IT NTPC Information Security Peeyush Arya paryantpc co


- Slides: 20
IT @ NTPC Information Security Peeyush Arya parya@ntpc. co. in 19 th December, 2015 1
Agenda • About NTPC • NTPC’s IT Adoption Journey – Project Lakshya • Introduction, Terminology & Types of IT Security Threats • IT Security Infrastructure at NTPC 2
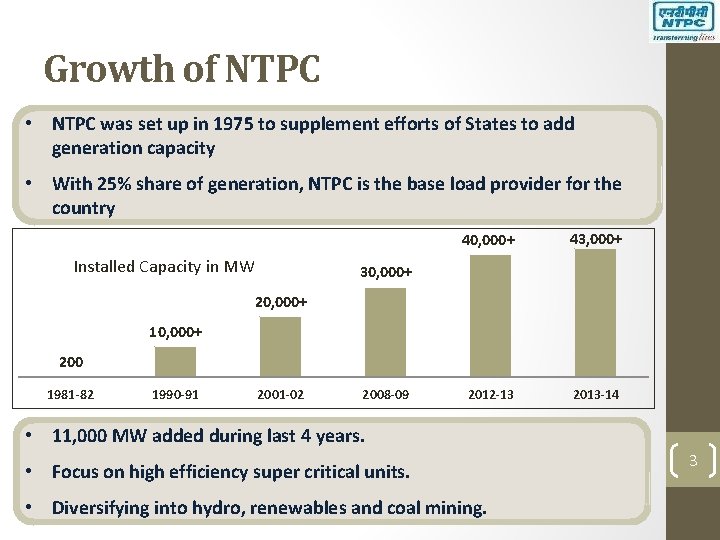
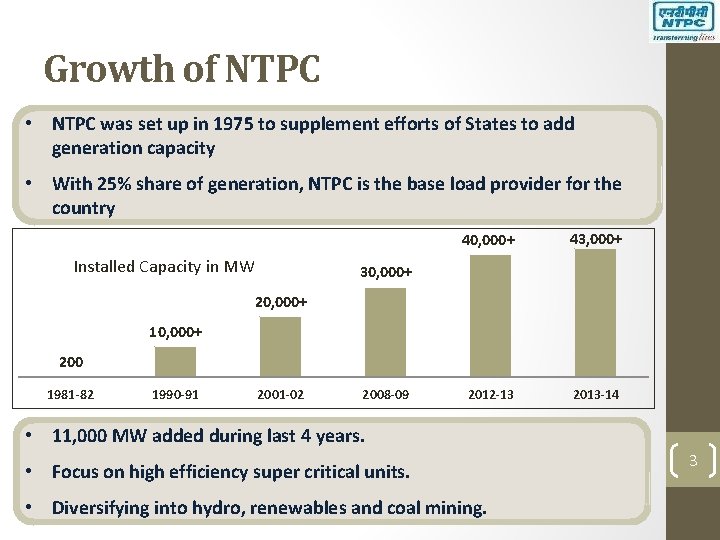
Growth of NTPC • NTPC was set up in 1975 to supplement efforts of States to add generation capacity • With 25% share of generation, NTPC is the base load provider for the country Installed Capacity in MW 40, 000+ 43, 000+ 2012 -13 2013 -14 30, 000+ 20, 000+ 10, 000+ 200 1981 -82 1990 -91 2001 -02 2008 -09 • 11, 000 MW added during last 4 years. • Focus on high efficiency super critical units. • Diversifying into hydro, renewables and coal mining. 3
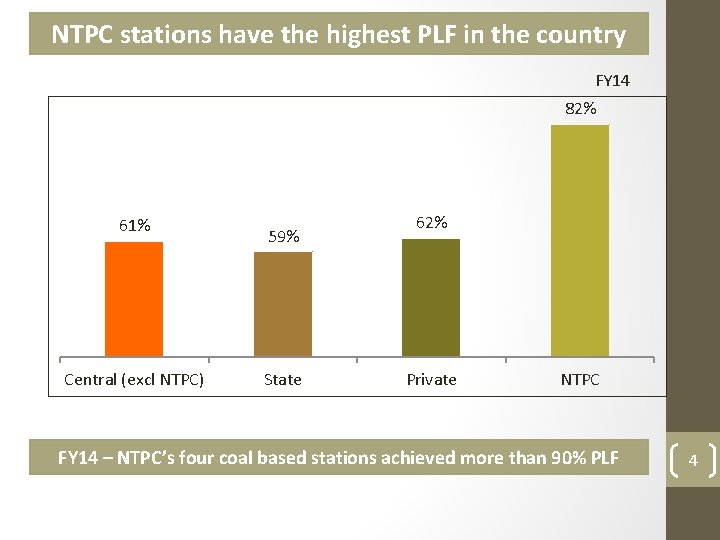
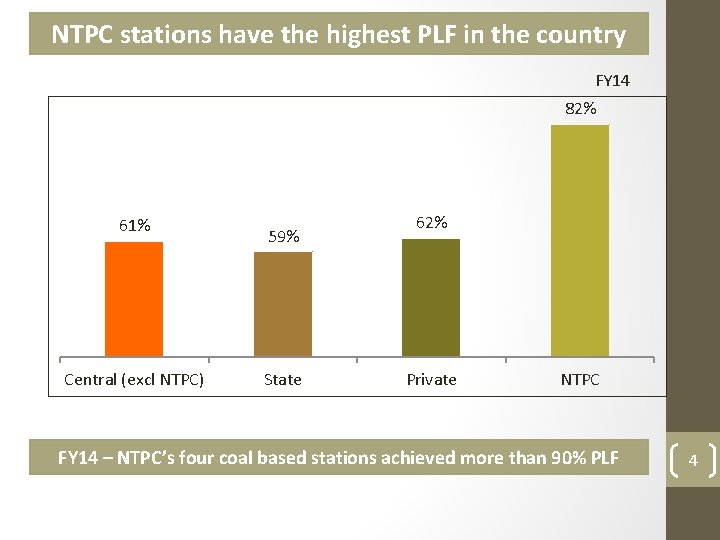
NTPC stations have the highest PLF in the country FY 14 82% 61% Central (excl NTPC) 59% State 62% Private NTPC FY 14 – NTPC’s four coal based stations achieved more than 90% PLF 4
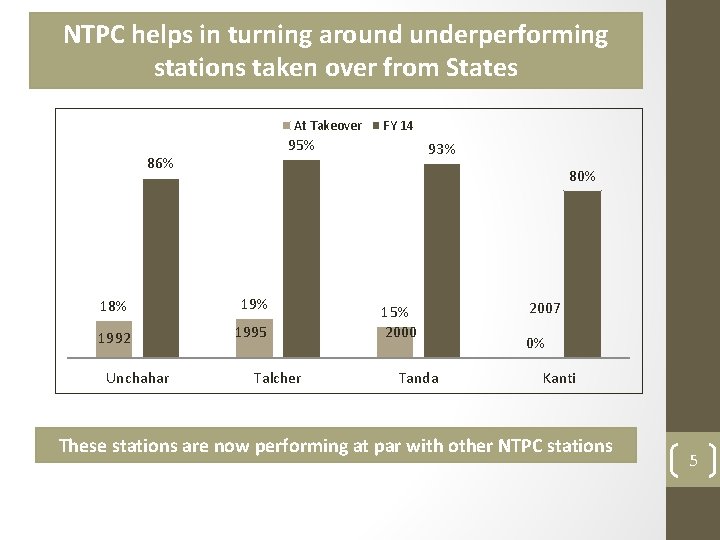
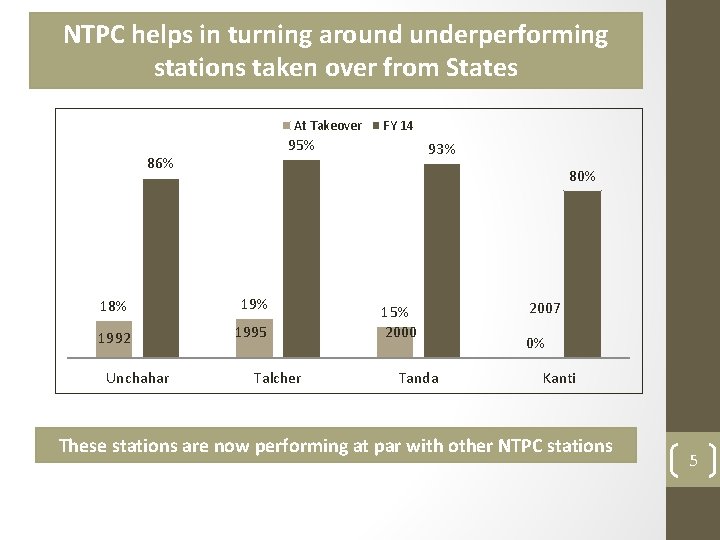
NTPC helps in turning around underperforming stations taken over from States At Takeover 95% 86% 93% 80% 18% 1992 1995 Unchahar FY 14 Talcher 15% 2000 Tanda 2007 0% Kanti These stations are now performing at par with other NTPC stations 5
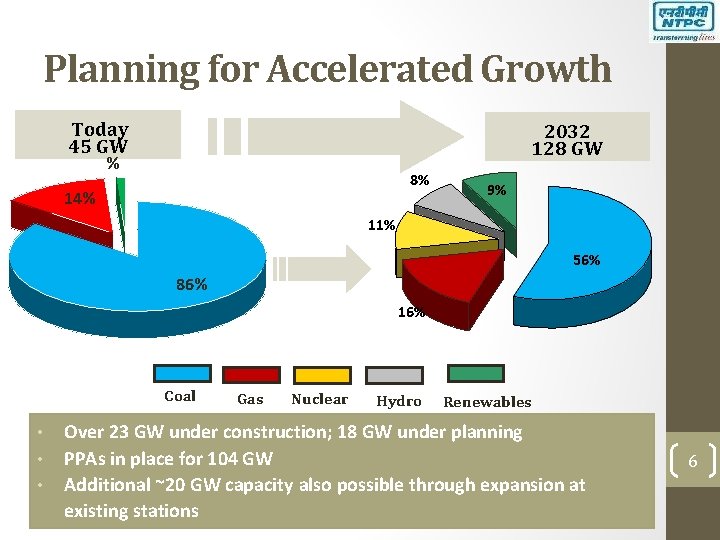
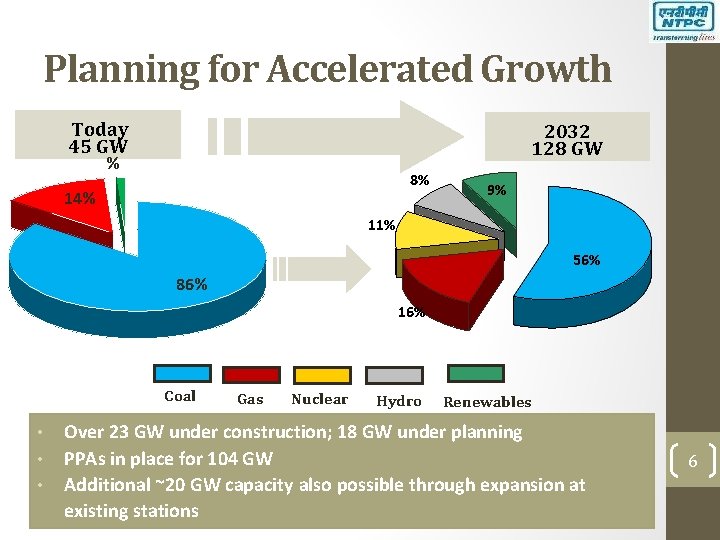
Planning for Accelerated Growth Today 45 GW 2032 128 GW % 8% 14% 9% 11% 56% 86% 16% Coal • • • Gas Nuclear Hydro Renewables Over 23 GW under construction; 18 GW under planning PPAs in place for 104 GW Additional ~20 GW capacity also possible through expansion at existing stations 6
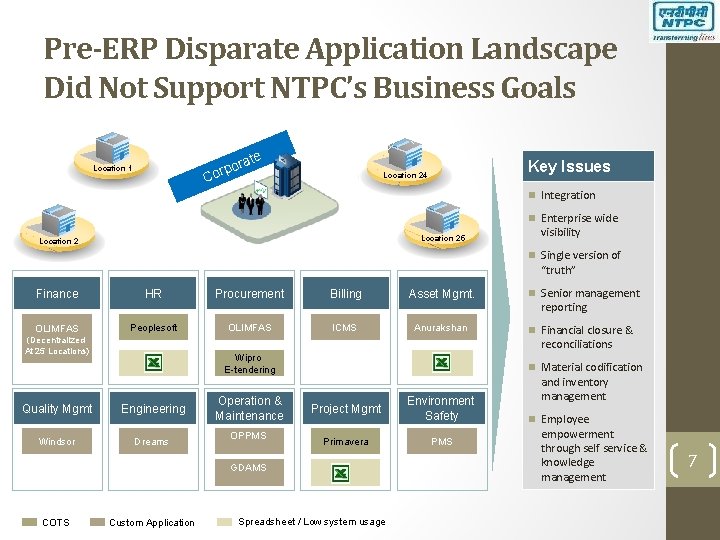
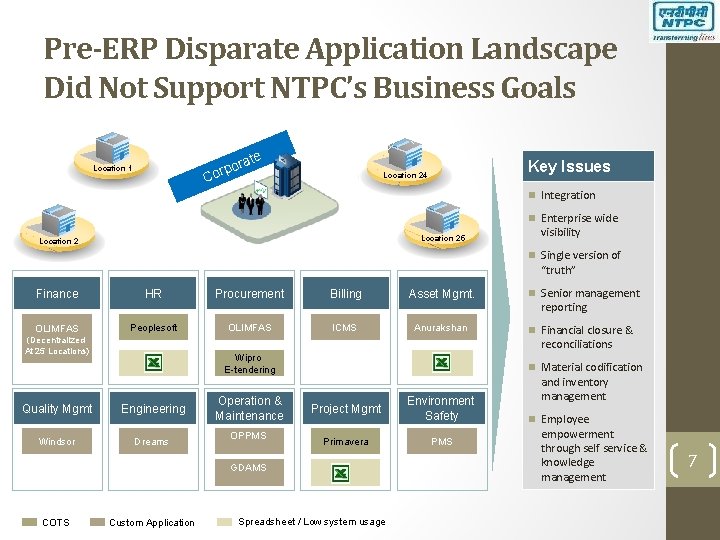
Pre-ERP Disparate Application Landscape Did Not Support NTPC’s Business Goals ate por Cor Location 1 Key Issues Location 24 Integration Enterprise wide Location 25 Location 2 visibility Single version of “truth” Finance HR Procurement Billing Asset Mgmt. OLIMFAS Peoplesoft OLIMFAS ICMS Anurakshan (Decentralized At 25 Locations) reporting Financial closure & reconciliations Wipro E-tendering Quality Mgmt Engineering Windsor Dreams Operation & Maintenance OPPMS Material codification Project Mgmt Environment Safety Primavera PMS GDAMS COTS Senior management Custom Application Spreadsheet / Low system usage and inventory management Employee empowerment through self service & knowledge management 7
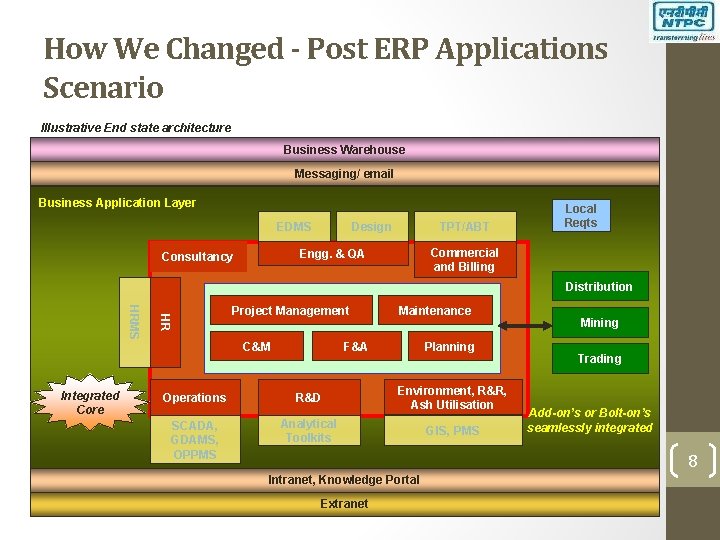
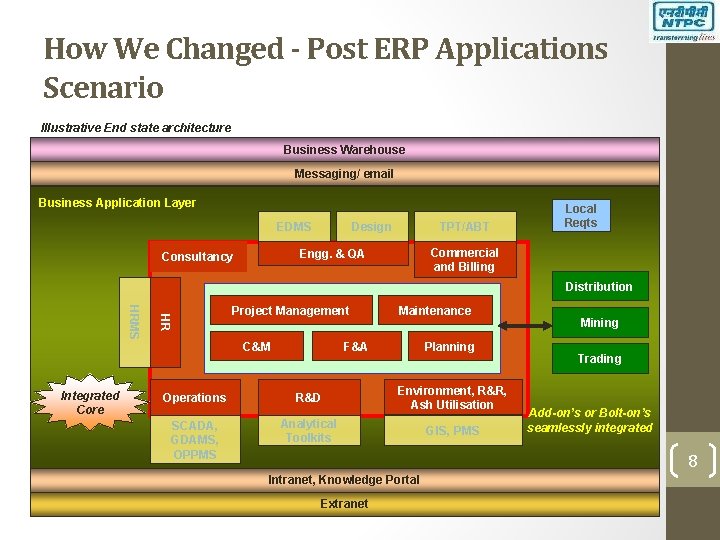
How We Changed - Post ERP Applications Scenario Illustrative End state architecture Business Warehouse Messaging/ email Business Application Layer EDMS Design TPT/ABT Commercial and Billing Engg. & QA Consultancy Local Reqts Distribution HR HRMS Integrated Core Project Management C&M Maintenance F&A Operations R&D SCADA, GDAMS, OPPMS Analytical Toolkits Planning Environment, R&R, Ash Utilisation GIS, PMS Mining Trading Add-on’s or Bolt-on’s seamlessly integrated 8 Intranet, Knowledge Portal Extranet
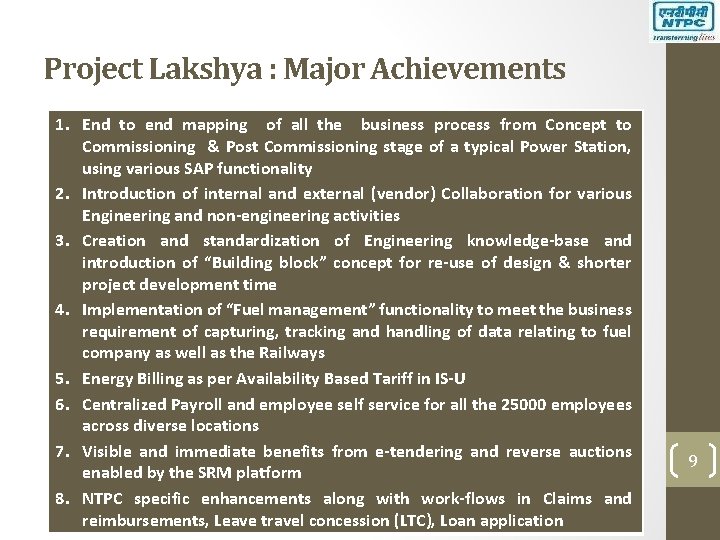
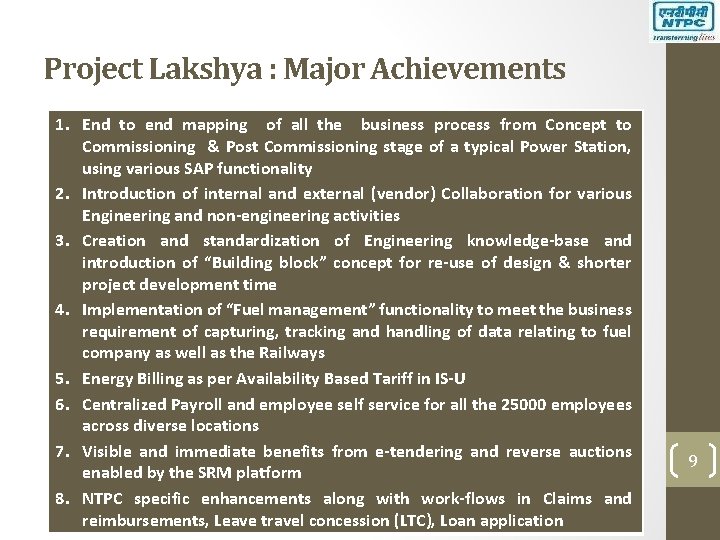
Project Lakshya : Major Achievements 1. End to end mapping of all the business process from Concept to Commissioning & Post Commissioning stage of a typical Power Station, using various SAP functionality 2. Introduction of internal and external (vendor) Collaboration for various Engineering and non-engineering activities 3. Creation and standardization of Engineering knowledge-base and introduction of “Building block” concept for re-use of design & shorter project development time 4. Implementation of “Fuel management” functionality to meet the business requirement of capturing, tracking and handling of data relating to fuel company as well as the Railways 5. Energy Billing as per Availability Based Tariff in IS-U 6. Centralized Payroll and employee self service for all the 25000 employees across diverse locations 7. Visible and immediate benefits from e-tendering and reverse auctions enabled by the SRM platform 8. NTPC specific enhancements along with work-flows in Claims and reimbursements, Leave travel concession (LTC), Loan application 9
Importance of IT Security • Information is the oxygen of the modern age. • In the current environment, almost everything is IT enabled. • Wide variety of personal, financial and organizational assets are in digital form. • Social life of individuals is increasingly becoming IT centric. • Crime related to IT is progressing in tandem with IT growth. 10
Why IT Security is a concern? • • Privacy Concerns Copyright Violations Identity Theft Resource Violations Reputation Protection Meet Expectations Laws & Regulations 11
Cyber Security Terminology • Vulnerability • A Weakness which allows an attacker to reduce a system's information security. • Attribute of the system itself. • Vulnerability CAN be treated or patched. • Zero day Vulnerability • A zero-day vulnerability is previously unknown vulnerability in a software, which gets exploited or attacked. • It is called zero-day, since the developer has had no time to fix it, and no patch has been released for it yet. 12
Cyber Security Terminology • Threat • A threat is an agent that may want to harm the target organization. • Threats include organized crime, spyware, malware, adware companies, and disgruntled internal employees. • Hackers • A hacker is someone who seeks and exploits weaknesses in a computer system or a computer network • Blackhat: violates computer security for maliciousness or for personal gain • Whitehat : breaks security for non-malicious reasons. • Script Kiddies: An unskilled hacker who breaks into computer systems by using automated tools written by others 13
Types of IT Security Threats • Password Cracking • Password cracking is the process of recovering passwords from data that have been stored in or transmitted by a computer system. • Common methods of Password Cracking • • • Dictionary attacks Brute Force attacks Key loggers Phishing Social Engineering 14
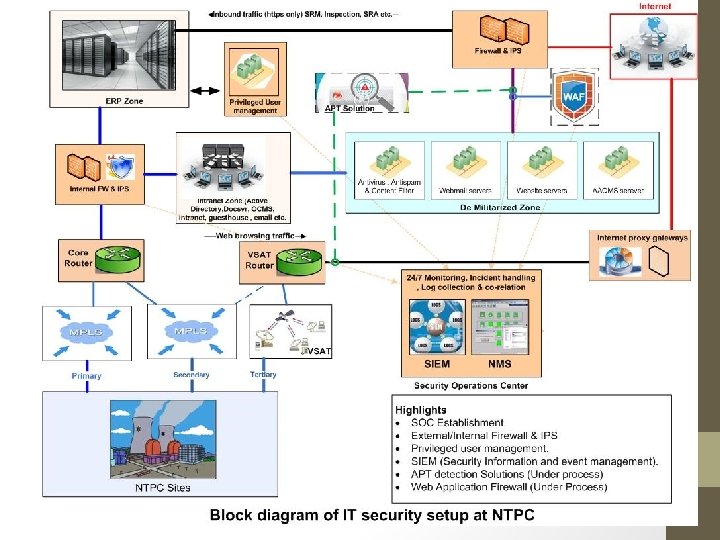
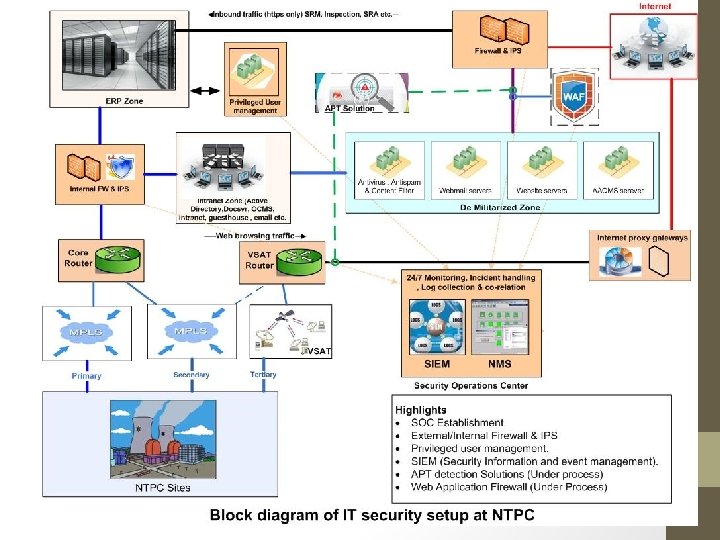
IT Security Infrastructure at NTPC • Perimeter Firewall with IPS (HA) at DC and DR • FW & IPS for LAN Security • SIEM (Security Information & Event Management) • Privileged User Management 15

Perimeter Firewall at DC and DR • Fortigate 1000 C in High availability • Next generation Firewall with Application control and Intrusion prevention system • Blocking based on Geo-location possible. 16
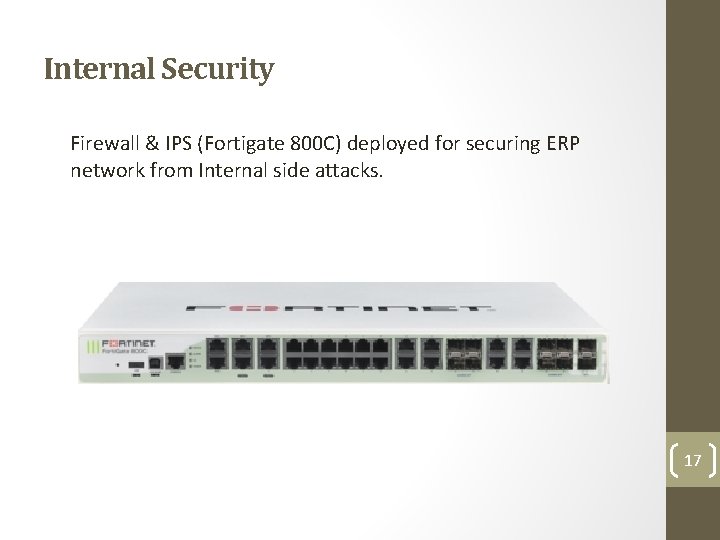
Internal Security Firewall & IPS (Fortigate 800 C) deployed for securing ERP network from Internal side attacks. 17

Q&A 19
Thank You 20