ISTIO Cadi Sidecars Capabilities map ONAP Sec Com
ISTIO /Cadi Sidecars Capabilities map ONAP Sec. Com
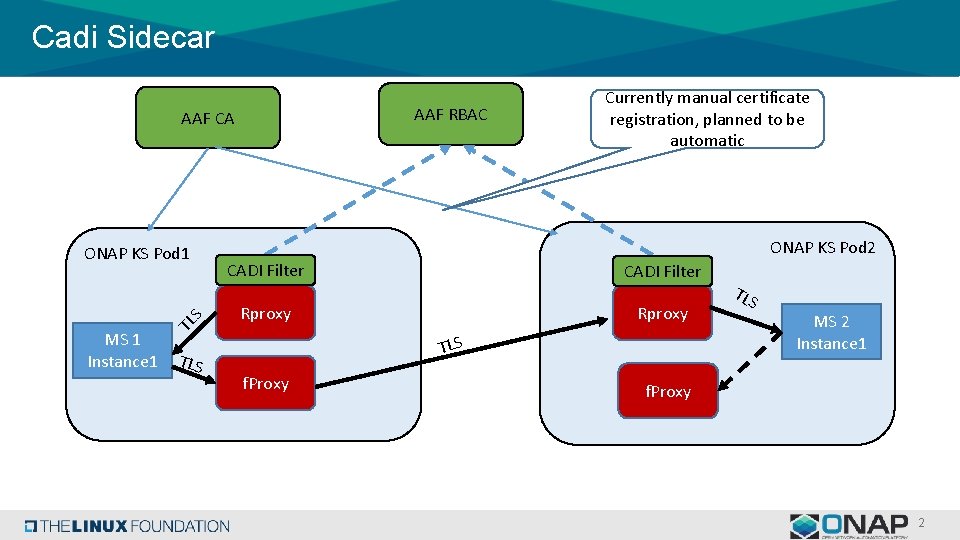
Cadi Sidecar AAF RBAC AAF CA MS 1 Instance 1 TL S ONAP KS Pod 1 TLS Currently manual certificate registration, planned to be automatic ONAP KS Pod 2 CADI Filter Rproxy TLS f. Proxy TLS MS 2 Instance 1 f. Proxy 2
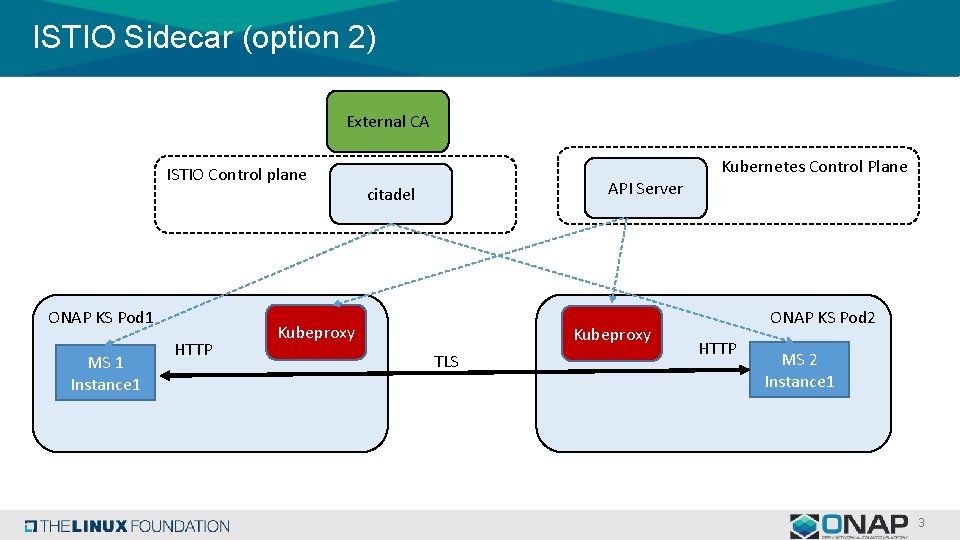
ISTIO Sidecar (option 2) External CA ISTIO Control plane ONAP KS Pod 1 MS 1 Instance 1 HTTP Kubernetes Control Plane API Server citadel Kubeproxy TLS ONAP KS Pod 2 HTTP MS 2 Instance 1 3
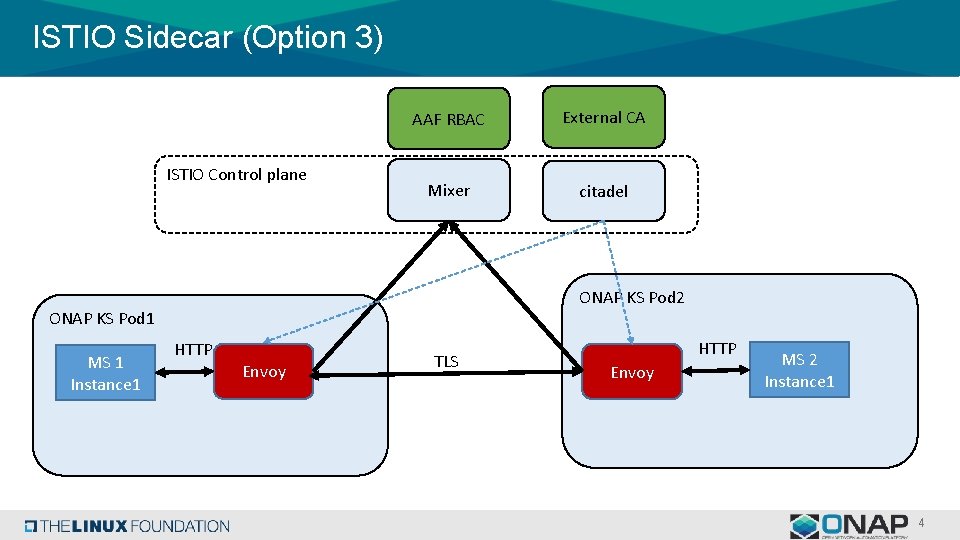
ISTIO Sidecar (Option 3) ISTIO Control plane AAF RBAC External CA Mixer citadel ONAP KS Pod 2 ONAP KS Pod 1 MS 1 Instance 1 HTTP Envoy TLS HTTP Envoy MS 2 Instance 1 4
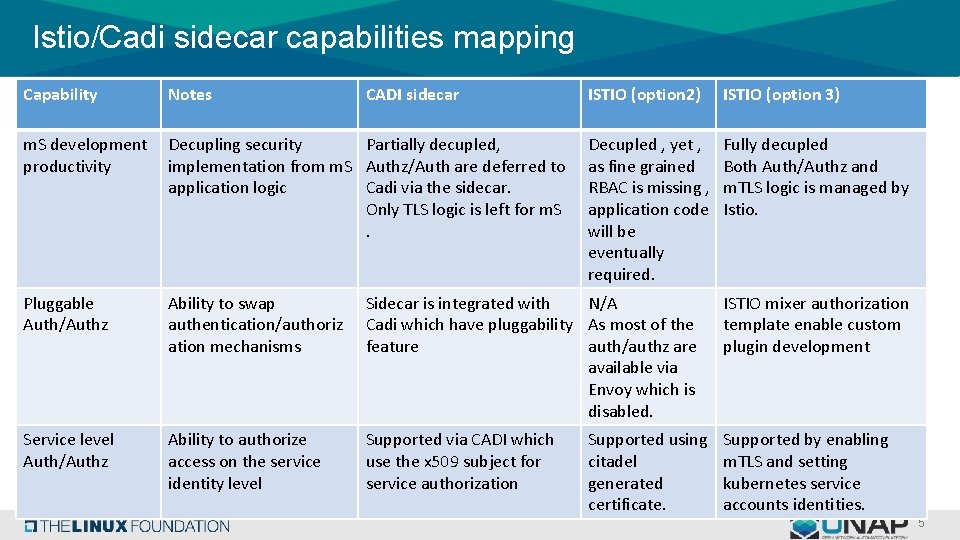
Istio/Cadi sidecar capabilities mapping Capability Notes CADI sidecar ISTIO (option 2) ISTIO (option 3) m. S development productivity Decupling security Partially decupled, implementation from m. S Authz/Auth are deferred to application logic Cadi via the sidecar. Only TLS logic is left for m. S. Decupled , yet , as fine grained RBAC is missing , application code will be eventually required. Fully decupled Both Auth/Authz and m. TLS logic is managed by Istio. Pluggable Auth/Authz Ability to swap authentication/authoriz ation mechanisms Sidecar is integrated with N/A Cadi which have pluggability As most of the feature auth/authz are available via Envoy which is disabled. ISTIO mixer authorization template enable custom plugin development Service level Auth/Authz Ability to authorize access on the service identity level Supported via CADI which use the x 509 subject for service authorization Supported by enabling m. TLS and setting kubernetes service accounts identities. Supported using citadel generated certificate. 5
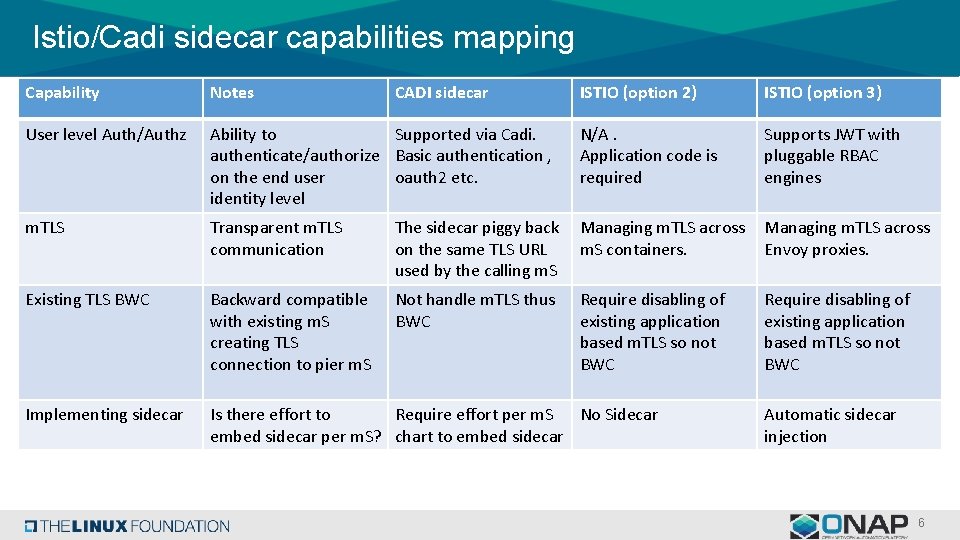
Istio/Cadi sidecar capabilities mapping Capability Notes User level Auth/Authz CADI sidecar ISTIO (option 2) ISTIO (option 3) Ability to Supported via Cadi. authenticate/authorize Basic authentication , on the end user oauth 2 etc. identity level N/A. Application code is required Supports JWT with pluggable RBAC engines m. TLS Transparent m. TLS communication The sidecar piggy back on the same TLS URL used by the calling m. S Managing m. TLS across m. S containers. Managing m. TLS across Envoy proxies. Existing TLS BWC Backward compatible with existing m. S creating TLS connection to pier m. S Not handle m. TLS thus BWC Require disabling of existing application based m. TLS so not BWC Implementing sidecar Is there effort to Require effort per m. S No Sidecar embed sidecar per m. S? chart to embed sidecar Automatic sidecar injection 6
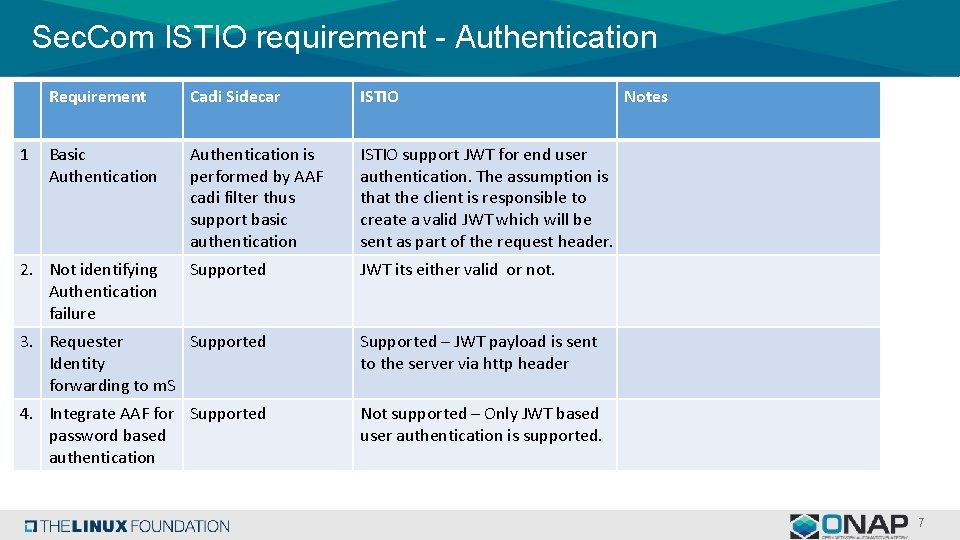
Sec. Com ISTIO requirement - Authentication 1 Requirement Cadi Sidecar ISTIO Basic Authentication is performed by AAF cadi filter thus support basic authentication ISTIO support JWT for end user authentication. The assumption is that the client is responsible to create a valid JWT which will be sent as part of the request header. Supported JWT its either valid or not. 2. Not identifying Authentication failure 3. Requester Supported Identity forwarding to m. S Supported – JWT payload is sent to the server via http header 4. Integrate AAF for Supported password based authentication Not supported – Only JWT based user authentication is supported. Notes 7
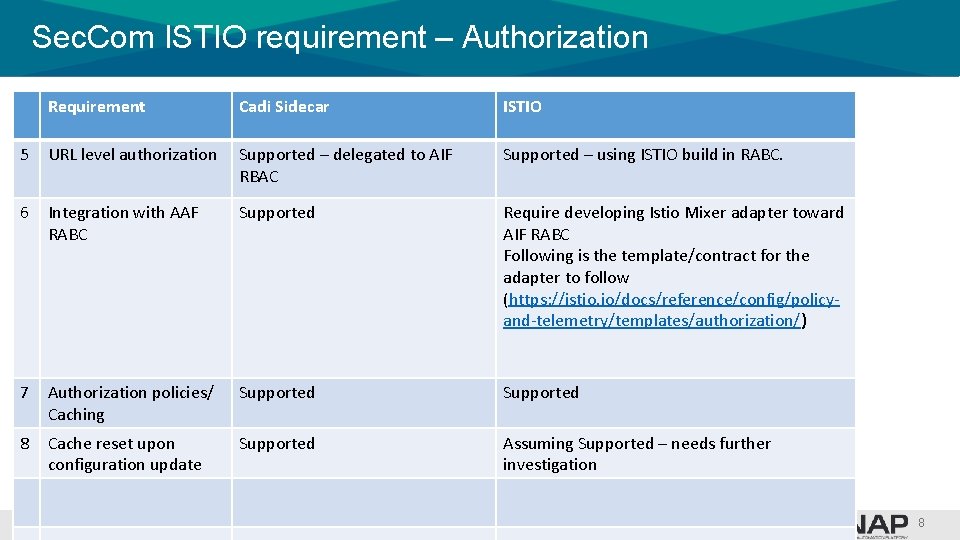
Sec. Com ISTIO requirement – Authorization Requirement Cadi Sidecar ISTIO 5 URL level authorization Supported – delegated to AIF RBAC Supported – using ISTIO build in RABC. 6 Integration with AAF RABC Supported Require developing Istio Mixer adapter toward AIF RABC Following is the template/contract for the adapter to follow (https: //istio. io/docs/reference/config/policyand-telemetry/templates/authorization/) 7 Authorization policies/ Caching Supported 8 Cache reset upon configuration update Supported Assuming Supported – needs further investigation 8
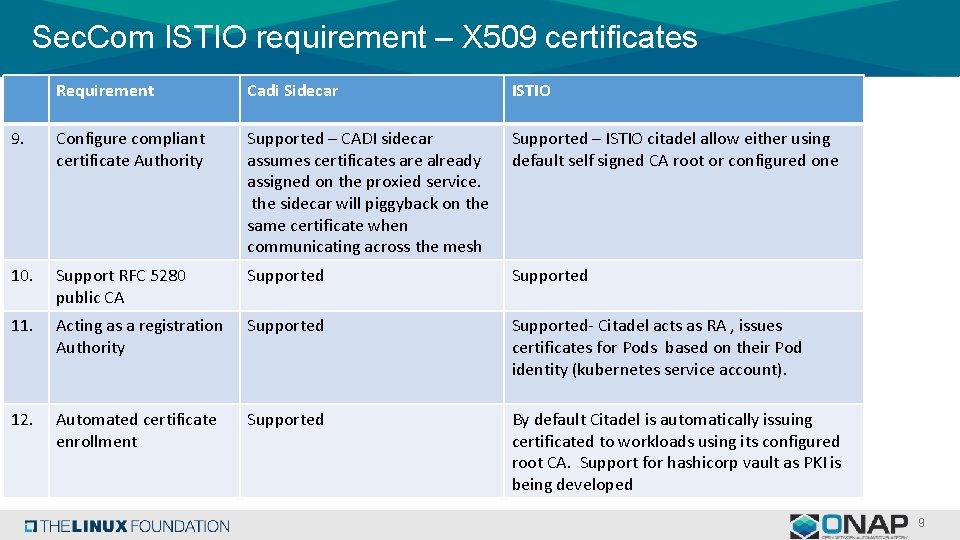
Sec. Com ISTIO requirement – X 509 certificates Requirement Cadi Sidecar ISTIO 9. Configure compliant certificate Authority Supported – CADI sidecar assumes certificates are already assigned on the proxied service. the sidecar will piggyback on the same certificate when communicating across the mesh Supported – ISTIO citadel allow either using default self signed CA root or configured one 10. Support RFC 5280 public CA Supported 11. Acting as a registration Authority Supported- Citadel acts as RA , issues certificates for Pods based on their Pod identity (kubernetes service account). 12. Automated certificate enrollment Supported By default Citadel is automatically issuing certificated to workloads using its configured root CA. Support for hashicorp vault as PKI is being developed 9
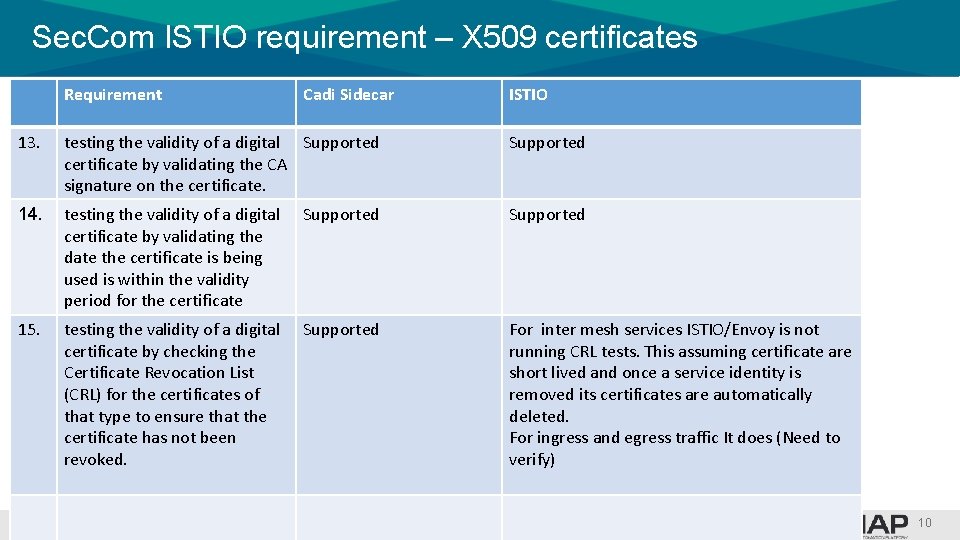
Sec. Com ISTIO requirement – X 509 certificates Requirement Cadi Sidecar ISTIO 13. testing the validity of a digital Supported certificate by validating the CA signature on the certificate. Supported 14. testing the validity of a digital certificate by validating the date the certificate is being used is within the validity period for the certificate Supported 15. testing the validity of a digital certificate by checking the Certificate Revocation List (CRL) for the certificates of that type to ensure that the certificate has not been revoked. Supported For inter mesh services ISTIO/Envoy is not running CRL tests. This assuming certificate are short lived and once a service identity is removed its certificates are automatically deleted. For ingress and egress traffic It does (Need to verify) 10
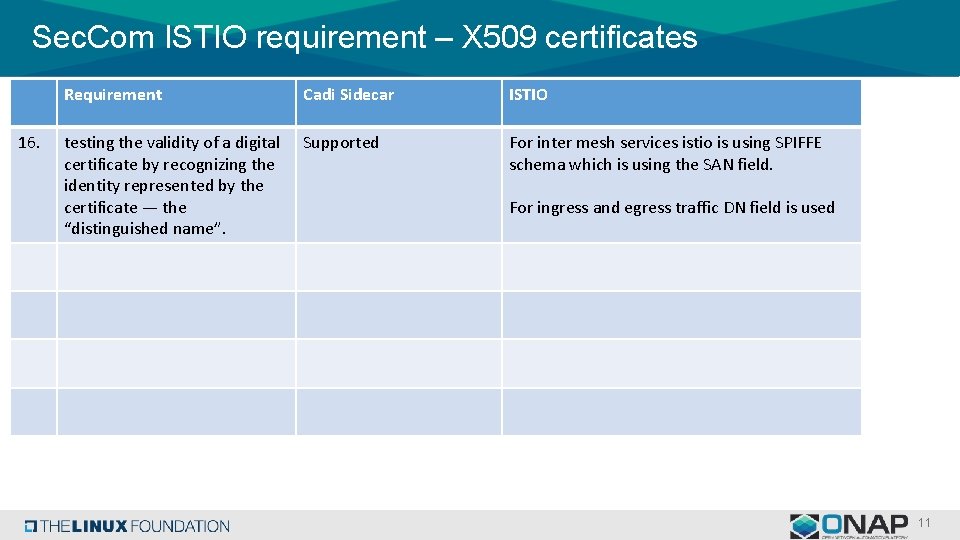
Sec. Com ISTIO requirement – X 509 certificates 16. Requirement Cadi Sidecar ISTIO testing the validity of a digital certificate by recognizing the identity represented by the certificate — the “distinguished name”. Supported For inter mesh services istio is using SPIFFE schema which is using the SAN field. For ingress and egress traffic DN field is used 11
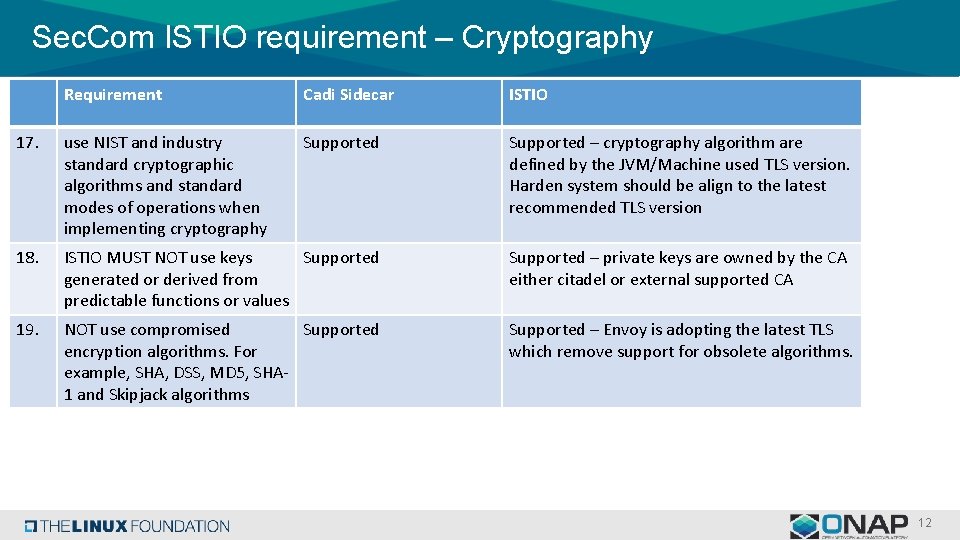
Sec. Com ISTIO requirement – Cryptography Requirement Cadi Sidecar ISTIO 17. use NIST and industry standard cryptographic algorithms and standard modes of operations when implementing cryptography Supported – cryptography algorithm are defined by the JVM/Machine used TLS version. Harden system should be align to the latest recommended TLS version 18. ISTIO MUST NOT use keys Supported generated or derived from predictable functions or values Supported – private keys are owned by the CA either citadel or external supported CA 19. NOT use compromised Supported encryption algorithms. For example, SHA, DSS, MD 5, SHA 1 and Skipjack algorithms Supported – Envoy is adopting the latest TLS which remove support for obsolete algorithms. 12
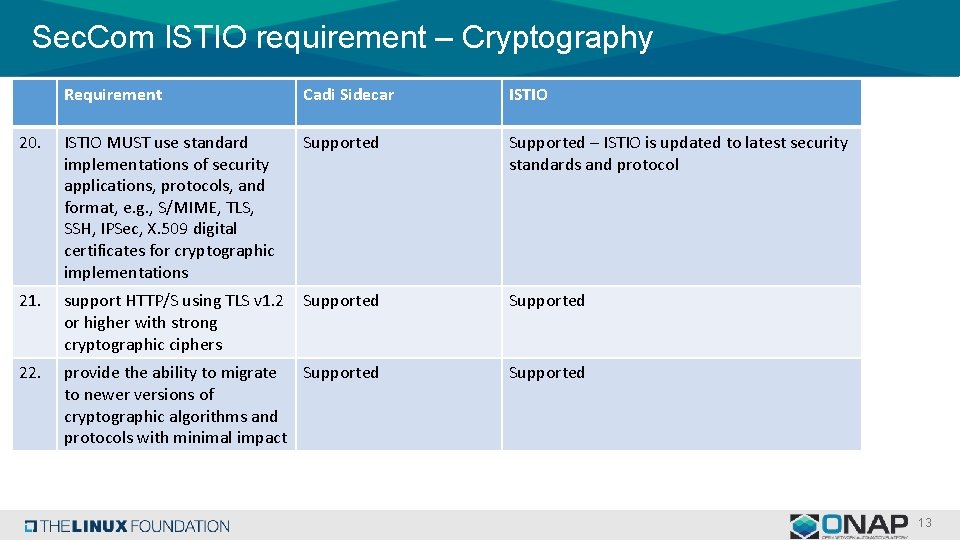
Sec. Com ISTIO requirement – Cryptography Requirement Cadi Sidecar ISTIO 20. ISTIO MUST use standard implementations of security applications, protocols, and format, e. g. , S/MIME, TLS, SSH, IPSec, X. 509 digital certificates for cryptographic implementations Supported – ISTIO is updated to latest security standards and protocol 21. support HTTP/S using TLS v 1. 2 or higher with strong cryptographic ciphers Supported 22. provide the ability to migrate Supported to newer versions of cryptographic algorithms and protocols with minimal impact Supported 13
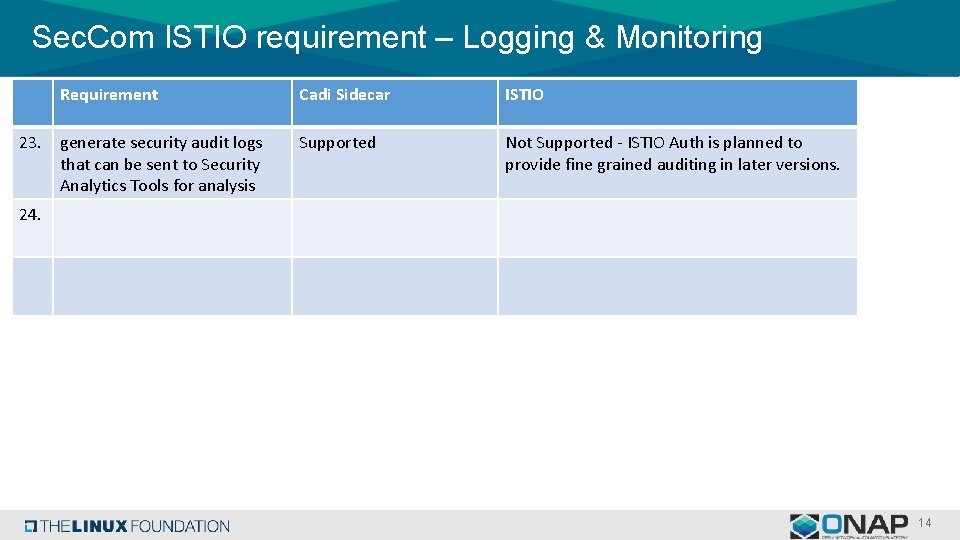
Sec. Com ISTIO requirement – Logging & Monitoring 23. Requirement Cadi Sidecar ISTIO generate security audit logs that can be sent to Security Analytics Tools for analysis Supported Not Supported - ISTIO Auth is planned to provide fine grained auditing in later versions. 24. 14

s
- Slides: 15