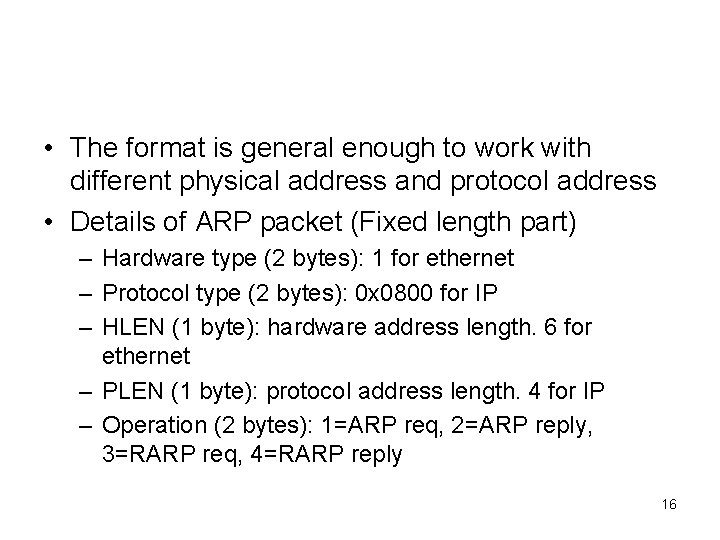
• The format is general enough to work with different physical address and protocol address • Details of ARP packet (Fixed length part) – Hardware type (2 bytes): 1 for ethernet – Protocol type (2 bytes): 0 x 0800 for IP – HLEN (1 byte): hardware address length. 6 for ethernet – PLEN (1 byte): protocol address length. 4 for IP – Operation (2 bytes): 1=ARP req, 2=ARP reply, 3=RARP req, 4=RARP reply 16
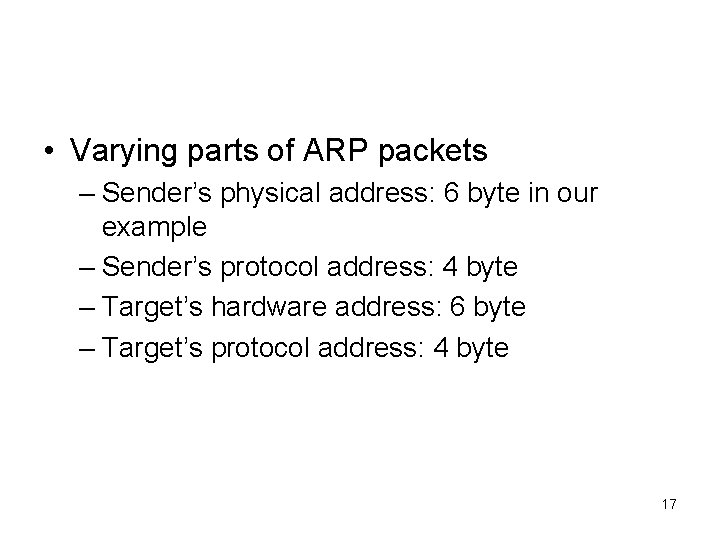
• Varying parts of ARP packets – Sender’s physical address: 6 byte in our example – Sender’s protocol address: 4 byte – Target’s hardware address: 6 byte – Target’s protocol address: 4 byte 17
• ARP cache – To reduce ARP overhead, the machine keeps a cache for recently got IP-PHY address mapping – Cache has a limited size: replacement policy – ARP entry has a lifetime: why do not we keep it forever? ? 18
• How does the node learn ARP information – From received ARP request – From received ARP reply (no matter they have sent a ARP request or not) (depend on OS) – Gratuitous message: both the source and destination address are the same • Used to detect IP conflict • When physical address changes, use this to notify other nodes after reboot 19

20
ARP poisoning • Potential attack to ARP – There is no protection on the mapping b/w Physical and IP address – An example attack: if ARP cache is poisoned, the packet going to node A will be sent to Node B’s physical address, and node B will get them. – Is this the same as promiscuous mode? Not really 21
• Two simple and not-so-effective MAC address attacks – Poison a switch by sending out an ethernet packet with the target’s physical address as the source of the packet. The switch tries to learn from the packet. – Problems • The real node also sends out packet • Static configuration of switches 22
• Attack 2: – Sends out ARP reply and tries to beat the real node – Problem: the conflict is relatively easy to detect 23
• ARP cache poisoning – Through ARP poisoning, the packets targeting at node A may be sent to node B – Methods to poison ARP cache • ARP request • ARP reply • Gratuitous packets – Instead of broadcast, we can use unicast to poison node 24
• Examples of attacks – Send a unicast ARP request to poison ARP cache – Send a unicast ARP reply to poison ARP cache 25
• Which systems are vulnerable to ARP poisoning? – Windows 9 x, NT, 2000, XP – Solaris 8 – Linux Kernel 2. 2 and 2. 4 – Cisco IOS 12 – Nokia IPSO 3. 5 26

27
• Complicated attacks and their impacts • Man-in-the-middle attack – Cheat both sides of a connection and get access to the traffic b/w them – The malicious node will forward packets to both sides to avoiding detection – Disable attacker’s ICMP redirect functionality – Microsoft IE certificate can be compromised by this attack 28
• Hijacking HTTP connections and run a manipulated web server through Mi. M attacks • Escaping firewall – Some companies use IP based authentication and only allow a few IP addresses to get out (HTTP server, mail server) – Through ARP poisoning, you can bypass the firewall 29
• Do. S attacks – After poisoning the ARP cache, discard all packets sent to you – Using a non-existing physical address to poison ARP cache • Poisoning a SMTP relaying server to send out junk mails 30
• Defending against ARP poisoning – Network IDS: detect duplicate IP address or flip-flop of the IP-PHY bindings – Host IDS: maintain a record of IP-PHY bindings, detect abnormal changes of the bindings (arpwatch in UNIX) – Do not use IP-address based authentication 31

32
IP protocol and fragmentation • IP layer provides the fundamental service in Internet: unreliable, connectionless, and best-effort based packet delivery – Unreliable: packet may lost, duplicated, delayed, out of order – Connectionless: every packet is handled independently – Best-effort: no quality guarantee 33
• IP protocol will – Define the format of IP packet – Routing – Determine • Packet processing procedures • Error reporting and handling procedures 34
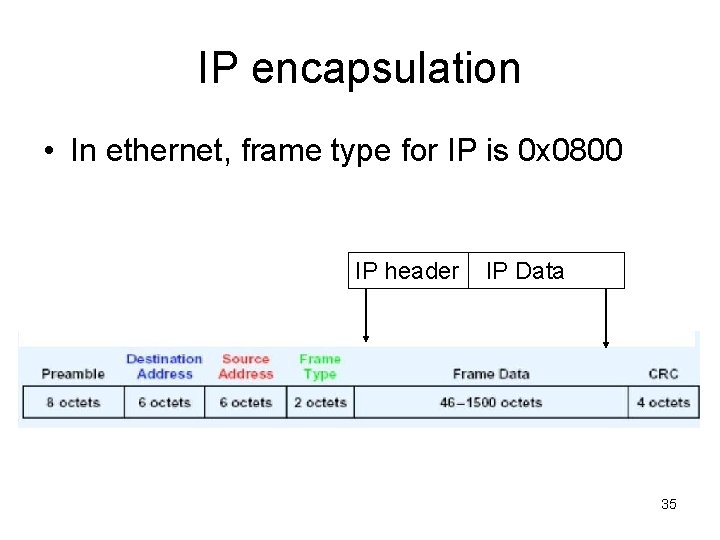
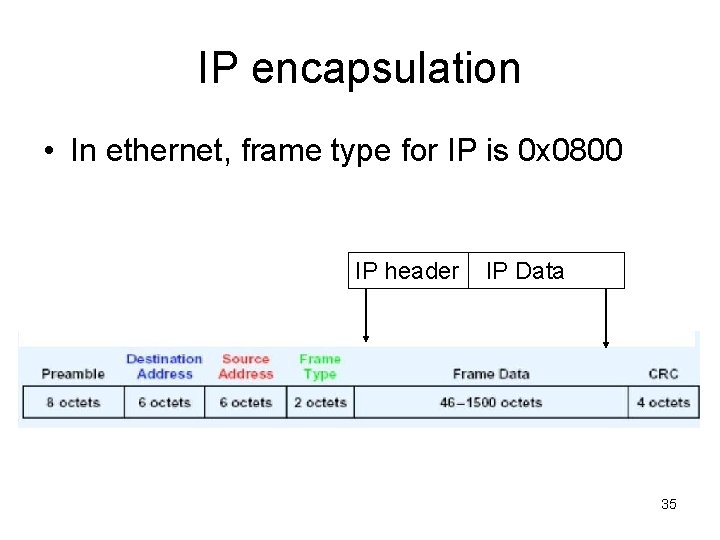
IP encapsulation • In ethernet, frame type for IP is 0 x 0800 IP header IP Data 35
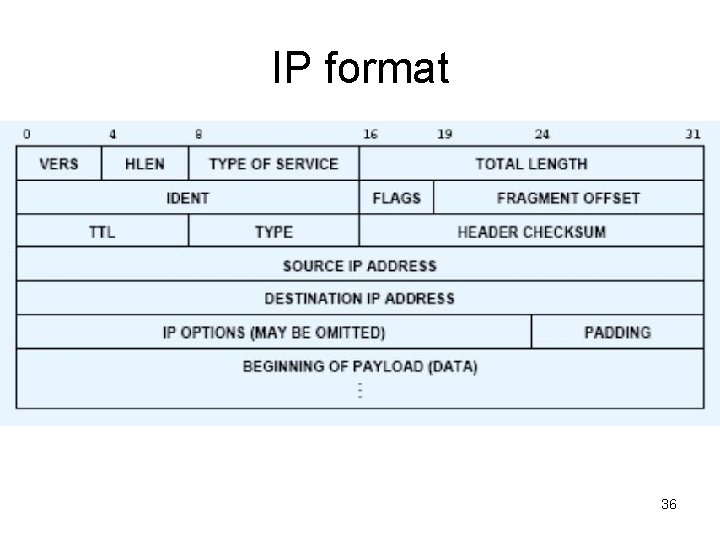
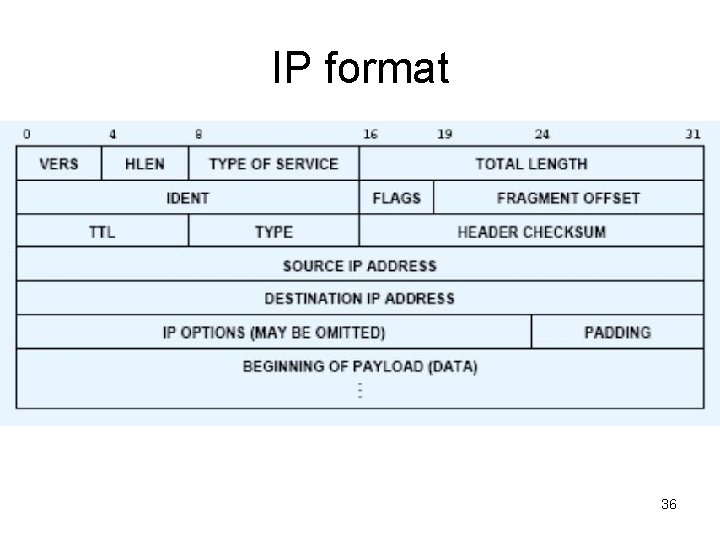
IP format 36
• Details of IP packet – Vers: current version is 4 – HLEN: header length in 32 bit word. Usually is 5 (20 byte), max can be 60 bytes (IP options) – Type of services: usually all 0 (best effort), can be used for diffserv and Qo. S – Total length: 16 bit can represent 64 K byte long packet 37
• Identification, flags, and offset: used for fragmentation and reassemble (later) • TTL: time to live: number of routers a packet can pass. – Every router will reduce this value by one. When reach 0, the packet will be discarded. – Can be used to prevent routing loop – Use TTL to implement traceroute 38
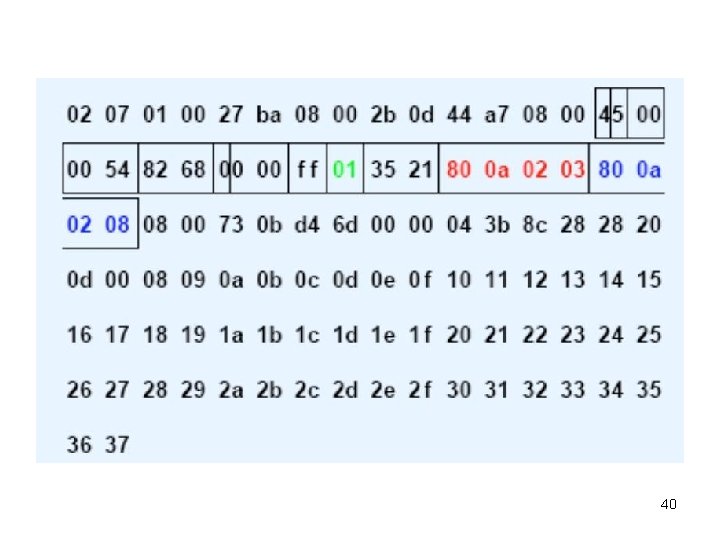
• Type: the high level protocol the IP packet contains: ICMP (0 x 01), TCP (0 x 06), UDP (0 x 11) • Header checksum • Example: an ICMP packet b/w 128. 10. 2. 3 and 128. 10. 2. 8. Header length is 20 bytes. 39
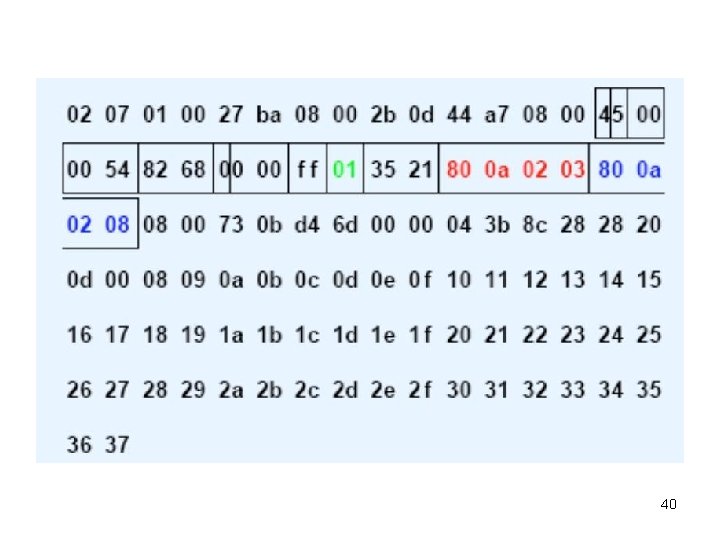
40
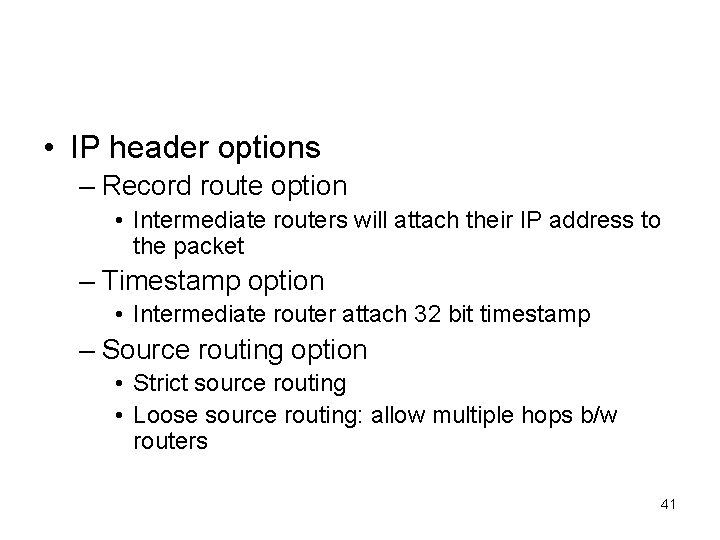
• IP header options – Record route option • Intermediate routers will attach their IP address to the packet – Timestamp option • Intermediate router attach 32 bit timestamp – Source routing option • Strict source routing • Loose source routing: allow multiple hops b/w routers 41