Iron Port Gateway Security Products Next Generation Perimeter





- Slides: 59
Iron. Port Gateway Security Products Next Generation Perimeter Security Gateway for Email & Web Anurak Chuetanapinyo Technical Consultant – Thailand Vietnam Iron. Port Systems, A Cisco Business Unit anurak@ironport. com / anurak@cisco. com
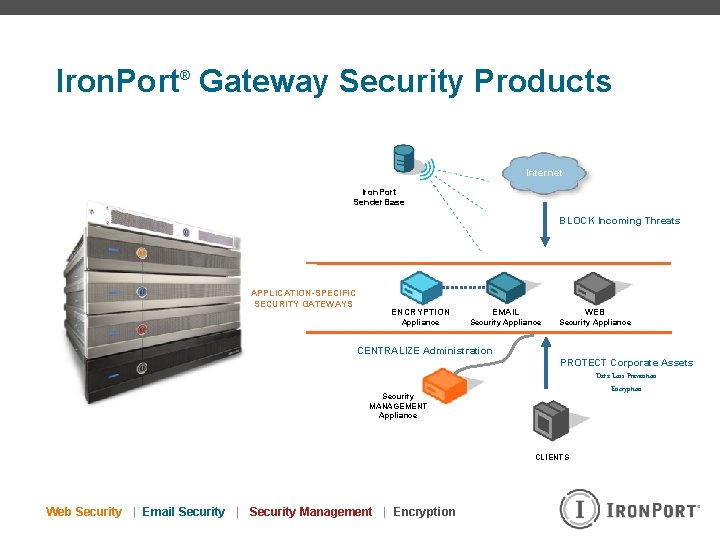
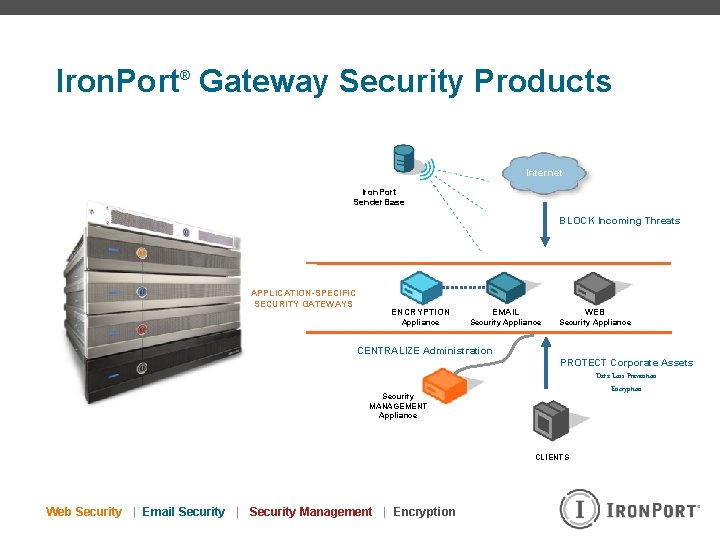
Iron. Port® Gateway Security Products Internet Iron. Port Sender. Base BLOCK Incoming Threats APPLICATION-SPECIFIC SECURITY GATEWAYS ENCRYPTION EMAIL WEB Appliance Security Appliance CENTRALIZE Administration Security MANAGEMENT Appliance PROTECT Corporate Assets Data Loss Prevention Encryption CLIENTS Web Security | Email Security | Security Management | Encryption
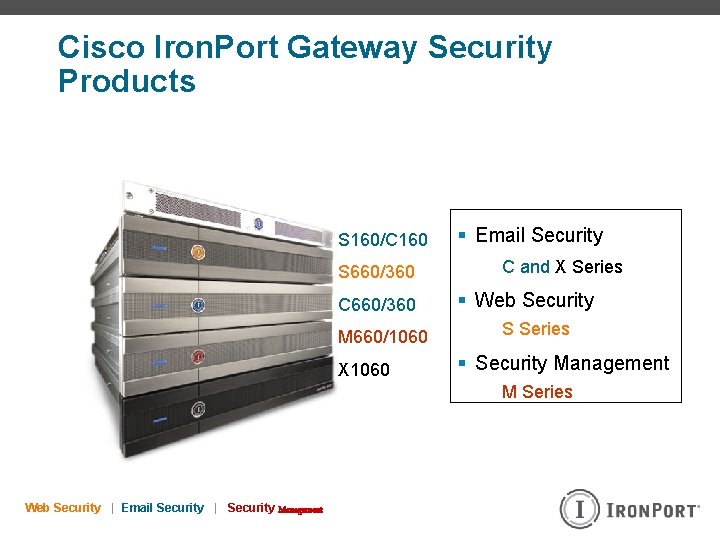
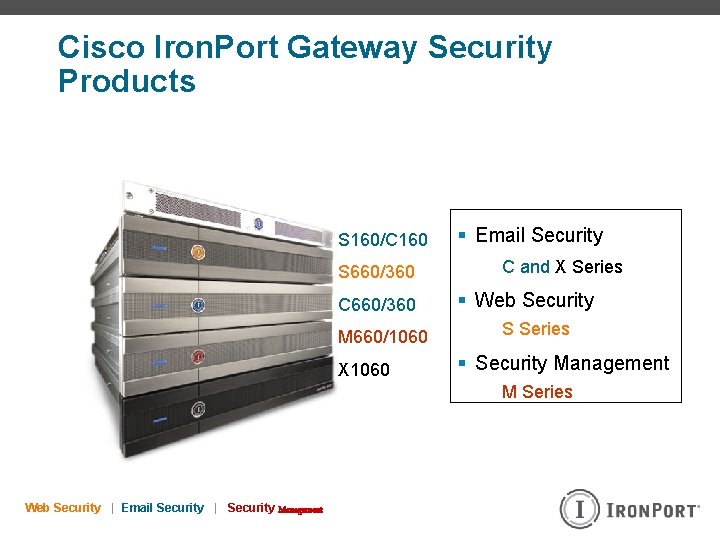
Cisco Iron. Port Gateway Security Products S 160/C 160 S 660/360 C 660/360 M 660/1060 X 1060 § Email Security C and X Series § Web Security S Series § Security Management M Series Web Security | Email Security | Security Management
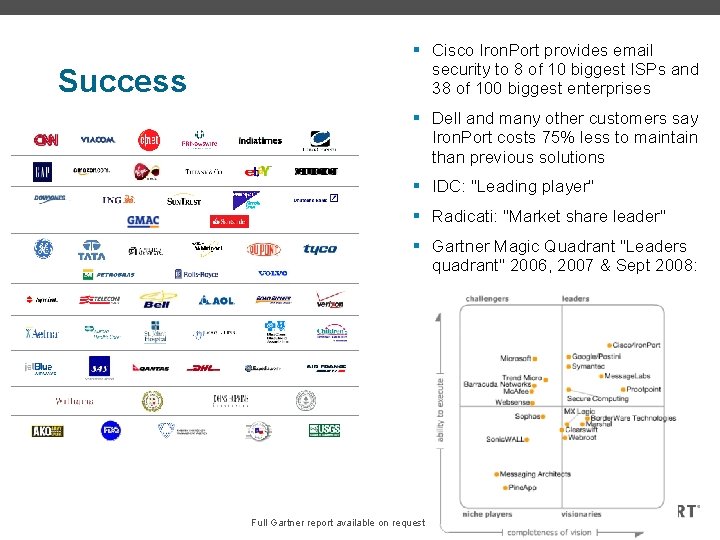
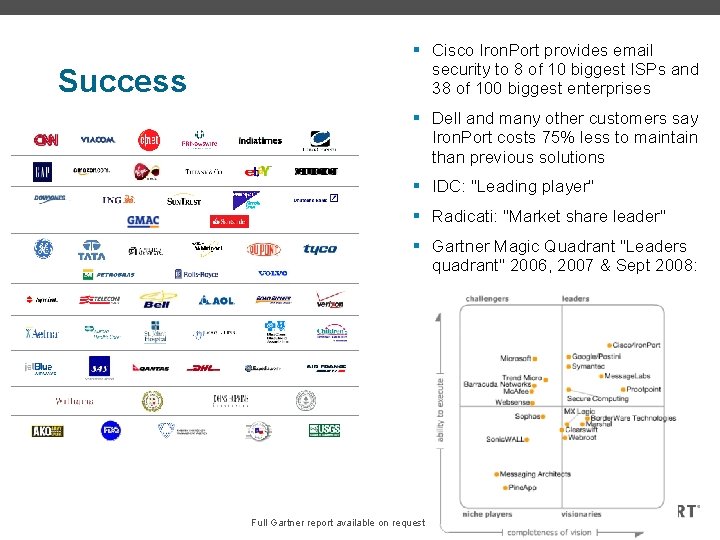
Success § Cisco Iron. Port provides email security to 8 of 10 biggest ISPs and 38 of 100 biggest enterprises § Dell and many other customers say Iron. Port costs 75% less to maintain than previous solutions § IDC: "Leading player" § Radicati: "Market share leader" § Gartner Magic Quadrant "Leaders quadrant" 2006, 2007 & Sept 2008: Full Gartner report available on request

Cisco Iron. Port Protects Fortune Top Companies § 40% of the Fortune 10 § 42% of the Fortune 50 § 42% of the Fortune 100 § 28% of the Fortune 500 § 39% of the Fortune 1000 § 35% of the Fortune Global 500 § 95% of the Fortune 100 Most Accountable Companies* * This list ranks the world’s largest 100 corporations by their quality of their commitment to social and environmental goals.
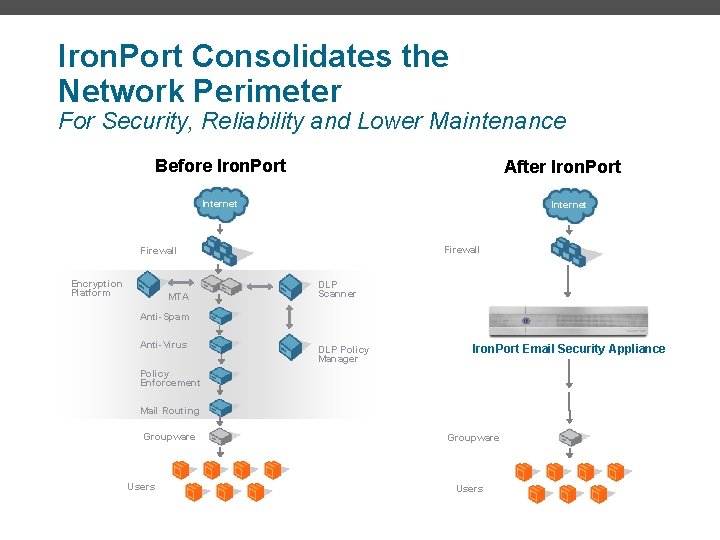
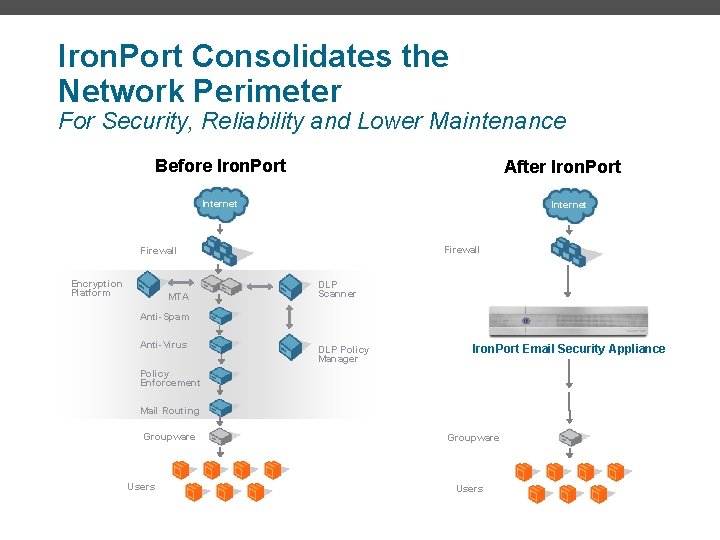
Iron. Port Consolidates the Network Perimeter For Security, Reliability and Lower Maintenance Before Iron. Port After Iron. Port Internet Firewall Encryption Platform MTA DLP Scanner Anti-Spam Anti-Virus DLP Policy Manager Iron. Port Email Security Appliance Policy Enforcement Mail Routing Groupware Users
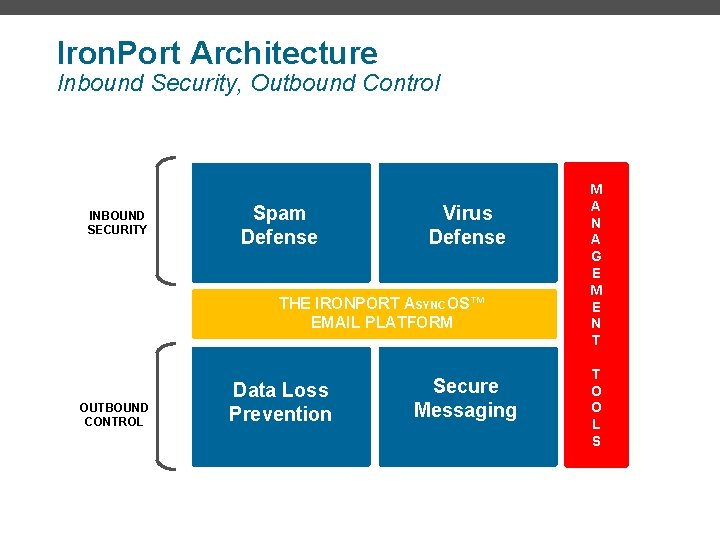
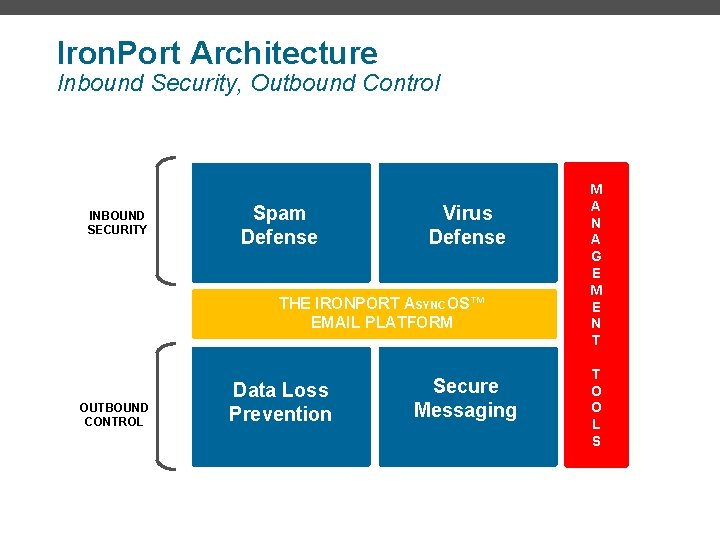
Iron. Port Architecture Inbound Security, Outbound Control INBOUND SECURITY Spam Defense Virus Defense THE IRONPORT ASYNCOS™ EMAIL PLATFORM OUTBOUND CONTROL Data Loss Prevention Secure Messaging M A N A G E M E N T T O O L S
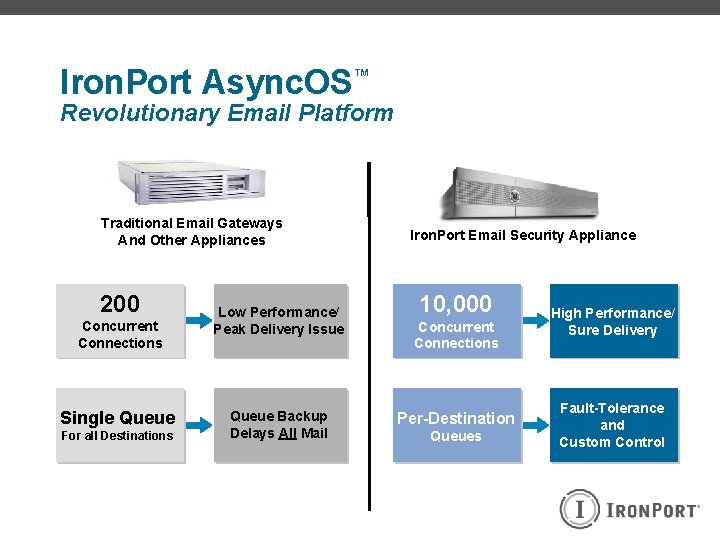
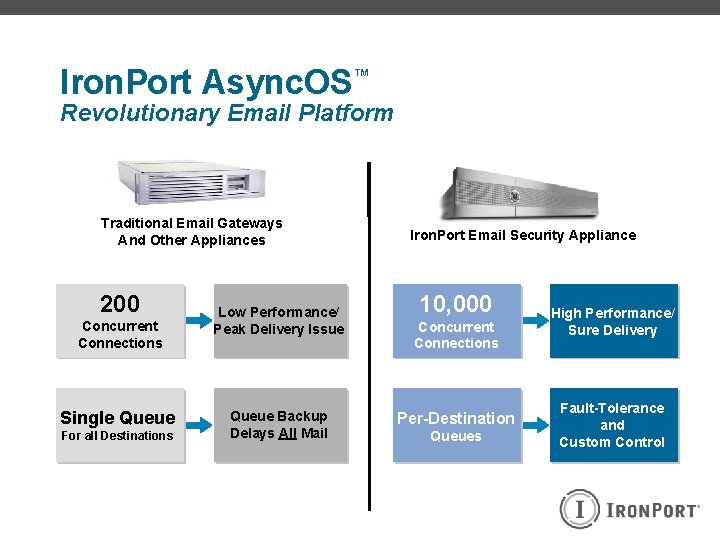
Iron. Port Async. OS™ Revolutionary Email Platform Traditional Email Gateways And Other Appliances 200 Concurrent Connections Single Queue For all Destinations Low Performance/ Peak Delivery Issue Queue Backup Delays All Mail Iron. Port Email Security Appliance 10, 000 Concurrent Connections Per-Destination Queues High Performance/ Sure Delivery Fault-Tolerance and Custom Control
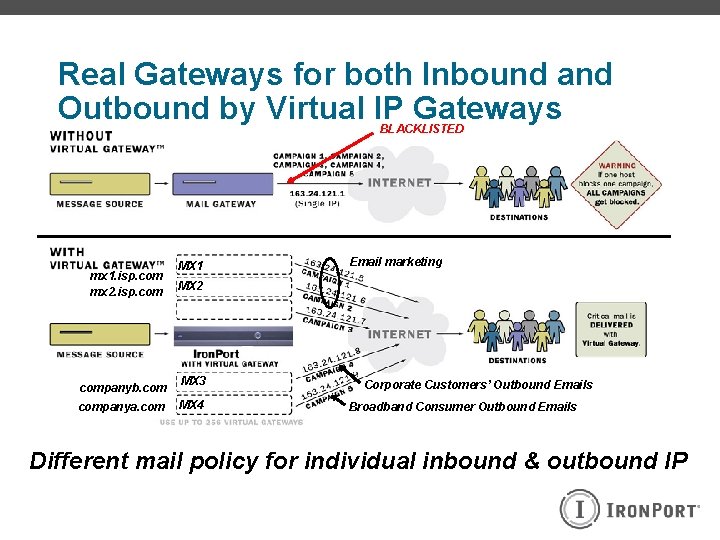
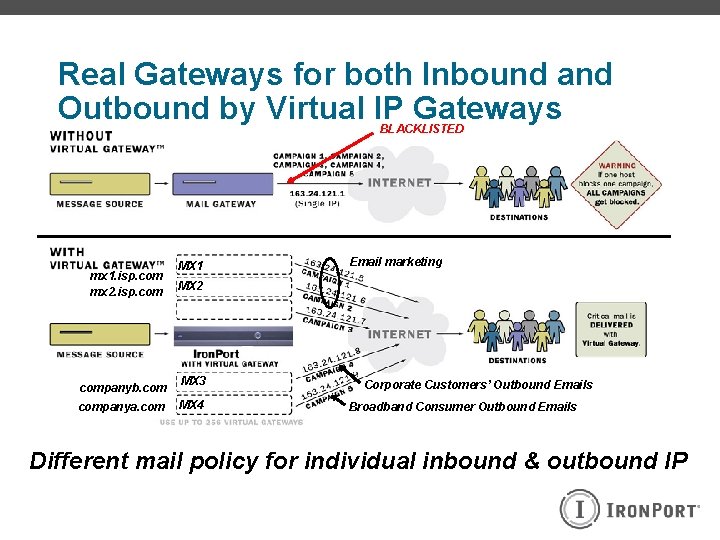
Real Gateways for both Inbound and Outbound by Virtual IP Gateways BLACKLISTED mx 1. isp. com mx 2. isp. companyb. companya. com MX 1 Email marketing MX 2 MX 3 MX 4 Corporate Customers’ Outbound Emails Broadband Consumer Outbound Emails Different mail policy for individual inbound & outbound IP
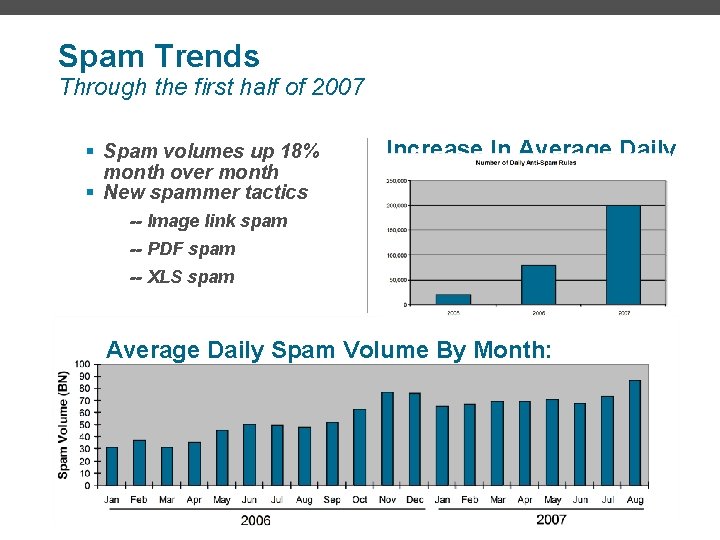
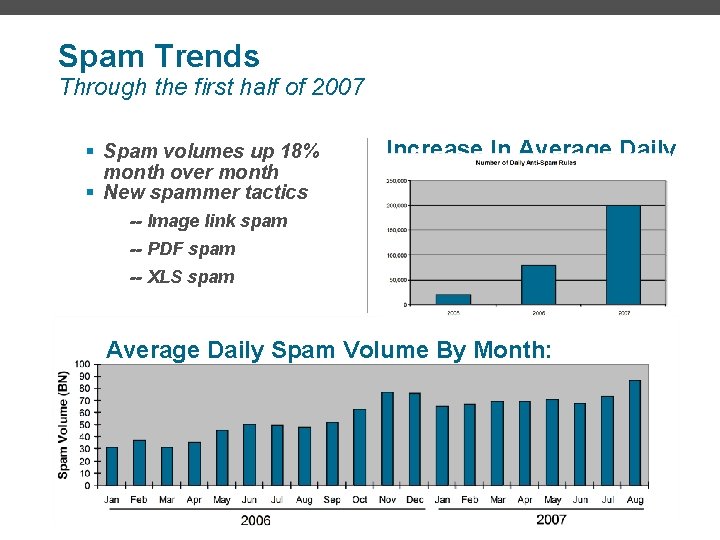
Spam Trends Through the first half of 2007 § Spam volumes up 18% month over month § New spammer tactics Increase In Average Daily Spam Rules -- Image link spam -- PDF spam -- XLS spam Average Daily Spam Volume By Month: 2006 -2007
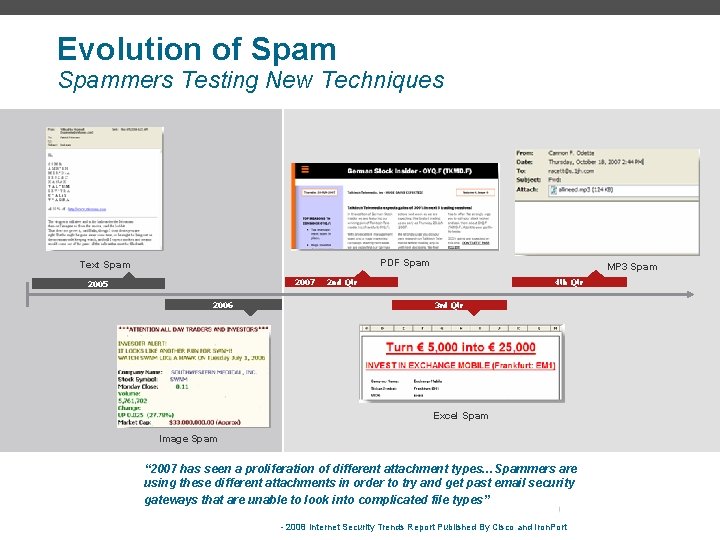
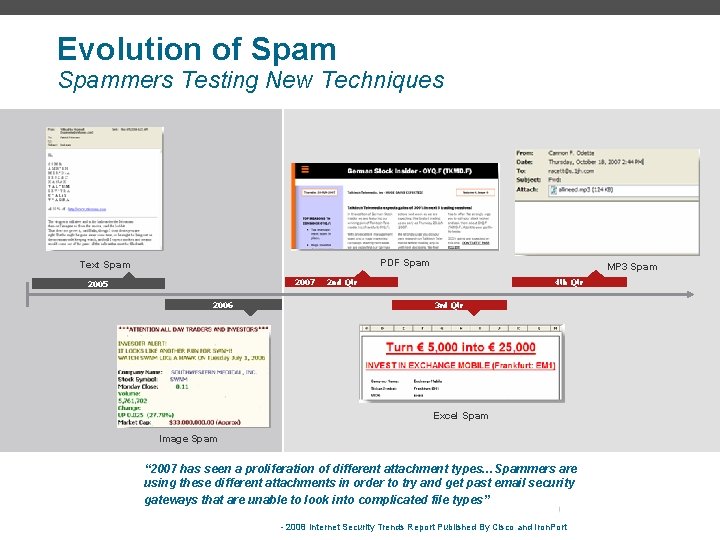
Evolution of Spammers Testing New Techniques PDF Spam Text Spam 2007 2005 2006 MP 3 Spam 2 nd Qtr 4 th Qtr 3 rd Qtr Excel Spam Image Spam “ 2007 has seen a proliferation of different attachment types…Spammers are using these different attachments in order to try and get past email security gateways that are unable to look into complicated file types” - 2008 Internet Security Trends Report Published By Cisco and Iron. Port
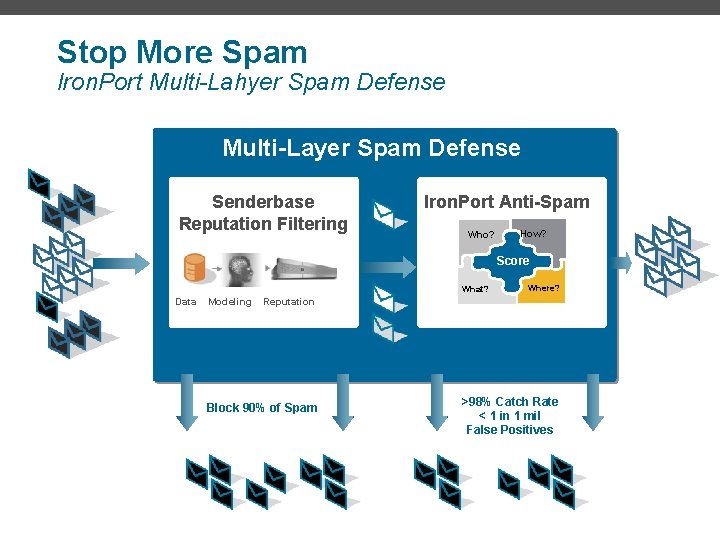
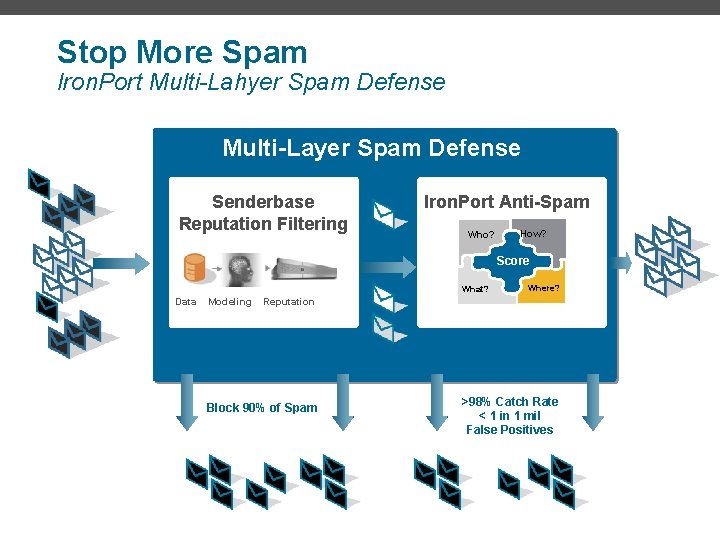
Stop More Spam Iron. Port Multi-Lahyer Spam Defense Multi-Layer Spam Defense Senderbase Reputation Filtering Iron. Port Anti-Spam Who? How? Score CASE What? Data Modeling Where? Reputation Block 90% of Spam >98% Catch Rate < 1 in 1 mil False Positives
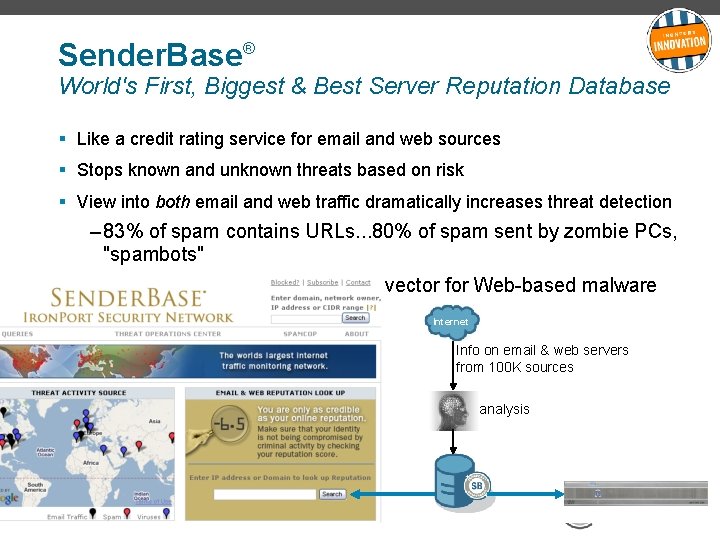
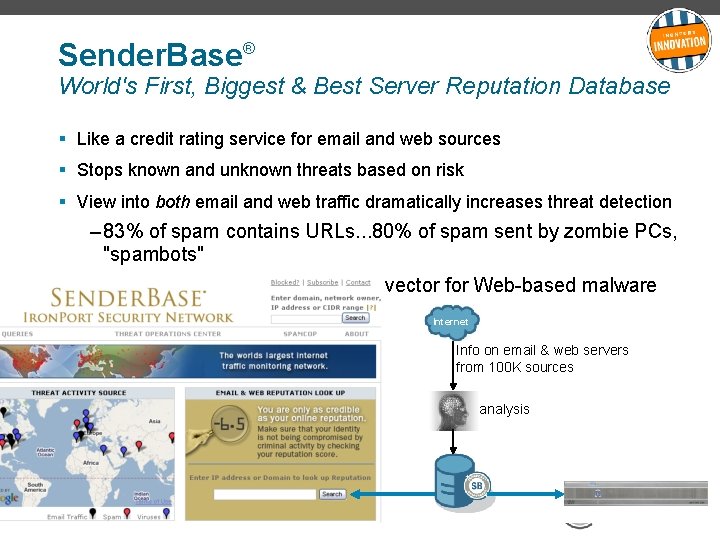
Sender. Base® World's First, Biggest & Best Server Reputation Database § Like a credit rating service for email and web sources § Stops known and unknown threats based on risk § View into both email and web traffic dramatically increases threat detection – 83% of spam contains URLs. . . 80% of spam sent by zombie PCs, "spambots" – Email is a still a key distribution vector for Web-based malware Internet Info on email & web servers from 100 K sources analysis
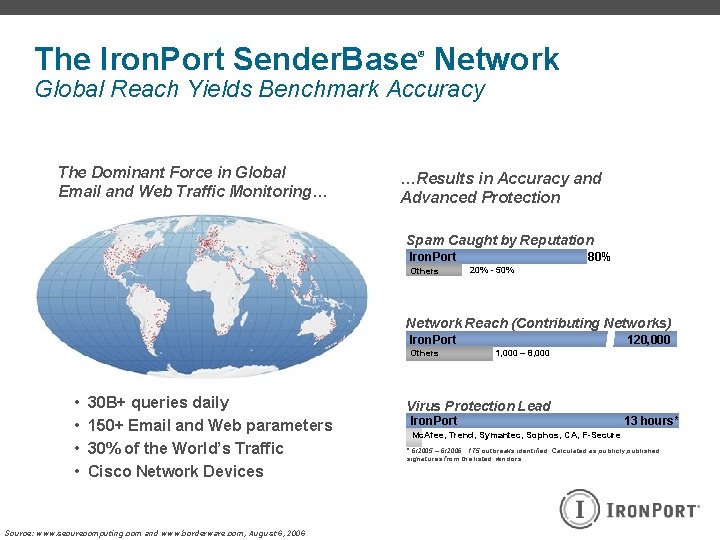
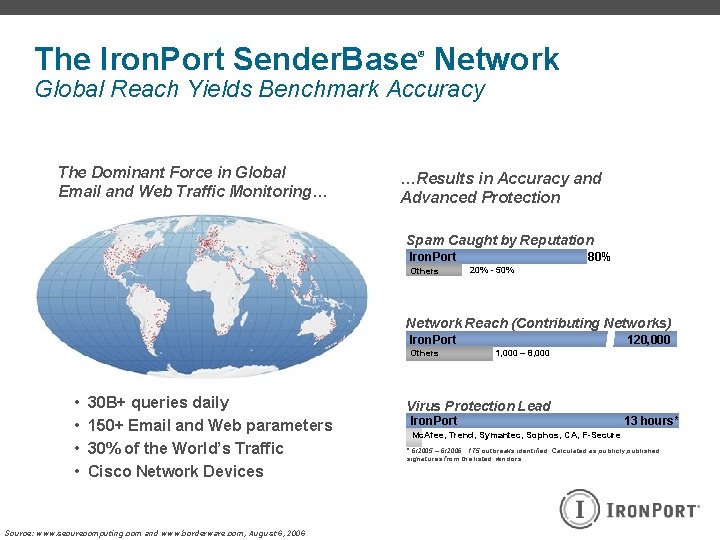
The Iron. Port Sender. Base Network ® Global Reach Yields Benchmark Accuracy The Dominant Force in Global Email and Web Traffic Monitoring… …Results in Accuracy and Advanced Protection Spam Caught by Reputation 80% Iron. Port Others 20% - 50% Network Reach (Contributing Networks) Iron. Port Others • • 30 B+ queries daily 150+ Email and Web parameters 30% of the World’s Traffic Cisco Network Devices Source: www. securecomputing. com and www. borderware. com, August 6, 2006 120, 000 1, 000 – 8, 000 Virus Protection Lead Iron. Port 13 hours* Mc. Afee, Trend, Symantec, Sophos, CA, F-Secure * 6/2005 – 6/2006. 175 outbreaks identified. Calculated as publicly published signatures from the listed vendors.
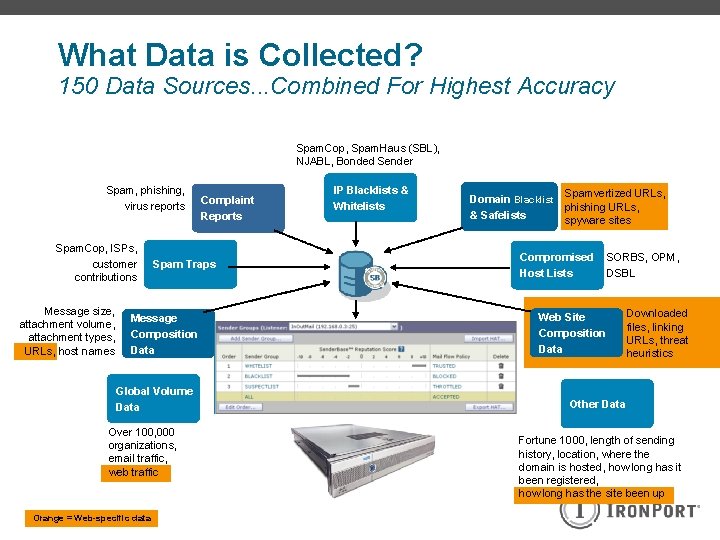
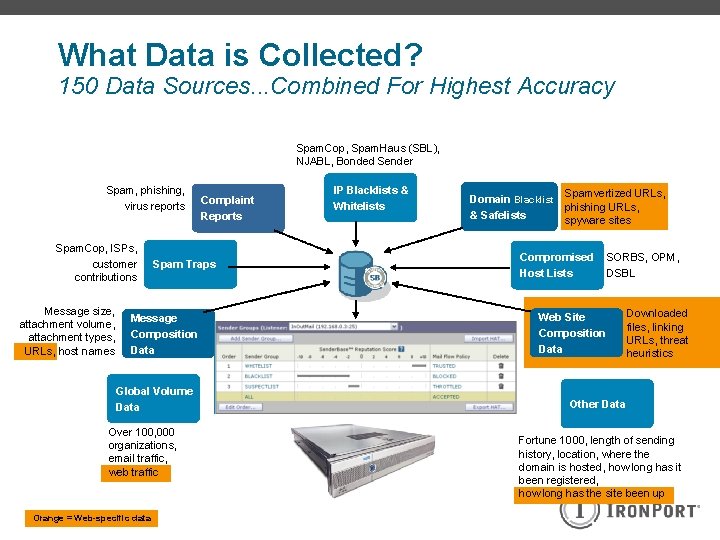
What Data is Collected? 150 Data Sources. . . Combined For Highest Accuracy Spam. Cop, Spam. Haus (SBL), NJABL, Bonded Sender Spam, phishing, virus reports Spam. Cop, ISPs, customer contributions Message size, attachment volume, attachment types, URLs, host names Spam Traps Message Composition Data Global Volume Data Over 100, 000 organizations, email traffic, web traffic Orange = Web-specific data Complaint Reports IP Blacklists & Whitelists Domain Blacklist Spamvertized URLs, phishing URLs, & Safelists spyware sites Compromised Host Lists SORBS, OPM, DSBL Web Site Composition Data Downloaded files, linking URLs, threat heuristics Other Data Fortune 1000, length of sending history, location, where the domain is hosted, how long has it been registered, how long has the site been up
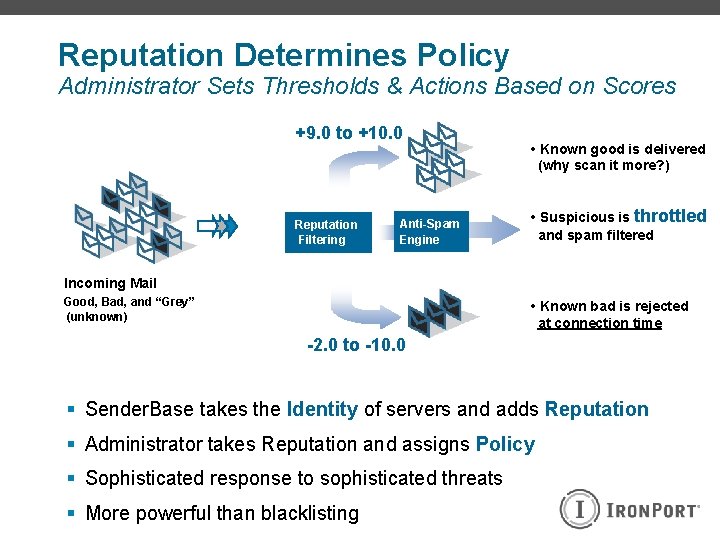
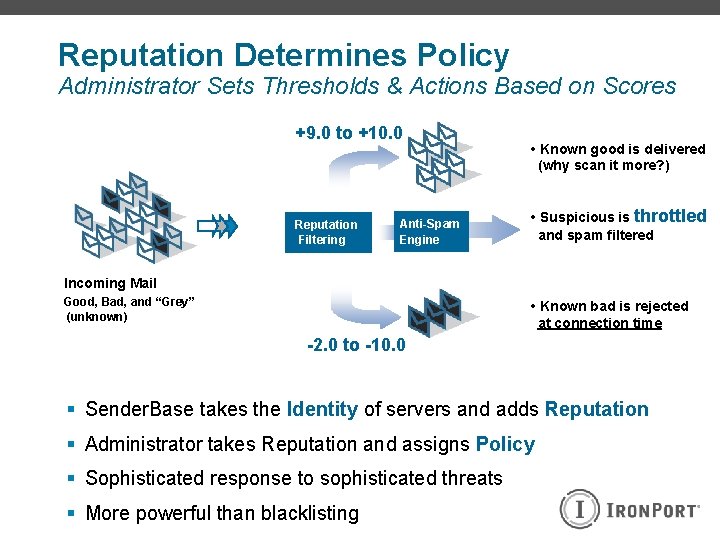
Reputation Determines Policy Administrator Sets Thresholds & Actions Based on Scores +9. 0 to +10. 0 Reputation Filtering Anti-Spam Engine • Known good is delivered (why scan it more? ) • Suspicious is throttled and spam filtered Incoming Mail Good, Bad, and “Grey” (unknown) • Known bad is rejected at connection time -2. 0 to -10. 0 § Sender. Base takes the Identity of servers and adds Reputation § Administrator takes Reputation and assigns Policy § Sophisticated response to sophisticated threats § More powerful than blacklisting
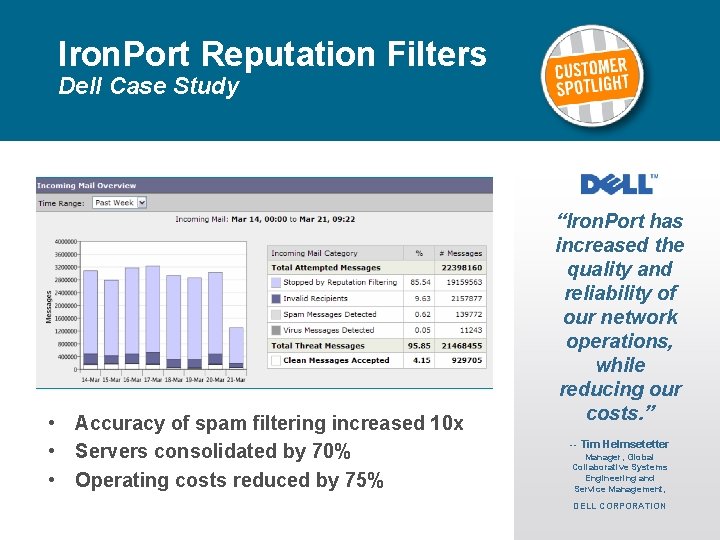
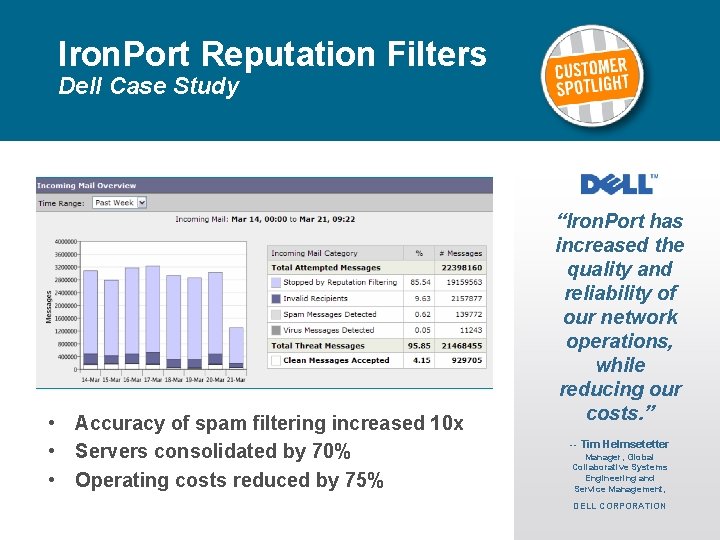
Iron. Port Reputation Filters Dell Case Study • Accuracy of spam filtering increased 10 x • Servers consolidated by 70% • Operating costs reduced by 75% “Iron. Port has increased the quality and reliability of our network operations, while reducing our costs. ” -- Tim Helmsetetter Manager, Global Collaborative Systems Engineering and Service Management, DELL CORPORATION
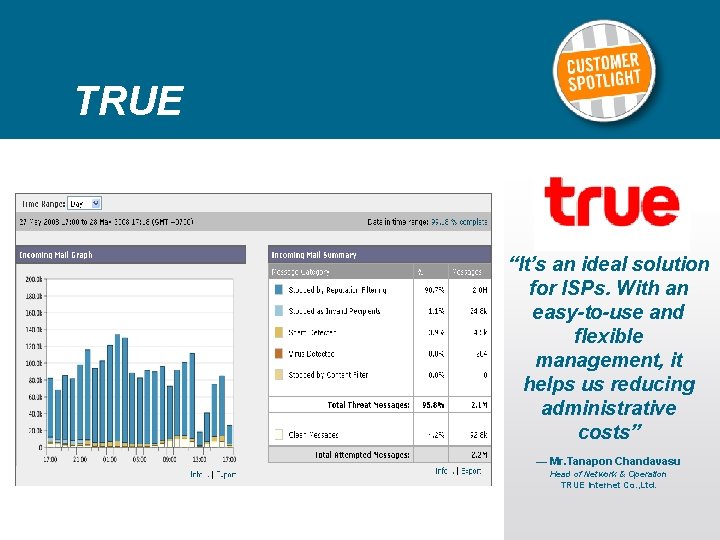
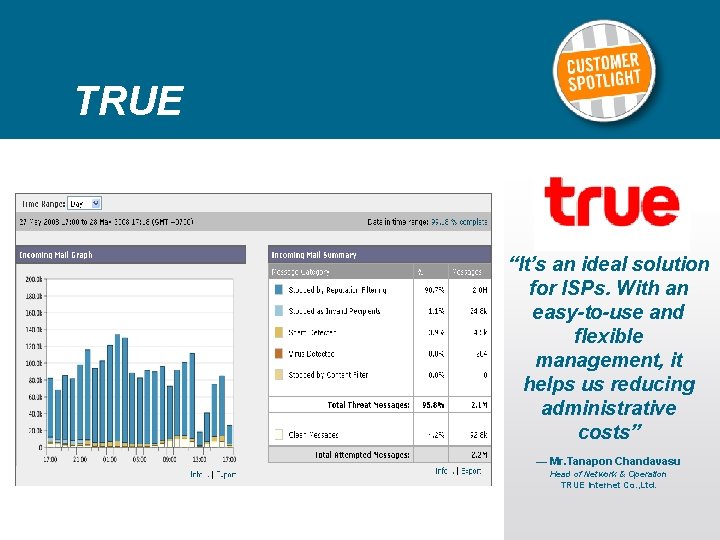
TRUE “It’s an ideal solution for ISPs. With an easy-to-use and flexible management, it helps us reducing administrative costs” — Mr. Tanapon Chandavasu Head of Network & Operation TRUE Internet Co. , Ltd.
Cisco Iron. Port Spam Defense Thompson Machinery Case Study “I simply plugged it in, set it up and walked away. No more spam problems! The ROI on this product is a no-brainer. ” — David Jones IT Administrator USERS PROTECTED 500+
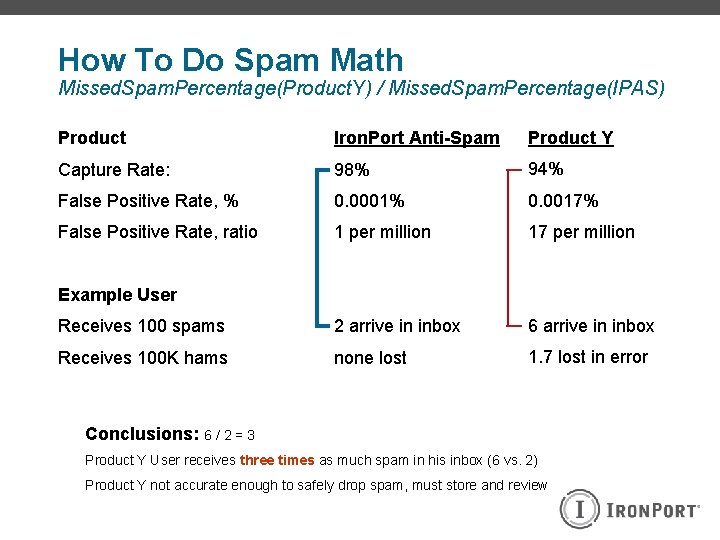
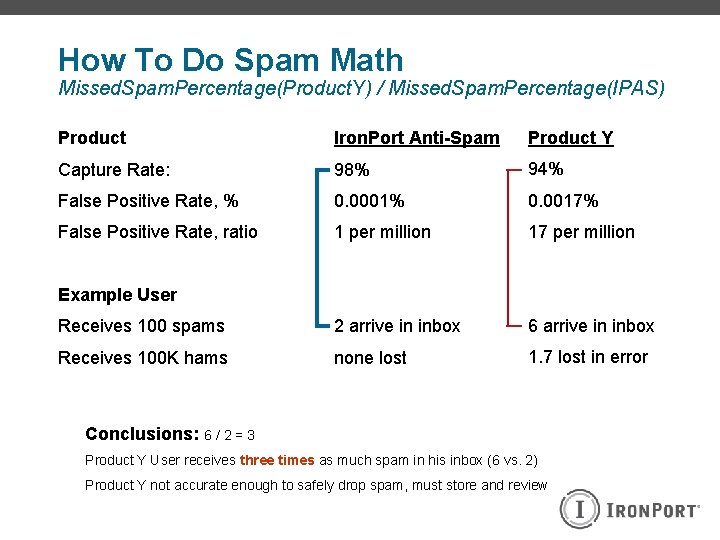
How To Do Spam Math Missed. Spam. Percentage(Product. Y) / Missed. Spam. Percentage(IPAS) Product Iron. Port Anti-Spam Product Y Capture Rate: 98% 94% False Positive Rate, % 0. 0001% 0. 0017% False Positive Rate, ratio 1 per million 17 per million Receives 100 spams 2 arrive in inbox 6 arrive in inbox Receives 100 K hams none lost 1. 7 lost in error Example User Conclusions: 6 / 2 = 3 Product Y User receives three times as much spam in his inbox (6 vs. 2) Product Y not accurate enough to safely drop spam, must store and review
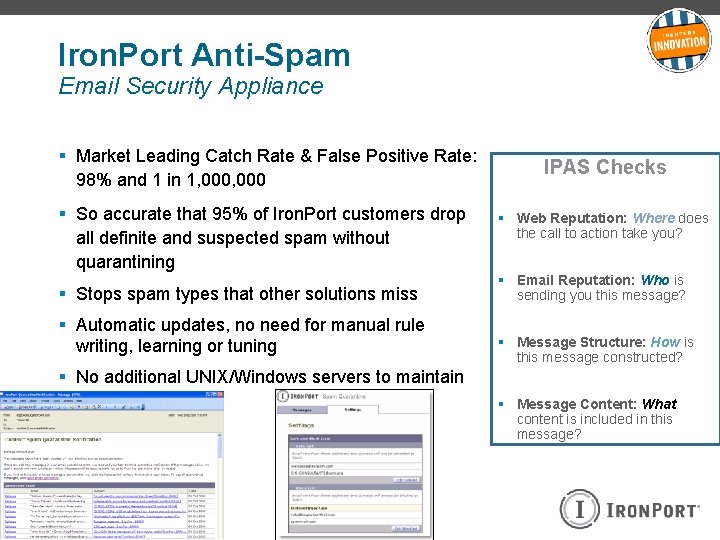
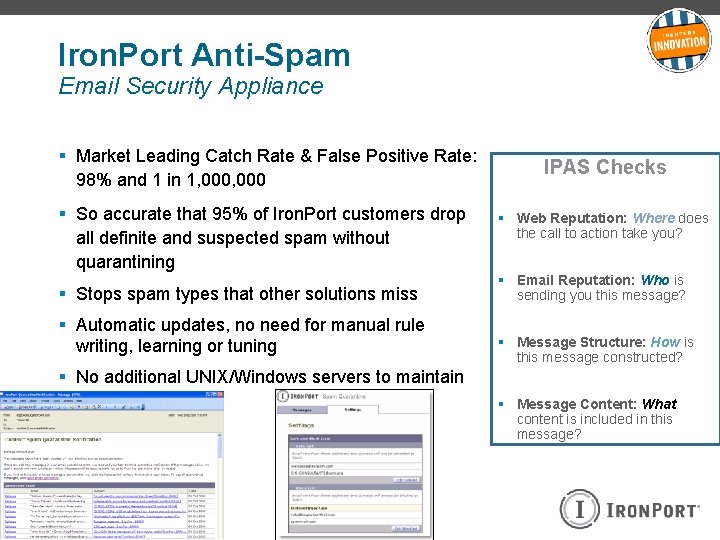
Iron. Port Anti-Spam Email Security Appliance § Market Leading Catch Rate & False Positive Rate: 98% and 1 in 1, 000 § So accurate that 95% of Iron. Port customers drop all definite and suspected spam without quarantining § Stops spam types that other solutions miss § Automatic updates, no need for manual rule writing, learning or tuning IPAS Checks § Web Reputation: Where does the call to action take you? § Email Reputation: Who is sending you this message? § Message Structure: How is this message constructed? § No additional UNIX/Windows servers to maintain § Message Content: What content is included in this message?
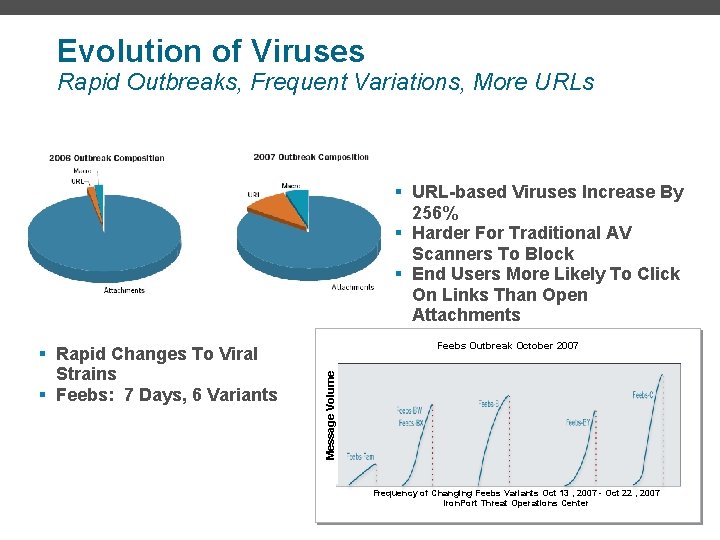
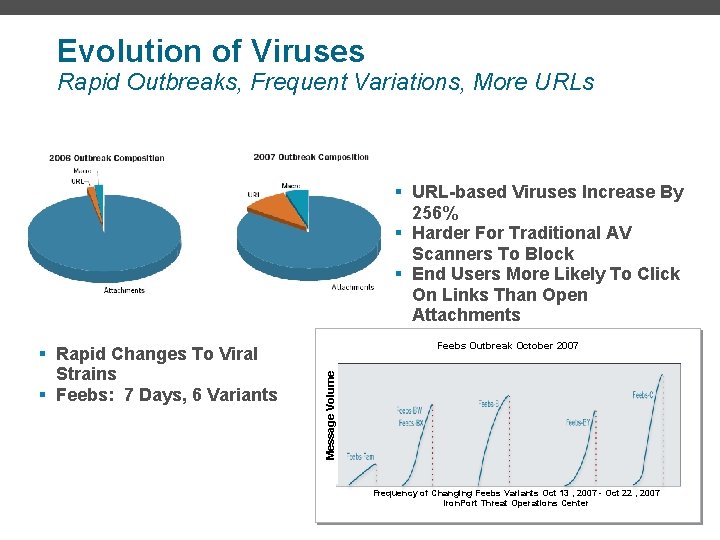
Evolution of Viruses Rapid Outbreaks, Frequent Variations, More URLs § URL-based Viruses Increase By 256% § Harder For Traditional AV Scanners To Block § End Users More Likely To Click On Links Than Open Attachments Feebs Outbreak October 2007 Message Volume § Rapid Changes To Viral Strains § Feebs: 7 Days, 6 Variants Frequency of Changing Feebs Variants Oct 13 , 2007 - Oct 22 , 2007 Iron. Port Threat Operations Center
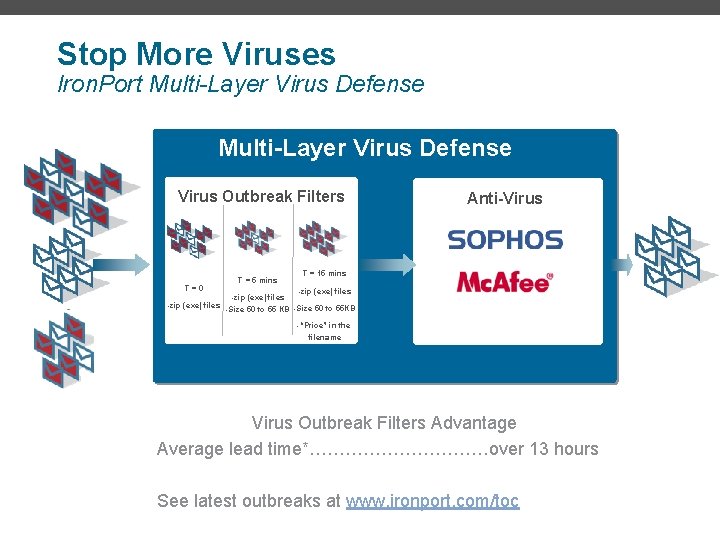
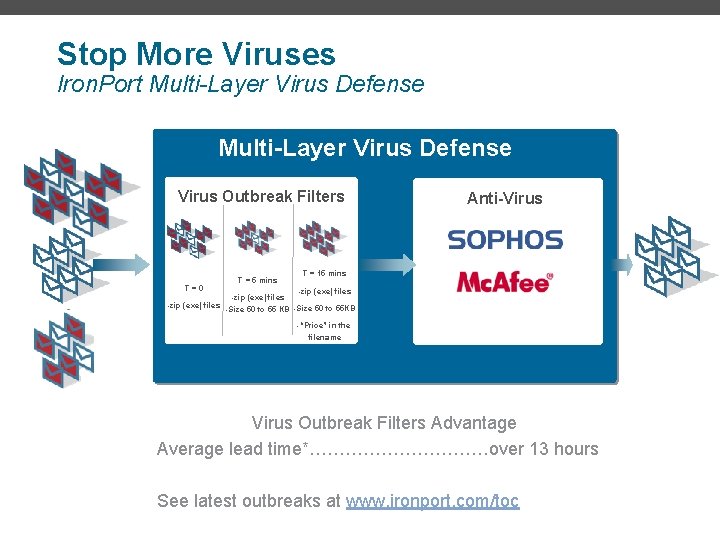
Stop More Viruses Iron. Port Multi-Layer Virus Defense Virus Outbreak Filters T=0 -zip (exe) files T = 5 mins Anti-Virus T = 15 mins -zip (exe) files -Size 50 to 55 KB -Size 50 to 55 KB -“Price” in the filename Virus Outbreak Filters Advantage Average lead time*……………over 13 hours See latest outbreaks at www. ironport. com/toc
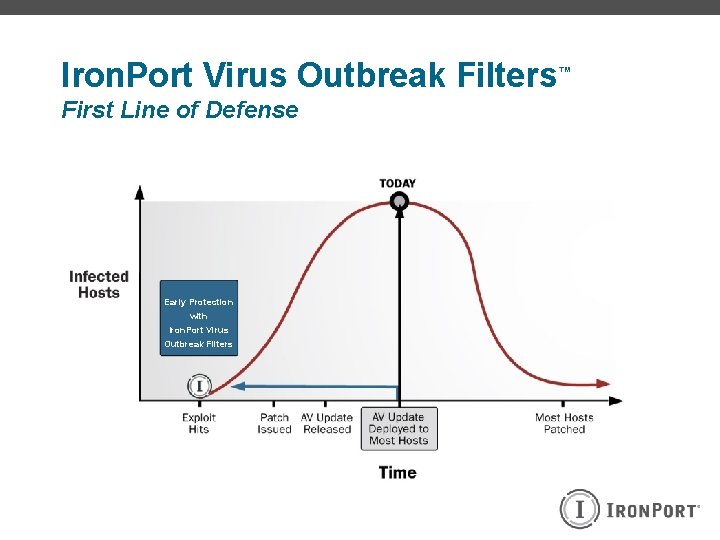
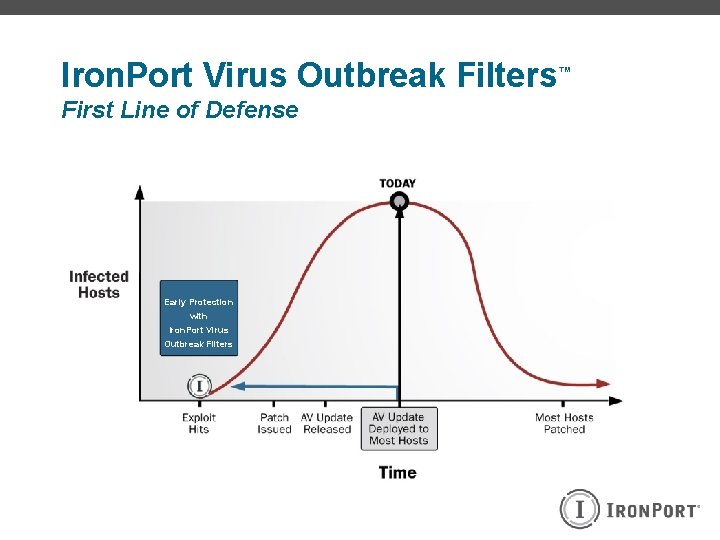
Iron. Port Virus Outbreak Filters First Line of Defense Early Protection with Iron. Port Virus Outbreak Filters ™
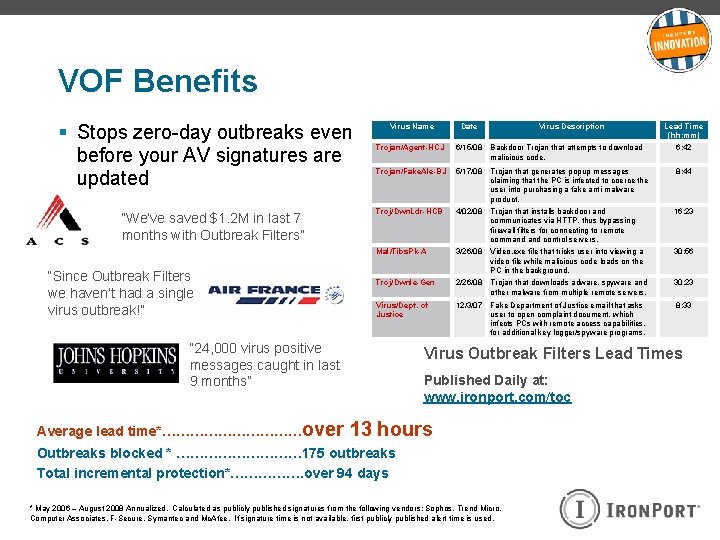
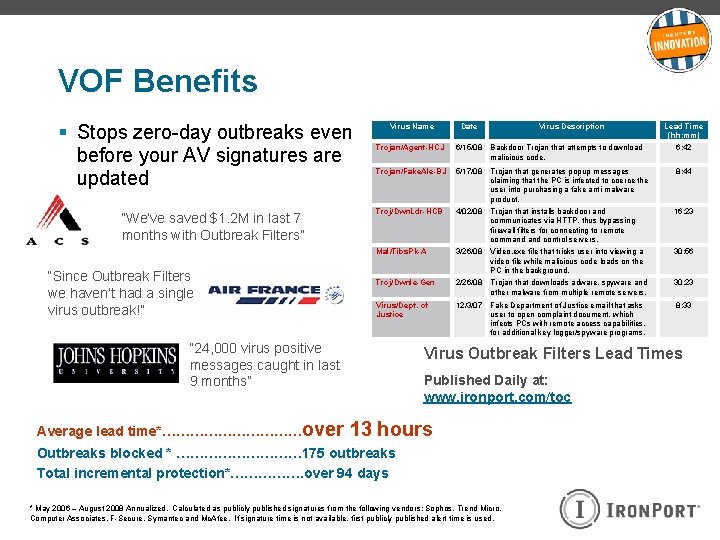
VOF Benefits § Stops zero-day outbreaks even before your AV signatures are updated “We’ve saved $1. 2 M in last 7 months with Outbreak Filters” “Since Outbreak Filters we haven’t had a single virus outbreak!” Virus Name Lead Time (hh: mm) 6/15/08 Backdoor Trojan that attempts to download malicious code. 6: 42 Trojan/Fake. Ale-BJ 5/17/08 Trojan that generates popup messages claiming that the PC is infected to coerce the user into purchasing a fake anti-malware product. 8: 44 Troj/Dwn. Ldr-HCB 4/02/08 Trojan that installs backdoor and communicates via HTTP, thus bypassing firewall filters for connecting to remote command control servers. 16: 23 Mal/Tibs. Pk-A 3/26/08 Video. exe file that tricks user into viewing a video file while malicious code loads on the PC in the background. 30: 56 Troj/Dwnle-Gen 2/26/08 Trojan that downloads adware, spyware and other malware from multiple remote servers. 30: 23 Virus/Dept. of Justice 12/3/07 Fake Department of Justice email that asks user to open complaint document, which infects PCs with remote access capabilities, for additional key logger/spyware programs. 8: 33 Virus Outbreak Filters Lead Times Published Daily at: www. ironport. com/toc 13 hours Outbreaks blocked * …………… 175 outbreaks Total incremental protection*……………. over 94 days VOF Virus Description Trojan/Agent-HCJ “ 24, 000 virus positive messages caught in last 9 months” Average lead time*……………over Date * May 2006 – August 2008 Annualized. Calculated as publicly published signatures from the following vendors: Sophos, Trend Micro, Computer Associates, F-Secure, Symantec and Mc. Afee. If signature time is not available, first publicly published alert time is used.
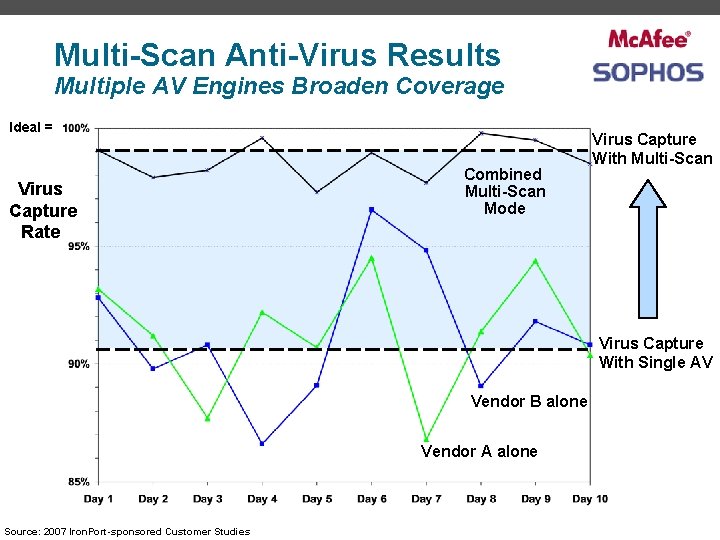
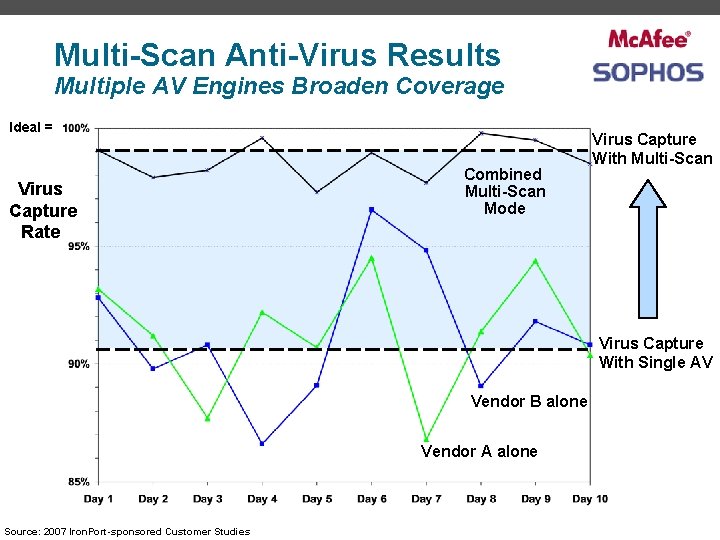
Multi-Scan Anti-Virus Results Multiple AV Engines Broaden Coverage Ideal = Virus Capture Rate Combined Multi-Scan Mode Virus Capture With Multi-Scan Virus Capture With Single AV Vendor B alone Vendor A alone Source: 2007 Iron. Port-sponsored Customer Studies
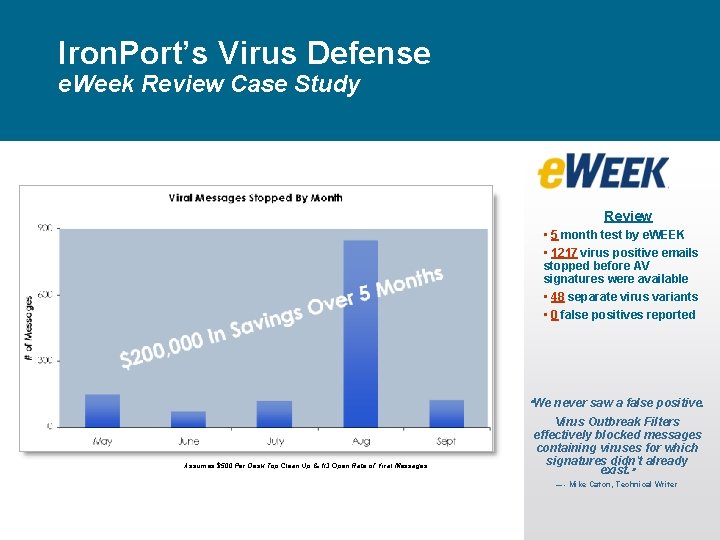
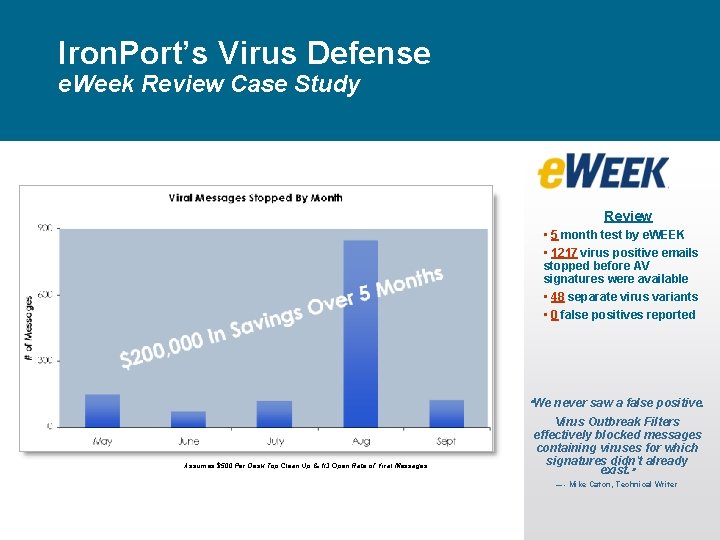
Iron. Port’s Virus Defense e. Week Review Case Study Review The In 0 0 , 0 0 5 5 $ d “We’ve Save hs With VOF” Last 6 Mont • 5 month test by e. WEEK • 1217 virus positive emails stopped before AV signatures were available • 48 separate virus variants • 0 false positives reported “We never saw a false positive. Assumes $500 Per Desk Top Clean Up & 1/3 Open Rate of Viral Messages Virus Outbreak Filters effectively blocked messages containing viruses for which signatures didn't already exist. ” — - Mike Caton, Technical Writer
Iron. Port Systems Data Loss Prevention PROTECTING SENSITIVE COMMMUNICATIONS
Email Challenges Standard Email STILL Does Not Offer What’s Needed Privacy & Control Junk Mail Viruses Regulations
Data leaks continue to impact Businesses
Intellectual Property Leakage § Estimated $300 billion per year in losses § IP theft laws are hit and miss internationally § Surveyed organizations estimated 2. 4 incidents per year at $500 k per incident § Appearance of “whistle-blower” public wiki’s.
Protect Sensitive Data: It’s the Law § Breach Laws (e. g. California SB 1386) Enacted in 44 states Companies forced to disclose any personal information leakage § State Encryption Laws Personal Information to be encrypted as it goes over the Internet § Healthcare Laws (e. g. HIPAA) Protect Patient information or pay large penalties § Financial Regulations Protect Credit Card Information (PCI) Don’t disclose financial information (SOX)
Historical Barriers to DLP Adoption § Inaccurate False Positives & False Negatives Constant Tuning Required § Difficult to Configure Complex Integration Limited Policy Coverage § Expensive High Up Front Deployment Cost Resource Intensive
Iron. Port DLP: Comprehensive, Accurate, Easy Comprehensive Worldwide regulatory compliance coverage, numerous remediation options Accurate Easy No managing false positives Quickly deploy and manage
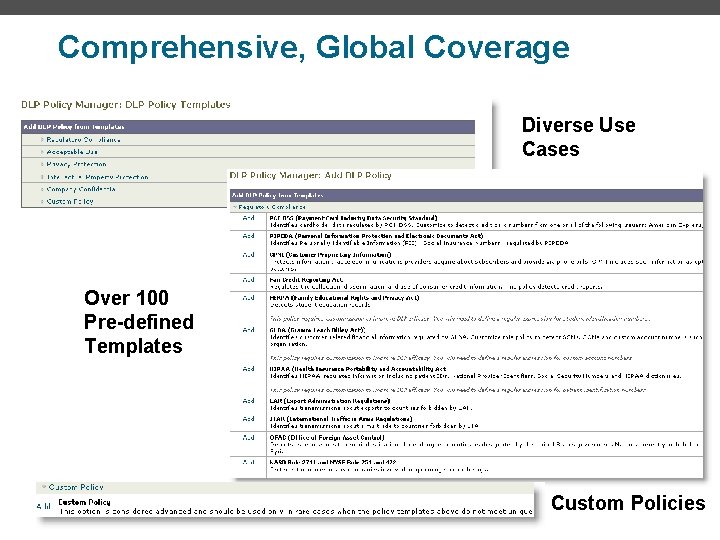
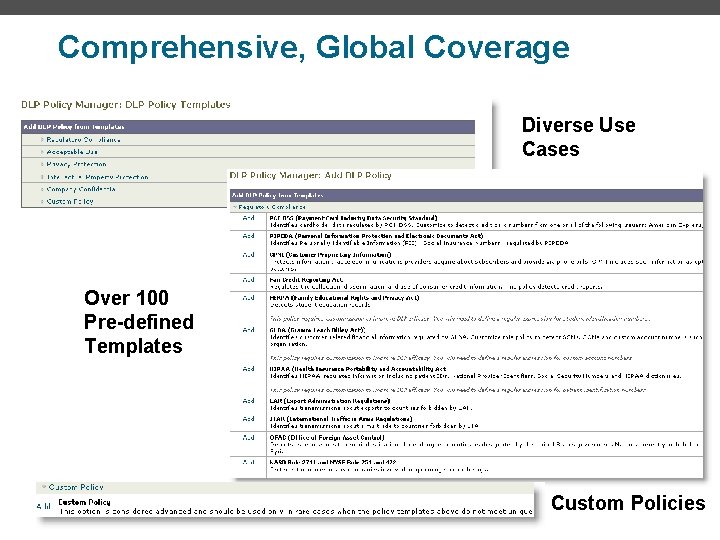
Comprehensive, Global Coverage Diverse Use Cases Over 100 Pre-defined Templates Custom Policies
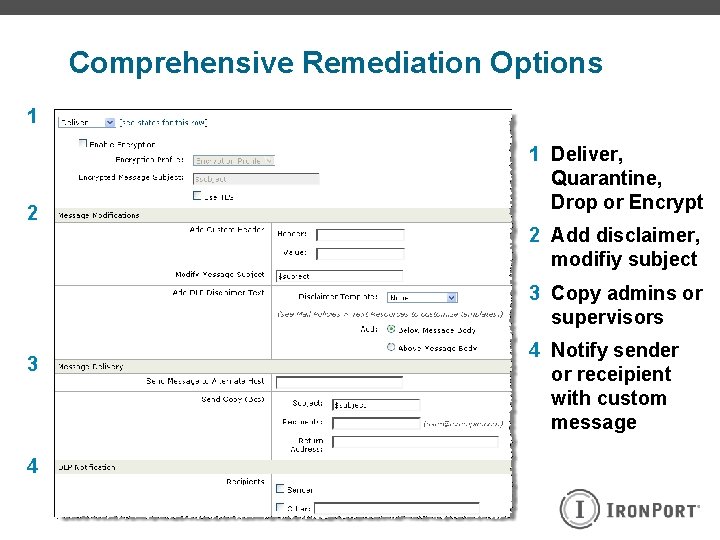
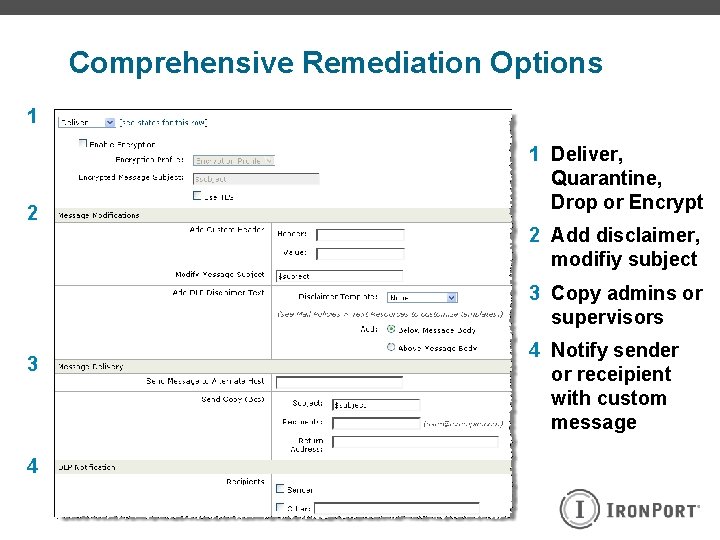
Comprehensive Remediation Options 1 2 1 Deliver, Quarantine, Drop or Encrypt 2 Add disclaimer, modifiy subject 3 Copy admins or supervisors 3 4 4 Notify sender or receipient with custom message
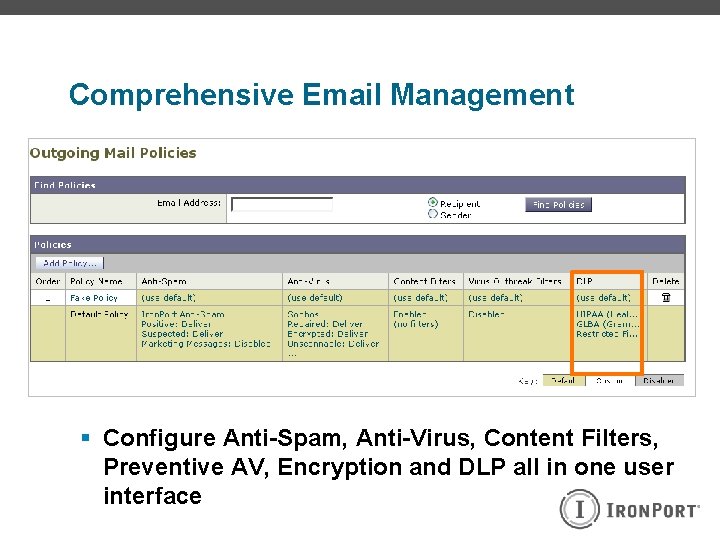
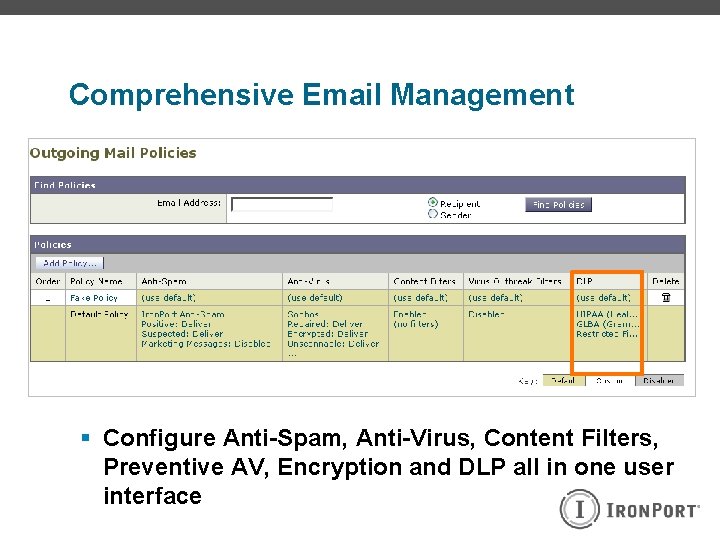
Comprehensive Email Management § Configure Anti-Spam, Anti-Virus, Content Filters, Preventive AV, Encryption and DLP all in one user interface
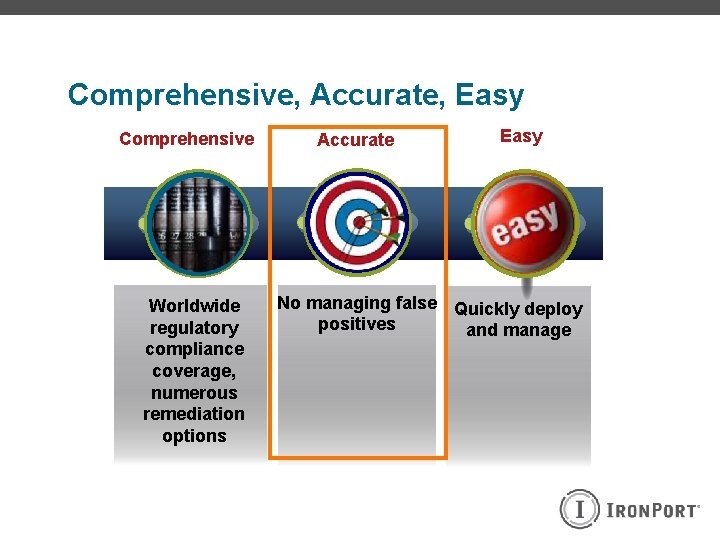
Comprehensive, Accurate, Easy Comprehensive Worldwide regulatory compliance coverage, numerous remediation options Accurate Easy No managing false Quickly deploy positives and manage

RSA – Market & Technology Leader § Ranked as “Leader” in Gartner Magic Quadrant § Focus on accuracy: large research team staffed specifically to write and refine content polices “RSA has strong described content capabilities enabled by a formal knowledge-engineering process” - Gartner
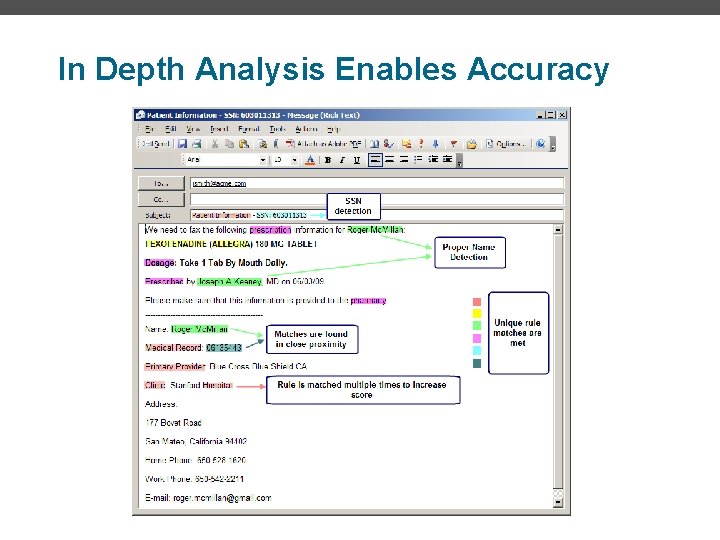
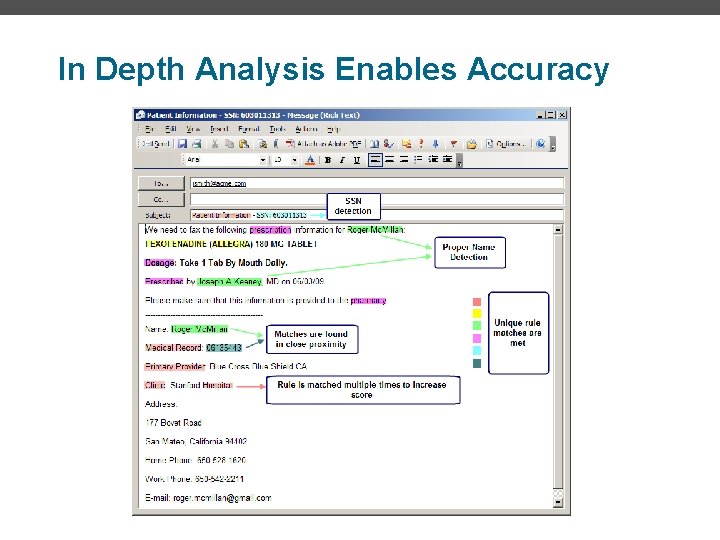
In Depth Analysis Enables Accuracy

Comprehensive, Accurate, Easy Comprehensive Worldwide regulatory compliance coverage, numerous remediation options Accurate Easy No managing false Quickly deploy positives and manage
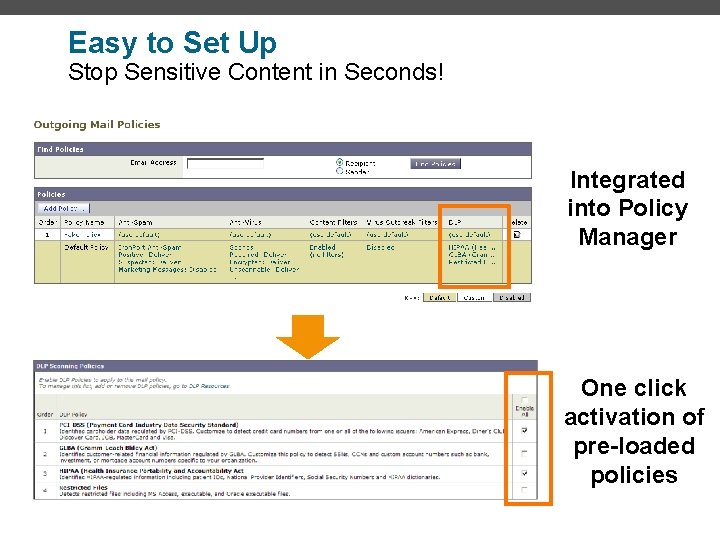
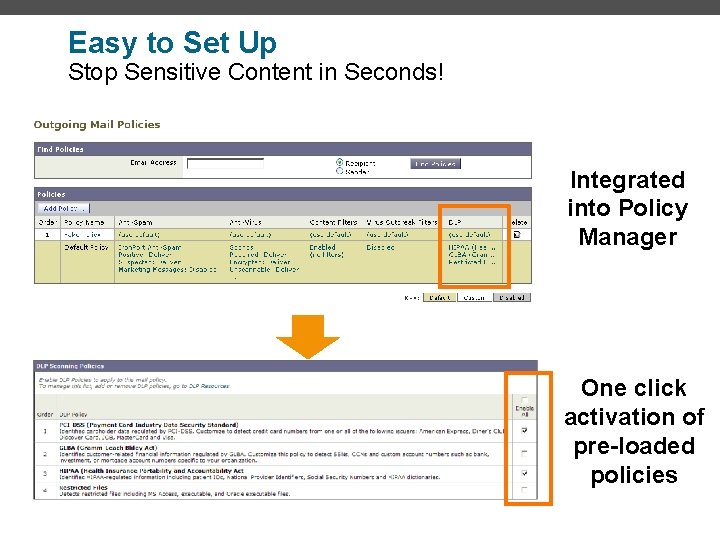
Easy to Set Up Stop Sensitive Content in Seconds! Integrated into Policy Manager One click activation of pre-loaded policies
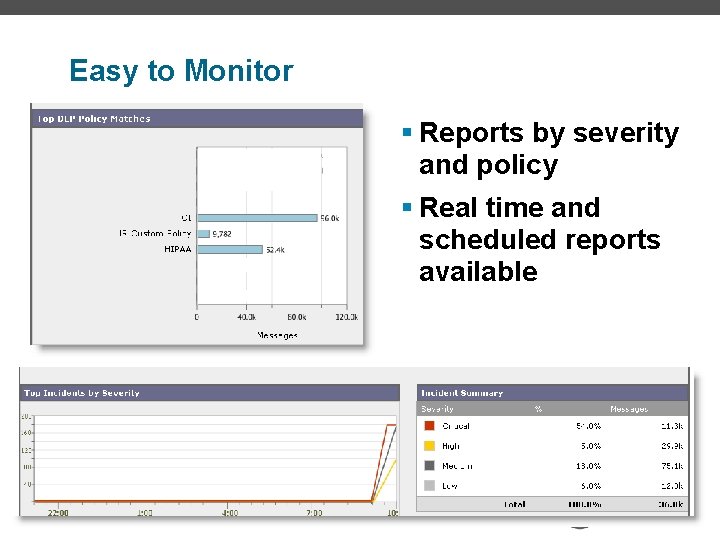
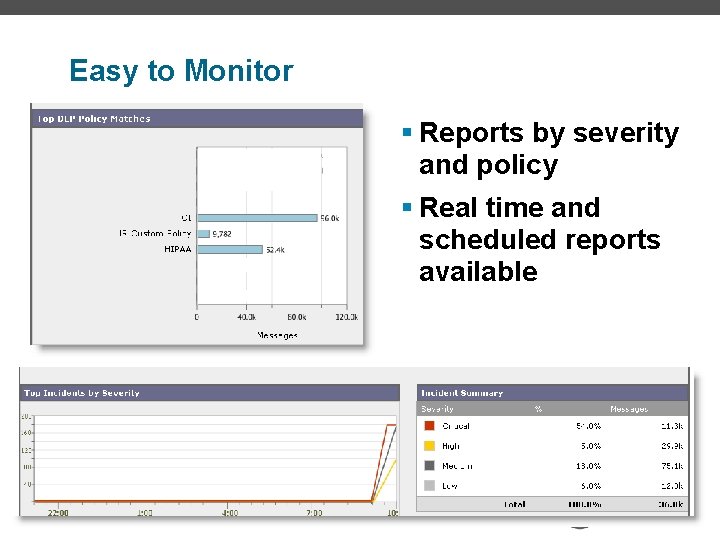
Easy to Monitor § Reports by severity and policy § Real time and scheduled reports available
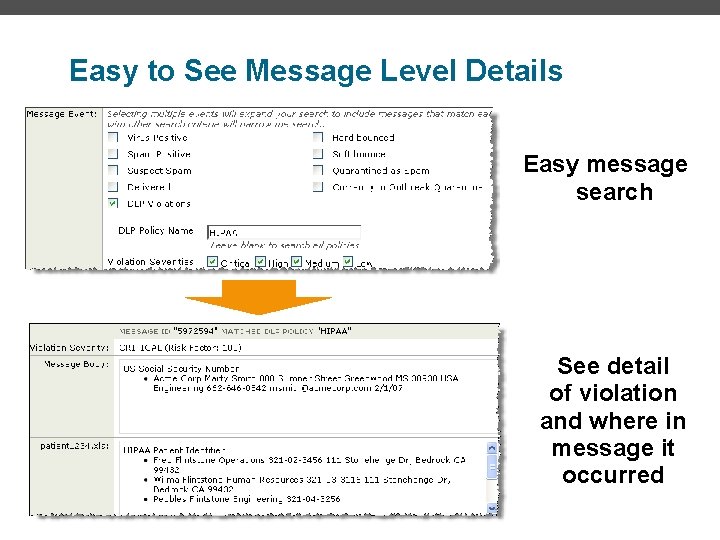
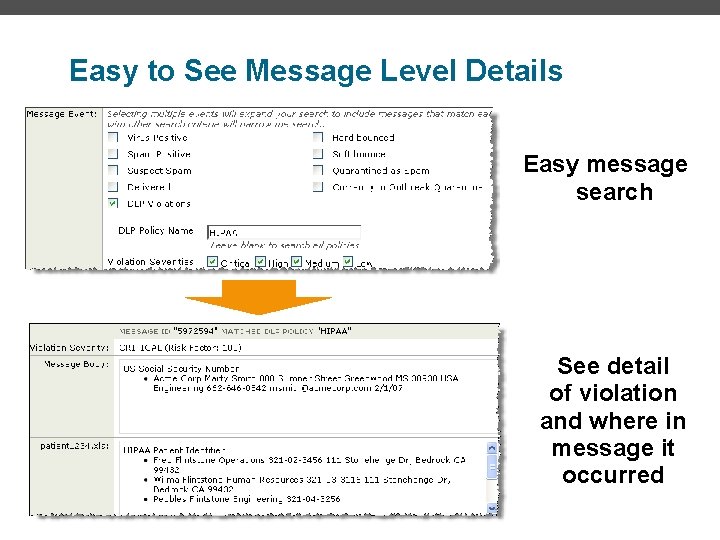
Easy to See Message Level Details Easy message search See detail of violation and where in message it occurred
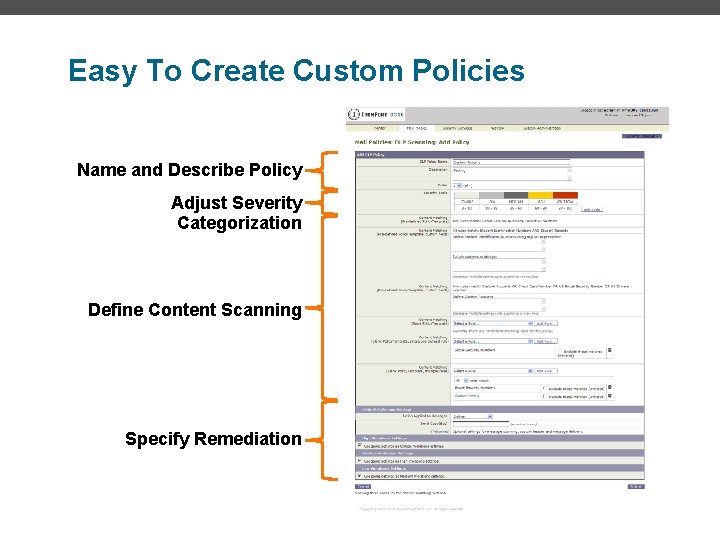
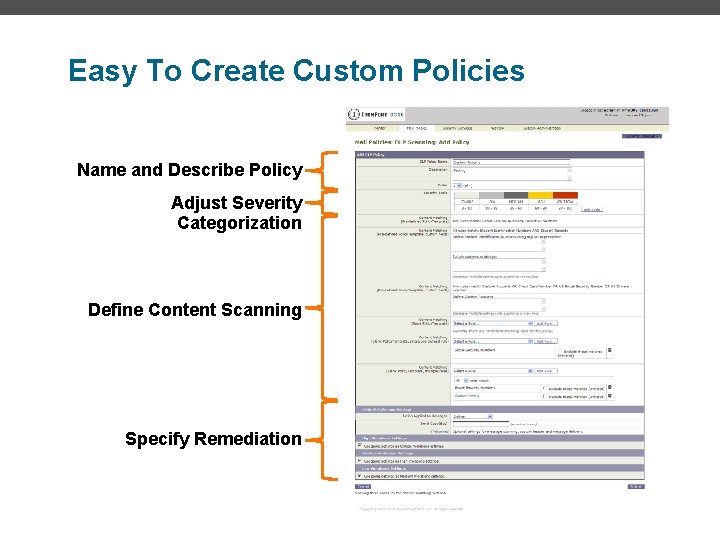
Easy To Create Custom Policies Name and Describe Policy Adjust Severity Categorization Define Content Scanning Specify Remediation
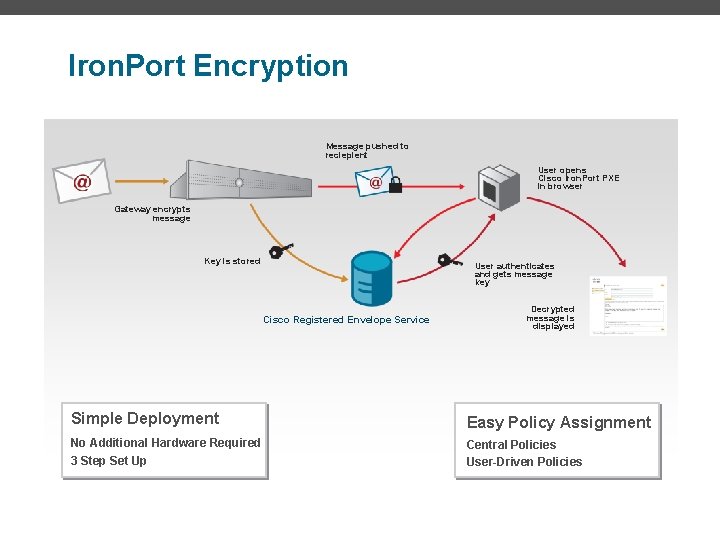
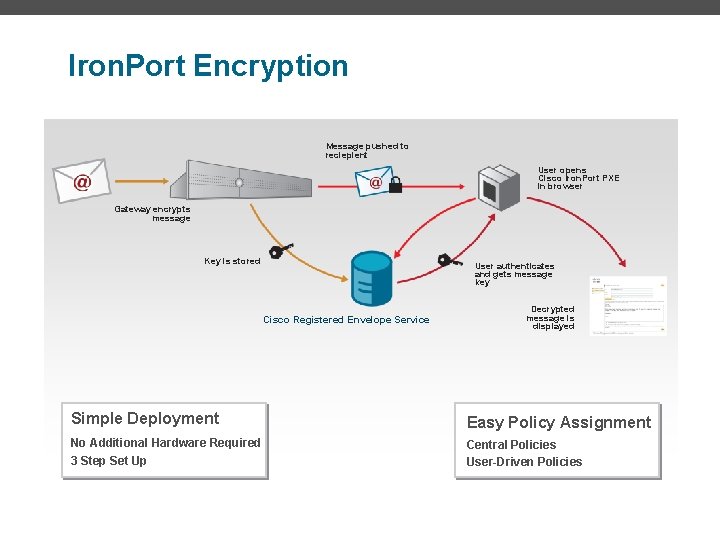
Iron. Port Encryption Message pushed to reciepient User opens Cisco Iron. Port PXE in browser Gateway encrypts message Key is stored User authenticates and gets message key Cisco Registered Envelope Service Decrypted message is displayed Simple Deployment Easy Policy Assignment No Additional Hardware Required Central Policies User-Driven Policies 3 Step Set Up
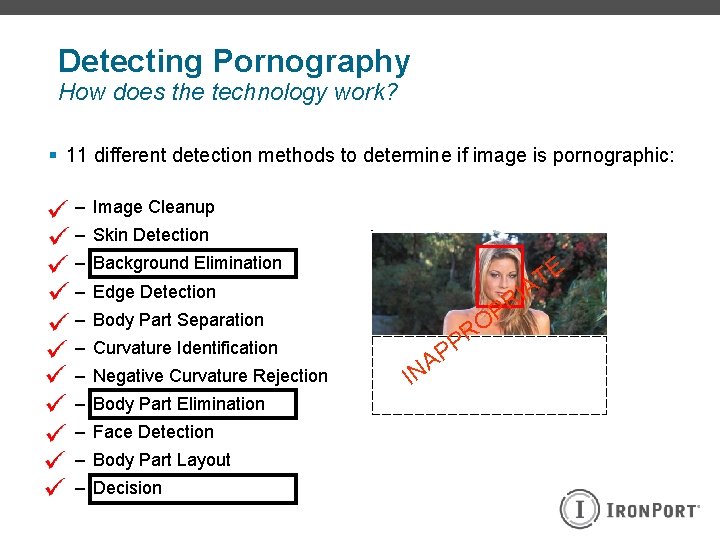
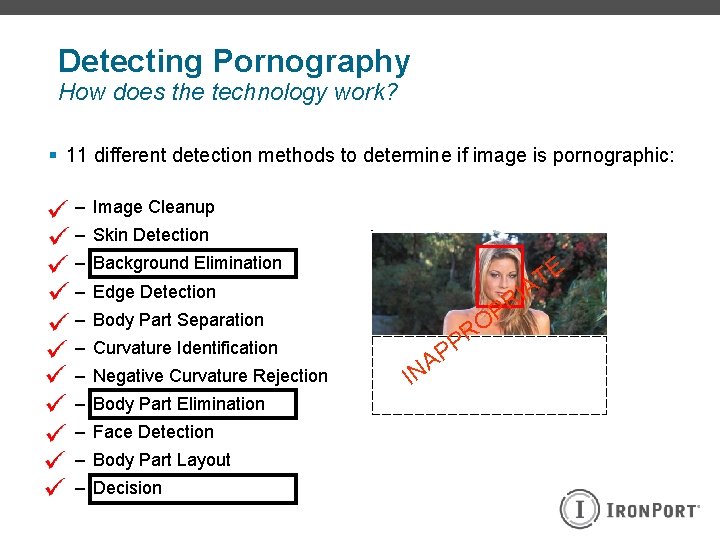
Detecting Pornography How does the technology work? § 11 different detection methods to determine if image is pornographic: – Image Cleanup – Skin Detection – Background Elimination E T A RI – Edge Detection P O PR – Body Part Separation – Curvature Identification – Negative Curvature Rejection – Body Part Elimination – Face Detection – Body Part Layout – Decision I P A N
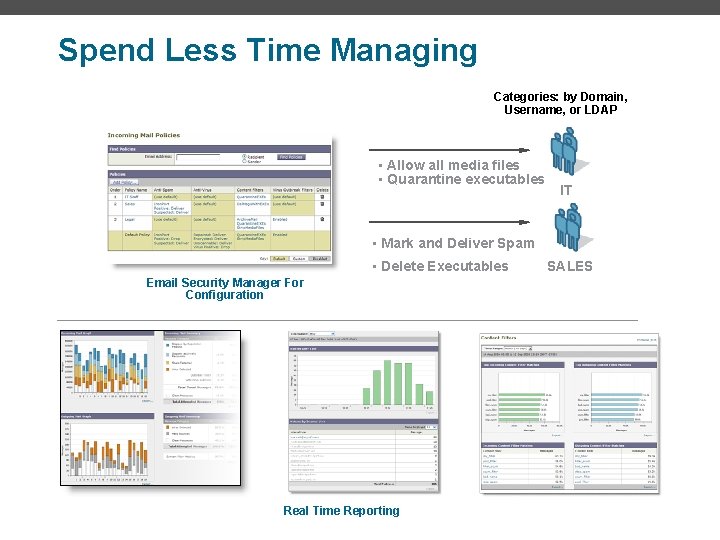
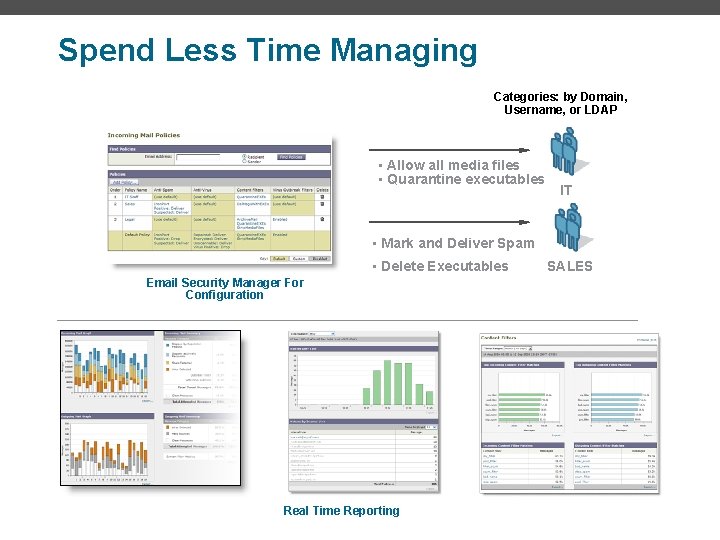
Spend Less Time Managing Categories: by Domain, Username, or LDAP • Allow all media files • Quarantine executables IT • Mark and Deliver Spam • Delete Executables Email Security Manager For Configuration Real Time Reporting SALES
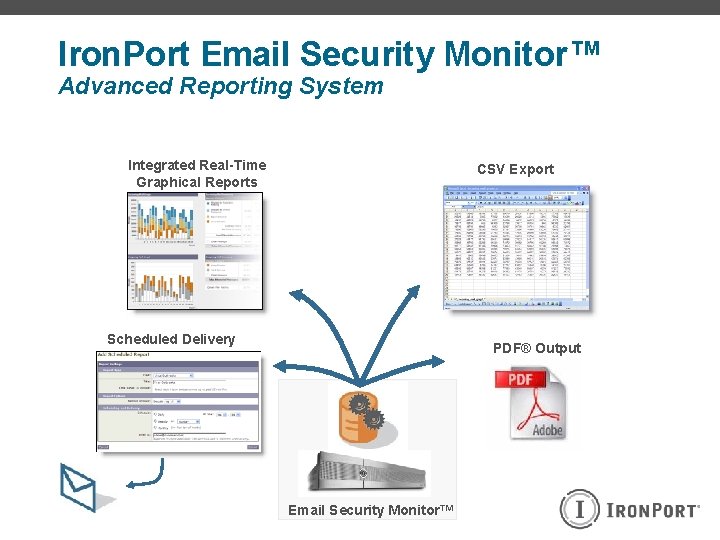
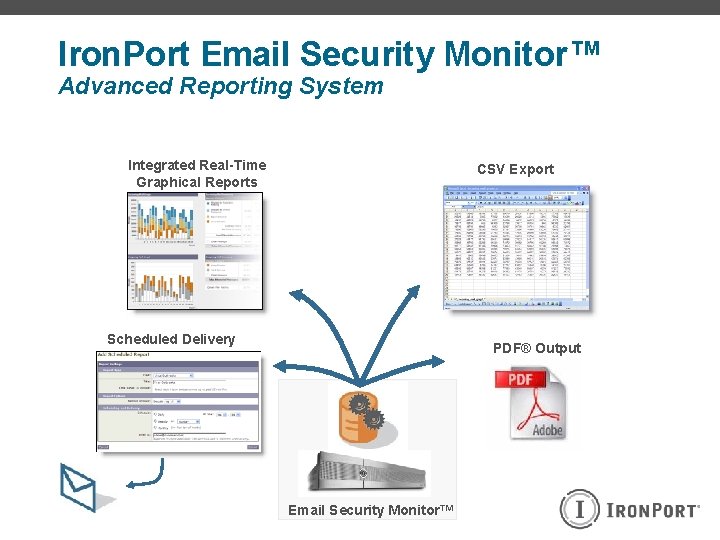
Iron. Port Email Security Monitor™ Advanced Reporting System Integrated Real-Time Graphical Reports CSV Export Scheduled Delivery PDF® Output Email Security Monitor™
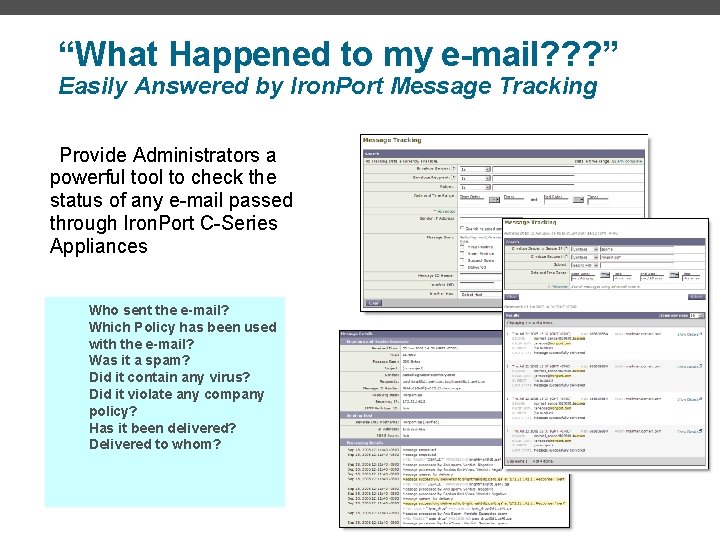
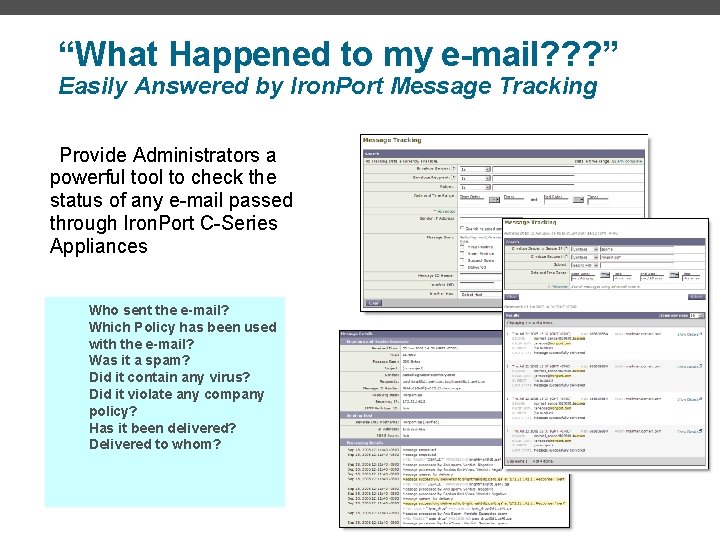
“What Happened to my e-mail? ? ? ” Easily Answered by Iron. Port Message Tracking Provide Administrators a powerful tool to check the status of any e-mail passed through Iron. Port C-Series Appliances Who sent the e-mail? Which Policy has been used with the e-mail? Was it a spam? Did it contain any virus? Did it violate any company policy? Has it been delivered? Delivered to whom?
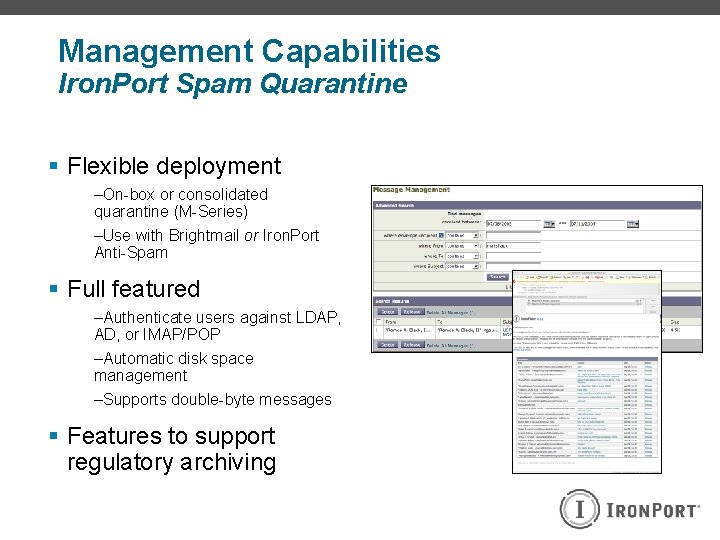
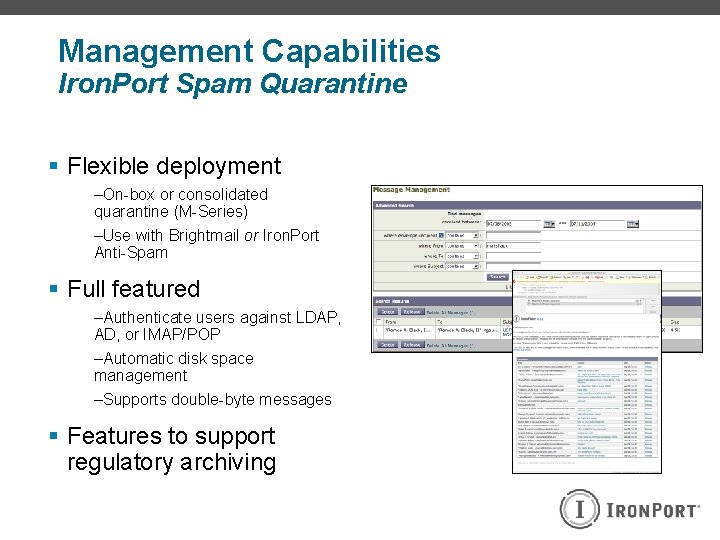
Management Capabilities Iron. Port Spam Quarantine § Flexible deployment –On-box or consolidated quarantine (M-Series) –Use with Brightmail or Iron. Port Anti-Spam § Full featured –Authenticate users against LDAP, AD, or IMAP/POP –Automatic disk space management –Supports double-byte messages § Features to support regulatory archiving
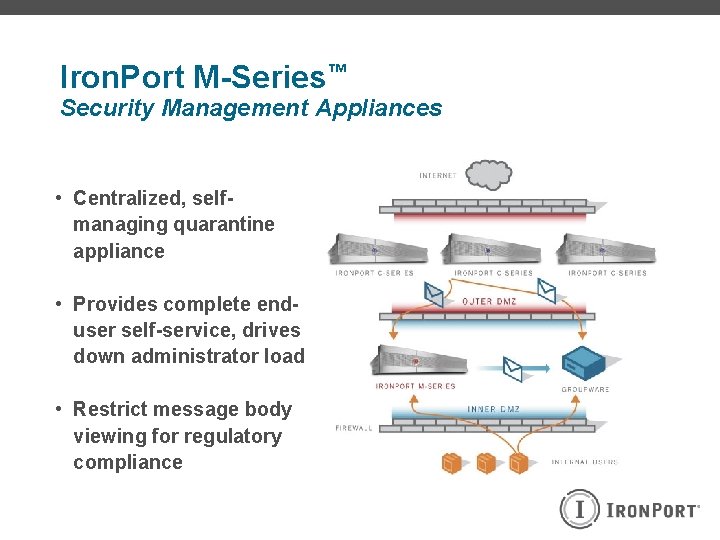
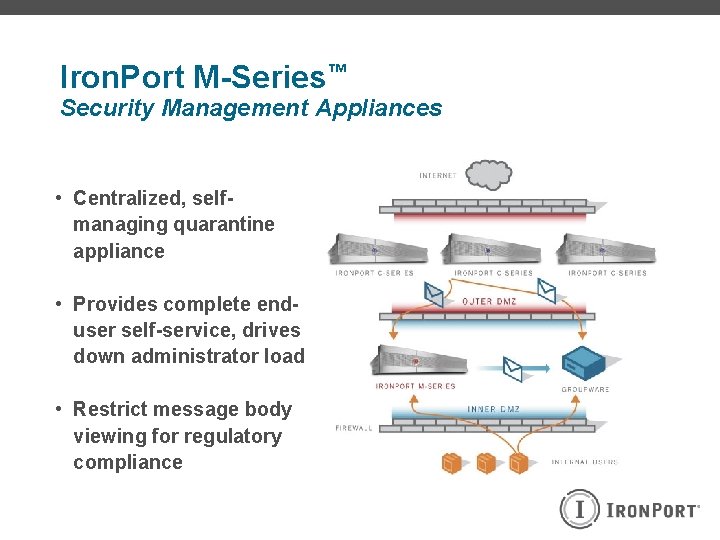
Iron. Port M-Series™ Security Management Appliances • Centralized, selfmanaging quarantine appliance • Provides complete enduser self-service, drives down administrator load • Restrict message body viewing for regulatory compliance
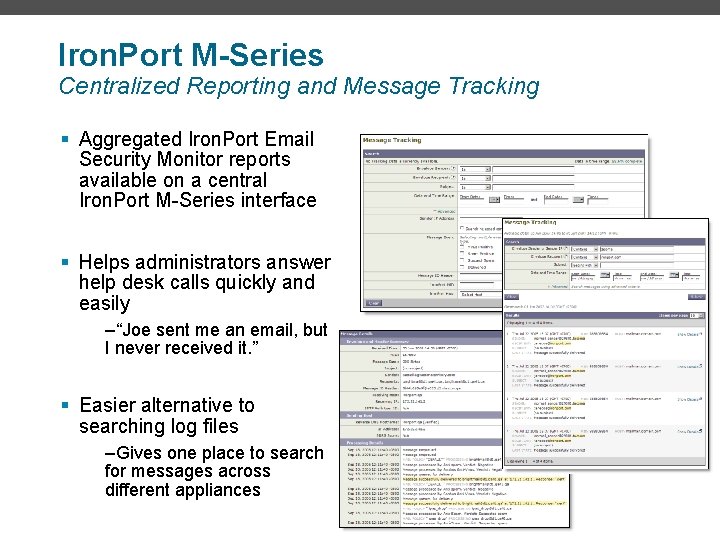
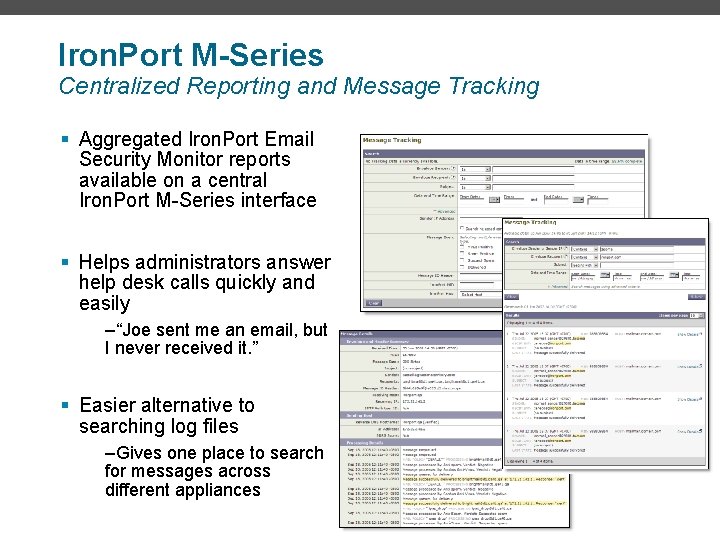
Iron. Port M-Series Centralized Reporting and Message Tracking § Aggregated Iron. Port Email Security Monitor reports available on a central Iron. Port M-Series interface § Helps administrators answer help desk calls quickly and easily –“Joe sent me an email, but I never received it. ” § Easier alternative to searching log files –Gives one place to search for messages across different appliances
Thai Military Bank Challenge: The existing system can’t keep up with new threats like spam, viruses, phishing, etc. Use ISP gateway as the first line of defenses (Barracuda) Reliability for both inbound and outbound The Iron. Port solution: Powerful, first line of defense for Lotus Notes Block over 75% of the emails that Barracuda couldn’t catch. LDAP integration with Lotus Note LDAP capability Reports for security audits. Manageability, scalability, and reliability
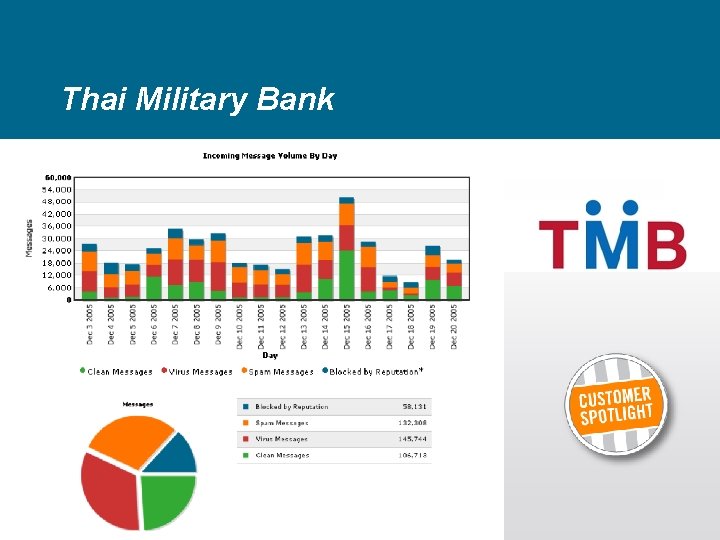
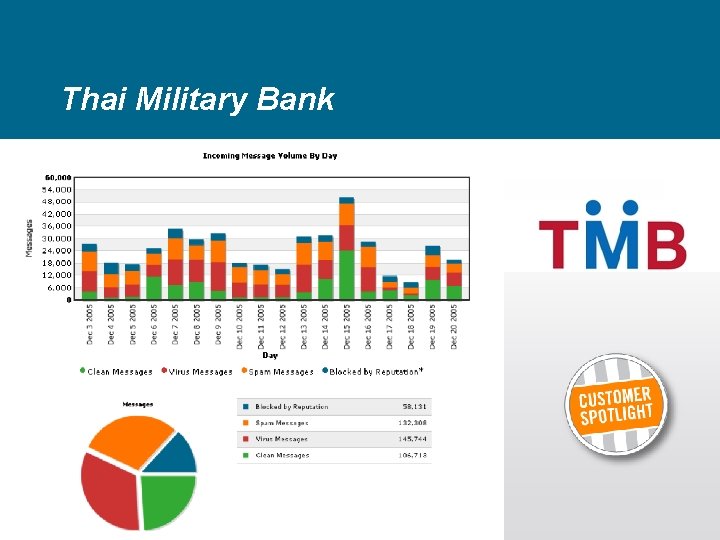
Thai Military Bank

Iron. Port Customer Snapshot Over 95% of Our Customers Use Iron. Port to Define Acceptable Use Policies Regulated Industries Financial Health Care Retail All-Comers
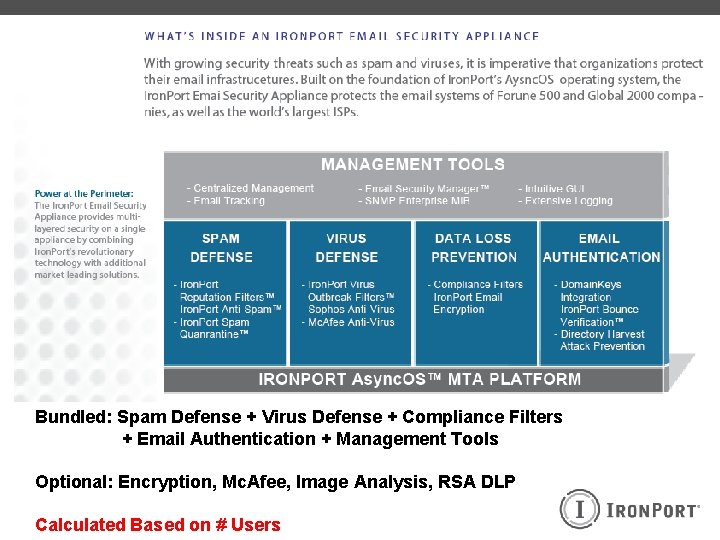
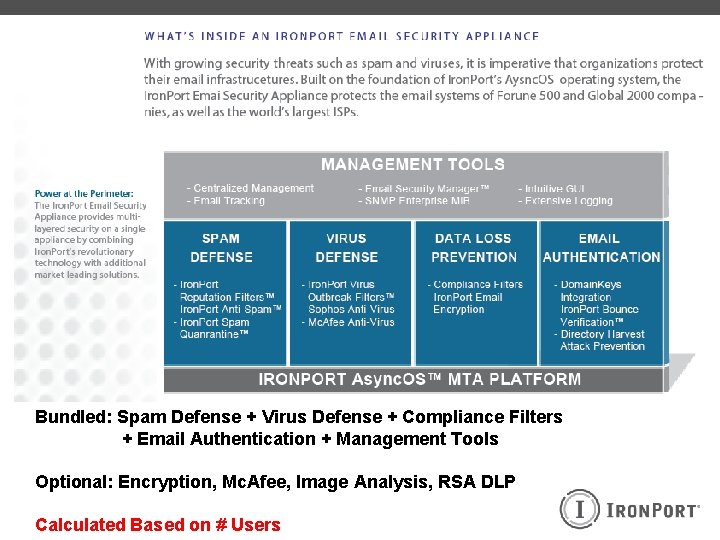
Bundled: Spam Defense + Virus Defense + Compliance Filters + Email Authentication + Management Tools Optional: Encryption, Mc. Afee, Image Analysis, RSA DLP Calculated Based on # Users
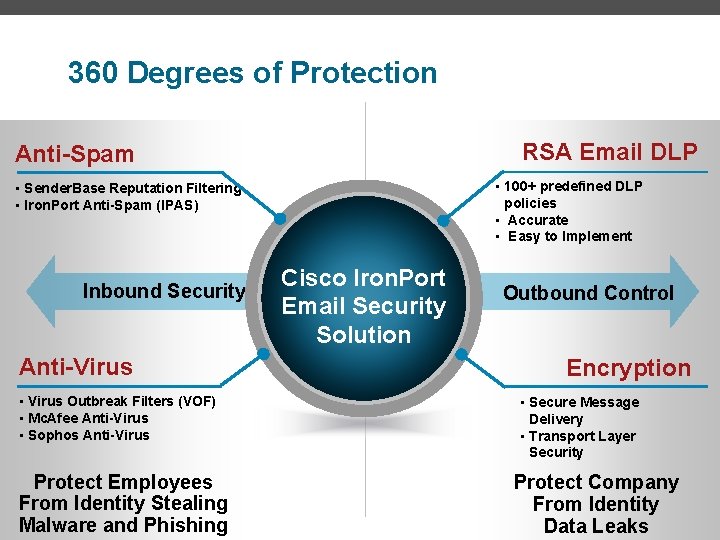
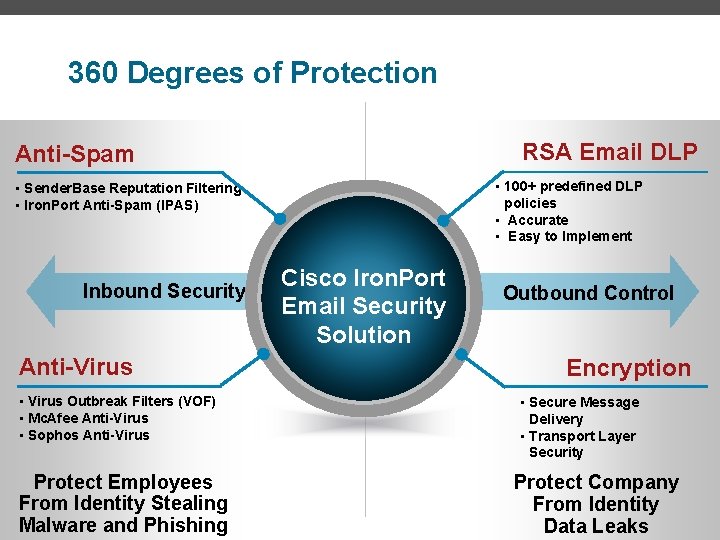
360 Degrees of Protection RSA Email DLP Anti-Spam • 100+ predefined DLP policies • Accurate • Easy to Implement • Sender. Base Reputation Filtering • Iron. Port Anti-Spam (IPAS) Inbound Security Anti-Virus • Virus Outbreak Filters (VOF) • Mc. Afee Anti-Virus • Sophos Anti-Virus Protect Employees From Identity Stealing Malware and Phishing Cisco Iron. Port Email Security Solution Outbound Control Encryption • Secure Message Delivery • Transport Layer Security Protect Company From Identity Data Leaks

Q&A