Investigating Liberty Alliance and Shibboleth Integration Nishen Naidoo
Investigating Liberty Alliance and Shibboleth Integration Nishen Naidoo, 30396468 Supervisor: Dr. Steve Cassidy Workshop Presentation [1]
Talk Outline • Introduction to Federated Identity Management – Example • Multiple Frameworks – Shibboleth – Liberty Alliance • Project Objectives and Motivation • Deconstructing the Frameworks • Conclusion Workshop Presentation [2]
Federated Identity Management (FIM) • • Reduce number of online identities Reduce privacy exposure User controls who sees what Enables easy sharing of resources Workshop Presentation [3]
Main Actors in FIM • Users – Using a User Agent (Browser) • Service Provider – Provide resources and services – Protect resources and services • Identity Provider – Authenticates users – Provides security assertions to Service Providers Workshop Presentation [4]
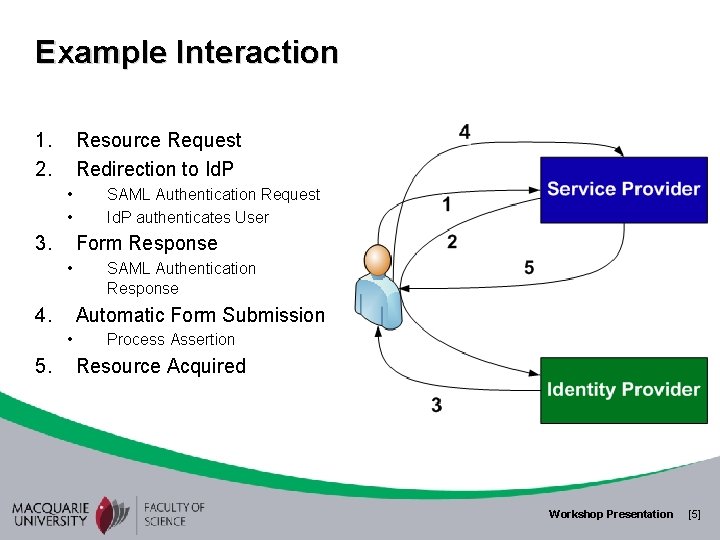
Example Interaction 1. 2. Resource Request Redirection to Id. P • • 3. Form Response • 4. SAML Authentication Response Automatic Form Submission • 5. SAML Authentication Request Id. P authenticates User Process Assertion Resource Acquired Workshop Presentation [5]
Multiple Frameworks • Shibboleth – Higher Education focus – Resource Sharing, privacy, security – In. Common, AAF • Liberty Alliance – Commercial sector focus – Service integration, privacy, security – Intel, GM Workshop Presentation [6]
Issues with Multiple Frameworks • User perspective – More credentials due to technology limitation – Less privacy • Unnecessary federations – Formed from having to support multiple technologies • Increases difficulty of forming federations – Need to support services within each framework? What do you do? Workshop Presentation [7]
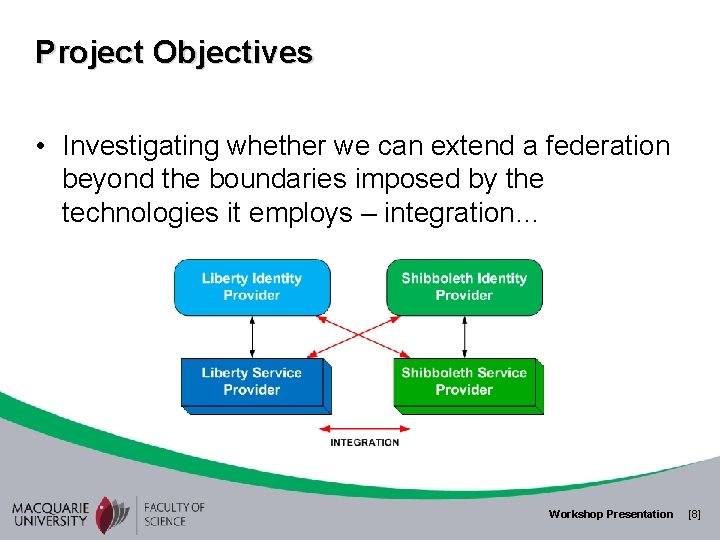
Project Objectives • Investigating whether we can extend a federation beyond the boundaries imposed by the technologies it employs – integration… Workshop Presentation [8]
Deconstructing the Frameworks • Both frameworks base on SAML specification • Identified the following: – – Assertions – identical to each other (both SAML) Protocols – identical (SAML) Bindings - Different Profiles – Similar enough (derived from SAML). Workshop Presentation [9]
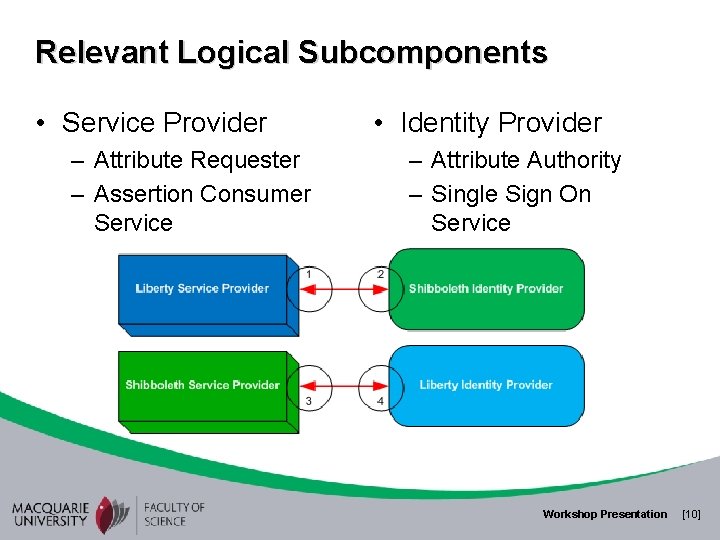
Relevant Logical Subcomponents • Service Provider – Attribute Requester – Assertion Consumer Service • Identity Provider – Attribute Authority – Single Sign On Service Workshop Presentation [10]
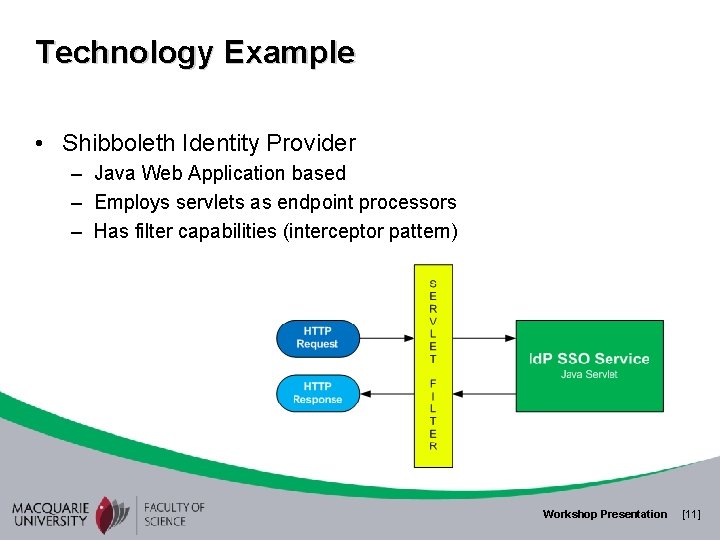
Technology Example • Shibboleth Identity Provider – Java Web Application based – Employs servlets as endpoint processors – Has filter capabilities (interceptor pattern) Workshop Presentation [11]
Conclusion • Identified the binding differences and conversions – Message structure – Parameter referencing • Identified strategic architectural locations for adaptation • Provided technology example • Identified implementation as future work Workshop Presentation [12]
- Slides: 12