ITIL Service Management security IT Service Availability Management
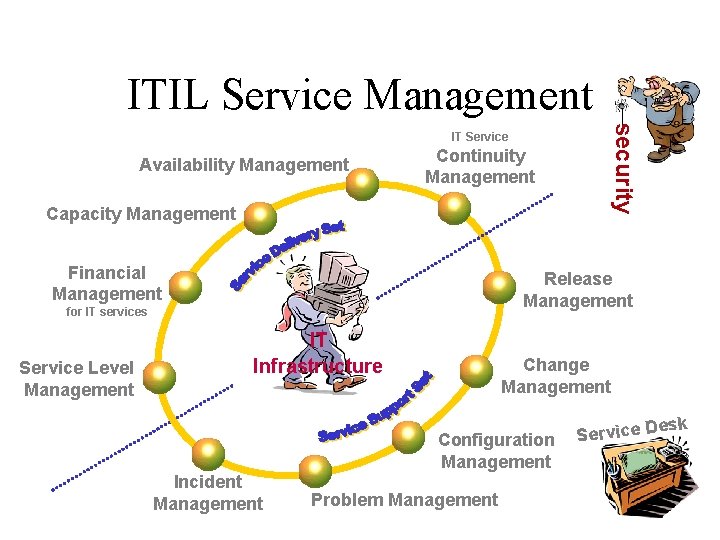
ITIL Service Management security IT Service Availability Management Continuity Management Capacity Management Financial Management Release Management for IT services Service Level Management IT Infrastructure Change Management Configuration Management Incident Management Problem Management esk Service D
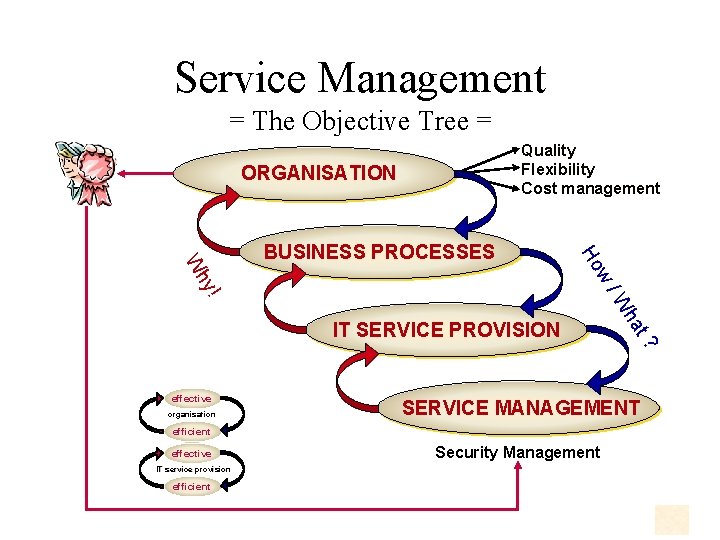
Service Management = The Objective Tree = Quality Flexibility Cost management ORGANISATION Ho ! /W hy w W BUSINESS PROCESSES organisation SERVICE MANAGEMENT efficient effective IT service provision efficient t? effective ha IT SERVICE PROVISION Security Management
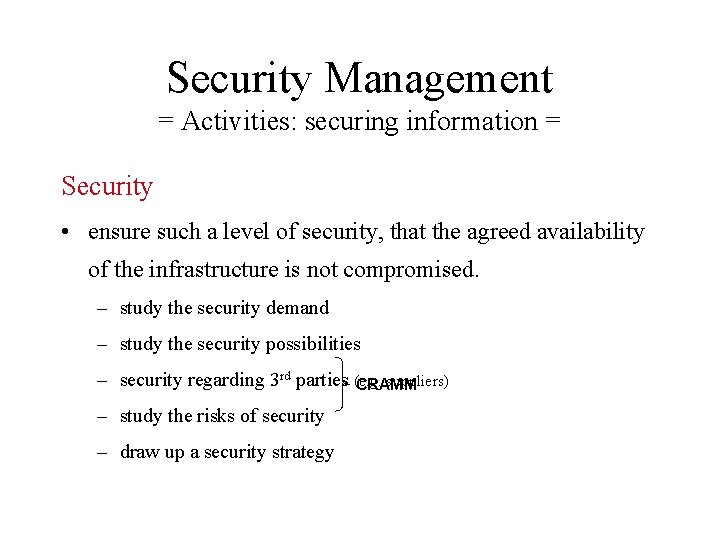
Security Management = Activities: securing information = Security • ensure such a level of security, that the agreed availability of the infrastructure is not compromised. – study the security demand – study the security possibilities – security regarding 3 rd parties (e. g. suppliers) CRAMM – study the risks of security – draw up a security strategy
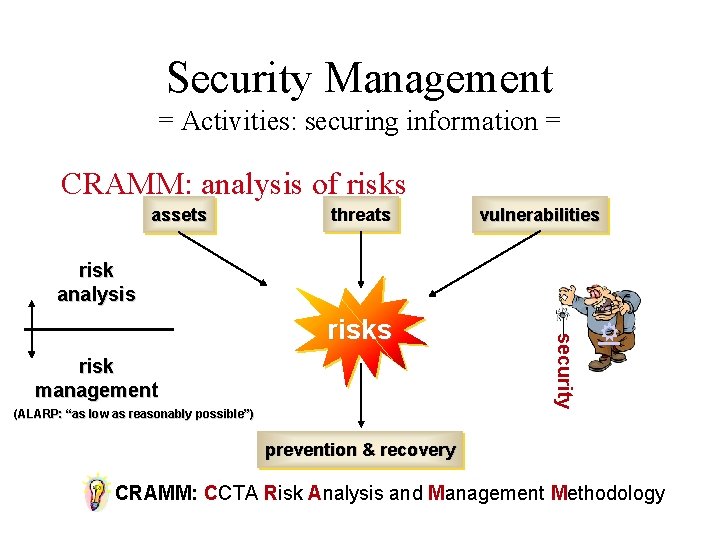
Security Management = Activities: securing information = CRAMM: analysis of risks assets threats vulnerabilities risk analysis risk management (ALARP: “as low as reasonably possible”) security risks prevention & recovery CRAMM: CCTA Risk Analysis and Management Methodology
Security Management = the basics = • CIA – Confidentiality • protecting information against unauthorised use – Integrity • accuracy and completeness of information – Availability • information is available at any moment within the agreed timeframe • Security Baseline • the basic level of security – these standard security measures are listed in the Service Catalogue
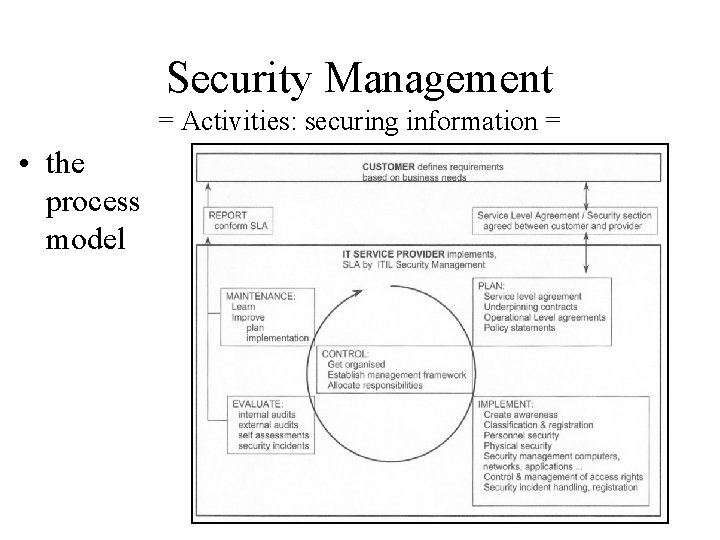
Security Management = Activities: securing information = • the process model
Security Management = Activities: securing information = • Steering: policy and organisation of securing information – Policy • develop and implement policy • awareness campaign: the goal, the common principles and the importance placed on security • determine the sub processes • determine responsibilities and authorities • determine the relationships with other ITIL-processes • how to deal with security incidents
Security Management = Activities: securing information = • Steering: policy and organisation of securing information – Organisation • • • set up organisation structure and management frame allocate responsibilities and authorities choose tools (for e. g. risk analysis) implement the “Taskforce Information Security” TIS coordination of securing information (and providing specialist advice) • ensure independent audits (EDP-audits) • ensure information security in 3 rd party contracts • ensure physical and logical access security regarding 3 rd parties
Security Management = Activities: securing information = • Planning – draw up the security paragraph in the SLA together with SLM • record in OLAs / SPAs as security plan per - organisation-unit - IT platform - application - network -… – draw up security paragraphs in underpinning contracts • the security plan per organisation-unit within the organisation of the external IT service provider
Security Management = Activities: securing information = • Implementation – classification and managing IT resources • input for maintenance of CI’s in the CMDB – staff security • screening • security statements / agreements • training – security awareness – how to deal with security incidents – how to deal with flaws in security • disciplinary measures
Security Management = Activities: securing information = • Implementation – managing security • • allocation of responsibilities and authorities written manuals / guidelines house rules guidelines for security during the full lifecycle (development - test - acceptance - operation – phase out) • implementation of contingency provisions • handling and securing data carriers – access security • implementation of the policy of securing information • maintenance of access rights of customers and applications • maintenance of security measures in networks (firewalls, dial-in facilities, bridges, routers, …)
Security Management = Activities: securing information = • Evaluation (audit & evaluation) – self assessments • are mainly carried out by the business processes themselves • internal audits • by internal EDP-auditors – external audits • by external (independent) EDP-auditors – verification of the security policy – verification of security plans – evaluate security incidents • detect and react to unwanted use of IT resources
Security Management = Activities: securing information = • Maintenance – of both the SLA (the security paragraph) as well as the OLAs – is based on the results of the sub process “Evaluate” and insight in changing risks – proposes changes to be carried out: • • • in the sub process “Plan” in the regular SLA maintenance the changes go through Change Management !!!
Security Management = Activities: securing information = • Reporting – on sub process “Plan” • degree of confirmation to SLAs (including CPIs on security) • status of (and possible problems with): - OLAs / SPAs - Underpinning Contracts - security year plans / action plans – on sub process “Implementation” • status accounting – regarding the implementation of securing information – regarding the awareness campaign on securing information • account of security incidents and the reactions • trend analysis regarding security incidents
Security Management = Activities: securing information = • Reporting – on sub process “Evaluation” • results of audits, reviews and internal assessments • warnings about and identification of new threats – specific reports • with the individual customer agreed SLA-reports • procedures regarding communication in special (unforseen) situations
Security Management = Costs, Points of Attention, Advantages = • Costs – P ersonnel Êcarrying out of the risk-analysis, draw up and maintenance of the security plan, management of (supporting) contracts, … – A ccommodation Êalso physical storage of process documents, … – S oftware tools for analysis, contract management, security plans, – H ardware costs, … implementation costs of security equipment, test
Security Management = Costs, Points of Attention, Advantages = • Points of Attention – commitment of the organisation and the management • security measures constrain (long fought) privileges • no security incidents = tendency to decrease budget – attitude and awareness • “real” security is often new to the organisation • integrate security procedures in daily routine – controllability • have right actions been taken (and have the right procedures been followed)? • have the right decisions been made? • is the authority of decision makers verifiable?
Security Management = Costs, Points of Attention, Advantages = • Points of Attention – Change Management • in assessing a change no slackening may occur regarding (a basic level of) security – too high ambition • don’t do everything at once • implementation of organisational measures is harder than implementation of technical measures – lack of detection mechanisms • “new” applications (e. g. internet) run the risk, under the influence of short “time to market” and desired low development costs, of being not capable of “intrusion detection”
Security Management = Costs, Points of Attention, Advantages = • Advantages – pro-active approach of the organisation • optimal security measures – ensuring a technically reliable information flow • internal importance: - availability in time of accurate and complete information • external importance: - adequate provision of information leads to mature services and/or products for the external market - support for the continuity of the organisation
Security Management = Functionally Oriented vs. Process Driven = mainframe The Art of network pc-lan Security Management
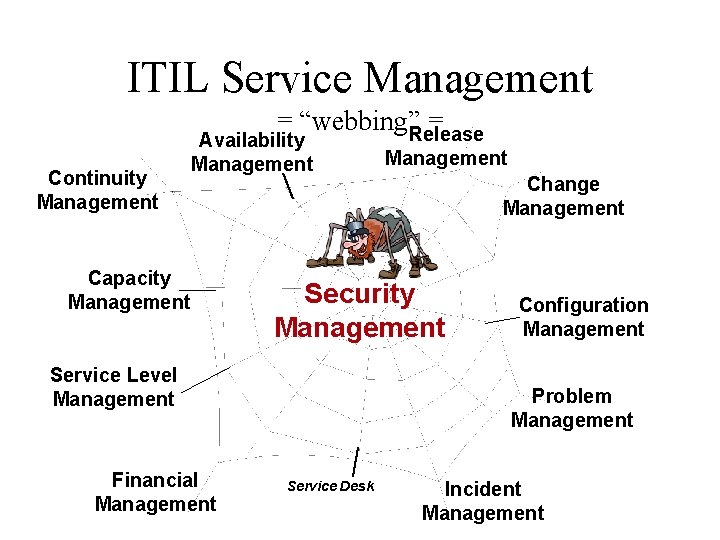
ITIL Service Management = “webbing”Release = Continuity Management Availability Management Capacity Management Change Management Security Management Service Level Management Financial Management Configuration Management Problem Management Service Desk Incident Management
- Slides: 21