Introduction to Mobile IP Golden G Richard III
Introduction to Mobile IP Golden G. Richard III, Ph. D. University of New Orleans (With thanks to Sumi Helal @ U of F)
2 For More Information. . . 4 Mobile IP: The Internet Unplugged, by James D. Solomon, Prentice Hall. 4 "Mobility Support in IPv 6, " C. Perkins and D. Johnson, Proceedings of the Second Annual International Conference on Mobile Computing and Networking (Mobi. Com '96). 4 "Supporting Mobility in Mosquito. Net, " M. Baker et al, Proceedings of the 1996 USENIX Technical Conference. 4 "Mobile Networking Through Mobile IP, " C. Perkins, http: //www. computer. org/internet/v 2 n 1/perkins. htm
3 Mobile Computing: Why? 4 Dream: Seamless, ubiquitous network access for mobile hosts – Laptop computers – PDAs – Electronic books 4 Impacts: – Tourism (electronic tour guides) – Field research – Collaborative applications – Lots more 4 Computing in your garden!!
4 Why Mobile IP? 4 Need a protocol which allows network connectivity across host movement 4 Protocol to enable mobility must not require massive changes to router software, etc. 4 Must be compatible with large installed base of IPv 4 networks/hosts 4 Confine changes to mobile hosts and a few support hosts which enable mobility
5 Talk Overview 4 Will cover: – Why IP routing breaks under mobility – Mobile IPv 4 basics – Some Mobile IP security issues 4 Won't cover: – Details of IP routing – IPv 6 in detail – Low-level protocol details (message formats, headers, etc. ) – All of the Mobile IP-related security issues – Any of the other problems with mobile computing!
6 Internet Protocol (IP) 4 Network layer, "best-effort" packet delivery 4 Supports UDP and TCP (transport layer protocols) 4 IP host addresses consist of two parts – network id + host id 4 By design, IP host address is tied to home network address – Hosts are assumed to be wired, immobile – Intermediate routers look only at network address – Mobility without a change in IP address results in un-route-able packets
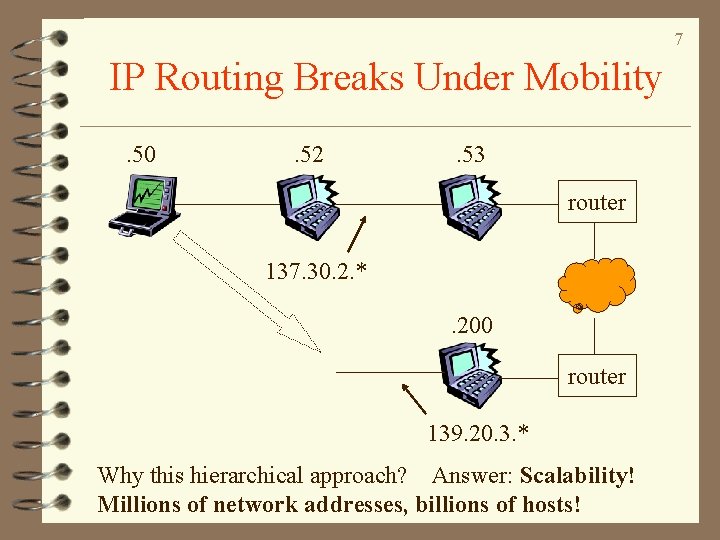
7 IP Routing Breaks Under Mobility. 50 . 52 . 53 router 137. 30. 2. *. 200 router 139. 20. 3. * Why this hierarchical approach? Answer: Scalability! Millions of network addresses, billions of hosts!
Mobile IP: Basics 8 4 Proposed by IETF (Internet Engineering Task Force) – Standards development body for the Internet 4 Mobile IP allows a mobile host to move about without changing its permanent IP address 4 Each mobile host has a home agent on its home network 4 Mobile host establishes a care-of address when it's away from home
9 Mobile IP: Basics, Cont. 4 Correspondent host is a host that wants to send packets to the mobile host 4 Correspondent host sends packets to the mobile host’s IP permanent address 4 These packets are routed to the mobile host’s home network 4 Home agent forwards IP packets for mobile host to current care-of address 4 Mobile host sends packets directly to correspondent, using permanent home IP as source IP
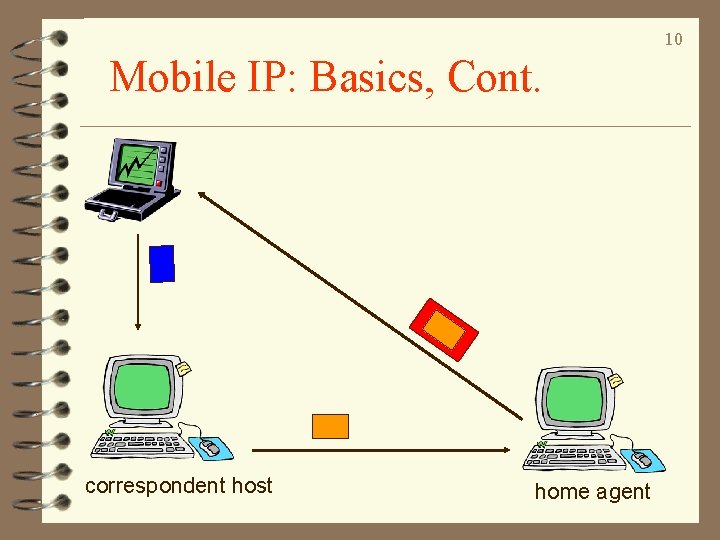
10 Mobile IP: Basics, Cont. correspondent host home agent
Mobile IP: Care-of Addresses 11 4 Whenever a mobile host connects to a remote network, two choices: – care-of can be the address of a foreign agent on the remote network • foreign agent delivers packets forwarded from home agent to mobile host – care-of can be a temporary, foreign IP address obtained through, e. g. , DHCP • home agent tunnels packets directly to the temporary IP address 4 Regardless, care-of address must be registered with home agent
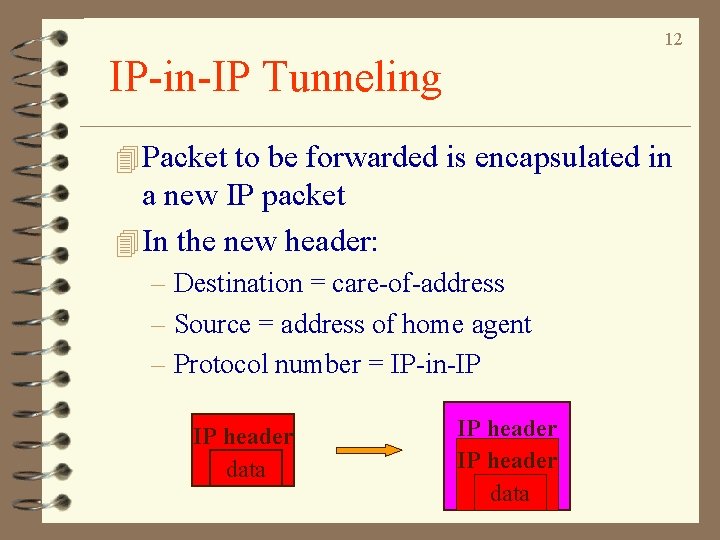
12 IP-in-IP Tunneling 4 Packet to be forwarded is encapsulated in a new IP packet 4 In the new header: – Destination = care-of-address – Source = address of home agent – Protocol number = IP-in-IP IP header data
13 At the Other End. . . 4 Depending on type of care-of address: – Foreign agent or – Mobile host 4 … strips outer IP header of tunneled packet, which is then fed to the mobile host 4 Aside: Any thoughts on advantages of foreign agent vs. co-located (foreign IP) address?
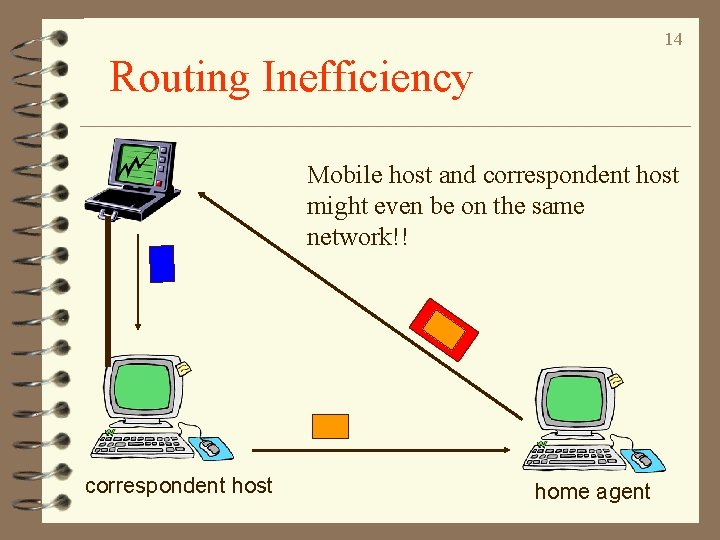
14 Routing Inefficiency Mobile host and correspondent host might even be on the same network!! correspondent host home agent
15 Route Optimizations 4 Possible Solution: – Home agent sends current care-of address to correspondent host – Correspondent host caches care-of address – Future packets tunneled directly to care-of address 4 But! – An instance of the cache consistency problem arises. . . – Cached care-of address becomes stale when the mobile host moves – Potential security issues with providing care-of address to correspondent (ask me about this when we talk about security!)
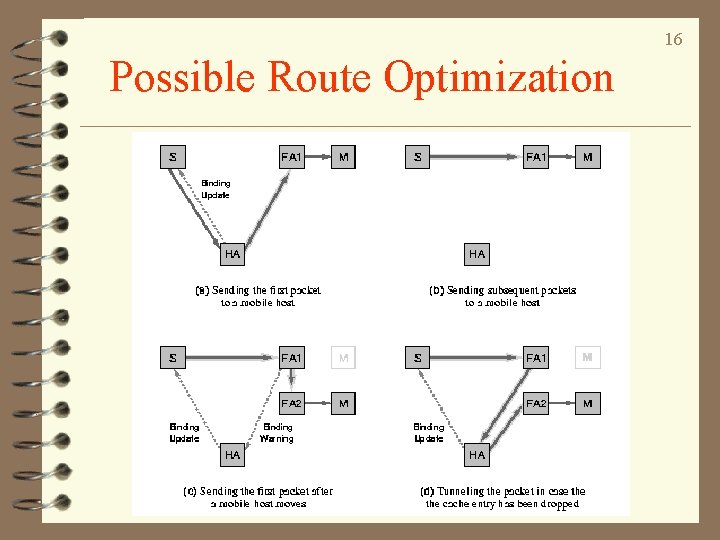
16 Possible Route Optimization
17 The Devil is in the Details! 4 How does the mobile host get a remote IP? – Router advertisements, DHCP, manual. . . 4 How can a mobile host tell where it is? – Am I at home? – Am I visiting a foreign network? – Have I moved? – What if I'm in two places at once?
18 Devil, Cont. 4 Redundancy: What if the home agent doesn't answer a registration request? – Registration request to broadcast address – Rejection carries new home agent ID 4 "Ingress" filtering – Routers which see packets coming from a direction from which they would not have routed the source address are dropped
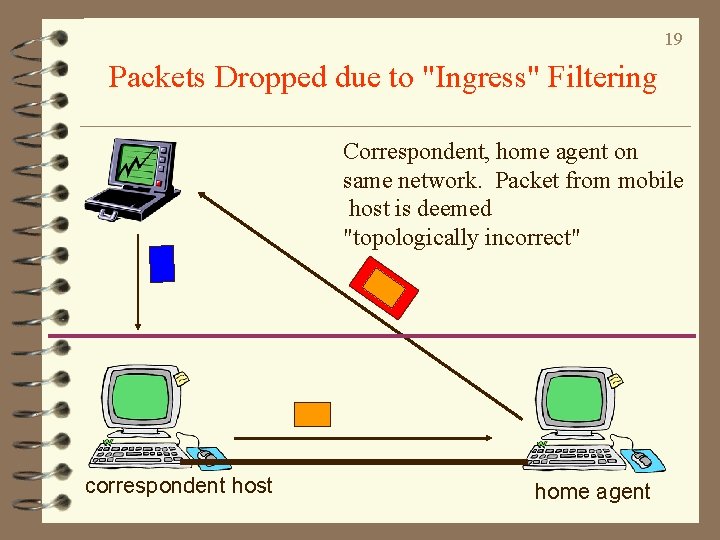
19 Packets Dropped due to "Ingress" Filtering Correspondent, home agent on same network. Packet from mobile host is deemed "topologically incorrect" correspondent host home agent
20 Another Devil: Security Issues 4 We'll look at only one of the "godzillions" of security issues: 4 Bogus registration (denial of service) attacks – Malicious host sends fake registration messages to home agent "on behalf" of the mobile host – Packets could be forwarded to malicious host or to the bit bucket
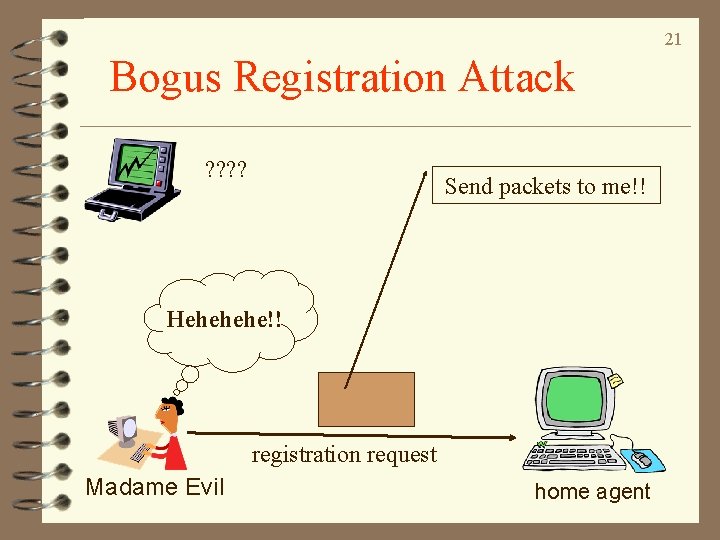
21 Bogus Registration Attack ? ? Send packets to me!! Hehehehe!! registration request Madame Evil home agent
22 Authentication 4 To fix this problem, authenticate registration attempts 4 Use private key encryption to generate a message digest 4 Home agent applies private key to message to see if message digest is identical
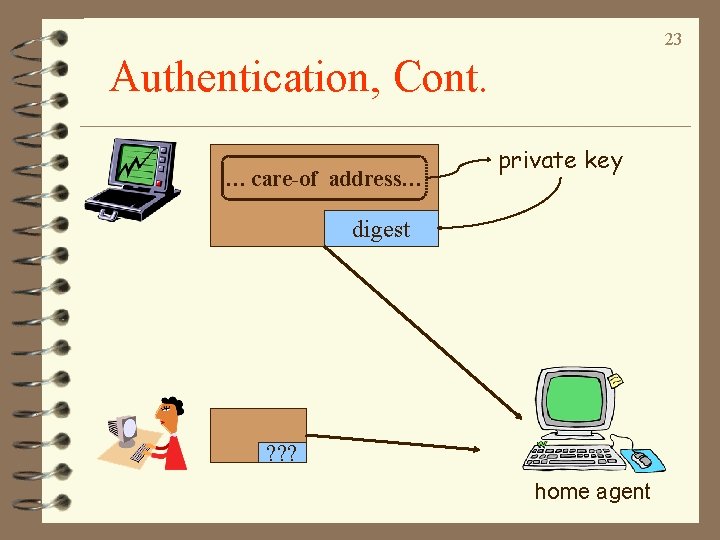
23 Authentication, Cont. … care-of address… private key digest ? ? ? home agent
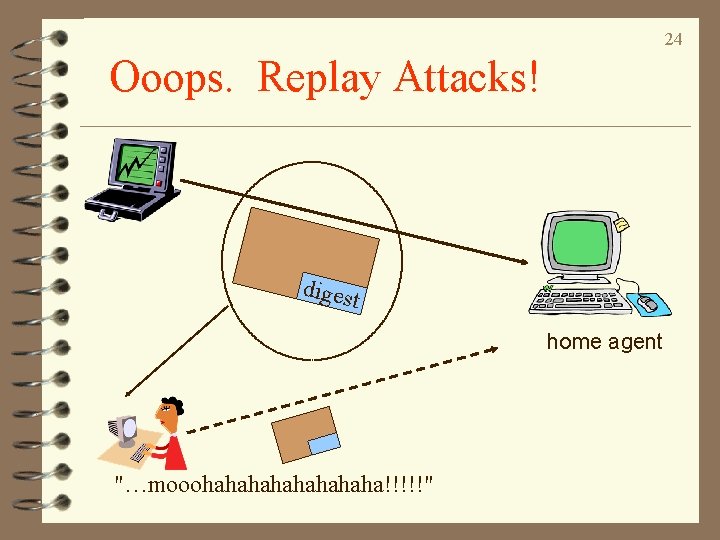
24 Ooops. Replay Attacks! diges t home agent "…mooohahahaha!!!!!"
25 Avoiding Replay Attacks 4 Avoid replay attacks by making registration requests un-replayable 4 Add estimate of local time or a pseudo-random number to registration request/reply 4 If time estimate or random number is not the expected number, provide info in "NO!" reply for resynchronization 4 Insufficient information to help malicious host
26 Abrupt Conclusions. . . 4 Great potential for mobile application deployment using Mobile IP 4 Minimizes impact on existing Internet infrastructure 4 Security issues being looked at 4 (Complicated) firewall solutions proposed 4 Several working implementations (e. g. , Monarch project at CMU) 4 Some things still need work: e. g. , integration of Mobile IP and 802. 11 wireless LANs 4 Lots of research to do on mobile computing!
- Slides: 26