Introduction to Network Programming in UNIX LINUX Daniel
- Slides: 58
Introduction to Network Programming in UNIX & LINUX © Daniel Zinchin Tel-Ran Ltd 2008 -2009 © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX
Instead of Preamble… בס"ד Rabbi Avraham Yaakov 100 years ago taught his Chassids: - It is possible to learn from anything. Everything in this world exists to edify us. Not only what the Lord has made, but also what people have made, makes us wise. - What, for example, do we learn from a railway? - one Chassid asked in doubt - That, having been late for an instant, it is possible to miss entirely. - And telegraph? - That each word is taken into account. - And phone? - That everything told by you here, is audible there. And what could we learn from the INTERNET ? © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 2
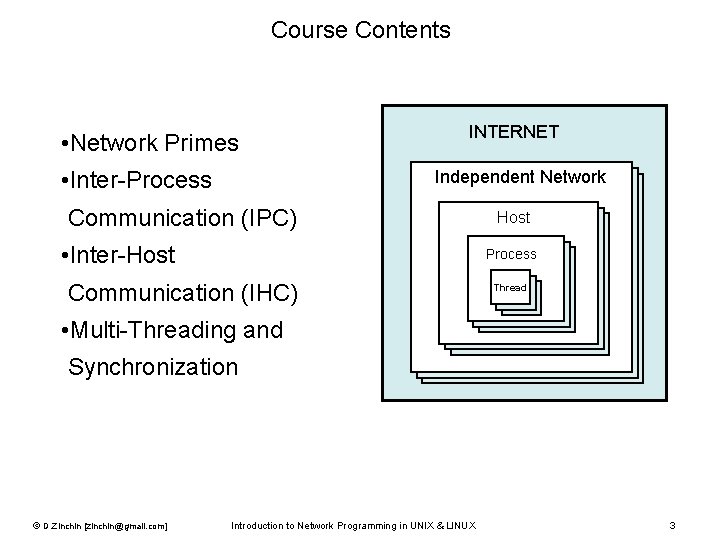
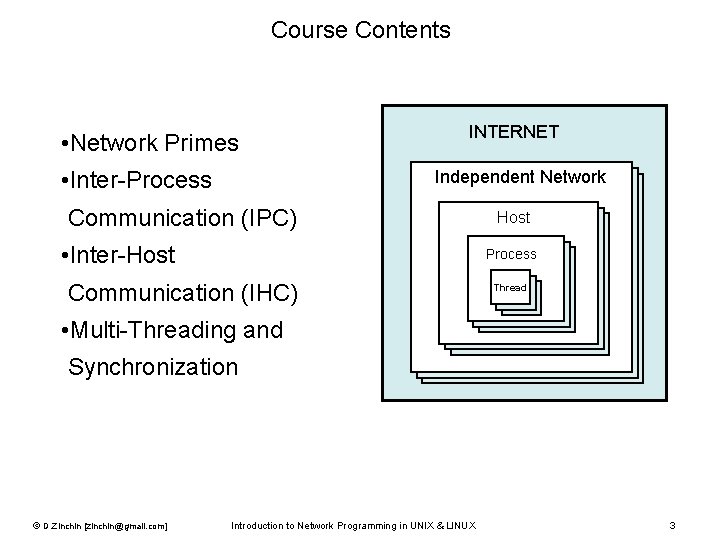
Course Contents • Network Primes • Inter-Process INTERNET Independent Network Communication (IPC) • Inter-Host Process Communication (IHC) Thread • Multi-Threading and Synchronization © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 3
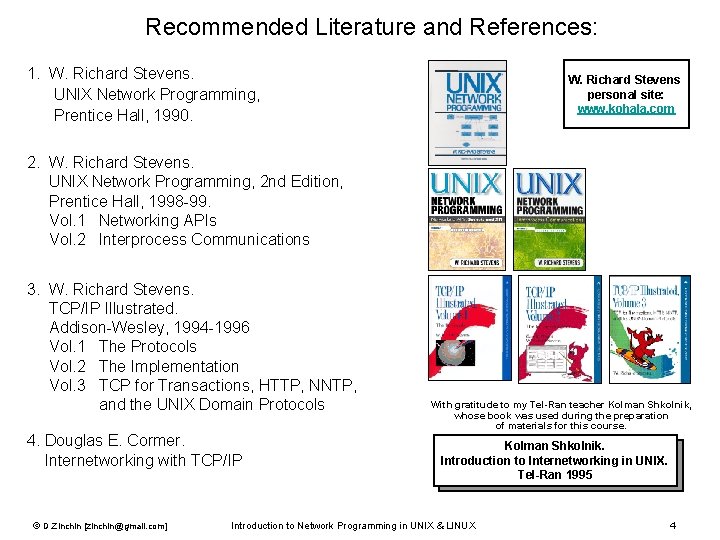
Recommended Literature and References: 1. W. Richard Stevens. UNIX Network Programming, Prentice Hall, 1990. W. Richard Stevens personal site: www. kohala. com 2. W. Richard Stevens. UNIX Network Programming, 2 nd Edition, Prentice Hall, 1998 -99. Vol. 1 Networking APIs Vol. 2 Interprocess Communications 3. W. Richard Stevens. TCP/IP Illustrated. Addison-Wesley, 1994 -1996 Vol. 1 The Protocols Vol. 2 The Implementation Vol. 3 TCP for Transactions, HTTP, NNTP, and the UNIX Domain Protocols 4. Douglas E. Cormer. Internetworking with TCP/IP © D. Zinchin [zinchin@gmail. com] With gratitude to my Tel-Ran teacher Kolman Shkolnik, whose book was used during the preparation of materials for this course. Kolman Shkolnik. Introduction to Internetworking in UNIX. Tel-Ran 1995 Introduction to Network Programming in UNIX & LINUX 4
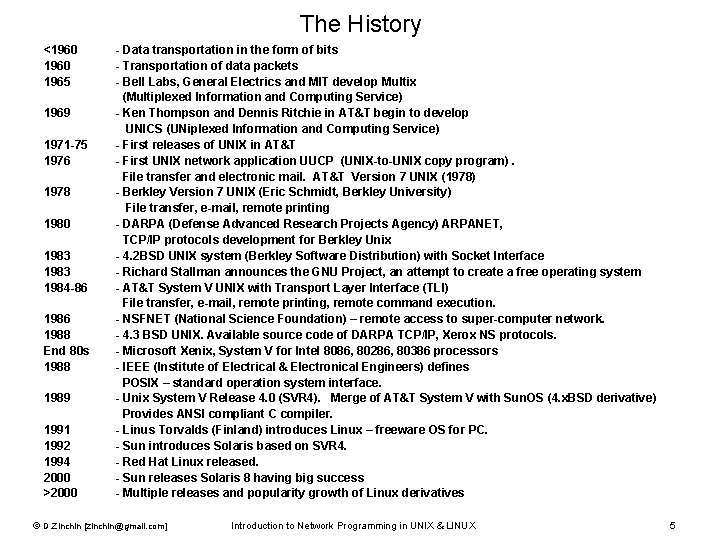
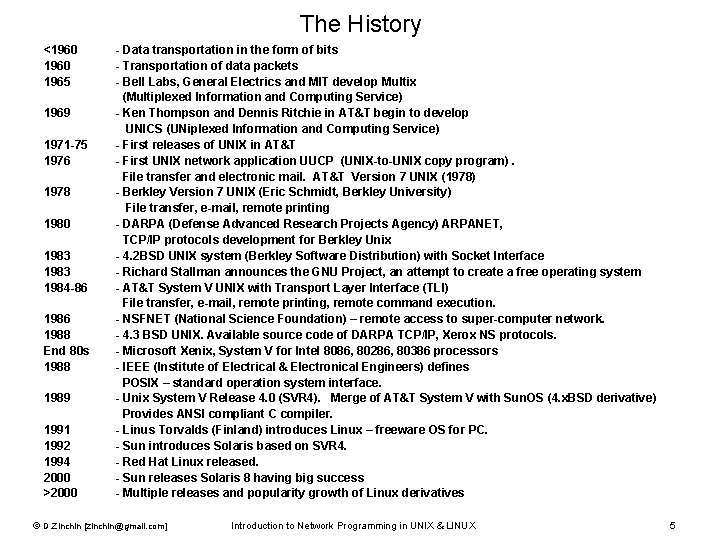
The History <1960 1965 1969 1971 -75 1976 1978 1980 1983 1984 -86 1988 End 80 s 1988 1989 1991 1992 1994 2000 >2000 - Data transportation in the form of bits - Transportation of data packets - Bell Labs, General Electrics and MIT develop Multix (Multiplexed Information and Computing Service) - Ken Thompson and Dennis Ritchie in AT&T begin to develop UNICS (UNiplexed Information and Computing Service) - First releases of UNIX in AT&T - First UNIX network application UUCP (UNIX-to-UNIX copy program). File transfer and electronic mail. AT&T Version 7 UNIX (1978) - Berkley Version 7 UNIX (Eric Schmidt, Berkley University) File transfer, e-mail, remote printing - DARPA (Defense Advanced Research Projects Agency) ARPANET, TCP/IP protocols development for Berkley Unix - 4. 2 BSD UNIX system (Berkley Software Distribution) with Socket Interface - Richard Stallman announces the GNU Project, an attempt to create a free operating system - AT&T System V UNIX with Transport Layer Interface (TLI) File transfer, e-mail, remote printing, remote command execution. - NSFNET (National Science Foundation) – remote access to super-computer network. - 4. 3 BSD UNIX. Available source code of DARPA TCP/IP, Xerox NS protocols. - Microsoft Xenix, System V for Intel 8086, 80286, 80386 processors - IEEE (Institute of Electrical & Electronical Engineers) defines POSIX – standard operation system interface. - Unix System V Release 4. 0 (SVR 4). Merge of AT&T System V with Sun. OS (4. x. BSD derivative) Provides ANSI compliant C compiler. - Linus Torvalds (Finland) introduces Linux – freeware OS for PC. - Sun introduces Solaris based on SVR 4. - Red Hat Linux released. - Sun releases Solaris 8 having big success - Multiple releases and popularity growth of Linux derivatives © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 5
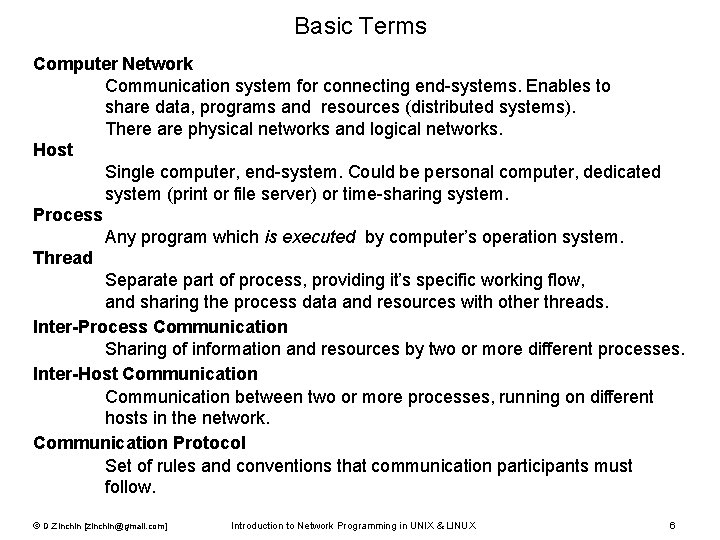
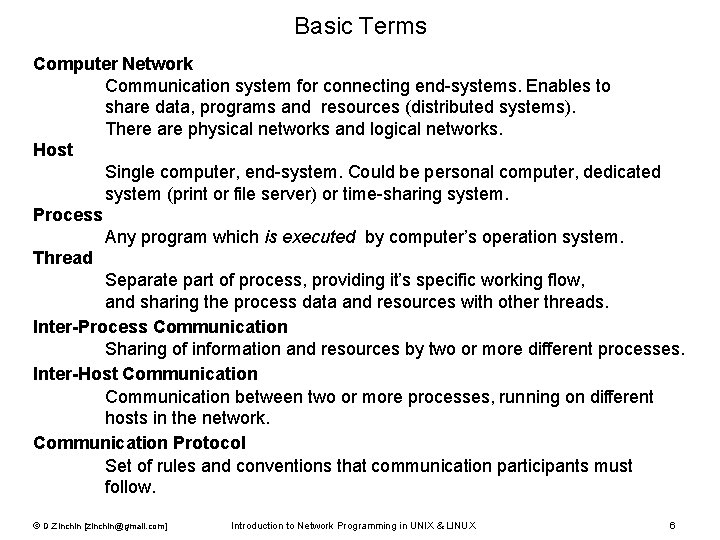
Basic Terms Computer Network Communication system for connecting end-systems. Enables to share data, programs and resources (distributed systems). There are physical networks and logical networks. Host Single computer, end-system. Could be personal computer, dedicated system (print or file server) or time-sharing system. Process Any program which is executed by computer’s operation system. Thread Separate part of process, providing it’s specific working flow, and sharing the process data and resources with other threads. Inter-Process Communication Sharing of information and resources by two or more different processes. Inter-Host Communication between two or more processes, running on different hosts in the network. Communication Protocol Set of rules and conventions that communication participants must follow. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 6
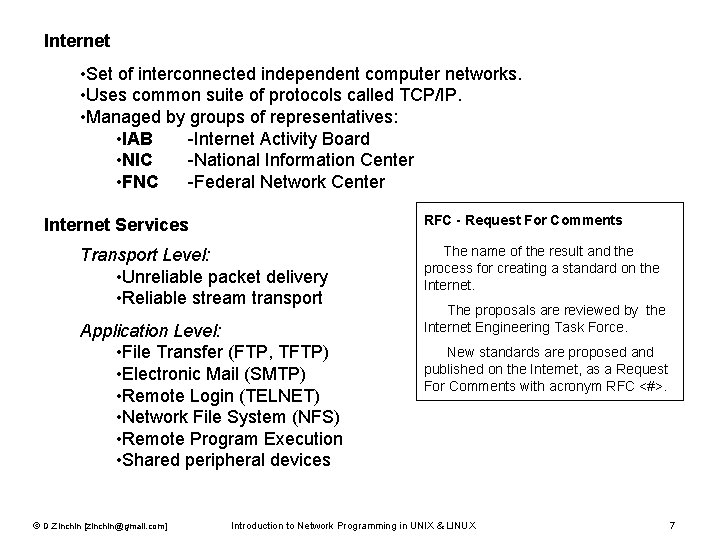
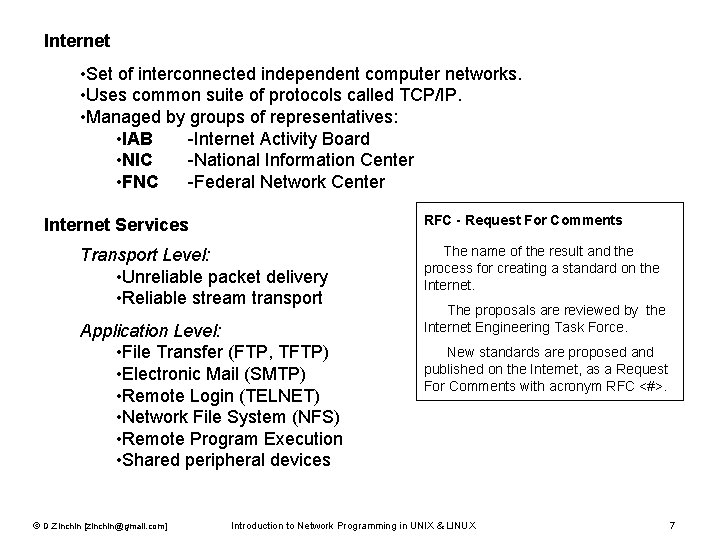
What is Internet • Set of interconnected independent computer networks. • Uses common suite of protocols called TCP/IP. • Managed by groups of representatives: • IAB -Internet Activity Board • NIC -National Information Center • FNC -Federal Network Center RFC - Request For Comments Internet Services Transport Level: • Unreliable packet delivery • Reliable stream transport Application Level: • File Transfer (FTP, TFTP) • Electronic Mail (SMTP) • Remote Login (TELNET) • Network File System (NFS) • Remote Program Execution • Shared peripheral devices © D. Zinchin [zinchin@gmail. com] The name of the result and the process for creating a standard on the Internet. The proposals are reviewed by the Internet Engineering Task Force. New standards are proposed and published on the Internet, as a Request For Comments with acronym RFC <#>. Introduction to Network Programming in UNIX & LINUX 7
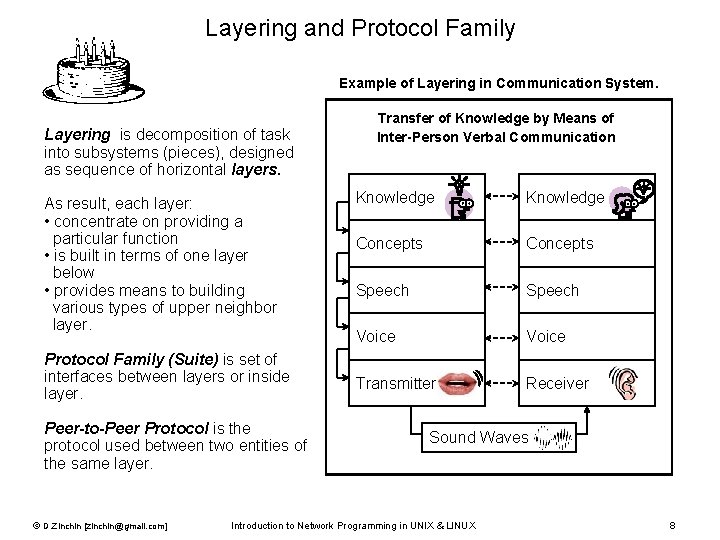
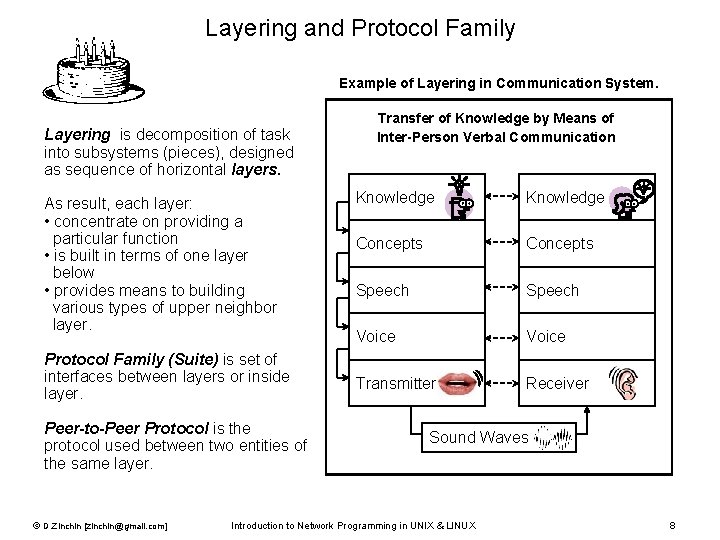
Layering and Protocol Family Example of Layering in Communication System. Layering is decomposition of task into subsystems (pieces), designed as sequence of horizontal layers. As result, each layer: • concentrate on providing a particular function • is built in terms of one layer below • provides means to building various types of upper neighbor layer. Protocol Family (Suite) is set of interfaces between layers or inside layer. Peer-to-Peer Protocol is the protocol used between two entities of the same layer. © D. Zinchin [zinchin@gmail. com] Transfer of Knowledge by Means of Inter-Person Verbal Communication Knowledge Concepts Speech Voice Transmitter Receiver Sound Waves Introduction to Network Programming in UNIX & LINUX 8
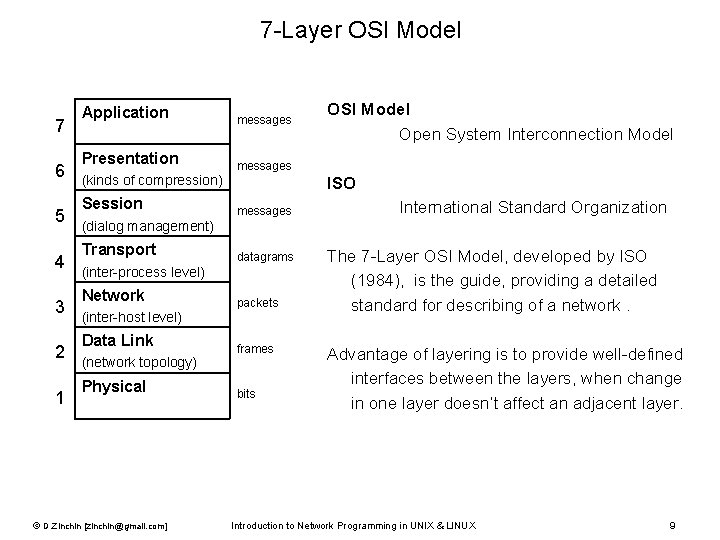
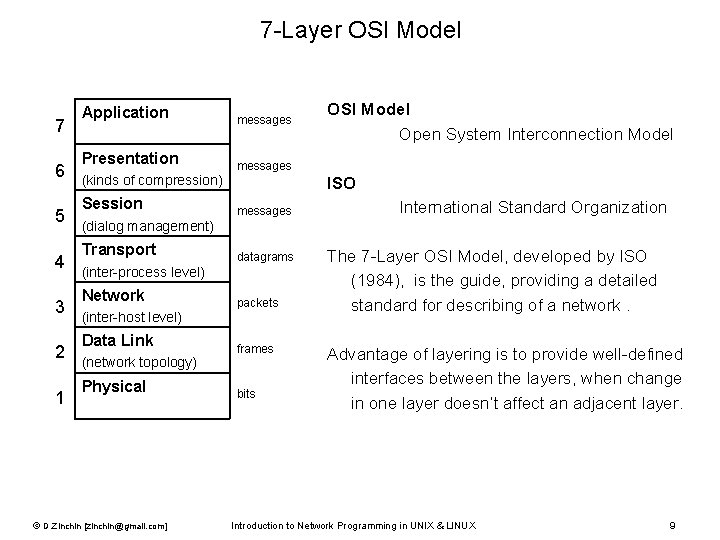
7 -Layer OSI Model 7 6 5 4 3 2 1 Application messages Presentation messages (kinds of compression) Session OSI Model Open System Interconnection Model ISO messages International Standard Organization (dialog management) Transport datagrams (inter-process level) Network packets (inter-host level) Data Link (network topology) Physical © D. Zinchin [zinchin@gmail. com] frames bits The 7 -Layer OSI Model, developed by ISO (1984), is the guide, providing a detailed standard for describing of a network. Advantage of layering is to provide well-defined interfaces between the layers, when change in one layer doesn’t affect an adjacent layer. Introduction to Network Programming in UNIX & LINUX 9
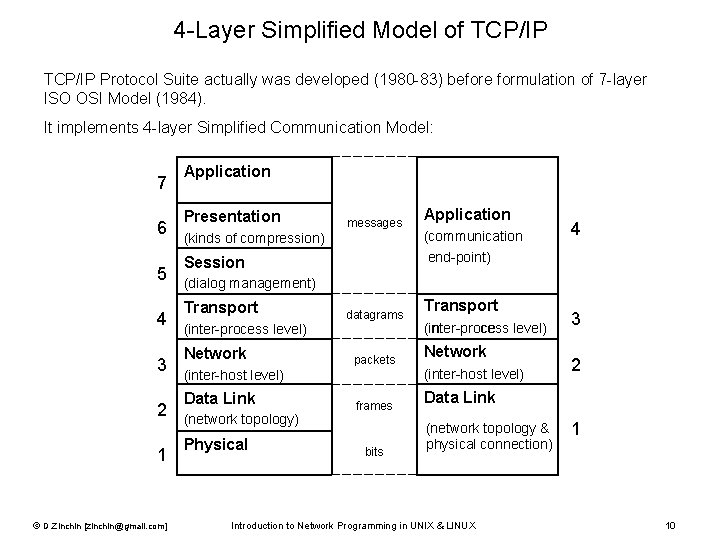
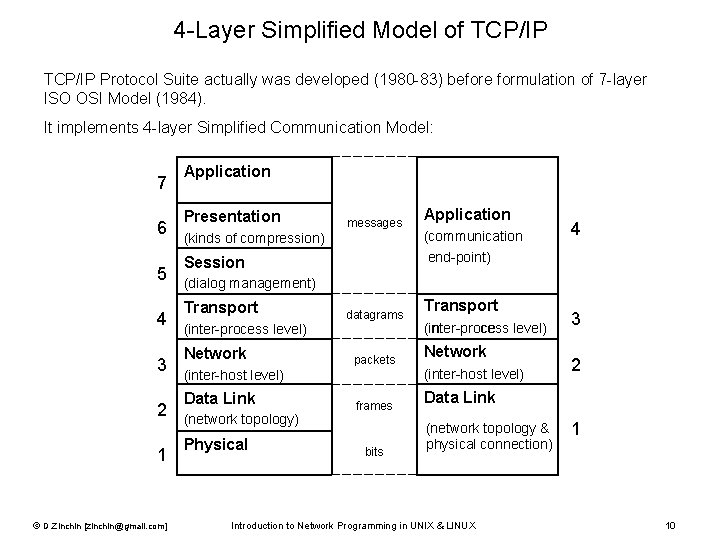
4 -Layer Simplified Model of TCP/IP Protocol Suite actually was developed (1980 -83) before formulation of 7 -layer ISO OSI Model (1984). It implements 4 -layer Simplified Communication Model: 7 6 5 4 3 2 1 © D. Zinchin [zinchin@gmail. com] Application Presentation messages (kinds of compression) Session Application (communication end-point) 4 (dialog management) Transport datagrams (inter-process level) Network packets (inter-host level) Data Link (network topology) Physical frames bits Transport (inter-process level) Network (inter-host level) 3 2 Data Link (network topology & physical connection) Introduction to Network Programming in UNIX & LINUX 1 10
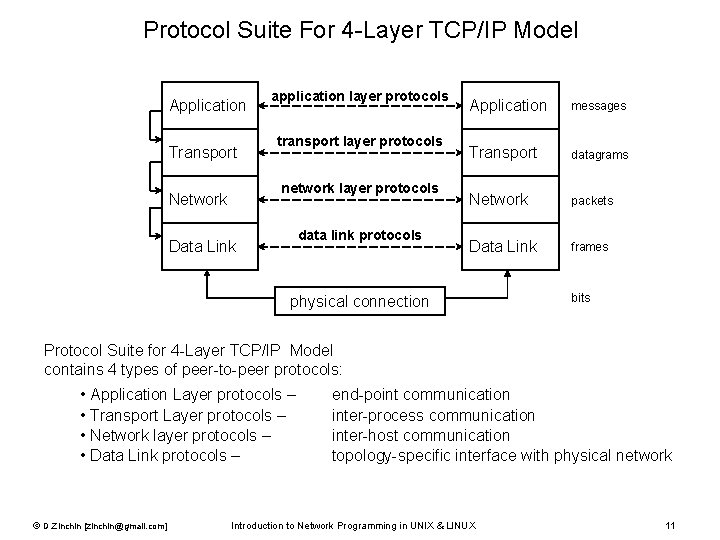
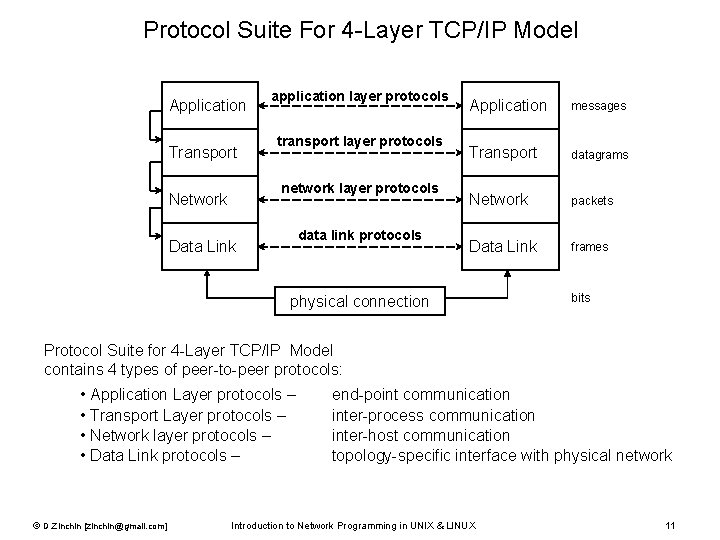
Protocol Suite For 4 -Layer TCP/IP Model Application Transport application layer protocols transport layer protocols network layer protocols Network data link protocols Data Link Application messages Transport datagrams Network packets Data Link frames physical connection bits Protocol Suite for 4 -Layer TCP/IP Model contains 4 types of peer-to-peer protocols: • Application Layer protocols – • Transport Layer protocols – • Network layer protocols – • Data Link protocols – © D. Zinchin [zinchin@gmail. com] end-point communication inter-process communication inter-host communication topology-specific interface with physical network Introduction to Network Programming in UNIX & LINUX 11
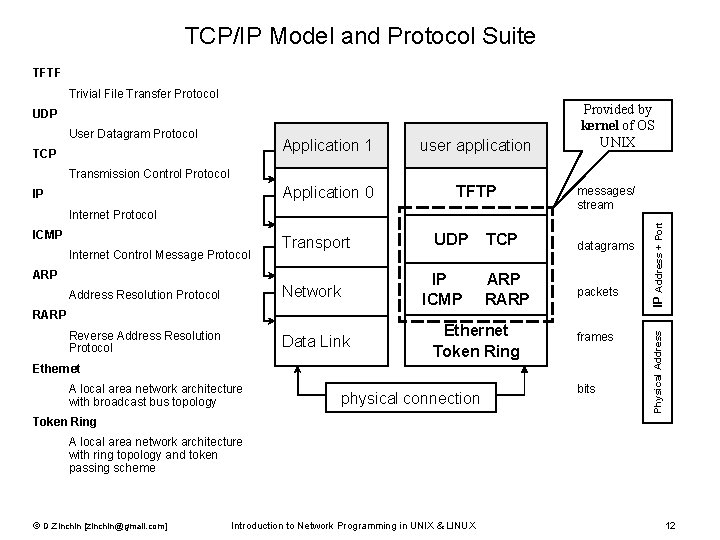
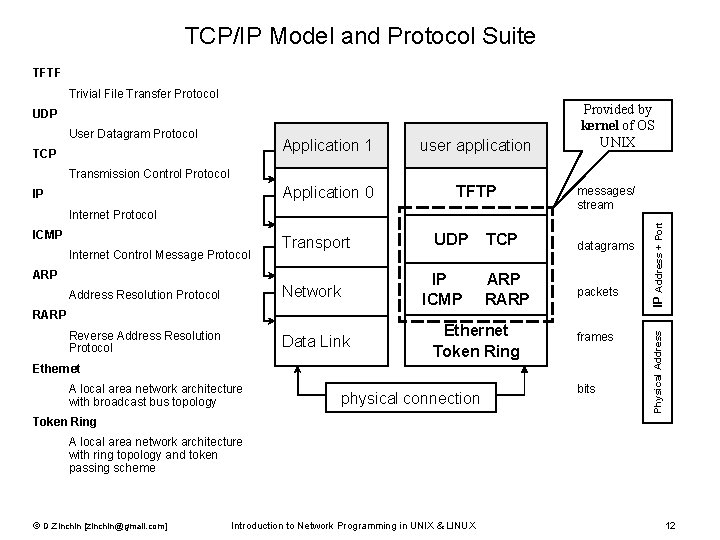
TCP/IP Model and Protocol Suite TFTF Trivial File Transfer Protocol UDP User Datagram Protocol TCP Application 1 user application Application 0 TFTP Provided by kernel of OS UNIX Transmission Control Protocol ICMP Internet Control Message Protocol Transport ARP UDP TCP datagrams Address Resolution Protocol Network IP ARP ICMP RARP packets Reverse Address Resolution Protocol Data Link Ethernet Token Ring frames RARP Ethernet A local area network architecture with broadcast bus topology physical connection bits IP Address + Port Internet Protocol messages/ stream Physical Address IP Token Ring A local area network architecture with ring topology and token passing scheme © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 12
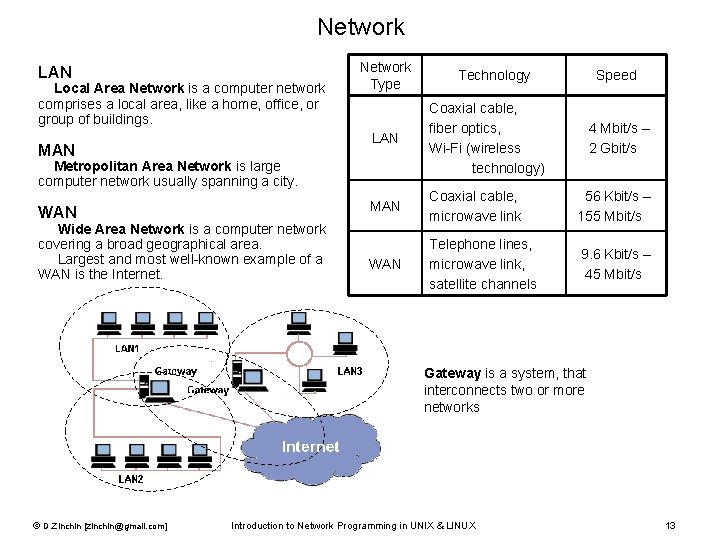
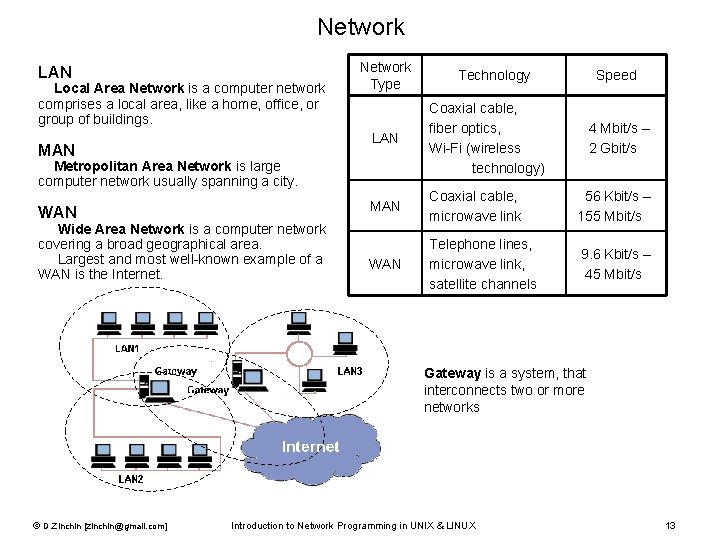
Network LAN Local Area Network is a computer network comprises a local area, like a home, office, or group of buildings. MAN Network Type Wide Area Network is a computer network covering a broad geographical area. Largest and most well-known example of a WAN is the Internet. Speed LAN Coaxial cable, fiber optics, Wi-Fi (wireless technology) MAN Coaxial cable, microwave link 56 Kbit/s – 155 Mbit/s WAN Telephone lines, microwave link, satellite channels 9. 6 Kbit/s – 45 Mbit/s Metropolitan Area Network is large computer network usually spanning a city. WAN Technology 4 Mbit/s – 2 Gbit/s Gateway is a system, that interconnects two or more networks © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 13
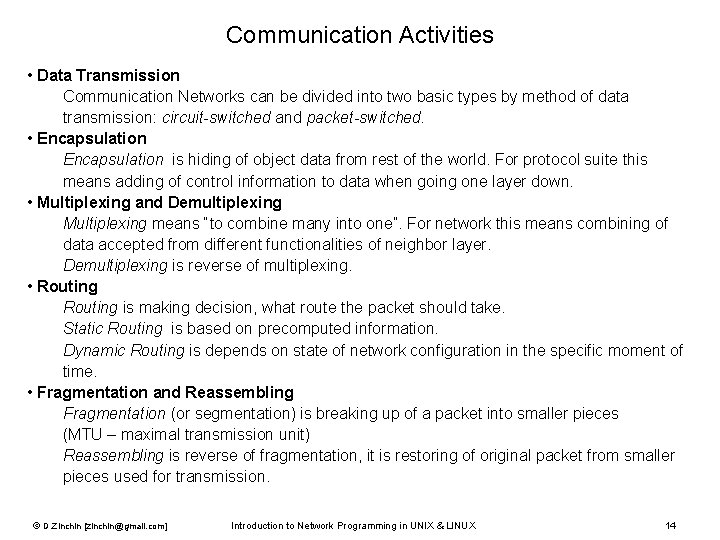
Communication Activities • Data Transmission Communication Networks can be divided into two basic types by method of data transmission: circuit-switched and packet-switched. • Encapsulation is hiding of object data from rest of the world. For protocol suite this means adding of control information to data when going one layer down. • Multiplexing and Demultiplexing Multiplexing means “to combine many into one”. For network this means combining of data accepted from different functionalities of neighbor layer. Demultiplexing is reverse of multiplexing. • Routing is making decision, what route the packet should take. Static Routing is based on precomputed information. Dynamic Routing is depends on state of network configuration in the specific moment of time. • Fragmentation and Reassembling Fragmentation (or segmentation) is breaking up of a packet into smaller pieces (MTU – maximal transmission unit) Reassembling is reverse of fragmentation, it is restoring of original packet from smaller pieces used for transmission. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 14
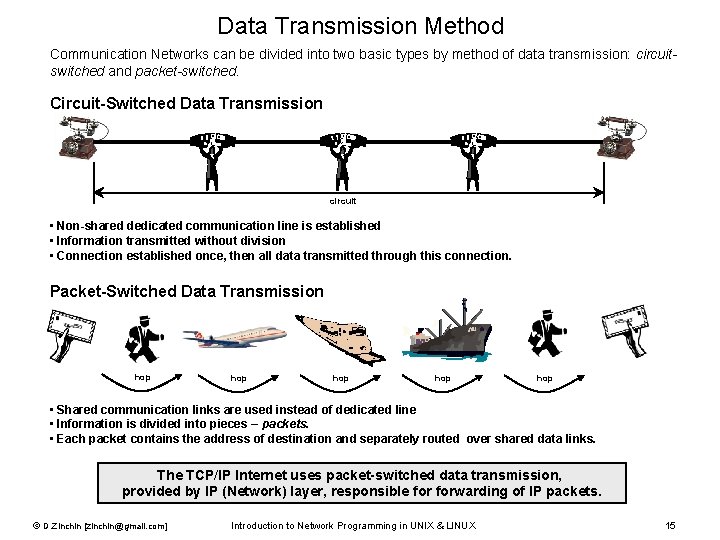
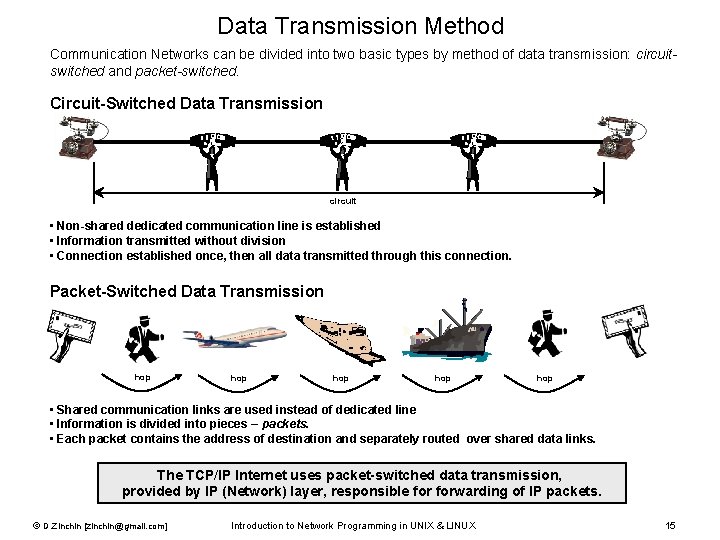
Data Transmission Method Communication Networks can be divided into two basic types by method of data transmission: circuitswitched and packet-switched. Circuit-Switched Data Transmission circuit • Non-shared dedicated communication line is established • Information transmitted without division • Connection established once, then all data transmitted through this connection. Packet-Switched Data Transmission hop hop hop • Shared communication links are used instead of dedicated line • Information is divided into pieces – packets. • Each packet contains the address of destination and separately routed over shared data links. The TCP/IP Internet uses packet-switched data transmission, provided by IP (Network) layer, responsible forwarding of IP packets. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 15
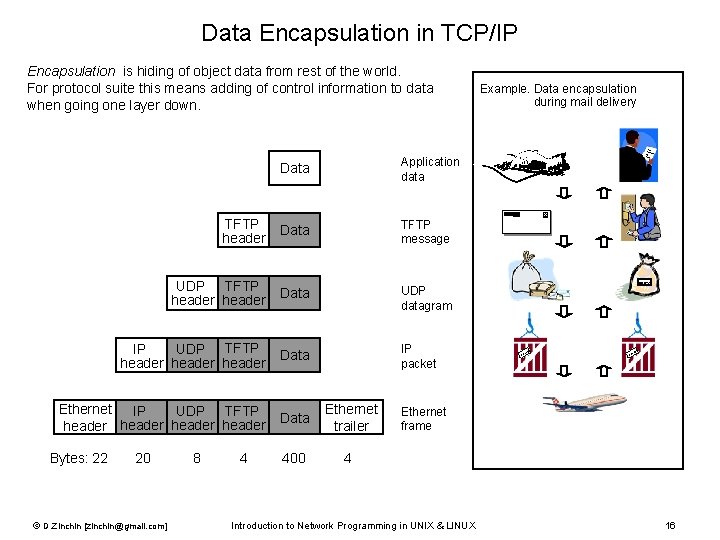
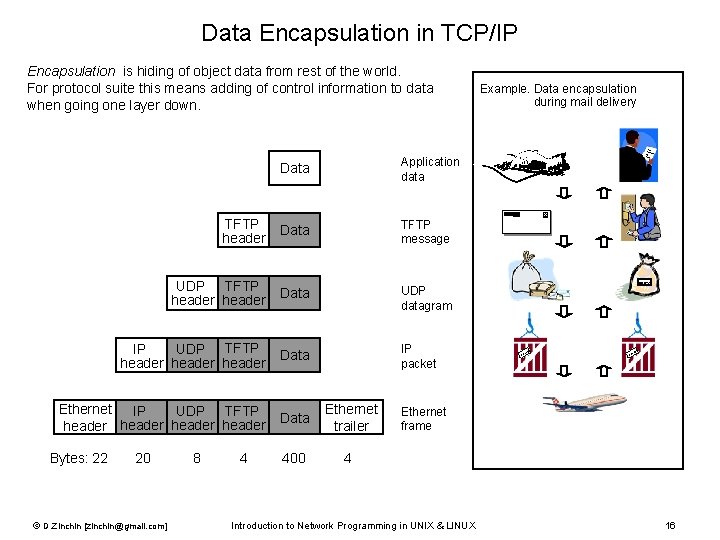
Data Encapsulation in TCP/IP Encapsulation is hiding of object data from rest of the world. For protocol suite this means adding of control information to data when going one layer down. Data Application data Data TFTP message UDP TFTP header Data UDP datagram IP UDP TFTP header Data IP packet Ethernet IP UDP TFTP header Data Ethernet trailer 400 4 TFTP header Bytes: 22 20 © D. Zinchin [zinchin@gmail. com] 8 4 Example. Data encapsulation during mail delivery intere sti ng letter address ss dre ad Ethernet frame Introduction to Network Programming in UNIX & LINUX 16
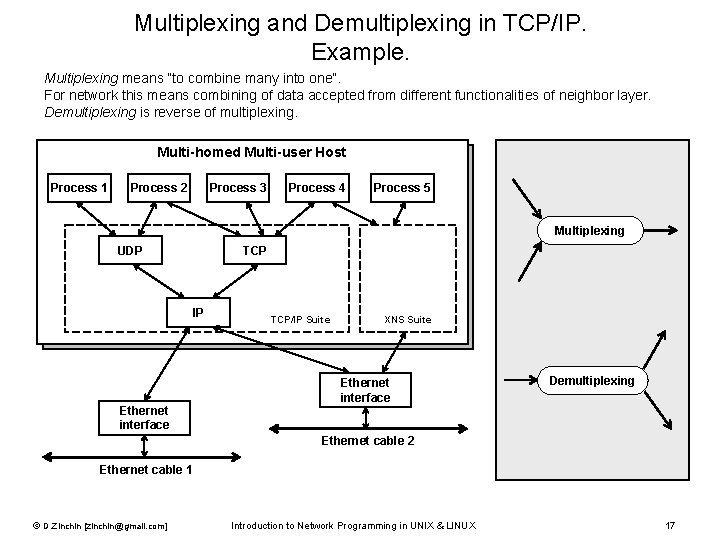
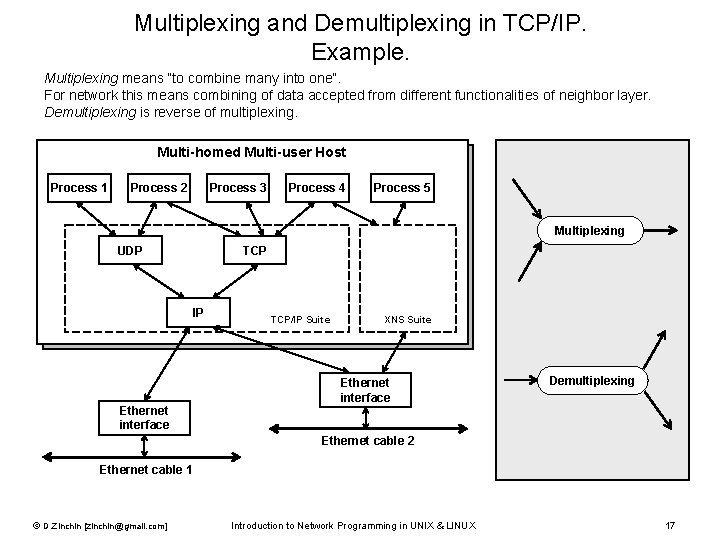
Multiplexing and Demultiplexing in TCP/IP. Example. Multiplexing means “to combine many into one”. For network this means combining of data accepted from different functionalities of neighbor layer. Demultiplexing is reverse of multiplexing. Multi-homed Multi-user Host Process 1 Process 2 Process 3 Process 4 Process 5 Multiplexing UDP TCP IP Ethernet interface TCP/IP Suite XNS Suite Ethernet interface Demultiplexing Ethernet cable 2 Ethernet cable 1 © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 17
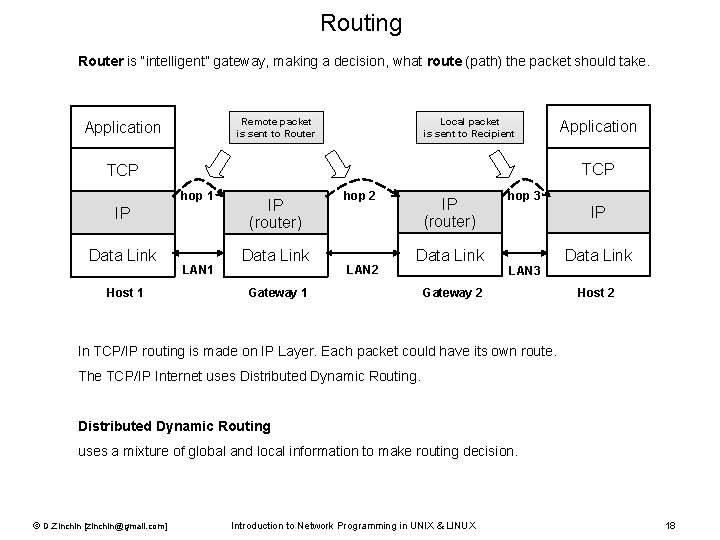
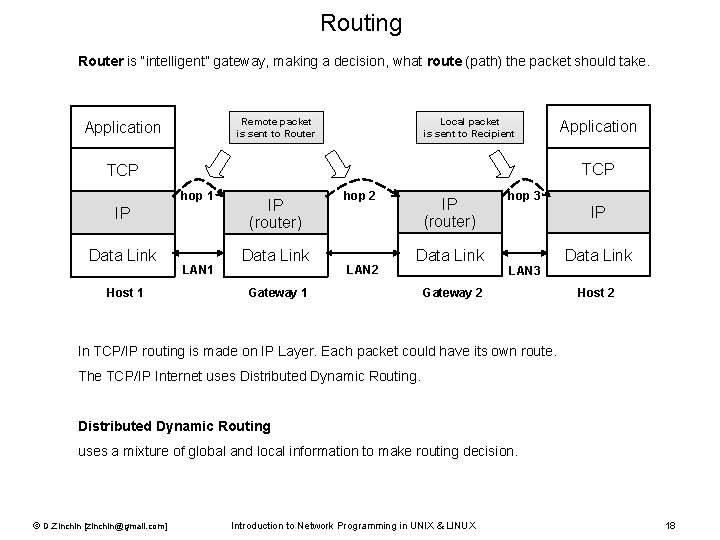
Routing Router is “intelligent” gateway, making a decision, what route (path) the packet should take. Remote packet is sent to Router Application Local packet is sent to Recipient TCP hop 1 IP Data Link Host 1 Application LAN 1 IP (router) Data Link hop 2 LAN 2 IP (router) Data Link Gateway 1 hop 3 IP LAN 3 Gateway 2 Data Link Host 2 In TCP/IP routing is made on IP Layer. Each packet could have its own route. The TCP/IP Internet uses Distributed Dynamic Routing uses a mixture of global and local information to make routing decision. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 18
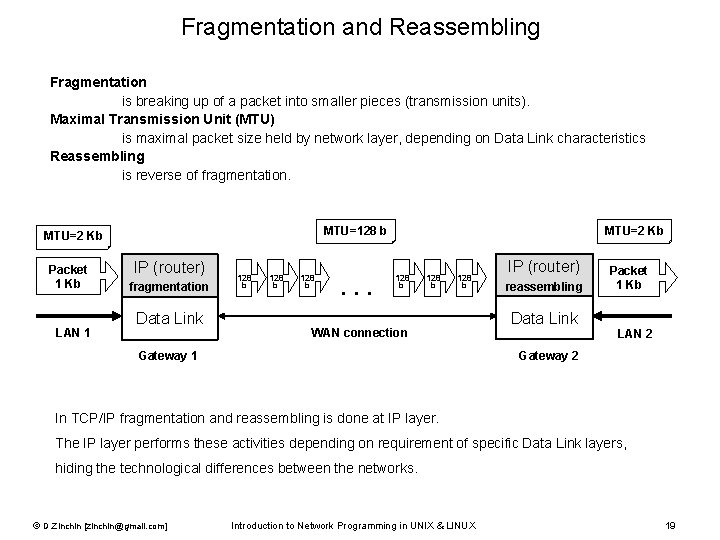
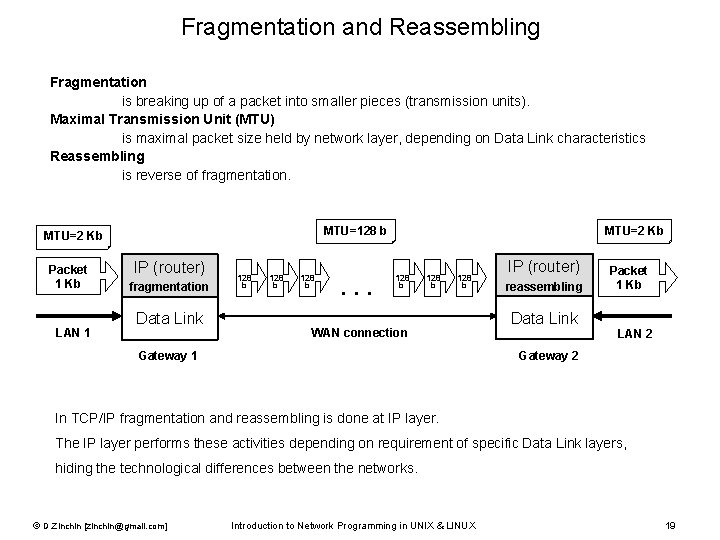
Fragmentation and Reassembling Fragmentation is breaking up of a packet into smaller pieces (transmission units). Maximal Transmission Unit (MTU) is maximal packet size held by network layer, depending on Data Link characteristics Reassembling is reverse of fragmentation. MTU=128 b MTU=2 Kb Packet 1 Kb LAN 1 IP (router) fragmentation Data Link 128 b . . . MTU=2 Kb 128 b WAN connection Gateway 1 IP (router) reassembling Data Link Packet 1 Kb LAN 2 Gateway 2 In TCP/IP fragmentation and reassembling is done at IP layer. The IP layer performs these activities depending on requirement of specific Data Link layers, hiding the technological differences between the networks. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 19
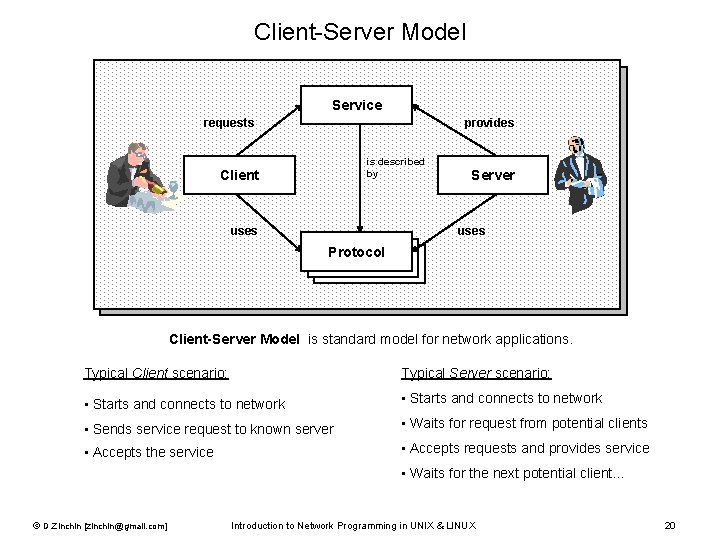
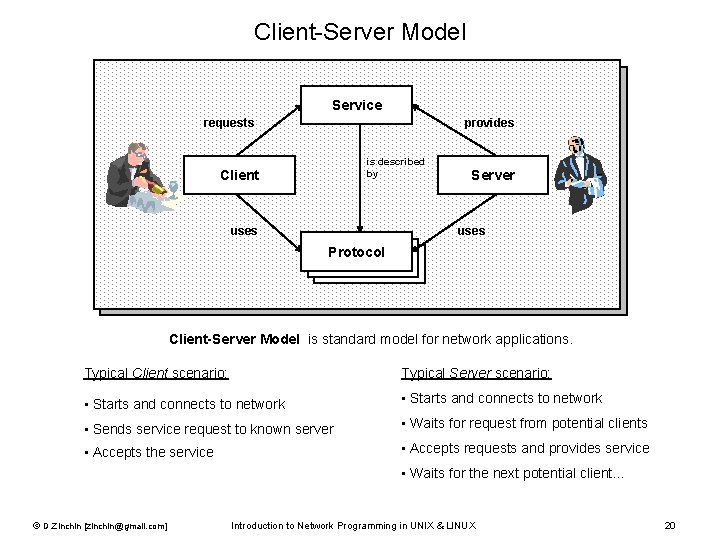
Client-Server Model Service requests provides is described by Client uses Server uses Protocol Client-Server Model is standard model for network applications. Typical Client scenario: Typical Server scenario: • Starts and connects to network • Sends service request to known server • Waits for request from potential clients • Accepts the service • Accepts requests and provides service • Waits for the next potential client… © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 20
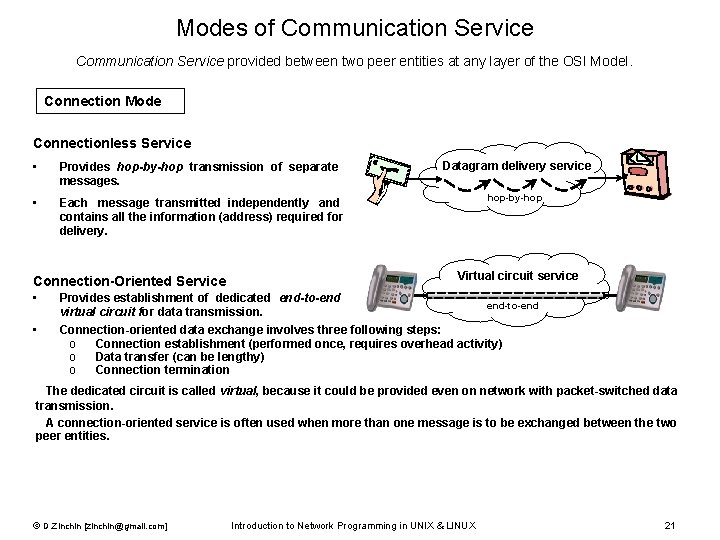
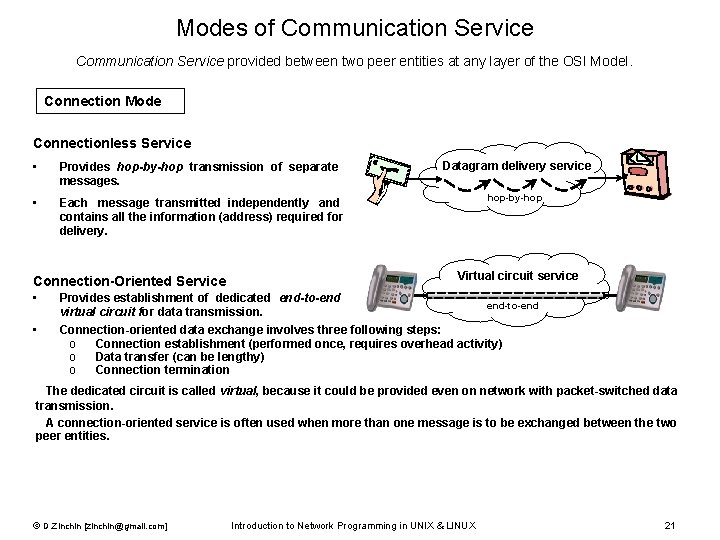
Modes of Communication Service provided between two peer entities at any layer of the OSI Model. Connection Mode Connectionless Service • Provides hop-by-hop transmission of separate messages. Datagram delivery service • Each message transmitted independently and contains all the information (address) required for delivery. hop-by-hop Connection-Oriented Service • • Virtual circuit service Provides establishment of dedicated end-to-end virtual circuit for data transmission. Connection-oriented data exchange involves three following steps: o Connection establishment (performed once, requires overhead activity) o Data transfer (can be lengthy) o Connection termination The dedicated circuit is called virtual, because it could be provided even on network with packet-switched data transmission. A connection-oriented service is often used when more than one message is to be exchanged between the two peer entities. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 21
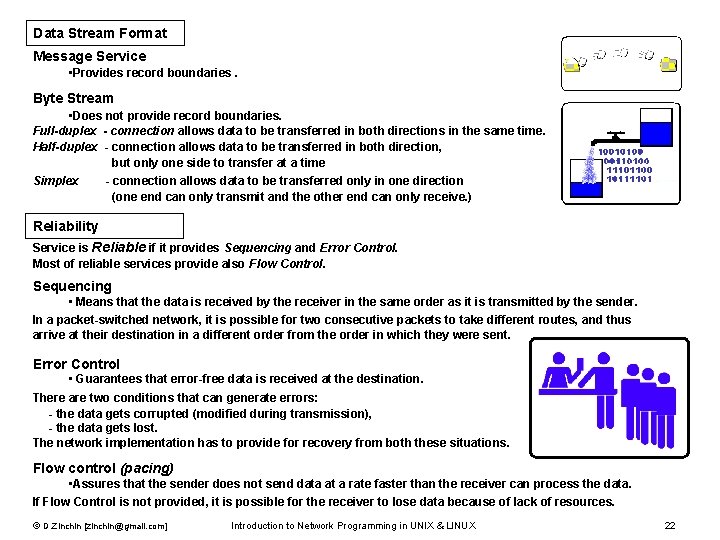
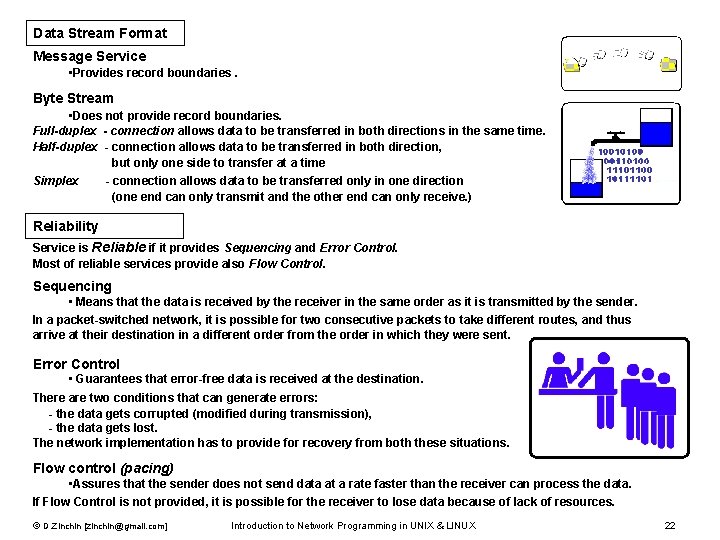
Modes of Communication Service (continuation) Data Stream Format Message Service • Provides record boundaries. Byte Stream • Does not provide record boundaries. Full-duplex - connection allows data to be transferred in both directions in the same time. Half-duplex - connection allows data to be transferred in both direction, but only one side to transfer at a time Simplex - connection allows data to be transferred only in one direction (one end can only transmit and the other end can only receive. ) Reliability Service is Reliable if it provides Sequencing and Error Control. Most of reliable services provide also Flow Control. Sequencing • Means that the data is received by the receiver in the same order as it is transmitted by the sender. In a packet-switched network, it is possible for two consecutive packets to take different routes, and thus arrive at their destination in a different order from the order in which they were sent. Error Control • Guarantees that error-free data is received at the destination. There are two conditions that can generate errors: - the data gets corrupted (modified during transmission), - the data gets lost. The network implementation has to provide for recovery from both these situations. Flow control (pacing) • Assures that the sender does not send data at a rate faster than the receiver can process the data. If Flow Control is not provided, it is possible for the receiver to lose data because of lack of resources. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 22
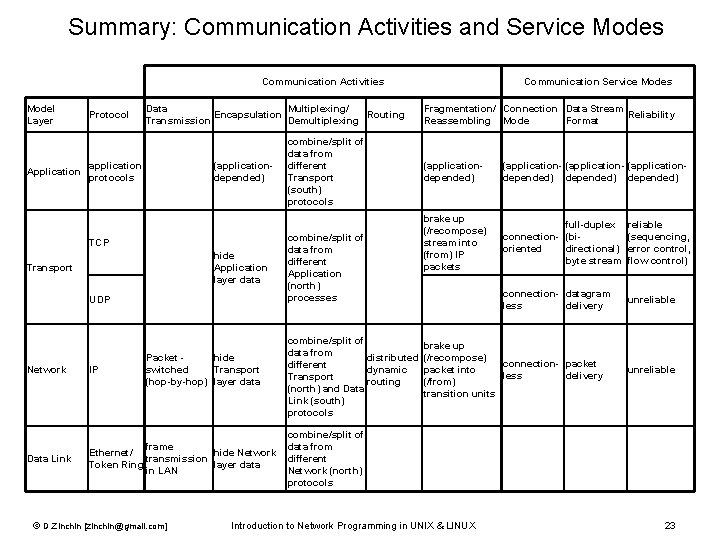
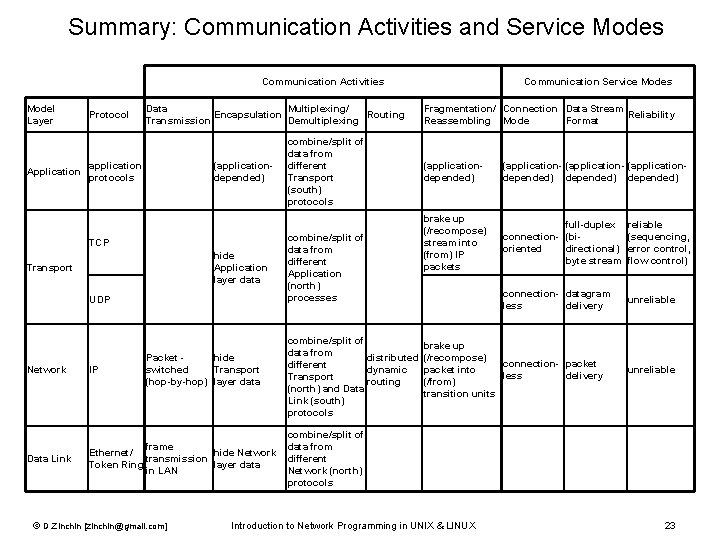
Summary: Communication Activities and Service Modes Communication Activities Model Layer Application Protocol Data Multiplexing/ Encapsulation Routing Transmission Demultiplexing application protocols (applicationdepended) TCP Transport hide Application layer data UDP Packet hide switched Transport (hop-by-hop) layer data combine/split of data from different Transport (south) protocols combine/split of data from different Application (north) processes Fragmentation/ Connection Data Stream Reliability Reassembling Mode Format (applicationdepended) (application- (applicationdepended) brake up (/recompose) stream into (from) IP packets full-duplex connection- (bioriented directional) byte stream reliable (sequencing, error control, flow control) connection- datagram less delivery unreliable combine/split of brake up data from distributed (/recompose) connection- packet different dynamic packet into less delivery Transport routing (/from) (north) and Data transition units Link (south) protocols Network IP Data Link combine/split of frame data from Ethernet/ hide Network transmission different Token Ring layer data in LAN Network (north) protocols © D. Zinchin [zinchin@gmail. com] Communication Service Modes Introduction to Network Programming in UNIX & LINUX unreliable 23
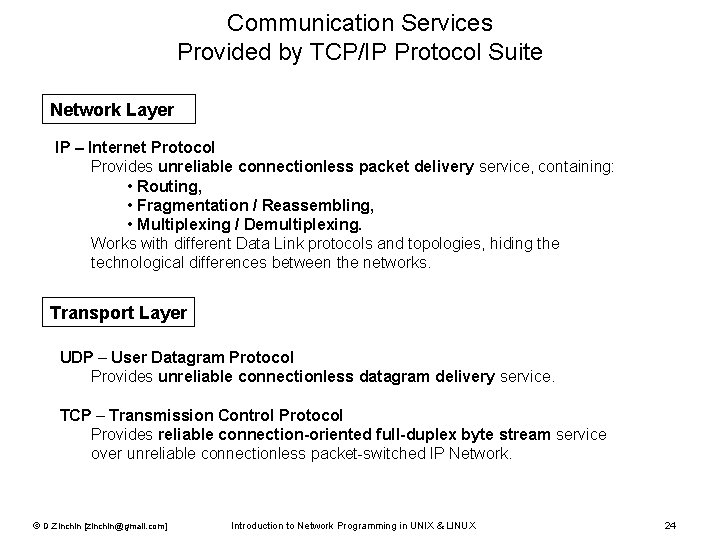
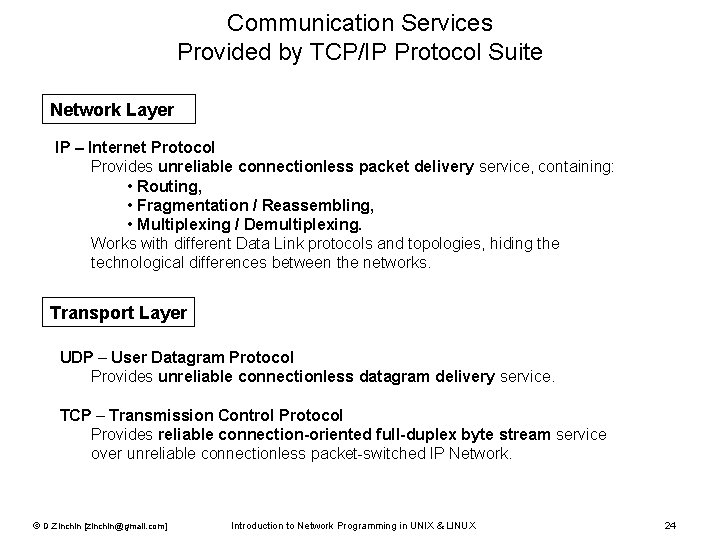
Communication Services Provided by TCP/IP Protocol Suite Network Layer IP – Internet Protocol Provides unreliable connectionless packet delivery service, containing: • Routing, • Fragmentation / Reassembling, • Multiplexing / Demultiplexing. Works with different Data Link protocols and topologies, hiding the technological differences between the networks. Transport Layer UDP – User Datagram Protocol Provides unreliable connectionless datagram delivery service. TCP – Transmission Control Protocol Provides reliable connection-oriented full-duplex byte stream service over unreliable connectionless packet-switched IP Network. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 24
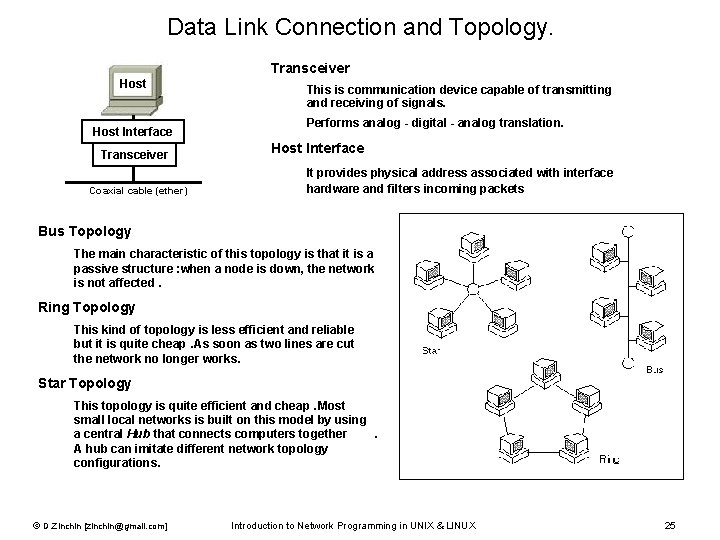
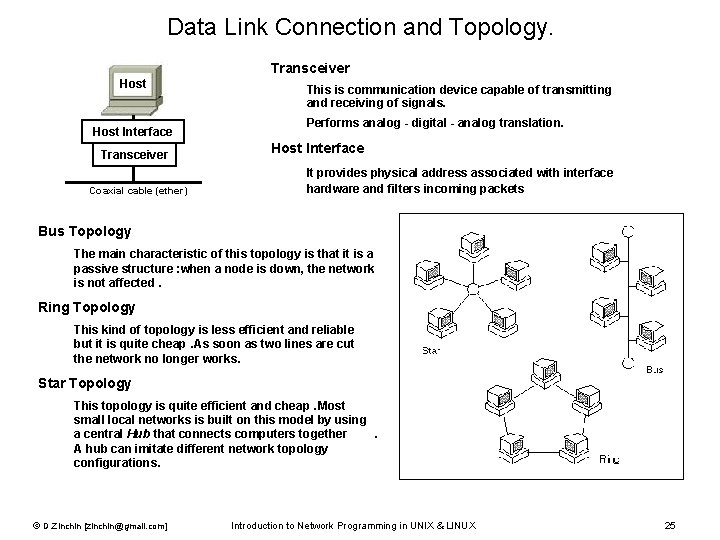
Data Link Connection and Topology. Transceiver Host Interface Transceiver Coaxial cable (ether) This is communication device capable of transmitting and receiving of signals. Performs analog - digital - analog translation. Host Interface It provides physical address associated with interface hardware and filters incoming packets Bus Topology The main characteristic of this topology is that it is a passive structure : when a node is down, the network is not affected. Ring Topology This kind of topology is less efficient and reliable but it is quite cheap. As soon as two lines are cut the network no longer works. Star Topology This topology is quite efficient and cheap. Most small local networks is built on this model by using a central Hub that connects computers together . A hub can imitate different network topology configurations. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 25
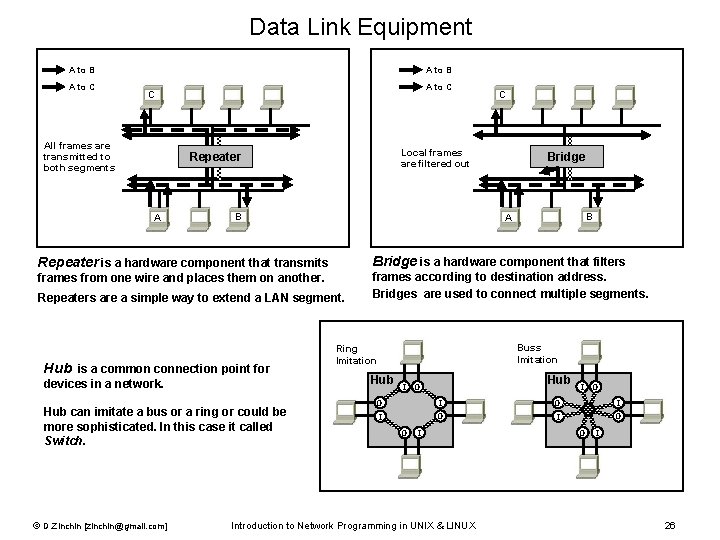
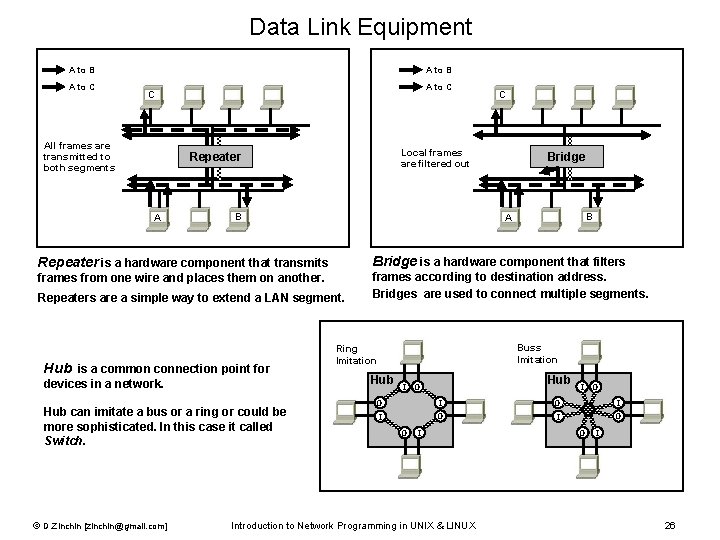
Data Link Equipment A to B A to C C All frames are transmitted to both segments Local frames are filtered out Repeater A C B Bridge B A Repeater is a hardware component that transmits Bridge is a hardware component that filters frames from one wire and places them on another. frames according to destination address. Bridges are used to connect multiple segments. Repeaters are a simple way to extend a LAN segment. Hub is a common connection point for devices in a network. Hub can imitate a bus or a ring or could be more sophisticated. In this case it called Switch. © D. Zinchin [zinchin@gmail. com] Buss Imitation Ring Imitation Hub I Hub O I O I I O O I Introduction to Network Programming in UNIX & LINUX O I 26
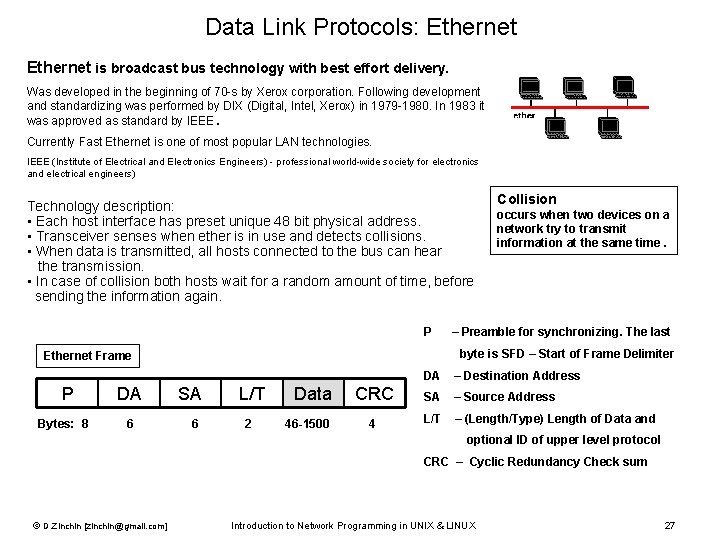
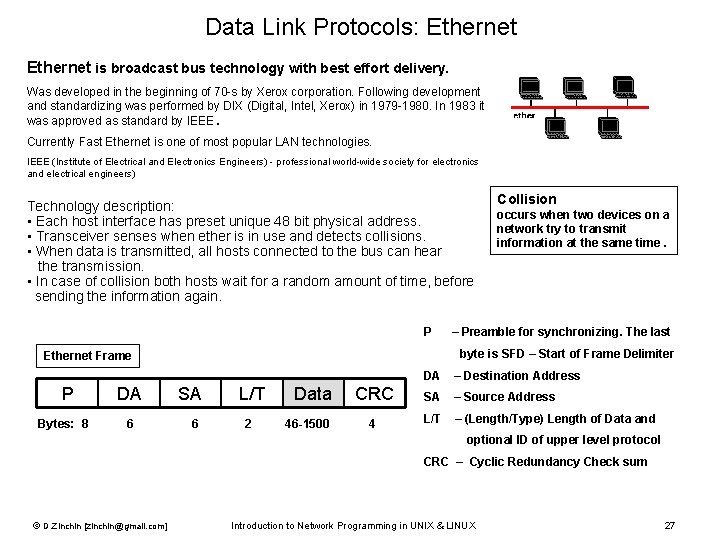
Data Link Protocols: Ethernet is broadcast bus technology with best effort delivery. Was developed in the beginning of 70 -s by Xerox corporation. Following development and standardizing was performed by DIX (Digital, Intel, Xerox) in 1979 -1980. In 1983 it was approved as standard by IEEE. Currently Fast Ethernet is one of most popular LAN technologies. IEEE (Institute of Electrical and Electronics Engineers) - professional world-wide society for electronics and electrical engineers) Technology description: • Each host interface has preset unique 48 bit physical address. • Transceiver senses when ether is in use and detects collisions. • When data is transmitted, all hosts connected to the bus can hear the transmission. • In case of collision both hosts wait for a random amount of time, before sending the information again. Collision occurs when two devices on a network try to transmit information at the same time. P – Preamble for synchronizing. The last byte is SFD – Start of Frame Delimiter Ethernet Frame DA – Destination Address P Bytes: 8 DA 6 SA L/T Data CRC 6 2 46 -1500 4 SA – Source Address L/T – (Length/Type) Length of Data and optional ID of upper level protocol CRC – Cyclic Redundancy Check sum © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 27
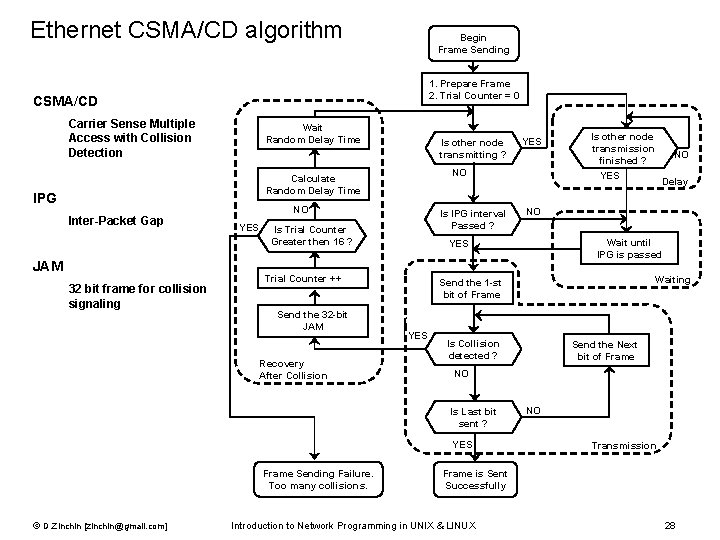
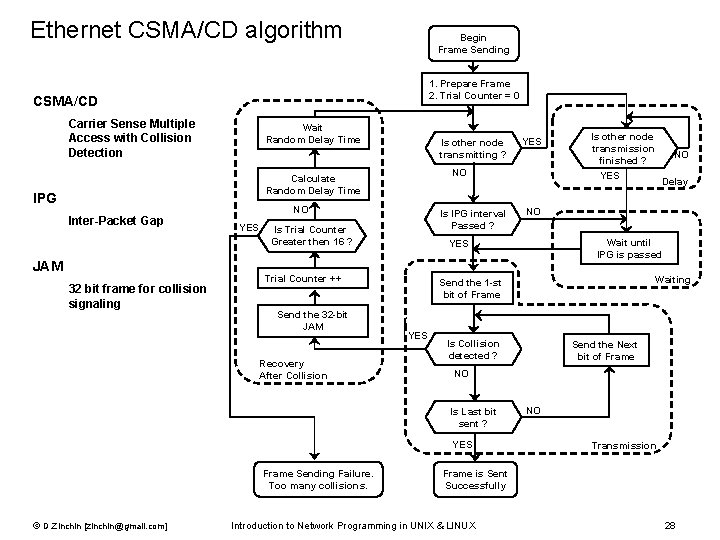
Ethernet CSMA/CD algorithm Begin Frame Sending 1. Prepare Frame 2. Trial Counter = 0 CSMA/CD Carrier Sense Multiple Access with Collision Detection Wait Random Delay Time Is other node transmitting ? NO Calculate Random Delay Time IPG Inter-Packet Gap JAM 32 bit frame for collision signaling NO YES Is IPG interval Passed ? Is Trial Counter Greater then 16 ? Recovery After Collision YES Delay Wait until IPG is passed Waiting Is Collision detected ? Send the Next bit of Frame NO YES © D. Zinchin [zinchin@gmail. com] NO NO Send the 1 -st bit of Frame Is Last bit sent ? Frame Sending Failure. Too many collisions. Is other node transmission finished ? YES Trial Counter ++ Send the 32 -bit JAM YES NO Transmission Frame is Sent Successfully Introduction to Network Programming in UNIX & LINUX 28
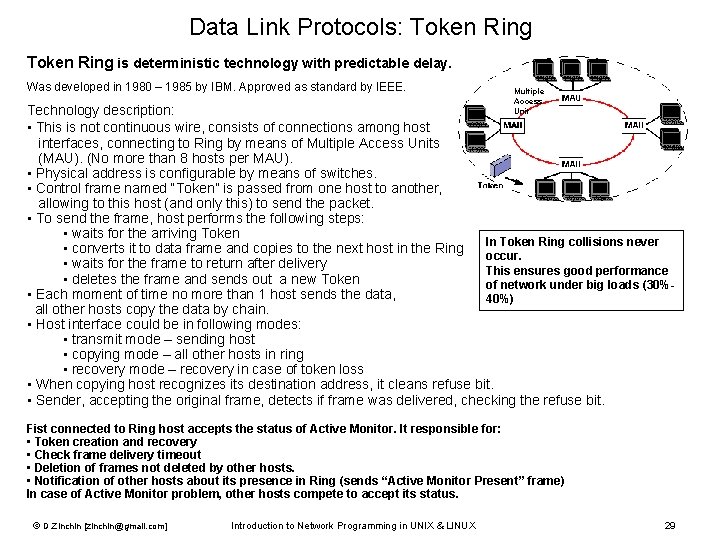
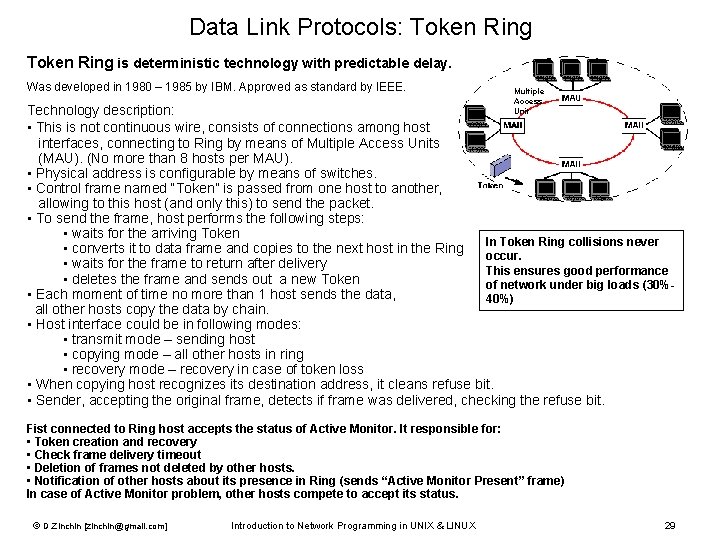
Data Link Protocols: Token Ring is deterministic technology with predictable delay. Was developed in 1980 – 1985 by IBM. Approved as standard by IEEE. Multiple Access Unit Technology description: • This is not continuous wire, consists of connections among host interfaces, connecting to Ring by means of Multiple Access Units (MAU). (No more than 8 hosts per MAU). • Physical address is configurable by means of switches. • Control frame named “Token” is passed from one host to another, allowing to this host (and only this) to send the packet. • To send the frame, host performs the following steps: • waits for the arriving Token In Token Ring collisions never • converts it to data frame and copies to the next host in the Ring occur. • waits for the frame to return after delivery This ensures good performance • deletes the frame and sends out a new Token of network under big loads (30% • Each moment of time no more than 1 host sends the data, 40%) all other hosts copy the data by chain. • Host interface could be in following modes: • transmit mode – sending host • copying mode – all other hosts in ring • recovery mode – recovery in case of token loss • When copying host recognizes its destination address, it cleans refuse bit. • Sender, accepting the original frame, detects if frame was delivered, checking the refuse bit. Fist connected to Ring host accepts the status of Active Monitor. It responsible for: • Token creation and recovery • Check frame delivery timeout • Deletion of frames not deleted by other hosts. • Notification of other hosts about its presence in Ring (sends “Active Monitor Present” frame) In case of Active Monitor problem, other hosts compete to accept its status. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 29
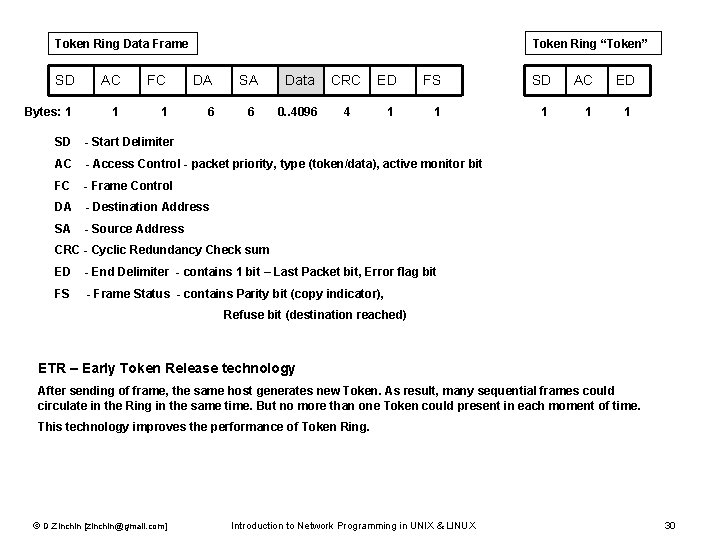
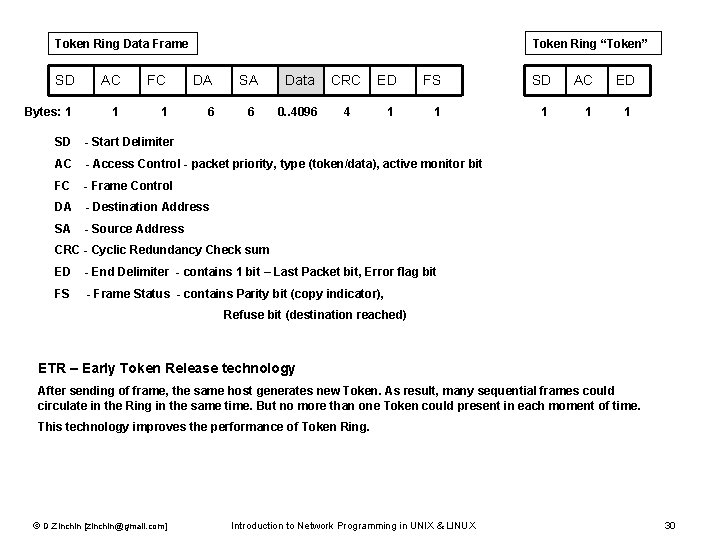
Token Ring (continuation) Token Ring “Token” Token Ring Data Frame SD AC FC DA SA Data CRC ED FS Bytes: 1 1 6 0. . 4096 4 1 1 SD AC ED 1 1 SD - Start Delimiter AC - Access Control - packet priority, type (token/data), active monitor bit FC - Frame Control DA - Destination Address SA - Source Address CRC - Cyclic Redundancy Check sum ED - End Delimiter - contains 1 bit – Last Packet bit, Error flag bit FS - Frame Status - contains Parity bit (copy indicator), Refuse bit (destination reached) ETR – Early Token Release technology After sending of frame, the same host generates new Token. As result, many sequential frames could circulate in the Ring in the same time. But no more than one Token could present in each moment of time. This technology improves the performance of Token Ring. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 30
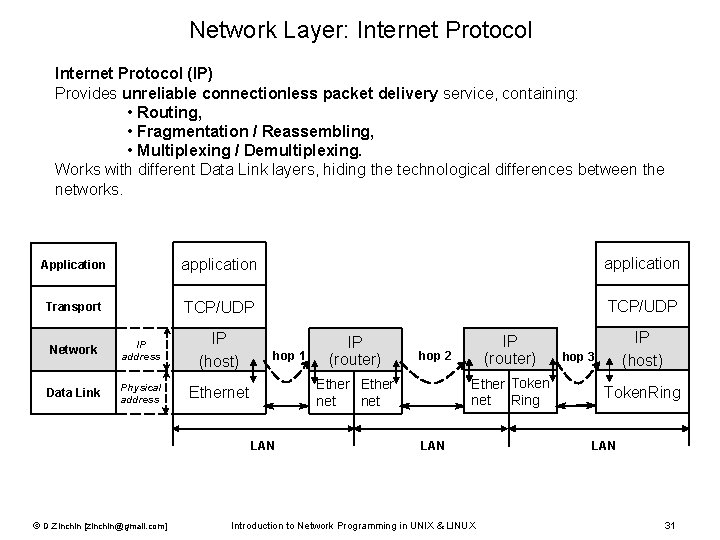
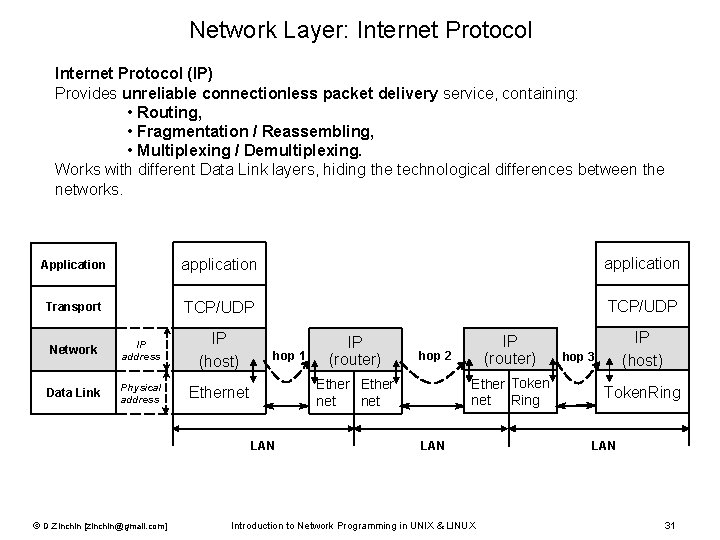
Network Layer: Internet Protocol (IP) Provides unreliable connectionless packet delivery service, containing: • Routing, • Fragmentation / Reassembling, • Multiplexing / Demultiplexing. Works with different Data Link layers, hiding the technological differences between the networks. Application application Transport TCP/UDP Network IP address IP (host) Data Link Physical address Ethernet hop 1 IP (router) hop 2 Ether Token net Ring Ether net LAN © D. Zinchin [zinchin@gmail. com] IP (router) LAN Introduction to Network Programming in UNIX & LINUX IP (host) hop 3 Token. Ring LAN 31
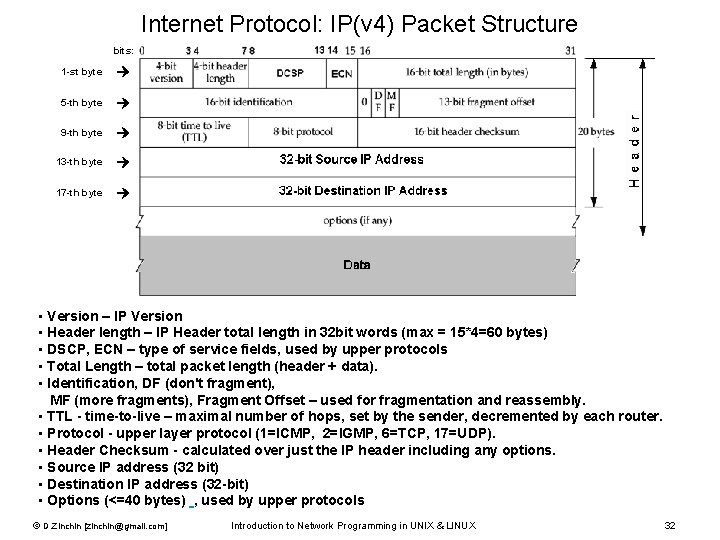
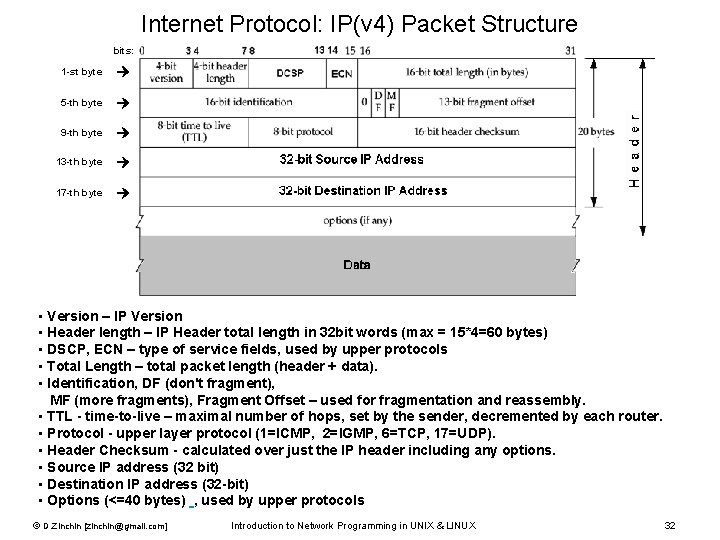
Internet Protocol: IP(v 4) Packet Structure bits: 1 -st byte 5 -th byte 9 -th byte 13 -th byte 17 -th byte • Version – IP Version • Header length – IP Header total length in 32 bit words (max = 15*4=60 bytes) • DSCP, ECN – type of service fields, used by upper protocols • Total Length – total packet length (header + data). • Identification, DF (don't fragment), MF (more fragments), Fragment Offset – used for fragmentation and reassembly. • TTL - time-to-live – maximal number of hops, set by the sender, decremented by each router. • Protocol - upper layer protocol (1=ICMP, 2=IGMP, 6=TCP, 17=UDP). • Header Checksum - calculated over just the IP header including any options. • Source IP address (32 bit) • Destination IP address (32 -bit) • Options (<=40 bytes) , used by upper protocols © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 32
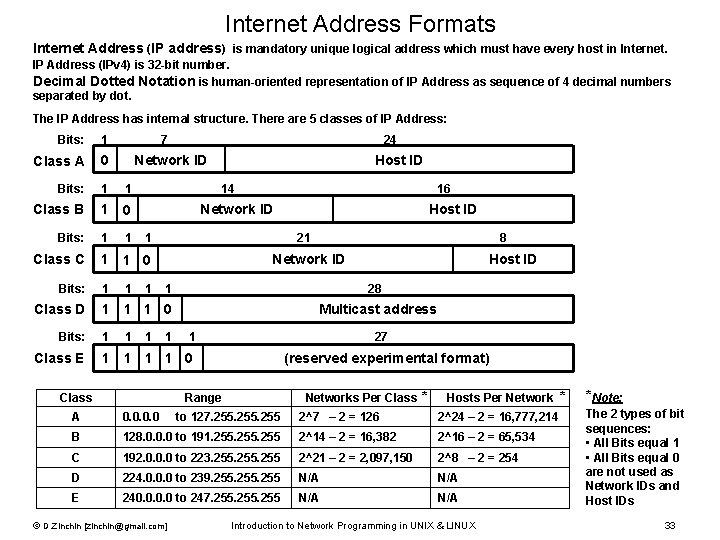
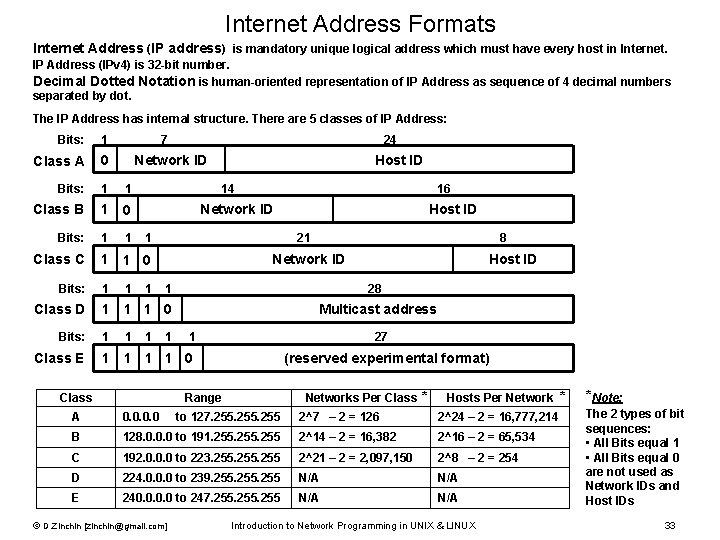
Internet Address Formats Internet Address (IP address) is mandatory unique logical address which must have every host in Internet. IP Address (IPv 4) is 32 -bit number. Decimal Dotted Notation is human-oriented representation of IP Address as sequence of 4 decimal numbers separated by dot. The IP Address has internal structure. There are 5 classes of IP Address: Bits: 1 7 24 Class A 0 Network ID Host ID Bits: 1 1 14 16 Class B 1 0 Network ID Host ID Bits: 1 1 1 21 8 Class C 1 1 0 Network ID Host ID Bits: 1 1 1 1 28 Class D 1 1 1 0 Multicast address Bits: 1 1 1 1 1 27 Class E 1 1 0 (reserved experimental format) Hosts Per Network * Range A 0. 0 to 127. 255 2^7 – 2 = 126 2^24 – 2 = 16, 777, 214 B 128. 0. 0. 0 to 191. 255 2^14 – 2 = 16, 382 2^16 – 2 = 65, 534 C 192. 0. 0. 0 to 223. 255 2^21 – 2 = 2, 097, 150 2^8 – 2 = 254 D 224. 0. 0. 0 to 239. 255 N/A E 240. 0 to 247. 255 N/A © D. Zinchin [zinchin@gmail. com] Networks Per Class * Class Introduction to Network Programming in UNIX & LINUX *Note: The 2 types of bit sequences: • All Bits equal 1 • All Bits equal 0 are not used as Network IDs and Host IDs 33
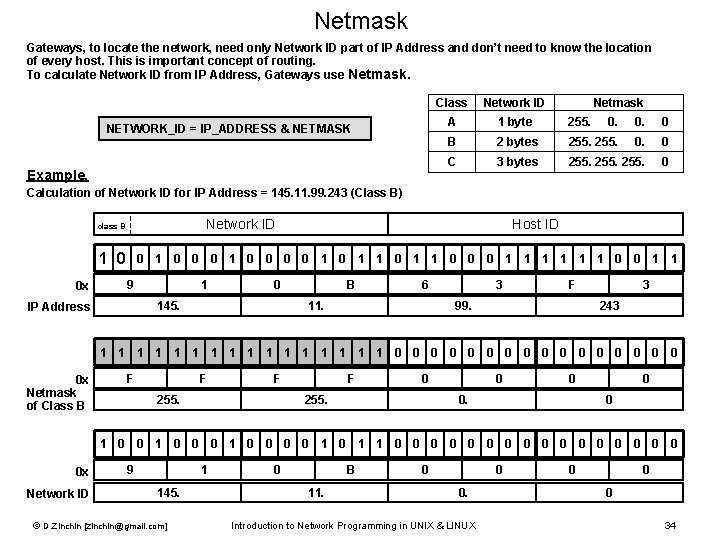
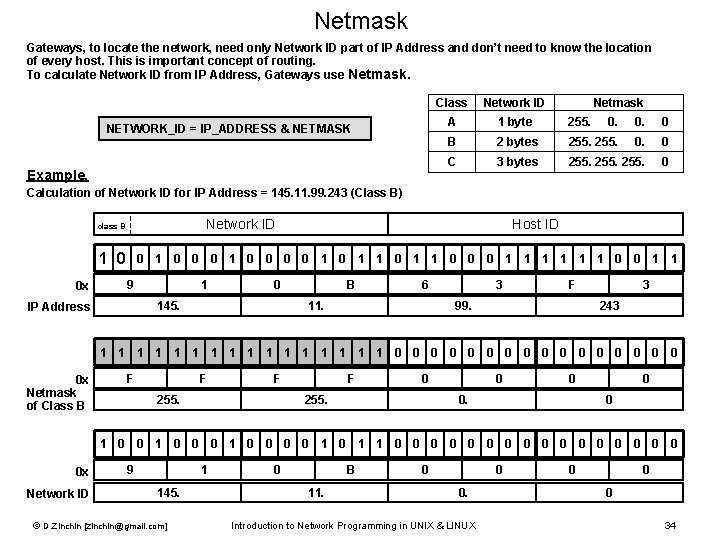
Netmask Gateways, to locate the network, need only Network ID part of IP Address and don’t need to know the location of every host. This is important concept of routing. To calculate Network ID from IP Address, Gateways use Netmask. NETWORK_ID = IP_ADDRESS & NETMASK Example. Class Network ID Netmask A 1 byte 255. 0. 0. 0 B 2 bytes 255. 0. 0 C 3 bytes 255. 0 Calculation of Network ID for IP Address = 145. 11. 99. 243 (Class B) Network ID class B 1 0 0 x Host ID 0 1 0 0 0 0 1 1 0 0 0 1 1 1 0 0 1 1 9 1 0 145. IP Address B 6 11. 3 F 99. 3 243 1 1 1 1 0 0 0 0 0 x Netmask of Class B F F F 255. F 0 255. 0 0 0 1 0 1 1 0 0 0 0 0 x Network ID 9 1 145. © D. Zinchin [zinchin@gmail. com] 0 B 11. 0 0 0. Introduction to Network Programming in UNIX & LINUX 0 0 0 34
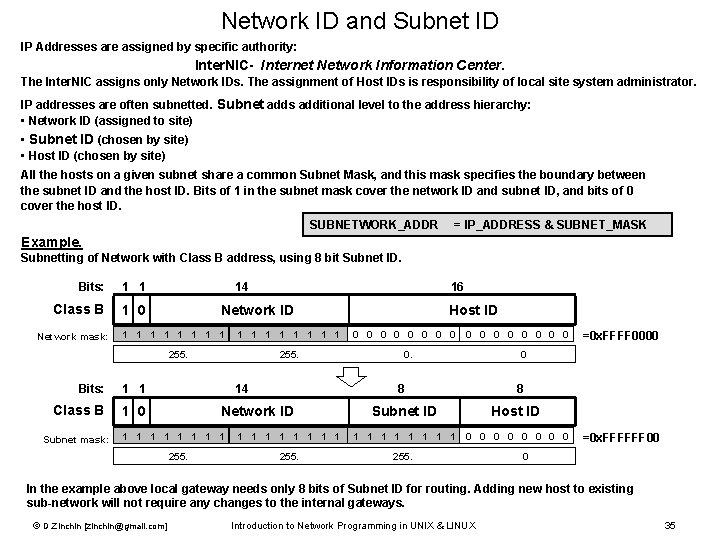
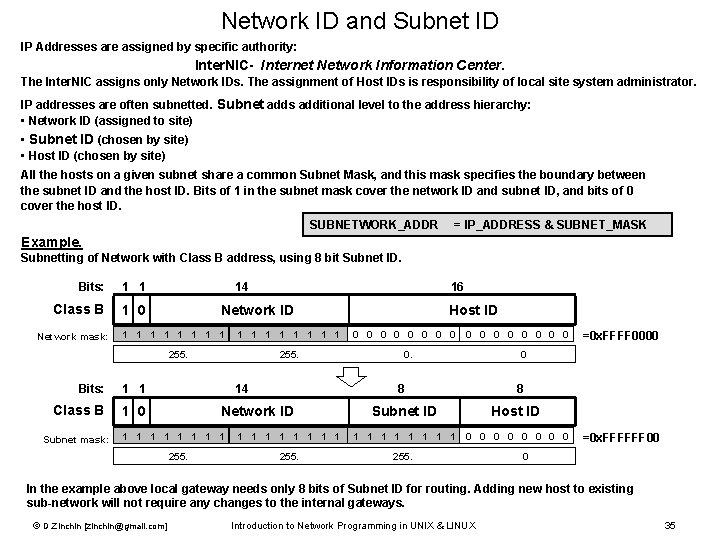
Network ID and Subnet ID IP Addresses are assigned by specific authority: Inter. NIC- Internet Network Information Center. The Inter. NIC assigns only Network IDs. The assignment of Host IDs is responsibility of local site system administrator. IP addresses are often subnetted. Subnet adds additional level to the address hierarchy: • Network ID (assigned to site) • Subnet ID (chosen by site) • Host ID (chosen by site) All the hosts on a given subnet share a common Subnet Mask, and this mask specifies the boundary between the subnet ID and the host ID. Bits of 1 in the subnet mask cover the network ID and subnet ID, and bits of 0 cover the host ID. SUBNETWORK_ADDR = IP_ADDRESS & SUBNET_MASK Example. Subnetting of Network with Class B address, using 8 bit Subnet ID. Bits: 1 1 14 16 Class B Network mask: 1 0 Network ID 1 1 1 1 Host ID 0 0 0 0 =0 x. FFFF 0000 255. 0 Bits: 1 1 14 8 Class B Subnet mask: 1 0 Network ID 1 1 1 1 Subnet ID Host ID 1 1 0 0 =0 x. FFFFFF 00 255. 0 In the example above local gateway needs only 8 bits of Subnet ID for routing. Adding new host to existing sub-network will not require any changes to the internal gateways. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 35
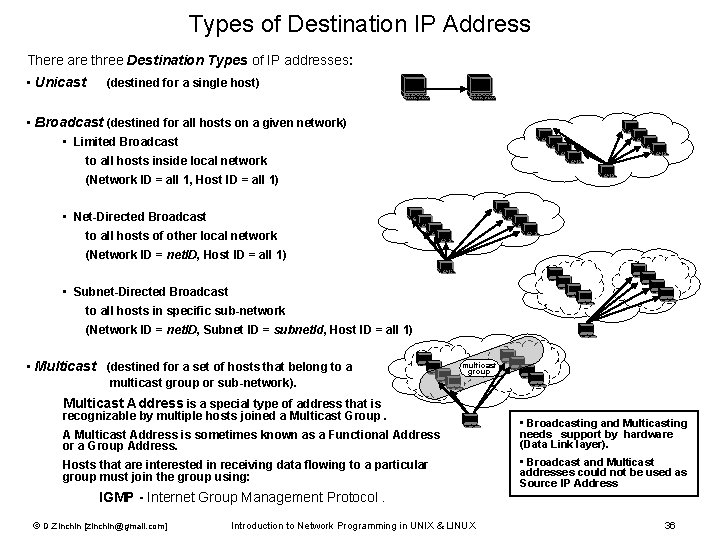
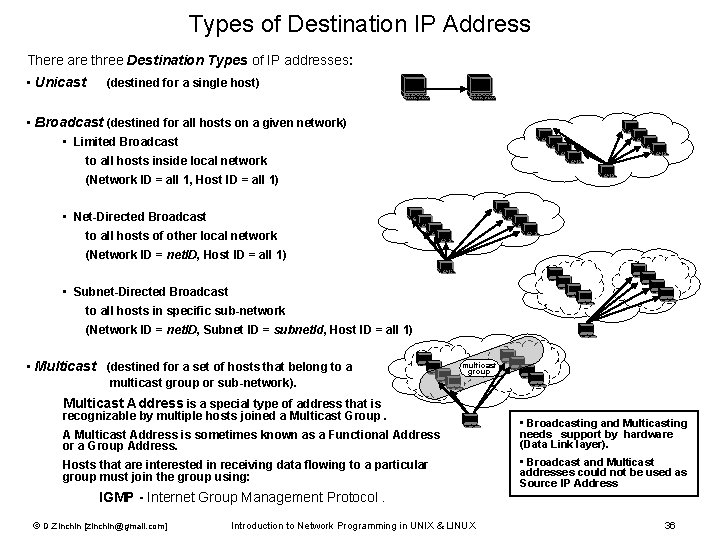
Types of Destination IP Address There are three Destination Types of IP addresses: • Unicast (destined for a single host) • Broadcast (destined for all hosts on a given network) • Limited Broadcast to all hosts inside local network (Network ID = all 1, Host ID = all 1) • Net-Directed Broadcast to all hosts of other local network (Network ID = net. ID, Host ID = all 1) • Subnet-Directed Broadcast to all hosts in specific sub-network (Network ID = net. ID, Subnet ID = subnet. Id, Host ID = all 1) • Multicast (destined for a set of hosts that belong to a multicast group or sub-network). multicast group Multicast Address is a special type of address that is recognizable by multiple hosts joined a Multicast Group. A Multicast Address is sometimes known as a Functional Address or a Group Address. Hosts that are interested in receiving data flowing to a particular group must join the group using: • Broadcasting and Multicasting needs support by hardware (Data Link layer). • Broadcast and Multicast addresses could not be used as Source IP Address IGMP - Internet Group Management Protocol. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 36
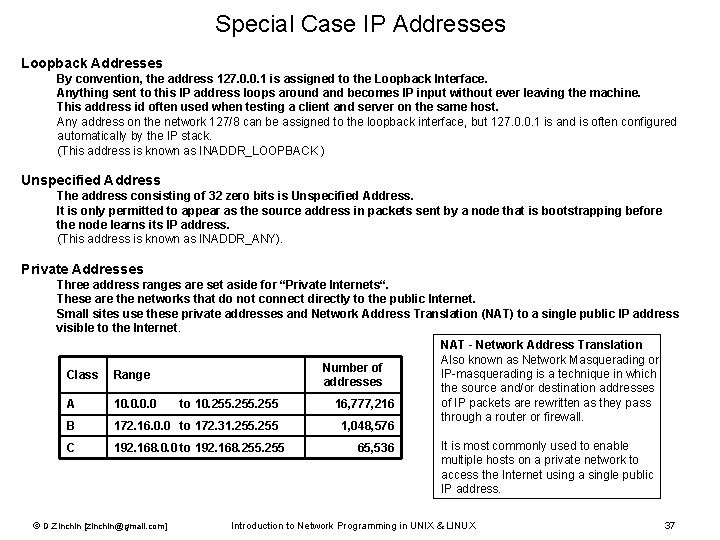
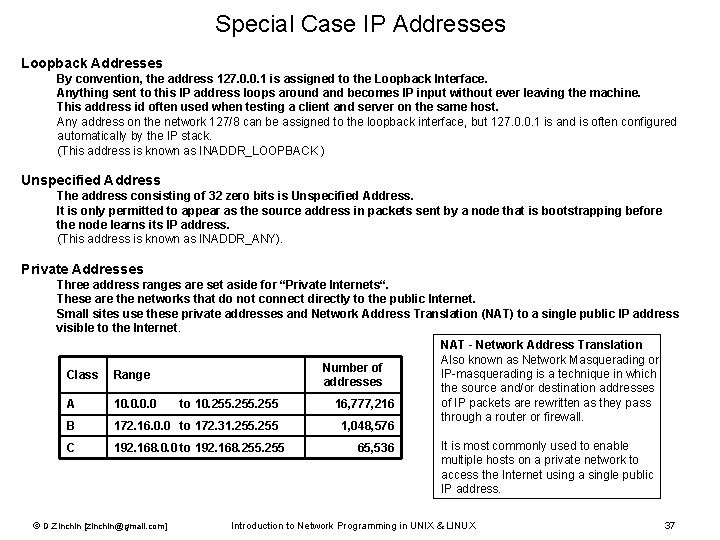
Special Case IP Addresses Loopback Addresses By convention, the address 127. 0. 0. 1 is assigned to the Loopback Interface. Anything sent to this IP address loops around and becomes IP input without ever leaving the machine. This address id often used when testing a client and server on the same host. Any address on the network 127/8 can be assigned to the loopback interface, but 127. 0. 0. 1 is and is often configured automatically by the IP stack. (This address is known as INADDR_LOOPBACK ) Unspecified Address The address consisting of 32 zero bits is Unspecified Address. It is only permitted to appear as the source address in packets sent by a node that is bootstrapping before the node learns its IP address. (This address is known as INADDR_ANY). Private Addresses Three address ranges are set aside for “Private Internets“. These are the networks that do not connect directly to the public Internet. Small sites use these private addresses and Network Address Translation (NAT) to a single public IP address visible to the Internet. NAT - Network Address Translation Also known as Network Masquerading or Number of IP-masquerading is a technique in which Class Range addresses the source and/or destination addresses of IP packets are rewritten as they pass A 10. 0 to 10. 255 16, 777, 216 through a router or firewall. B 172. 16. 0. 0 to 172. 31. 255 1, 048, 576 C 192. 168. 0. 0 to 192. 168. 255 © D. Zinchin [zinchin@gmail. com] 65, 536 It is most commonly used to enable multiple hosts on a private network to access the Internet using a single public IP address. Introduction to Network Programming in UNIX & LINUX 37
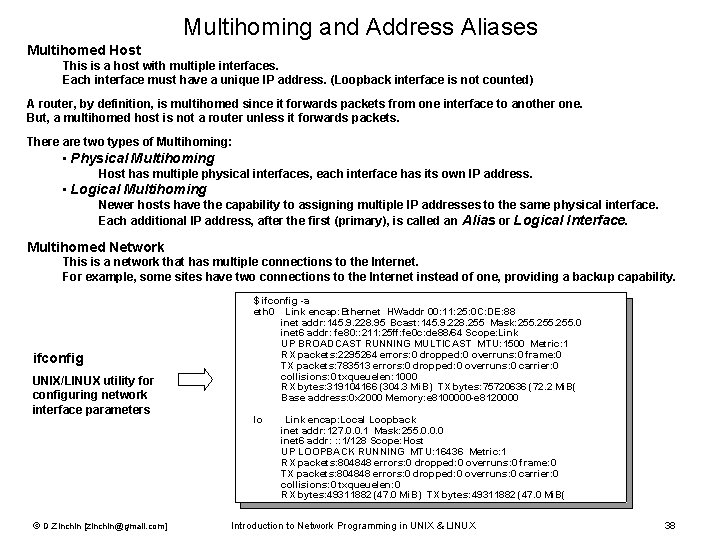
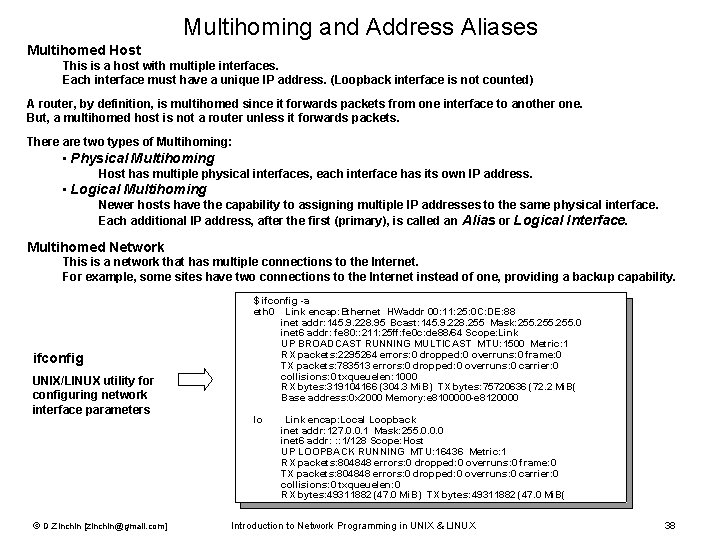
Multihoming and Address Aliases Multihomed Host This is a host with multiple interfaces. Each interface must have a unique IP address. (Loopback interface is not counted) A router, by definition, is multihomed since it forwards packets from one interface to another one. But, a multihomed host is not a router unless it forwards packets. There are two types of Multihoming: • Physical Multihoming Host has multiple physical interfaces, each interface has its own IP address. • Logical Multihoming Newer hosts have the capability to assigning multiple IP addresses to the same physical interface. Each additional IP address, after the first (primary), is called an Alias or Logical Interface. Multihomed Network This is a network that has multiple connections to the Internet. For example, some sites have two connections to the Internet instead of one, providing a backup capability. ifconfig UNIX/LINUX utility for configuring network interface parameters © D. Zinchin [zinchin@gmail. com] $ ifconfig -a eth 0 Link encap: Ethernet HWaddr 00: 11: 25: 0 C: DE: 88 inet addr: 145. 9. 228. 95 Bcast: 145. 9. 228. 255 Mask: 255. 0 inet 6 addr: fe 80: : 211: 25 ff: fe 0 c: de 88/64 Scope: Link UP BROADCAST RUNNING MULTICAST MTU: 1500 Metric: 1 RX packets: 2295264 errors: 0 dropped: 0 overruns: 0 frame: 0 TX packets: 783513 errors: 0 dropped: 0 overruns: 0 carrier: 0 collisions: 0 txqueuelen: 1000 RX bytes: 319104166 (304. 3 Mi. B) TX bytes: 75720636 (72. 2 Mi. B( Base address: 0 x 2000 Memory: e 8100000 -e 8120000 lo Link encap: Local Loopback inet addr: 127. 0. 0. 1 Mask: 255. 0. 0. 0 inet 6 addr: : : 1/128 Scope: Host UP LOOPBACK RUNNING MTU: 16436 Metric: 1 RX packets: 804848 errors: 0 dropped: 0 overruns: 0 frame: 0 TX packets: 804848 errors: 0 dropped: 0 overruns: 0 carrier: 0 collisions: 0 txqueuelen: 0 RX bytes: 49311882 (47. 0 Mi. B) TX bytes: 49311882 (47. 0 Mi. B( Introduction to Network Programming in UNIX & LINUX 38
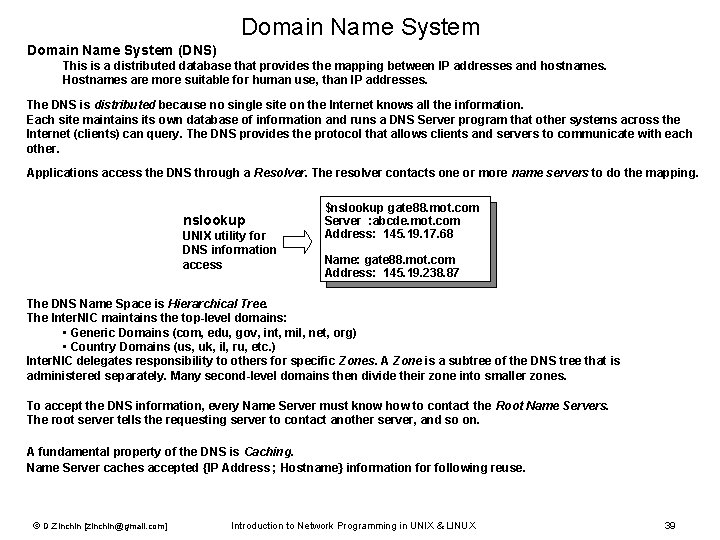
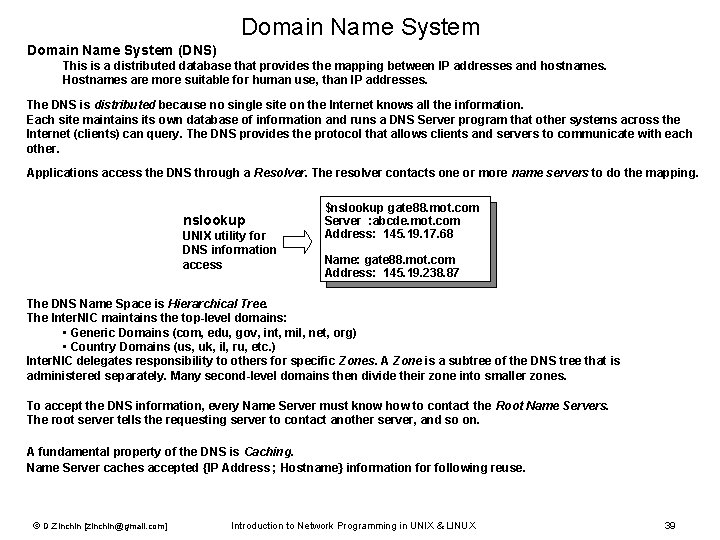
Domain Name System (DNS) This is a distributed database that provides the mapping between IP addresses and hostnames. Hostnames are more suitable for human use, than IP addresses. The DNS is distributed because no single site on the Internet knows all the information. Each site maintains its own database of information and runs a DNS Server program that other systems across the Internet (clients) can query. The DNS provides the protocol that allows clients and servers to communicate with each other. Applications access the DNS through a Resolver. The resolver contacts one or more name servers to do the mapping. nslookup UNIX utility for DNS information access $nslookup gate 88. mot. com Server : abcde. mot. com Address: 145. 19. 17. 68 Name: gate 88. mot. com Address: 145. 19. 238. 87 The DNS Name Space is Hierarchical Tree. The Inter. NIC maintains the top-level domains: • Generic Domains (com, edu, gov, int, mil, net, org) • Country Domains (us, uk, il, ru, etc. ) Inter. NIC delegates responsibility to others for specific Zones. A Zone is a subtree of the DNS tree that is administered separately. Many second-level domains then divide their zone into smaller zones. To accept the DNS information, every Name Server must know how to contact the Root Name Servers. The root server tells the requesting server to contact another server, and so on. A fundamental property of the DNS is Caching. Name Server caches accepted {IP Address ; Hostname} information for following reuse. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 39
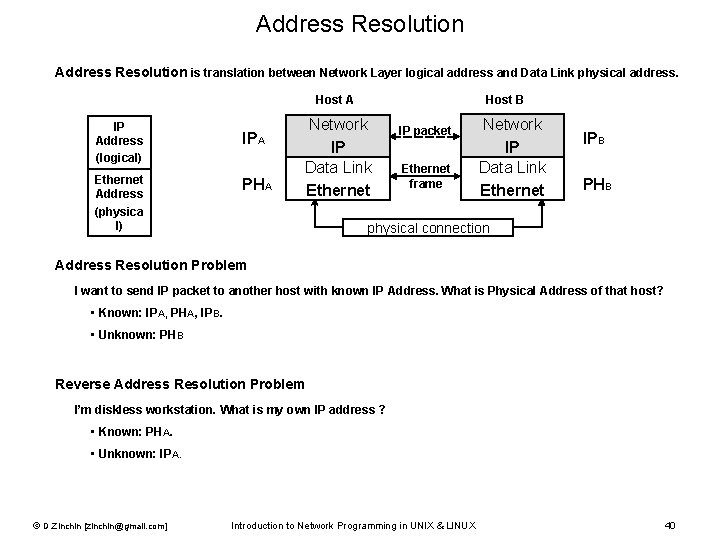
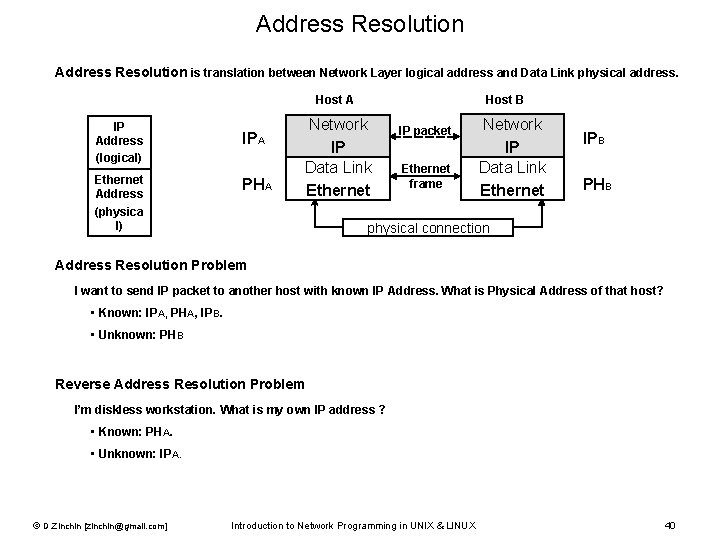
Address Resolution is translation between Network Layer logical address and Data Link physical address. Host A IP Address (logical) Ethernet Address (physica l) IPA PHA Host B Network IP Data Link Ethernet IP packet Ethernet frame Network IP Data Link Ethernet IPB PHB physical connection Address Resolution Problem I want to send IP packet to another host with known IP Address. What is Physical Address of that host? • Known: IPA, PHA, IPB. • Unknown: PHB Reverse Address Resolution Problem I’m diskless workstation. What is my own IP address ? • Known: PHA. • Unknown: IPA. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 40
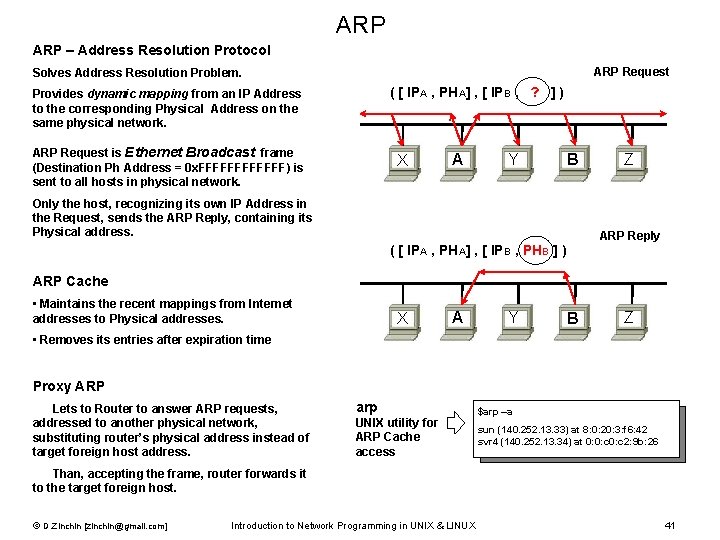
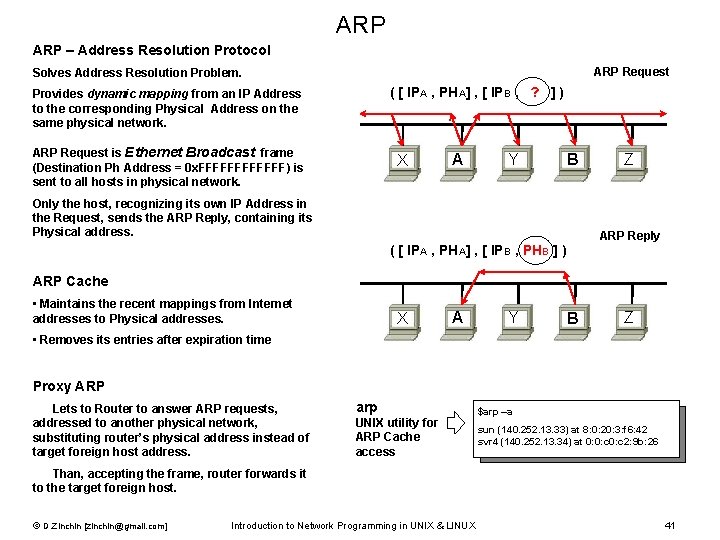
ARP – Address Resolution Protocol ARP Request Solves Address Resolution Problem. ( [ IPA , PHA] , [ IPB , ? ] ) Provides dynamic mapping from an IP Address to the corresponding Physical Address on the same physical network. ARP Request is Ethernet Broadcast frame (Destination Ph Address = 0 x. FFFFFF) is sent to all hosts in physical network. X A Y B Only the host, recognizing its own IP Address in the Request, sends the ARP Reply, containing its Physical address. Z ARP Reply ( [ IPA , PHA] , [ IPB , PHB ] ) ARP Cache • Maintains the recent mappings from Internet addresses to Physical addresses. X A Y B Z • Removes its entries after expiration time Proxy ARP Lets to Router to answer ARP requests, addressed to another physical network, substituting router’s physical address instead of target foreign host address. arp UNIX utility for ARP Cache access $arp –a sun (140. 252. 13. 33) at 8: 0: 20: 3: f 6: 42 svr 4 (140. 252. 13. 34) at 0: 0: c 2: 9 b: 26 Than, accepting the frame, router forwards it to the target foreign host. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 41
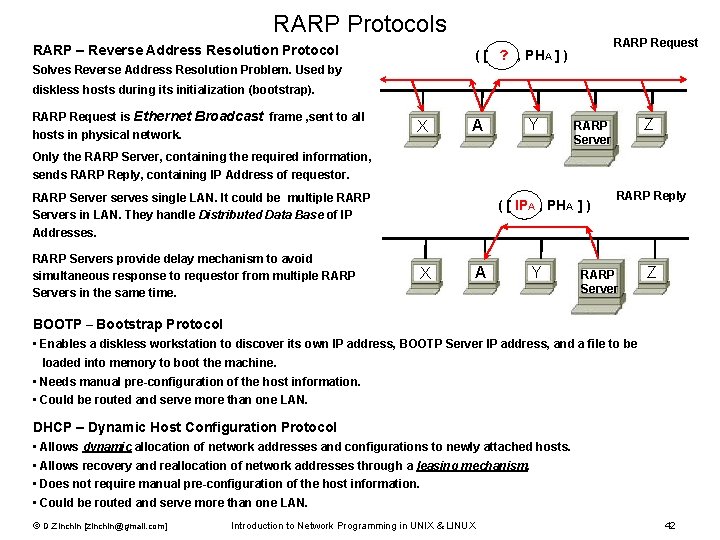
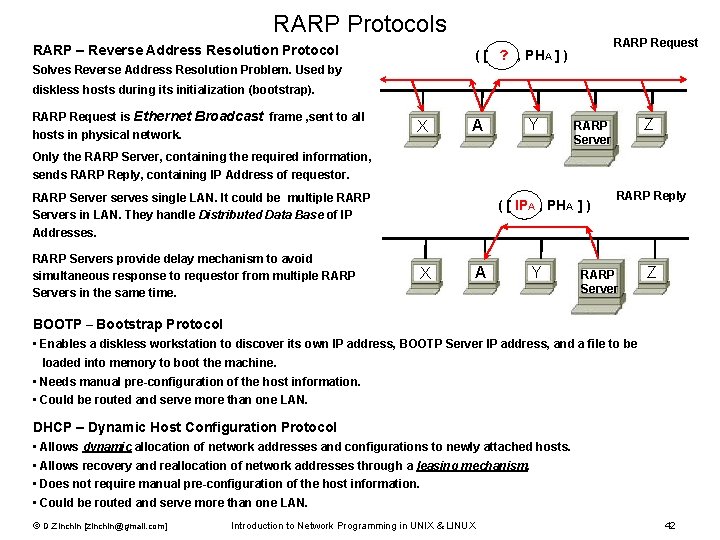
RARP Protocols RARP – Reverse Address Resolution Protocol RARP Request ( [ ? , PHA ] ) Solves Reverse Address Resolution Problem. Used by diskless hosts during its initialization (bootstrap). RARP Request is Ethernet Broadcast frame , sent to all hosts in physical network. X A Y Only the RARP Server, containing the required information, Z RARP Server sends RARP Reply, containing IP Address of requestor. RARP Server serves single LAN. It could be multiple RARP Servers in LAN. They handle Distributed Data Base of IP Addresses. RARP Servers provide delay mechanism to avoid simultaneous response to requestor from multiple RARP Servers in the same time. ( [ IPA , PHA ] ) X A Y RARP Reply RARP Server Z BOOTP – Bootstrap Protocol • Enables a diskless workstation to discover its own IP address, BOOTP Server IP address, and a file to be loaded into memory to boot the machine. • Needs manual pre-configuration of the host information. • Could be routed and serve more than one LAN. DHCP – Dynamic Host Configuration Protocol • Allows dynamic allocation of network addresses and configurations to newly attached hosts. • Allows recovery and reallocation of network addresses through a leasing mechanism. • Does not require manual pre-configuration of the host information. • Could be routed and serve more than one LAN. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 42
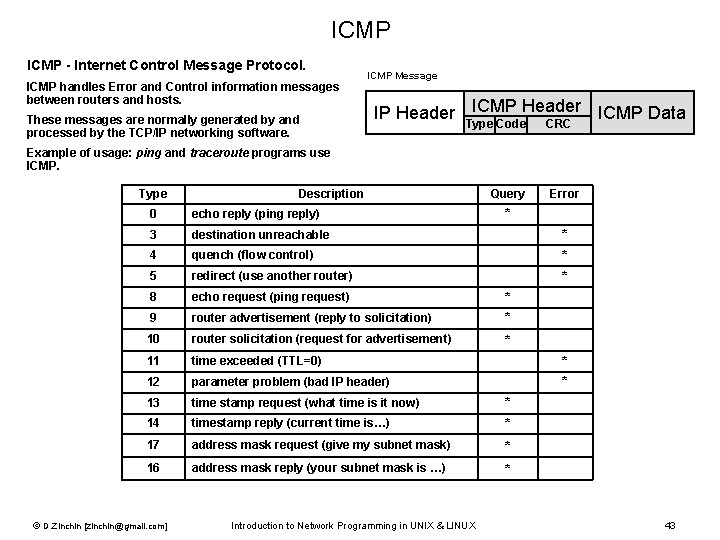
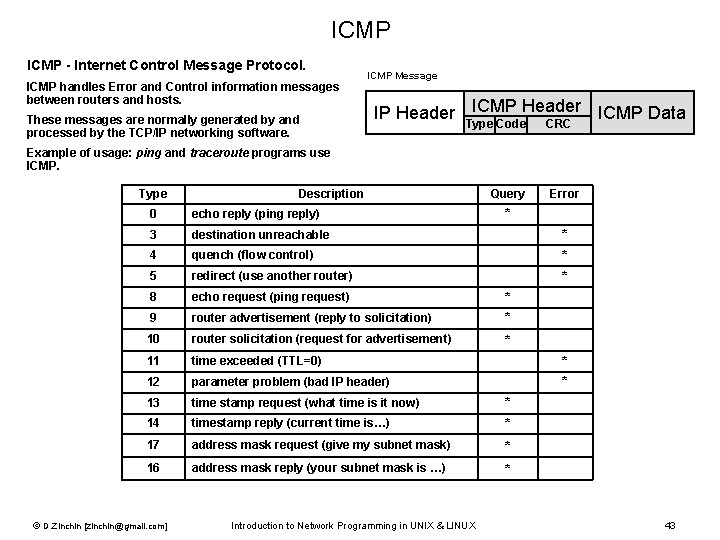
ICMP - Internet Control Message Protocol. ICMP handles Error and Control information messages between routers and hosts. These messages are normally generated by and processed by the TCP/IP networking software. ICMP Message ICMP Header ICMP Data IP Header Type Code CRC Example of usage: ping and traceroute programs use ICMP. Type Description Query Error * * * * 0 echo reply (ping reply) 3 destination unreachable 4 quench (flow control) 5 redirect (use another router) 8 echo request (ping request) 9 router advertisement (reply to solicitation) 10 router solicitation (request for advertisement) 11 time exceeded (TTL=0) 12 parameter problem (bad IP header) 13 time stamp request (what time is it now) 14 timestamp reply (current time is…) * * * 17 address mask request (give my subnet mask) * 16 address mask reply (your subnet mask is …) * © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 43
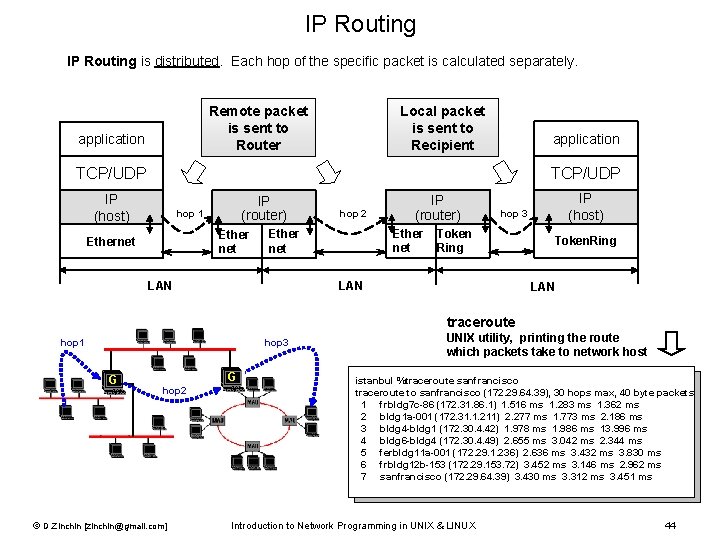
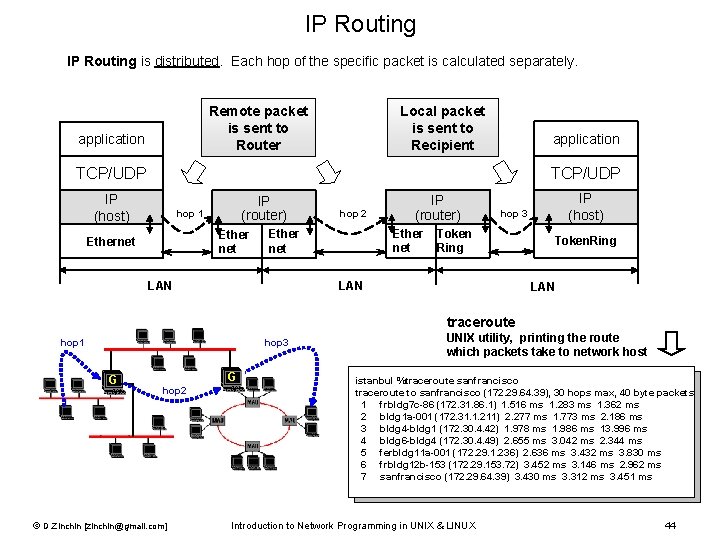
IP Routing is distributed. Each hop of the specific packet is calculated separately. Remote packet is sent to Router application Local packet is sent to Recipient application TCP/UDP IP (host) IP (router) hop 1 Ether net Ethernet hop 2 IP (host) hop 3 Ether Token Ring net Ether net LAN IP (router) LAN Token. Ring LAN traceroute hop 1 hop 3 G G hop 2 © D. Zinchin [zinchin@gmail. com] UNIX utility, printing the route which packets take to network host istanbul %traceroute sanfrancisco traceroute to sanfrancisco (172. 29. 64. 39), 30 hops max, 40 byte packets 1 frbldg 7 c-86 (172. 31. 86. 1) 1. 516 ms 1. 283 ms 1. 362 ms 2 bldg 1 a-001 (172. 31. 1. 211) 2. 277 ms 1. 773 ms 2. 186 ms 3 bldg 4 -bldg 1 (172. 30. 4. 42) 1. 978 ms 1. 986 ms 13. 996 ms 4 bldg 6 -bldg 4 (172. 30. 4. 49) 2. 655 ms 3. 042 ms 2. 344 ms 5 ferbldg 11 a-001 (172. 29. 1. 236) 2. 636 ms 3. 432 ms 3. 830 ms 6 frbldg 12 b-153 (172. 29. 153. 72) 3. 452 ms 3. 146 ms 2. 962 ms 7 sanfrancisco (172. 29. 64. 39) 3. 430 ms 3. 312 ms 3. 451 ms Introduction to Network Programming in UNIX & LINUX 44
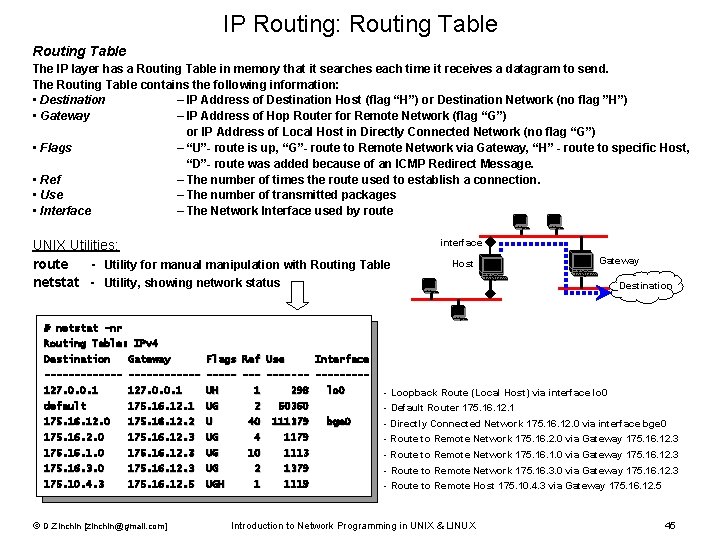
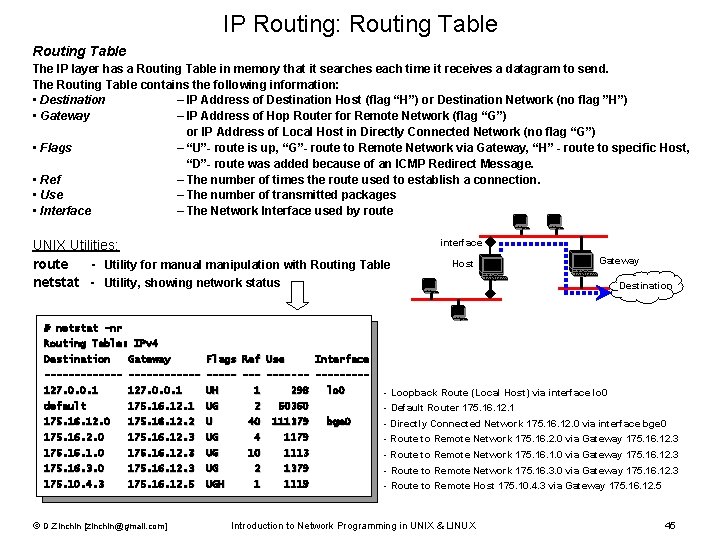
IP Routing: Routing Table The IP layer has a Routing Table in memory that it searches each time it receives a datagram to send. The Routing Table contains the following information: • Destination – IP Address of Destination Host (flag “H”) or Destination Network (no flag ”H”) • Gateway – IP Address of Hop Router for Remote Network (flag “G”) or IP Address of Local Host in Directly Connected Network (no flag “G”) • Flags – “U”- route is up, “G”- route to Remote Network via Gateway, “H” - route to specific Host, “D”- route was added because of an ICMP Redirect Message. • Ref – The number of times the route used to establish a connection. • Use – The number of transmitted packages • Interface – The Network Interface used by route UNIX Utilities: route - Utility for manual manipulation with Routing Table netstat - Utility, showing network status interface Host Gateway Destination # netstat -nr Routing Table: IPv 4 Destination Gateway Flags Ref Use Interface ------- ------- ----127. 0. 0. 1 UH 1 298 default 175. 16. 12. 1 UG 2 50360 175. 16. 12. 2 U 40 111379 175. 16. 2. 0 175. 16. 12. 3 UG 4 1179 175. 16. 1. 0 175. 16. 12. 3 UG 10 1113 175. 16. 3. 0 175. 16. 12. 3 UG 2 1379 175. 10. 4. 3 175. 16. 12. 5 UGH 1 1119 © D. Zinchin [zinchin@gmail. com] lo 0 bge 0 - Loopback Route (Local Host) via interface lo 0 - Default Router 175. 16. 12. 1 - Directly Connected Network 175. 16. 12. 0 via interface bge 0 - Route to Remote Network 175. 16. 2. 0 via Gateway 175. 16. 12. 3 - Route to Remote Network 175. 16. 1. 0 via Gateway 175. 16. 12. 3 - Route to Remote Network 175. 16. 3. 0 via Gateway 175. 16. 12. 3 - Route to Remote Host 175. 10. 4. 3 via Gateway 175. 16. 12. 5 Introduction to Network Programming in UNIX & LINUX 45
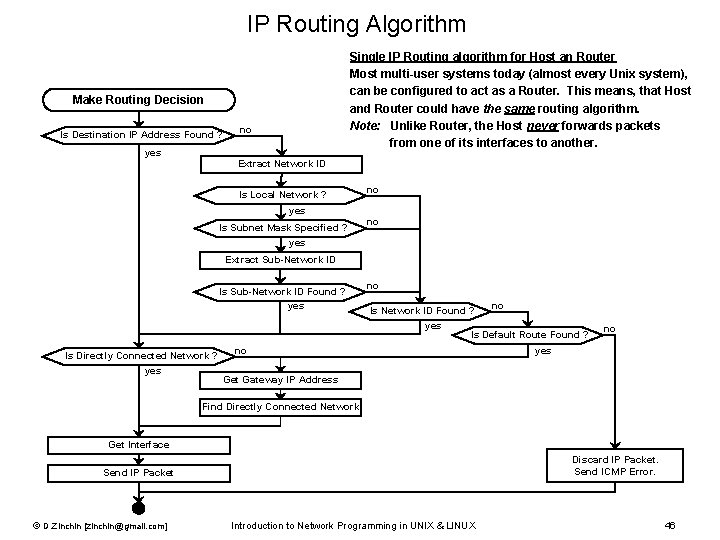
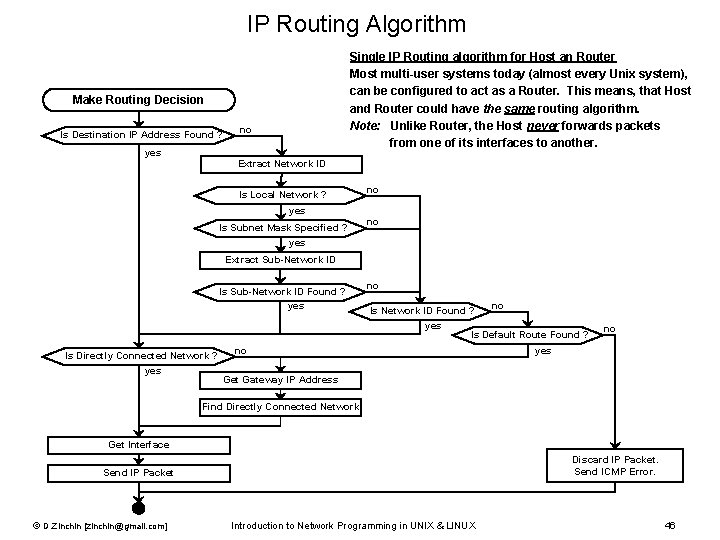
IP Routing Algorithm Single IP Routing algorithm for Host an Router Most multi-user systems today (almost every Unix system), can be configured to act as a Router. This means, that Host and Router could have the same routing algorithm. Note: Unlike Router, the Host never forwards packets from one of its interfaces to another. Make Routing Decision Is Destination IP Address Found ? yes no Extract Network ID Is Local Network ? yes Is Subnet Mask Specified ? no no yes Extract Sub-Network ID Is Sub-Network ID Found ? yes no Is Network ID Found ? yes Is Directly Connected Network ? yes no Is Default Route Found ? no no yes Get Gateway IP Address Find Directly Connected Network Get Interface Discard IP Packet. Send ICMP Error. Send IP Packet © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 46
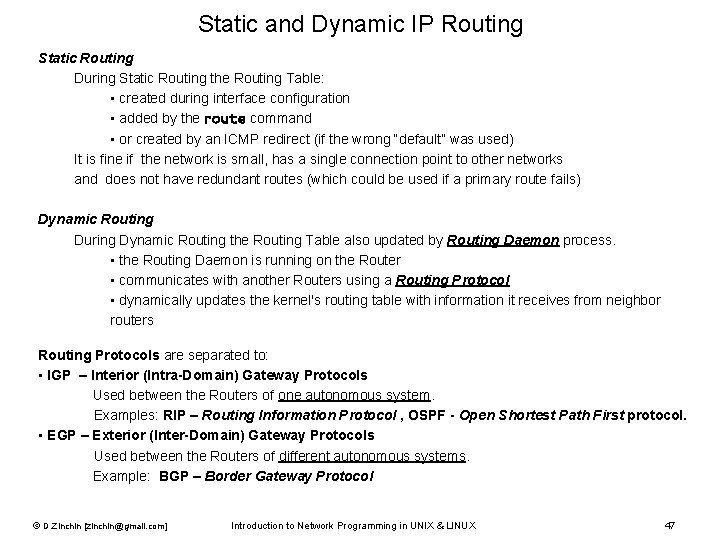
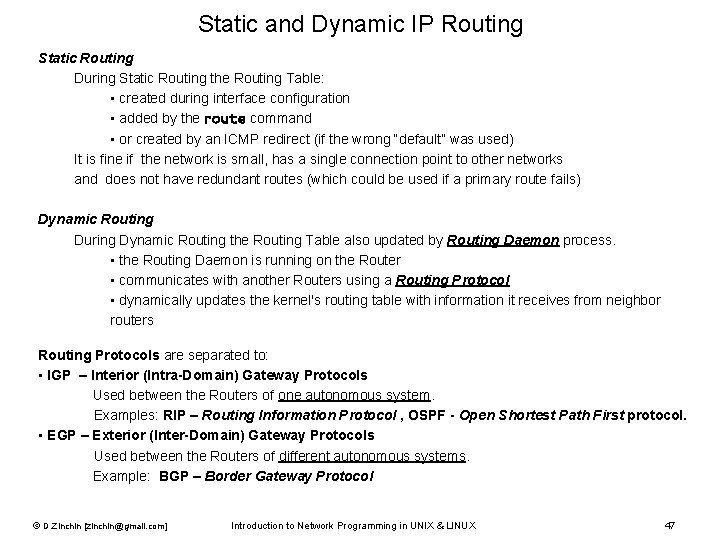
Static and Dynamic IP Routing Static Routing During Static Routing the Routing Table: • created during interface configuration • added by the route command • or created by an ICMP redirect (if the wrong “default” was used) It is fine if the network is small, has a single connection point to other networks and does not have redundant routes (which could be used if a primary route fails) Dynamic Routing During Dynamic Routing the Routing Table also updated by Routing Daemon process. • the Routing Daemon is running on the Router • communicates with another Routers using a Routing Protocol • dynamically updates the kernel's routing table with information it receives from neighbor routers Routing Protocols are separated to: • IGP – Interior (Intra-Domain) Gateway Protocols Used between the Routers of one autonomous system. Examples: RIP – Routing Information Protocol , OSPF - Open Shortest Path First protocol. • EGP – Exterior (Inter-Domain) Gateway Protocols Used between the Routers of different autonomous systems. Example: BGP – Border Gateway Protocol © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 47
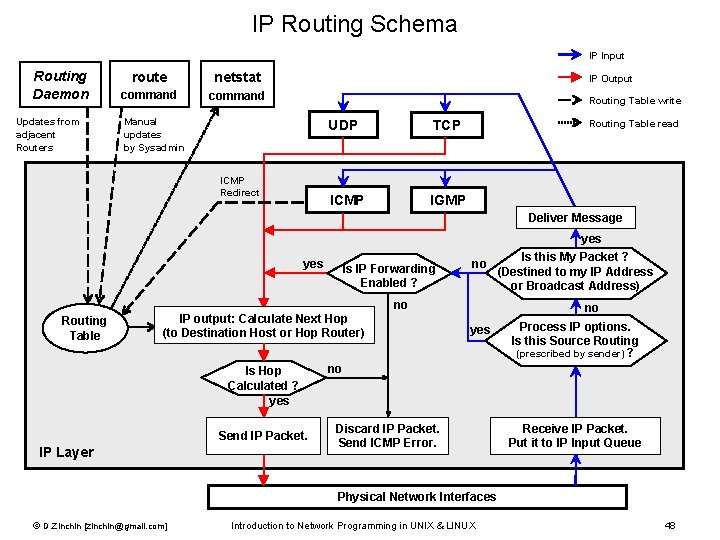
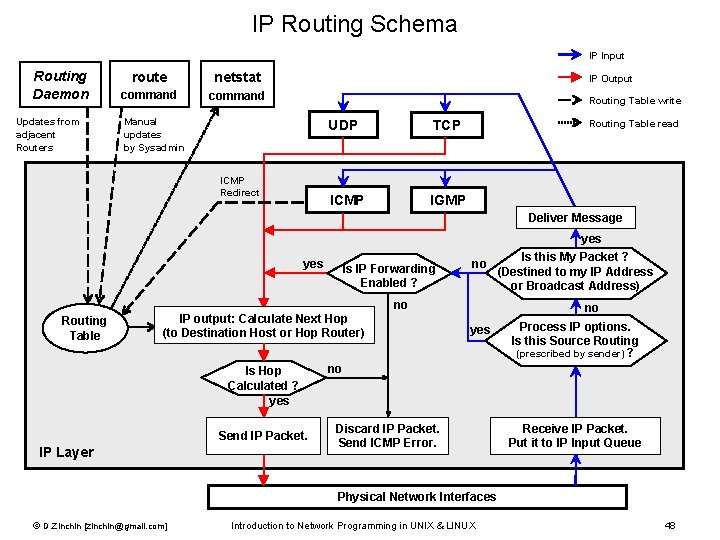
IP Routing Schema IP Input Routing Daemon Updates from adjacent Routers route netstat command IP Output Routing Table write Manual updates by Sysadmin ICMP Redirect UDP TCP ICMP IGMP Routing Table read Deliver Message yes Is IP Forwarding Enabled ? no no Routing Table IP output: Calculate Next Hop (to Destination Host or Hop Router) Is Hop Calculated ? yes Send IP Packet. IP Layer Is this My Packet ? (Destined to my IP Address or Broadcast Address) no yes Process IP options. Is this Source Routing (prescribed by sender) ? no Discard IP Packet. Send ICMP Error. Receive IP Packet. Put it to IP Input Queue Physical Network Interfaces © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 48
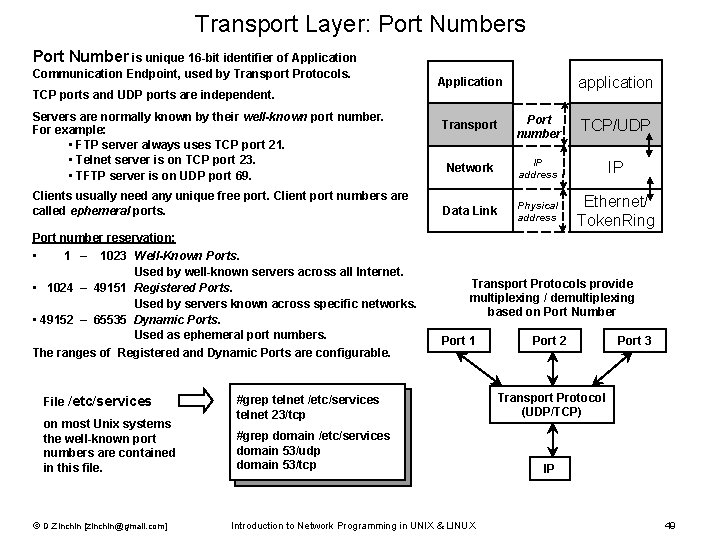
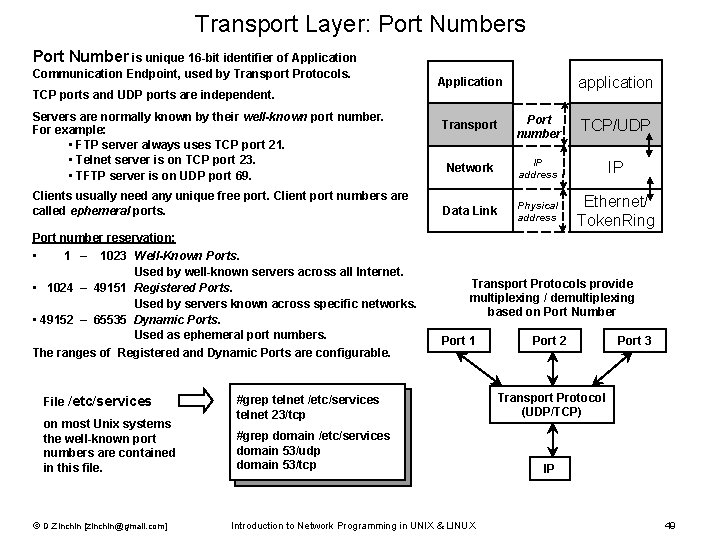
Transport Layer: Port Numbers Port Number is unique 16 -bit identifier of Application Communication Endpoint, used by Transport Protocols. TCP ports and UDP ports are independent. Servers are normally known by their well-known port number. For example: • FTP server always uses TCP port 21. • Telnet server is on TCP port 23. • TFTP server is on UDP port 69. Clients usually need any unique free port. Client port numbers are called ephemeral ports. application Application Transport Port number TCP/UDP Network IP address IP Data Link Physical address Ethernet/ Token. Ring Port number reservation: • 1 – 1023 Well-Known Ports. Used by well-known servers across all Internet. • 1024 – 49151 Registered Ports. Used by servers known across specific networks. • 49152 – 65535 Dynamic Ports. Used as ephemeral port numbers. The ranges of Registered and Dynamic Ports are configurable. File /etc/services on most Unix systems the well-known port numbers are contained in this file. © D. Zinchin [zinchin@gmail. com] Transport Protocols provide multiplexing / demultiplexing based on Port Number Port 1 #grep telnet /etc/services telnet 23/tcp #grep domain /etc/services domain 53/udp domain 53/tcp Introduction to Network Programming in UNIX & LINUX Port 2 Port 3 Transport Protocol (UDP/TCP) IP 49
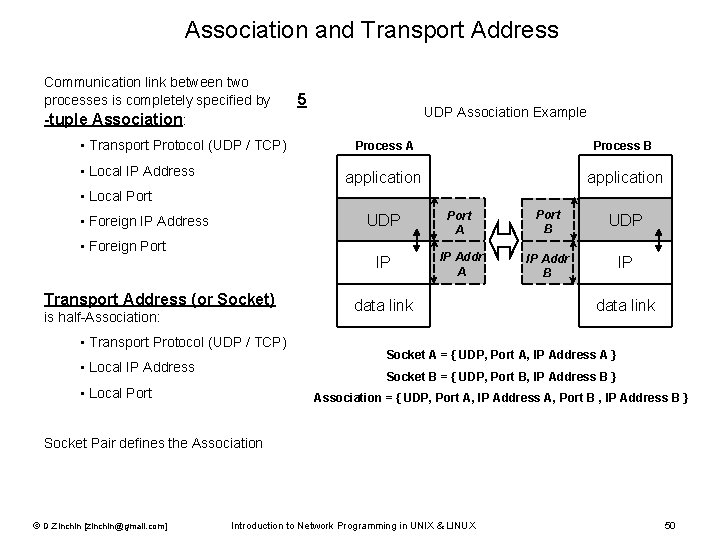
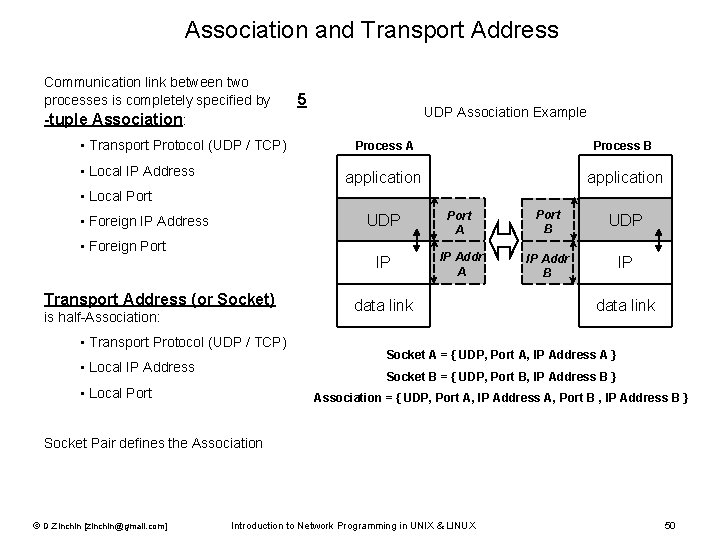
Association and Transport Address Communication link between two processes is completely specified by -tuple Association: • Transport Protocol (UDP / TCP) • Local IP Address 5 UDP Association Example Process A Process B application • Local Port • Foreign IP Address • Foreign Port Transport Address (or Socket) is half-Association: • Transport Protocol (UDP / TCP) • Local IP Address UDP Port A Port B UDP IP IP Addr A IP Addr B IP data link Socket A = { UDP, Port A, IP Address A } Socket B = { UDP, Port B, IP Address B } • Local Port Association = { UDP, Port A, IP Address A, Port B , IP Address B } Socket Pair defines the Association © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 50
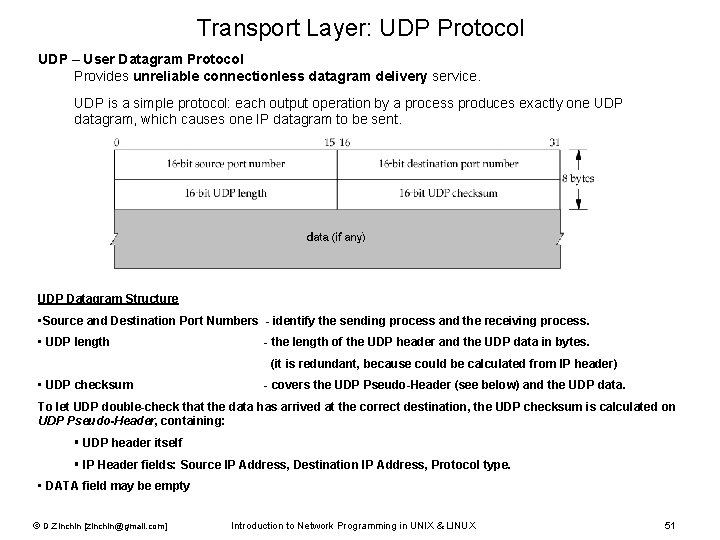
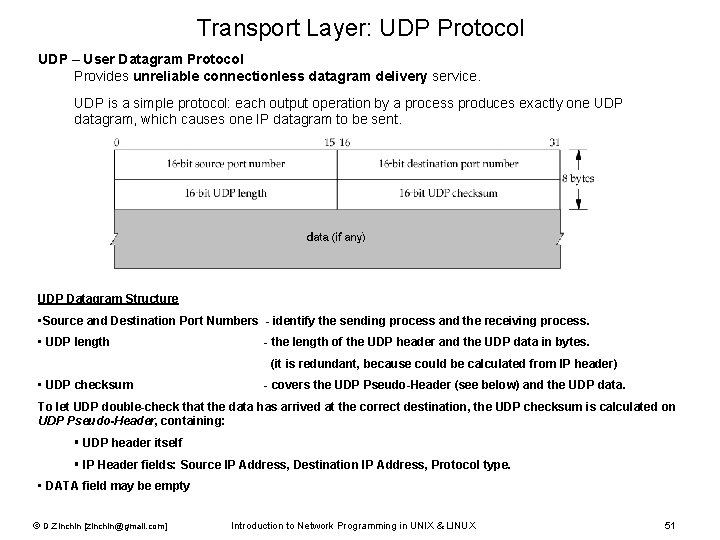
Transport Layer: UDP Protocol UDP – User Datagram Protocol Provides unreliable connectionless datagram delivery service. UDP is a simple protocol: each output operation by a process produces exactly one UDP datagram, which causes one IP datagram to be sent. UDP Datagram Structure • Source and Destination Port Numbers - identify the sending process and the receiving process. • UDP length - the length of the UDP header and the UDP data in bytes. (it is redundant, because could be calculated from IP header) • UDP checksum - covers the UDP Pseudo-Header (see below) and the UDP data. To let UDP double-check that the data has arrived at the correct destination, the UDP checksum is calculated on UDP Pseudo-Header, containing: § UDP header itself § IP Header fields: Source IP Address, Destination IP Address, Protocol type. • DATA field may be empty © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 51
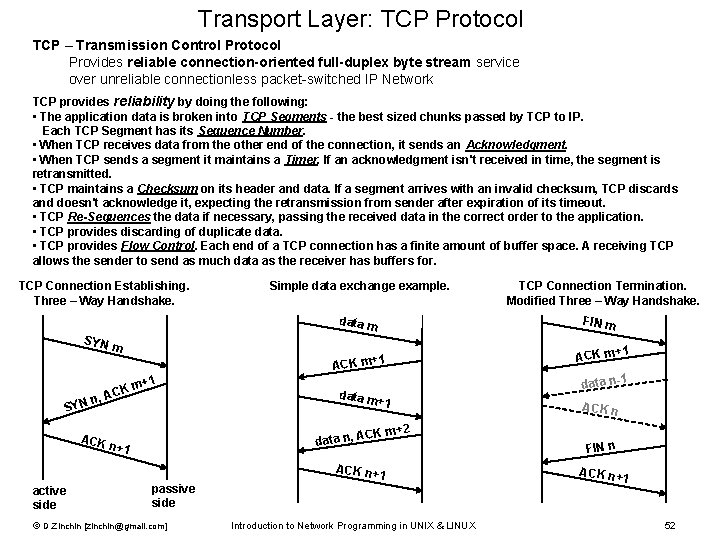
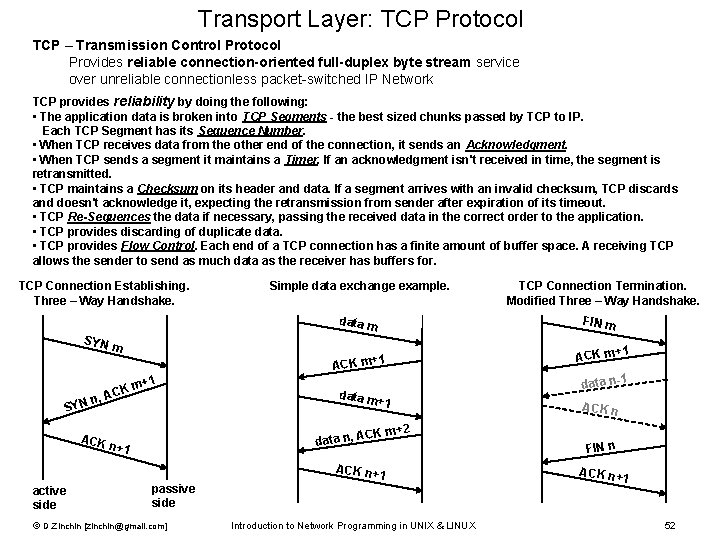
Transport Layer: TCP Protocol TCP – Transmission Control Protocol Provides reliable connection-oriented full-duplex byte stream service over unreliable connectionless packet-switched IP Network TCP provides reliability by doing the following: • The application data is broken into TCP Segments - the best sized chunks passed by TCP to IP. Each TCP Segment has its Sequence Number. • When TCP receives data from the other end of the connection, it sends an Acknowledgment. • When TCP sends a segment it maintains a Timer. If an acknowledgment isn't received in time, the segment is retransmitted. • TCP maintains a Checksum on its header and data. If a segment arrives with an invalid checksum, TCP discards and doesn't acknowledge it, expecting the retransmission from sender after expiration of its timeout. • TCP Re-Sequences the data if necessary, passing the received data in the correct order to the application. • TCP provides discarding of duplicate data. • TCP provides Flow Control. Each end of a TCP connection has a finite amount of buffer space. A receiving TCP allows the sender to send as much data as the receiver has buffers for. TCP Connection Establishing. Three – Way Handshake. Simple data exchange example. data m SYN n, SYN m m ACK 1 ACK m+ +1 data m +1 CK m+2 data n, A ACK n+1 ACK n+ 1 active side passive side © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX TCP Connection Termination. Modified Three – Way Handshake. FIN m 1 ACK m+ data n-1 ACK n FIN n ACK n+ 1 52
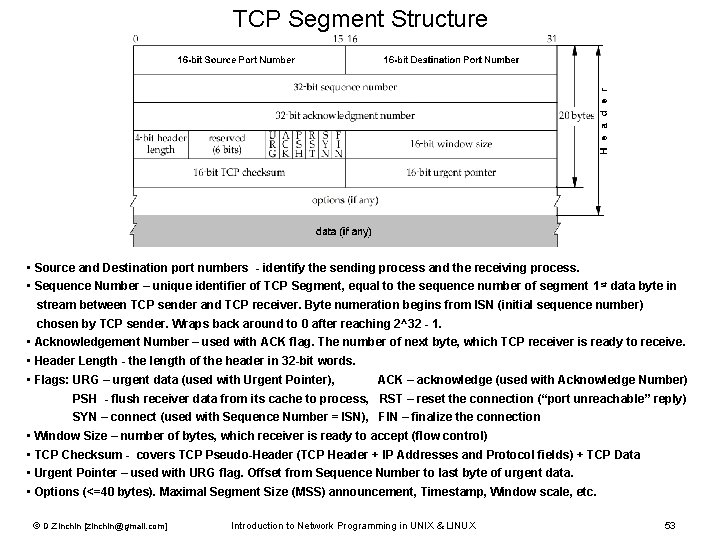
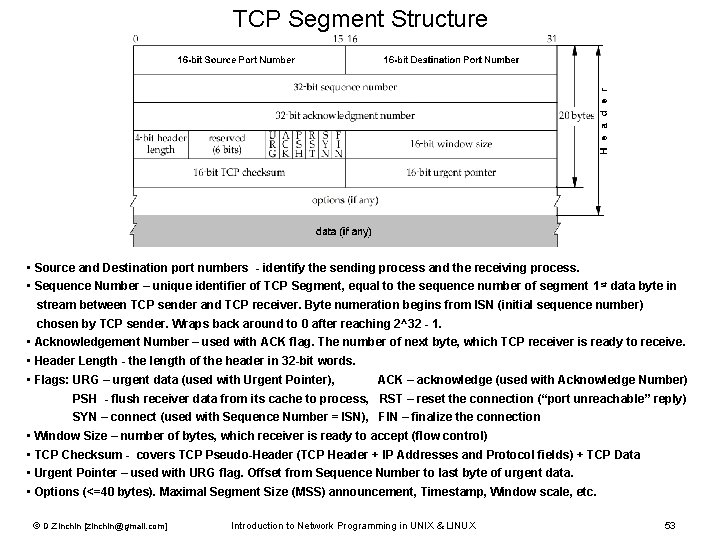
TCP Segment Structure • Source and Destination port numbers - identify the sending process and the receiving process. • Sequence Number – unique identifier of TCP Segment, equal to the sequence number of segment 1 st data byte in stream between TCP sender and TCP receiver. Byte numeration begins from ISN (initial sequence number) chosen by TCP sender. Wraps back around to 0 after reaching 2^32 - 1. • Acknowledgement Number – used with ACK flag. The number of next byte, which TCP receiver is ready to receive. • Header Length - the length of the header in 32 -bit words. • Flags: URG – urgent data (used with Urgent Pointer), ACK – acknowledge (used with Acknowledge Number) PSH - flush receiver data from its cache to process, RST – reset the connection (“port unreachable” reply) SYN – connect (used with Sequence Number = ISN), FIN – finalize the connection • Window Size – number of bytes, which receiver is ready to accept (flow control) • TCP Checksum - covers TCP Pseudo-Header (TCP Header + IP Addresses and Protocol fields) + TCP Data • Urgent Pointer – used with URG flag. Offset from Sequence Number to last byte of urgent data. • Options (<=40 bytes). Maximal Segment Size (MSS) announcement, Timestamp, Window scale, etc. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 53
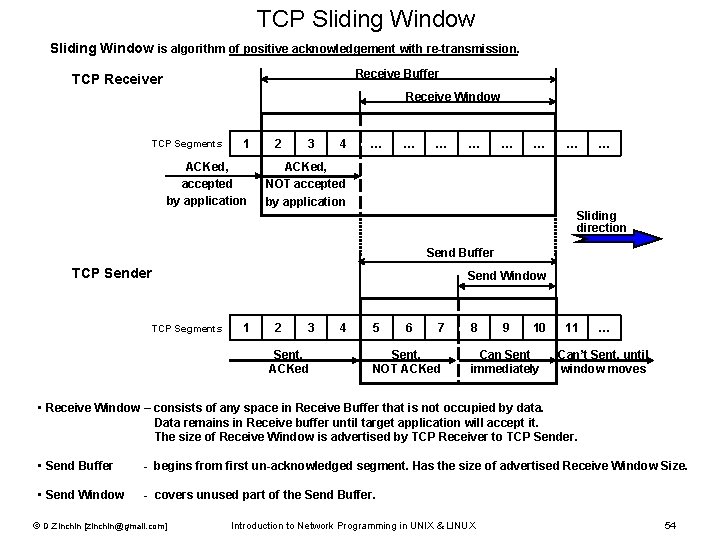
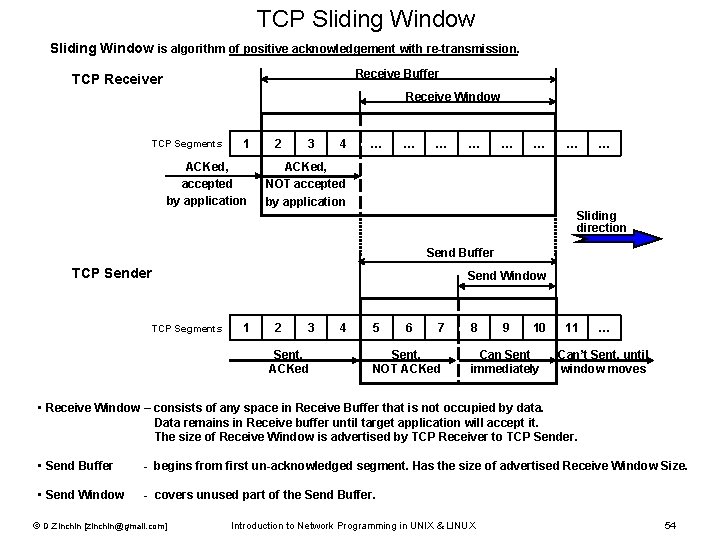
TCP Sliding Window is algorithm of positive acknowledgement with re-transmission. Receive Buffer TCP Receiver Receive Window TCP Segments 1 ACKed, accepted by application 2 3 4 … … … … ACKed, NOT accepted by application Sliding direction Send Buffer TCP Sender Send Window TCP Segments 1 2 3 Sent, ACKed 4 5 6 7 Sent, NOT ACKed 8 9 10 Can Sent immediately 11 … Can’t Sent, until window moves • Receive Window – consists of any space in Receive Buffer that is not occupied by data. Data remains in Receive buffer until target application will accept it. The size of Receive Window is advertised by TCP Receiver to TCP Sender. • Send Buffer - begins from first un-acknowledged segment. Has the size of advertised Receive Window Size. • Send Window - covers unused part of the Send Buffer. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 54
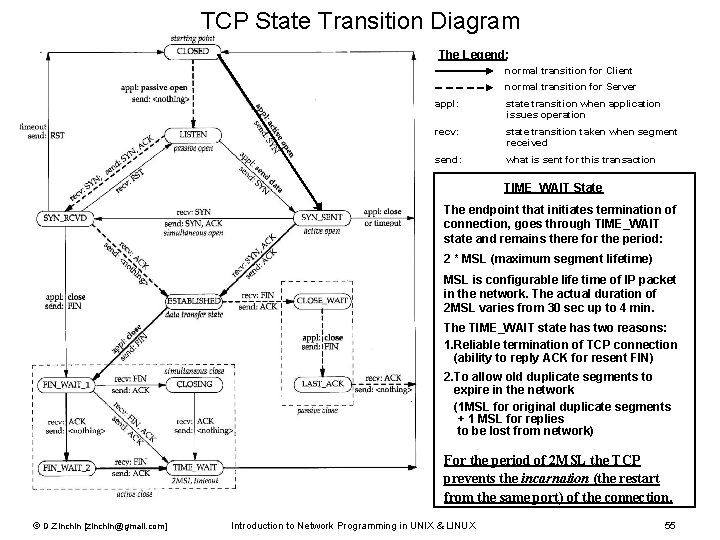
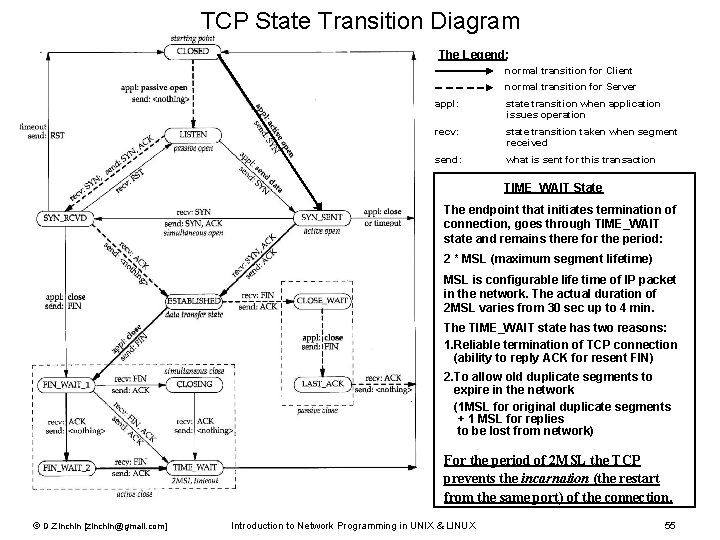
TCP State Transition Diagram The Legend: normal transition for Client normal transition for Server appl: state transition when application issues operation recv: state transition taken when segment received send: what is sent for this transaction TIME_WAIT State The endpoint that initiates termination of connection, goes through TIME_WAIT state and remains there for the period: 2 * MSL (maximum segment lifetime) MSL is configurable life time of IP packet in the network. The actual duration of 2 MSL varies from 30 sec up to 4 min. The TIME_WAIT state has two reasons: 1. Reliable termination of TCP connection (ability to reply ACK for resent FIN) 2. To allow old duplicate segments to expire in the network (1 MSL for original duplicate segments + 1 MSL for replies to be lost from network) For the period of 2 MSL the TCP prevents the incarnation (the restart from the same port) of the connection. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 55
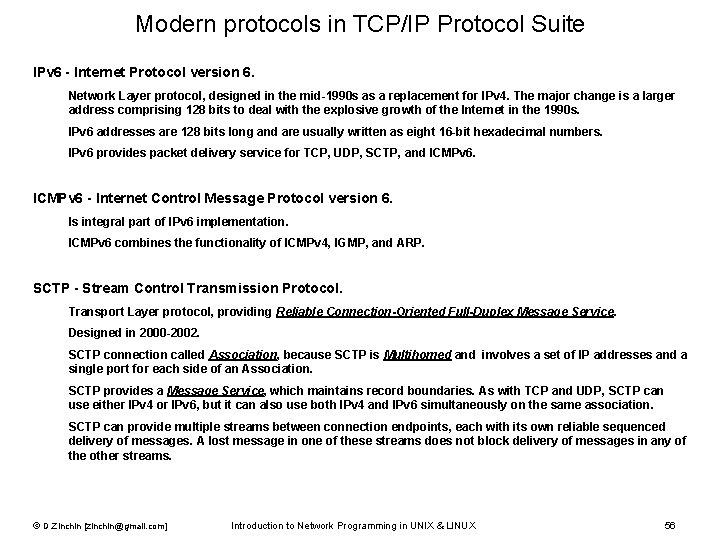
Modern protocols in TCP/IP Protocol Suite IPv 6 - Internet Protocol version 6. Network Layer protocol, designed in the mid-1990 s as a replacement for IPv 4. The major change is a larger address comprising 128 bits to deal with the explosive growth of the Internet in the 1990 s. IPv 6 addresses are 128 bits long and are usually written as eight 16 -bit hexadecimal numbers. IPv 6 provides packet delivery service for TCP, UDP, SCTP, and ICMPv 6 - Internet Control Message Protocol version 6. Is integral part of IPv 6 implementation. ICMPv 6 combines the functionality of ICMPv 4, IGMP, and ARP. SCTP - Stream Control Transmission Protocol. Transport Layer protocol, providing Reliable Connection-Oriented Full-Duplex Message Service. Designed in 2000 -2002. SCTP connection called Association, because SCTP is Multihomed and involves a set of IP addresses and a single port for each side of an Association. SCTP provides a Message Service, which maintains record boundaries. As with TCP and UDP, SCTP can use either IPv 4 or IPv 6, but it can also use both IPv 4 and IPv 6 simultaneously on the same association. SCTP can provide multiple streams between connection endpoints, each with its own reliable sequenced delivery of messages. A lost message in one of these streams does not block delivery of messages in any of the other streams. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 56
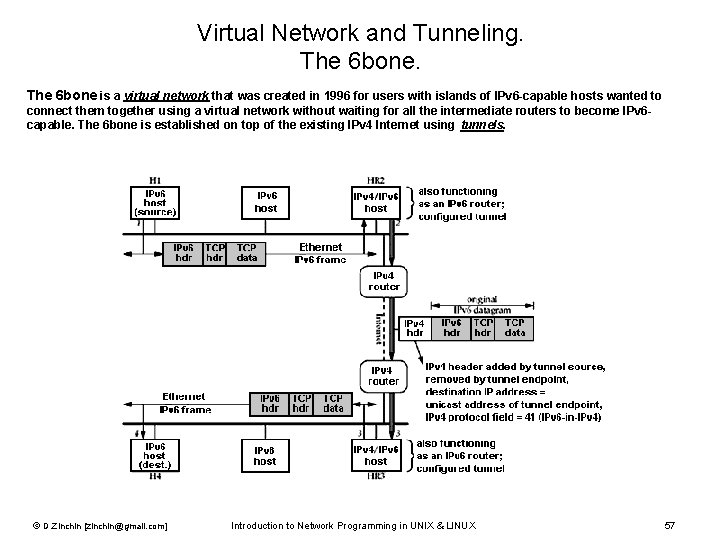
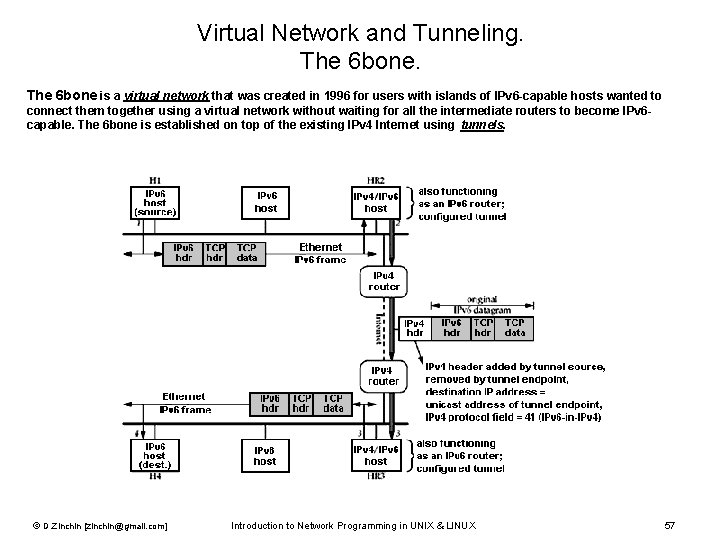
Virtual Network and Tunneling. The 6 bone is a virtual network that was created in 1996 for users with islands of IPv 6 -capable hosts wanted to connect them together using a virtual network without waiting for all the intermediate routers to become IPv 6 capable. The 6 bone is established on top of the existing IPv 4 Internet using tunnels. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 57
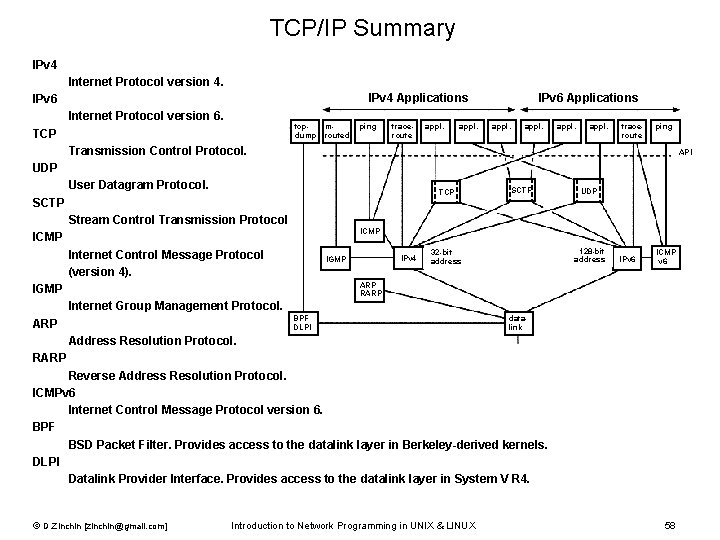
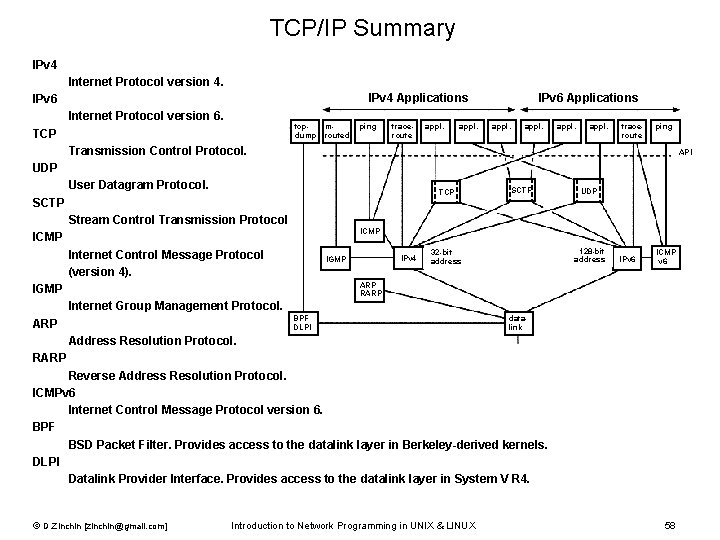
TCP/IP Summary IPv 4 Internet Protocol version 4. IPv 4 Applications IPv 6 Internet Protocol version 6. tcpdump TCP mrouted ping traceroute appl. IPv 6 Applications appl. traceroute ping Transmission Control Protocol. API UDP User Datagram Protocol. TCP SCTP UDP Stream Control Transmission Protocol. ICMP Internet Control Message Protocol (version 4). IPv 4 IGMP 128 -bit address 32 -bit address IPv 6 ICMP v 6 ARP RARP IGMP Internet Group Management Protocol. BPF DLPI ARP datalink Address Resolution Protocol. RARP Reverse Address Resolution Protocol. ICMPv 6 Internet Control Message Protocol version 6. BPF BSD Packet Filter. Provides access to the datalink layer in Berkeley-derived kernels. DLPI Datalink Provider Interface. Provides access to the datalink layer in System V R 4. © D. Zinchin [zinchin@gmail. com] Introduction to Network Programming in UNIX & LINUX 58