IP Communications Secure By Design Roger W Farnsworth
IP Communications, Secure – By Design Roger W. Farnsworth January 23 -26, 2007 • Ft. Lauderdale, Florida
A Bit of Hyperbole? January 23 -26, 2007 • Ft. Lauderdale, Florida
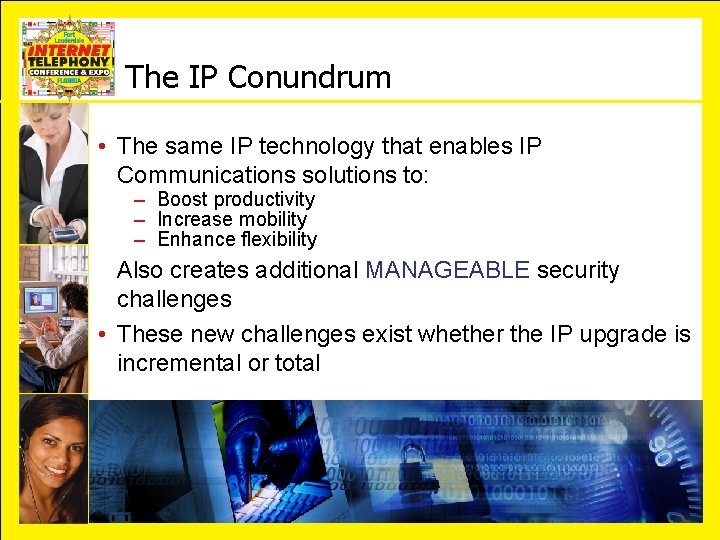
The IP Conundrum • The same IP technology that enables IP Communications solutions to: – Boost productivity – Increase mobility – Enhance flexibility Also creates additional MANAGEABLE security challenges • These new challenges exist whether the IP upgrade is incremental or total January 23 -26, 2007 • Ft. Lauderdale, Florida
The Challenge of Securing IP Voice • The threats are familiar to both voice and data professionals: – – Eavesdropping Impersonation Toll fraud Denial of service • Both “phreakers” and “hackers” are lurking • The protection of both voice and data communication is critical to the business 5 January 23 -26, 2007 • Ft. Lauderdale, Florida
Reality Check Before After January 23 -26, 2007 • Ft. Lauderdale, Florida
Evaluate the Threats Objectively • Understand the costs of security incidents: – Measurable: fraud, downtime, man-hours, physical destruction, intellectual property, lawsuits – Non-measurable: reputation, customer privacy, medical information, loss of life • Assign risk and quantify the costs • Determine appropriate levels of protection January 23 -26, 2007 • Ft. Lauderdale, Florida
The Paradigm Must Change: A Network-Based Systems Approach • An automated security system is required to address unknown (or “Day Zero”) threats • Security must be applied at multiple layers of the system to address sophisticated blended threats and defend against multiple avenues of attack • All elements of the security system must be integrated to initiate a coordinated response January 23 -26, 2007 • Ft. Lauderdale, Florida
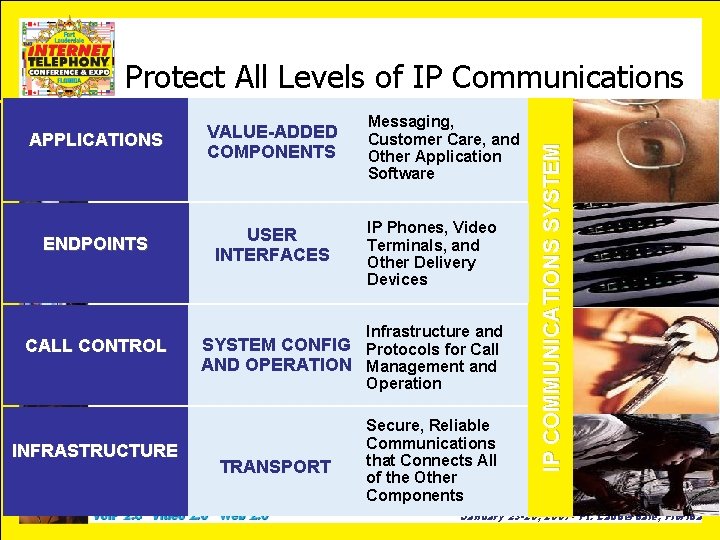
APPLICATIONS VALUE-ADDED COMPONENTS ENDPOINTS USER INTERFACES CALL CONTROL Messaging, Customer Care, and Other Application Software IP Phones, Video Terminals, and Other Delivery Devices Infrastructure and SYSTEM CONFIG Protocols for Call AND OPERATION Management and Operation INFRASTRUCTURE TRANSPORT Secure, Reliable Communications that Connects All of the Other Components IP COMMUNICATIONS SYSTEM Protect All Levels of IP Communications January 23 -26, 2007 • Ft. Lauderdale, Florida
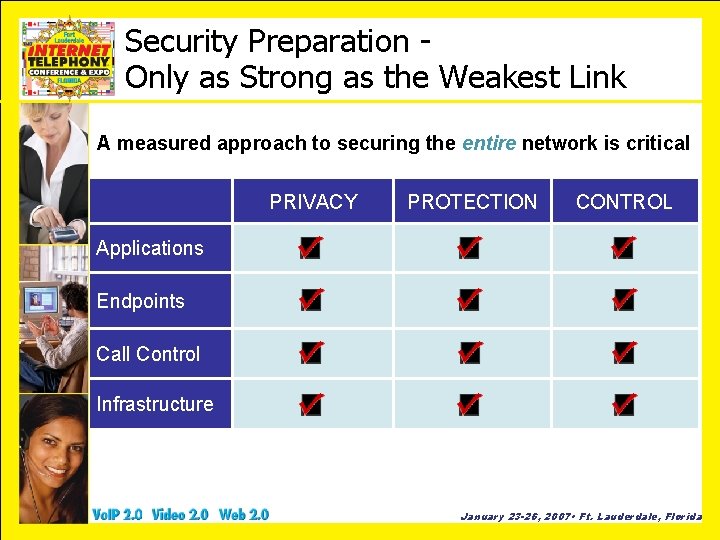
Security Preparation Only as Strong as the Weakest Link A measured approach to securing the entire network is critical PRIVACY PROTECTION CONTROL Applications X X X Endpoints X X X Call Control X X X Infrastructure X X X January 23 -26, 2007 • Ft. Lauderdale, Florida
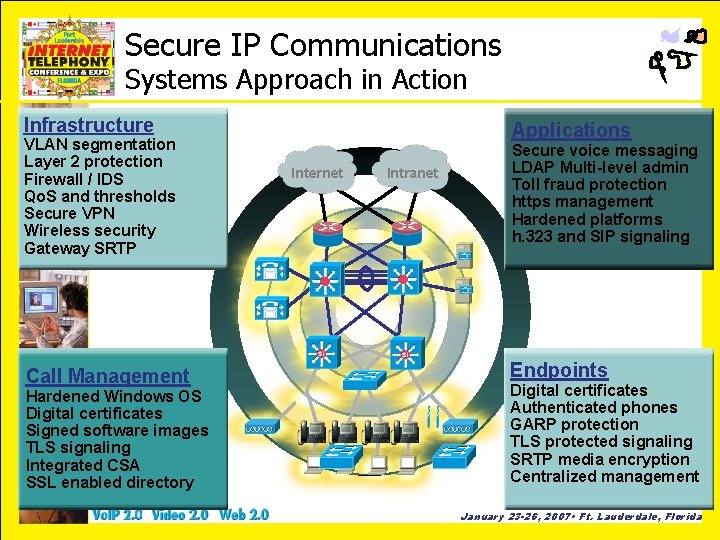
Secure IP Communications Systems Approach in Action Infrastructure VLAN segmentation Layer 2 protection Firewall / IDS Qo. S and thresholds Secure VPN Wireless security Gateway SRTP Call Management Hardened Windows OS Digital certificates Signed software images TLS signaling Integrated CSA SSL enabled directory Applications Internet Intranet Secure voice messaging LDAP Multi-level admin Toll fraud protection https management Hardened platforms h. 323 and SIP signaling Endpoints Digital certificates Authenticated phones GARP protection TLS protected signaling SRTP media encryption Centralized management January 23 -26, 2007 • Ft. Lauderdale, Florida
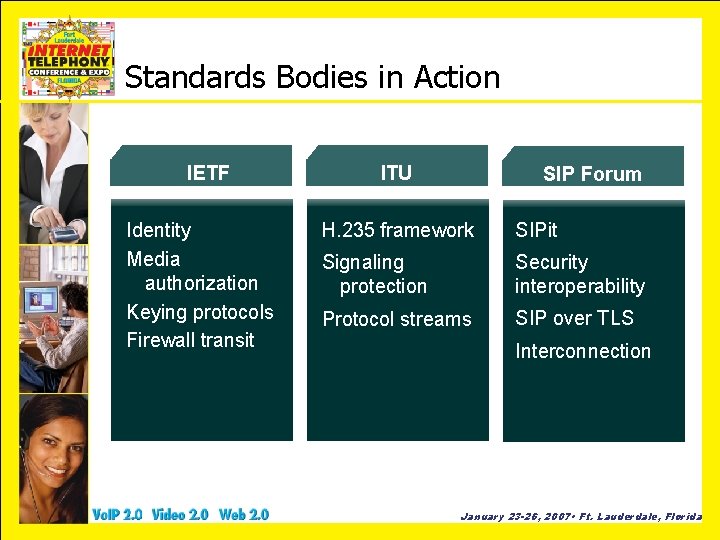
Standards Bodies in Action IETF Identity Media authorization Keying protocols Firewall transit ITU SIP Forum H. 235 framework SIPit Signaling protection Security interoperability Protocol streams SIP over TLS Interconnection January 23 -26, 2007 • Ft. Lauderdale, Florida
There is Nothing to Fear Except Fear Itself • IP Communications solutions can be as secure, or more secure, than traditional PBX systems – Security remains a top issue of IP Communications customers – A comprehensive, systems approach is best – The industry is committed to delivering the most secure, reliable solutions possible – The future holds great promise for new applications January 23 -26, 2007 • Ft. Lauderdale, Florida
More Information • www. nist. gov • www. cert. org • Your vendor or partner January 23 -26, 2007 • Ft. Lauderdale, Florida
- Slides: 14