ISO 17799ITS APPLICATION Prepared by aatay Boztrk 14
ISO 17799&ITS APPLICATION Prepared by Çağatay Boztürk 14. 06. 2005
Outline n What is ISO 17799? n History n Who’s it for ? n Implementation n Conclusion
What is ISO 17799? . • A set of controls based on the best practices in information security; • An international standard covering every aspect of information security: – – Equipment; Management policies; Human resources; Legal aspects.
BS 7799 or ISO 17799 ? . • ISO 17799 (part 1) is a guide containing controls and recommendations by which an organization can ensure the security of its information. • BS 7799 (part 2) proposes measures for an efficient information security management framework. BS 7799 -2 helps an organization establish an information security management system (ISMS) and thus prepare for the audit.
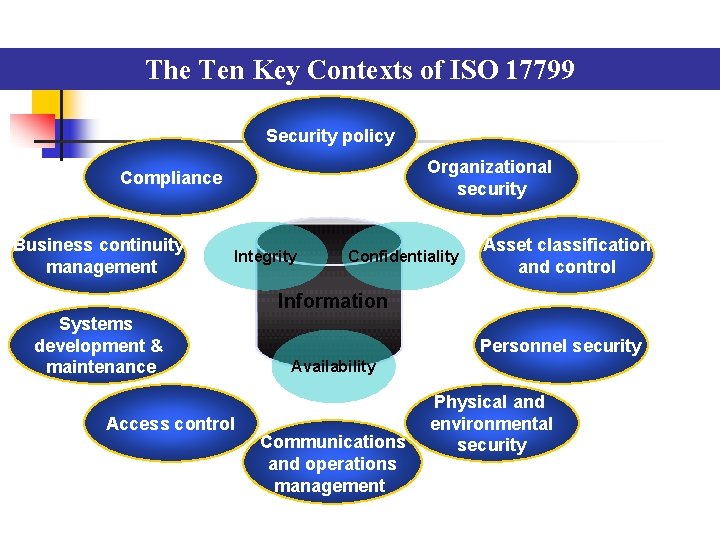
The Ten Key Contexts of ISO 17799 Security policy Organizational security Compliance Business continuity management Integrity Confidentiality Asset classification and control Information Systems development & maintenance Access control Personnel security Availability Communications and operations management Physical and environmental security
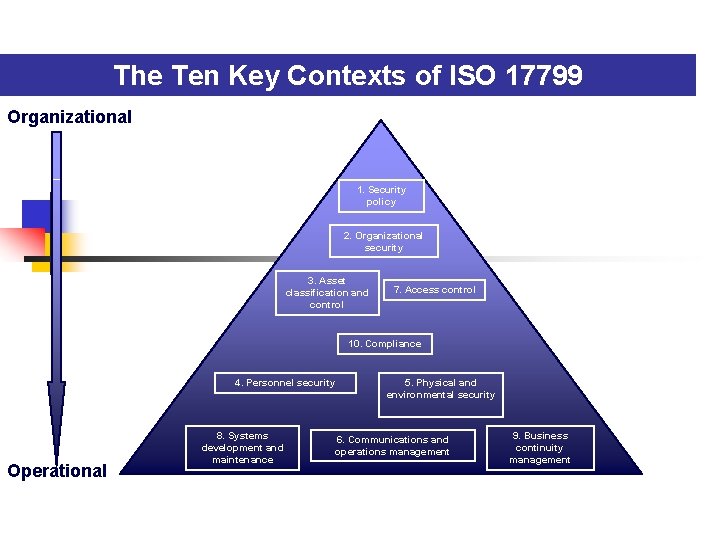
The Ten Key Contexts of ISO 17799 Organizational 1. Security policy 2. Organizational security 3. Asset classification and control 7. Access control 10. Compliance 4. Personnel security Operational 8. Systems development and maintenance 5. Physical and environmental security 6. Communications and operations management 9. Business continuity management
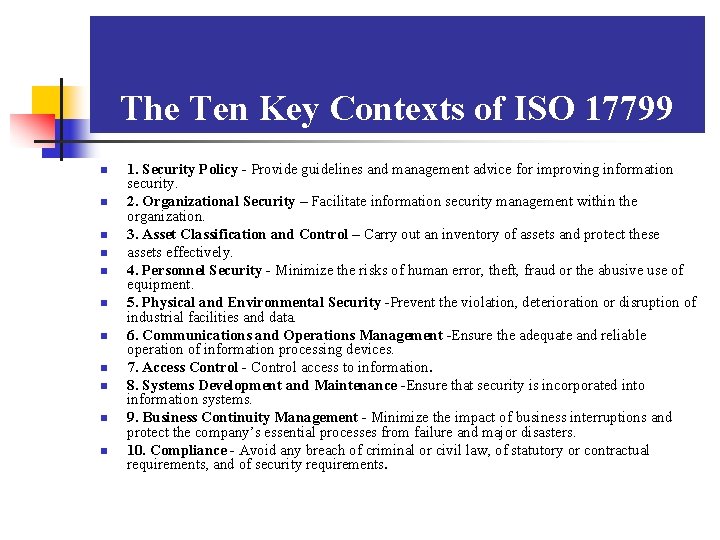
The Ten Key Contexts of ISO 17799 n n n 1. Security Policy - Provide guidelines and management advice for improving information security. 2. Organizational Security – Facilitate information security management within the organization. 3. Asset Classification and Control – Carry out an inventory of assets and protect these assets effectively. 4. Personnel Security - Minimize the risks of human error, theft, fraud or the abusive use of equipment. 5. Physical and Environmental Security -Prevent the violation, deterioration or disruption of industrial facilities and data. 6. Communications and Operations Management -Ensure the adequate and reliable operation of information processing devices. 7. Access Control - Control access to information. 8. Systems Development and Maintenance -Ensure that security is incorporated into information systems. 9. Business Continuity Management - Minimize the impact of business interruptions and protect the company’s essential processes from failure and major disasters. 10. Compliance - Avoid any breach of criminal or civil law, of statutory or contractual requirements, and of security requirements.
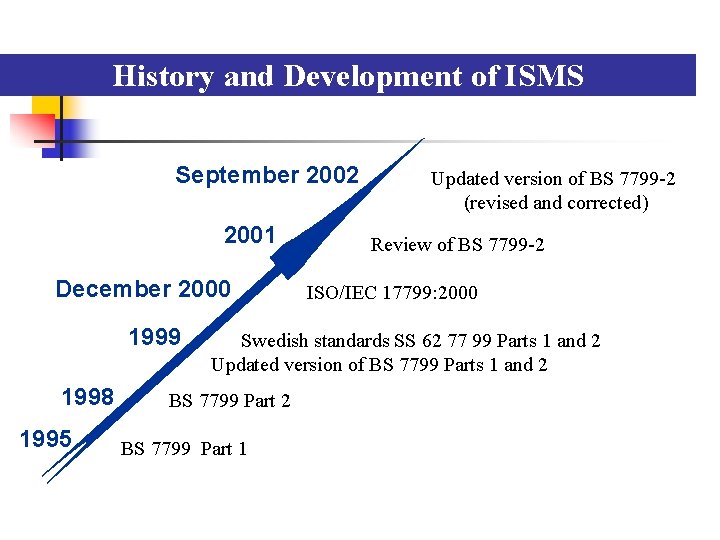
History and Development of ISMS September 2002 2001 December 2000 1999 1998 1995 Updated version of BS 7799 -2 (revised and corrected) Review of BS 7799 -2 ISO/IEC 17799: 2000 Swedish standards SS 62 77 99 Parts 1 and 2 Updated version of BS 7799 Parts 1 and 2 BS 7799 Part 1
Who’s it for ? n BS 7799/ISO 17799 can be used by any organization or company. If your organization uses computer systems internally or externally, possesses confidential data, depends upon information systems in the context of its business activities, or simply wants to adopt a high level of security while complying with a standard, BS 7799/ISO 17799 is the solution.
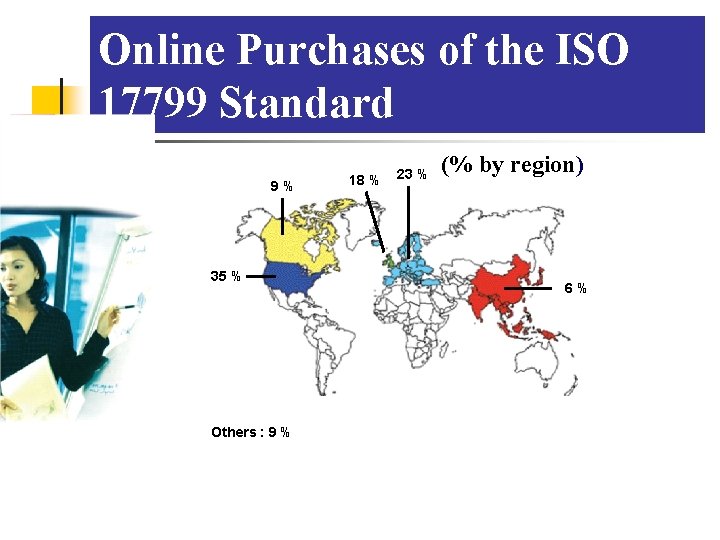
Online Purchases of the ISO 17799 Standard 9% 35 % Others : 9 % 18 % 23 % (% by region) 6%
BS 7799 / ISO 17799 Audit and Certification n ISO 17799 certification does not exist at the moment. A company can comply with ISO 17799 and then become BS 7799 -2: 2002 certified. The audit process can be documented : n n n Internal audit External audit (letter of opinion) BSI Registrar (official certification)

List of Certified Firms n Over 80 000 firms around the world are BS 7799/ISO 17799 compliant: • • Fujitsu Limited; Insight Consulting Limited; KPMG ; Marconi Secure Systems ; Samsung Electronics Co Ltd; Sony Bank inc. ; Symantec Security Services ; Toshiba IS Corporate
Advantages n n Compliance with governance rules for risk management; Better protection of the company’s confidential information ; n Reduced risk of hacker attacks ; n Faster and easier recovery from attack.
Advantages (cont’d) n n Structured security methodology that has gained international recognition; Increased mutual confidence between partners; Potentially lower premiums for computer risk insurance; Improved privacy practices and compliance with privacy laws.
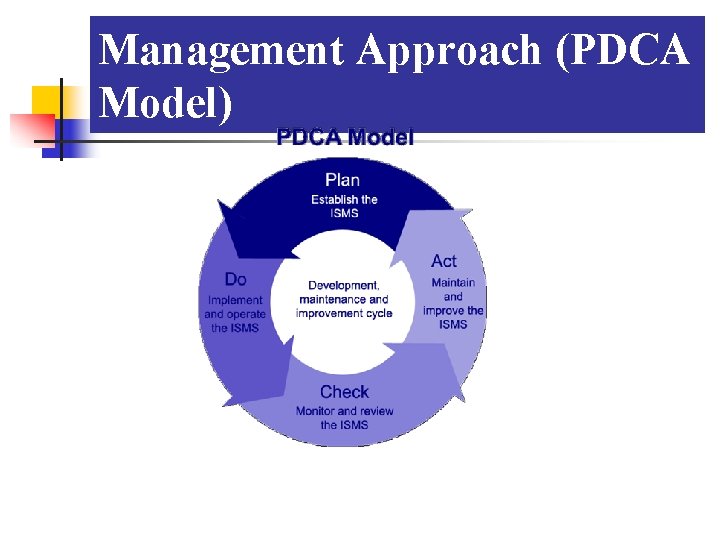
Management Approach (PDCA Model)
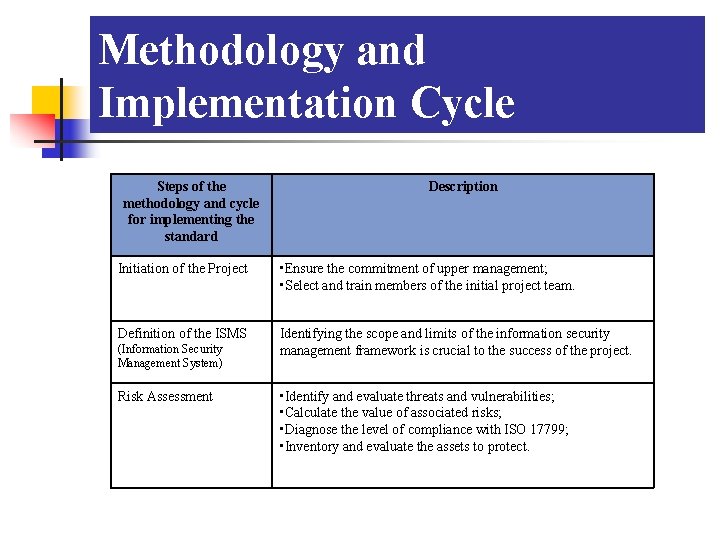
Methodology and Implementation Cycle Steps of the methodology and cycle for implementing the standard Description Initiation of the Project • Ensure the commitment of upper management; • Select and train members of the initial project team. Definition of the ISMS Identifying the scope and limits of the information security management framework is crucial to the success of the project. (Information Security Management System) Risk Assessment • Identify and evaluate threats and vulnerabilities; • Calculate the value of associated risks; • Diagnose the level of compliance with ISO 17799; • Inventory and evaluate the assets to protect.
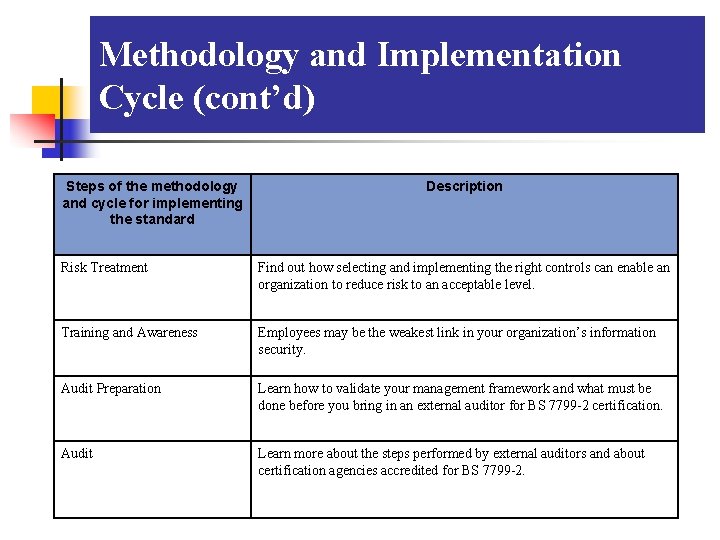
Methodology and Implementation Cycle (cont’d) Steps of the methodology and cycle for implementing the standard Description Risk Treatment Find out how selecting and implementing the right controls can enable an organization to reduce risk to an acceptable level. Training and Awareness Employees may be the weakest link in your organization’s information security. Audit Preparation Learn how to validate your management framework and what must be done before you bring in an external auditor for BS 7799 -2 certification. Audit Learn more about the steps performed by external auditors and about certification agencies accredited for BS 7799 -2.
Implementation Aim: Examination of how ISO 17799 is used and inspection of a company whether they apply the ISO 17799 standarts and how it is applied. A audit is prepared for helping enterprises to measure their security level. Questions which are asked in the survey about the ISO 17799 (BS 77991: 2000) and BS 7799 -2: 2002 Information Security Management Systems are grouped under 10 main titles basing on 127 security control lists. In this direction, the survey is applied to the IT department of a company which has ISO 9001 and ISO 14001 certification. Company which applied the survey does not permit the use of its name because of the information security’s reasons.
Deliverables – ISO 17799 Results of Survey SECURITY POLICY The company has 2 NO over 2 questions on this step. ORGANIZATIONAL SECURITY The company has 7 NO over 10 questions on this step. ASSET CLASSIFICATION & CONTROL The company has 2 NO over 3 questions on this step. PERSONNEL SECURITY The company has 3 NO over 10 questions on this step. PHYSICAL & ENVIRONMENTAL SECURITY The company has 7 NO over 13 questions on this step. COMMUNICATIONS AND OPERATIONS MANAGEMENT The company has 12 NO over 24 questions on this step. ACCESS CONTROL The company has 14 NO over 31 questions on this step. SYSTEMS DEVELOPMENT & MAINTENANCE The company has 7 NO over 18 questions on this step. BUSINESS CONTINUITY MANAGEMENT The company has 1 NO over 5 questions on this step. COMPLIANCE The company has 5 NO over 11 questions on this step. At the end of the survey, Total of YES is 66 over 127 question. This result shows that company’s security status is POOR.
Potential Obstacles /Success Factors n n n Fear, resistance to change; Risk of contiguity; Increased costs; Insufficient knowledge for the approach selected; Seemingly insurmountable task. n n n Dedicated personnel and resources; External expertise; Good understanding of risk management functions (management) and processes (operations); Frequent communication; Manager and employee awareness; Commitment from upper management; Structured approach.
Conclusion Now more than ever, it is essential to align information security with the corporate mission. The confidentiality, integrity and availability of information are crucial factors in conserving a competitive edge, cash flow, legal compliance and a good business image. Seeking certification is also a demonstration that business executives and upper management are showing due diligence in protecting corporate assets. Development of information security policy based on ISO 17799 is thus at the very core of information security management. BS 7799 / ISO 17799 is especially pertinent in this context. Simply by learning the requirements of the standard, companies will improve their understanding of information security management.
References n n n BSI documents (www. bsi. org. uk/index. xhtml) Information Security Management: An Introduction (PD 3000) Provides an overview of the accredited certification process and serves as a useful preface to the other guides. Guide to BS 7799 Risk Assessment and Risk Management (PD 3002) Describes the concepts underlying the BS 7799 risk assessment, including terminology, the evaluation process and risk management. ISO/IEC Guidelines for the Management of IT Security (GMITS) Selecting BS 7799 Controls (PD 3005) Describes the process for selecting appropriate controls.
Thanks for listening
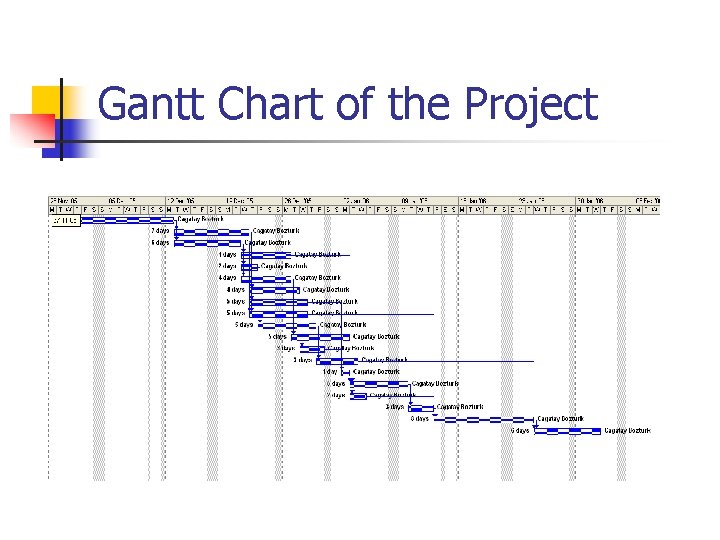
Gantt Chart of the Project
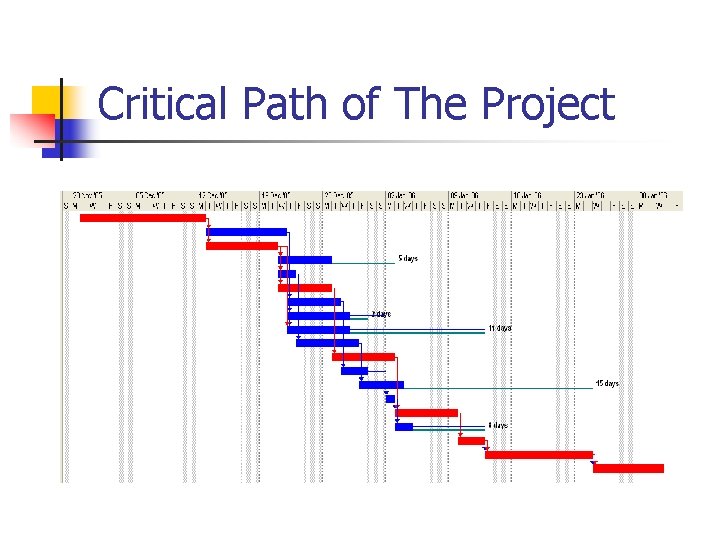
Critical Path of The Project
- Slides: 25