ISO 21827 System Security Engineering Capability Maturity Model
ISO 21827 System Security Engineering Capability Maturity Model Presented By John W. Lindquist Founding Member of the HIPAA Alliance, LLC and President and CEO EWA Information & Infrastructure Technologies, Inc. 13873 Park Center Rd. , Ste. 200, Herndon VA 20171 703 478 7600 6 th Annual HIPAA Summit Session: 5. 06 On-Going HIPAA Compliance: Securing Tracked Data - March 28, 2003 Copyright © EWA IIT, Inc. 1
Problem How does management establish and track an information security program when: • Risks are real • Risks are nearly infinite • The information environment is highly dynamic • Resources are finite 2 Copyright © EWA IIT, Inc.
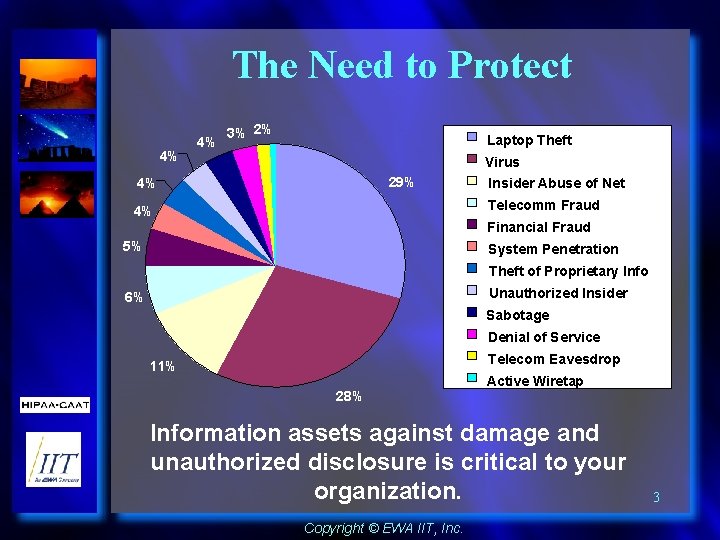
The Need to Protect 4% 4% 3% 2% Laptop Theft Virus 29% 4% Insider Abuse of Net Telecomm Fraud 4% Financial Fraud 5% System Penetration Theft of Proprietary Info Unauthorized Insider 6% Sabotage Denial of Service Telecom Eavesdrop 11% 28% Active Wiretap Information assets against damage and unauthorized disclosure is critical to your organization. Copyright © EWA IIT, Inc. 3
Information Assurance Solutions Must Address: v. People v. Process v. Technology alone won’t make you safe. “Get rid of the techno-babble. This is a management problem. ” Steve Katz, CISO, Citibank 4 Copyright © EWA IIT, Inc.
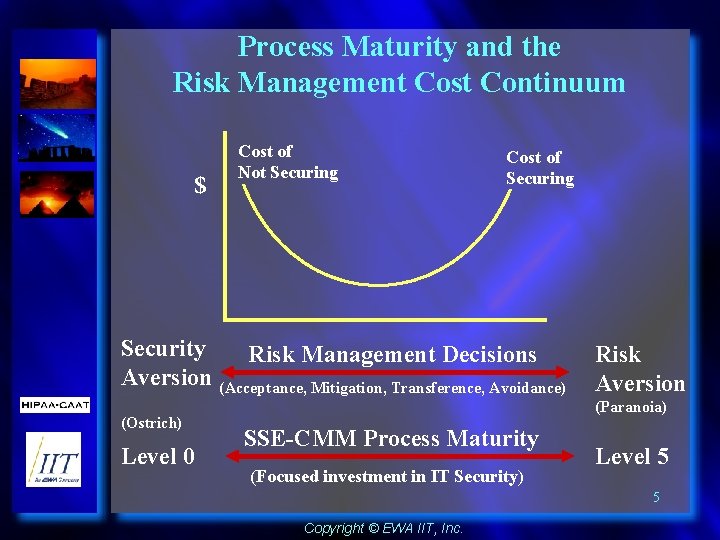
Process Maturity and the Risk Management Cost Continuum $ Cost of Not Securing Cost of Securing Security Risk Management Decisions Aversion (Acceptance, Mitigation, Transference, Avoidance) (Ostrich) Level 0 Risk Aversion (Paranoia) SSE-CMM Process Maturity (Focused investment in IT Security) Level 5 5 Copyright © EWA IIT, Inc.
SYSTEM SECURITY ENGINEERING CAPABILITY MATURITY MODEL • SSE - CMM is both a Model and a Process • A Community-owned Model (50 companies / agencies led by the US National Security Agency (NSA) and Canadian Communications Security Establishment (CSE)) • Model Presents Security Engineering as a Defined, Mature and Measurable Discipline • Model and Appraisal Method Enable: – Capability-based assurance i. e. . Security/trustworthiness inferred from the maturity of processes – Focused investment in security engineering tools, training, process definition, management practices and improvements based on risk assessment and available resources – Qualifying vendors, suppliers, and organizations connecting to a system 6 Copyright © EWA IIT, Inc.
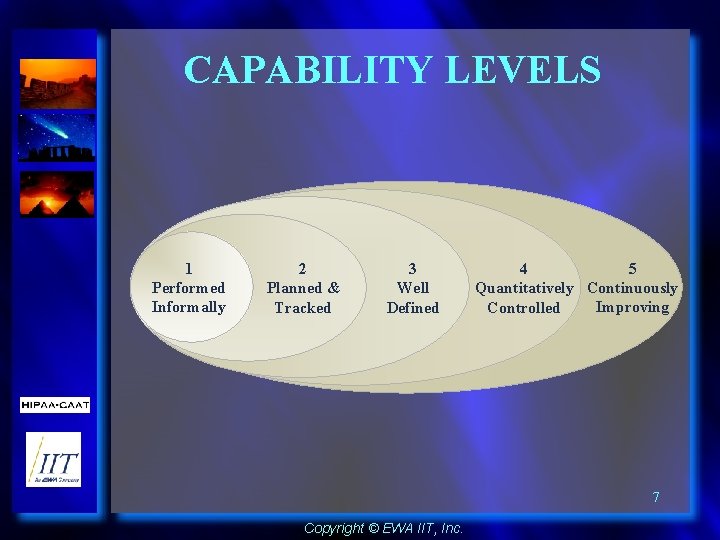
CAPABILITY LEVELS 1 Performed Informally 2 Planned & Tracked 3 Well Defined 5 4 Quantitatively Continuously Improving Controlled 7 Copyright © EWA IIT, Inc.
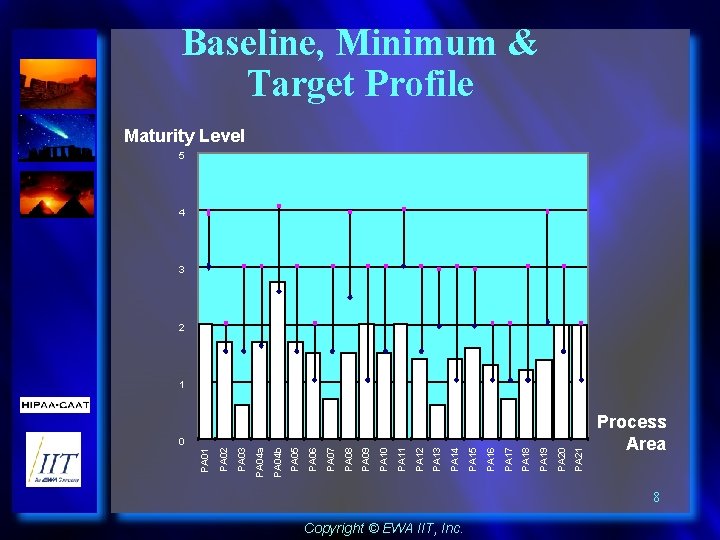
Baseline, Minimum & Target Profile Maturity Level 5 4 3 2 PA 21 PA 20 PA 19 PA 18 PA 17 PA 16 PA 15 PA 14 PA 13 PA 12 PA 11 PA 10 PA 09 PA 08 PA 07 PA 06 PA 05 PA 04 b PA 04 a PA 03 PA 01 0 PA 02 1 Process Area 8 Copyright © EWA IIT, Inc.
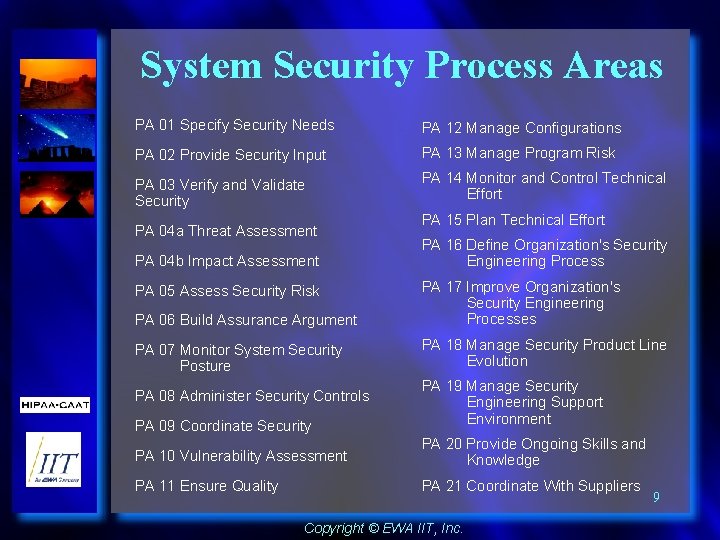
System Security Process Areas PA 01 Specify Security Needs PA 12 Manage Configurations PA 02 Provide Security Input PA 13 Manage Program Risk PA 03 Verify and Validate Security PA 14 Monitor and Control Technical Effort PA 04 a Threat Assessment PA 04 b Impact Assessment PA 15 Plan Technical Effort PA 16 Define Organization's Security Engineering Process PA 06 Build Assurance Argument PA 17 Improve Organization's Security Engineering Processes PA 07 Monitor System Security Posture PA 18 Manage Security Product Line Evolution PA 08 Administer Security Controls PA 09 Coordinate Security PA 19 Manage Security Engineering Support Environment PA 10 Vulnerability Assessment PA 20 Provide Ongoing Skills and Knowledge PA 11 Ensure Quality PA 21 Coordinate With Suppliers PA 05 Assess Security Risk Copyright © EWA IIT, Inc. 9
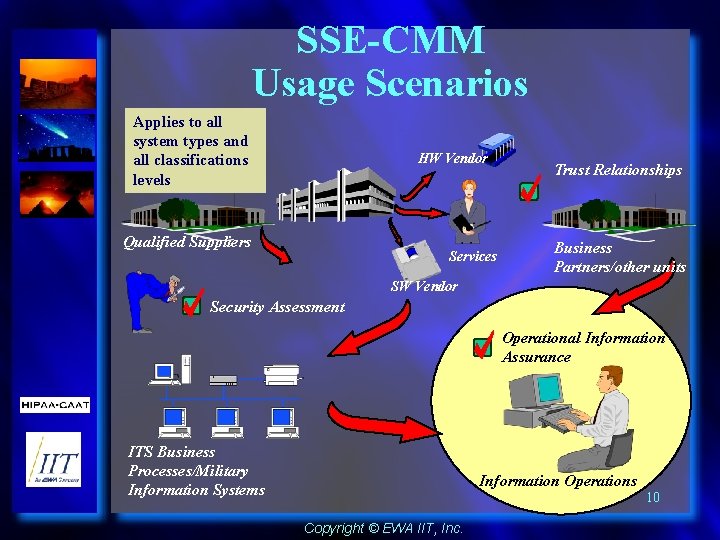
SSE-CMM Usage Scenarios Applies to all system types and all classifications levels HW Vendor Qualified Suppliers Services Trust Relationships Business Partners/other units SW Vendor Security Assessment Operational Information Assurance ITS Business Processes/Military Information Systems Information Operations Copyright © EWA IIT, Inc. 10
Summary • Can’t Protect Everything All The Time • The Dynamic Environment Requires a Flexible Response • Effective Information Assurance Must Address People, Process and Technology • Information Assurance is Risk Management not Risk Avoidance (There is No Silver Bullet) • The SSE-CMM is an IA Tool Developed in Consideration the Above 11 Copyright © EWA IIT, Inc.
- Slides: 11