Intrusion Detection Systems with Snort Hailun Yan 564
- Slides: 30
Intrusion Detection Systems with Snort Hailun Yan 564 -project
Outline n n n IDS category Installation Procedure Components of Snort Most frequently used functions Testing of Snort/ACID
Components of Security System A security system consists: n Firewalls n Intrusion detection systems (IDS) n Vulnerability assessment tools
Category of IDS n Network Intrusion Detection System (NIDS) n n Listens & analyses traffic in a network Capture data package Compare with database signatures Host-based Intrusion Detection System (HIDS) n n Installed as an agent of a host Listens & analyses system logs
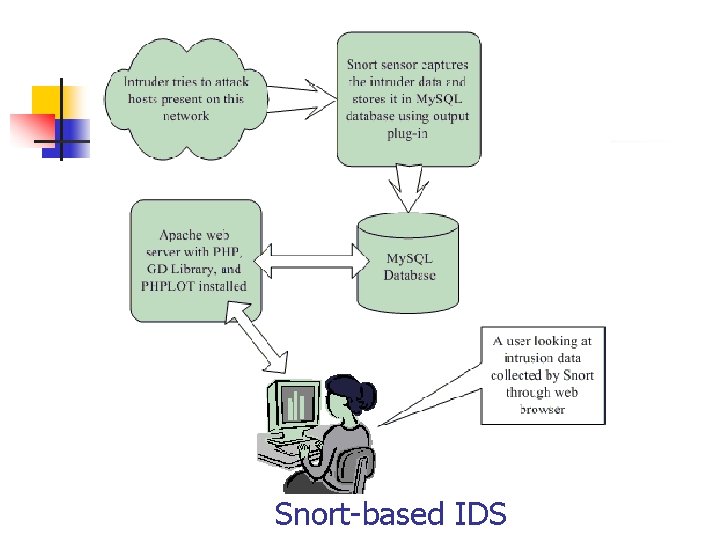
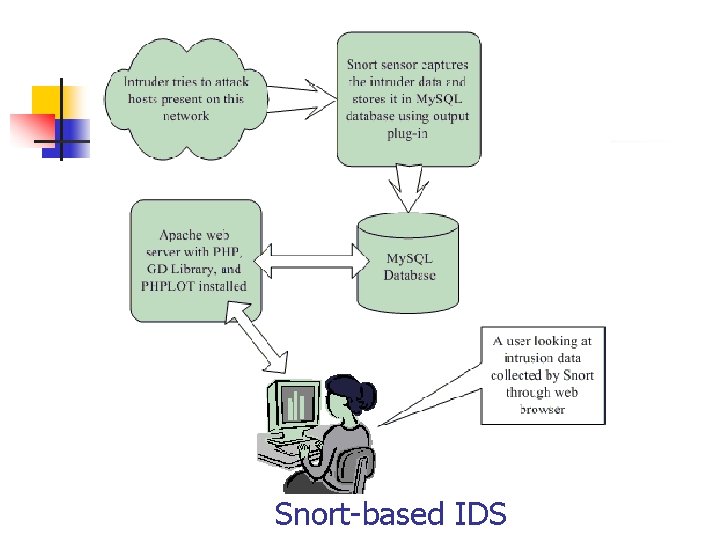
Snort-based IDS
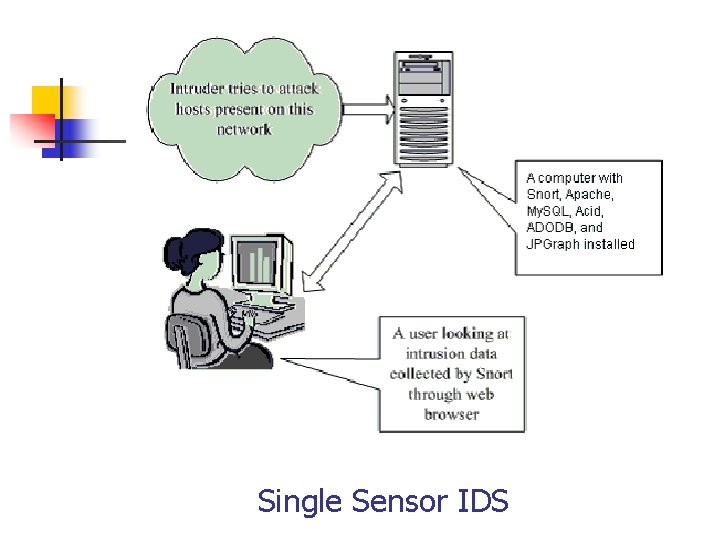
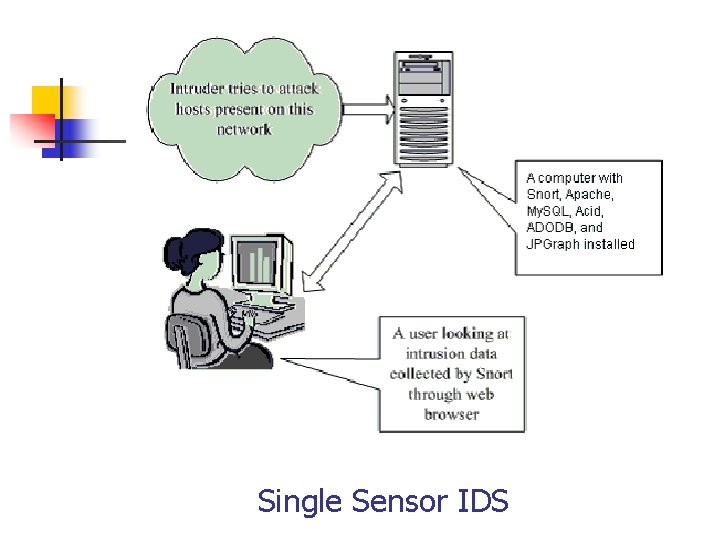
Single Sensor IDS
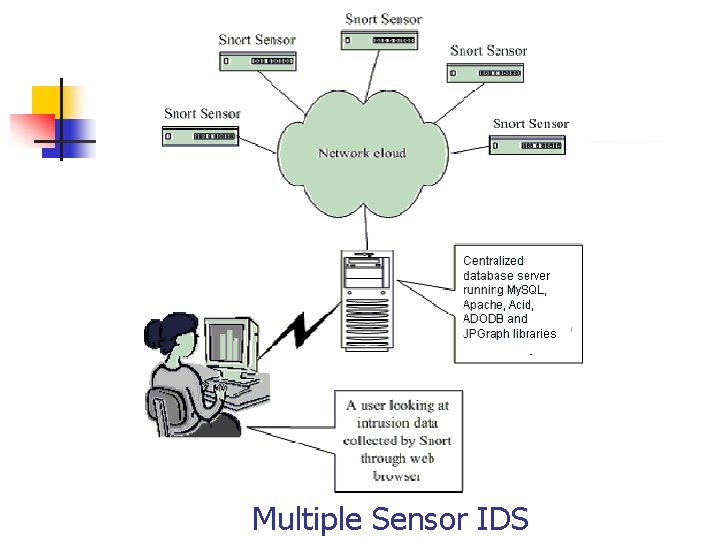
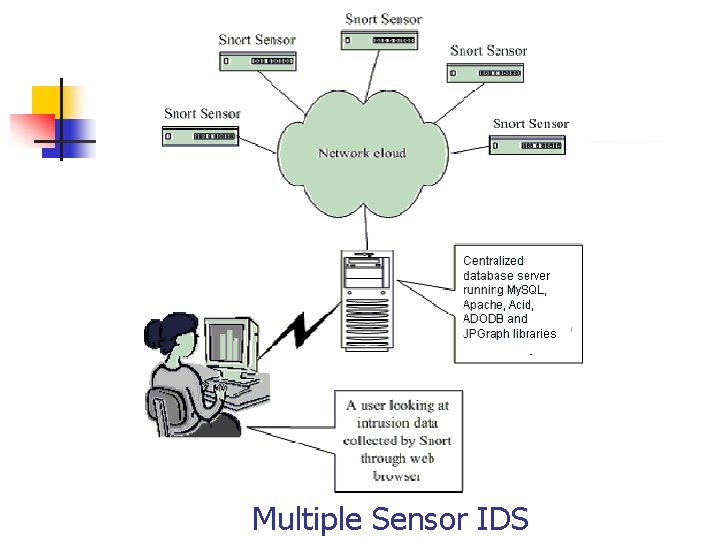
Multiple Sensor IDS
Installation n n Snort can be download from http: //www. snort. org Supported platform includes: n n n n Linux Free. BSD Open. BSD Solaris AIX HP-UX Mac. OS Windows
Installation (Cont. ) n Pre-installation n n Zlib 1. 2. 1 Lib. Pcap 0. 7. 2 My. SQL 4. 0. 15 Apache 2. 0. 52 PHP 4. 3. 3
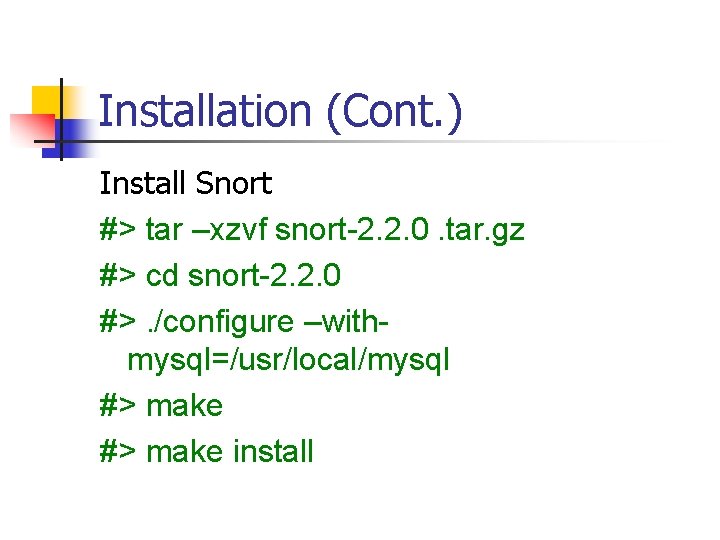
Installation (Cont. ) Install Snort #> tar –xzvf snort-2. 2. 0. tar. gz #> cd snort-2. 2. 0 #>. /configure –withmysql=/usr/local/mysql #> make install
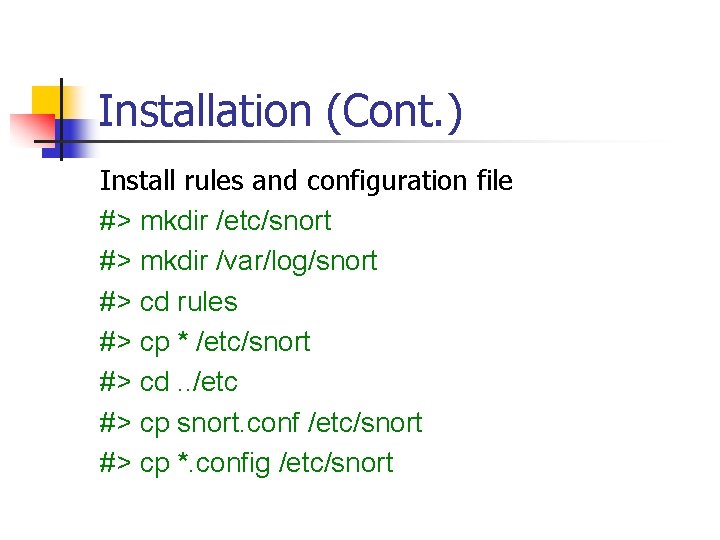
Installation (Cont. ) Install rules and configuration file #> mkdir /etc/snort #> mkdir /var/log/snort #> cd rules #> cp * /etc/snort #> cd. . /etc #> cp snort. conf /etc/snort #> cp *. config /etc/snort
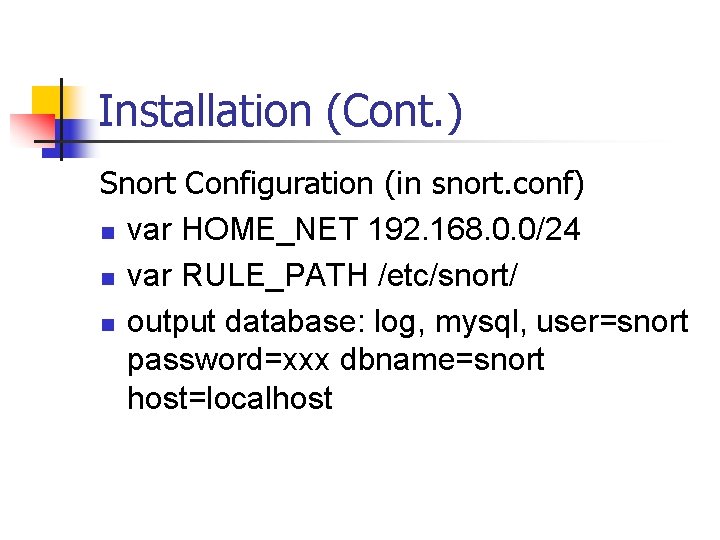
Installation (Cont. ) Snort Configuration (in snort. conf) n var HOME_NET 192. 168. 0. 0/24 n var RULE_PATH /etc/snort/ n output database: log, mysql, user=snort password=xxx dbname=snort host=localhost
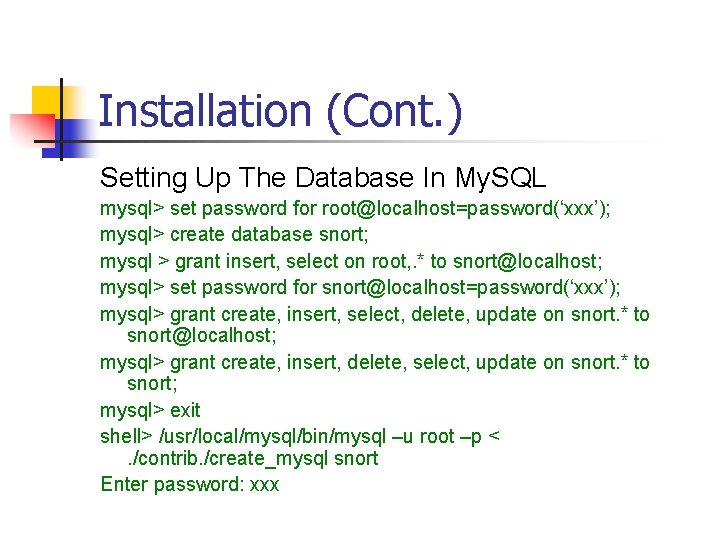
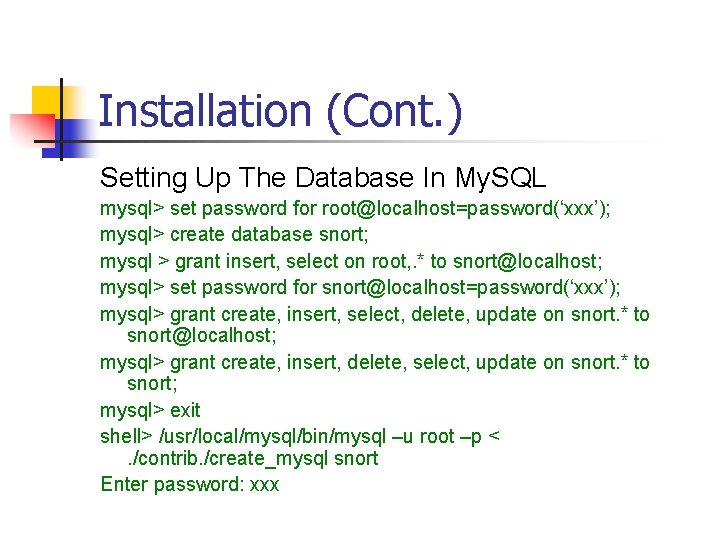
Installation (Cont. ) Setting Up The Database In My. SQL mysql> set password for root@localhost=password(‘xxx’); mysql> create database snort; mysql > grant insert, select on root, . * to snort@localhost; mysql> set password for snort@localhost=password(‘xxx’); mysql> grant create, insert, select, delete, update on snort. * to snort@localhost; mysql> grant create, insert, delete, select, update on snort. * to snort; mysql> exit shell> /usr/local/mysql/bin/mysql –u root –p <. /contrib. /create_mysql snort Enter password: xxx
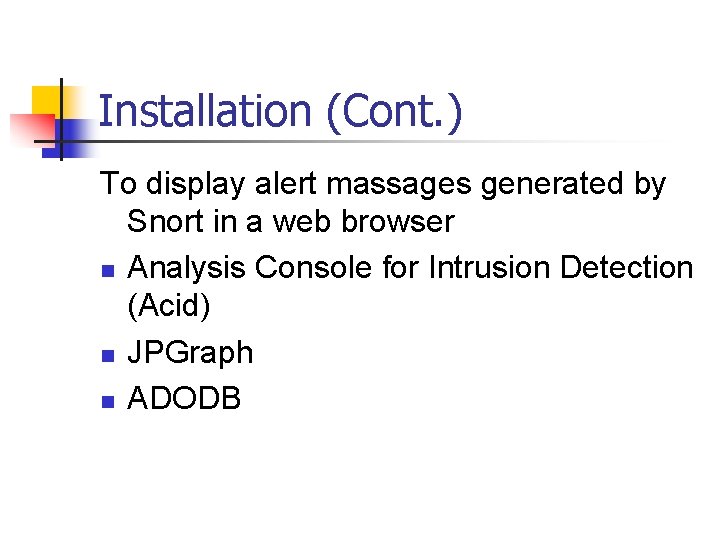
Installation (Cont. ) To display alert massages generated by Snort in a web browser n Analysis Console for Intrusion Detection (Acid) n JPGraph n ADODB
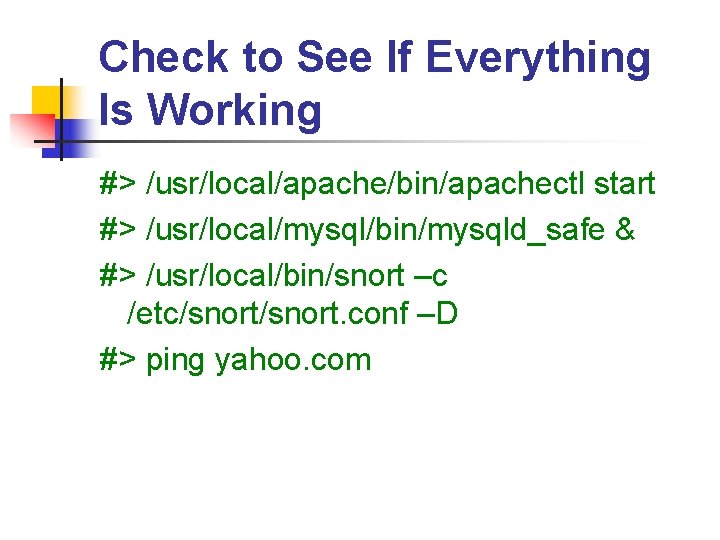
Check to See If Everything Is Working #> /usr/local/apache/bin/apachectl start #> /usr/local/mysql/bin/mysqld_safe & #> /usr/local/bin/snort –c /etc/snort. conf –D #> ping yahoo. com
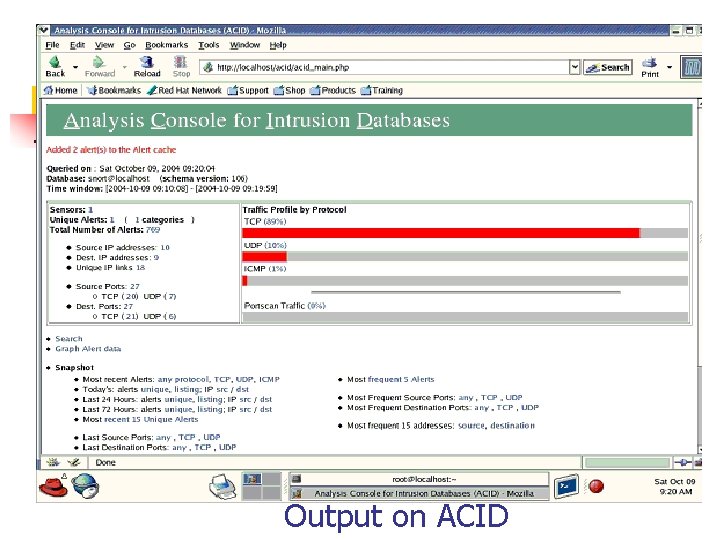
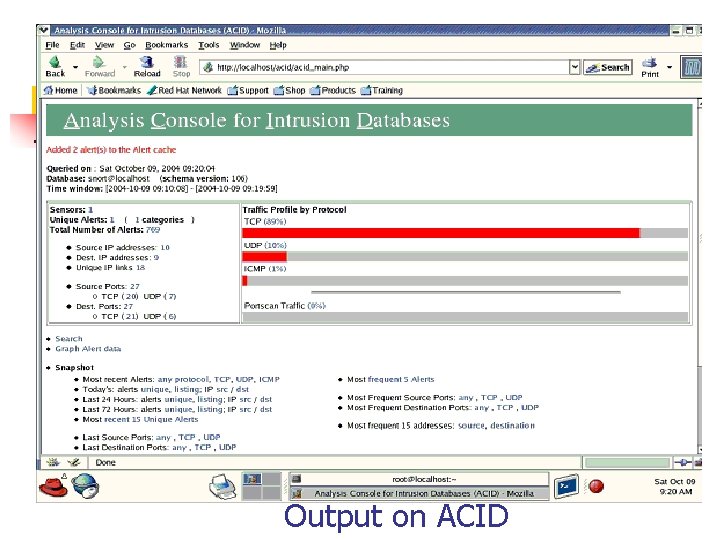
Output on ACID
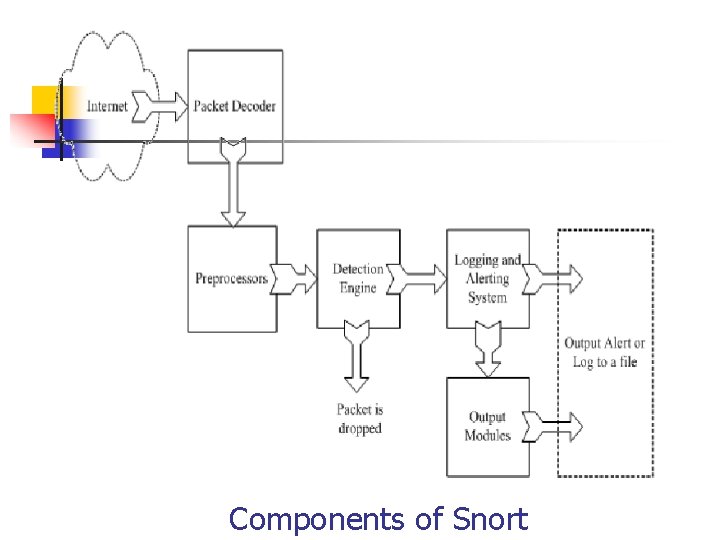
Components of Snort A Snort-based IDS contains the following components: n Packet Decoder n Preprocessors n Detection Engine n Logging and Alerting System n Output Modules
Packet Detector n n n Takes packets from different types of network interfaces Send the packets to the preprocessor Send the packets to the detection engine
Preprocessor Hackers use different techniques to fool an IDS n Exact match: You created a rule to find a signature “httpd/conf” in HTTP packets, a hacker can easily fool you by modifying the string as “httpd/. /conf” or “httpd. . /httpd/conf”. A preprocessor can rearrange the string so that it is detectable by the IDS. n Packets fragmentation: Hackers can use fragmentation to hide a signature into several small units to fool the IDS. A Preprocessor can reassemble these small units first and send the whole packet to the detection engine for signature testing.
The Detection Engine n n Its responsibility is to detect if any intrusion activity exists in a packet. It can dissert a packet and apply rules on different parts of the packet. n n The IP header of the packet The Transport layer header: e. g. TCP, UDP. The application layer level header: e. g. DNS, FTP, SNMP, and SMTP Packet payload: you can create a rule to find a string inside the data.
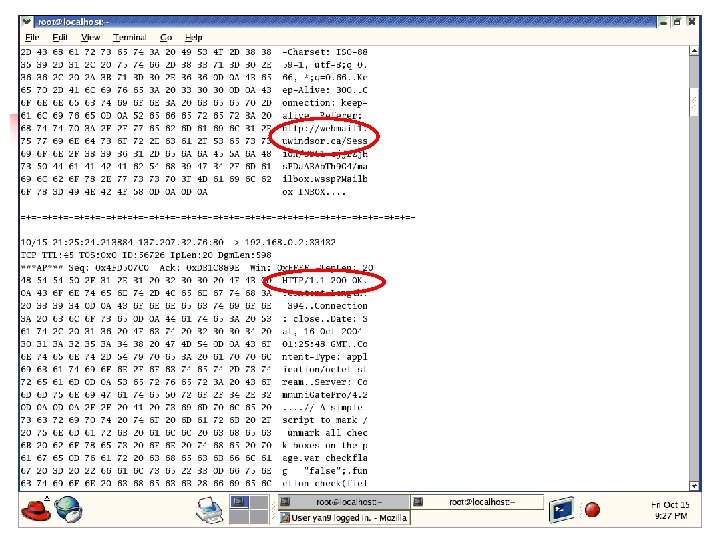
Logging and Alerting System n n The captured packet may be used to log the activity or generate an alert. Logs are kept in n n simple text files tcpdump-style files some other form log files are stored under /var/log/snort folder by default use –l parameter to modify the log location
Output Modules Depending on the configuration, output modules can do things like the following: n n n n Simply logging to /var/log/snort/alerts file Sending SNMP traps Sending messages to syslog facility Logging to a database like My. SQL or Oracle. Generating XML output Modifying configuration on routers and firewalls Sending Server Message Block (SMB) messages to Microsoft Windows-based machines
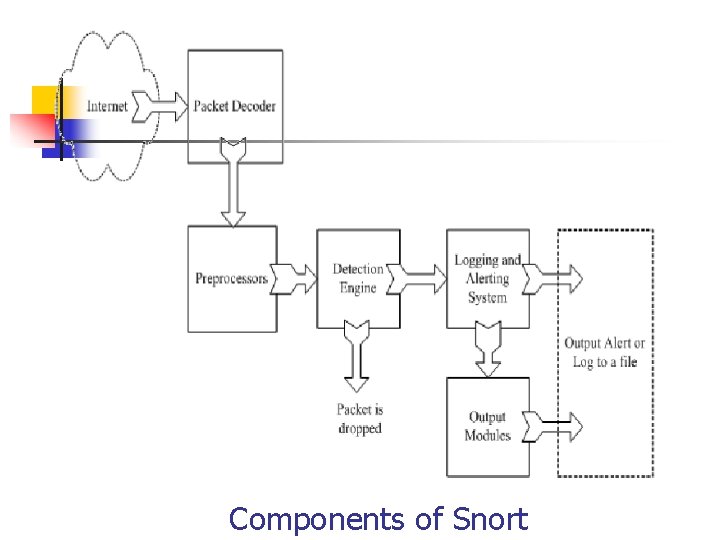
Components of Snort
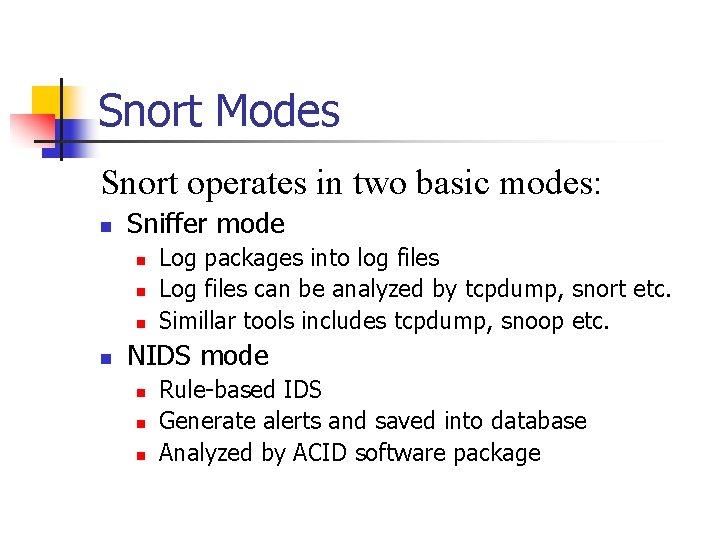
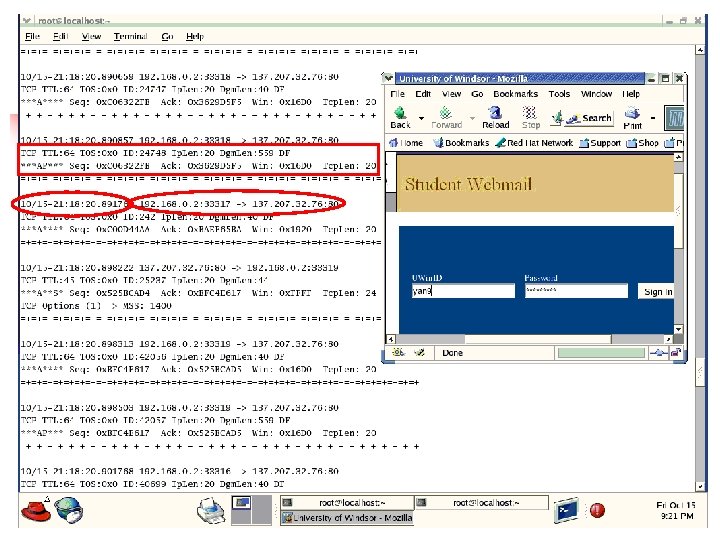
Snort Modes Snort operates in two basic modes: n Sniffer mode n n Log packages into log files Log files can be analyzed by tcpdump, snort etc. Simillar tools includes tcpdump, snoop etc. NIDS mode n n n Rule-based IDS Generate alerts and saved into database Analyzed by ACID software package
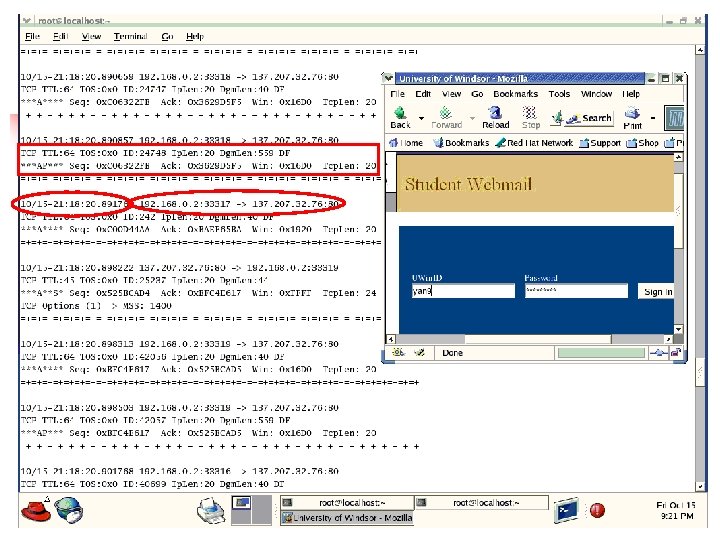
Sniffing Mode #> snort -v
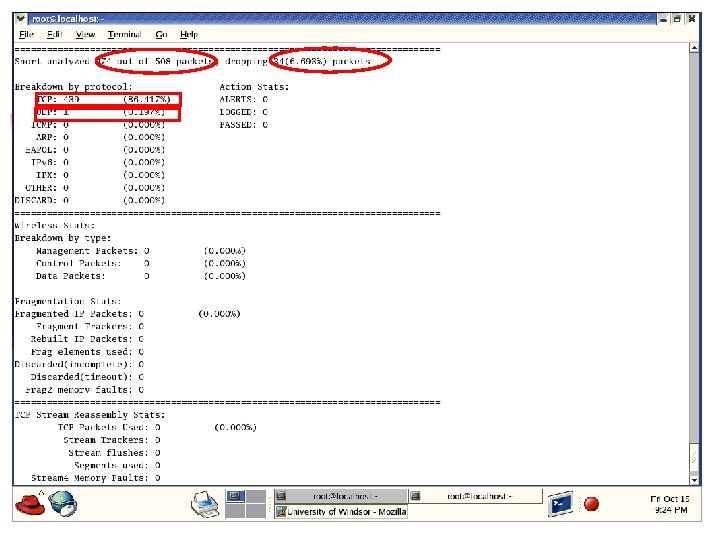
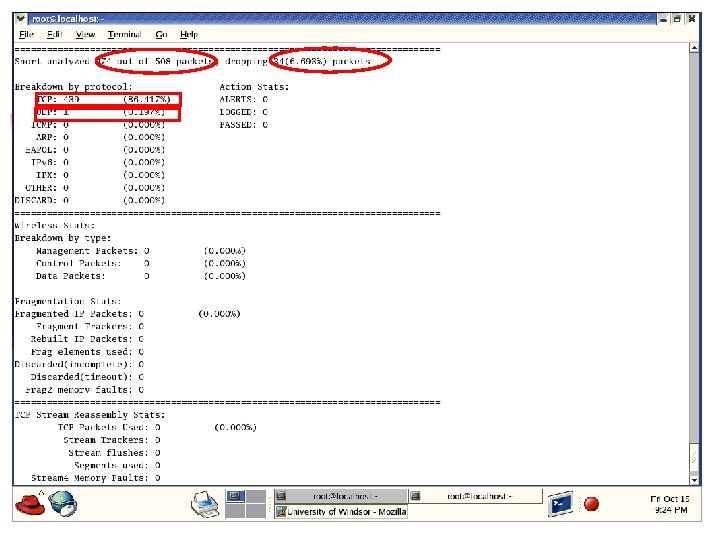
Sniffing Mode (Cont. ) Ctrl+C, generate statistics before exiting Snort
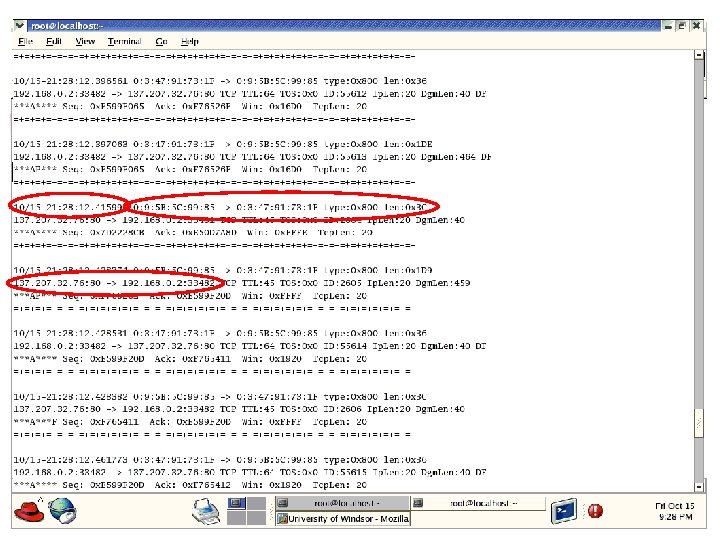
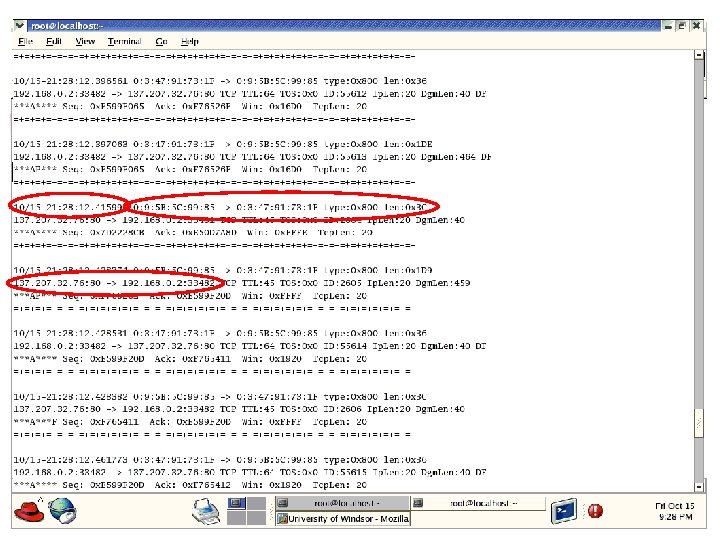
Sniffing Mode (Cont. ) Parameter e allows Snort to capture layer 2 packets #> snort -ve
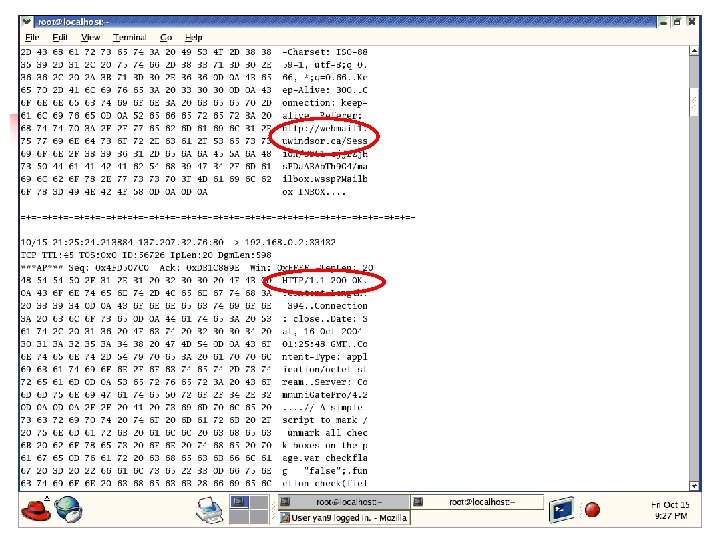
Sniffing Mode (Cont. ) Parameter d allows Snort to capture payload information #> snort -vd
Network Intrusion Detection Mode n n n It does not log each captured packet It applies rules on all captured packets It read the configuration file snort. conf and all other files included in it before start
Structure of A Rule A Snort rule is divided into two parts: n rule header n n n information about what action a rule takes criteria for matching a rule against data packets rule options