ISP Responsibility Working at a SmalltoMedium Business or
ISP Responsibility Working at a Small-to-Medium Business or ISP – Chapter 8 Version 4. 1 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 1
Objectives § Describe ISP security policies and procedures. § Describe the tools used in implementing security at the ISP. § Describe the monitoring and managing of the ISP. § Describe the responsibilities of the ISP with regard to maintenance and recovery. © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 2
ISP Security Considerations § Helping clients to create secure passwords § Securing applications § Removing vulnerabilities § Configuring firewalls § Performing security scans © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 3
ISP Security Considerations Common security practices: § Encrypting data stored on servers § Using permissions to secure access § Implement user accounts § Assign levels of access © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 4
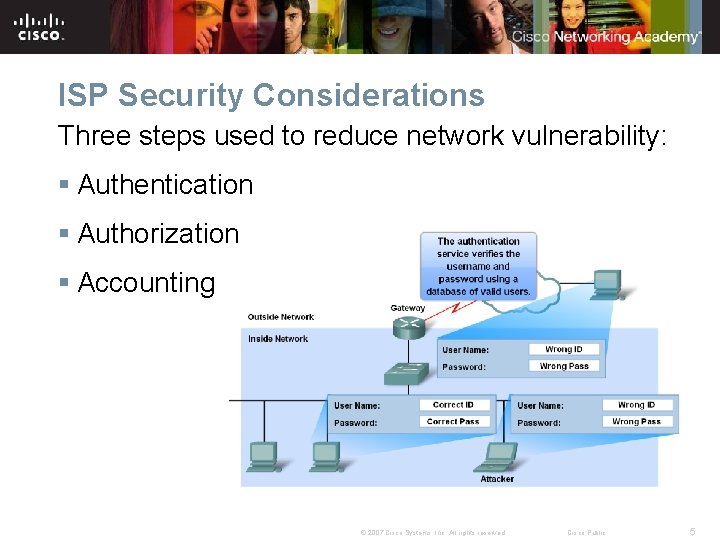
ISP Security Considerations Three steps used to reduce network vulnerability: § Authentication § Authorization § Accounting © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 5
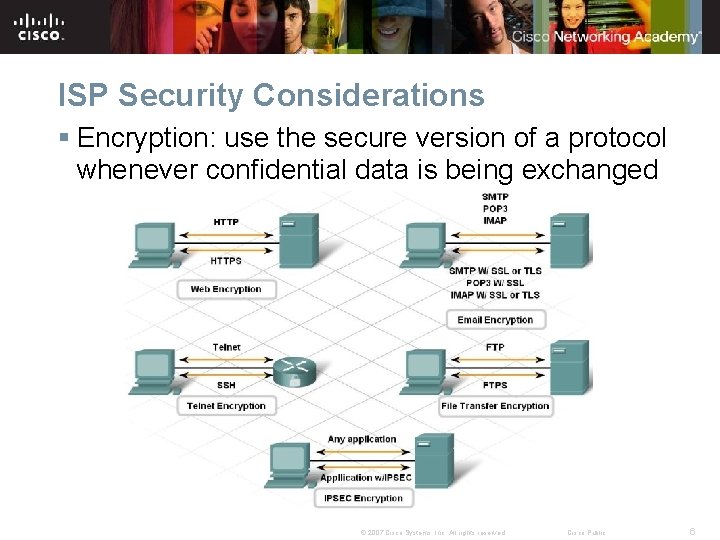
ISP Security Considerations § Encryption: use the secure version of a protocol whenever confidential data is being exchanged © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 6
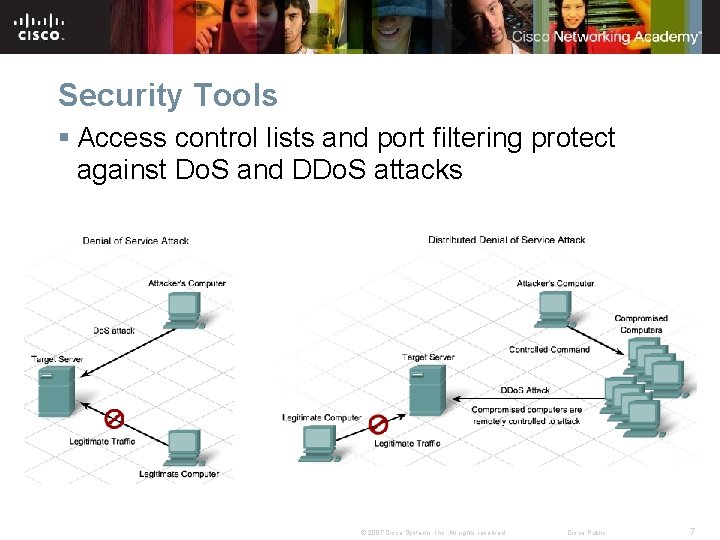
Security Tools § Access control lists and port filtering protect against Do. S and DDo. S attacks © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 7
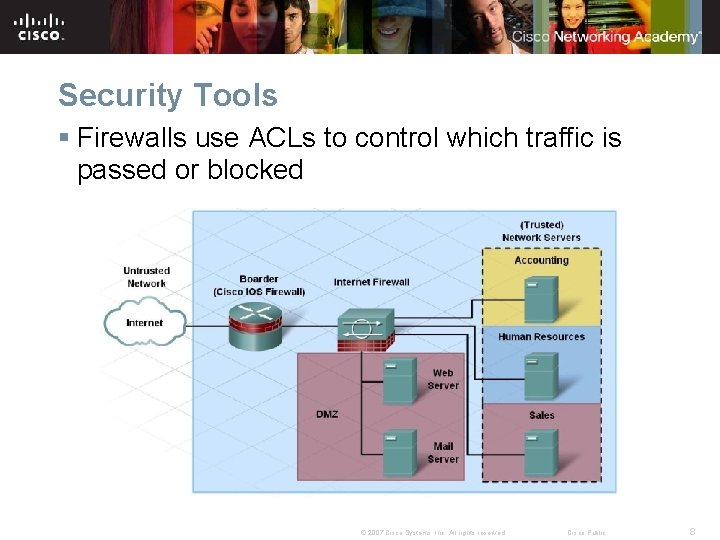
Security Tools § Firewalls use ACLs to control which traffic is passed or blocked © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 8
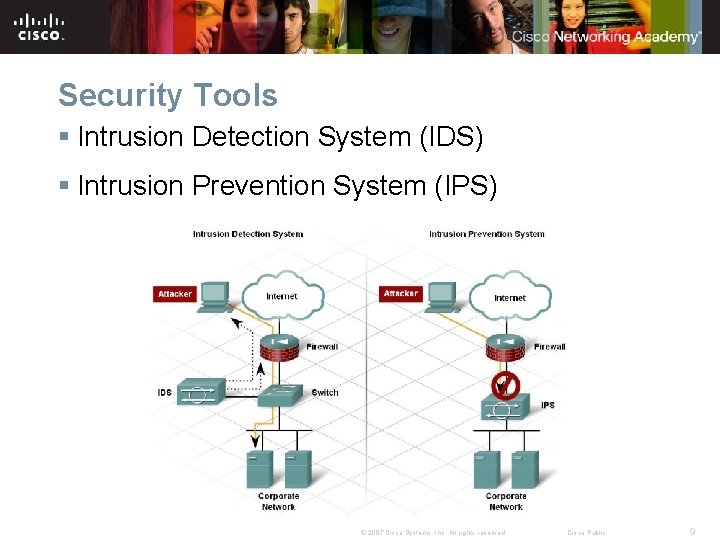
Security Tools § Intrusion Detection System (IDS) § Intrusion Prevention System (IPS) © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 9
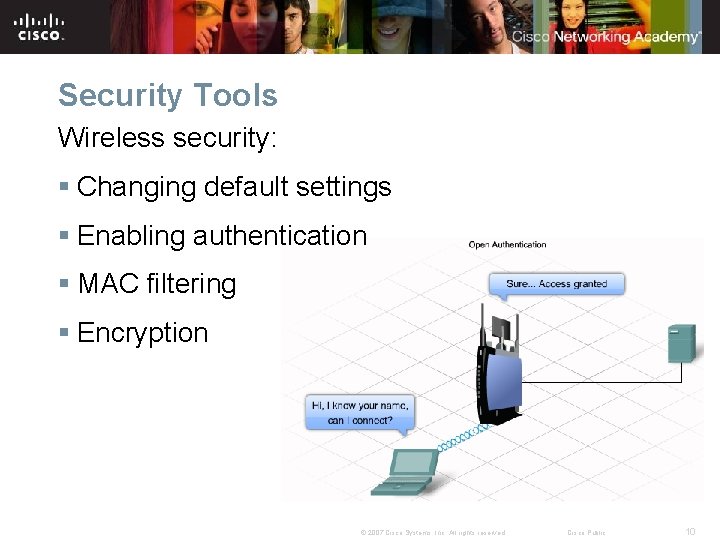
Security Tools Wireless security: § Changing default settings § Enabling authentication § MAC filtering § Encryption © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 10
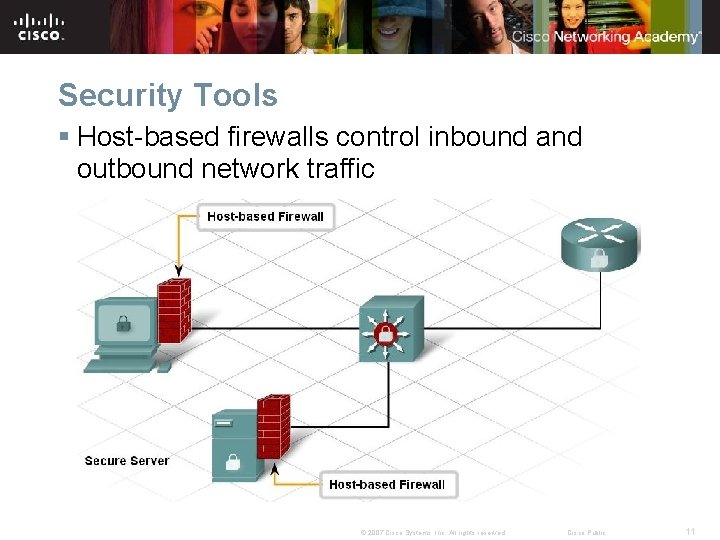
Security Tools § Host-based firewalls control inbound and outbound network traffic © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 11
Security Tools Targets of host security: § Known attacks § Exploitable services § Worms and viruses § Back doors and Trojans © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 12
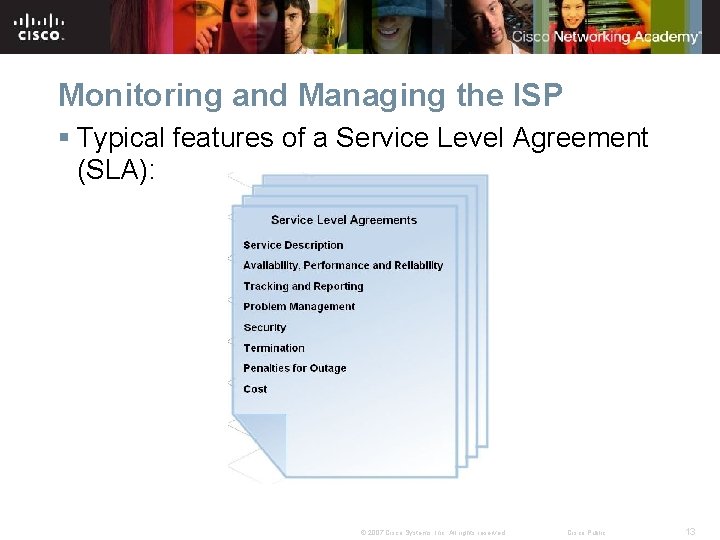
Monitoring and Managing the ISP § Typical features of a Service Level Agreement (SLA): © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 13
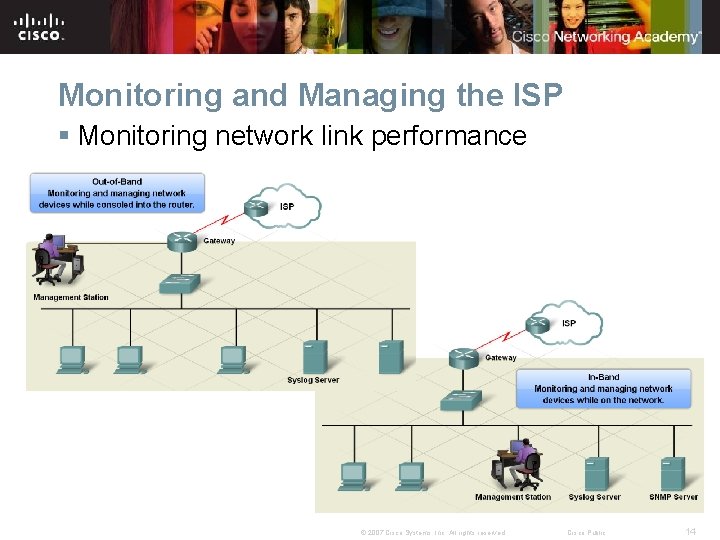
Monitoring and Managing the ISP § Monitoring network link performance © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 14

Monitoring and Managing the ISP In-band management: § Telnet Virtual Terminal (VTY) session § Secure Shell (SSH): preferred for security © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 15
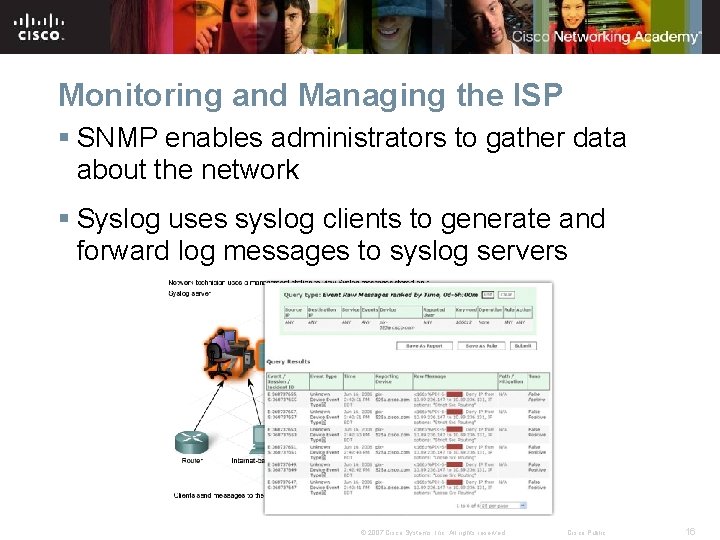
Monitoring and Managing the ISP § SNMP enables administrators to gather data about the network § Syslog uses syslog clients to generate and forward log messages to syslog servers © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 16
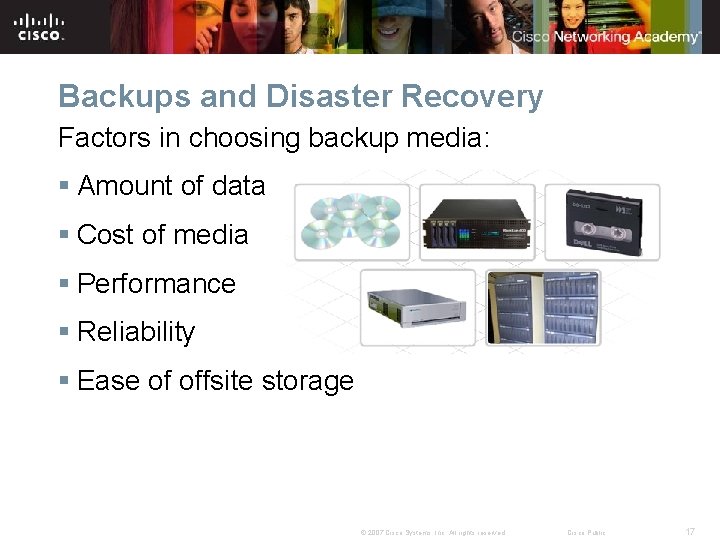
Backups and Disaster Recovery Factors in choosing backup media: § Amount of data § Cost of media § Performance § Reliability § Ease of offsite storage © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 17
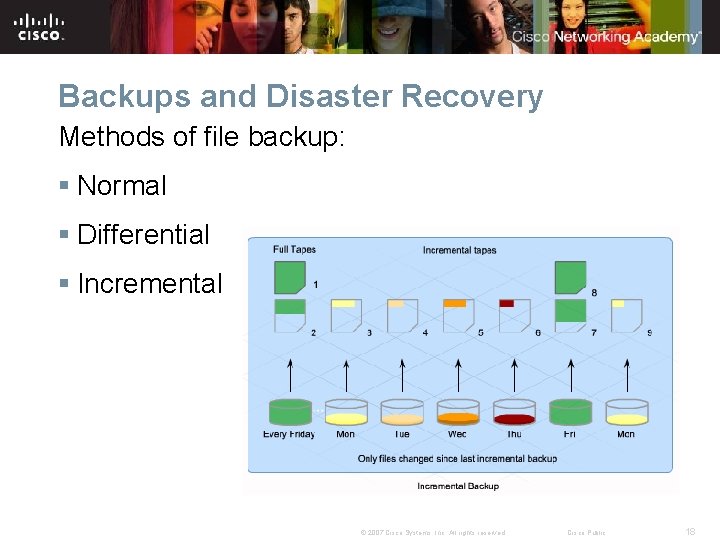
Backups and Disaster Recovery Methods of file backup: § Normal § Differential § Incremental © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 18
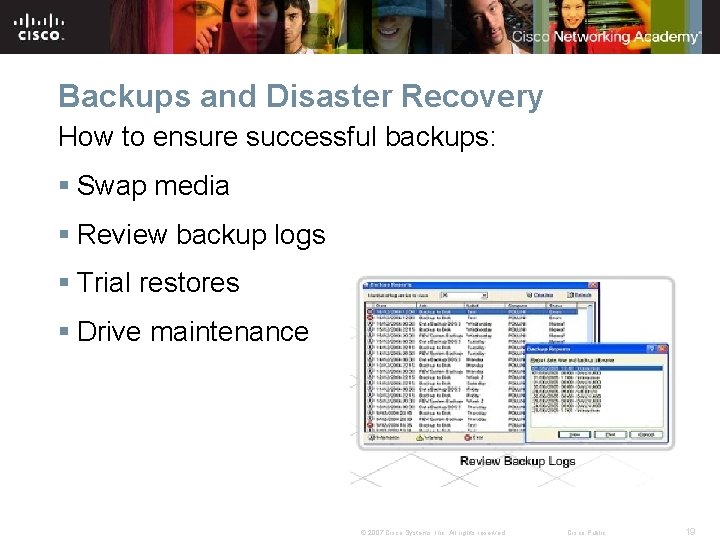
Backups and Disaster Recovery How to ensure successful backups: § Swap media § Review backup logs § Trial restores § Drive maintenance © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 19
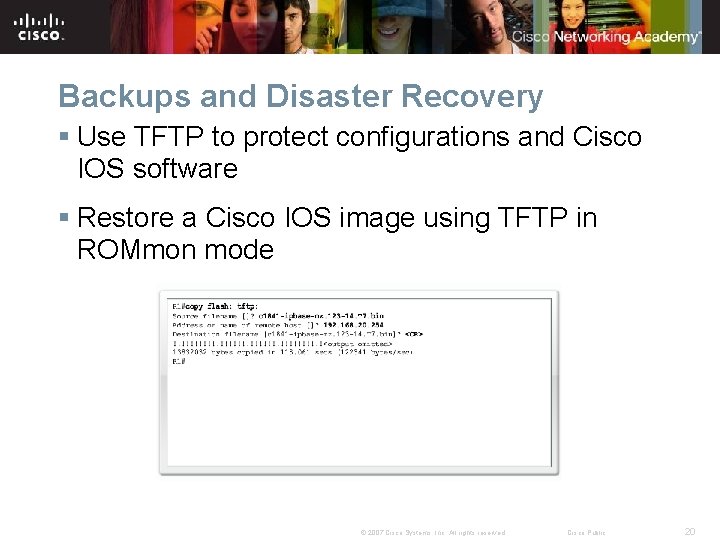
Backups and Disaster Recovery § Use TFTP to protect configurations and Cisco IOS software § Restore a Cisco IOS image using TFTP in ROMmon mode © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 20

Backups and Disaster Recovery § Steps to designing an effective recovery plan: © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 21

Backups and Disaster Recovery § Phases to creating and implementing a disaster recovery plan: © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 22
Summary § ISPs provide desktop security services for customers, such as creating passwords, implementing patches and updates, and assigning permissions. § Many protocols offer secure versions utilizing digital encryption, which should be used when the data being exchanged is confidential. § Port filtering and Access Lists use TCP and UDP port features to permit or deny traffic. § Firewalls can utilize hardware or software to define what traffic can come into or go out of parts of a network. § ISPs are responsible for providing efficient and effective backup and disaster recovery methods for their customers. © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 23

© 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 24
- Slides: 24