Introduction to PKI Certificates Public Key Cryptography Erwan
Introduction to PKI, Certificates & Public Key Cryptography Erwan Lemonnier
Introduction to PKI, Certificates & Public Key Cryptography – erwan@defcom. com Role of Computer Security CIA • Confidentiality: protection against data disclosure • Integrity: protection against data modification • Availability: protection against data disponibility Identification & Authentication (I&A) Provide a way of identifying entities, and controlling this identity Non-repudiability Bind an entity to its actions
Introduction to PKI, Certificates & Public Key Cryptography – erwan@defcom. com How to implement CIA, I&A, N-R ? With Cryptography ! Main cryptographic tools: • Hash Functions • Secret Key Cryptography • Public Key Cryptography And their combinations: • Certificates • PKI
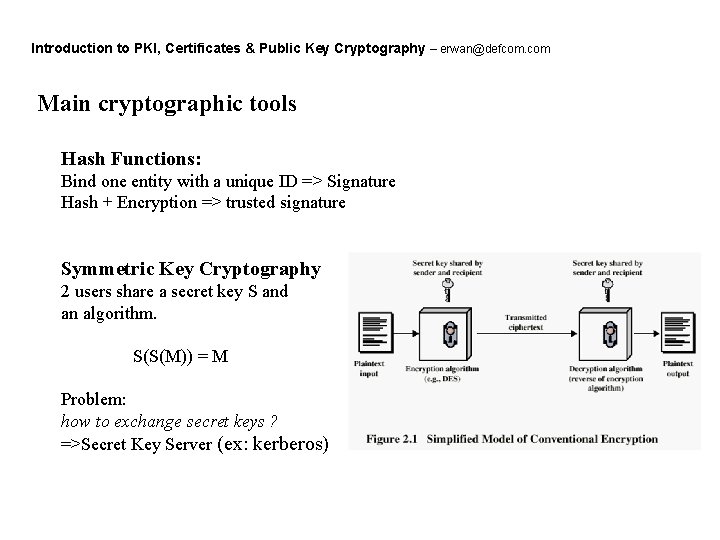
Introduction to PKI, Certificates & Public Key Cryptography – erwan@defcom. com Main cryptographic tools Hash Functions: Bind one entity with a unique ID => Signature Hash + Encryption => trusted signature Symmetric Key Cryptography 2 users share a secret key S and an algorithm. S(S(M)) = M Problem: how to exchange secret keys ? =>Secret Key Server (ex: kerberos)
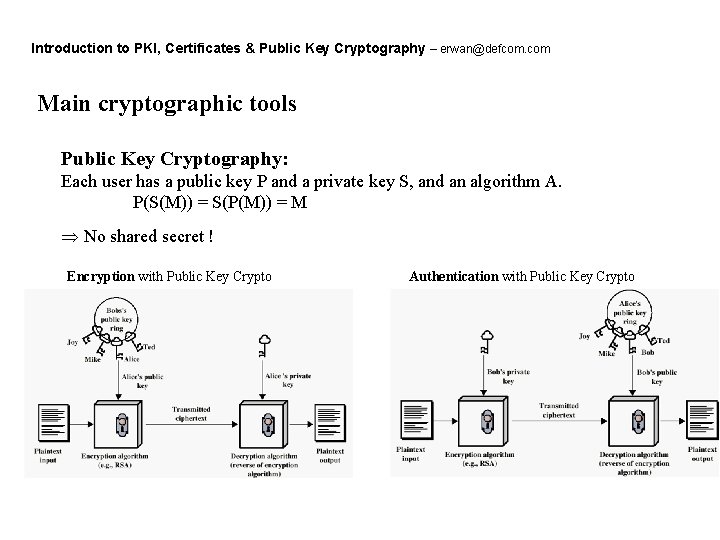
Introduction to PKI, Certificates & Public Key Cryptography – erwan@defcom. com Main cryptographic tools Public Key Cryptography: Each user has a public key P and a private key S, and an algorithm A. P(S(M)) = S(P(M)) = M Þ No shared secret ! Encryption with Public Key Crypto Authentication with Public Key Crypto
Introduction to PKI, Certificates & Public Key Cryptography – erwan@defcom. com Main cryptographic tools, PKI How to distribute public keys ? Þ Public Key Server (PKS), key exchange protocols Public Key Infrastructure (PKI): PKI = N x (Entities with private keys) + public key exchange system REM: Public Key algorithms are slow Þ Need to use both Public & Secret Key Cryptography Þ Public Key Protocols work in 3 phases 1. Authentication via Public Key Cryptography (challenge) 2. Exchange of a session Secret Key, encrypted with Public Key Crypto 3. Session encrypted with Symmetric Cryptography
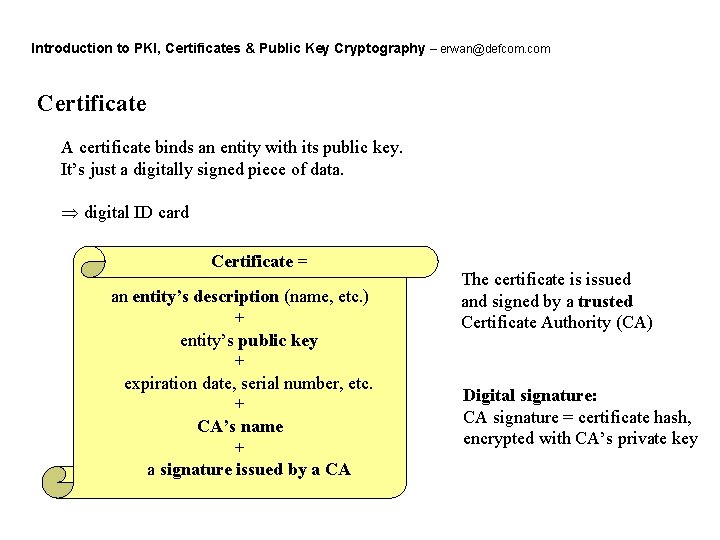
Introduction to PKI, Certificates & Public Key Cryptography – erwan@defcom. com Certificate A certificate binds an entity with its public key. It’s just a digitally signed piece of data. Þ digital ID card Certificate = an entity’s description (name, etc. ) + entity’s public key + expiration date, serial number, etc. + CA’s name + a signature issued by a CA The certificate is issued and signed by a trusted Certificate Authority (CA) Digital signature: CA signature = certificate hash, encrypted with CA’s private key
Introduction to PKI, Certificates & Public Key Cryptography – erwan@defcom. com Certificate The certificate’s CA is the only entity able to create/modify the certificate Þ the CA has to be trusted Certificates enable: • Clients to authenticate servers • Servers to authenticate clients • Public key exchange without Public Key Server Þ No disclosure of private/secret keys. Certificates are usually stored encrypted. Special features: • chains of CAs, to distribute the task of issuing Certificates • Certificate Revocation List, to disable certificates
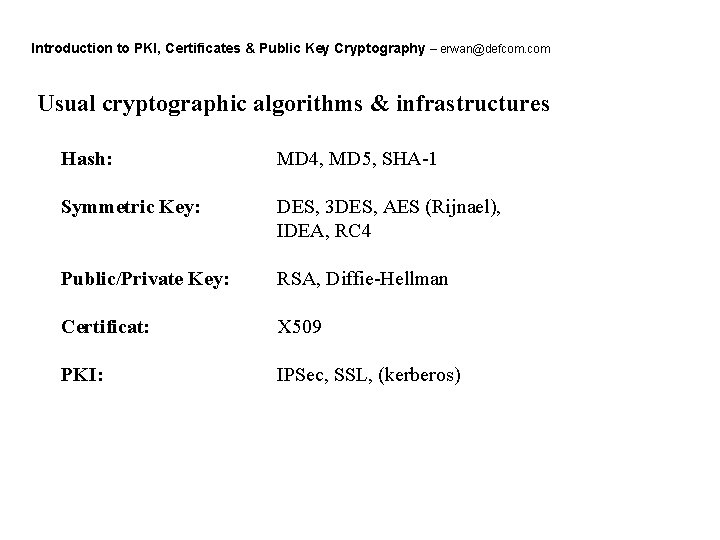
Introduction to PKI, Certificates & Public Key Cryptography – erwan@defcom. com Usual cryptographic algorithms & infrastructures Hash: MD 4, MD 5, SHA-1 Symmetric Key: DES, 3 DES, AES (Rijnael), IDEA, RC 4 Public/Private Key: RSA, Diffie-Hellman Certificat: X 509 PKI: IPSec, SSL, (kerberos)
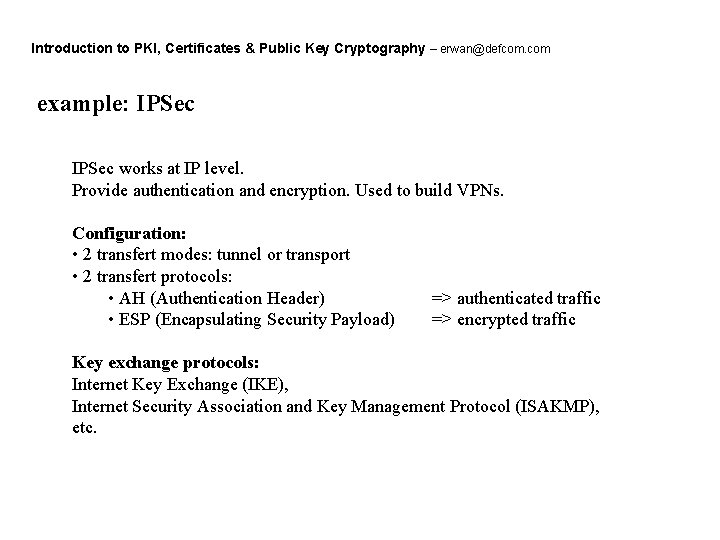
Introduction to PKI, Certificates & Public Key Cryptography – erwan@defcom. com example: IPSec works at IP level. Provide authentication and encryption. Used to build VPNs. Configuration: • 2 transfert modes: tunnel or transport • 2 transfert protocols: • AH (Authentication Header) • ESP (Encapsulating Security Payload) => authenticated traffic => encrypted traffic Key exchange protocols: Internet Key Exchange (IKE), Internet Security Association and Key Management Protocol (ISAKMP), etc.
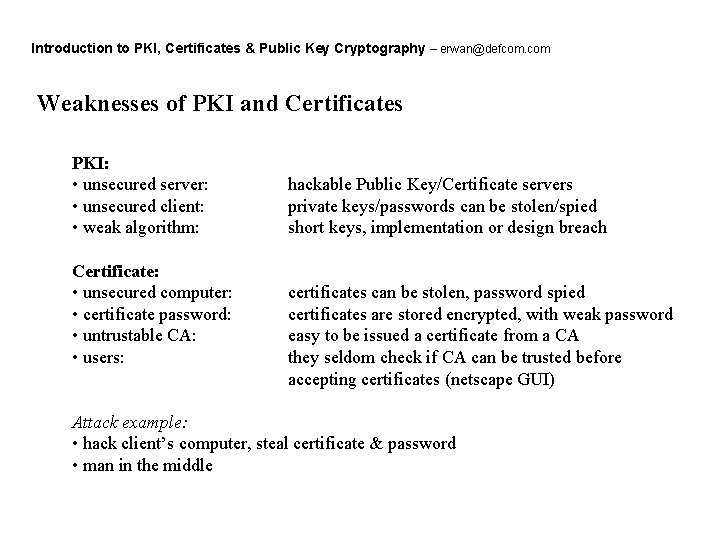
Introduction to PKI, Certificates & Public Key Cryptography – erwan@defcom. com Weaknesses of PKI and Certificates PKI: • unsecured server: • unsecured client: • weak algorithm: Certificate: • unsecured computer: • certificate password: • untrustable CA: • users: hackable Public Key/Certificate servers private keys/passwords can be stolen/spied short keys, implementation or design breach certificates can be stolen, password spied certificates are stored encrypted, with weak password easy to be issued a certificate from a CA they seldom check if CA can be trusted before accepting certificates (netscape GUI) Attack example: • hack client’s computer, steal certificate & password • man in the middle
Introduction to PKI, Certificates & Public Key Cryptography – erwan@defcom. com Links Book: Applied cryptography, Bruce Schneier URLs: theory. lcs. mit. edu/~rivest/crypto-security. html www. counterpane. com/pki-risks. html www. csc. gatech. edu/~copeland/8813/slides/ www. iplanet. com/developer/docs/articles/security/pki. html web. mit. edu/6. 857/Old. Stuff/Fall 96/www/main. html
- Slides: 12