IST2002 506883 Secure contracts signed by mobile Phone
IST-2002 -506883 Secure contracts signed by mobile Phone Secure. Phone: a mobile phone with biometric authentication and e-signature support for dealing secure transactions on the fly Jacques Koreman, ISK
What is a Secure. Phone? • Mobile communications device that enables exchange of text/audio documents during a phone call to draw legally valid transactions. • Secure communication uses e-signing in a system using front-edge technologies (wireless networking, double-key cryptography). • Biometric recogniser enables strong authentication by comparing live biometric features with models trained on enrolment data. • Biometric authentication grants access to built-in e-signing facilities integrated on the PDA/SIM. Dept. of Telematics, NTNU, 07. 12. 2006 2
Presentation Outline • • • Secure. Phone concept and use Project aim 1: secure exchange Project aim 2: biometric recognition – on PDA, high performance – on SIMcard, proof-of-concept Conclusion Outlook Dept. of Telematics, NTNU, 07. 12. 2006 3
Project aim 1: secure exchange Secure PKI (personal key infrastructure) • Public key encryption technology is used for e-signature, i. e. to enforce data integrity and non-repudiation • Standard e-signature certificates and procedures are used for certificate verification and management, so documents e-signed by means of the Secure. Phone have the same legal validity as documents e-signed by other means. Dept. of Telematics, NTNU, 07. 12. 2006 4
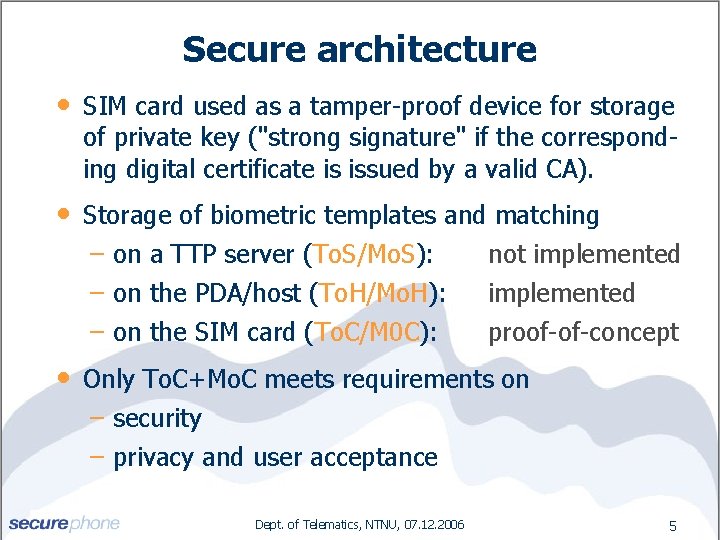
Secure architecture • SIM card used as a tamper-proof device for storage of private key ("strong signature" if the corresponding digital certificate is issued by a valid CA). • Storage of biometric templates and matching on a TTP server (To. S/Mo. S): not implemented on the PDA/host (To. H/Mo. H): implemented on the SIM card (To. C/M 0 C): proof-of-concept • Only To. C+Mo. C meets requirements on security privacy and user acceptance Dept. of Telematics, NTNU, 07. 12. 2006 5
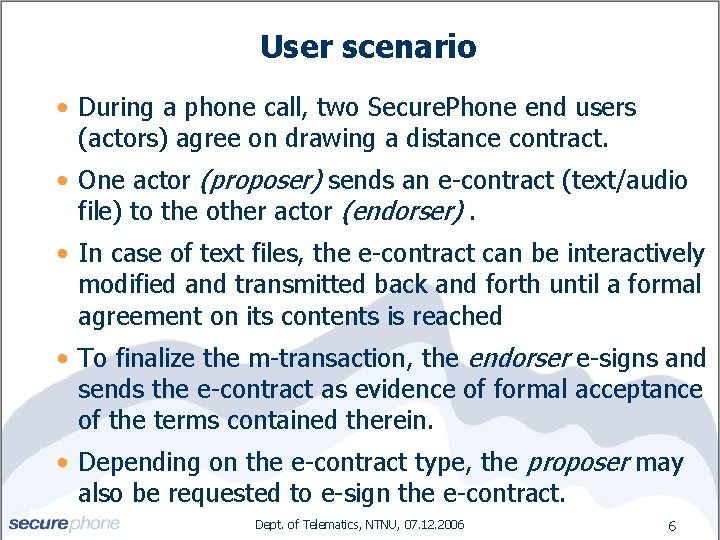
User scenario • During a phone call, two Secure. Phone end users (actors) agree on drawing a distance contract. • One actor (proposer) sends an e-contract (text/audio file) to the other actor (endorser). • In case of text files, the e-contract can be interactively modified and transmitted back and forth until a formal agreement on its contents is reached • To finalize the m-transaction, the endorser e-signs and sends the e-contract as evidence of formal acceptance of the terms contained therein. • Depending on the e-contract type, the proposer may also be requested to e-sign the e-contract. Dept. of Telematics, NTNU, 07. 12. 2006 6
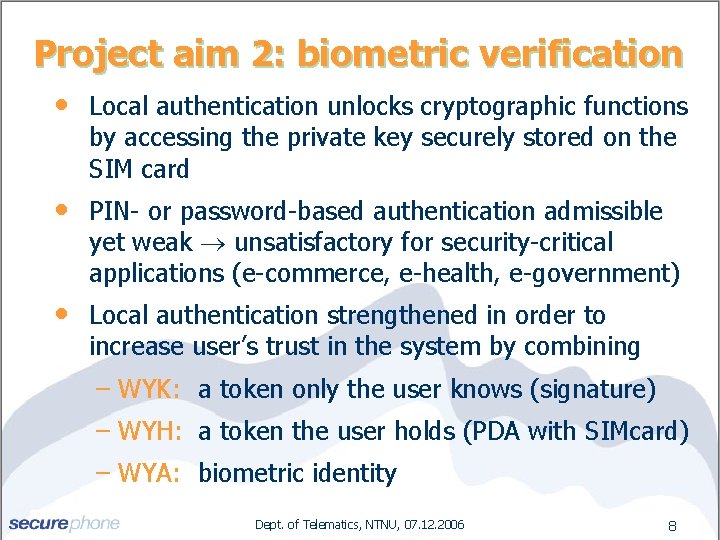
Project aim 2: biometric verification • Local authentication unlocks cryptographic functions by accessing the private key securely stored on the SIM card • PIN- or password-based authentication admissible yet weak unsatisfactory for security-critical applications (e-commerce, e-health, e-government) • Local authentication strengthened in order to increase user’s trust in the system by combining WYK: a token only the user knows (signature) WYH: a token the user holds (PDA with SIMcard) WYA: biometric identity Dept. of Telematics, NTNU, 07. 12. 2006 8
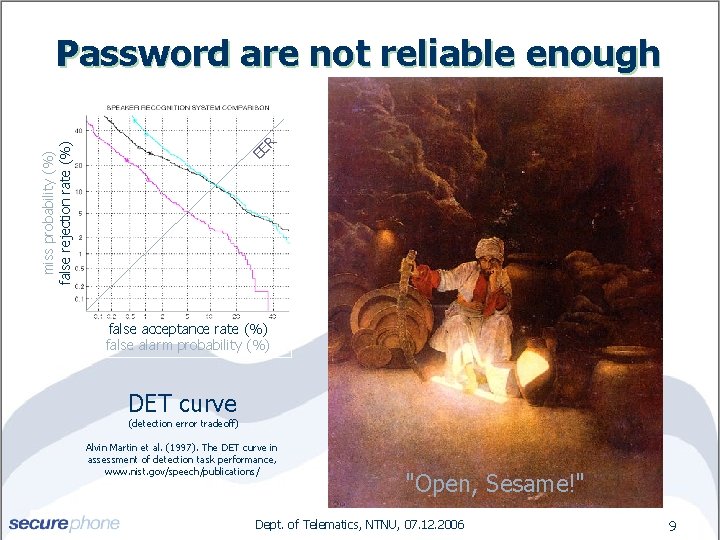
EE R miss probability (%) false rejection rate (%) Password are not reliable enough false acceptance rate (%) false alarm probability (%) DET curve (detection error tradeoff) Alvin Martin et al. (1997). The DET curve in assessment of detection task performance, www. nist. gov/speech/publications/ "Open, Sesame!" Dept. of Telematics, NTNU, 07. 12. 2006 9

Fusion of multiple modalities The Incredibles Dept. of Telematics, NTNU, 07. 12. 2006 10
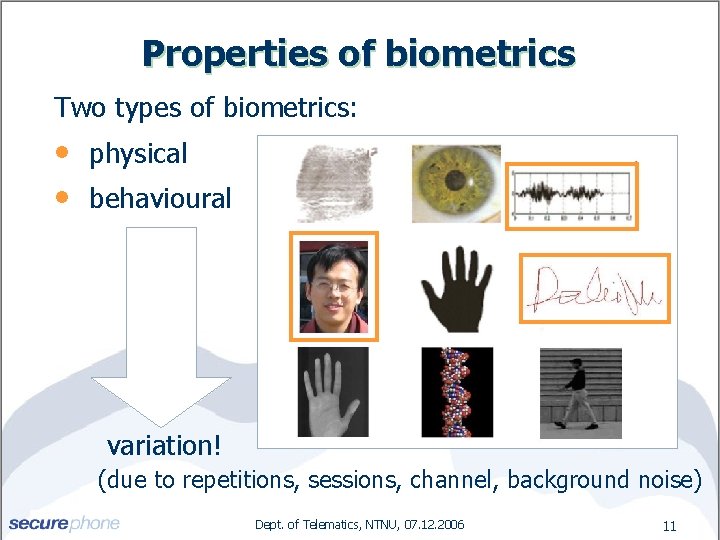
Properties of biometrics Two types of biometrics: • • physical behavioural variation! (due to repetitions, sessions, channel, background noise) Dept. of Telematics, NTNU, 07. 12. 2006 11
Why face, voice and signature? These biometrics have a high user acceptance: • • • chosen biometrics are user-friendly very short enrolment session capture does not require special hardware difficult to impostorise all three modalities biometric profile remains local, guaranteeing privacy processing of the biometric data also local (privacy) Dept. of Telematics, NTNU, 07. 12. 2006 12
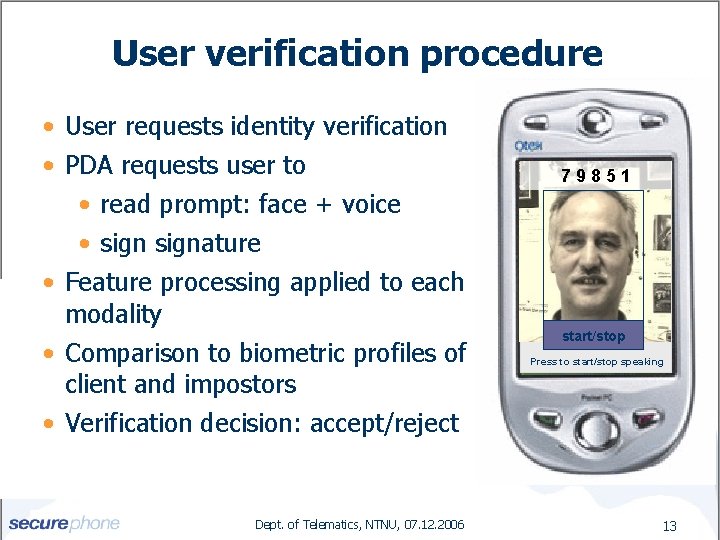
User verification procedure • User requests identity verification • PDA requests user to • read prompt: face + voice • signature • Feature processing applied to each modality • Comparison to biometric profiles of client and impostors • Verification decision: accept/reject Dept. of Telematics, NTNU, 07. 12. 2006 79851 start/stop Press to start/stop speaking 13
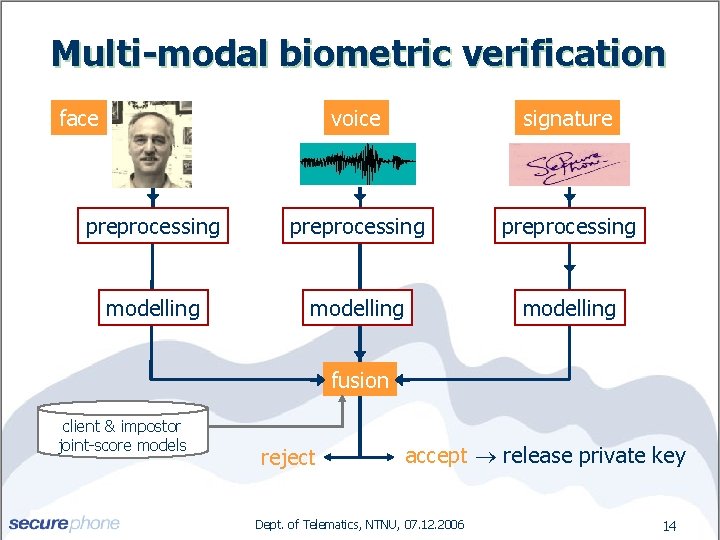
Multi-modal biometric verification face voice signature preprocessing modelling fusion client & impostor joint-score models reject accept release private key Dept. of Telematics, NTNU, 07. 12. 2006 14
Voice verification • Fixed 5 -digits prompt – conceptually neutral, easily extendable • 22 KHz sampling • Online energy based non-speech frame removal • MFCCs with online CMS and first-order time difference features (10 -ms frames) • Features modelled by 100 -Gaussian GMM, with UBM for model initialisation and score normalisation • Training on data from 2 indoor and 2 outdoor recordings from one session, testing on similar data from another session Dept. of Telematics, NTNU, 07. 12. 2006 15
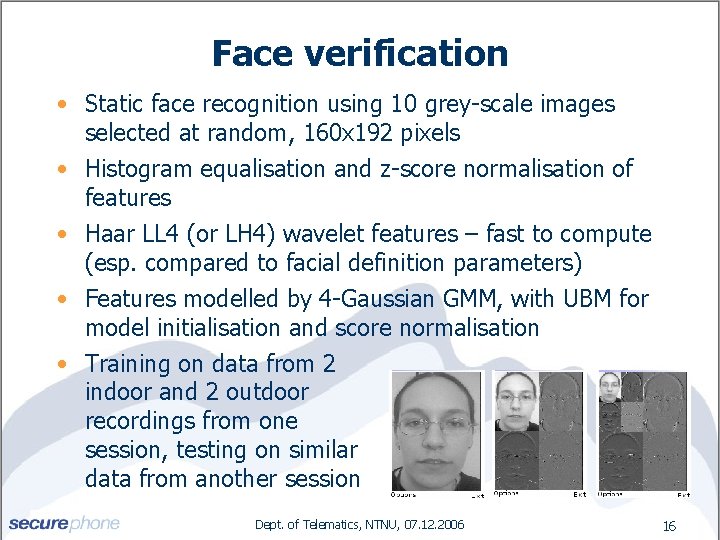
Face verification • Static face recognition using 10 grey-scale images selected at random, 160 x 192 pixels • Histogram equalisation and z-score normalisation of features • Haar LL 4 (or LH 4) wavelet features – fast to compute (esp. compared to facial definition parameters) • Features modelled by 4 -Gaussian GMM, with UBM for model initialisation and score normalisation • Training on data from 2 indoor and 2 outdoor recordings from one session, testing on similar data from another session Dept. of Telematics, NTNU, 07. 12. 2006 16
Signature verification • Shift normalisation, but no rotation or scaling • 2 D coordinates (100 Hz) augmented by time difference features, curvature, etc. – total 19 features Note: no pressure or angles available, since obtained from PDA’s touch screen, not from writing pad • Fast to compute • Features modelled by 100 Gaussian GMM pdf – UBM used for model initialisation and score normalisation • Training and testing on data from one session Dept. of Telematics, NTNU, 07. 12. 2006 17
Fusion • For each modality S(i) = log p(Xi|C) - log p(Xi|I), latter for casual impostors, only signatures impostorised by experts W O E D O M • Best LLR score fusion was obtained for GMM scores modelling, i. e. modelling both client and impostor joint score pdf’s by diagonal covariance GMMs: Fused-score = log p(S|C) - log p(S|I) H S
Tests on PDAtabase • Database recorded on Qtek 2020 PDA for realistic conditions (sensors, environment) • 60 English subjects: 24 for UBM, 18 for g 1, 18 for g 2. Accept/reject threshold optimised on g 1, then evaluated on g 2, and vice versa • Video (voice + face): 6 x 5 -digit, 10 -digit and phrase prompts; 2 sessions, with 2 inside and 2 outside recordings per session • Signatures in one session, 20 expert impostorisations each • Virtual couplings of audio-visual with signature data • Automatic test script to test many possible configuration • User just provides executables for feature modelling, scores generation and scores fusion
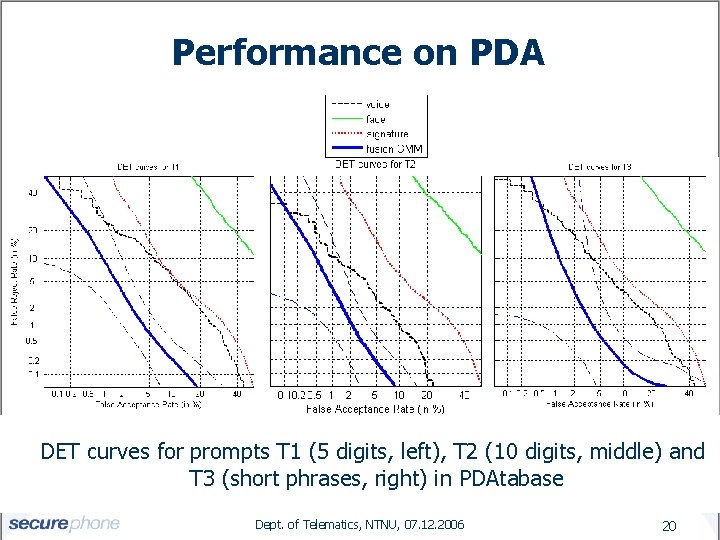
Performance on PDA DET curves for prompts T 1 (5 digits, left), T 2 (10 digits, middle) and T 3 (short phrases, right) in PDAtabase Dept. of Telematics, NTNU, 07. 12. 2006 20
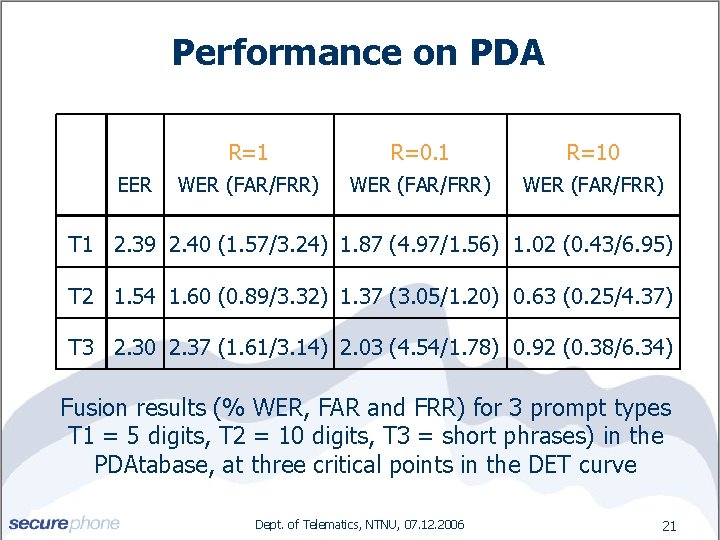
Performance on PDA EER R=1 R=0. 1 R=10 WER (FAR/FRR) T 1 2. 39 2. 40 (1. 57/3. 24) 1. 87 (4. 97/1. 56) 1. 02 (0. 43/6. 95) T 2 1. 54 1. 60 (0. 89/3. 32) 1. 37 (3. 05/1. 20) 0. 63 (0. 25/4. 37) T 3 2. 30 2. 37 (1. 61/3. 14) 2. 03 (4. 54/1. 78) 0. 92 (0. 38/6. 34) Fusion results (% WER, FAR and FRR) for 3 prompt types T 1 = 5 digits, T 2 = 10 digits, T 3 = short phrases) in the PDAtabase, at three critical points in the DET curve Dept. of Telematics, NTNU, 07. 12. 2006 21
Implementation constraints • PDA main processor allows speech preprocessing in real time for 22 k. Hz signals Note: signal directly from mic, therefore > 8 k. Hz • Only data on the SIM card is secure, so all biometric models must be stored and processed on the SIM, which has very limited computational resources • SIM model storage limited to 40 K: text-dependent prompts Note: text-independent prompts or varied textdependent prompts are more secure, but would require 200 -400 K • Enrolment can use only one short indoor session Dept. of Telematics, NTNU, 07. 12. 2006 22
Performance on SIMcard • SIM processor very slow: single verification 53 min. ! • Most time goes to voice and signature processing: large #frames and models with many Gaussians. • Drastic measures needed: global processing. • By using means and standard deviations across all frames in the utterance/signature, the number of frames is reduced to one. • Simpler data require few mixtures for GMM modelling • Single verification now under 1 second, but performance for T 1 is now 10. 5% EER proof-of-concept, but performance must be improved! Dept. of Telematics, NTNU, 07. 12. 2006 23
Conclusion Deal secure m-contracts during a mobile phone call • secure: PKI with private key stored on SIM card • dependable: multi-modal: voice, face, signature • user-friendly: familiar, intuitive, non-intrusive • flexible: legally binding text/audio transactions • low-cost: no special hardware needed • dynamic: mobile (anytime, anywhere) Dept. of Telematics, NTNU, 07. 12. 2006 25
Outlook • In FP 7, many opportunities for security and trust projects • Security and trust do not only depend on the communication channel • • but also on the identity of the communication partner for which biometric recognition can be used If you see a role for biometric recognition in your proposal, do not hesitate to contact me! Dept. of Telematics, NTNU, 07. 12. 2006 26

Secure contracts signed by mobile Phone IST-2002 -506883 http: //www. secure-phone. info Please take my business card or e-mail me at jacques. koreman@hf. ntnu. no Dept. of Telematics, NTNU, 07. 12. 2006 27
- Slides: 25