IPsec Problems and Solutions Yasir Jan Future Internet
IPsec Problems and Solutions Yasir Jan Future Internet 29 th May, 2008 1/19
Contents o o o o Definition Architecture Types Modes of Operation Key Exchange Multiple Options IPsec problems and solutions Summary References 2
IPsec Definition o IP security refers to security mechanisms implemented at the IP (Internet Protocol) Layer to ensure integrity, authentication and confidentiality of data during transmission in the open Internet environment. Fig: Security 3
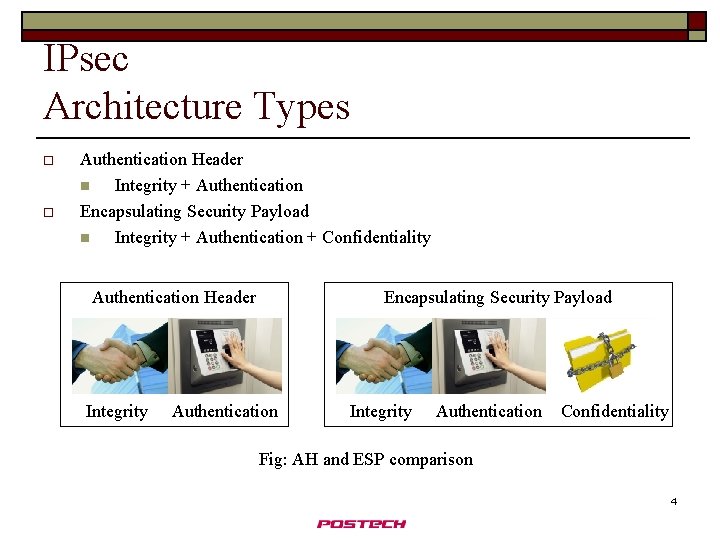
IPsec Architecture Types o o Authentication Header n Integrity + Authentication Encapsulating Security Payload n Integrity + Authentication + Confidentiality Authentication Header Integrity Encapsulating Security Payload Authentication Integrity Authentication Confidentiality Fig: AH and ESP comparison 4
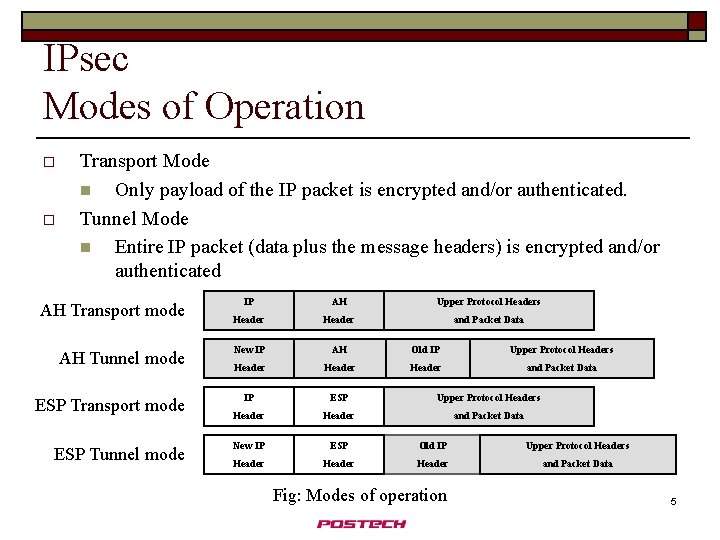
IPsec Modes of Operation o o Transport Mode n Only payload of the IP packet is encrypted and/or authenticated. Tunnel Mode n Entire IP packet (data plus the message headers) is encrypted and/or authenticated AH Transport mode AH Tunnel mode ESP Transport mode ESP Tunnel mode IP AH Upper Protocol Headers Header and Packet Data New IP AH Old IP Upper Protocol Headers Header and Packet Data IP ESP Upper Protocol Headers Header and Packet Data New IP ESP Old IP Upper Protocol Headers Header and Packet Data Fig: Modes of operation 5
IPsec Key Exchange o IPsec Key Exchange Protocol is a combination of many protocols n ISAKMP is a generic protocol n OAKLEY is a specific mechanism using various modes. Most of IKE is done using OAKLEY n SKEME provides features of public key encryption and fast re-keying feature n IKEv 2 also concerns protection against denial-of-service attacks using spoofed packets Fig: Key exchange 6
IPsec Multiple options o Use any Authentication method n Cryptographic hash algorithms such as MD 5 or SHA-1, or Hashed Message Authentication Code (HMAC) o Use any Encryption Schemes n Data Encryption Standard (DES), triple -DES, Advanced Encryption Standard (AES), and Blowfish in common use o Use any protocols in IKE Fig: Many options 7
IPsec problems and solutions 1) Key Management in Large Networks n When IPsec is largely developed, key management becomes very difficult 2) Difficult Traffic analysis n Cannot check and process flags at intermediate devices because of encryptions Fig: Big Networks 8
IPsec problems and solutions 3) Resource Consumption n Encryption decryption processes are computational intensive n Cisco designed VPN accelerator card to handle computation separately 4) Too much flexibility n Unnecessary multiple options available for choosing algorithms and modes n Solution: Reduced flexibility is sometimes better (Remove AH) Fig: Consume many resources 9
IPsec problems and solutions 5) Client software n IPsec is not implemented in TCP/IP stack, needs a client installed n Danger of installing malicious unreliable software by a user n Solution: Install clients from reliable sources 6) Relayed ICMP messages Fig: Malicious Software n ICMP inner data is revealed to attacker, so it can be intercepted n Using ICMP header information IPsec packets could be redirected, in some cases, or error messages can be generated [1] n Solution: Use ESP along with AH 10
IPsec problems and solutions 7) Scrambled Group passwords recovery n IPsec passwords were first sniffed from memories, when used, so Cisco VPN clients were designed to scramble the passwords in memory, but they were hacked again n Once getting group password, an attacker can hijack a connection from a user and get other usernames and passwords 8) No End-End Protection n Applications use their own SSL or other techniques n IETF working on API integrated with IPsec to achieve maximum use Fig: Scrambled passwords 11
IPsec problems and solutions 9) Firewalls n firewalls monitor the ports and protocols that the traffic originates from and is designated for, to determine the traffic’s “acceptability” before allowing the traffic through n Firewall is easy to setup with the standard exceptions and any customizations you need n With IPsec you have to create rules with filter lists and actions and then add these to a policy, and then distribute them and …. n But IPsec has many good things as compared to firewalls like encryption, no bottle necks etc Fig: IPsec vs firewalls 12
IPsec problems and solutions 10) Vo. IP Quality loss n Scheduling causes packet loss in real time applications n Latency in Vo. IPs 11) Denial of Service n Send too many acknowledge messages to the victim during wait period of TCP connection timeout n Solution: IKEv 2 has the solution Fig: Voice quality and Denial of service 13
IPsec problems and solutions 12) Multicast Traffic n Packets have single destination addresses, so difficult to mange SPI n Some applications using streaming multimedia assign port numbers dynamically, so IPsec policy becomes difficult to assign n IPsec has multicast option but is not enough for all occasions 13) Security within algorithms n IPsec works with other protocols for security. They should be secure enough to stop attacker otherwise only secure IPsec is useless Fig: Multicast traffic 14
IPsec problems and solutions 14) Brute Force Attack n ESP initiation scheme is fixed 3 steps of Aggressive mode, so intruder may try to delay the initiation during which it will find the key by brute force attack n Crack Tool was used with Pre-Shared-Key IKE authentication [2] for guessing with brute force Fig: Trying out ALL options by brute force 15
IPsec problems and solutions 15) Incompatibility with NAT (RFC 3715) n Network Address Translation (NAT) was developed to answer the impending problems of the limit of IPv 4 addresses n When NAT changes the IP addresses or ports in the IP header, IPSec cannot recalculate the hash because it is not knowledgeable about the key and so IPsec drops the packets. In ESP the NAT device cannot access and change the port information inside the encrypted TCP headers of the packets n Solution: NAT-T (encapsulation of the IPsec part of the IP packet in yet another UDP header between the ESP portion of the packet and the original IP header. ) Fig: IPsec and NAT are incompatible 16
Summary o o IPsec has multiple components Security and authentication is provided by additional components so they should be also secure IPsec have some incompatibility issues IPsec is overall complex, needs simplification Fig: Summary 17
References o o o o http: //searchsecurity. techtarget. com/news/article/0, 289142, sid 14_gci 1086803, 00. h tml http: //ikecrack. sourceforge. net/ http: //www. securitydocs. com/pdf/2926. PDF http: //www. cisco. com http: //www. springerlink. com/content/t 84 w 482122 jt 81 x 3/fulltext. pdf http: //blogs. msdn. com/james_morey/default. aspx Images taken from various sources on internet Fig: References 18

Thankyou Fig: Questions 19
- Slides: 19