IPv 6 Transition Why a new security mechanisms

- Slides: 19
IPv 6 Transition : Why a new security mechanisms model is necessary? Abidah Hj Mat Taib abidah@perlis. uitm. edu. my abidah@nav 6. org Universiti Teknologi Mara, Perlis Malaysia
Outline l l l l Transition / coexistence Security Threats due to Transition Mechanisms Current Security Mechanisms Current IPv 4 Security Model New Security Model Conclusion
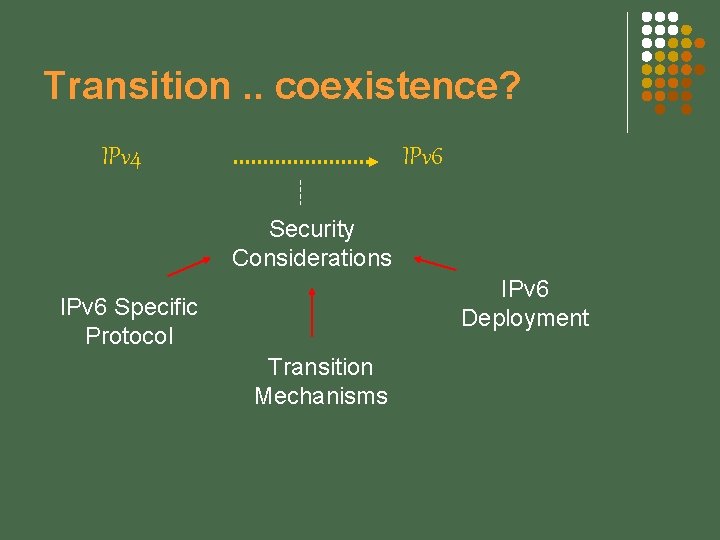
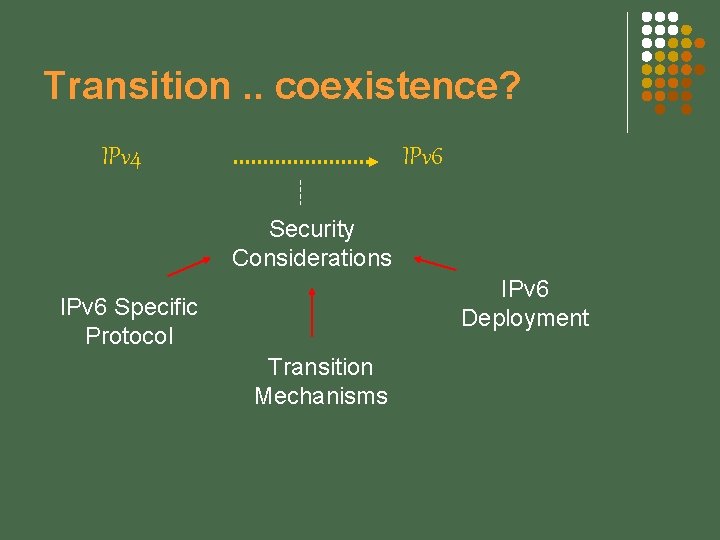
Transition. . coexistence? IPv 4 IPv 6 Security Considerations IPv 6 Deployment IPv 6 Specific Protocol Transition Mechanisms
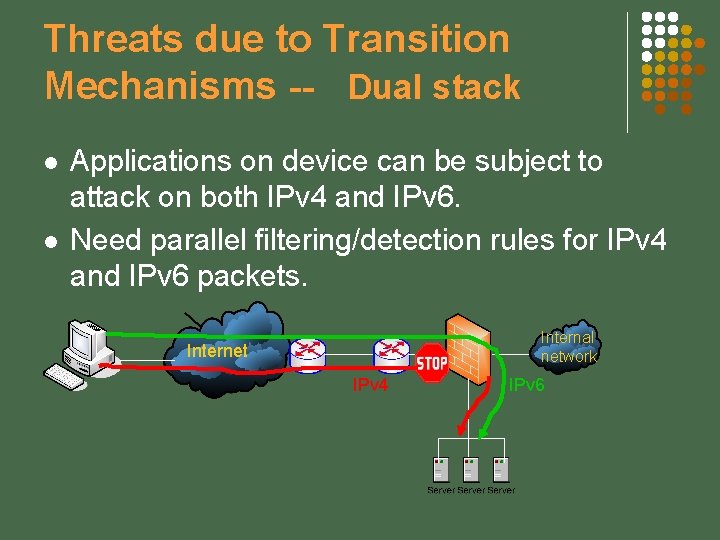
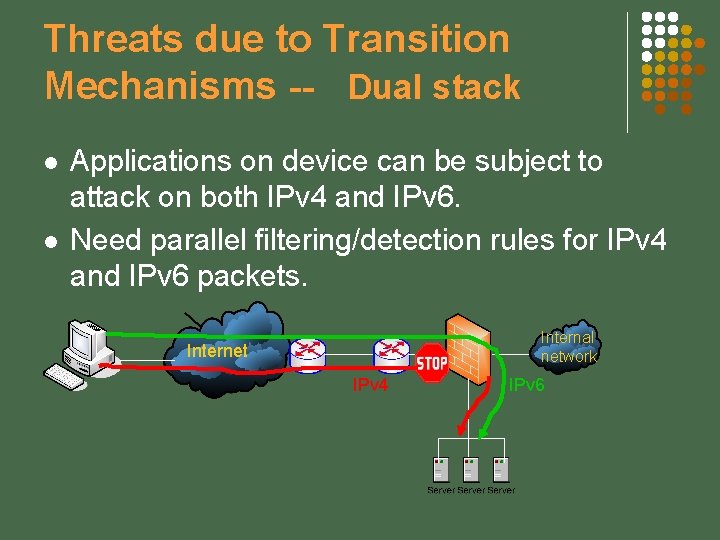
Threats due to Transition Mechanisms -- Dual stack l l Applications on device can be subject to attack on both IPv 4 and IPv 6. Need parallel filtering/detection rules for IPv 4 and IPv 6 packets. Internal network Internet IPv 4 IPv 6
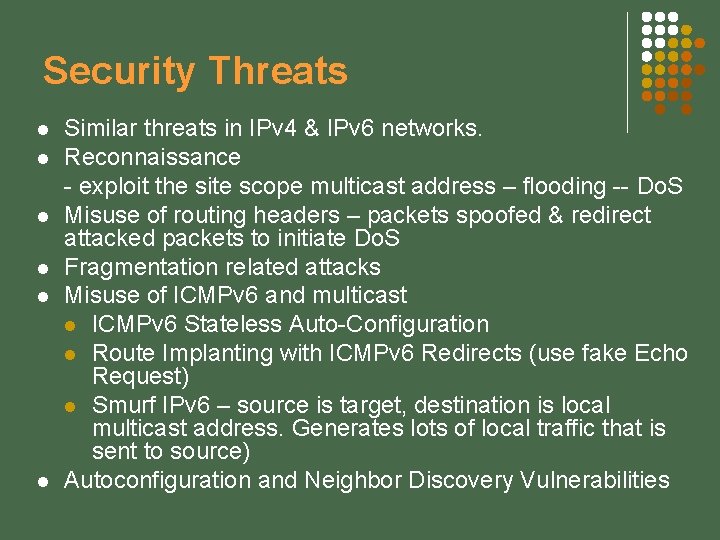
Security Threats l l l Similar threats in IPv 4 & IPv 6 networks. Reconnaissance - exploit the site scope multicast address – flooding -- Do. S Misuse of routing headers – packets spoofed & redirect attacked packets to initiate Do. S Fragmentation related attacks Misuse of ICMPv 6 and multicast l ICMPv 6 Stateless Auto-Configuration l Route Implanting with ICMPv 6 Redirects (use fake Echo Request) l Smurf IPv 6 – source is target, destination is local multicast address. Generates lots of local traffic that is sent to source) Autoconfiguration and Neighbor Discovery Vulnerabilities
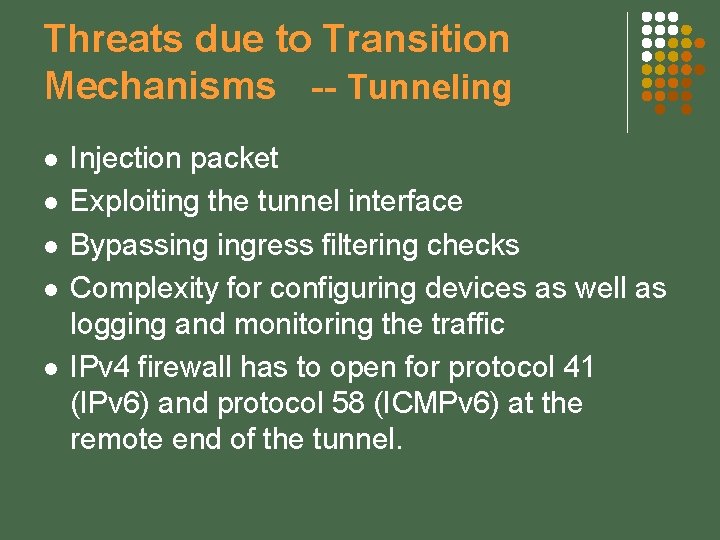
Threats due to Transition Mechanisms -- Tunneling l l l Injection packet Exploiting the tunnel interface Bypassing ingress filtering checks Complexity for configuring devices as well as logging and monitoring the traffic IPv 4 firewall has to open for protocol 41 (IPv 6) and protocol 58 (ICMPv 6) at the remote end of the tunnel.
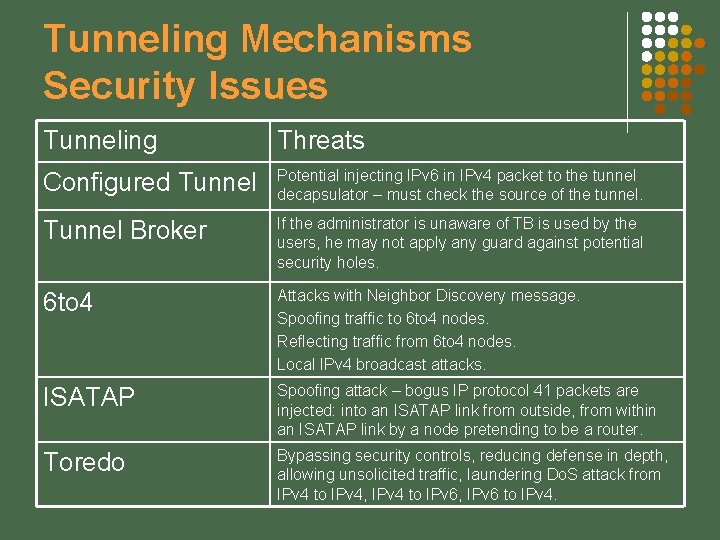
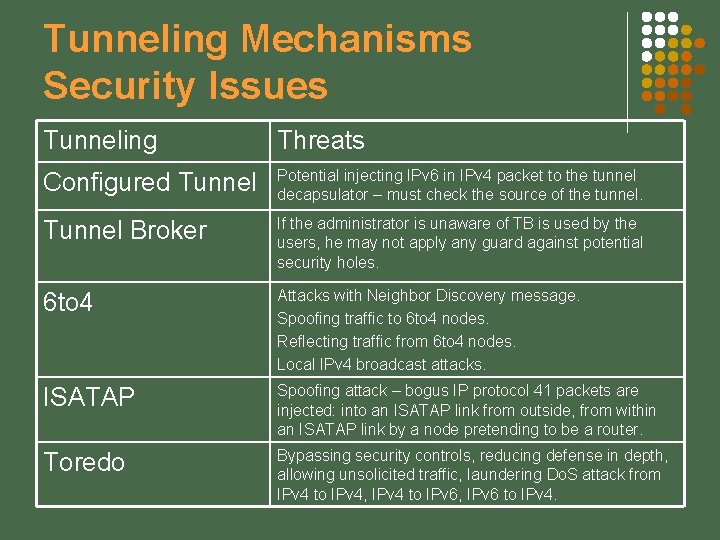
Tunneling Mechanisms Security Issues Tunneling Threats Configured Tunnel Potential injecting IPv 6 in IPv 4 packet to the tunnel decapsulator – must check the source of the tunnel. Tunnel Broker If the administrator is unaware of TB is used by the users, he may not apply any guard against potential security holes. 6 to 4 Attacks with Neighbor Discovery message. Spoofing traffic to 6 to 4 nodes. Reflecting traffic from 6 to 4 nodes. Local IPv 4 broadcast attacks. ISATAP Spoofing attack – bogus IP protocol 41 packets are injected: into an ISATAP link from outside, from within an ISATAP link by a node pretending to be a router. Toredo Bypassing security controls, reducing defense in depth, allowing unsolicited traffic, laundering Do. S attack from IPv 4 to IPv 4, IPv 4 to IPv 6, IPv 6 to IPv 4.
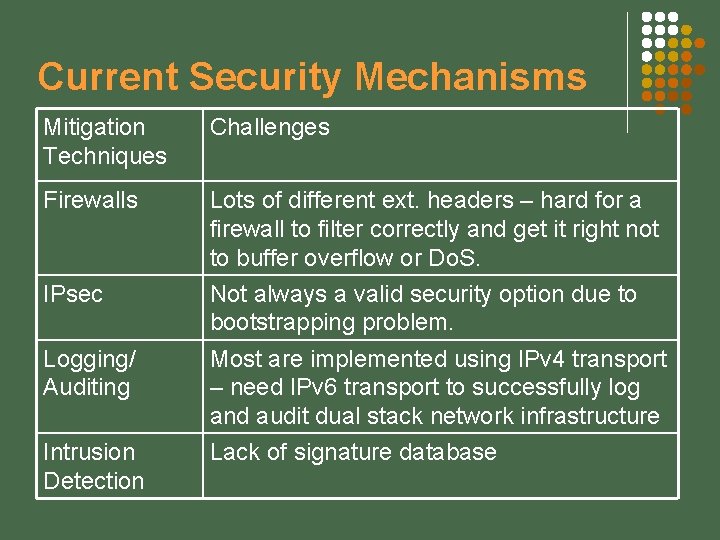
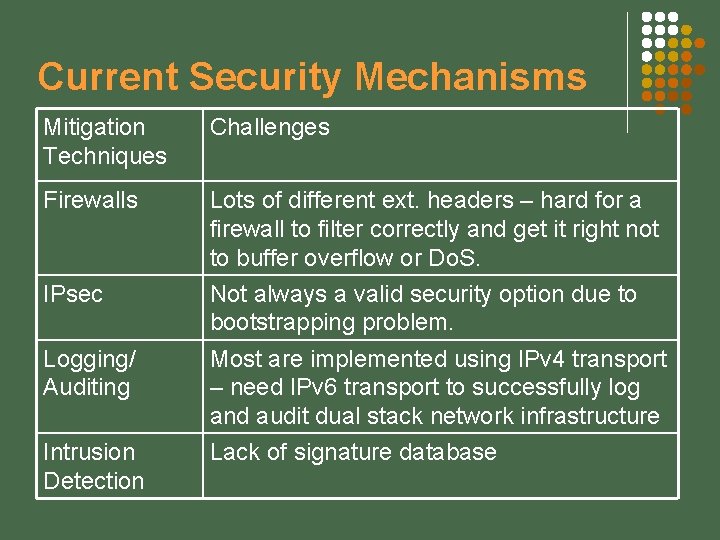
Current Security Mechanisms Mitigation Techniques Challenges Firewalls Lots of different ext. headers – hard for a firewall to filter correctly and get it right not to buffer overflow or Do. S. Not always a valid security option due to bootstrapping problem. IPsec Logging/ Auditing Most are implemented using IPv 4 transport – need IPv 6 transport to successfully log and audit dual stack network infrastructure Intrusion Detection Lack of signature database
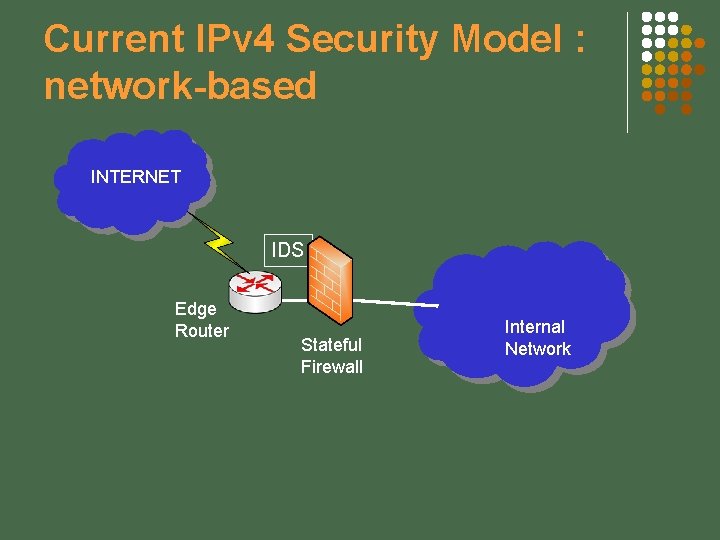
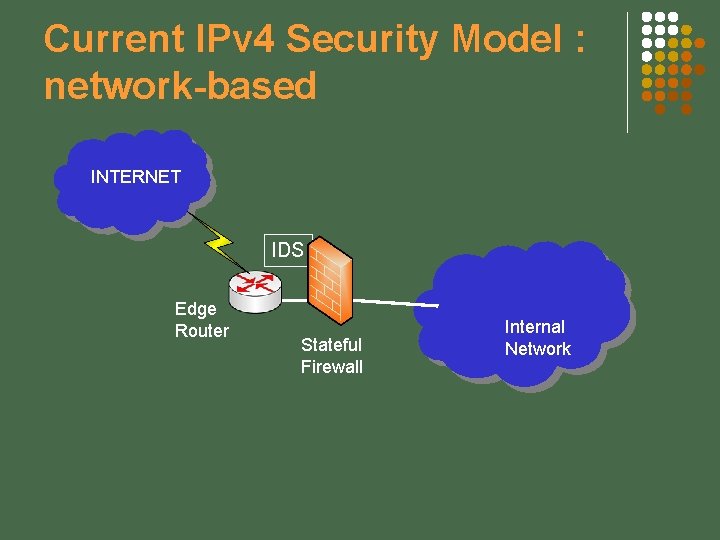
Current IPv 4 Security Model : network-based INTERNET IDS Edge Router Stateful Firewall Internal Network
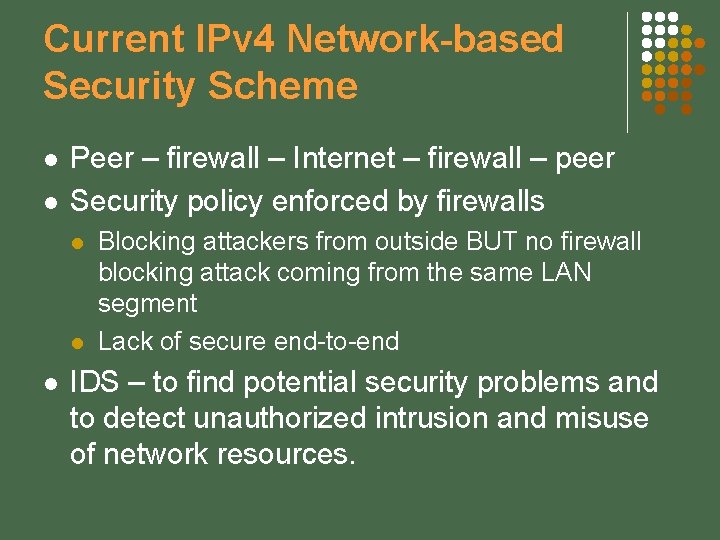
Current IPv 4 Network-based Security Scheme l l Peer – firewall – Internet – firewall – peer Security policy enforced by firewalls l l l Blocking attackers from outside BUT no firewall blocking attack coming from the same LAN segment Lack of secure end-to-end IDS – to find potential security problems and to detect unauthorized intrusion and misuse of network resources.
Current IPv 4 Network-based Security Scheme. . cont… l Perimeter defense IP firewalls, HTTP/HTTPS firewalls, content analysis: antivirus, anti spam, etc l Defense in depth and network segmentation l § l DMZ, layered architecture TLS/SSL based business application and VPNs for remote access
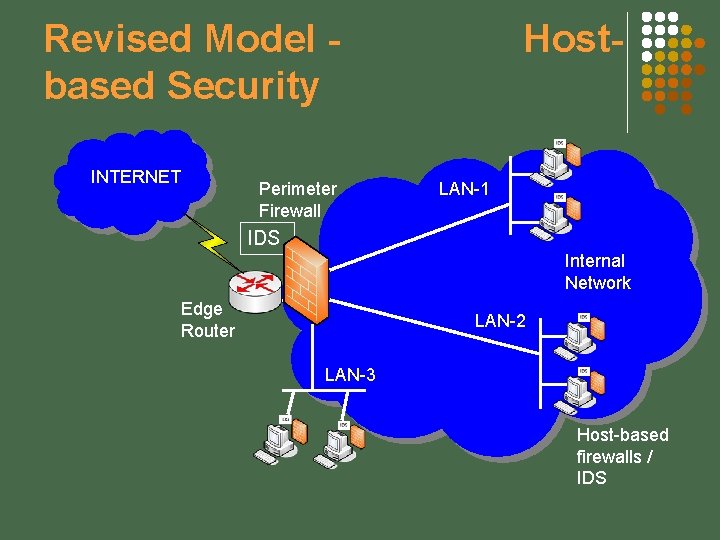
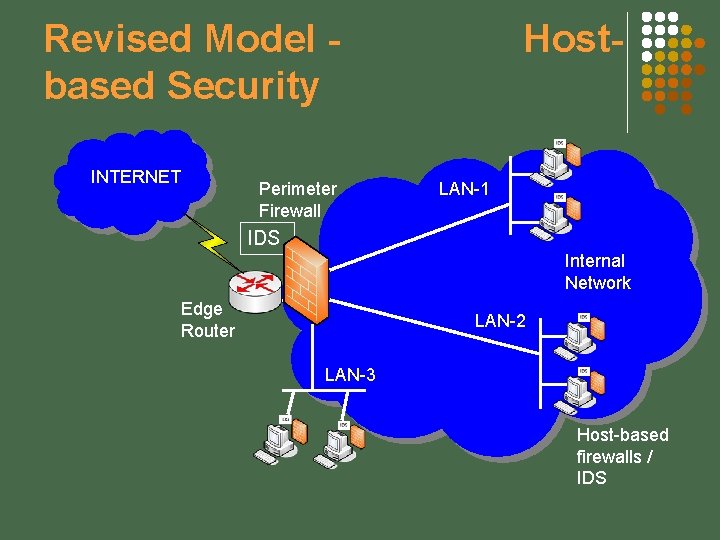
Revised Model based Security INTERNET Perimeter Firewall Host- LAN-1 IDS Internal Network Edge Router LAN-2 LAN-3 Host-based firewalls / IDS
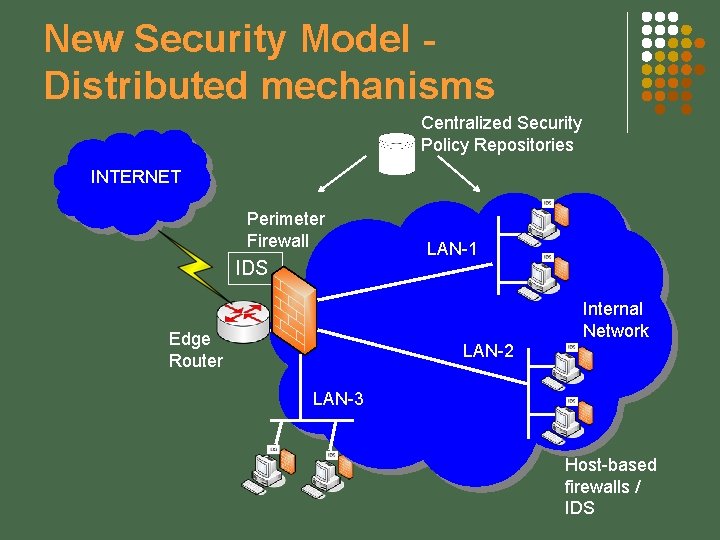
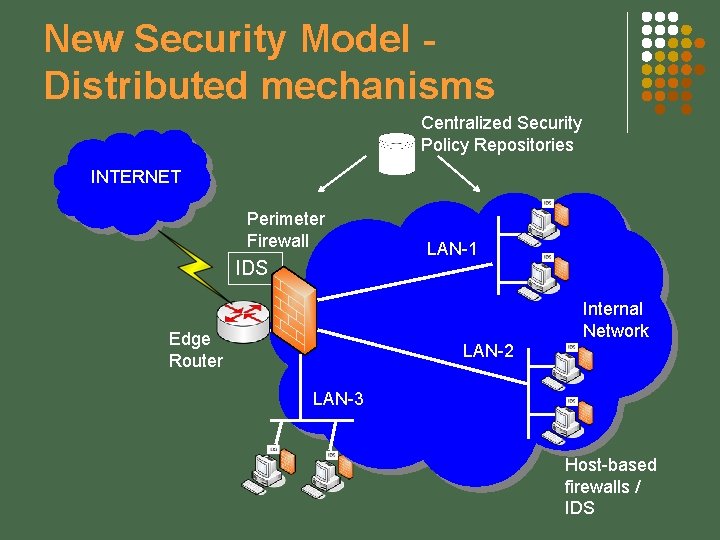
New Security Model Distributed mechanisms Centralized Security Policy Repositories INTERNET Perimeter Firewall IDS LAN-1 Internal Network Edge Router LAN-2 LAN-3 Host-based firewalls / IDS
New Security Model l l End-to-End IPsec Distributed security with the communicating hosts providing the policy enforcement for their own communication. l l Creating specific policies for securing comm. based on currently running appl. Rather than having a central enforcement point try and provide a single group-based policy. Possible to create more dynamic security policies which can vary over time based on changing trust relationships.
Distributed security endpoints l l l Consists of host-resident firewalls, intrusion detection, security patching, and security status monitoring – can be accomplished by kernel-mode processes within an OS. A managed distributed host-based firewall system utilizing end-to-end IPsec can implement separate multi-level security policies with fine granularity. Using end-to-end model, it is possible to divide users and servers into various trust groups and interest communities to implement separate security rules.
Conclusion To design a new security mechanisms model l In depth understanding of IPsec Define optimum security policies associated to network requirements Build a comprehensive distributed firewalls to counter security issues in IPv 4 as well as IPv 6 l l As well as IDS and IPS, logging/auditing Security test using available attacking tools
Bibliographies • Kaeo, et. al. , 2006, IPv 6 Network Security Architecture 1. 0, NAv 6 tf, www. nav 6 tf. org. • Van Hauser, The Hackers Choice, 2006, http: //www. thc. org. • J. Mohacsi, IPv 6 Security: Threats and Solutions, http: //www. 6 net. org/events/workshop-2005/mohacsi. pdf • P. Nikander, J. Kempf, and E. Nordmark, “IPv 6 Neighbor Discovery (ND) Trust Models and Threats”, RFC 3756, May 2004. • E. Davies, S. Krishnan and P. Savola, “IPv 6 Transition/Coexistence Security Considerations”, draft-ietf-v 6 ops-securityoverview-06. txt (work in progress), Oct 2006. • Alvaro Vives and Jordi Palet, IPv 6 Distributed Security: Problem Statement, Proceedings of the 2005 Symposium on Applications and the Internet Workshops (SAINT-W’ 05), IEEE, 2005.
THANK YOU Q&A
