ISTIO Cadi Sidecars Capabilities map ONAP Sec Com
ISTIO /Cadi Sidecars Capabilities map ONAP Sec. Com
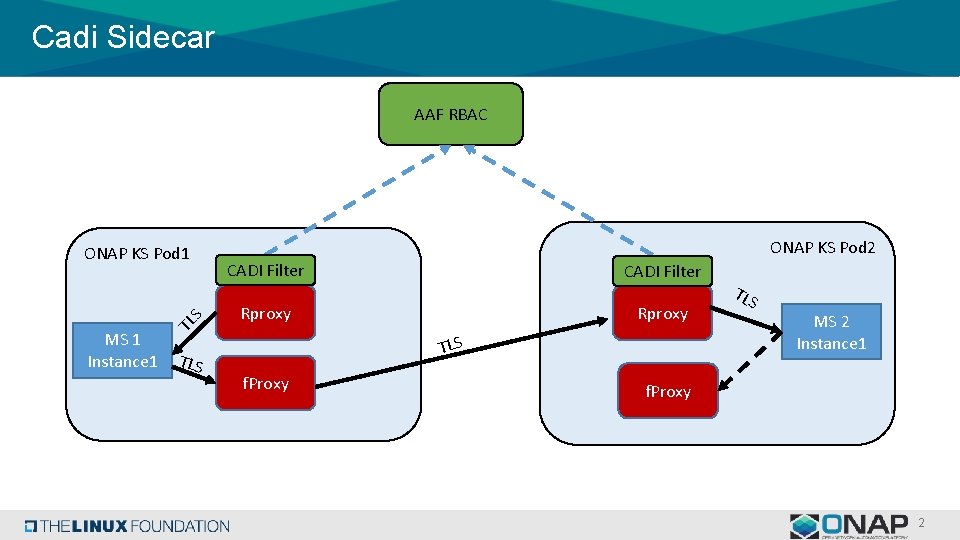
Cadi Sidecar AAF RBAC MS 1 Instance 1 TL S ONAP KS Pod 1 TLS ONAP KS Pod 2 CADI Filter Rproxy TLS f. Proxy TLS MS 2 Instance 1 f. Proxy 2
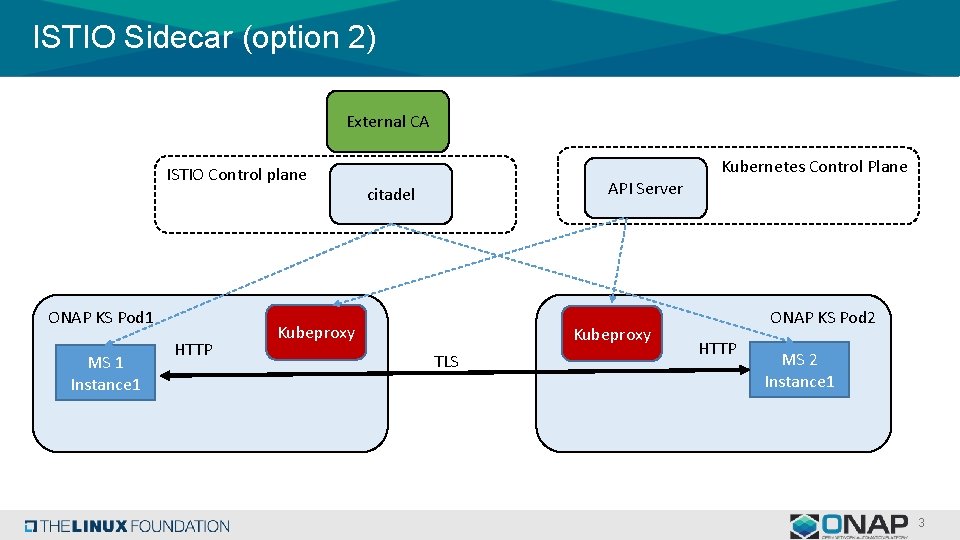
ISTIO Sidecar (option 2) External CA ISTIO Control plane ONAP KS Pod 1 MS 1 Instance 1 HTTP Kubernetes Control Plane API Server citadel Kubeproxy TLS ONAP KS Pod 2 HTTP MS 2 Instance 1 3
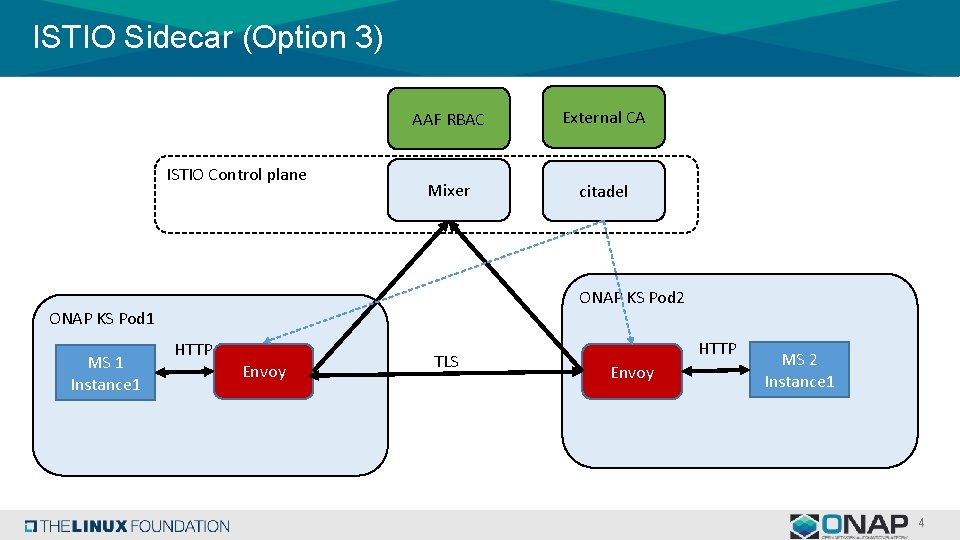
ISTIO Sidecar (Option 3) ISTIO Control plane AAF RBAC External CA Mixer citadel ONAP KS Pod 2 ONAP KS Pod 1 MS 1 Instance 1 HTTP Envoy TLS HTTP Envoy MS 2 Instance 1 4
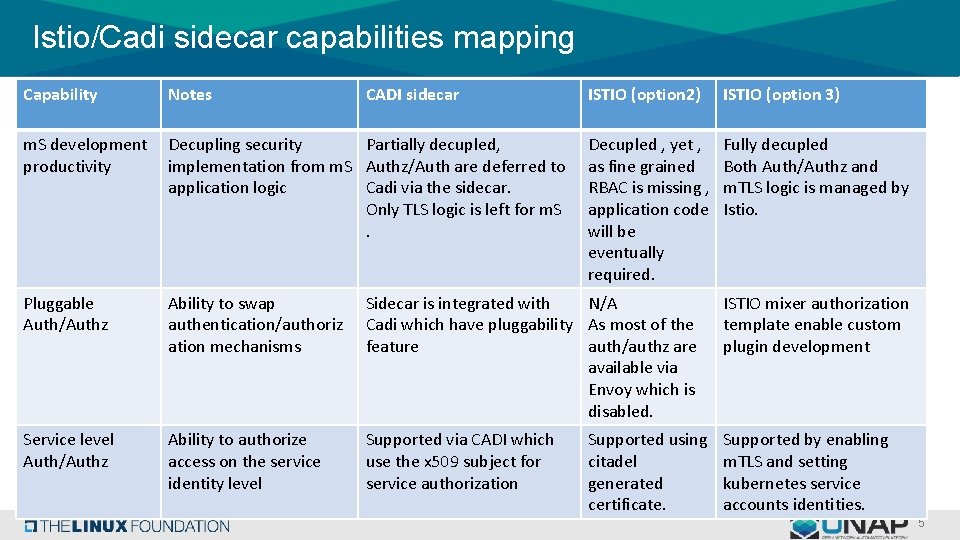
Istio/Cadi sidecar capabilities mapping Capability Notes CADI sidecar ISTIO (option 2) ISTIO (option 3) m. S development productivity Decupling security Partially decupled, implementation from m. S Authz/Auth are deferred to application logic Cadi via the sidecar. Only TLS logic is left for m. S. Decupled , yet , as fine grained RBAC is missing , application code will be eventually required. Fully decupled Both Auth/Authz and m. TLS logic is managed by Istio. Pluggable Auth/Authz Ability to swap authentication/authoriz ation mechanisms Sidecar is integrated with N/A Cadi which have pluggability As most of the feature auth/authz are available via Envoy which is disabled. ISTIO mixer authorization template enable custom plugin development Service level Auth/Authz Ability to authorize access on the service identity level Supported via CADI which use the x 509 subject for service authorization Supported by enabling m. TLS and setting kubernetes service accounts identities. Supported using citadel generated certificate. 5
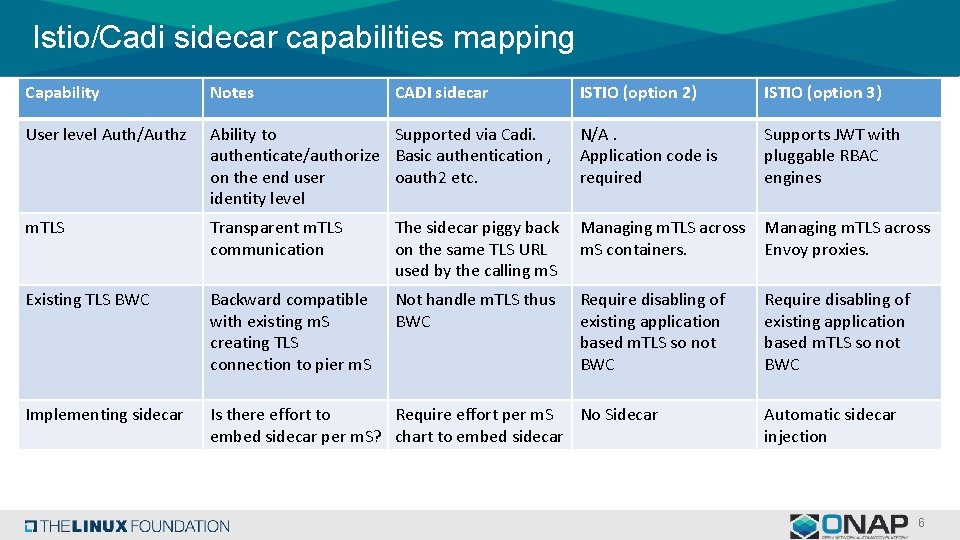
Istio/Cadi sidecar capabilities mapping Capability Notes User level Auth/Authz CADI sidecar ISTIO (option 2) ISTIO (option 3) Ability to Supported via Cadi. authenticate/authorize Basic authentication , on the end user oauth 2 etc. identity level N/A. Application code is required Supports JWT with pluggable RBAC engines m. TLS Transparent m. TLS communication The sidecar piggy back on the same TLS URL used by the calling m. S Managing m. TLS across m. S containers. Managing m. TLS across Envoy proxies. Existing TLS BWC Backward compatible with existing m. S creating TLS connection to pier m. S Not handle m. TLS thus BWC Require disabling of existing application based m. TLS so not BWC Implementing sidecar Is there effort to Require effort per m. S No Sidecar embed sidecar per m. S? chart to embed sidecar Automatic sidecar injection 6

s
- Slides: 7