Intrusion Detection and Prevention Objectives Purpose of IDSs
Intrusion Detection and Prevention
Objectives ● Purpose of IDS's ● Function of IDS's in a secure network design ● Install and use an IDS ● Customize the IDS signature database
IDS What are they? ● Dedicated hardened host ● Sensors ● Sits on a network that you want to protect ● Network sniffer ● Packet pattern analyzer ● Unlike firewalls an IDS is passive (this is changing) ● They are often on each layer of your layered network
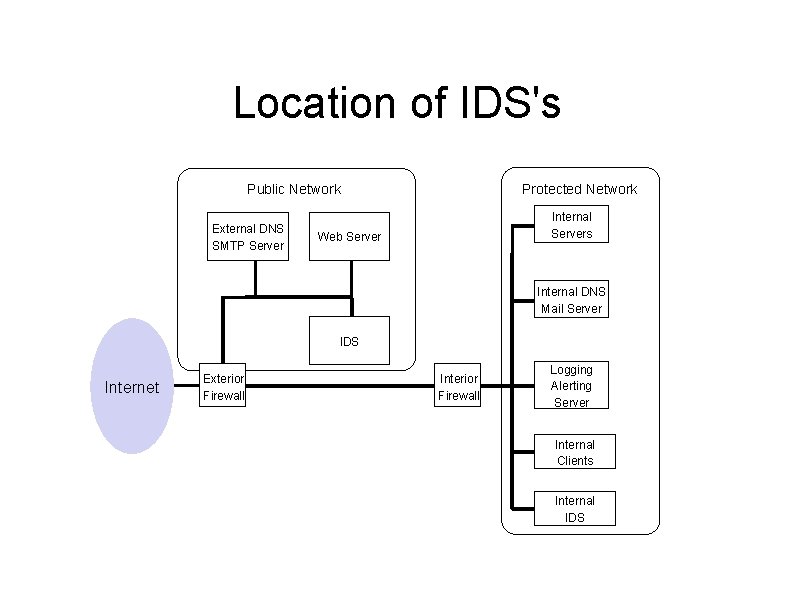
Location of IDS's Public Network External DNS SMTP Server Protected Network Internal Servers Web Server Internal DNS Mail Server IDS Internet Exterior Firewall Interior Firewall Logging Alerting Server Internal Clients Internal IDS
IDS The Need ● Detection of probes, scans ● Detection of network reconnaissance activity ● Record of attempted exploits ● Location of a compromised host on your network ● Determined compromised information
The Attack Plan ● Usually multiphased ● ● Phase 1: Network scan ● Characterizing the hosts on the network ● Looking for particular services, e. g DNS, HTTP ● Determining the versions and OS types Phase 2: Exploits a buffer overflow in DNS ● ● ● Compromises the DNS host Phase 3: Compromises other hosts on the network Without IDS you would not know
Protection Plan ● Analyze all packets continuously ● Look for patterns of known attacks ● Network IDS Signatures ● The science behind IDS ● Like virus signatures IDS signatures must be updated ● Do it your self signature writing ● ● Sometime necessary Look for statistical anomalies ● Not a very well developed science as yet
Land Attack 1997 ● Based on hand crafted packets ● Source IP and destination IP addresses are the same ● Older systems would crash ● NT & 95 depended on proper packets ● Basically a denial of service attack ● www. kb. cert. org/vuls/id/396645
Teardrop Attack 1997 – 1998 ● ● Improper packet sequence ● The IP fragment offset is malformed ● Consecutive packets overlap ● Newtear. c (on web site) Another Do. S attack
Teardrop cont'd ● Packet 1 ● Total length of IP datagram ● 48 bytes ● More fragments flag is set ● Fragment offset is 0 ● UDP length ● 48 bytes – incorrect length should be length – 20 = 28
Teardrop cont'd ● Packet 2 ● Total length of IP datagram ● 24 bytes ● Fragment offset is 3 (* 8 bytes) ● More fragments bit is cleared ● 24 bytes are sent
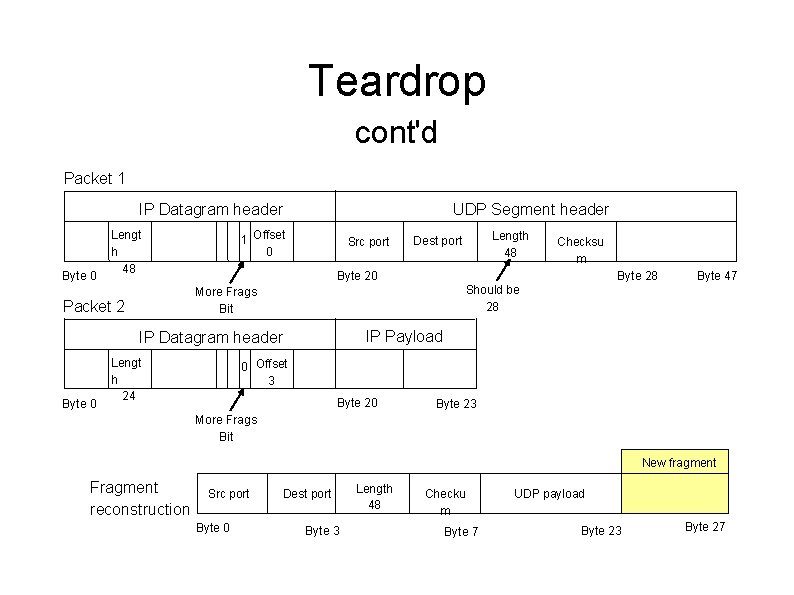
Teardrop cont'd Packet 1 IP Datagram header Byte 0 UDP Segment header 1 Offset 0 Lengt h 48 Src port Byte 28 Lengt h 24 Byte 47 Should be 28 IP Payload IP Datagram header Byte 0 Checksu m Byte 20 More Frags Bit Packet 2 Length 48 Dest port 0 Offset 3 Byte 20 Byte 23 More Frags Bit New fragment Fragment reconstruction Src port Byte 0 Dest port Byte 3 Length 48 Checku m Byte 7 UDP payload Byte 23 Byte 27
nimda worm 2001 ● ● Scan phase ● Determine if a web server is an unpatched MS IIS box ● Is it vulnerable to a Unicode-related exploit? Attack phase ● Exploit a buffer overflow
nimda worm cont'd ● ● IDS can detect the scan phase of nimda attack ● “%c 0%af. . /winnt/etc” is contained in the URL ● %c 0%af is the Unicode of a slash ● Most web servers scan for a “/”stuff indicating a cd to root Success of this attempt to change to the root directory indicates an unpatched IIS
nimda worm cont'd ● ● IDS rule ● /scripts/. . %c 0%af. . /winnt/system 32/cmd. exe? /c+dir ● Specific text search for %c 0%af ● Attack may change and this rule would not catch it Better approach ● Convert %c 0%af to “/” and then check for validity of URL ● More robust
False +/● ● ● False positives ● Classifying benign activity as malicious ● Get a lot of attention since people see the alerts ● Annoying, usually the rule gets shut off entirely False negatives ● Missing a malicious activity ● Not seen and ignored ● Dangerous The risks in classification
IDS Evasion Techniques ● The attacker is patient ● The attacker is clever ● The attacker has nothing else to do ● Examples ● cmd. exe in the URL is often bad ● However cmd. exe-analysis. html may be OK ● cmd. %65 xe is the same thing ● Text searches are not always good or effective
IDS Software ● ● Popular systems ● Snort – open source ● Cisco recommends using snort ● ISS Real. Secure ● NFR Security NID Centralizing all IDS logs ● Easier analysis ● Alerts – logs, e-mails, pagers, etc.
Distributed IDS ● IDS logs submitted to third party for collective analysis ● Attack Registry &Intelligence Service ● ● http: //aris. securityfocus. com/ Dshield ● http: //www. dshield. org/
Outsourced IDS ● Counterpane ● Trusecure ● Deloitte & Touche
- Slides: 20