INTRODUCTION TO INFORMATION SECURITY ROOTKITS Itamargi at post
- Slides: 11
INTRODUCTION TO INFORMATION SECURITY ROOTKITS Itamargi at post. tau. ac. il Nirkrako at post. tau. ac. il
Rootkits � � What are they? Various types of rootkits. Detection Famous case
What is a rootkit ? � � The name rootkit originally came from UNIX/linux set of utilities that was used post gaining root via a privilege escalation (PE) or a remote root exploit. The goal of the rootkit is to allow a hacker to roam free about the system, while still maintaining root. The rootkit hides the hacker and allows him to evade detection by the system admin. Modus operandi: 1. 2. 3. 4. Hack the system. Install the system. Explore the system. **** the system.
What can/should a rootkit do ? � Hide the hackers files – a hacker would usually have a drop-off directory where he will create temporary files (such as zip files) or keep a PE file: echo “int main{setuid(0); setgid(0); system(“/bin/sh”); } > a. c ; gcc a. c –o a ; chmod 4755 a � Eg: all files in /usr/bin/. w 00 t/ are completely hidden. � � Hide the hackers process: � � Eg. Any process starting with the words: “w 00 t” will not be visible. Hide sniffing: hide working in promiscuous mode. Hide open ports Let the hacker back in without using the exploit: � � Using the exploit to re-enter usually makes too much noise. No need to cleanup after re-entry.
Application based rootkits � � � The first rootkits seen in the 90 s were replacements for the set of system utilities in /bin/. For example hackers used a modified version of /bin/ls. In open-source systems such as linux this is very easy: � Download � original code, modify, compile, spread. In closed-source systems such as windows, older UNIX: � Binary patch the relevant files.
Application Layer Dilemmas � If you patch one program, you never know if you covered all your bases. Eg. : � patch ‘ps’ but forget to patch ‘top’ � Patch ‘ls’ but forget to patch ‘mc’ (midnight commander) � Software upgrades, if the software is upgraded
Library Rootkits � Patch the system libraries, such as libc, eg. : � readdir � Patching can be done offline to the library or via code injection techniques.
Code Injection/API Hooking � The idea is to dynamically patch a program’s behavior. � � This is necessary for debuggers to work properly We load a “shellcode” in the process memory using some technique. � Eg. Windows: BOOL Write. Process. Memory( HANDLE h. Process, LPVOID lp. Base. Address, LPVOID lp. Buffer, DWORD n. Size, LPDWORD lp. Number. Of. Bytes. Written ); � Eg. Linux: ptrace with POKETEXT: PTRACE_POKETEXT, PTRACE_POKEDATA Copies the word data to location addr in the child's memory. As above, the two requests are currently equivalent. � � The shellcode can load a DLL that does some more work. Subverting functions is done by patching the original code. � � � Linux: The code segment permissions can be changed via mprotect() Windows: Virtual. Protect(). Windows has Detours – a library used to Hook APIs
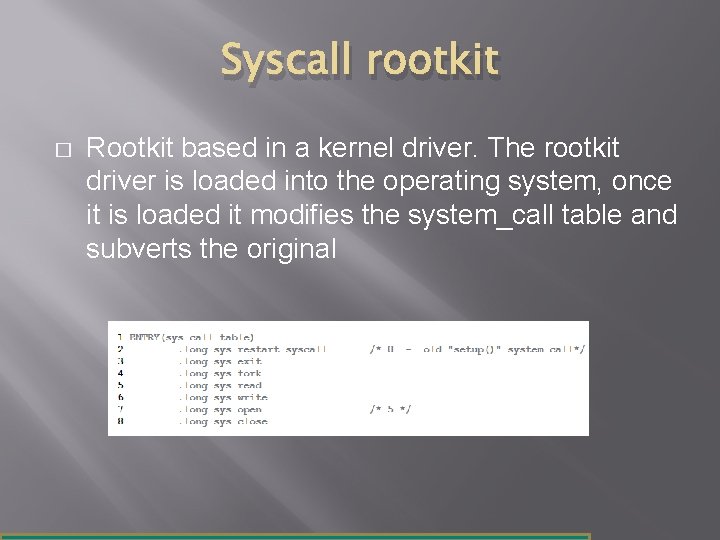
Syscall rootkit � Rootkit based in a kernel driver. The rootkit driver is loaded into the operating system, once it is loaded it modifies the system_call table and subverts the original
Rootkit detection � � Looking at the rootkit from a different perspective Signature based: Look for signatures in files and memory know to belong to the rootkit. blacklist based. � This is the technique most anti-viruses use. � � Difference based Difference between view from memory to view on disk. � Offline vs. Online. � � Integrity checking of binaries. Compare md 5 of files to whitelist. � Eg. : tripwire application for *n? x [Trace buster video]
Sony DRM: Famous Rootkit Case � https: //blogs. technet. com/b/markrussinovich/ar chive/2005/10/31/sony-rootkits-and-digitalrights-management-gone-toofar. aspx? Redirected=true