Introduction to Data Security Cryptography Slides Original Source
- Slides: 23
Introduction to Data Security & Cryptography Slides Original Source: 1. M. Stamp, “Information Security: Principles and Practice, ” John Wiley 2. B. Forouzan, “Cryptography and Network Security, ” Mc. Graw-Hill Introduction 1
The Cast of Characters q Alice and Bob are the good guys q Trudy is the bad “guy” q Trudy is our generic “intruder” 2
Alice’s Online Bank q Alice opens Alice’s Online Bank (AOB) q What are Alice’s security concerns? q If Bob is a customer of AOB, what are his security concerns? q How are Alice’s and Bob’s concerns similar? How are they different? q How Introduction does Trudy view the situation? 3
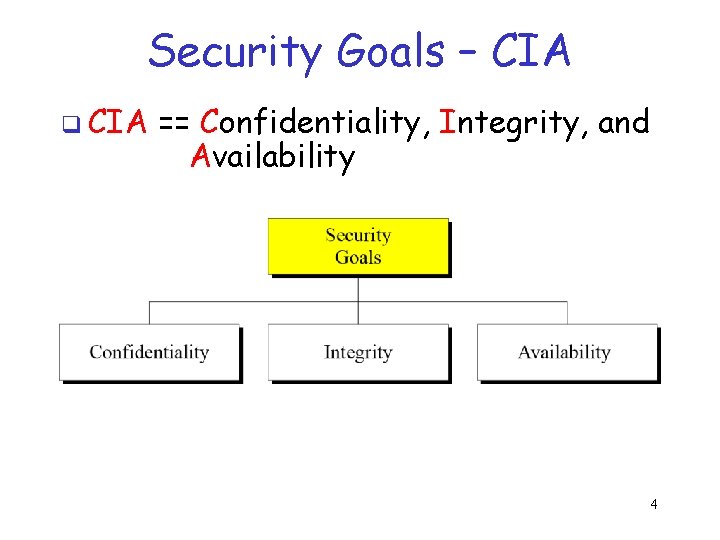
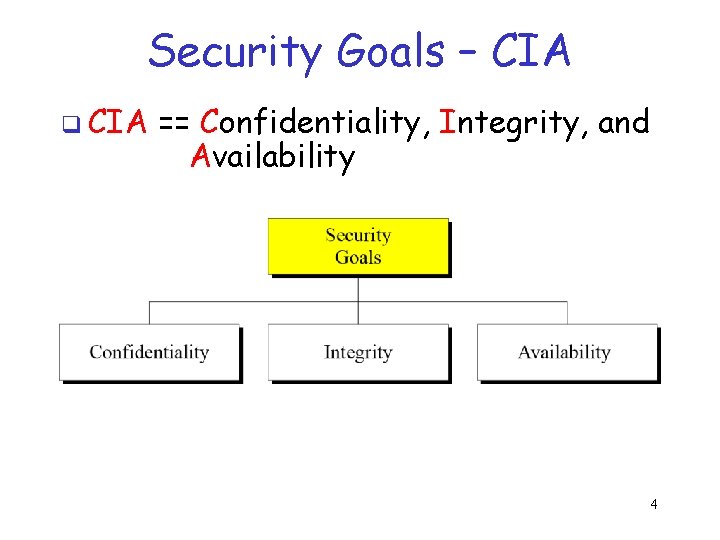
Security Goals – CIA q CIA == Confidentiality, Integrity, and _____Availability 4
CIA – Confidentiality q AOB must prevent Trudy from learning Bob’s account balance q Confidentiality: prevent unauthorized reading of information o Cryptography used for confidentiality 5
CIA – Integrity q Trudy must not be able to change Bob’s account balance q Bob must not be able to improperly change his own account balance q Integrity: detect unauthorized writing of information o Cryptography used for integrity 6
CIA – Availability q q AOB’s information must be available whenever it’s needed Bob must be able to make transaction o If not, he’ll take his business elsewhere q q Availability: Data is available in a timely manner when needed Availability is a “new” security concern o Denial of service (Do. S) attacks Introduction 7
Beyond CIA: Crypto q How does Bob’s computer know that “Bob” is really Bob and not Trudy? q Bob’s password must be verified o This requires some clever cryptography q What q Are Introduction are security concerns of pwds? there alternatives to passwords? 8
Beyond CIA: Protocols q q When Bob logs into AOB, how does AOB know that “Bob” is really Bob? As before, Bob’s password is verified Unlike the previous case, network security issues arise How do we secure network transactions? o Protocols are critically important o Crypto plays critical role in protocols Introduction 9
Beyond CIA: Access Control q Once Bob is authenticated by AOB, then AOB must restrict actions of Bob o Bob can’t view Charlie’s account info o Bob can’t install new software, etc. q q Enforcing these restrictions: authorization Access control includes both authentication and authorization 10
The People Problem q People often break security o Both intentionally and unintentionally o Here, we consider the unintentional q For example, suppose you want to buy something online o To make it concrete, suppose you want to buy a book from amazon. com Introduction 11
The People Problem q To o o buy from amazon. com… Your Web browser uses SSL protocol SSL relies on cryptography Access control issues arise All security mechanisms are in software q Suppose all of this security stuff works perfectly o Then you would be safe, right? Introduction 12
The People Problem q What could go wrong? q Trudy tries man-in-the-middle attack o SSL is secure, so attack doesn’t “work” o But, Web browser issues a warning o What do you, the user, do? q If user ignores warning, attack works! o None of the security mechanisms failed o But user unintentionally broke security Introduction 13
Think Like Trudy q In the past, no respectable sources talked about “hacking” in detail o After all, such info might help Trudy q Recently, this has changed o Lots of books on network hacking, evil software, how to hack software, etc. o Classes teach virus writing, SRE, etc. Introduction 14
Think Like Trudy q Good q. A guys must think like bad guys! police detective… o …must study and understand criminals q In information security o We want to understand Trudy’s methods o Might think about Trudy’s motives o We’ll often pretend to be Trudy Introduction 15
Think Like Trudy q We must try to think like Trudy q We must study Trudy’s methods q We can admire Trudy’s cleverness q Often, we can’t help but laugh at Alice’s and/or Bob’s stupidity q But, we cannot act like Trudy o Except in this class… Introduction 16
In This Course… q Think like the bad guy q Always look for weaknesses o Find the weak link before Trudy does q It’s OK to break the rules o What rules? q Think like Trudy q But don’t do anything illegal! Introduction 17
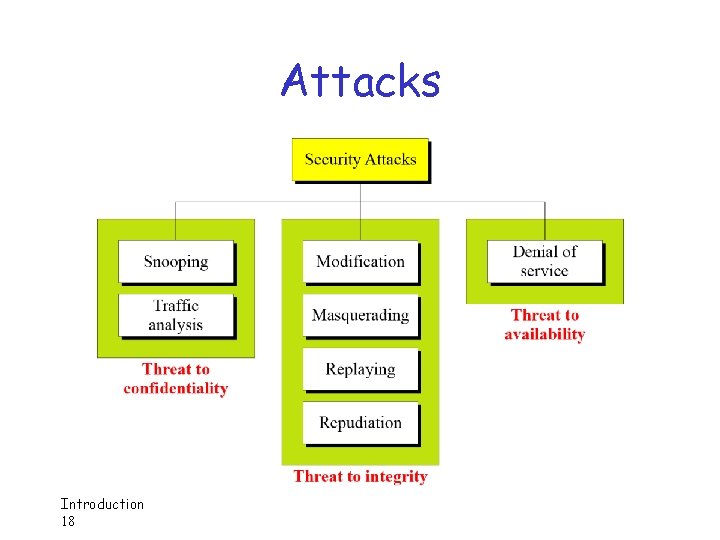
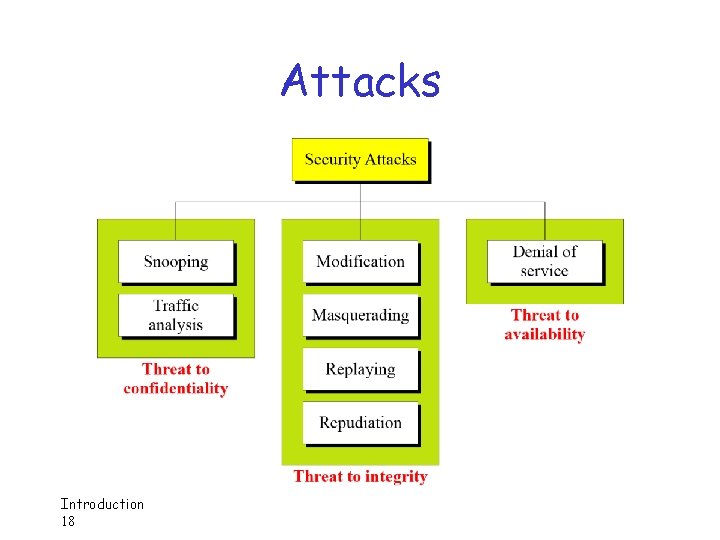
Attacks Introduction 18
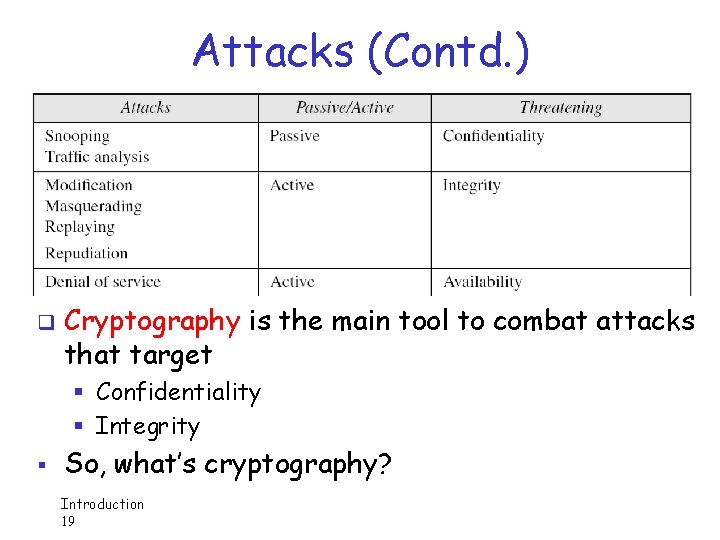
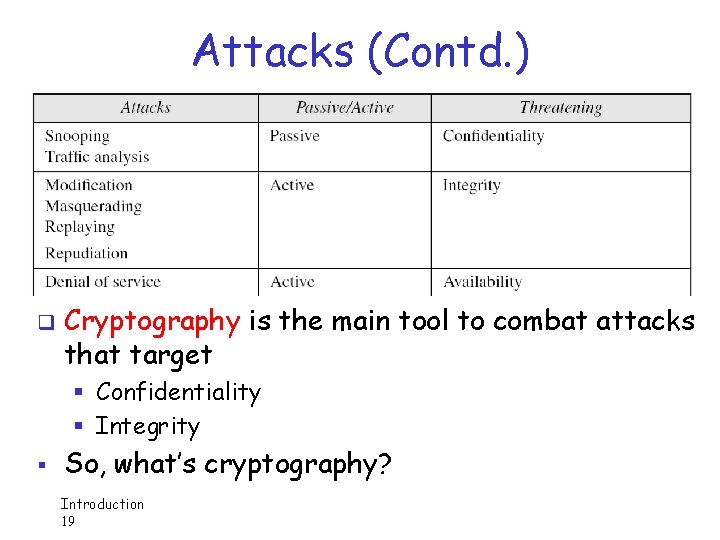
Attacks (Contd. ) q Cryptography is the main tool to combat attacks that target § Confidentiality § Integrity § So, what’s cryptography? Introduction 19
Security Jargons q Cryptology The art and science of making and breaking “secret codes” q Cryptography making “secret codes” q Cryptanalysis breaking “secret codes” q Crypto all of the above (and more) 2 0
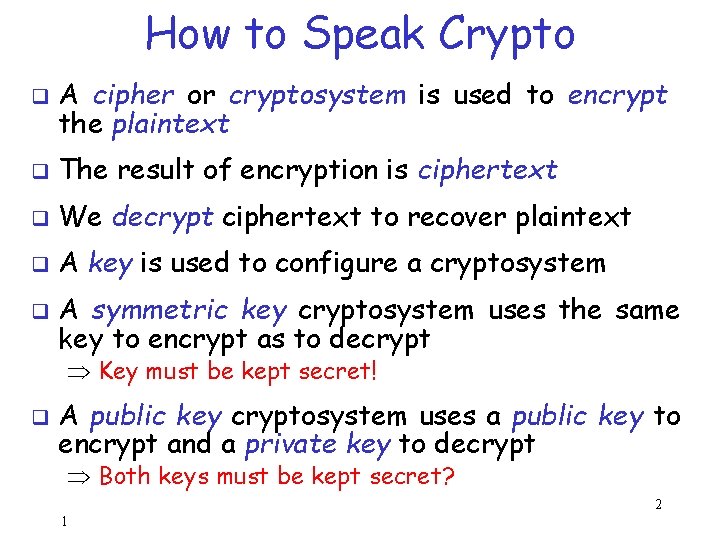
How to Speak Crypto q A cipher or cryptosystem is used to encrypt the plaintext q The result of encryption is ciphertext q We decrypt ciphertext to recover plaintext q A key is used to configure a cryptosystem q A symmetric key cryptosystem uses the same key to encrypt as to decrypt Key must be kept secret! q A public key cryptosystem uses a public key to encrypt and a private key to decrypt Both keys must be kept secret? 2 1
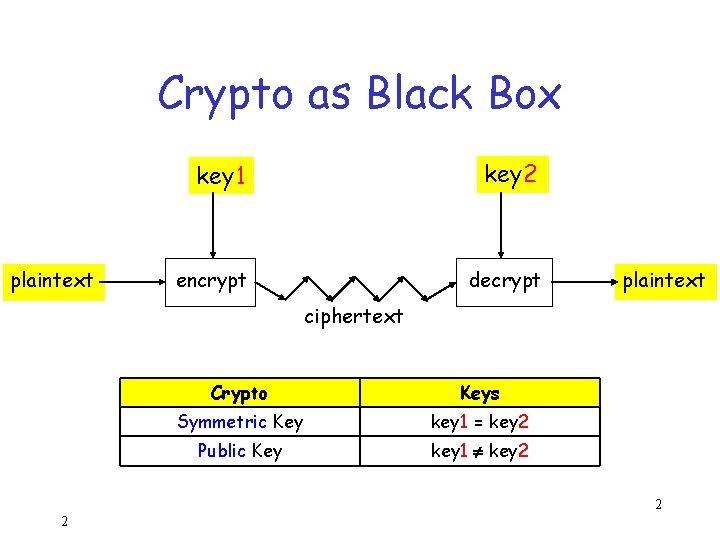
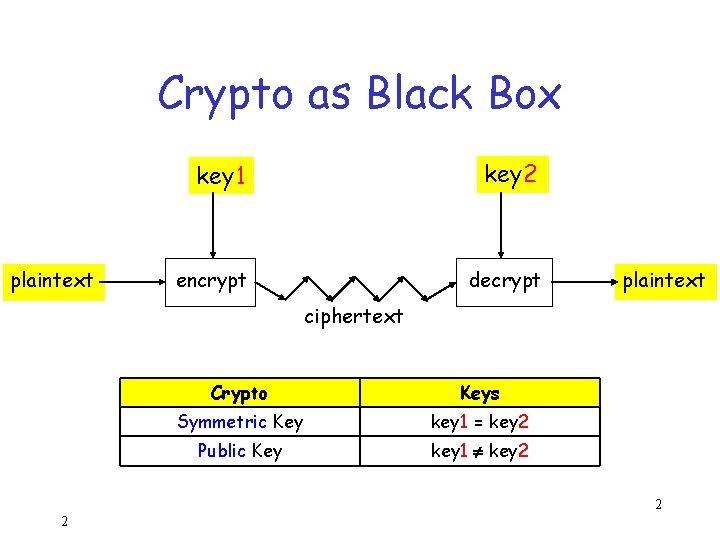
Crypto as Black Box plaintext key 1 key 2 encrypt decrypt plaintext ciphertext Crypto Keys Symmetric Key key 1 = key 2 Public Key key 1 key 2 2 2
Crypto q Basic assumptions o The system is completely known to the attacker o Only the key is secret (and, obviously, the plaintext!) o Crypto algorithms are not secret! q This is known as Kerckhoffs’ Principle q Why do we make these assumptions? o Experience has shown that secret algorithms are weak when exposed o Secret algorithms never remain secret o Better to find weaknesses beforehand 2 3