Introduction to Sensor Networks Rabie A Ramadan Ph
Introduction to Sensor Networks Rabie A. Ramadan, Ph. D Cairo University http: //rabieramadan. org rabie@rabieramadan. org 3
Virtual grid architecture routing l l l Utilizes data aggregation and in-network processing to maximize the network lifetime Inside each zone, a node is optimally selected to act as CH. Data aggregation is performed at two levels: • • l Local: the set of CHs performing local aggregation Global: the selection of global aggregation points is NP-hard Strategies for the selection of MAs: • • Exact alg: ILP Approximate algs: genetics-based, kmeans, greedy-based
Localization Techniques in WSNs 3
Why do I need localization ? l In sensor networks, nodes are deployed without priori knowledge about their locations. l Estimating spatial-coordinates of the node is referred to as localization. 4
Localization GPS l Global Positioning System (GPS) is an immediate solution. l There some factors against the usage of GPS: • GPS can work only outdoors. • GPS receivers are too expensive to unsuitable for • wide-range deployment. It cannot work in the presence of obstructions.
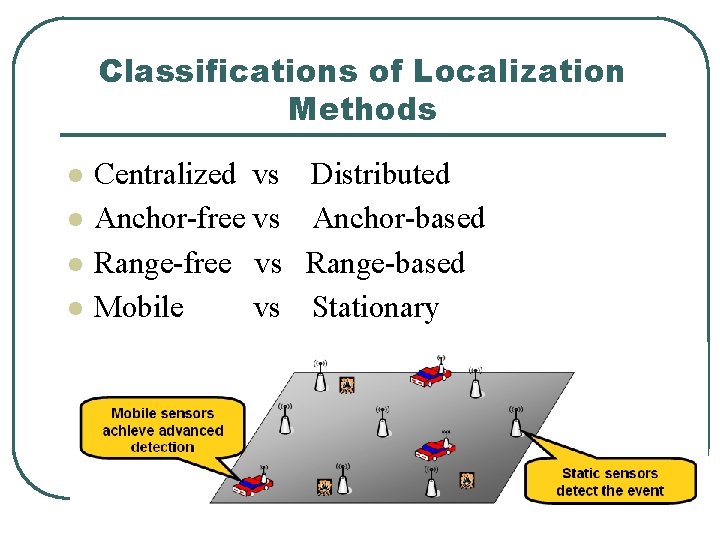
Classifications of Localization Methods l l Centralized vs Anchor-free vs Range-free vs Mobile vs Distributed Anchor-based Range-based Stationary
Centralized versus Distributed Localization Algorithms l l In centralized algorithms, • nodes send data to a central location where computation is performed and the location of each node is determined and sent back to the nodes. Drawbacks • high communication costs • intrinsic delay 7
Centralized versus Distributed Localization Algorithms l In distributed algorithms, • • l each node determines its location by communication with its neighboring nodes robust and energy efficient Drawback • Can be more complex to implement • At times may not be possible due to the limited computational capabilities of sensor nodes 8
Anchor-Free vs Anchor-Based l l l Anchor Nodes: • • • Nodes that know their coordinates a priori By use of GPS or manual placement For 2 D three and 3 D four anchor nodes are needed Anchor-free • Relative coordinates Anchor-based • Use anchor nodes to calculate global coordinates
Range-Free vs Range-Based l Range-Free • • • l Range-free techniques use connectivity information between neighboring nodes to estimate the nodes‟ position Local Techniques Hop-Counting Techniques Range-Based • Received Signal Strength Indicator (RSSI) • • Time of Arrival (To. A) • Angle of Arrival (Ao. A) • • Attenuation RF signal • time of flight • • • requires time synchronization electromagnetic (light, RF, microwave) sound (acoustic, ultrasound) • RF signal Time Difference of Arrival (TDo. A)
Range-Based Techniques l Time of Arrival • All sensors transmit a signal with a predefined • • velocity to their neighbors. Then, the nodes each send a signal back to their neighbors by using the transmission and received times each node estimates its distance to its neighbor 11
Range-Based Techniques l Received Signal Strength Indicator (RSSI) • The amount of power present in a received radio • • signal. Due to radio-propagation pathloss, received signal strength (RSS) decreases as the distance of the radio propagation increases. The distance between two sensor nodes can be compared using the RSS value at the receiver, assuming that the transmission power at the sender is either fixed or known 12
Range-Based Techniques l TDOA (Time Difference of Arrival) • Transmit both radio and ultrasonic signals at the same time to observe the arrival time difference. • Extra hardware, i. e. , ultrasonic channel, is required • Not only radio but also sound signals have multipath effects affected by humidity, temperature, … 13
Range-Based Techniques l Angle of Arrival (Ao. A) • Gather data using either radio or microphone arrays. • Allow a receiving node determines the direction of a • • • transmitting node. A single transmitted signal is heard by several spatially separated microphones. The phase or time difference between the signal‟s arrival at different microphones is calculated and thus the Ao. A of the signal is found. Requires directional antennae 14
Anchor‐Based versus Anchor‐Free Localization Techniques l Anchor-based methods l Anchor-free methods. • Anchor nodes have GPS; • Other nodes derive their locations by trilateration. • Connectivity only; • Distance estimation for all communication links. • Node locations that reflect the position of the sensor nodes relative to each other 15
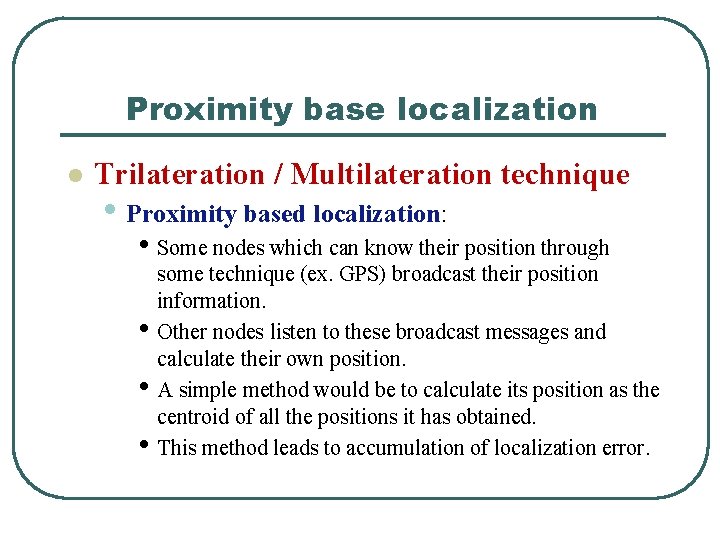
Proximity base localization l Trilateration / Multilateration technique • Proximity based localization: • Some nodes which can know their position through some technique (ex. GPS) broadcast their position information. • Other nodes listen to these broadcast messages and calculate their own position. • A simple method would be to calculate its position as the centroid of all the positions it has obtained. • This method leads to accumulation of localization error.
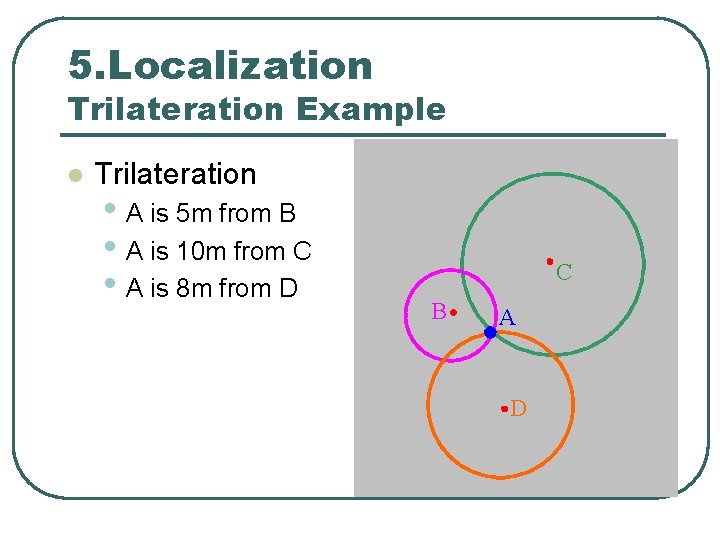
5. Localization Trilateration Example l Trilateration • A is 5 m from B • A is 10 m from C • A is 8 m from D C B A D
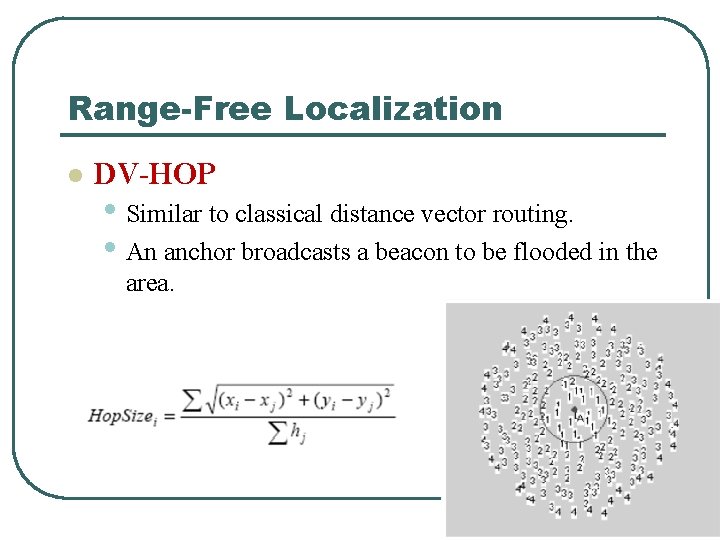
Range-Free Localization l DV-HOP • Similar to classical distance vector routing. • An anchor broadcasts a beacon to be flooded in the area.
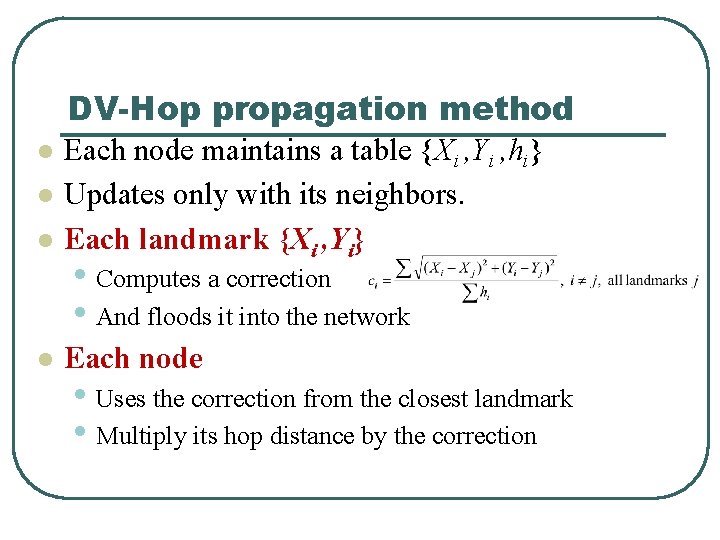
DV-Hop propagation method l Each node maintains a table {Xi , Yi , hi} Updates only with its neighbors. Each landmark {Xi , Yi} l Each node l l • Computes a correction • And floods it into the network • Uses the correction from the closest landmark • Multiply its hop distance by the correction
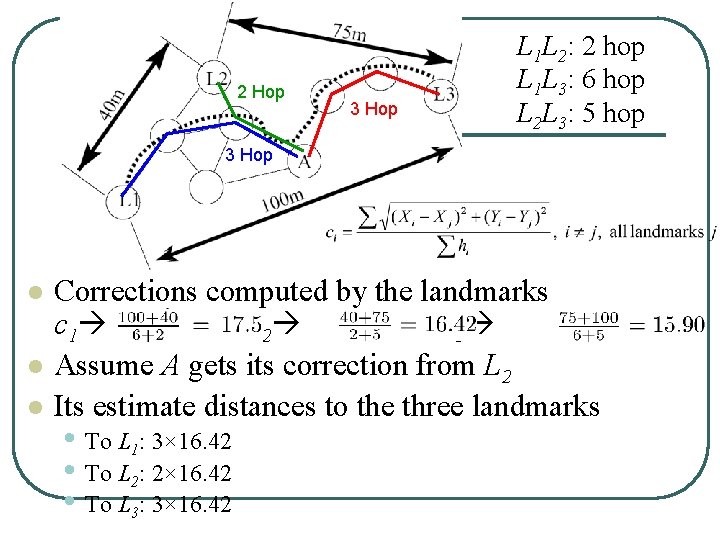
2 Hop 3 Hop L 1 L 2: 2 hop L 1 L 3: 6 hop L 2 L 3: 5 hop 3 Hop l l l Corrections computed by the landmarks c 1 c 2 c 3 Assume A gets its correction from L 2 Its estimate distances to the three landmarks • To L 1: 3× 16. 42 • To L 2: 2× 16. 42 • To L 3: 3× 16. 42
Range-Free Localization l DV-hop • Advantages • Simplicity • Dose not depend on measurement error • Disadvantage • Only work for isotropic networks
APIT Overview l Anchors • Nodes equipped with high • l powered transmitter Location information obtained from GPS or other mechanism Location estimation by isolating the environment into triangular regions between anchors

Location verification – Ser. Loc (Secure Range-independent localization) 23
What is location verification? l Different assumptions from general localization • What if some malicious nodes lie about their location? • Sample attack scenario • Claim to be very close to the sink • Attract many packets • Drop some or all of them • Very easy Do. S attack especially for geographic routing protocols
![Secure Location Services • Secure Verification of Location Claims [Sastry et al. WISE 2002]. Secure Location Services • Secure Verification of Location Claims [Sastry et al. WISE 2002].](http://slidetodoc.com/presentation_image/5d262e003eeb9fbf47538da2c2551cf1/image-25.jpg)
Secure Location Services • Secure Verification of Location Claims [Sastry et al. WISE 2002]. • Location Privacy-aware Location Sensor Networks [Gruteser et al. USENIX 2003]. • Secure Localization: Ensure robust location estimation even in the presence of adversaries. Se. RLoc: [Lazos and Poovendran, WISE 2004]. S-GPS: [Kuhn 2004]. SPINE: [Capkun & Hubeaux, Infocom 2005]. 25
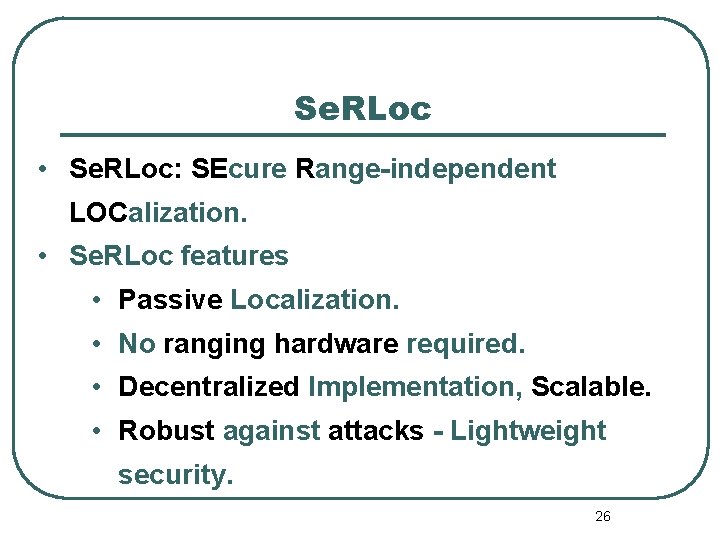
Se. RLoc • Se. RLoc: SEcure Range-independent LOCalization. • Se. RLoc features • Passive Localization. • No ranging hardware required. • Decentralized Implementation, Scalable. • Robust against attacks - Lightweight security. 26
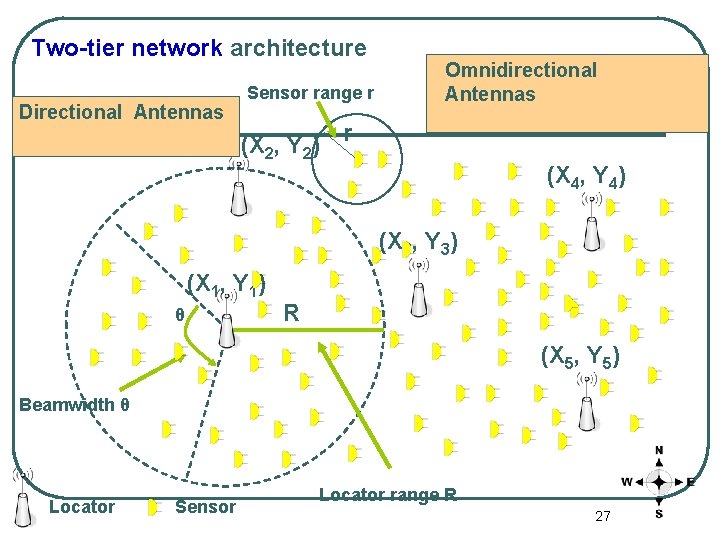
Two-tier network architecture Locators: Randomly Directional Known Location, Antennas deployed Orientation Sensor range r (X 2, Y 2) r Omnidirectional Sensors: Randomly Antennas deployed, unknown location (X 4, Y 4) (X 3, Y 3) (X 1, Y 1) θ R (X 5, Y 5) Beamwidth θ Locator Sensor Locator range R 27
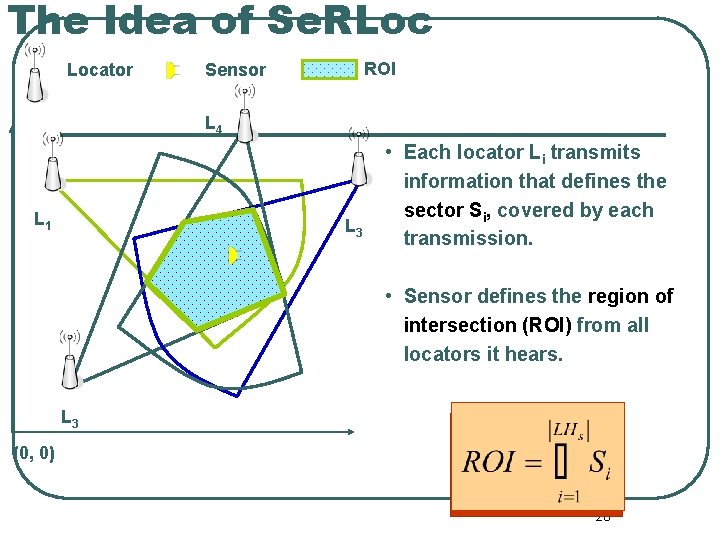
The Idea of Se. RLoc Locator ROI Sensor L 4 L 1 L 3 • Each locator Li transmits information that defines the sector Si, covered by each transmission. s • Sensor defines the region of intersection (ROI) from all locators it hears. L 3 (0, 0) 28
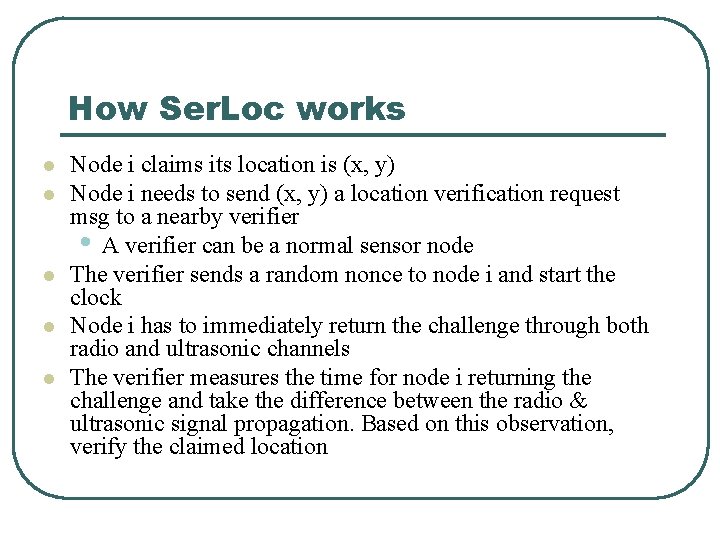
How Ser. Loc works l l l Node i claims its location is (x, y) Node i needs to send (x, y) a location verification request msg to a nearby verifier • A verifier can be a normal sensor node The verifier sends a random nonce to node i and start the clock Node i has to immediately return the challenge through both radio and ultrasonic channels The verifier measures the time for node i returning the challenge and take the difference between the radio & ultrasonic signal propagation. Based on this observation, verify the claimed location
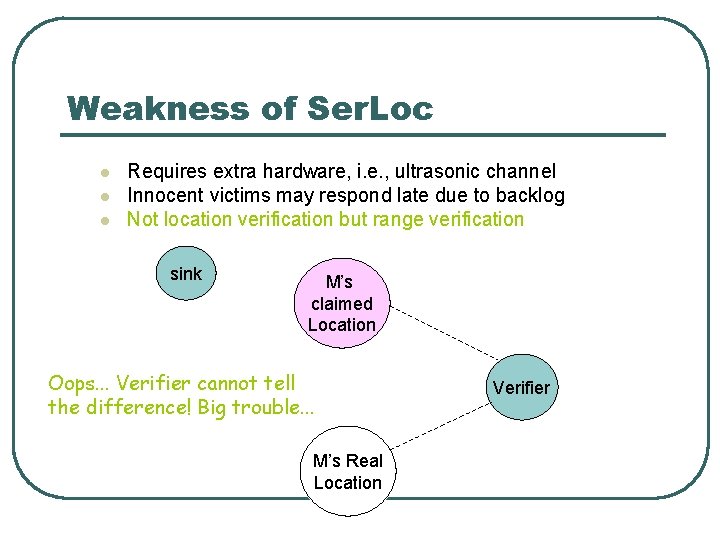
Weakness of Ser. Loc l l l Requires extra hardware, i. e. , ultrasonic channel Innocent victims may respond late due to backlog Not location verification but range verification sink M’s claimed Location Oops. . . Verifier cannot tell the difference! Big trouble. . . M’s Real Location Verifier
Possible Research Issues l Most localization work is mathematical and evaluated via (high level) simulations • More realistic work is needed l Indoor localization is harder l Location verification l Secure localization • Look at Code. Blue project at Harvard • Can’t trust sensors • Can’t trust anchors
Next time Security in WSN 32
- Slides: 32