IT Security and Cybercrime How theory transforms into
IT Security and Cybercrime - How theory transforms into best practice? Arthur Keleti
Agenda • Threats (Cybercrime) • What is cybercrime from the practical point of view? • What are the main risk factors, threats? • Trends and problems in the EU • Solutions (IT Security) • How regulation materializes in the real world? • Size, role, place of the IT Security organization locally • Who are the role players of IT Security and where are the frontlines? • What is the classic security procedure? • Minimizing or eliminating risk in real life? IT Security solutions • IT Seurity spending • Future trends KFKI Rendszerintegrációs Zrt. , 2009, Keleti 2

THREATS AND CYBERCRIME

What that could be? Land object Width: ~6 m Height: ~7 m Age: 2000 years Length: 6. 400 km The Big Wall of China KFKI Rendszerintegrációs Zrt. , 2009, Keleti 4
Many changes, development on the wa A thousand year of building Watchtowers in 400 m distance 14 gates Continuous guard shifts on full length KFKI Rendszerintegrációs Zrt. , 2009, Keleti 5
The 1 st gate: Shanhaiguan Gateway KFKI Rendszerintegrációs Zrt. , 2009, Keleti 6
The 1 st gate: Shanhaiguan Gateway KFKI Rendszerintegrációs Zrt. , 2009, Keleti 7
Weak point: the human KFKI Rendszerintegrációs Zrt. , 2009, Keleti Wu Sangui general: the most trusted, most faithful strategist guarded the 1 st gate. There was a rebel among inhabitants. Wu’s “service” maid was kidnapped. Wu, thinking he would get back his lady he willingly opened the gate for two thousand hundred mandurian horsemen. 8 the That put an end to the rule of

What is cybercrime from the practical point of view? • It is “complicated” > simply 'crime' with some sort of 'computer' or 'cyber' aspect • The Council of Europe's Cybercrime Treaty uses the term 'cybercrime' to refer to offenses ranging from criminal activity against data to content and copyright infringement [Krone, 2005] • [Zeviar-Geese, 1997 -98] suggest that the definition is including activities such as fraud, unauthorized access, child pornography, and cyberstalking • The United Nations Manual on the Prevention and Control of Computer Related Crime includes fraud, forgery, and unauthorized access [United Nations, 1995] in its cybercrime definition Source: Symantec • Symantec says: any crime that is committed using a 9 KFKI Rendszerintegrációs Zrt. , 2009, Keleti
What is cybercrime from the practical point of view? Type I cybercrime has the following characteristics: • It is generally a single event from the perspective of the victim. For example, the victim unknowingly downloads a Trojan horse which installs a keystroke logger on his or her machine. • It is often facilitated by crimeware programs such as keystroke loggers, viruses, rootkits or Trojan horses. • Software flaws or vulnerabilities often provide the foothold for the attacker. • Examples of this type of cybercrime include but are not limited to phishing, theft or manipulation of data or Source: Symantec services via hacking or viruses, identity theft, and bank or e-commerce fraud. 10 KFKI Rendszerintegrációs Zrt. , 2009, Keleti
What is cybercrime from the practical point of view? Type II cybercrime has the following characteristics: • At the other end of the spectrum, includes, but is not limited to activities such as cyberstalking and harassment, child predation, extortion, blackmail, stock market manipulation, complex corporate espionage, and planning or carrying out terrorist activities • It is generally an on-going series of events, involving repeated interactions with the target. For example, the target is contacted in a chat room by someone who, over time, attempts to establish a relationship. Eventually, the criminal exploits the relationship. Source: Symantec • It is generally facilitated by programs that do not fit into under the classification crimeware. For example, 11 KFKI Rendszerintegrációs Zrt. , 2009, Keleti
Barclays chairman’s identity stolen Marcus Agius, chairman of board at Barclays Bank was a victim of identity theft and fraud of 10. 000 GBP. The amount was withdrawn from his account using a credit card trick. The thief collected personal data of Aqius and used them to deceive a help desk operator to send him a new credit card as if he was Mr Aqius himself. The card was sent to him. The guy took the card to a high street branch of Barclays and withdrew the amount. "It was down to human error. Procedures were not followed fully and we have learned from it, " Barclaycard told the BBC. … Experts have already warned that 2008 will be a bumper year for identity fraudsters. http: //www. pcw. co. uk/vnunet/news/2207085/barclays-chairman-identity By Iain Thomson, vnunet. com, 11 Jan 2008 KFKI Rendszerintegrációs Zrt. , 2009, Keleti 12
How hacker work? Real life example of hacking into FBI’s National Crime Information Center in 6 hours, Chris Goggans – pen. tester Source: http: //www. infosecnews. org/hypermail/0805/14877. html, 27. , he 2008 1. Goggans (Patch. Advisor Inc. ) during a routine network. May scan, discovered a series of unpatched vulnerabilities in the civilian government agency's Web server. 2. He used a hole in the Web server to pull down usernames and passwords that were reused on a host of enterprise systems. 3. In those systems, he found further account details that allowed him to get Windows domain administrator privileges -- a classic escalation-ofprivileges attack. 4. Using this privileged access, he was able to gain full control of almost all Windows-based systems in the enterprise, including workstations used by the on-site police force. 5. He noticed that several police workstations had a second networking card installed that used the SNA protocol to directly talk to an IBM mainframe. 6. By covertly installing remote control software on those workstations, he found programs on their desktops that automatically connected the workstations to the FBI's NCIC database. 7. "That software, coupled with a keystroke capture program, would allow 13 KFKI Rendszerintegrációs Zrt. , 2009, Keleti the credentials needed to log into the FBI's National an attacker to grab
Cybercime – two things to • Don’t care about regulations know • Don’t know borders or continents No. 1. • Are awake when we are asleep Hackers Agencie s KFKI Rendszerintegrációs Zrt. , 2009, Keleti • Know a lot more about IT than a regular IT employee • Tend to erase their tracks • Target more and more precisely • Capable of unleashing attack/intelligence powers that could be beyond our resource capacity to block 14
Cybercime – two things to • Know more about our know organization than anybody else No. 2. • Are part of critical business Employe es KFKI Rendszerintegrációs Zrt. , 2009, Keleti procedures • Are difficult to manage 100% properly from the HR point of view • Differ widely in IT knowledge and in level of education • Tend to be negligent towards regulations and controls affecting their freedom 15 • Are more naive than suspicious
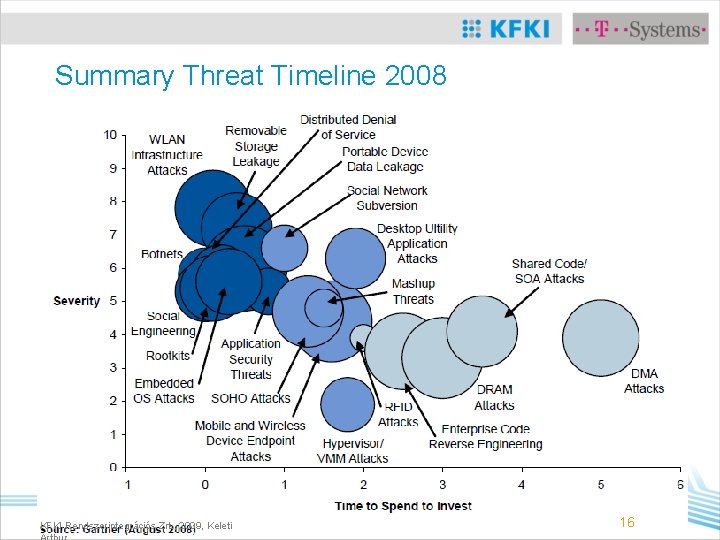
Summary Threat Timeline 2008 KFKI Rendszerintegrációs Zrt. , 2009, Keleti 16
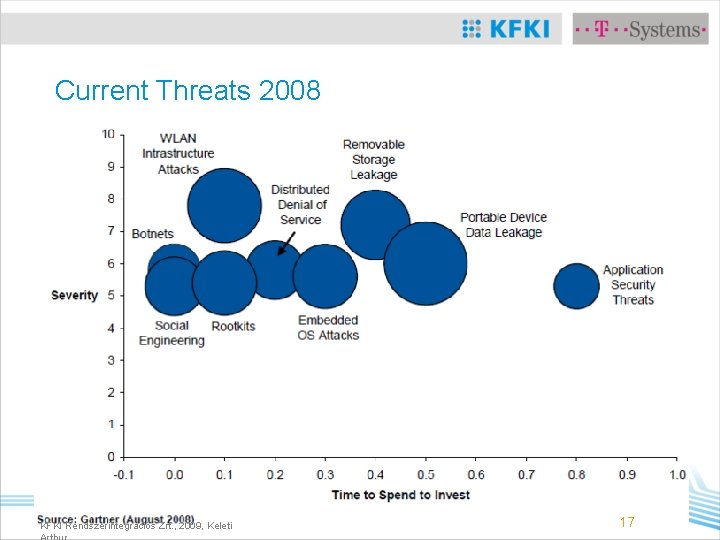
Current Threats 2008 KFKI Rendszerintegrációs Zrt. , 2009, Keleti 17

Trends and threats in the EU • Data theft represents the primary information security threat – more significant than either viruses or hacker infiltration • Of all possible results of compromised information security, the threat of leakage of confidential information is keeping more members of the IT department (93%) awake at night than any other • Europe’s primary data leakage channels are identified as portable storage devices, e-mail, and Internet-based channels such as web-mail and forums • Only 11% of those surveyed were confident their company’s information security had not been breached over the last year Source: Info. Watch Internal IT Threats in Europe 2 • The lack of industry standards is highlighted as the 18 KFKI Rendszerintegrációs Zrt. , 2009, Keleti
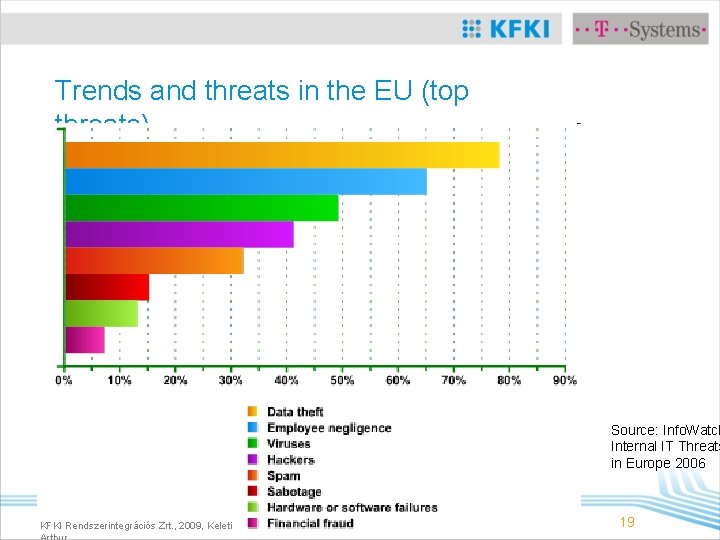
Trends and threats in the EU (top threats) Source: Info. Watch Internal IT Threats in Europe 2006 KFKI Rendszerintegrációs Zrt. , 2009, Keleti 19
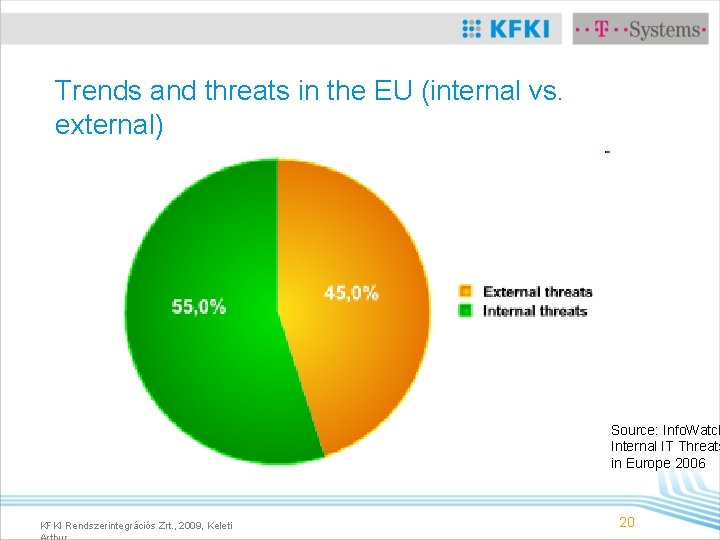
Trends and threats in the EU (internal vs. external) Source: Info. Watch Internal IT Threats in Europe 2006 KFKI Rendszerintegrációs Zrt. , 2009, Keleti 20
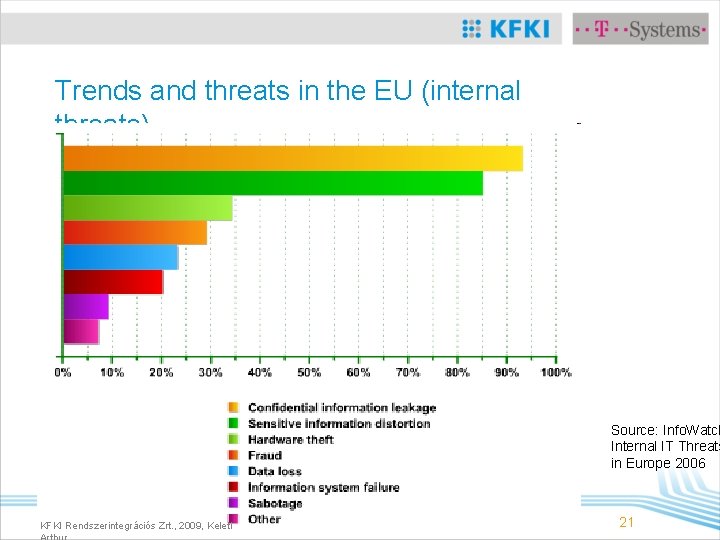
Trends and threats in the EU (internal threats) Source: Info. Watch Internal IT Threats in Europe 2006 KFKI Rendszerintegrációs Zrt. , 2009, Keleti 21
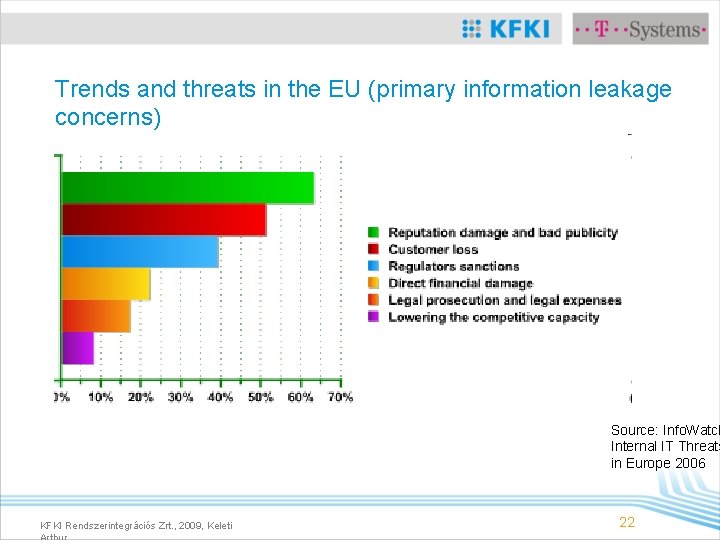
Trends and threats in the EU (primary information leakage concerns) Source: Info. Watch Internal IT Threats in Europe 2006 KFKI Rendszerintegrációs Zrt. , 2009, Keleti 22

SOLUTIONS (IT SECURITY)
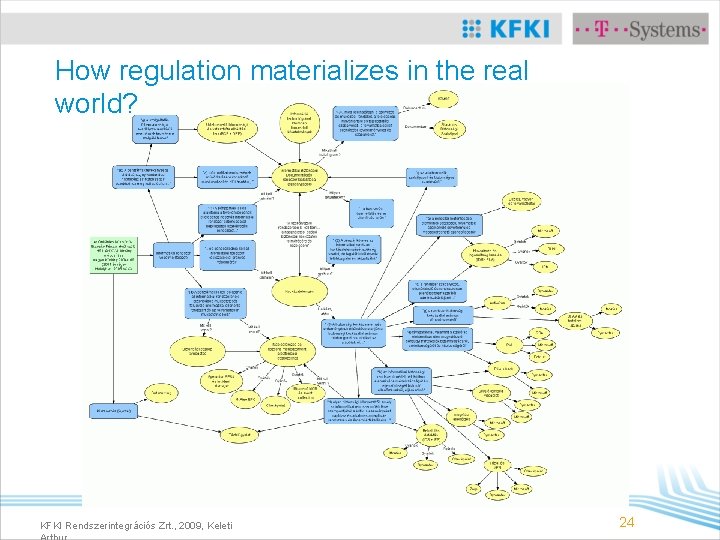
How regulation materializes in the real world? KFKI Rendszerintegrációs Zrt. , 2009, Keleti 24
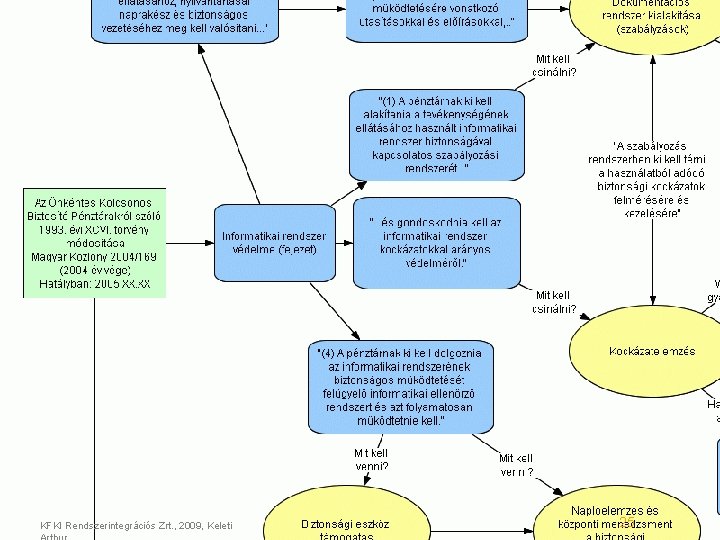
KFKI Rendszerintegrációs Zrt. , 2009, Keleti 25
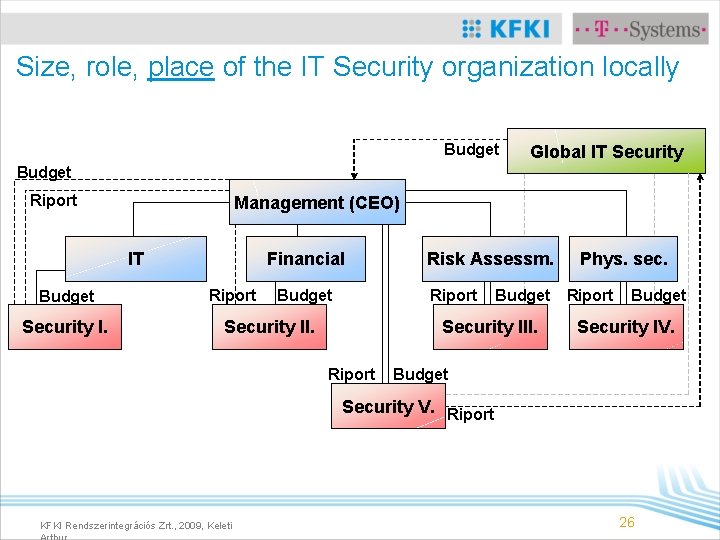
Size, role, place of the IT Security organization locally Budget Global IT Security Budget Riport Management (CEO) IT Budget Security I. Financial Riport Budget Risk Assessm. Riport Security II. Budget Security III. Riport Phys. sec. Riport Budget Security IV. Budget Security V. Riport KFKI Rendszerintegrációs Zrt. , 2009, Keleti 26
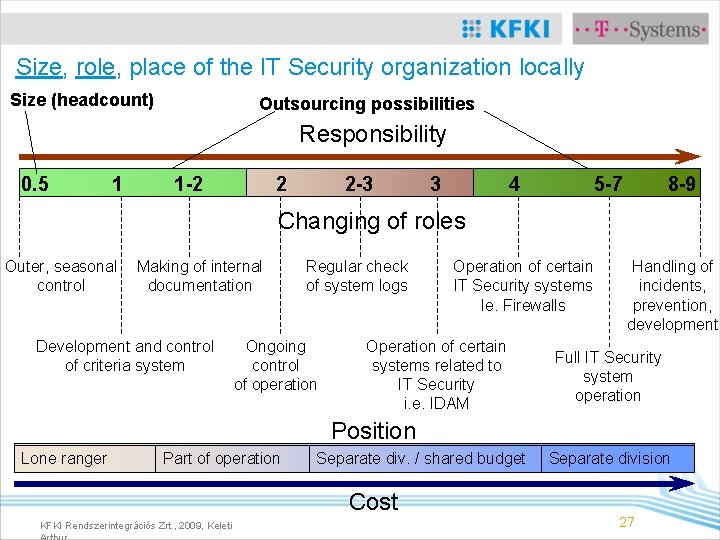
Size, role, place of the IT Security organization locally Size (headcount) Outsourcing possibilities Responsibility 0. 5 1 1 -2 2 2 -3 3 4 5 -7 8 -9 Changing of roles Outer, seasonal control Making of internal documentation Development and control of criteria system Regular check of system logs Ongoing control of operation Operation of certain IT Security systems Ie. Firewalls Operation of certain systems related to IT Security i. e. IDAM Handling of incidents, prevention, development Full IT Security system operation Position Lone ranger Part of operation Separate div. / shared budget Cost KFKI Rendszerintegrációs Zrt. , 2009, Keleti Separate division 27
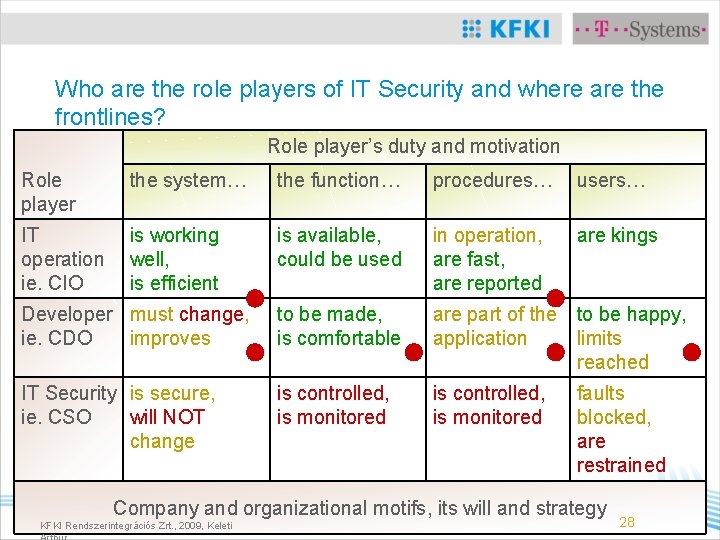
Who are the role players of IT Security and where are the frontlines? Role player’s duty and motivation Role player the system… the function… procedures… users… IT operation ie. CIO is working well, is efficient is available, could be used in operation, are fast, are reported are kings Developer must change, ie. CDO improves to be made, is comfortable are part of the to be happy, application limits reached IT Security is secure, ie. CSO will NOT change is controlled, is monitored faults blocked, are restrained Company and organizational motifs, its will and strategy KFKI Rendszerintegrációs Zrt. , 2009, Keleti 28
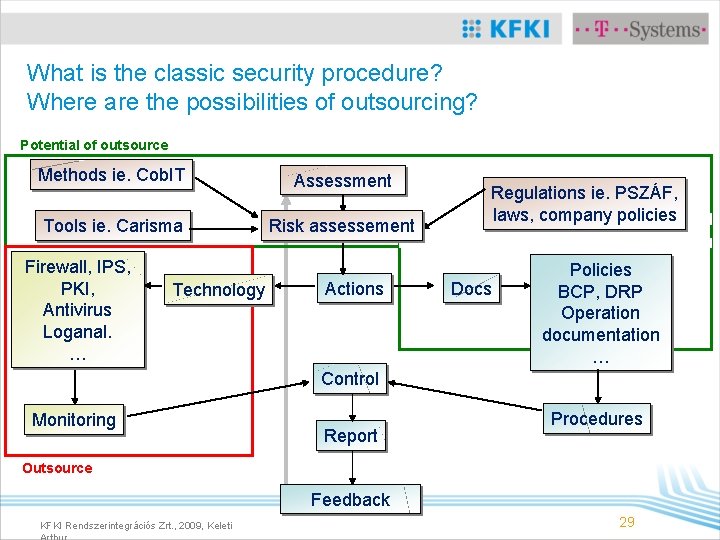
What is the classic security procedure? Where are the possibilities of outsourcing? Potential of outsource Methods ie. Cob. IT Assessment Tools ie. Carisma Risk assessement Firewall, IPS, PKI, Antivirus Loganal. … Technology Actions Regulations ie. PSZÁF, laws, company policies Docs Policies BCP, DRP Operation documentation … Control Monitoring Report Procedures Outsource Feedback KFKI Rendszerintegrációs Zrt. , 2009, Keleti 29
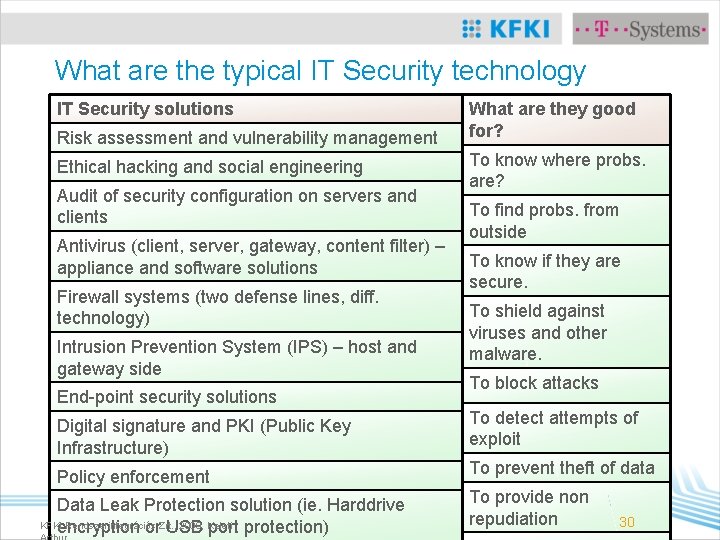
What are the typical IT Security technology areas? IT Security solutions What are they good Risk assessment and vulnerability management for? Ethical hacking and social engineering To know where probs. are? Audit of security configuration on servers and clients Antivirus (client, server, gateway, content filter) – appliance and software solutions Firewall systems (two defense lines, diff. technology) Intrusion Prevention System (IPS) – host and gateway side End-point security solutions To find probs. from outside To know if they are secure. To shield against viruses and other malware. To block attacks Digital signature and PKI (Public Key Infrastructure) To detect attempts of exploit Policy enforcement To prevent theft of data Data Leak Protection solution (ie. Harddrive KFKI Rendszerintegrációs 2009, Keleti encryption or. Zrt. , USB port protection) To provide non repudiation 30
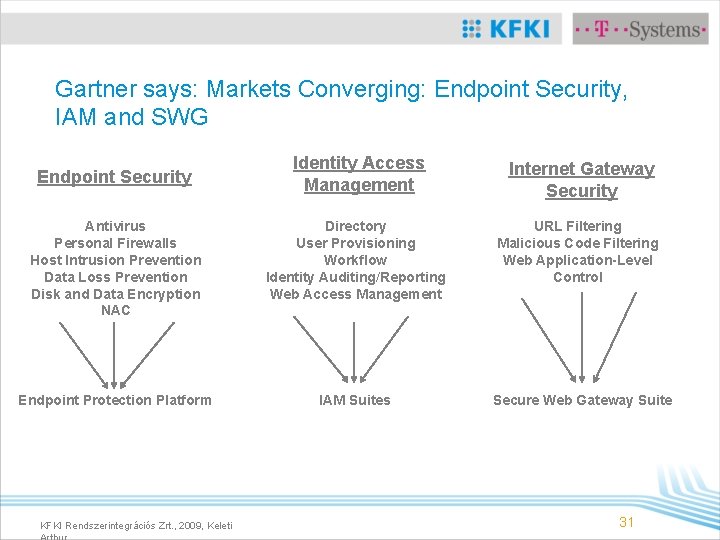
Gartner says: Markets Converging: Endpoint Security, IAM and SWG Identity Access Management Internet Gateway Security Antivirus Personal Firewalls Host Intrusion Prevention Data Loss Prevention Disk and Data Encryption NAC Directory User Provisioning Workflow Identity Auditing/Reporting Web Access Management URL Filtering Malicious Code Filtering Web Application-Level Control Endpoint Protection Platform IAM Suites Endpoint Security KFKI Rendszerintegrációs Zrt. , 2009, Keleti Secure Web Gateway Suite 31
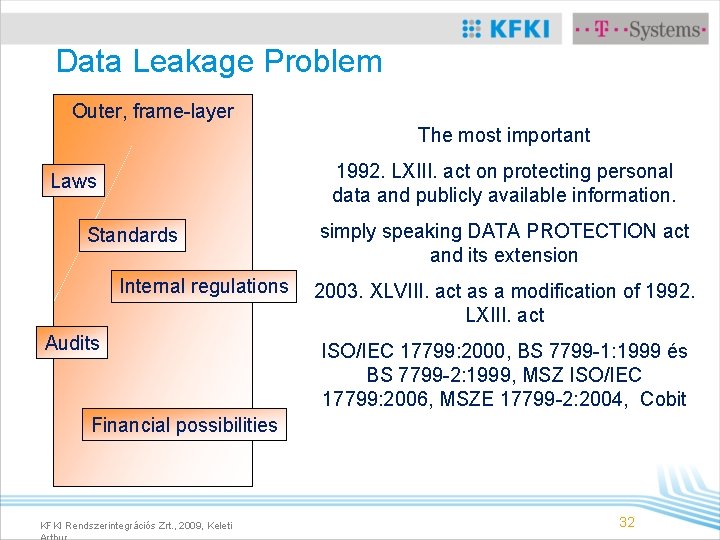
Data Leakage Problem Outer, frame-layer The most important 1992. LXIII. act on protecting personal data and publicly available information. Laws Standards Internal regulations Audits simply speaking DATA PROTECTION act and its extension 2003. XLVIII. act as a modification of 1992. LXIII. act ISO/IEC 17799: 2000, BS 7799 -1: 1999 és BS 7799 -2: 1999, MSZ ISO/IEC 17799: 2006, MSZE 17799 -2: 2004, Cobit Financial possibilities KFKI Rendszerintegrációs Zrt. , 2009, Keleti 32
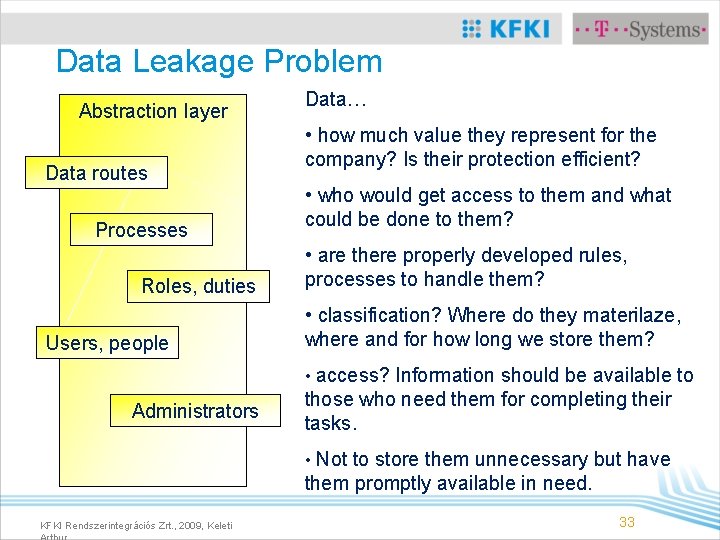
Data Leakage Problem Abstraction layer Data routes Processes Roles, duties Users, people Data… • how much value they represent for the company? Is their protection efficient? • who would get access to them and what could be done to them? • are there properly developed rules, processes to handle them? • classification? Where do they materilaze, where and for how long we store them? • access? Information should be available to Administrators those who need them for completing their tasks. • Not to store them unnecessary but have them promptly available in need. KFKI Rendszerintegrációs Zrt. , 2009, Keleti 33
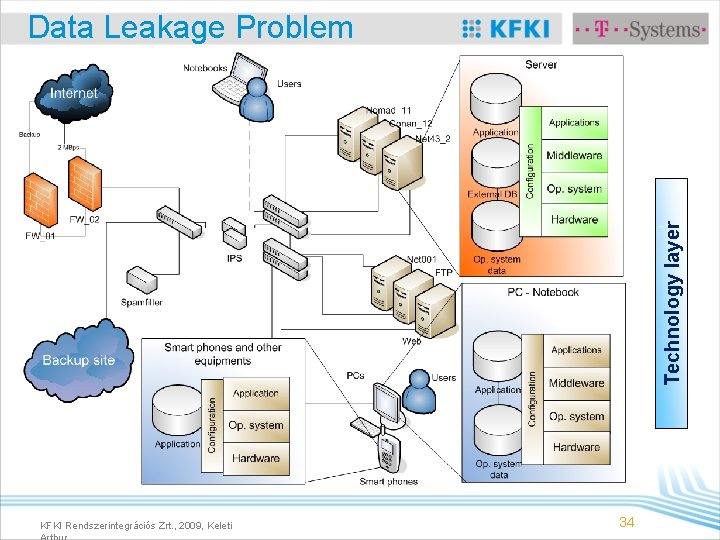
Technology layer Data Leakage Problem KFKI Rendszerintegrációs Zrt. , 2009, Keleti 34
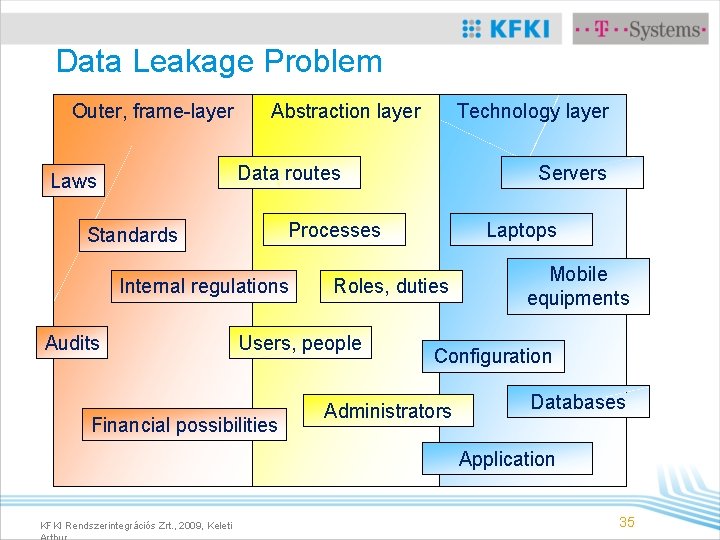
Data Leakage Problem Outer, frame-layer Abstraction layer Technology layer Data routes Laws Processes Standards Internal regulations Audits Servers Roles, duties Users, people Financial possibilities Laptops Mobile equipments Configuration Administrators Databases Application KFKI Rendszerintegrációs Zrt. , 2009, Keleti 35
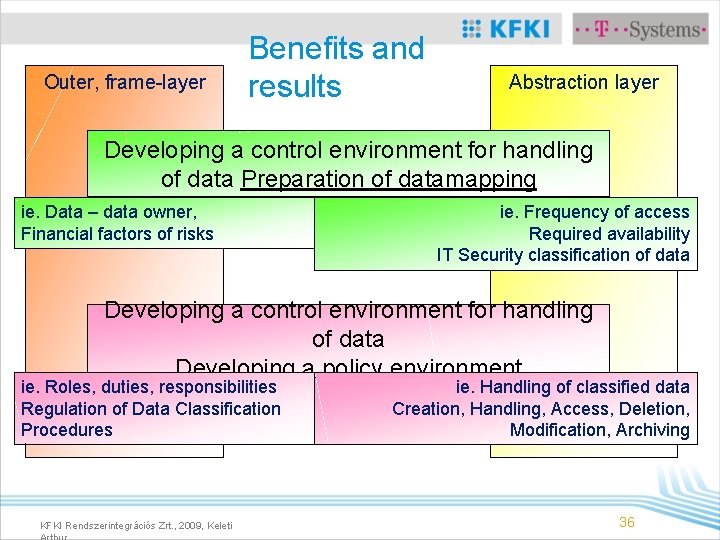
Outer, frame-layer Benefits and results Abstraction layer Developing a control environment for handling of data Preparation of datamapping ie. Data – data owner, Financial factors of risks ie. Frequency of access Required availability IT Security classification of data Developing a control environment for handling of data Developing a policy environment ie. Roles, duties, responsibilities Regulation of Data Classification Procedures KFKI Rendszerintegrációs Zrt. , 2009, Keleti ie. Handling of classified data Creation, Handling, Access, Deletion, Modification, Archiving 36
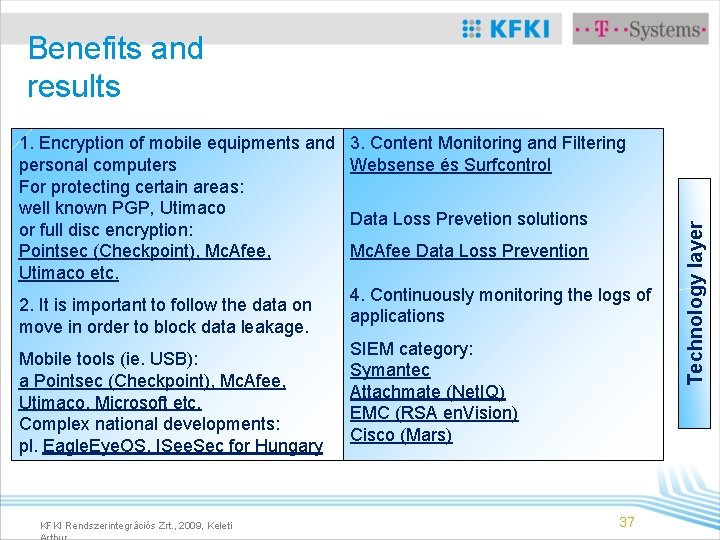
Benefits and results 2. It is important to follow the data on move in order to block data leakage. Mobile tools (ie. USB): a Pointsec (Checkpoint), Mc. Afee, Utimaco, Microsoft etc. Complex national developments: pl. Eagle. Eye. OS, ISee. Sec for Hungary KFKI Rendszerintegrációs Zrt. , 2009, Keleti 3. Content Monitoring and Filtering Websense és Surfcontrol Data Loss Prevetion solutions Mc. Afee Data Loss Prevention 4. Continuously monitoring the logs of applications SIEM category: Symantec Attachmate (Net. IQ) EMC (RSA en. Vision) Cisco (Mars) 37 Technology layer 1. Encryption of mobile equipments and personal computers For protecting certain areas: well known PGP, Utimaco or full disc encryption: Pointsec (Checkpoint), Mc. Afee, Utimaco etc.
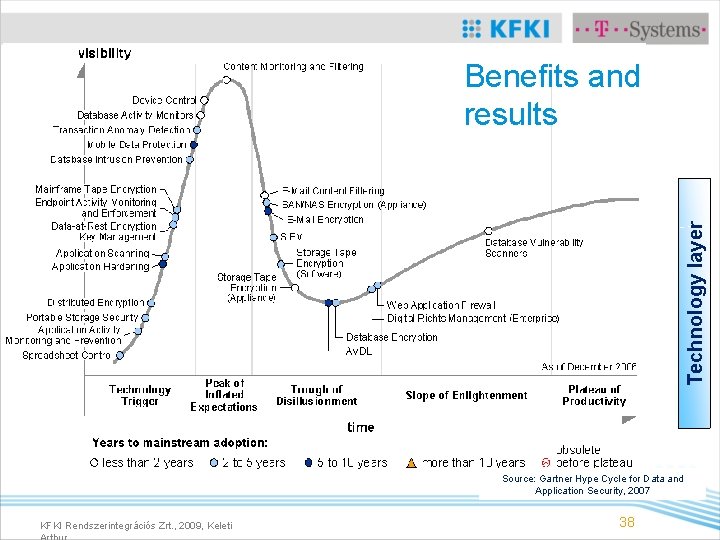
Technology layer Benefits and results Source: Gartner Hype Cycle for Data and Application Security, 2007 KFKI Rendszerintegrációs Zrt. , 2009, Keleti 38
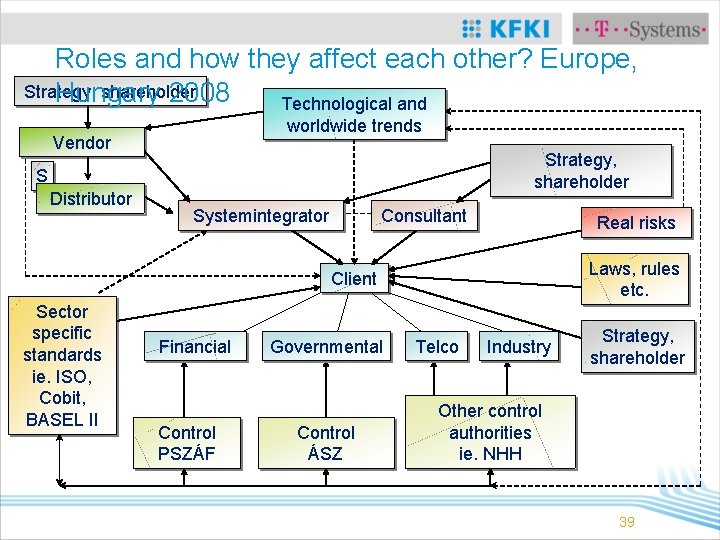
Roles and how they affect each other? Europe, Strategy, shareholder Hungary 2008 Technological and worldwide trends Vendor Strategy, shareholder S Distributor Systemintegrator Consultant Real risks Laws, rules etc. Client Sector specific standards ie. ISO, Cobit, BASEL II Financial Control PSZÁF Governmental Control ÁSZ Telco Industry Strategy, shareholder Other control authorities ie. NHH 39
Budget? Just how much we should spend on IT Security? • It depends on the role • If one operates IT Security, he needs shifts, professional knowledge, certification (vendor + CISA, CISSP) Managable and measurable security. That is definitively not cheap. • If one “just” analyses logs and monitors the IT Security components operated by someone else, he needs the eye of a professional and some technology to get the most out of logs and available resources, that’s not cheap but requires less people to deal with • What market researches say • A middle size company should spend at least 15 -20% of their IT budget on IT security. • That’s a lot. Today, most of those companies are not spending that much here in Hungary. KFKI Rendszerintegrációs Zrt. , 2009, Keleti 40
EMEA IT Security Services Market Overview (according to Gartner 01. 2008) • The IT 2008 security services market is expected to increase about 9% compared with 2007. • Spending on IT security services will reach $8. 7 billion by 2010. • IT management services will be the fastest-growing sector, while the more-sizable consulting services segment is expected to grow at a much-lower rate. KFKI Rendszerintegrációs Zrt. , 2009, Keleti 41
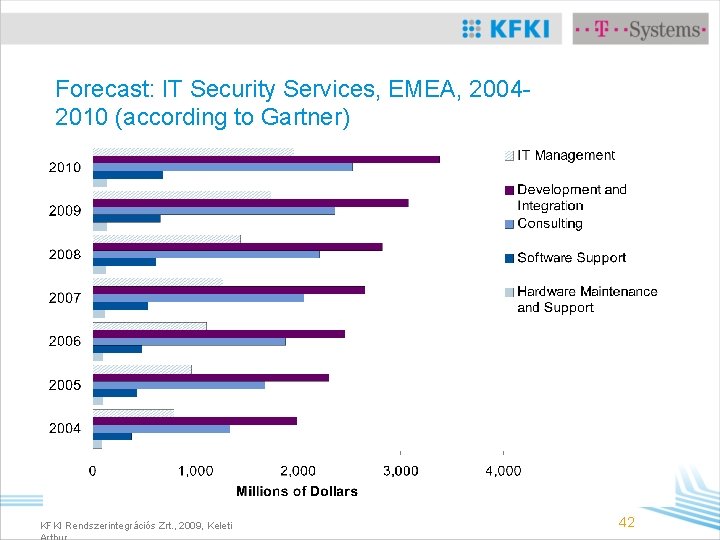
Forecast: IT Security Services, EMEA, 20042010 (according to Gartner) KFKI Rendszerintegrációs Zrt. , 2009, Keleti 42

Questions? Thank You for keeping with us! keleti. arthur@kfkizrt. hu keleti. arthur@yahoo. com KFKI Rendszerintegrációs Zrt. , 2009, Keleti 43
Course questions 1. What is the most significant, top threat for EU IT Security? (one answer applies) • A. Data theft • B. Virus attacks • C. Spam attacks • D. Malware problems KFKI Rendszerintegrációs Zrt. , 2009, Keleti 44
Course questions 2. What source most of the attacks were coming from at a typical organization in EU in 2006? (one answer applies) • A. Internal attacks (80%) • B. Internal attacks (55%) • C. External attacks (55%) • D. External attacks (75%) KFKI Rendszerintegrációs Zrt. , 2009, Keleti 45
Course questions 3. What would You think the best place is for IT Security division in the organizational chart? (one answer applies) • A. Under IT operation, CIO • B. Under CEO, management • C. Under Financial department • D. Under Physical Decurity division KFKI Rendszerintegrációs Zrt. , 2009, Keleti 46
- Slides: 46