ISE BYOD Jim Kotantoulas Consulting Systems Engineer Security

ISE BYOD Jim Kotantoulas Consulting Systems Engineer – Security Technologies 02/26/2014 © 2010 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 1

END USER EXPECTATIONS IT TRENDS Over 15 Billion devices by 2015, with average worker with 3 devices 50% workloads are virtualized — to increase efficiency New workspace: anywhere, anytime 2/3 of workloads will be in the cloud by 2016 71% Next Gen Y workforce do not obey policies 71% of the world’s mobile data traffic will be video in 2016 60% will download sensitive data on personal device Mobile malware has doubled (2010 to 2011) REDUCE SECURITY RISK © 2010 Cisco and/or its affiliates. All rights reserved. IMPROVE END USER PRODUCTIVITY INCREASE OPERATIONAL EFFICIENCIES Cisco Confidential 2
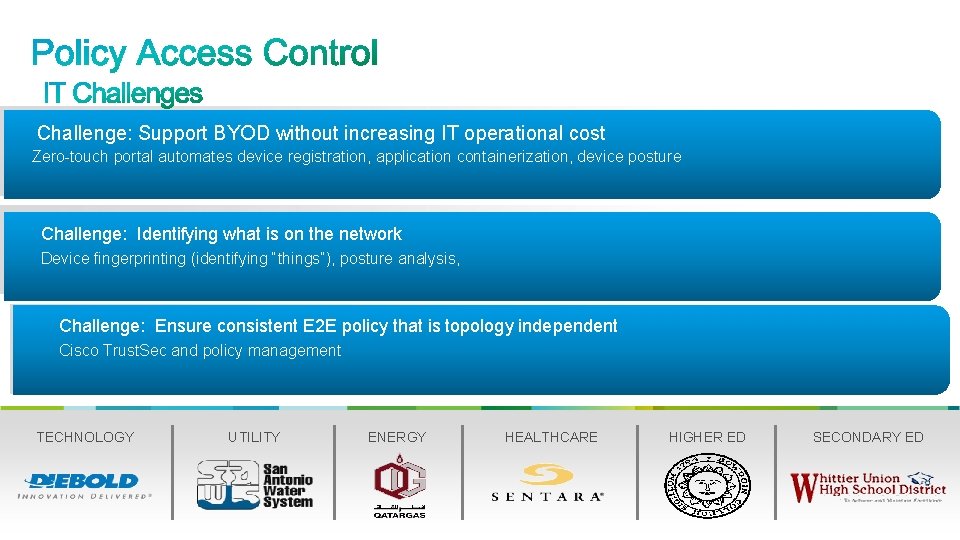
Challenge: BYOD Support BYOD without increasing IT operational cost Zero-touch portal automates device registration, application containerization, device posture Improved productivity, lower cost, added security Challenge: Identifying Control what is on–the network Secure Access Connecting Things Device fingerprinting (identifying posture, “things”), posture analysis, Device visibility (profiling), contextual control, AAA Challenge: Ensure consistent E 2 E policy that is topology independent Consistent Network-wide Policy Control Cisco Trust. Sec and policy management Differentiated access control TECHNOLOGY © 2010 Cisco and/or its affiliates. All rights reserved. UTILITY ENERGY HEALTHCARE HIGHER ED SECONDARY ED Cisco Confidential 3
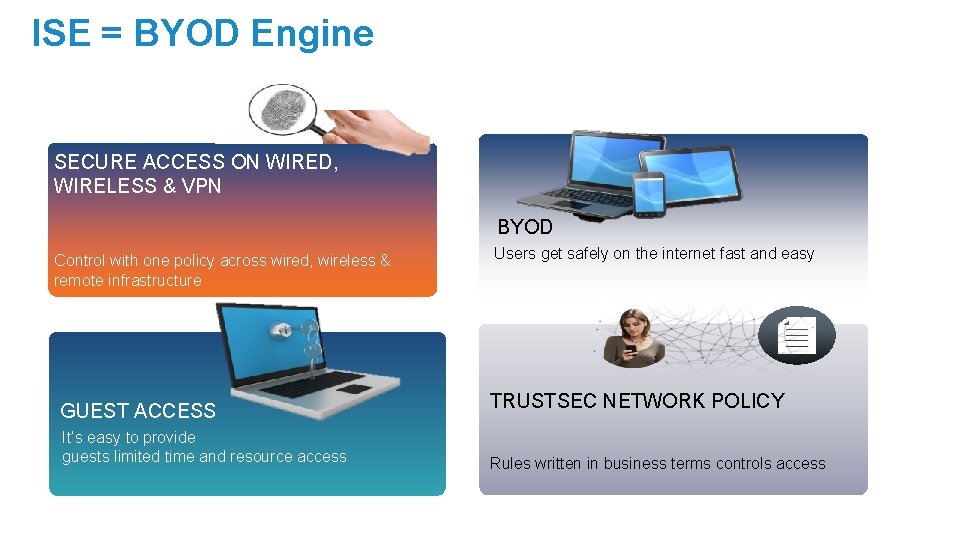
ISE = BYOD Engine SECURE ACCESS ON WIRED, WIRELESS & VPN BYOD Control with one policy across wired, wireless & remote infrastructure GUEST ACCESS It’s easy to provide guests limited time and resource access Users get safely on the internet fast and easy TRUSTSEC NETWORK POLICY Rules written in business terms controls access
BYOx Agenda What is all the hype about? Example Strategies On-Boarding Provisioning Policies Building a BYOD Auth. Z Policy 5
What is driving this new hype? Executive Bling & the “i-Revolution” § Top down demand & new generation: “Our CEO went to a Retail Conference recently and won an i. Pad. He demands we allow it access to the network, because it is a productivity tool and we prohibiting his productivity without the i. Pad” § New Requirement: ‒ Allow access to i-devices § New Term: “Bring Your Own Device” (BYOD) 6
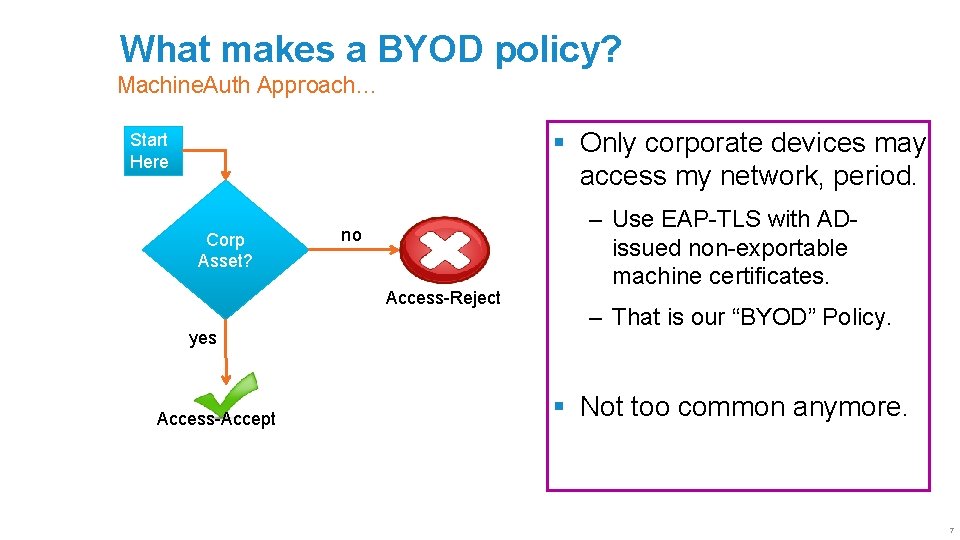
What makes a BYOD policy? Machine. Auth Approach… § Only corporate devices may access my network, period. Start Here Corp Asset? no Access-Reject yes Access-Accept ‒ Use EAP-TLS with ADissued non-exportable machine certificates. ‒ That is our “BYOD” Policy. § Not too common anymore. 7
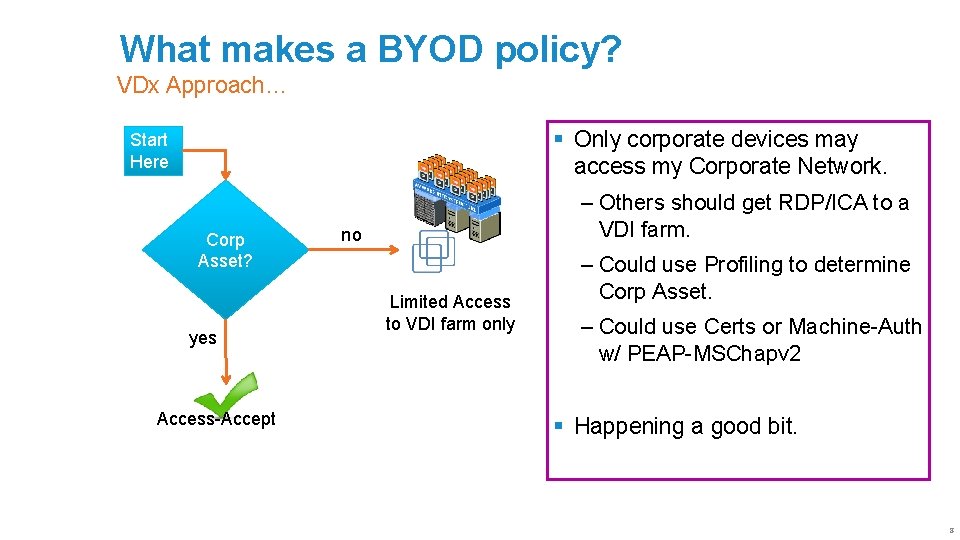
What makes a BYOD policy? VDx Approach… § Only corporate devices may access my Corporate Network. Start Here Corp Asset? yes Access-Accept ‒ Others should get RDP/ICA to a VDI farm. no Limited Access to VDI farm only ‒ Could use Profiling to determine Corp Asset. ‒ Could use Certs or Machine-Auth w/ PEAP-MSChapv 2 § Happening a good bit. 8
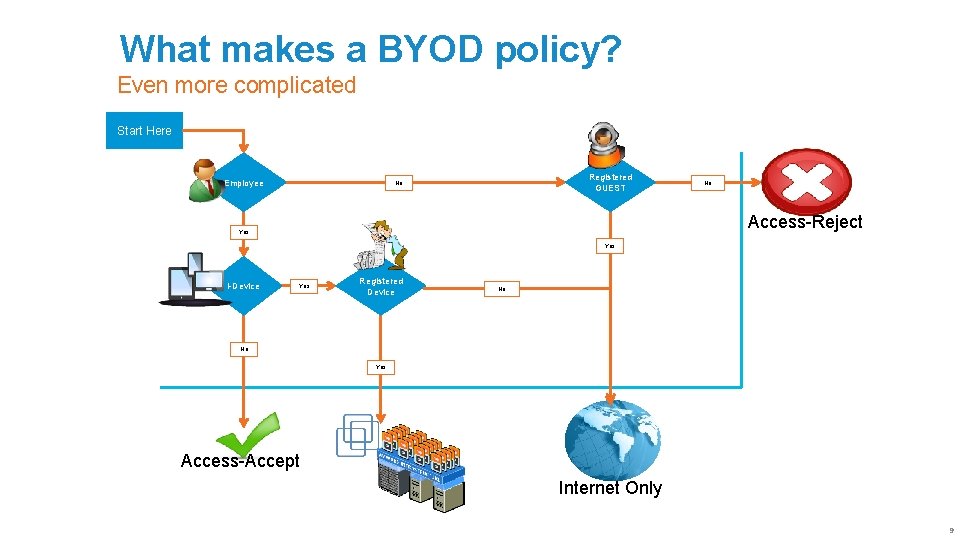
What makes a BYOD policy? Even more complicated Start Here Employee Registered GUEST No No Access-Reject Yes i-Device Yes Registered Device No No Yes Access-Accept Internet Only 9
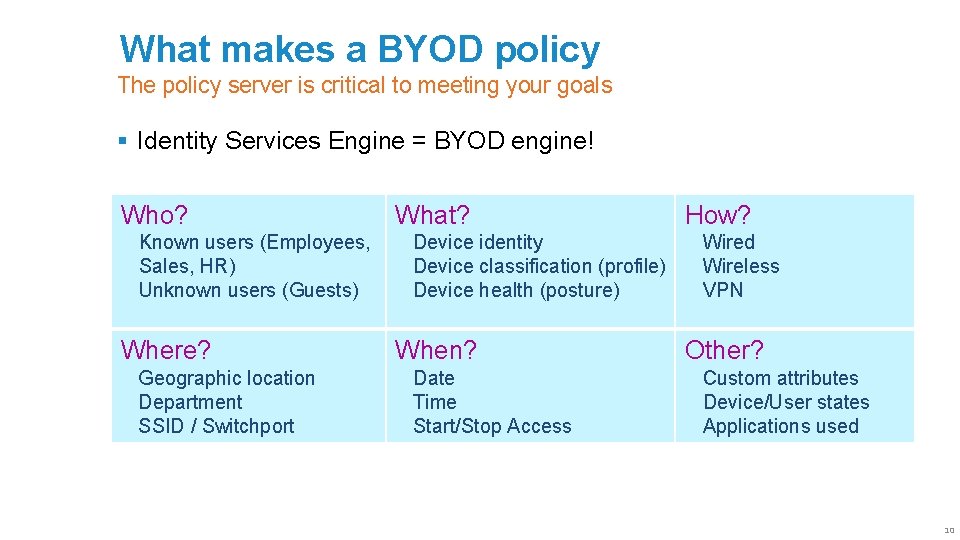
What makes a BYOD policy The policy server is critical to meeting your goals § Identity Services Engine = BYOD engine! Who? Known users (Employees, Sales, HR) Unknown users (Guests) Where? Geographic location Department SSID / Switchport What? Device identity Device classification (profile) Device health (posture) When? Date Time Start/Stop Access How? Wired Wireless VPN Other? Custom attributes Device/User states Applications used 10
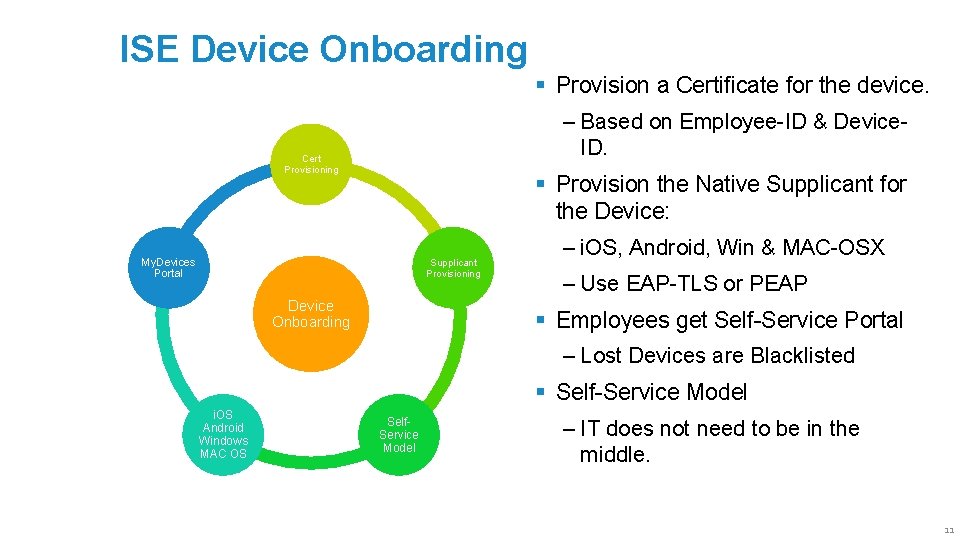
ISE Device Onboarding § Provision a Certificate for the device. ‒ Based on Employee-ID & Device. ID. Cert Provisioning § Provision the Native Supplicant for the Device: My. Devices Portal Supplicant Provisioning Device Onboarding ‒ i. OS, Android, Win & MAC-OSX ‒ Use EAP-TLS or PEAP § Employees get Self-Service Portal ‒ Lost Devices are Blacklisted § Self-Service Model i. OS Android Windows MAC OS Self. Service Model ‒ IT does not need to be in the middle. 11
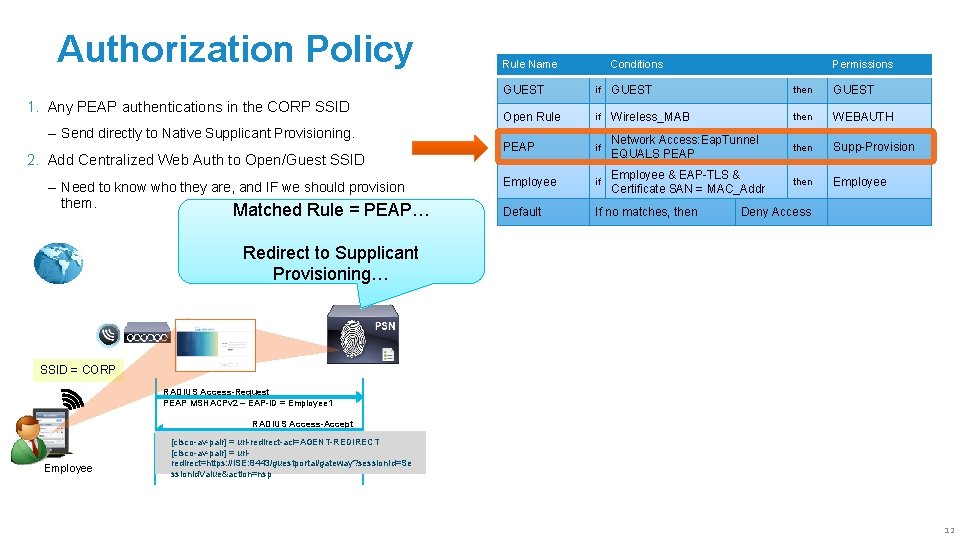
Authorization Policy 1. Any PEAP authentications in the CORP SSID ‒ Send directly to Native Supplicant Provisioning. 2. Add Centralized Web Auth to Open/Guest SSID ‒ Need to know who they are, and IF we should provision them. Matched Rule = PEAP… Rule Name Conditions Permissions GUEST if GUEST then GUEST Open Rule if Wireless_MAB then WEBAUTH PEAP if Network Access: Eap. Tunnel EQUALS PEAP then Supp-Provision Employee if Employee & EAP-TLS & Certificate SAN = MAC_Addr then Employee Default If no matches, then Deny Access Redirect to Supplicant Provisioning… SSID = CORP RADIUS Access-Request PEAP MSHACPv 2 – EAP-ID = Employee 1 RADIUS Access-Accept Employee [cisco-av-pair] = url-redirect-acl=AGENT-REDIRECT [cisco-av-pair] = urlredirect=https: //ISE: 8443/guestportal/gateway? session. Id=Se ssion. Id. Value&action=nsp 12
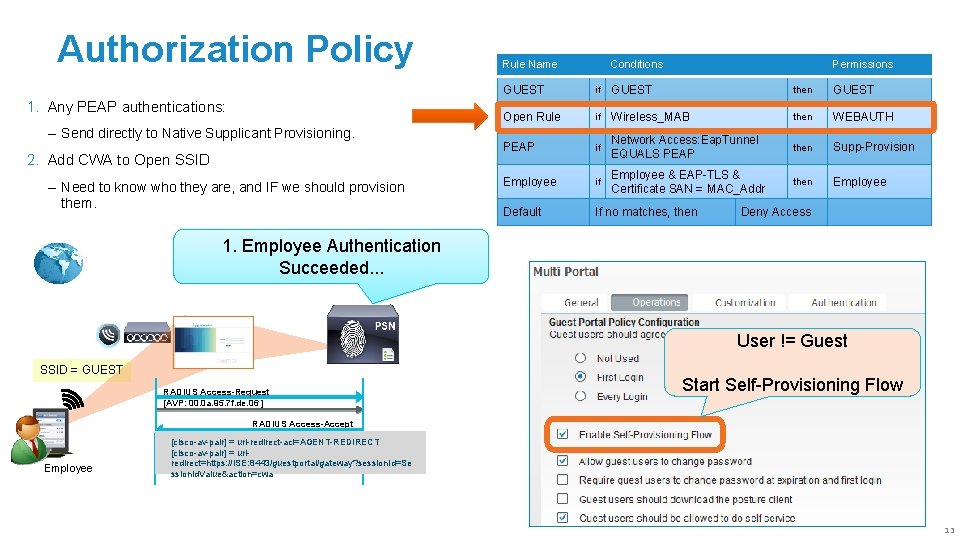
Authorization Policy 1. Any PEAP authentications: ‒ Send directly to Native Supplicant Provisioning. 2. Add CWA to Open SSID ‒ Need to know who they are, and IF we should provision them. Rule Name Conditions Permissions GUEST if GUEST then GUEST Open Rule if Wireless_MAB then WEBAUTH PEAP if Network Access: Eap. Tunnel EQUALS PEAP then Supp-Provision Employee if Employee & EAP-TLS & Certificate SAN = MAC_Addr then Employee Default If no matches, then Deny Access 1. Employee Authentication Succeeded. . . User != Guest SSID = GUEST RADIUS Access-Request [AVP: 00. 0 a. 95. 7 f. de. 06 ] Start Self-Provisioning Flow RADIUS Access-Accept Employee [cisco-av-pair] = url-redirect-acl=AGENT-REDIRECT [cisco-av-pair] = urlredirect=https: //ISE: 8443/guestportal/gateway? session. Id=Se ssion. Id. Value&action=cwa 13
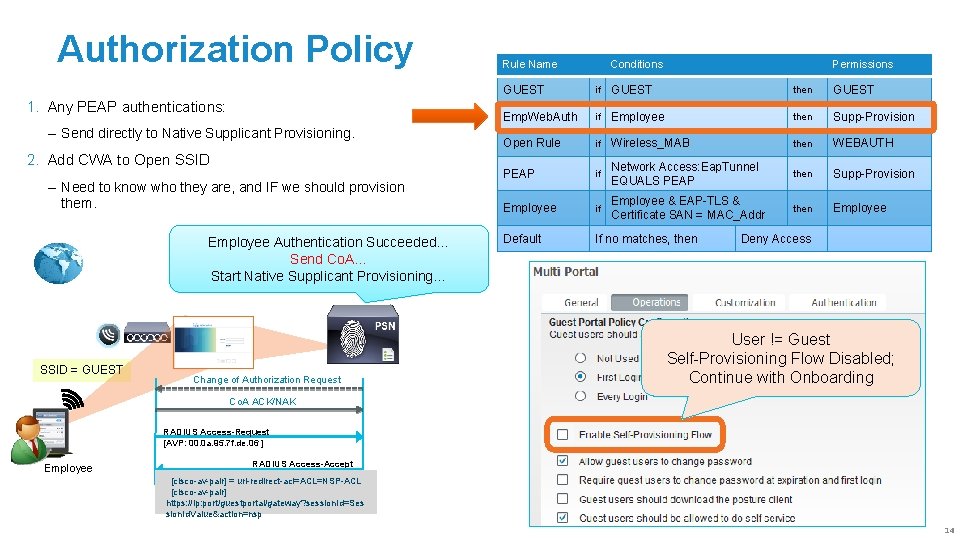
Authorization Policy 1. Any PEAP authentications: ‒ Send directly to Native Supplicant Provisioning. 2. Add CWA to Open SSID ‒ Need to know who they are, and IF we should provision them. Employee Authentication Succeeded… Send Co. A… Start Native Supplicant Provisioning… SSID = GUEST Change of Authorization Request Rule Name Conditions Permissions GUEST if GUEST then GUEST Emp. Web. Auth if Employee then Supp-Provision Open Rule if Wireless_MAB then WEBAUTH PEAP if Network Access: Eap. Tunnel EQUALS PEAP then Supp-Provision Employee if Employee & EAP-TLS & Certificate SAN = MAC_Addr then Employee Default If no matches, then Deny Access User != Guest Self-Provisioning Flow Disabled; Continue with Onboarding Co. A ACK/NAK RADIUS Access-Request [AVP: 00. 0 a. 95. 7 f. de. 06 ] Employee RADIUS Access-Accept [cisco-av-pair] = url-redirect-acl=ACL=NSP-ACL [cisco-av-pair] https: //ip: port/guestportal/gateway? session. Id=Ses sion. Id. Value&action=nsp 14
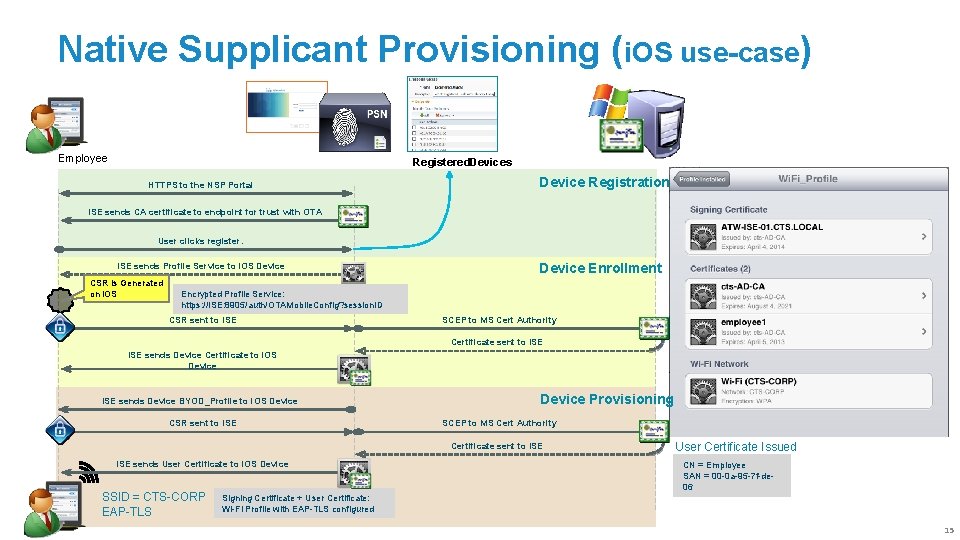
Native Supplicant Provisioning (i. OS use-case) Employee Registered. Devices HTTPS to the NSP Portal Device Registration ISE sends CA certificate to endpoint for trust with OTA User clicks register. ISE sends Profile Service to i. OS Device CSR is Generated on i. OS Device Enrollment Encrypted Profile Service: https: //ISE: 8905/auth/OTAMobile. Config? session. ID CSR sent to ISE SCEP to MS Cert Authority Certificate sent to ISE sends Device Certificate to i. OS Device ISE sends Device BYOD_Profile to i. OS Device CSR sent to ISE SSID = CTS-CORP EAP-TLS CN = 74 ba 333 ef 6548 dfc 82054 d 0 c 7 fec 36 e 6 ddddcbf 1 SAN = 00 -0 a-95 -7 f-de-06 Device Provisioning SCEP to MS Cert Authority Certificate sent to ISE sends User Certificate to i. OS Device Certificate Issued User Certificate Issued CN = Employee SAN = 00 -0 a-95 -7 f-de 06 Signing Certificate + User Certificate: Wi-Fi Profile with EAP-TLS configured 15
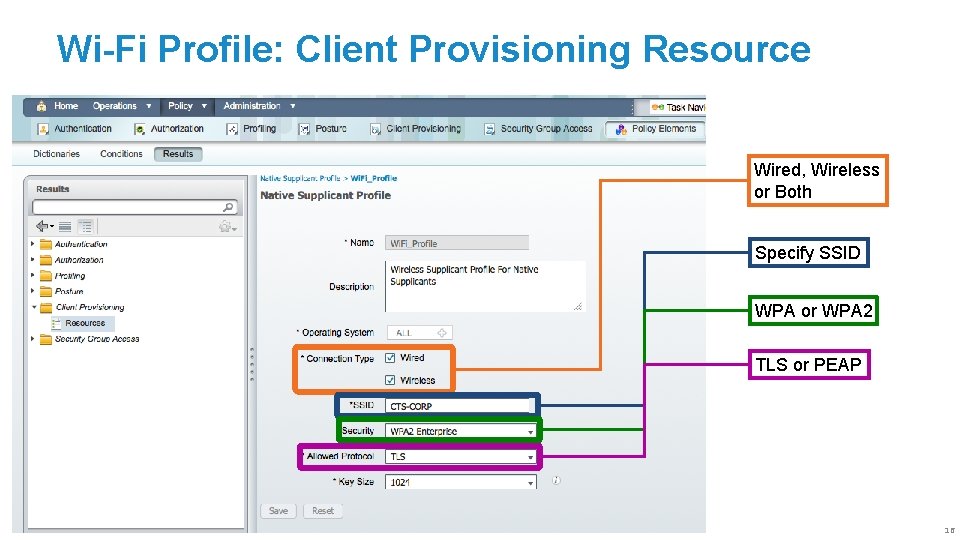
Wi-Fi Profile: Client Provisioning Resource Wired, Wireless or Both Specify SSID WPA or WPA 2 TLS or PEAP 16
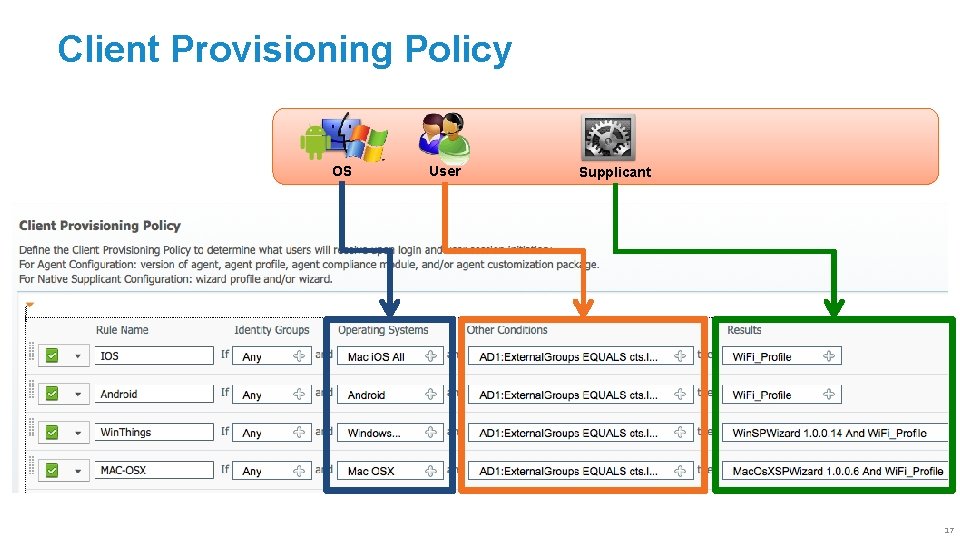
Client Provisioning Policy OS User Supplicant 17
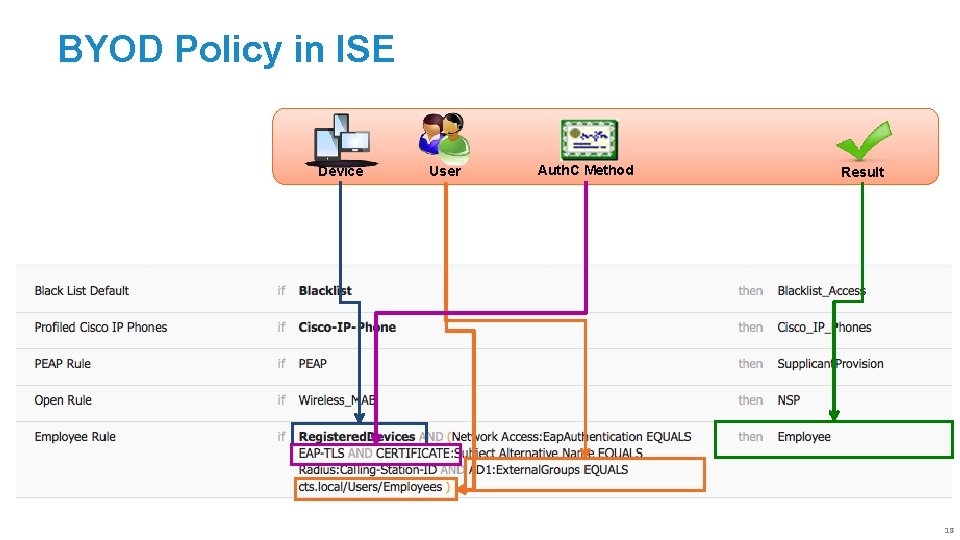
BYOD Policy in ISE Device User Auth. C Method Result 18
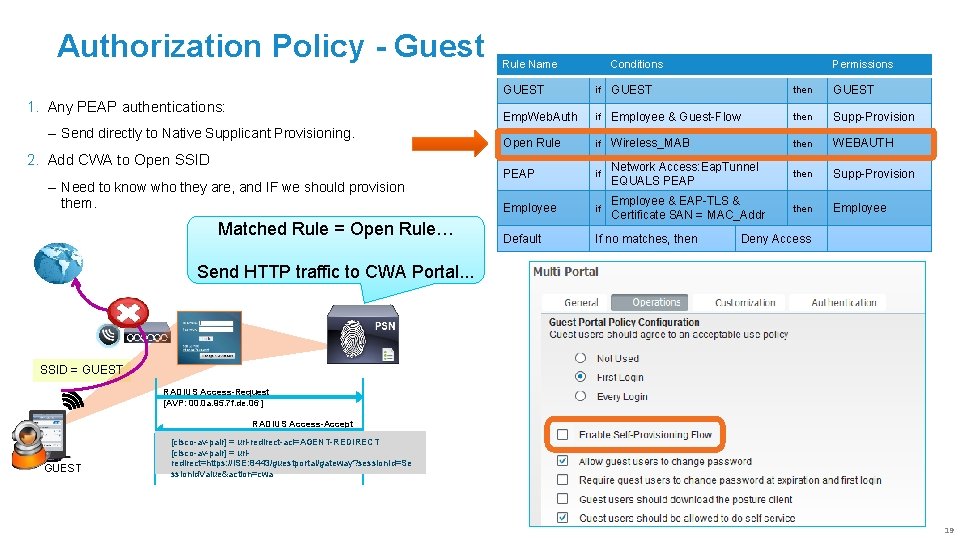
Authorization Policy - Guest 1. Any PEAP authentications: ‒ Send directly to Native Supplicant Provisioning. 2. Add CWA to Open SSID ‒ Need to know who they are, and IF we should provision them. Matched Rule = Open Rule… Rule Name Conditions Permissions GUEST if GUEST then GUEST Emp. Web. Auth if Employee & Guest-Flow then Supp-Provision Open Rule if Wireless_MAB then WEBAUTH PEAP if Network Access: Eap. Tunnel EQUALS PEAP then Supp-Provision Employee if Employee & EAP-TLS & Certificate SAN = MAC_Addr then Employee Default If no matches, then Deny Access Send HTTP traffic to CWA Portal. . . SSID = GUEST RADIUS Access-Request [AVP: 00. 0 a. 95. 7 f. de. 06 ] RADIUS Access-Accept GUEST [cisco-av-pair] = url-redirect-acl=AGENT-REDIRECT [cisco-av-pair] = urlredirect=https: //ISE: 8443/guestportal/gateway? session. Id=Se ssion. Id. Value&action=cwa 19
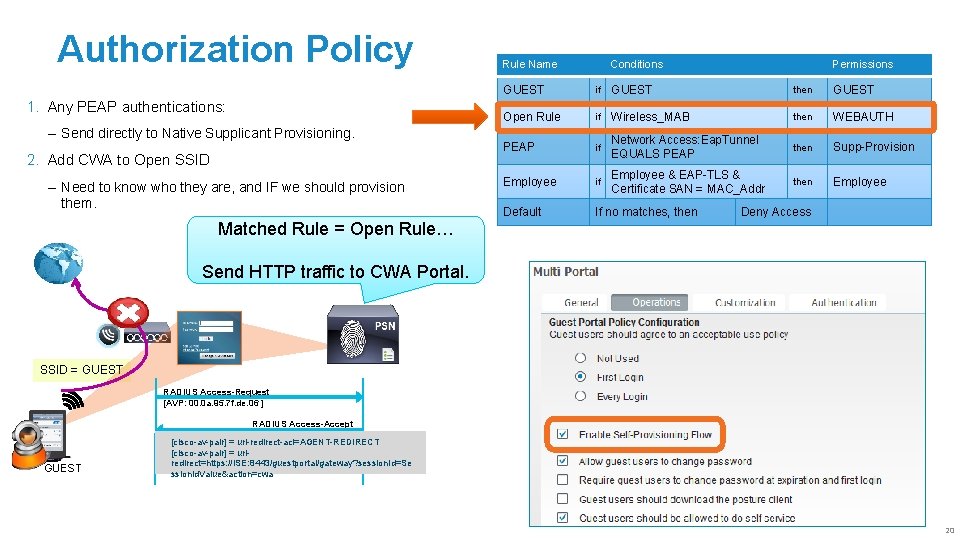
Authorization Policy 1. Any PEAP authentications: ‒ Send directly to Native Supplicant Provisioning. 2. Add CWA to Open SSID ‒ Need to know who they are, and IF we should provision them. Matched Rule = Open Rule… Rule Name Conditions Permissions GUEST if GUEST then GUEST Open Rule if Wireless_MAB then WEBAUTH PEAP if Network Access: Eap. Tunnel EQUALS PEAP then Supp-Provision Employee if Employee & EAP-TLS & Certificate SAN = MAC_Addr then Employee Default If no matches, then Deny Access Send HTTP traffic to CWA Portal. SSID = GUEST RADIUS Access-Request [AVP: 00. 0 a. 95. 7 f. de. 06 ] RADIUS Access-Accept GUEST [cisco-av-pair] = url-redirect-acl=AGENT-REDIRECT [cisco-av-pair] = urlredirect=https: //ISE: 8443/guestportal/gateway? session. Id=Se ssion. Id. Value&action=cwa 20
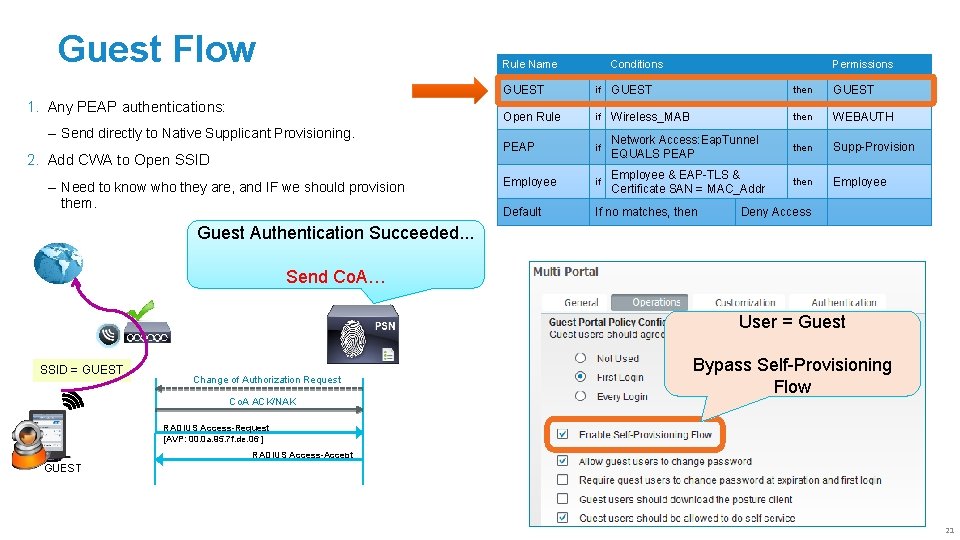
Guest Flow Rule Name 1. Any PEAP authentications: ‒ Send directly to Native Supplicant Provisioning. 2. Add CWA to Open SSID ‒ Need to know who they are, and IF we should provision them. Conditions Permissions GUEST if GUEST then GUEST Open Rule if Wireless_MAB then WEBAUTH PEAP if Network Access: Eap. Tunnel EQUALS PEAP then Supp-Provision Employee if Employee & EAP-TLS & Certificate SAN = MAC_Addr then Employee Default If no matches, then Deny Access Guest Authentication Succeeded. . . Send Co. A… User = Guest SSID = GUEST Change of Authorization Request Bypass Self-Provisioning Flow Co. A ACK/NAK RADIUS Access-Request [AVP: 00. 0 a. 95. 7 f. de. 06 ] RADIUS Access-Accept GUEST 21
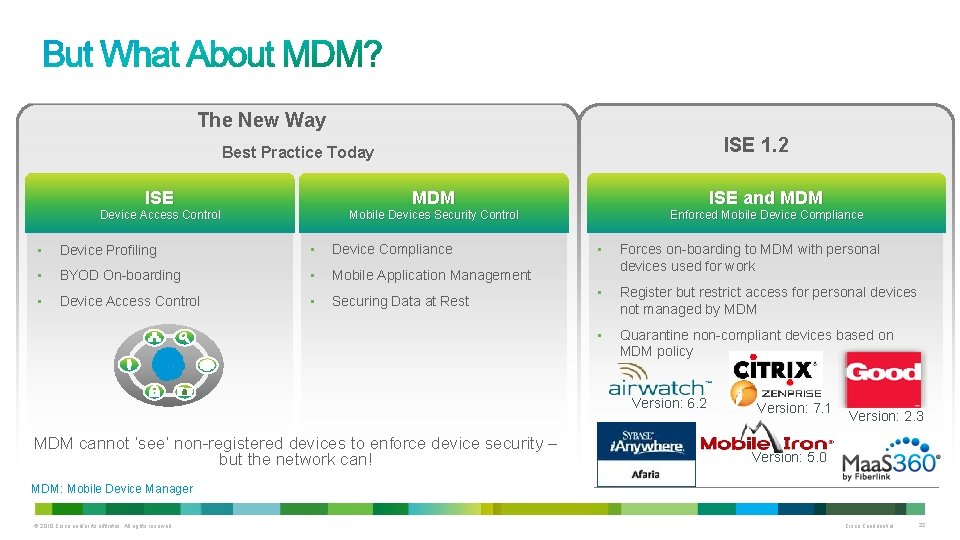
The New Way ISE 1. 2 Best Practice Today ISE MDM ISE and MDM Device Access Control Mobile Devices Security Control Enforced Mobile Device Compliance • Device Profiling • Device Compliance • BYOD On-boarding • Mobile Application Management • Device Access Control • Securing Data at Rest • Forces on-boarding to MDM with personal devices used for work • Register but restrict access for personal devices not managed by MDM • Quarantine non-compliant devices based on MDM policy Version: 6. 2 MDM cannot ‘see’ non-registered devices to enforce device security – but the network can! Version: 7. 1 Version: 2. 3 Version: 5. 0 MDM: Mobile Device Manager © 2010 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 22
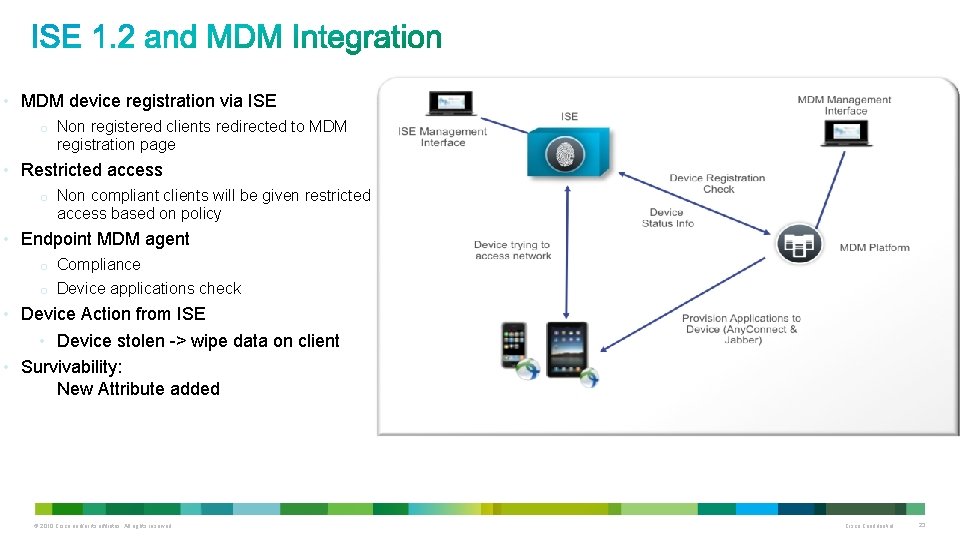
• MDM device registration via ISE o Non registered clients redirected to MDM registration page • Restricted access o Non compliant clients will be given restricted access based on policy • Endpoint MDM agent o Compliance o Device applications check • Device Action from ISE • Device stolen -> wipe data on client • Survivability: New Attribute added © 2010 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 23
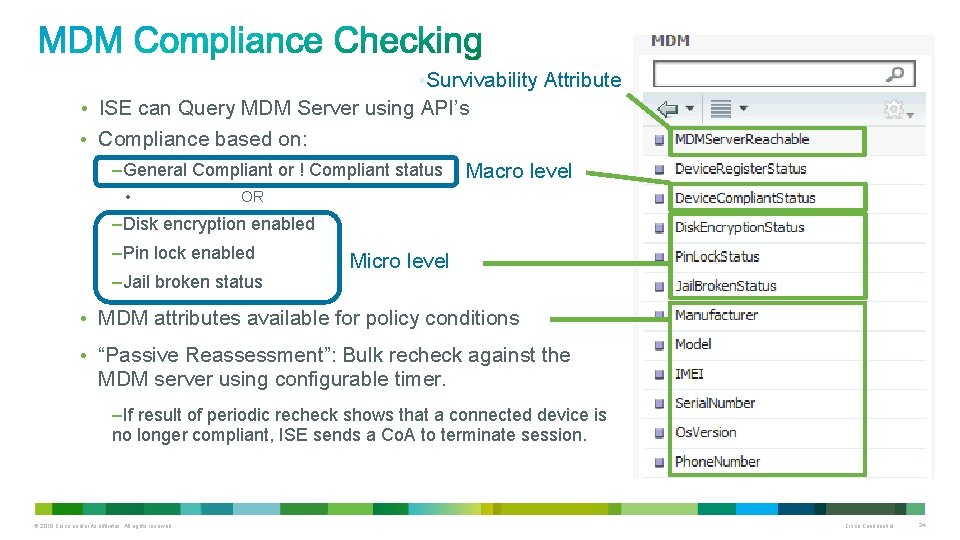
• Survivability Attribute • ISE can Query MDM Server using API’s • Compliance based on: –General Compliant or ! Compliant status • Macro level OR –Disk encryption enabled –Pin lock enabled –Jail broken status Micro level • MDM attributes available for policy conditions • “Passive Reassessment”: Bulk recheck against the MDM server using configurable timer. –If result of periodic recheck shows that a connected device is no longer compliant, ISE sends a Co. A to terminate session. © 2010 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 24
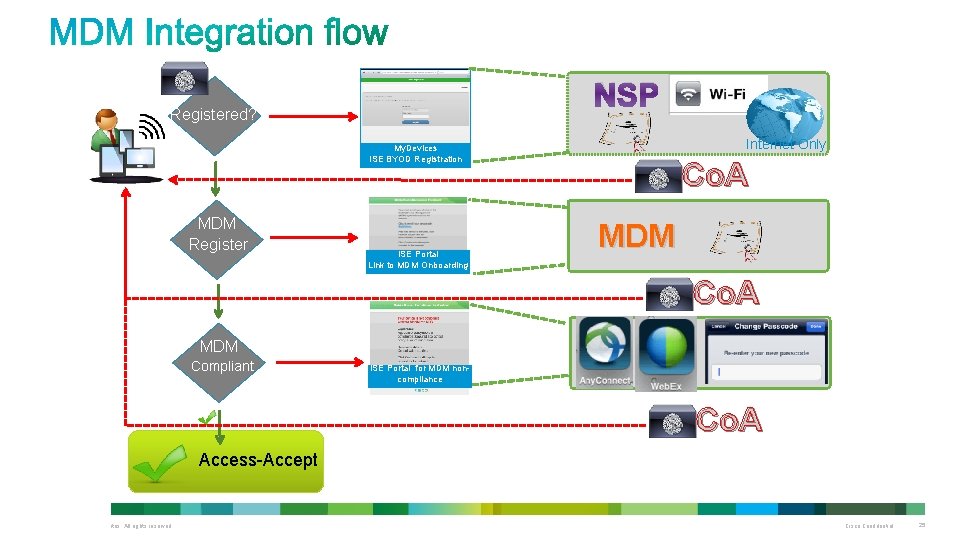
NSP Registered? Internet Only My. Devices ISE BYOD Registration MDM Register ISE Portal Link to MDM Onboarding Co. A MDM Compliant ISE Portal for MDM noncompliance Co. A Access-Accept © 2010 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 25
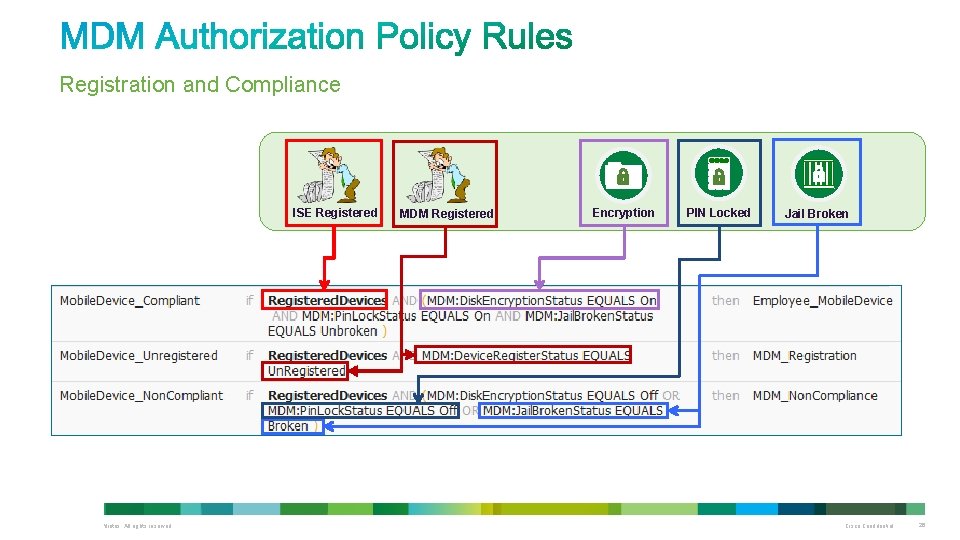
Registration and Compliance ISE Registered MDM Registered Encryption PIN Locked Jail Broken © 2010 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 26
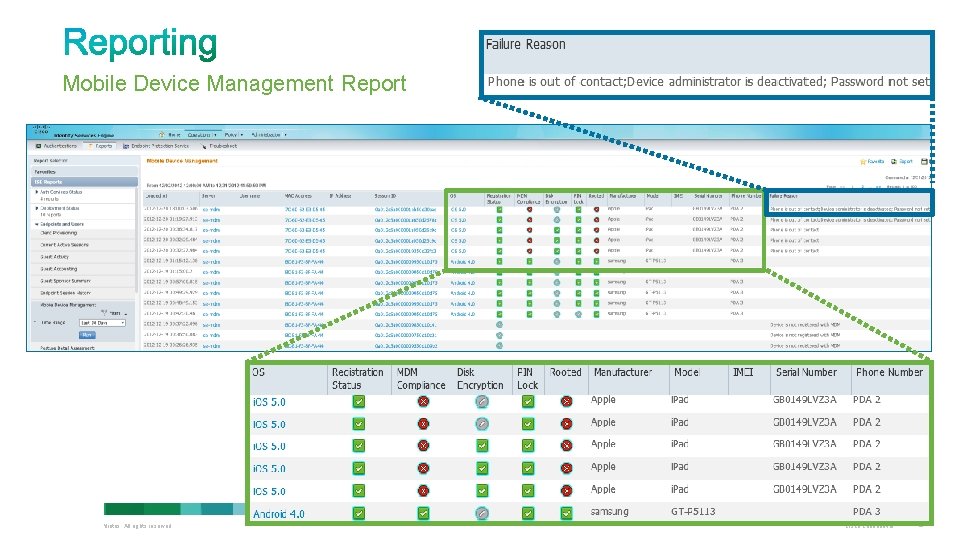
Mobile Device Management Report © 2010 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 27

Thank you.
- Slides: 28