IST 210 Is Secure Database an Oxymoron IST
IST 210 Is “Secure Database” an Oxymoron

IST 210 New technology n n We all demand more from our technology Devices’ functions start to converge n n n PDA/Phone/Pager devices Networks are extending a DBMSs functionality This can have unintended, and often negative consequences 2
IST 210 Bluetooth n Becoming pervasive n n n Acura, BMW and Daimler-Chrysler vehicles Nokia, Sony-Ericsson and Motorola cell phones Laptops PDAs The convenience and cool-factor are undeniable n n Lara Croft in Tomb Raider Wireless modems Wireless GPS modules Headsets and car phone kits 3
IST 210 Bluejacking or Bluesnarfing n n There’s a new sport - “Warnibbling” Using “Bluesnarf”, attackers can n Use your equipment without your knowledge or consent n n Download your contact list Your last-dialed number list Wireless Internet access Outgoing phone calls Text messages Bluejacking n Anonymous text messages to your phone 4
IST 210 n n Wireless LANs A whole new list of problems and threats Wireless LAN attacks n n n War Driving/War Flying (!) War Chalking Other issues n n n Drive-by spamming Drive-by worming Printer abuse Vo. IP over 802. 11 Theft of data and more 5
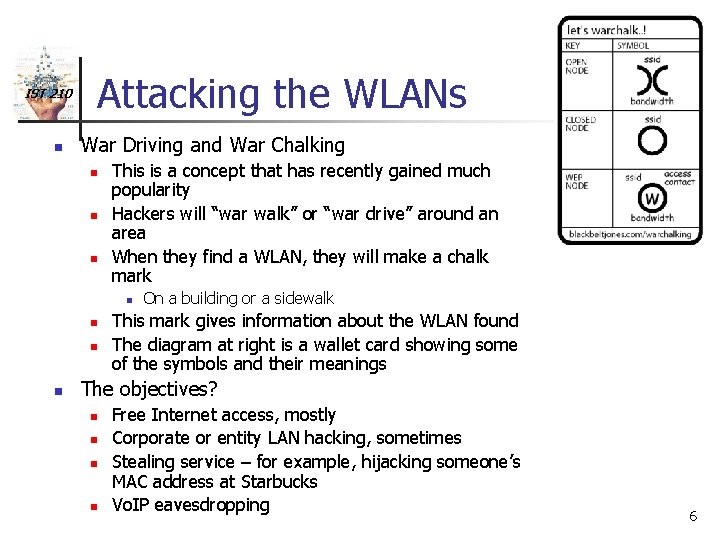
IST 210 n Attacking the WLANs War Driving and War Chalking n n n This is a concept that has recently gained much popularity Hackers will “war walk” or “war drive” around an area When they find a WLAN, they will make a chalk mark n n On a building or a sidewalk This mark gives information about the WLAN found The diagram at right is a wallet card showing some of the symbols and their meanings The objectives? n n Free Internet access, mostly Corporate or entity LAN hacking, sometimes Stealing service – for example, hijacking someone’s MAC address at Starbucks Vo. IP eavesdropping 6
IST 210 Drive-by Spamming n n n n New phenomenon Attackers equip a van with a toroidal antenna And a server farm Scout business districts and neighborhoods looking for WLANs Once they find an open network, they connect and look for a mail server Often, attackers dump upwards of 1, 000 emails per day through corporate mail servers Drive-by Worming 7
IST 210 What kind of security is needed? n n n Layered security approach “Defense in depth” Separation of networks from one another n n WLAN/Data/Vo. IP/Control System VLANs Monitoring and management can help Clean up-front design Don’t put all your eggs in one basket 8
IST 210 Conclusion n n n Cool tech can often lead to uncool problems Opportunity is a matter of perspective Just because I’m paranoid… Be careful with your Bluetooth phone A combination of different methods works best Nothing is 100% effective 9
IST 210 Security is like a lot of things. . . n n It can never be 100% effective. It contributes nothing to the performance. You can never be sure you actually need it at the time. You don’t know whether it has worked until after the event – sometimes long after! n n n The only way to measure its effectiveness is in terms of its failures. A combination of methods gives the greatest reduction in risk. You should never rely on someone else’s precautions to be certain, you have to take care of it yourself. 10
- Slides: 10