Issues Information Systems and Management Issues Privacy Ethics
- Slides: 37
Issues Information Systems and Management
Issues • • • Privacy Ethics Health Computer Crime Security
Privacy Ø The right to be left alone when you want to be, to have control over your personal possessions and not to be observed without your consent Ø The power of IT to store and retrieve information can have a negative affect on the “right of privacy” of every individual • Monitor e-mail • Collect data from website visits
Privacy and the Internet • There are few rules about what is private and what you can store • Censorship: Freedom of Information/Speech/The Press • Spamming: mass unsolicited e-mail • Flaming: critical, derogatory, vulgar e-mail
Privacy and Employees • Monitoring technology scans both incoming and outgoing e-mail • Eastman Kodak has a monitoring policy • Computer matching – Mistaken identity – Stolen identity • Terrorists use UNSENT e-mail as a virtual drop box
Privacy and Consumers • Consumers want businesses to know who they are, provide them with what they want, and tell them about their products – BUT leave them alone. • Cookies • Spyware
Privacy and Government • Canadians have the right to see all data held by the Federal Government about them – There is a database on who has made a request – Soviet Union 1974
Privacy and International Trade • Which countries’ laws apply? – Buy – Ship – Destination
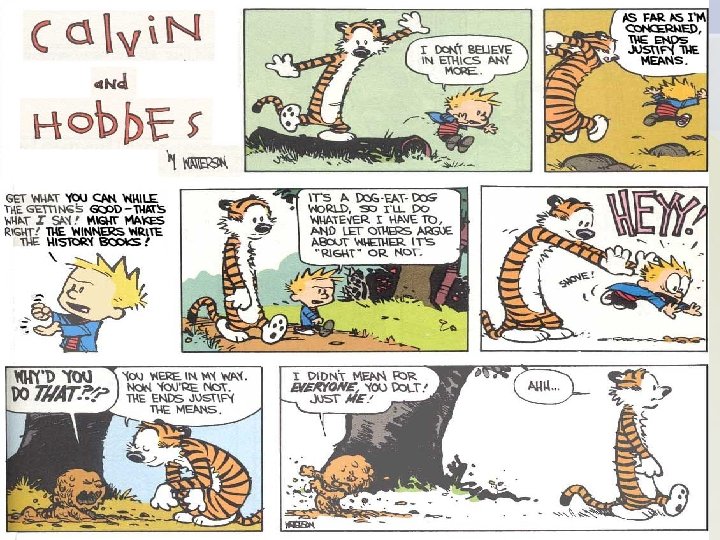
Ethics Ø The principles and standards that guide our behaviours toward other people. • • Technology has created many new ethical dilemmas Intellectual property: intangible Copyright: songs Fair use Doctrine: can legally use copyright material for education • Pirated Software: unauthorized duplication or sale of copyright software • Counterfeit Software: software manufactured to look real.
Developing Information Management Policies • Ethical Computer Use • Information Privacy • Acceptable Use • Email Privacy • Internet Use • Anti-Spam
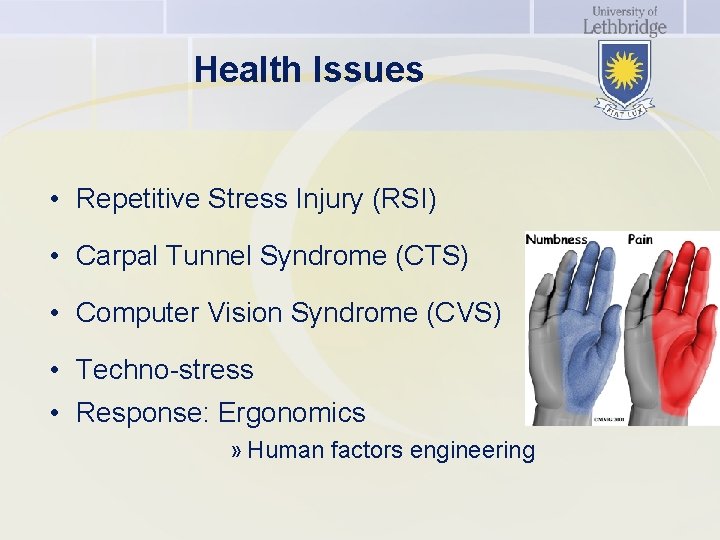
Health Issues • Repetitive Stress Injury (RSI) • Carpal Tunnel Syndrome (CTS) • Computer Vision Syndrome (CVS) • Techno-stress • Response: Ergonomics » Human factors engineering
You and Ethical Responsibility • As a managerial end user, you have a responsibility to do something about some of the abuses of information and technology in the workplace. • As IS Professionals there should be a code of ethics to follow – One that is generally accepted like other professions
Computer Crime • The commission of illegal acts through the use of a computer or against a computer system
Computer Crime • • Money theft Service theft Software theft Data alteration or theft Computer Viruses Malicious Access – Hacking Crimes against the computer SWP Internal Audit Seminar, 1975 -1980
Outside the Organization • Viruses: destructive software written with the intent to cause annoyance or damage • • • Benign Viruses Malignant Viruses Macro Viruses Worm Denial-of-service (single or distributed) Combinations Hoaxes Stand-alone Viruses Trojan Horse Viruses
The Players • • Hackers White-hat hackers Black-hat hackers Crackers Social Engineering Hactivists Cyber-terrorists Script Kiddies
Inside the Company • Be careful who you hire and how you investigate potential problems
Computer Forensics • The gathering, authentication, examination, and analysis of electronic information stored on any type of computer media, such as hard drives, floppy disks, or CD’s.
Recovery and Interpretation • Places to look for stray information – Deleted files and slack space – Unused space • Ways of hiding information – – – – Rename the file Make the information invisible Use Windows to hide files Protect the file with a password Encrypt the file Use Steganography Compress the file
Information Security • The protection of information from accidental or intentional misuse by persons inside or outside an organization • The First Line of Defence – People – Develop and enforce policies – Ontario Hydro – “Can I help you? ”
Social Engineering • Using one’s social skills to trick people into revealing access credentials or other information valuable to the attackers.
The Second Line of Defence Technology • Authentication – Confirm user’s identity • ID and password • Smart card • Fingerprint or voice signature • Prevention and Resistance • Firewalls • Encryption • Content filters • Detection and Response • Anti-virus software
Risk Management • • • Identify Threats Assess Consequences Select Countermeasures Prepare contingency plans Monitor and review
Effective Controls Provide Quality Assurance • Keep the information system free from errors and fraud • Data Accuracy • System Integrity Scan on data integrity within a database
Information System Controls 1. Input Controls 2. Processing Controls 3. Output Controls 4. Storage Controls
Information Systems Controls • Input Controls – Control totals: record count, batch total, hash total – Ensure a valid transaction • Processing Controls – Hardware controls: special checks built into the hardware to verify the accuracy of computer processing • Parity • Re-calculation – Software controls: check internal file labels, check points, audit trails; edits in application programs
Information Systems Controls • Output Controls – Ensure that information products are correct and complete and are transmitted to authorized users in a timely manner • Storage Controls – Program and database library – File back-up and retention
Facility Controls 1. Network Security 2. Physical Protection Controls 3. Biometric Controls 4. Computer Failure Controls
Facility Controls • Network Security – – Monitor the use of networks Protect networks from unauthorized use Give authorized users access through ID and passwords Encryption • Physical Protection – – Security doors ID badges Alarms Closed-circuit TV
Facility Controls • Biometric Controls – Measure unique physical traits of individuals • Signature, retinal scanning • Computer Failure Controls – Fault tolerant: multiple CPU, peripherals and system software – Fail Safe: capability to operate at the same level – Fail Soft: capability to operate at a reduced but acceptable level
Procedural Controls • Methods that specify how the information services organization should be operated for maximum security to facilitate the accuracy and integrity of computer operation and system development activities.
Procedural Controls • Separation of Duties • Standard Operating Procedures • Authorization Requirements • Disaster Recovery • Auditing Information Systems
Procedural Controls • Disaster Recovery (Business Continuity Planning) – Specifies duties of employees, what hardware, software, and facilities will be used, and the priority of applications that will be processed.
Procedural Controls • Auditing Information Systems – Auditing around the computer: verify accuracy of output given specific input – Auditing through the computer: detailed verification of the logic of computer programs – Audit trail • The presence of documentation that allows a transaction to be traced through all the stages of its information processing • RCMP Auditor
Issues Information Systems and Management