Invasive Browser Sniffing and Countermeasures Markus Jakobsson Sid
Invasive Browser Sniffing and Countermeasures Markus Jakobsson & Sid Stamm
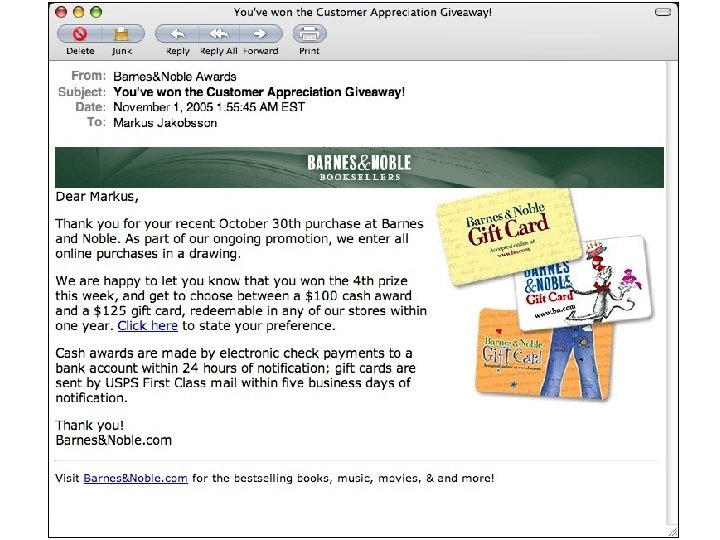
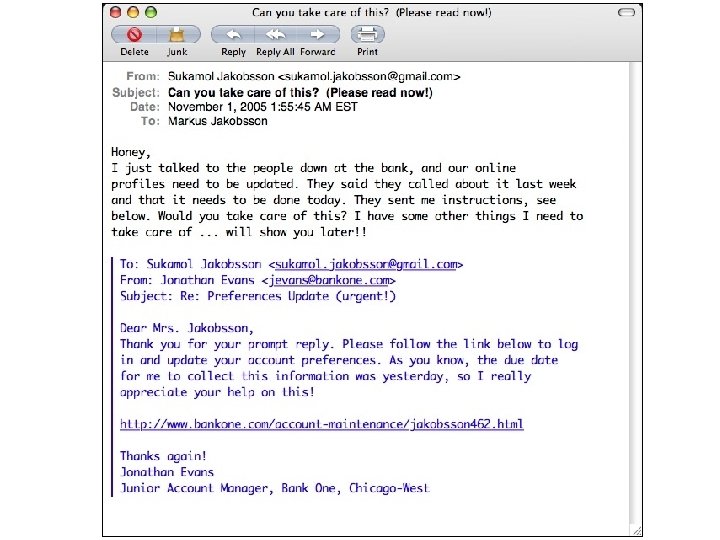
Context Aware Attacks • Data about targets obtained • Used to customize emails • Yields higher vulnerability rate
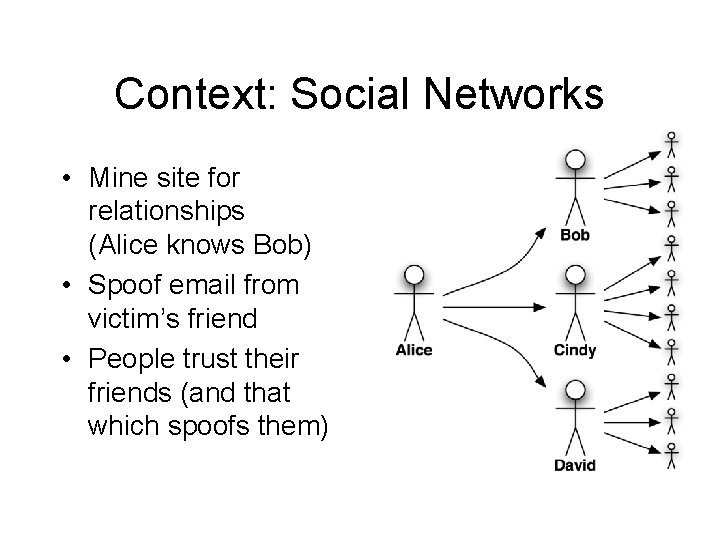
Context: Social Networks • Mine site for relationships (Alice knows Bob) • Spoof email from victim’s friend • People trust their friends (and that which spoofs them)
Context: Browser-Recon • Phisher mines browsers – �Browsing history – Cached data • Attacker can discover affiliations • Easy to pair browser history with email address
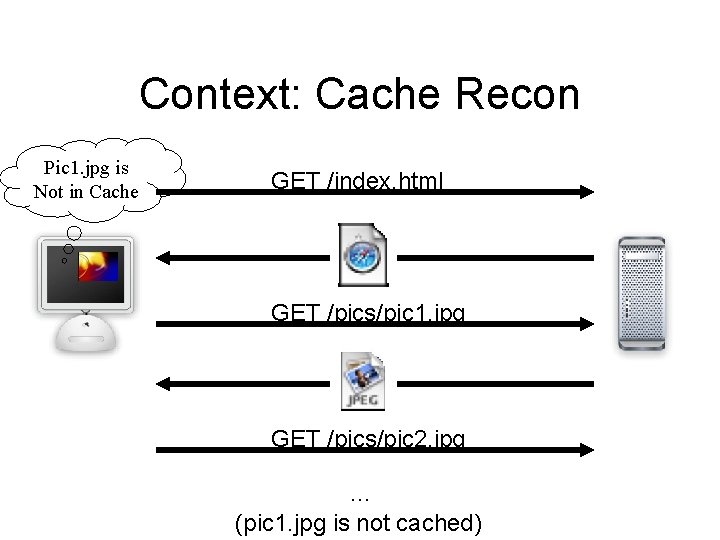
Context: Cache Recon Pic 1. jpg is Not in Cache GET /index. html GET /pics/pic 1. jpg GET /pics/pic 2. jpg … (pic 1. jpg is not cached)
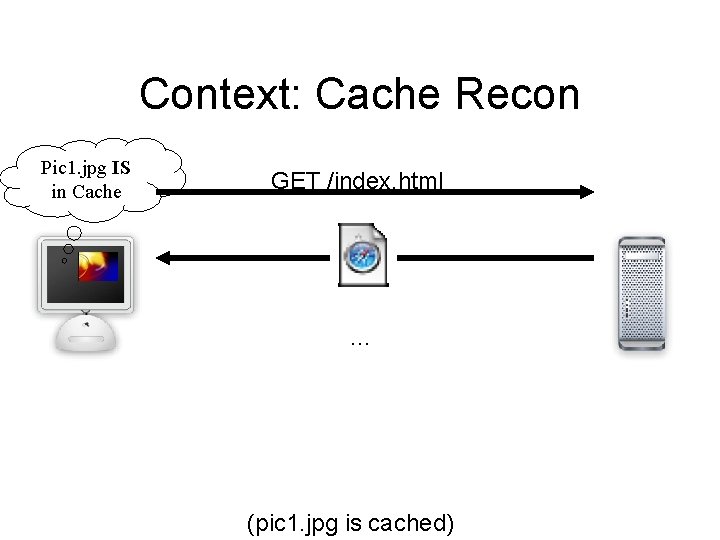
Context: Cache Recon Pic 1. jpg IS in Cache GET /index. html … (pic 1. jpg is cached)
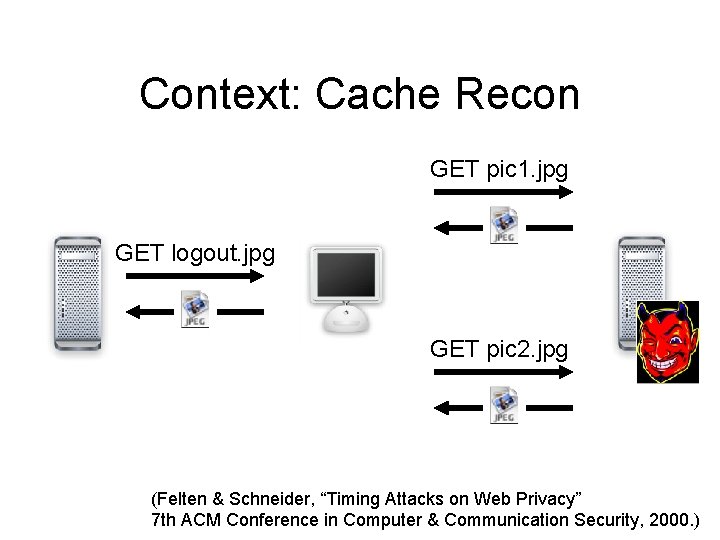
Context: Cache Recon GET pic 1. jpg GET logout. jpg GET pic 2. jpg (Felten & Schneider, “Timing Attacks on Web Privacy” 7 th ACM Conference in Computer & Communication Security, 2000. )
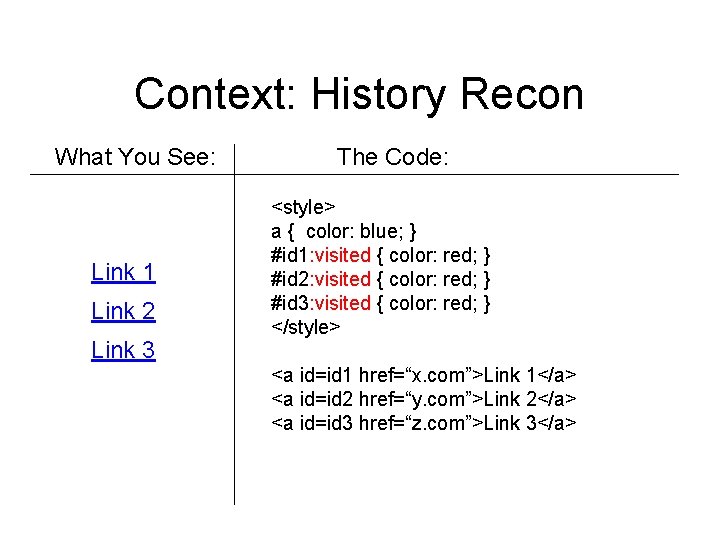
Context: History Recon What You See: Link 1 Link 2 Link 3 The Code: <style> a { color: blue; } #id 1: visited { color: red; } #id 2: visited { color: red; } #id 3: visited { color: red; } </style> <a id=id 1 href=“x. com”>Link 1</a> <a id=id 2 href=“y. com”>Link 2</a> <a id=id 3 href=“z. com”>Link 3</a>
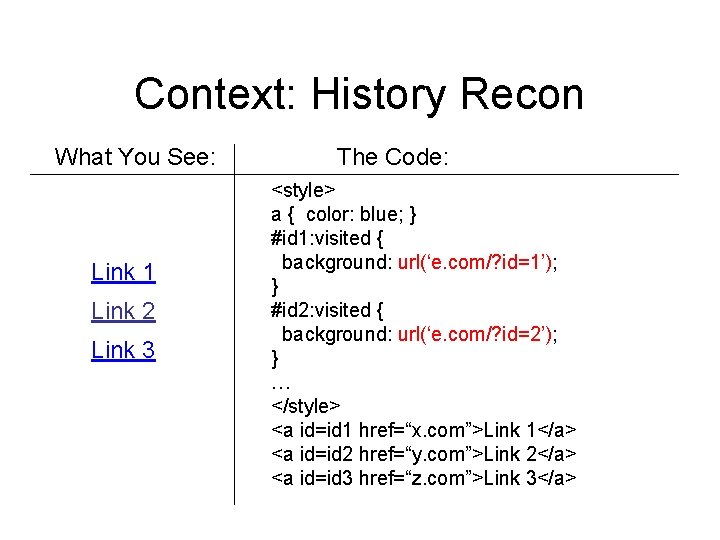
Context: History Recon What You See: Link 1 Link 2 Link 3 The Code: <style> a { color: blue; } #id 1: visited { background: url(‘e. com/? id=1’); } #id 2: visited { background: url(‘e. com/? id=2’); } … </style> <a id=id 1 href=“x. com”>Link 1</a> <a id=id 2 href=“y. com”>Link 2</a> <a id=id 3 href=“z. com”>Link 3</a>
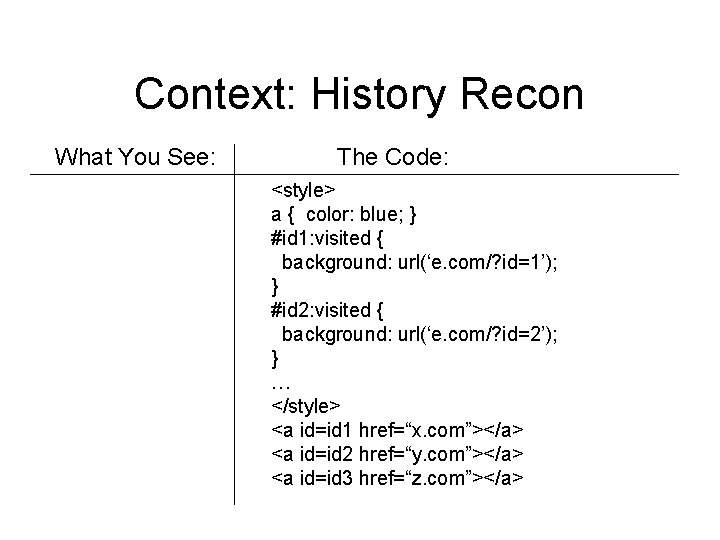
Context: History Recon What You See: The Code: <style> a { color: blue; } #id 1: visited { background: url(‘e. com/? id=1’); } #id 2: visited { background: url(‘e. com/? id=2’); } … </style> <a id=id 1 href=“x. com”></a> <a id=id 2 href=“y. com”></a> <a id=id 3 href=“z. com”></a>
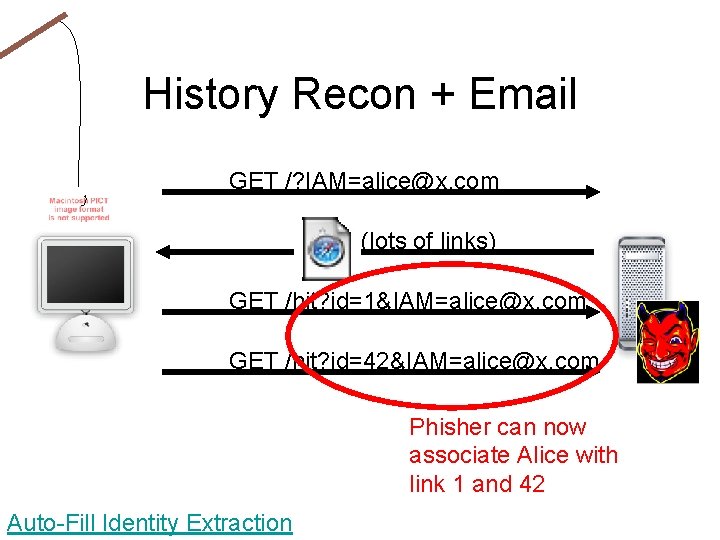
History Recon + Email GET /? IAM=alice@x. com (lots of links) GET /hit? id=1&IAM=alice@x. com GET /hit? id=42&IAM=alice@x. com Phisher can now associate Alice with link 1 and 42 Auto-Fill Identity Extraction
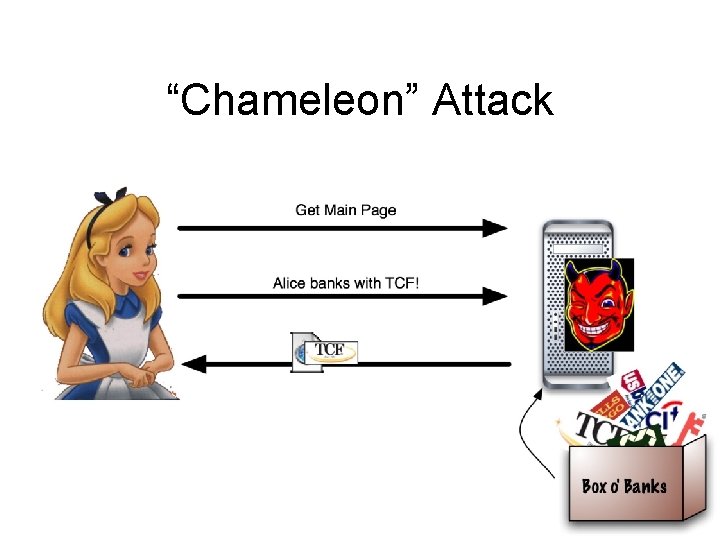
“Chameleon” Attack
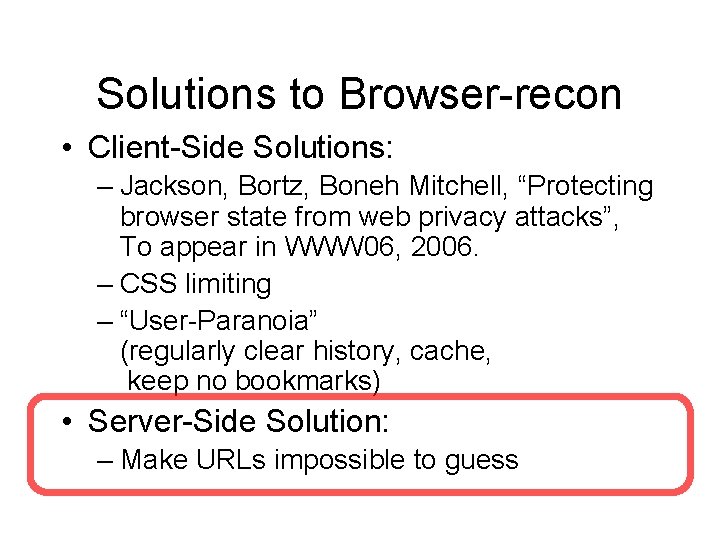
Solutions to Browser-recon • Client-Side Solutions: – Jackson, Bortz, Boneh Mitchell, “Protecting browser state from web privacy attacks”, To appear in WWW 06, 2006. – CSS limiting – “User-Paranoia” (regularly clear history, cache, keep no bookmarks) • Server-Side Solution: – Make URLs impossible to guess
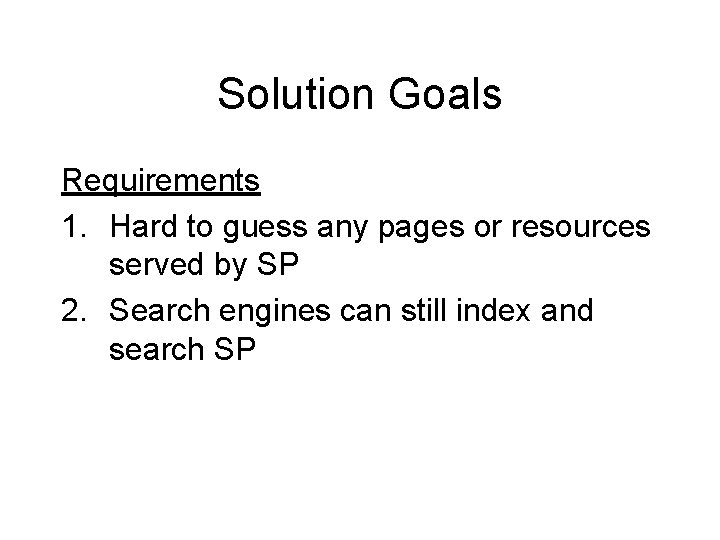
Solution Goals Requirements 1. Hard to guess any pages or resources served by SP 2. Search engines can still index and search SP
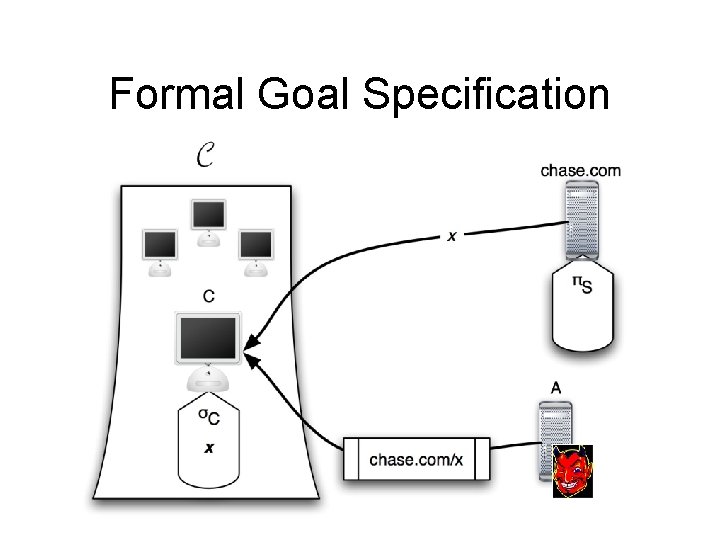
Formal Goal Specification
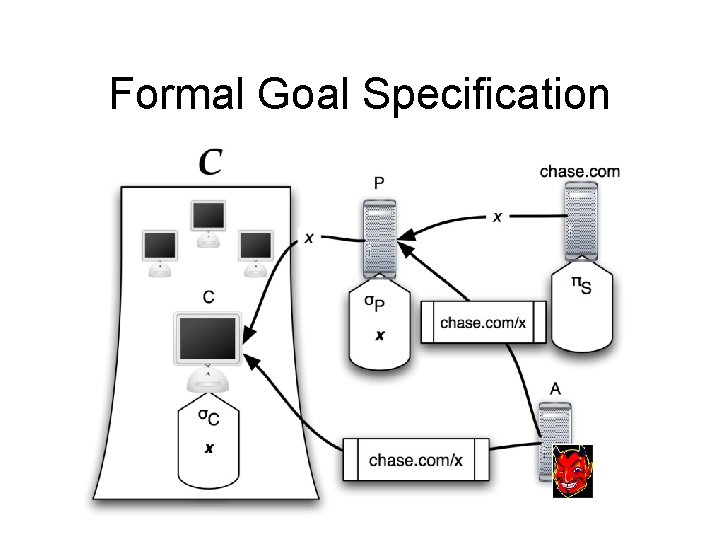
Formal Goal Specification
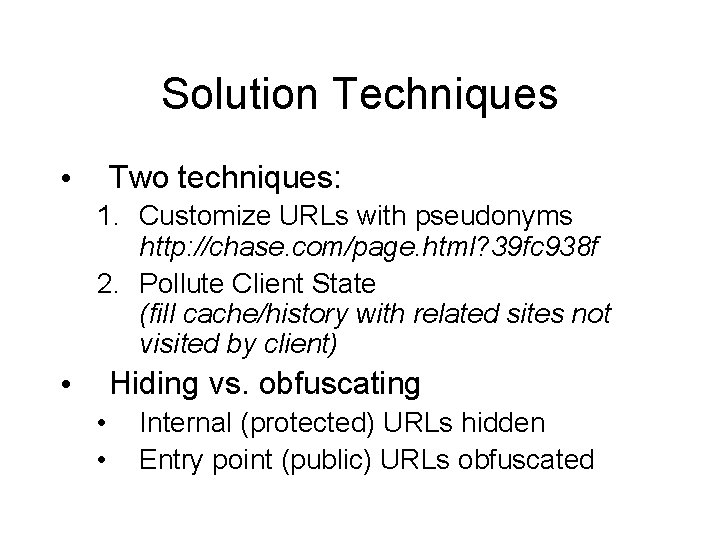
Solution Techniques Two techniques: • 1. Customize URLs with pseudonyms http: //chase. com/page. html? 39 fc 938 f 2. Pollute Client State (fill cache/history with related sites not visited by client) Hiding vs. obfuscating • • • Internal (protected) URLs hidden Entry point (public) URLs obfuscated
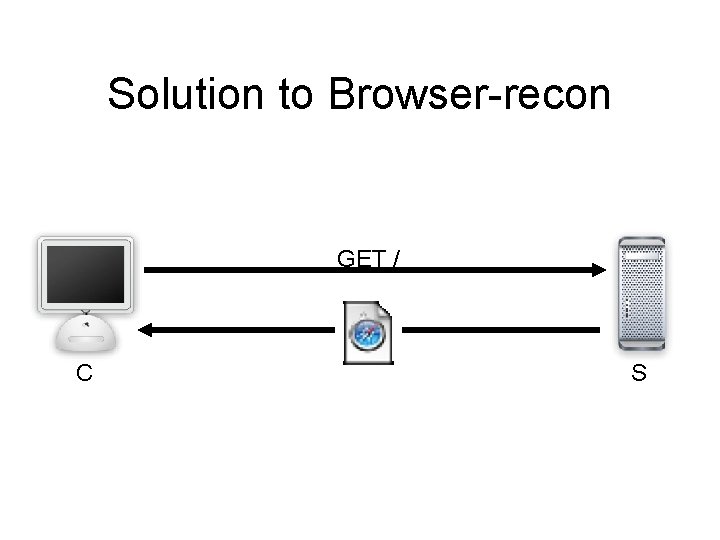
Solution to Browser-recon GET / C S
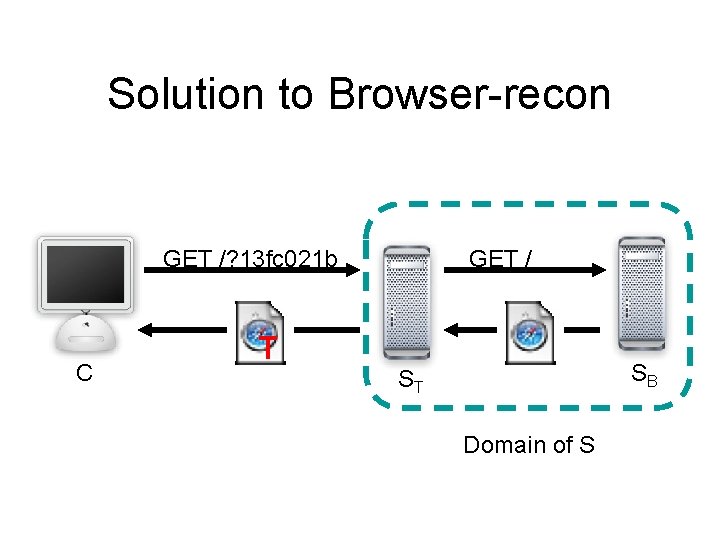
Solution to Browser-recon GET /? 13 fc 021 b C T GET / SB ST Domain of S
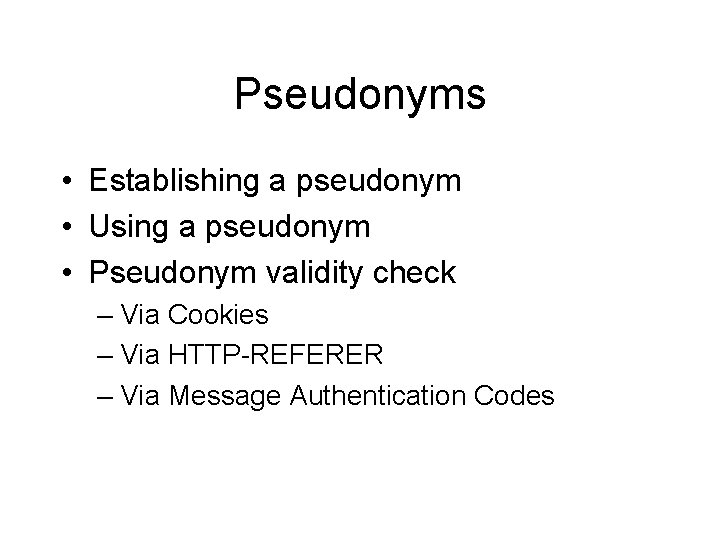
Pseudonyms • Establishing a pseudonym • Using a pseudonym • Pseudonym validity check – Via Cookies – Via HTTP-REFERER – Via Message Authentication Codes
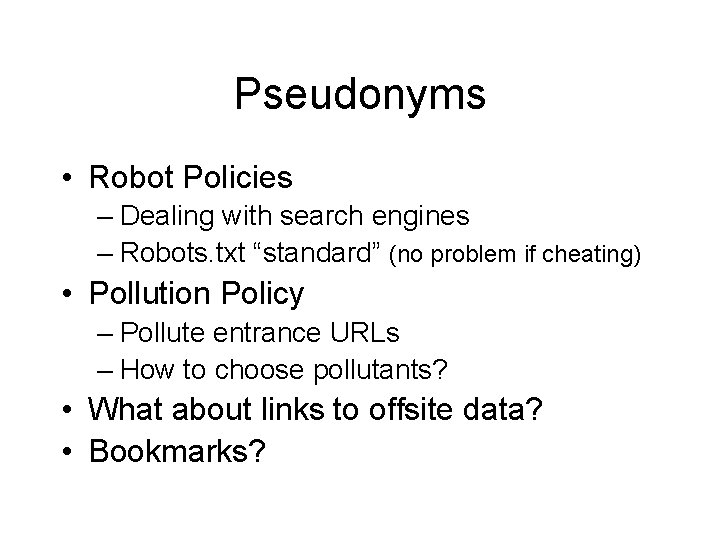
Pseudonyms • Robot Policies – Dealing with search engines – Robots. txt “standard” (no problem if cheating) • Pollution Policy – Pollute entrance URLs – How to choose pollutants? • What about links to offsite data? • Bookmarks?

Example GET /page. html? 83 fa 029 C GET /page. html Bank. com 10. 0. 0. 1

Example <a href=‘http: //www. g. com’>Go to G</a> <a href=‘http: //10. 0. 0. 1/login. jsp’>Log in</a> <img src=‘/img/hi. gif’> hm C Bank. com 10. 0. 0. 1
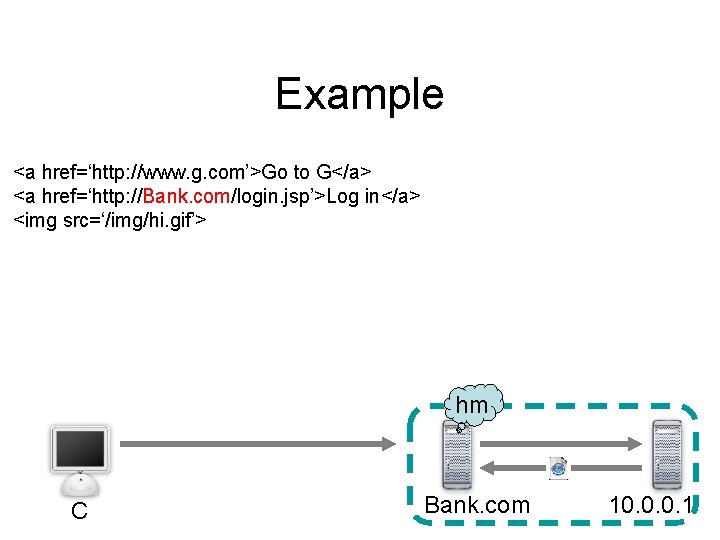
Example <a href=‘http: //www. g. com’>Go to G</a> <a href=‘http: //Bank. com/login. jsp’>Log in</a> <img src=‘/img/hi. gif’> hm C Bank. com 10. 0. 0. 1
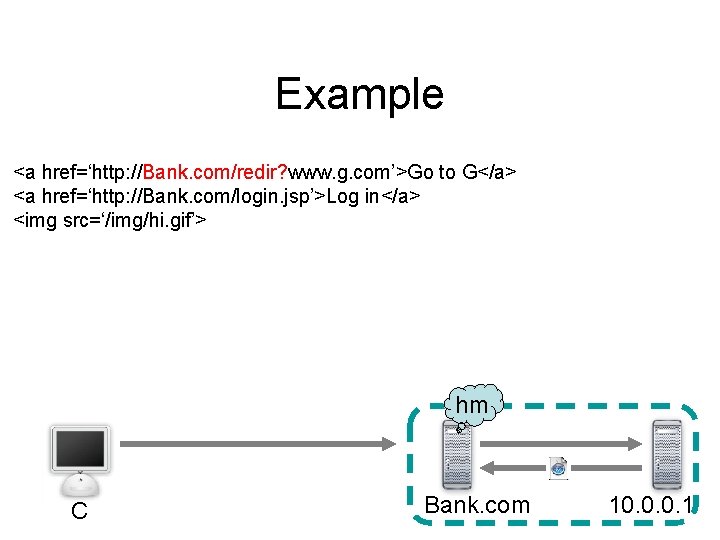
Example <a href=‘http: //Bank. com/redir? www. g. com’>Go to G</a> <a href=‘http: //Bank. com/login. jsp’>Log in</a> <img src=‘/img/hi. gif’> hm C Bank. com 10. 0. 0. 1
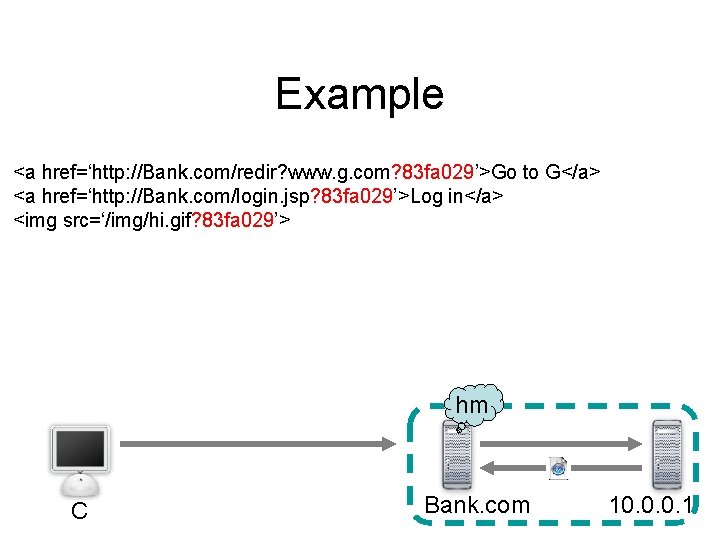
Example <a href=‘http: //Bank. com/redir? www. g. com? 83 fa 029’>Go to G</a> <a href=‘http: //Bank. com/login. jsp? 83 fa 029’>Log in</a> <img src=‘/img/hi. gif? 83 fa 029’> hm C Bank. com 10. 0. 0. 1
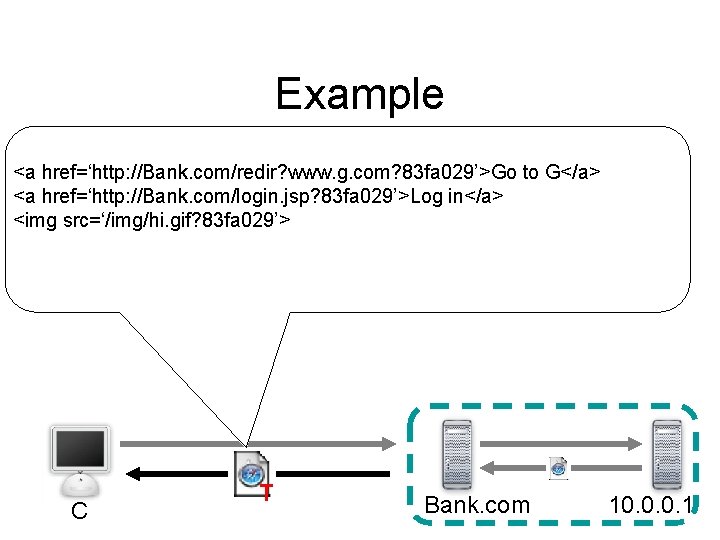
Example <a href=‘http: //Bank. com/redir? www. g. com? 83 fa 029’>Go to G</a> <a href=‘http: //Bank. com/login. jsp? 83 fa 029’>Log in</a> <img src=‘/img/hi. gif? 83 fa 029’> C T Bank. com 10. 0. 0. 1
Client’s Perception
Policies • Offsite Redirection Policy • Data Replacement Policy • Client vs. Robot Distinction
Special Cases Shared/Transfer Pseudonyms Cache pollution reciprocity
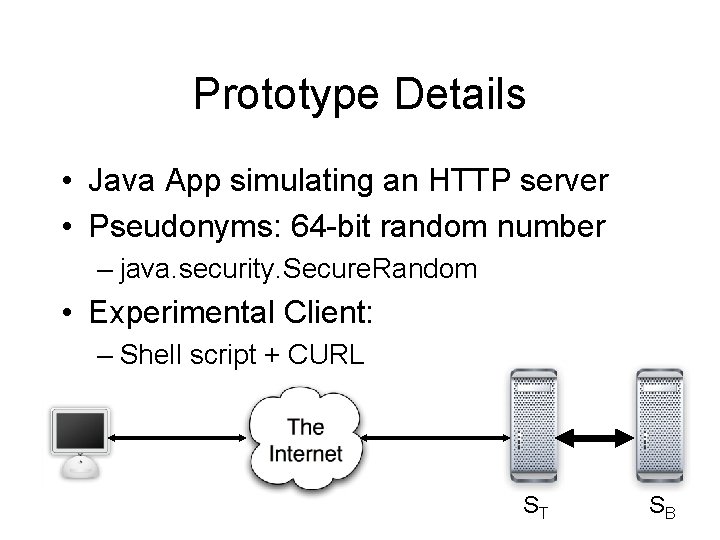
Prototype Details • Java App simulating an HTTP server • Pseudonyms: 64 -bit random number – java. security. Secure. Random • Experimental Client: – Shell script + CURL ST SB
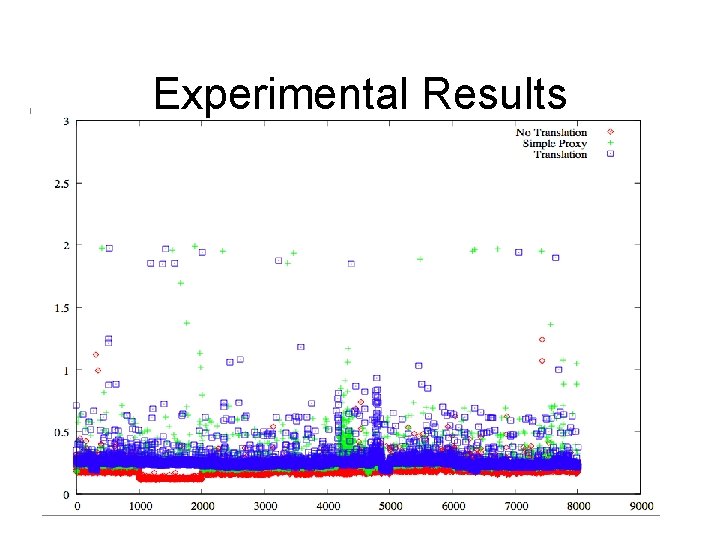
Experimental Results
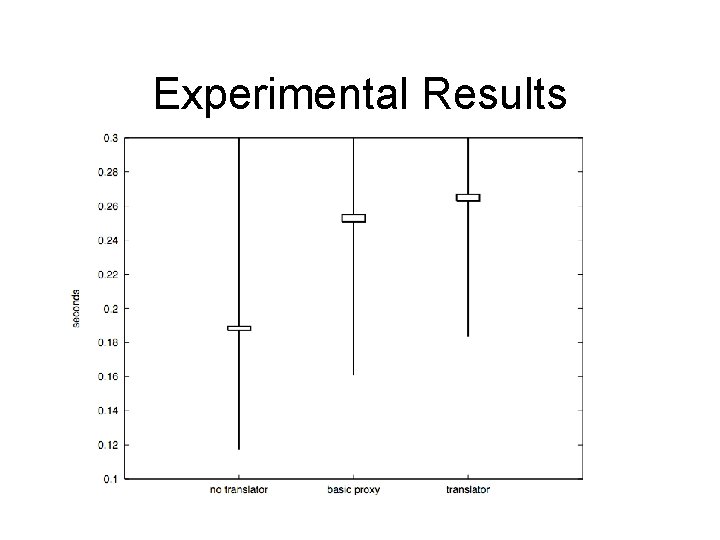
Experimental Results
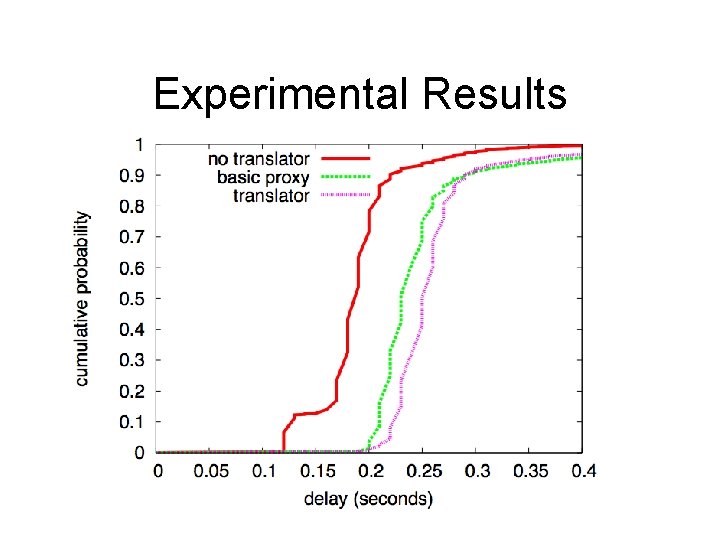
Experimental Results
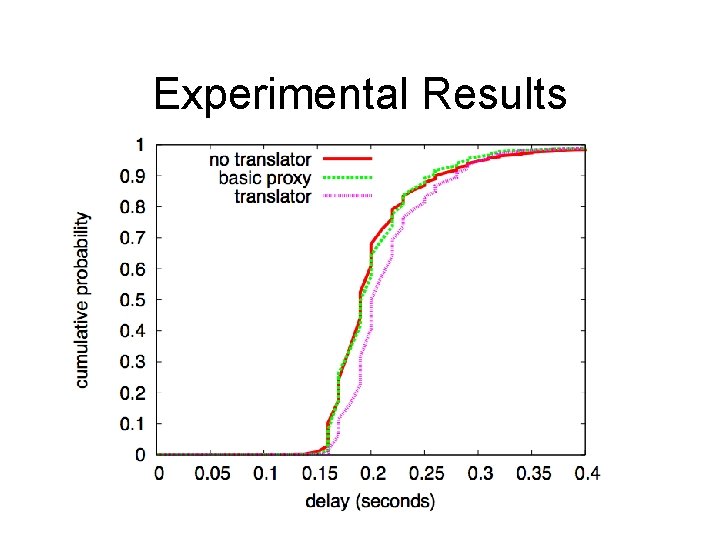
Experimental Results
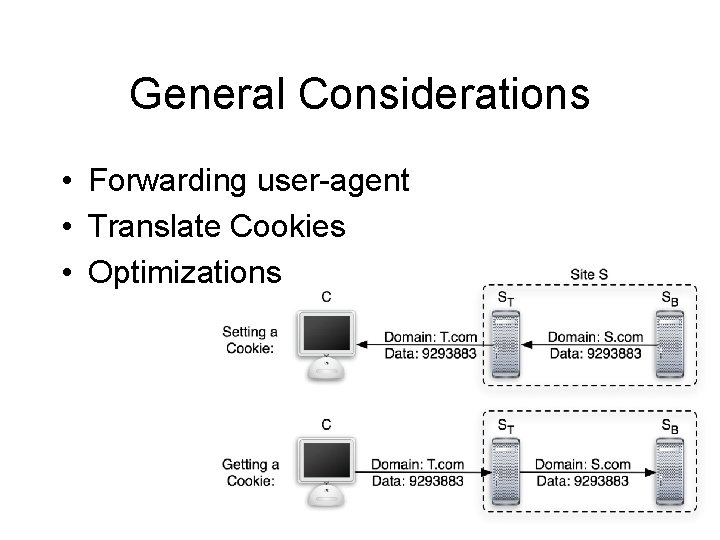
General Considerations • Forwarding user-agent • Translate Cookies • Optimizations
? Invasive Browser Sniffing and Countermeasures Markus Jakobsson & Sid Stamm
- Slides: 39