Introduction to Cryptography and Security Mechanisms Dr Keith

- Slides: 55
Introduction to Cryptography and Security Mechanisms Dr Keith Martin Mc. Crea 349 01784 443099 keith. martin@rhul. ac. uk Introduction to Cryptography and Security Mechanisms 2005

Before we start… Introduction to Cryptography and Security Mechanisms 2005
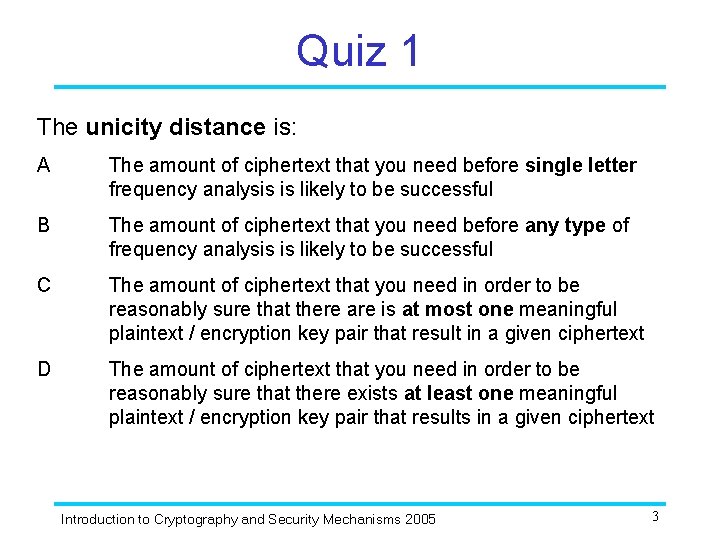
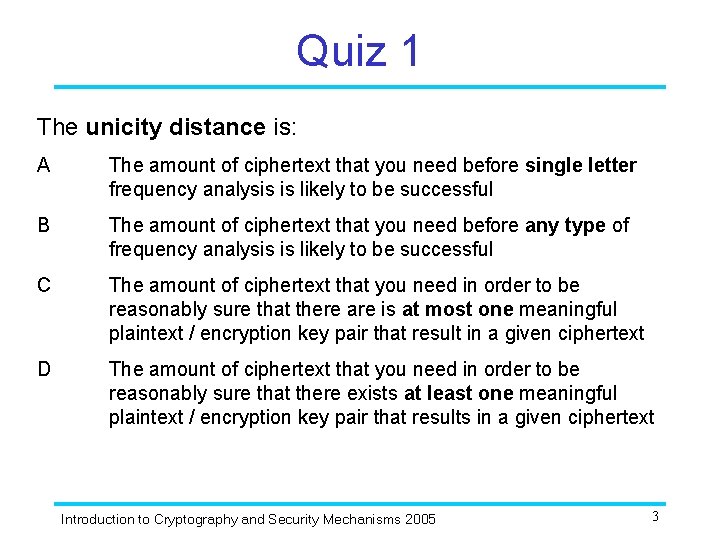
Quiz 1 The unicity distance is: A The amount of ciphertext that you need before single letter frequency analysis is likely to be successful B The amount of ciphertext that you need before any type of frequency analysis is likely to be successful C The amount of ciphertext that you need in order to be reasonably sure that there are is at most one meaningful plaintext / encryption key pair that result in a given ciphertext D The amount of ciphertext that you need in order to be reasonably sure that there exists at least one meaningful plaintext / encryption key pair that results in a given ciphertext Introduction to Cryptography and Security Mechanisms 2005 3
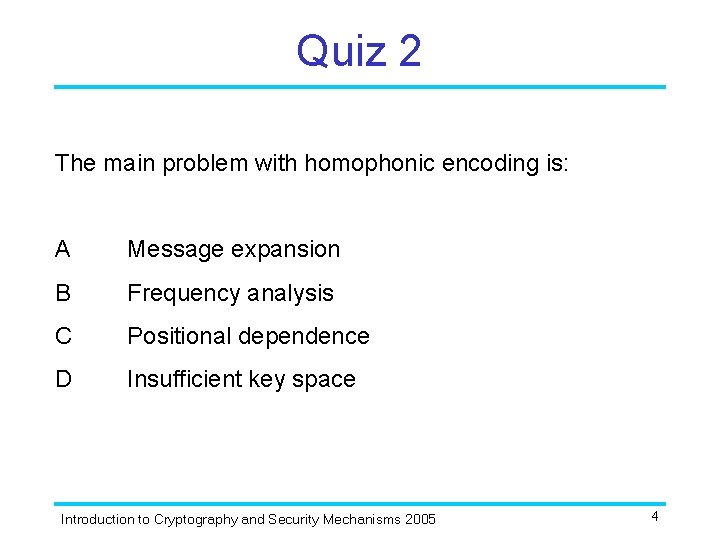
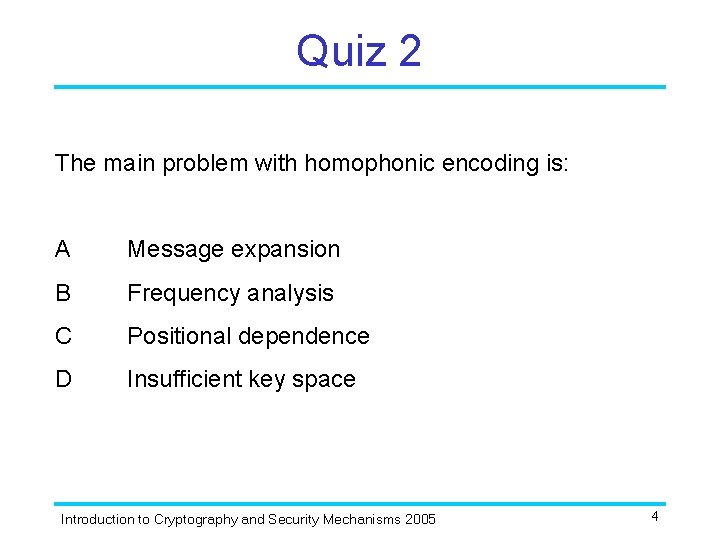
Quiz 2 The main problem with homophonic encoding is: A Message expansion B Frequency analysis C Positional dependence D Insufficient key space Introduction to Cryptography and Security Mechanisms 2005 4
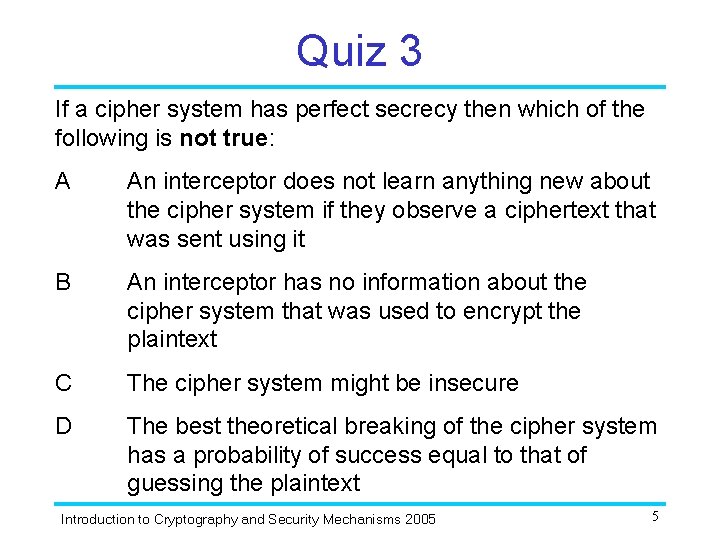
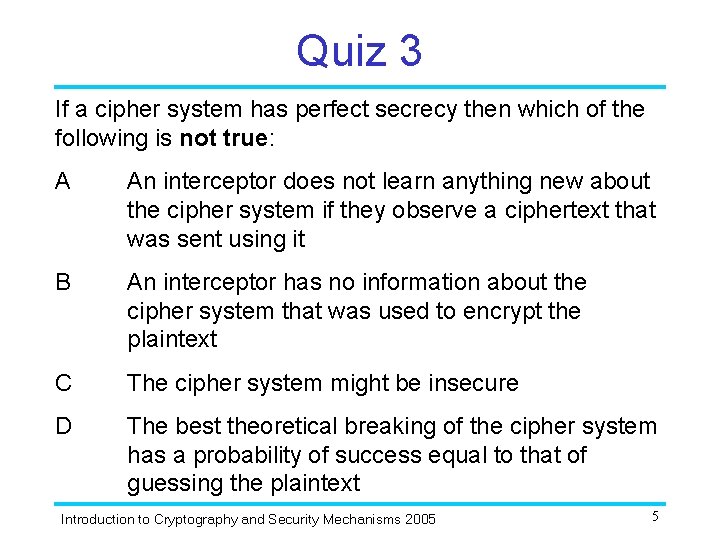
Quiz 3 If a cipher system has perfect secrecy then which of the following is not true: A An interceptor does not learn anything new about the cipher system if they observe a ciphertext that was sent using it B An interceptor has no information about the cipher system that was used to encrypt the plaintext C The cipher system might be insecure D The best theoretical breaking of the cipher system has a probability of success equal to that of guessing the plaintext Introduction to Cryptography and Security Mechanisms 2005 5
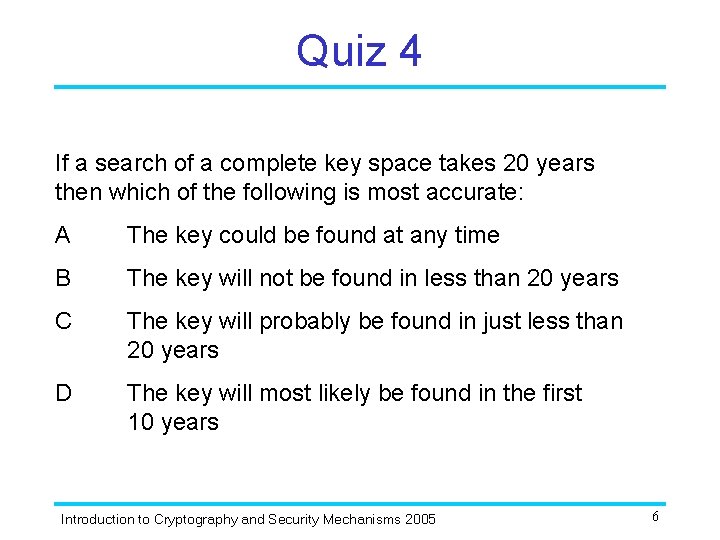
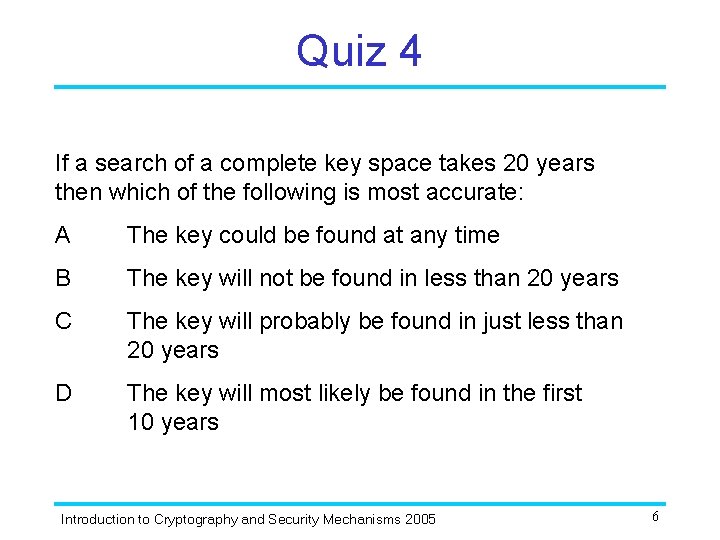
Quiz 4 If a search of a complete key space takes 20 years then which of the following is most accurate: A The key could be found at any time B The key will not be found in less than 20 years C The key will probably be found in just less than 20 years D The key will most likely be found in the first 10 years Introduction to Cryptography and Security Mechanisms 2005 6
Introduction to Cryptography and Security Mechanisms: Unit 6 Symmetric Algorithms Dr Keith Martin Mc. Crea 349 01784 443099 keith. martin@rhul. ac. uk Introduction to Cryptography and Security Mechanisms 2005
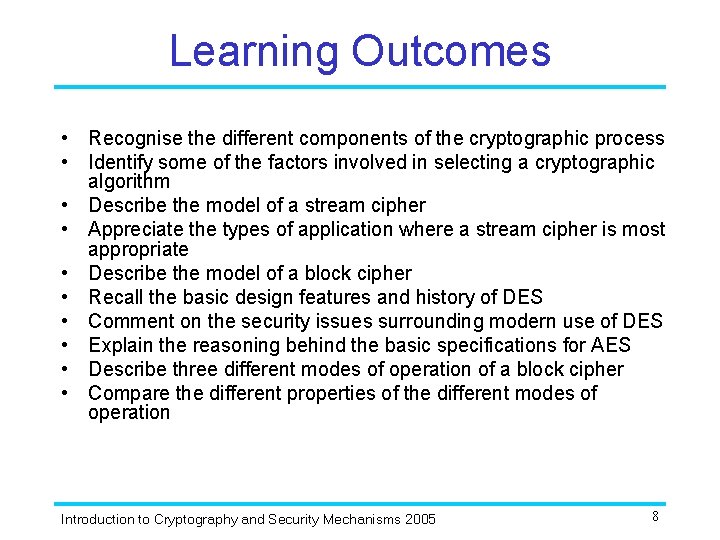
Learning Outcomes • Recognise the different components of the cryptographic process • Identify some of the factors involved in selecting a cryptographic algorithm • Describe the model of a stream cipher • Appreciate the types of application where a stream cipher is most appropriate • Describe the model of a block cipher • Recall the basic design features and history of DES • Comment on the security issues surrounding modern use of DES • Explain the reasoning behind the basic specifications for AES • Describe three different modes of operation of a block cipher • Compare the different properties of the different modes of operation Introduction to Cryptography and Security Mechanisms 2005 8
Sections 1. 2. 3. 4. Cryptographic algorithms Stream ciphers Block ciphers Modes of operation Introduction to Cryptography and Security Mechanisms 2005 9
1. Cryptographic algorithms Introduction to Cryptography and Security Mechanisms 2005
Cryptographic process A cryptographic algorithm itself is just one component part of an entire process, which must all come together before we can claim that any particular application is using a “secure cipher system”. This process includes: • Selection (or design) of an algorithm • Deciding how an algorithm is to be used • Implementing an algorithm within a communications system • Devising a key management scheme Introduction to Cryptography and Security Mechanisms 2005 11
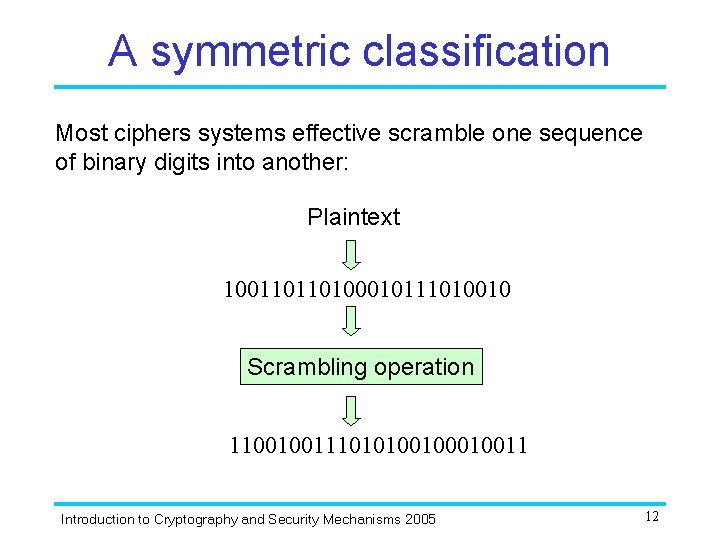
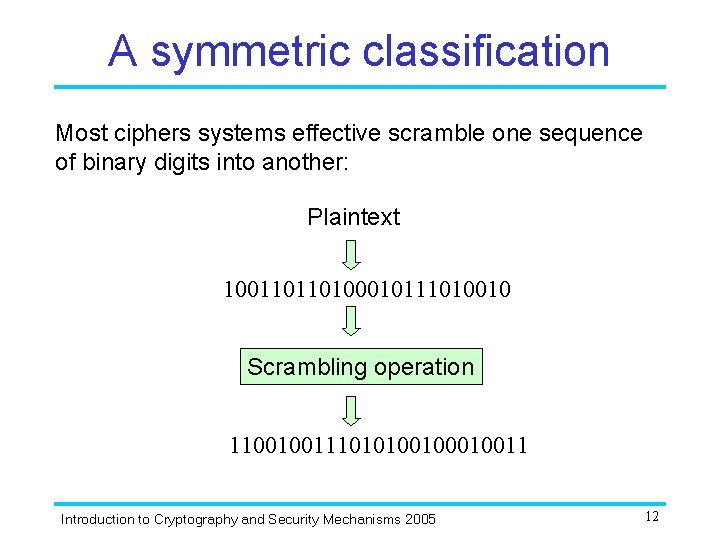
A symmetric classification Most ciphers systems effective scramble one sequence of binary digits into another: Plaintext 100110110100010111010010 Scrambling operation 110010011101010010011 Introduction to Cryptography and Security Mechanisms 2005 12
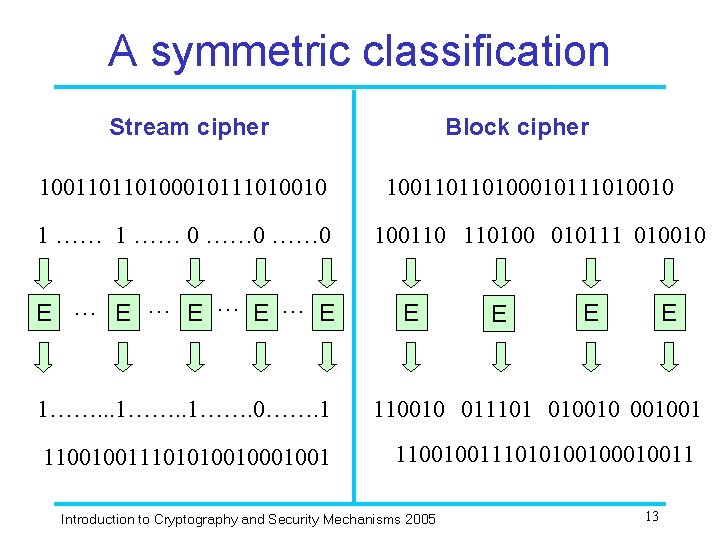
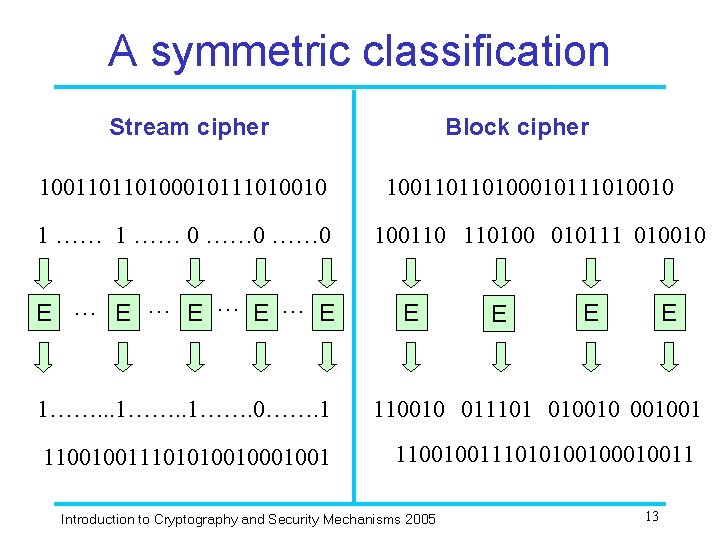
A symmetric classification Stream cipher 100110110100010111010010 1 …… 0 E … E … E Block cipher 100110110100010111010010 100110 110100 010111 010010 E E 1……. . . 1……. 0……. 1 110010 011101 01001001 1100100111010100100010011 Introduction to Cryptography and Security Mechanisms 2005 13
A public key classification? Can public key cipher systems also be classified into stream and block ciphers? Introduction to Cryptography and Security Mechanisms 2005 14
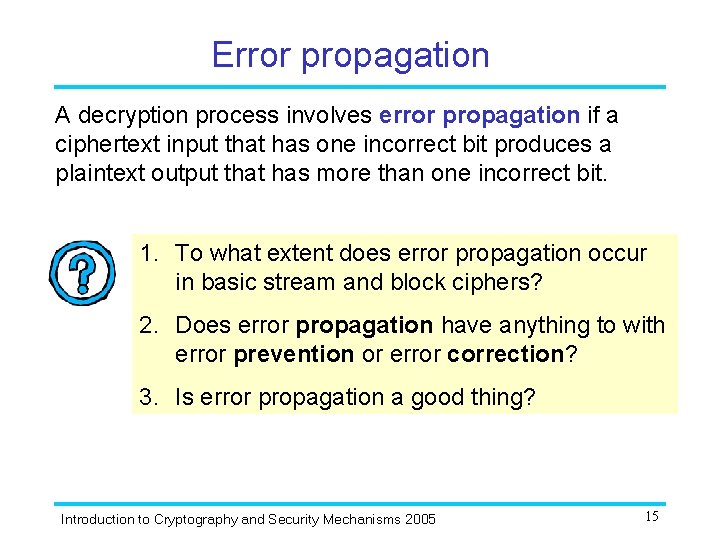
Error propagation A decryption process involves error propagation if a ciphertext input that has one incorrect bit produces a plaintext output that has more than one incorrect bit. 1. To what extent does error propagation occur in basic stream and block ciphers? 2. Does error propagation have anything to with error prevention or error correction? 3. Is error propagation a good thing? Introduction to Cryptography and Security Mechanisms 2005 15
2. Stream ciphers Introduction to Cryptography and Security Mechanisms 2005
The idea behind stream ciphers Recall from Unit 5… Stream ciphers attempt to simulate the onetime pad by using short keys to generate longer keys that can then be used in a onetime pad encryption Introduction to Cryptography and Security Mechanisms 2005 17
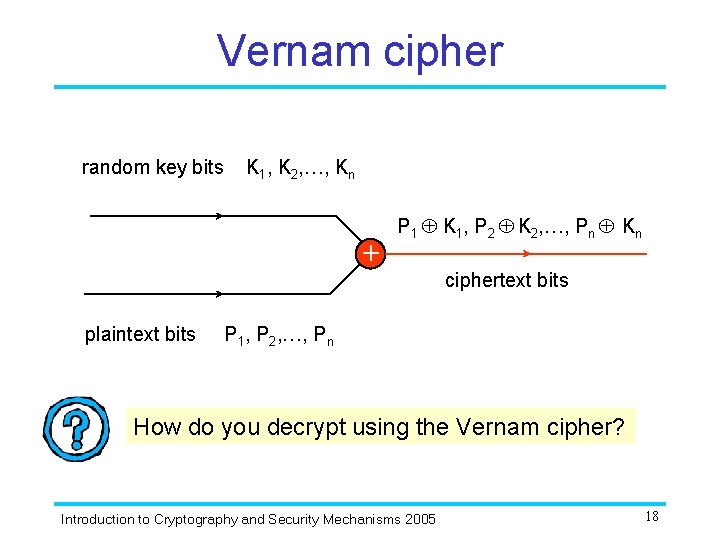
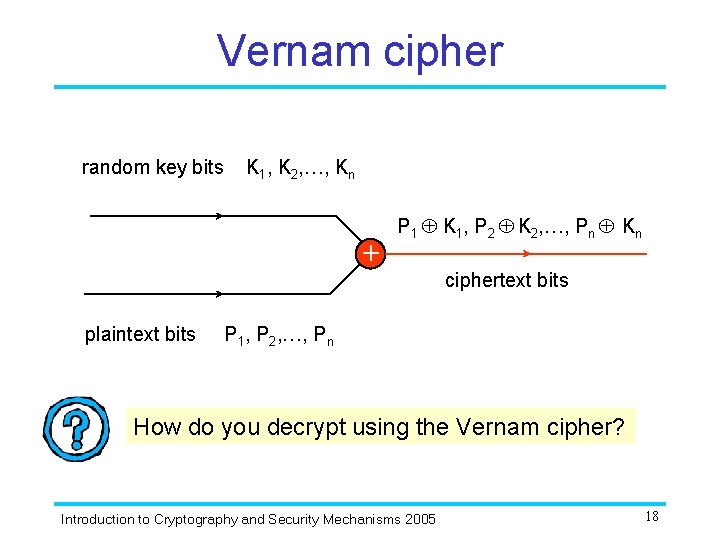
Vernam cipher random key bits K 1, K 2, …, Kn + plaintext bits P 1 K 1, P 2 K 2, …, Pn Kn ciphertext bits P 1, P 2, …, Pn How do you decrypt using the Vernam cipher? Introduction to Cryptography and Security Mechanisms 2005 18
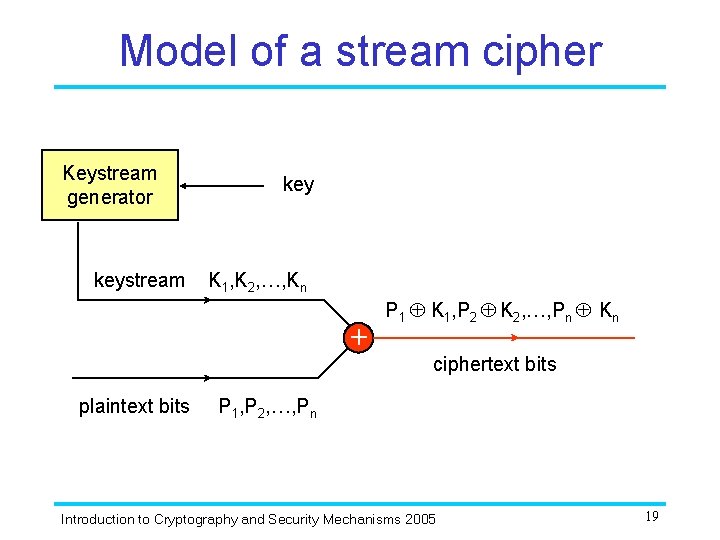
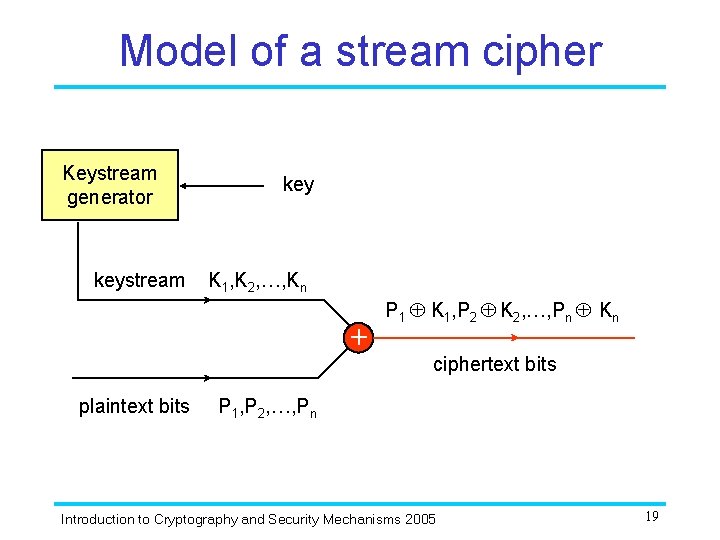
Model of a stream cipher Keystream generator keystream key K 1, K 2, …, Kn + plaintext bits P 1 K 1, P 2 K 2, …, Pn Kn ciphertext bits P 1, P 2, …, Pn Introduction to Cryptography and Security Mechanisms 2005 19
Model of a stream cipher 1. How do you decrypt using a stream cipher? 2. How would go about trying to break: a) The Vernam Cipher? b) A typical stream cipher? Introduction to Cryptography and Security Mechanisms 2005 20
Security of stream ciphers Designing good stream ciphers and assessing their security primarily involves analysis of the keystream generator and the properties of the resulting keystream. Research is focussed on designing keystream generators that produce a keystream that “looks random” (even though it clearly cannot be since it is generated using a deterministic process based on a finite key). Sequences of ones and zeros that “look random” (but aren’t) are usually referred to as pseudorandom sequences. Introduction to Cryptography and Security Mechanisms 2005 21
Pseudorandomness 1. How can you tell if a sequence has good pseudorandom properties? 2. What do you call a stream cipher whose keystream is truly random? Introduction to Cryptography and Security Mechanisms 2005 22
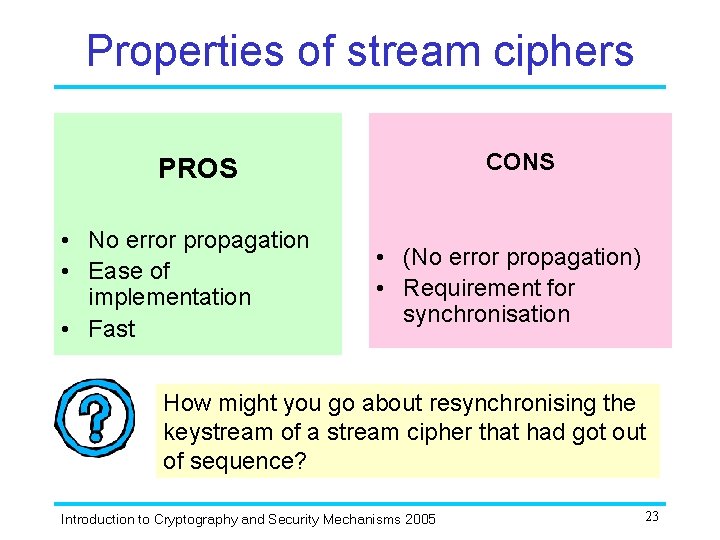
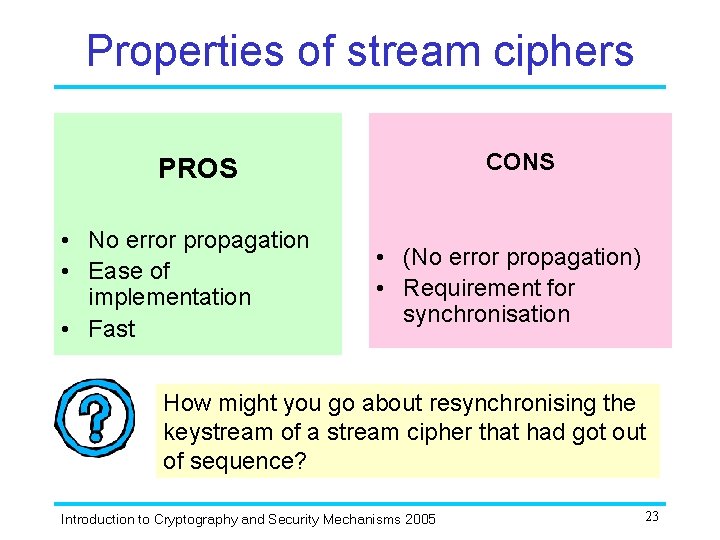
Properties of stream ciphers CONS PROS • No error propagation • Ease of implementation • Fast • (No error propagation) • Requirement for synchronisation How might you go about resynchronising the keystream of a stream cipher that had got out of sequence? Introduction to Cryptography and Security Mechanisms 2005 23
3. Block ciphers Introduction to Cryptography and Security Mechanisms 2005
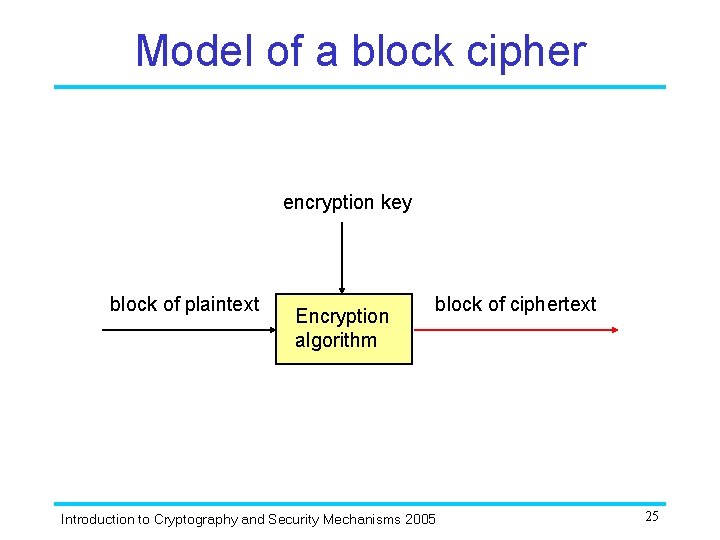
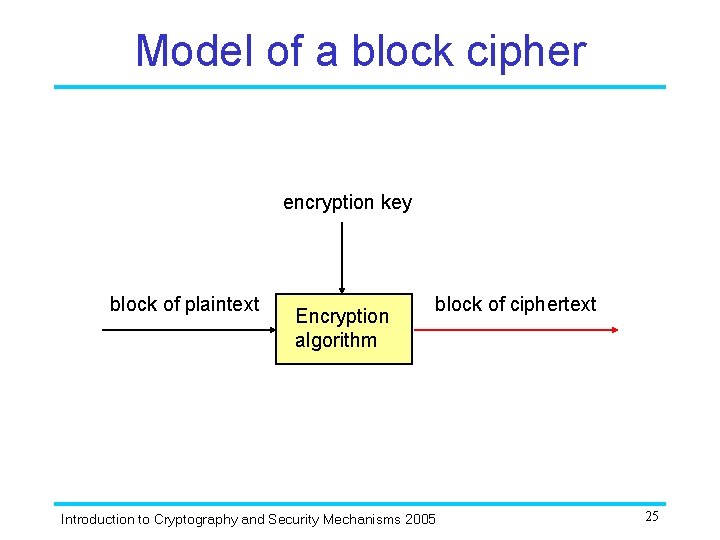
Model of a block cipher encryption key block of plaintext Encryption algorithm block of ciphertext Introduction to Cryptography and Security Mechanisms 2005 25
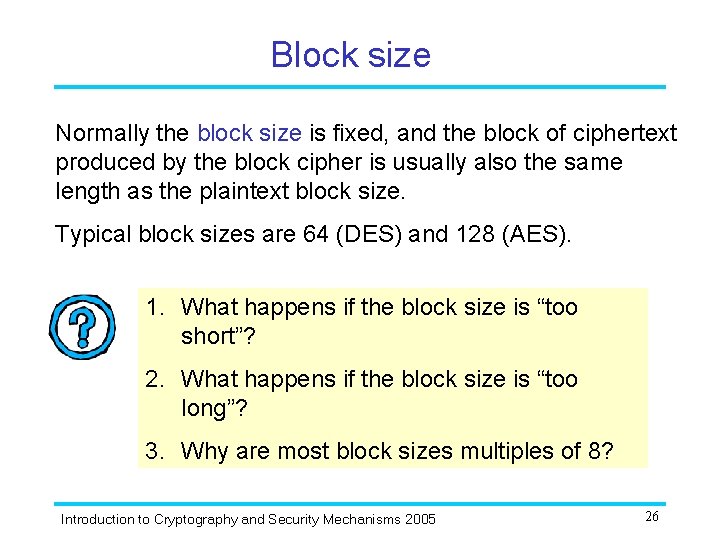
Block size Normally the block size is fixed, and the block of ciphertext produced by the block cipher is usually also the same length as the plaintext block size. Typical block sizes are 64 (DES) and 128 (AES). 1. What happens if the block size is “too short”? 2. What happens if the block size is “too long”? 3. Why are most block sizes multiples of 8? Introduction to Cryptography and Security Mechanisms 2005 26
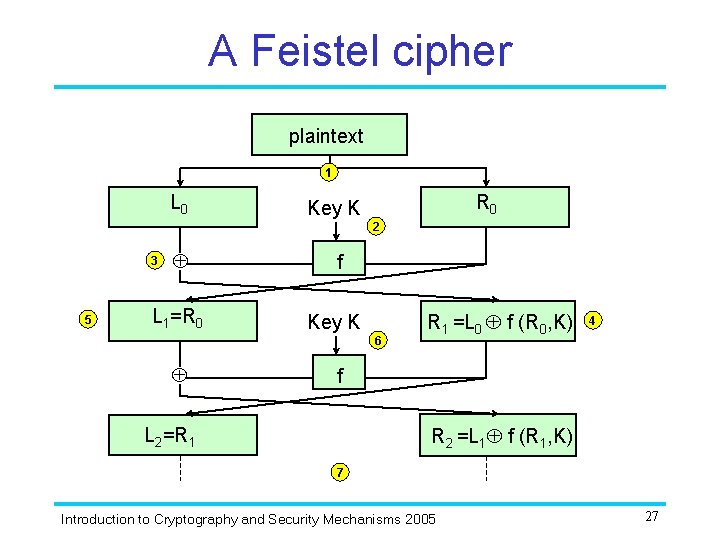
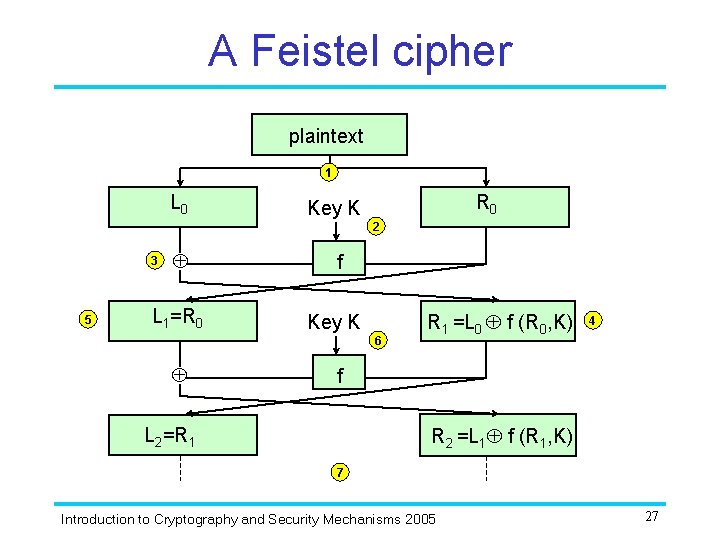
A Feistel cipher plaintext 1 L 0 R 0 Key K 2 3 5 L 1=R 0 f Key K 6 R 1 =L 0 f (R 0, K) 4 f R 2 =L 1 f (R 1, K) L 2=R 1 7 Introduction to Cryptography and Security Mechanisms 2005 27
Feistel ciphers 1. How do you choose the round function f ? 2. How do you decrypt using a Feistel cipher? 3. How many rounds should a Feistel cipher have? In order to understand the cleverness of the Feistel cipher design methodology, attempt Exercises 1 and 2 for this unit. Introduction to Cryptography and Security Mechanisms 2005 28
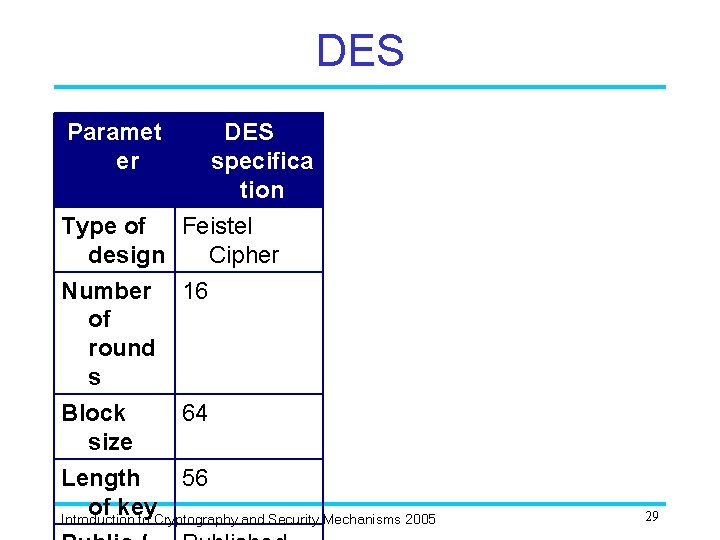
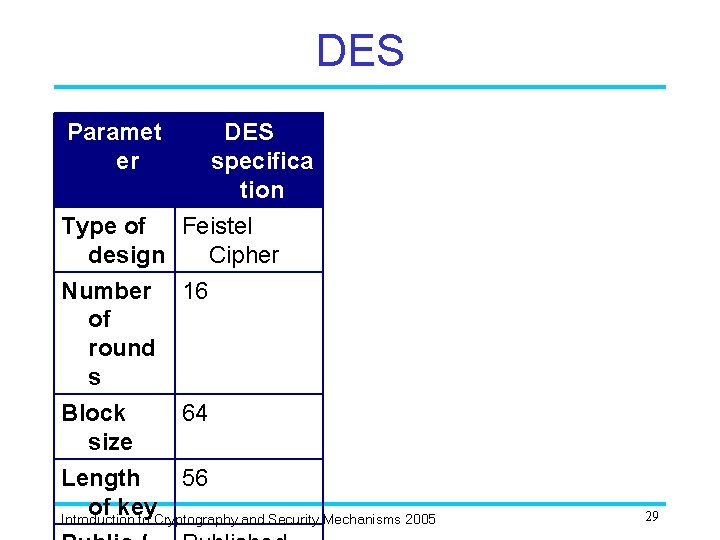
DES Paramet er DES specifica tion Type of Feistel design Cipher Number 16 of round s Block 64 size Length 56 of key Introduction to Cryptography and Security Mechanisms 2005 29
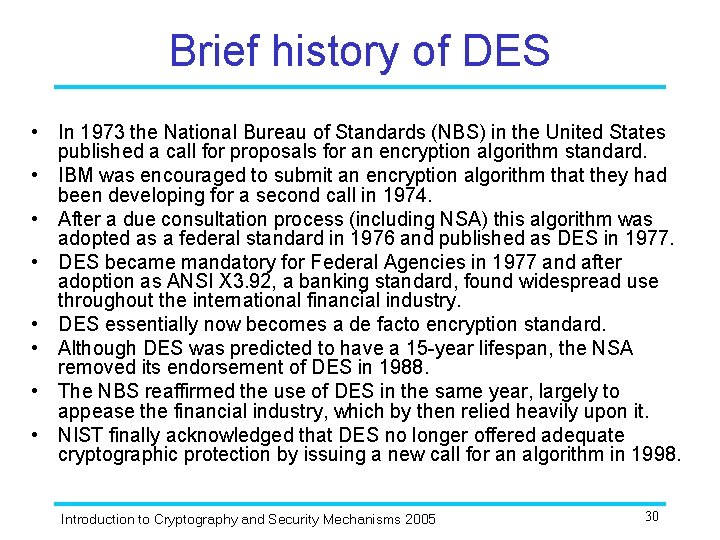
Brief history of DES • In 1973 the National Bureau of Standards (NBS) in the United States published a call for proposals for an encryption algorithm standard. • IBM was encouraged to submit an encryption algorithm that they had been developing for a second call in 1974. • After a due consultation process (including NSA) this algorithm was adopted as a federal standard in 1976 and published as DES in 1977. • DES became mandatory for Federal Agencies in 1977 and after adoption as ANSI X 3. 92, a banking standard, found widespread use throughout the international financial industry. • DES essentially now becomes a de facto encryption standard. • Although DES was predicted to have a 15 -year lifespan, the NSA removed its endorsement of DES in 1988. • The NBS reaffirmed the use of DES in the same year, largely to appease the financial industry, which by then relied heavily upon it. • NIST finally acknowledged that DES no longer offered adequate cryptographic protection by issuing a new call for an algorithm in 1998. Introduction to Cryptography and Security Mechanisms 2005 30
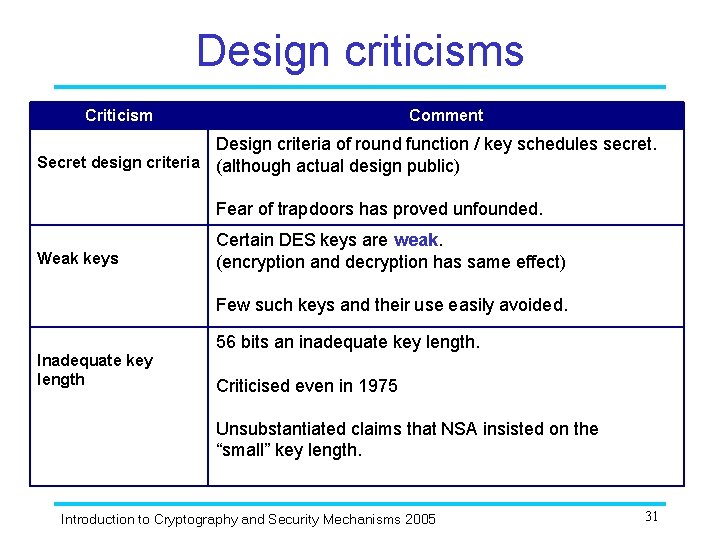
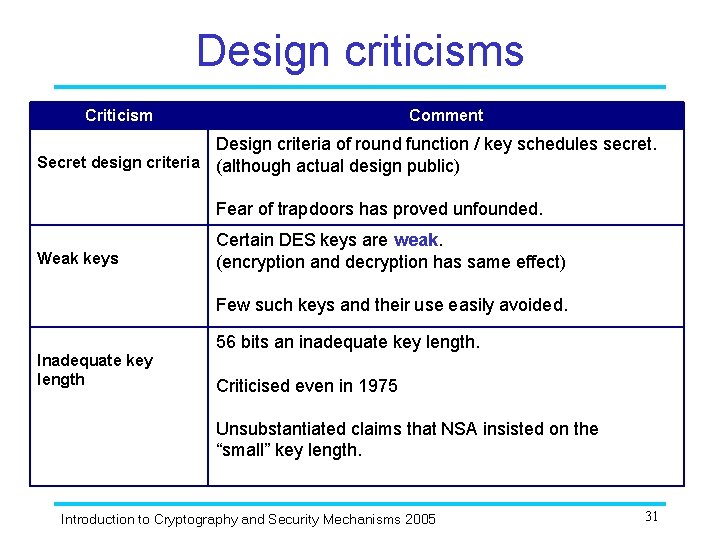
Design criticisms Criticism Comment Design criteria of round function / key schedules secret. Secret design criteria (although actual design public) Fear of trapdoors has proved unfounded. Weak keys Certain DES keys are weak. (encryption and decryption has same effect) Few such keys and their use easily avoided. Inadequate key length 56 bits an inadequate key length. Criticised even in 1975 Unsubstantiated claims that NSA insisted on the “small” key length. Introduction to Cryptography and Security Mechanisms 2005 31
Searching for a DES key Suppose that we have a machine consisting of one million processors, each of which can test one million keys per second. How long is it likely to take before we find a DES key during an exhaustive key search? Introduction to Cryptography and Security Mechanisms 2005 32
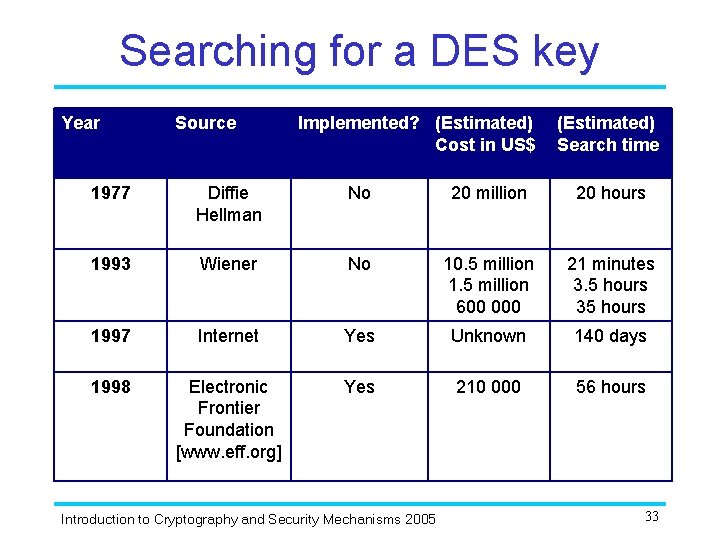
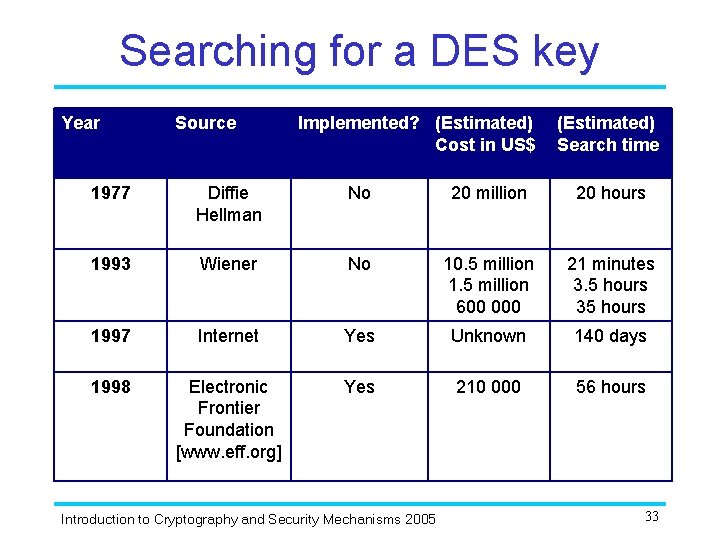
Searching for a DES key Year Source Implemented? (Estimated) Cost in US$ (Estimated) Search time 1977 Diffie Hellman No 20 million 20 hours 1993 Wiener No 10. 5 million 1. 5 million 600 000 21 minutes 3. 5 hours 35 hours 1997 Internet Yes Unknown 140 days 1998 Electronic Frontier Foundation [www. eff. org] Yes 210 000 56 hours Introduction to Cryptography and Security Mechanisms 2005 33
DES today • Well accepted that a DES key can be found by anyone determined enough. • Differential and linear cryptanalysis provide academic attacks on DES. • DES is still in use in many applications. • Triple DES or AES are commonly recommended instead of DES. Introduction to Cryptography and Security Mechanisms 2005 34
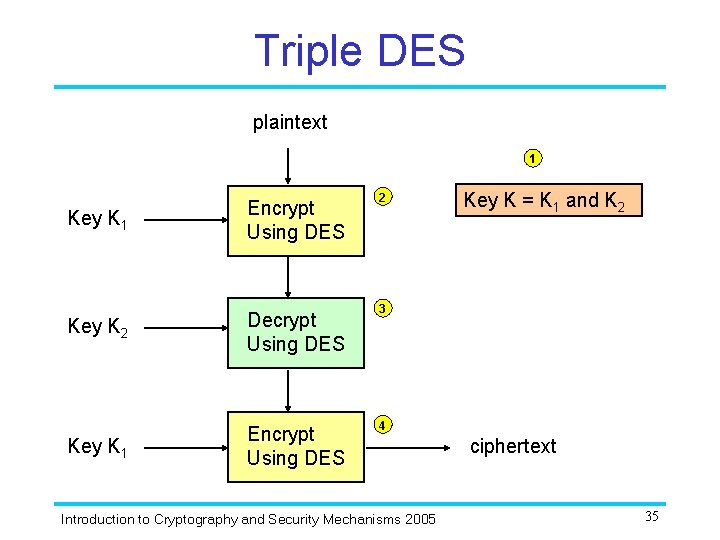
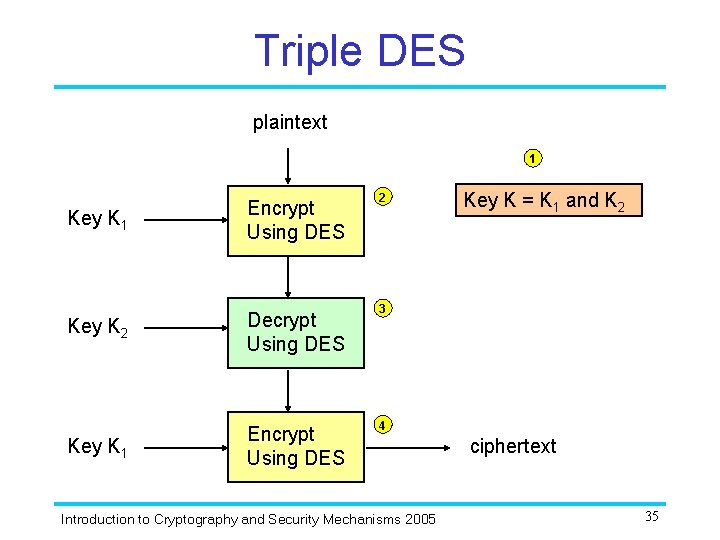
Triple DES plaintext 1 Key K 1 Encrypt Using DES Key K 2 Decrypt Using DES Key K 1 Encrypt Using DES 2 Key K = K 1 and K 2 3 4 Introduction to Cryptography and Security Mechanisms 2005 ciphertext 35
Triple DES 1. Could you encrypt at step 3 of Triple DES instead of decrypting? 2. Could you use a third key K 3 at step 4 of Triple DES, rather than reapplying K 1 ? Introduction to Cryptography and Security Mechanisms 2005 36
Design requirements of AES In 1998 NIST issued a call for proposals for a new block cipher standard, to be referred to as the Advanced Encryption Standard or AES. • • The selection would be a public process and the chosen algorithm and design details would be made freely available for public use. The block size should be 128 bits. The block cipher would be designed to offer variable key lengths of 128, 192 and 256 bits, to allow for future developments in exhaustive key search efforts. The block cipher had to operate at a faster speed than Triple DES across a number of different platforms. Introduction to Cryptography and Security Mechanisms 2005 37
Development of AES • 15 candidate proposals, quickly reduced to 11 in August 1998. • In April 1999, after a public consultation process, this was reduced to five candidates: MARS, RC 6, Rijndael, SERPENT and TWOFISH. • In October 2000 the winning algorithm Rijndael was selected. • Federal Information Processing Standard FIPS 197, the Advanced Encryption Standard, published early 2001. This standard specifies AES (Rijndael) as a FIPSapproved symmetric encryption algorithm that may be used by U. S. Government organizations (and others) to protect sensitive information. • AES now widely adopted and supported. Introduction to Cryptography and Security Mechanisms 2005 38
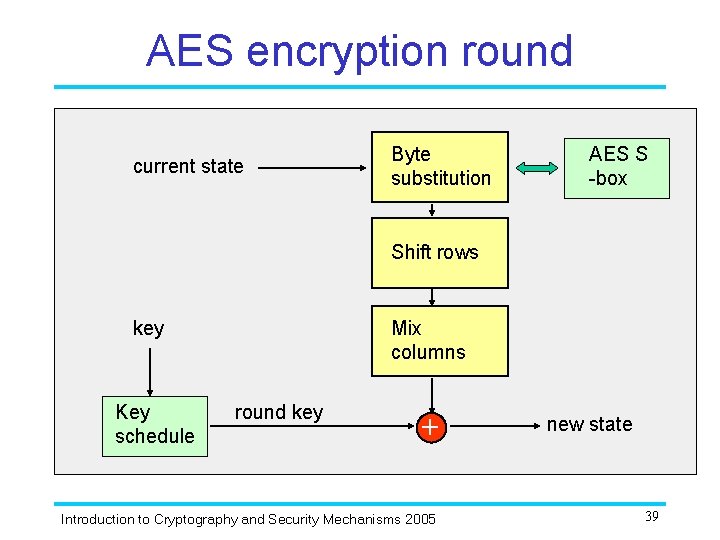
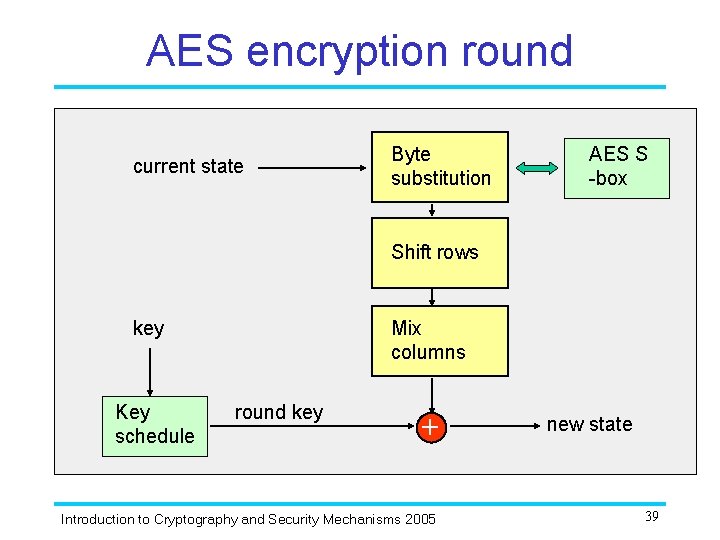
AES encryption round current state Byte substitution AES S -box Shift rows key Key schedule Mix columns round key ++ Introduction to Cryptography and Security Mechanisms 2005 new state 39
AES Do you think that the standardisation of AES means the end of Triple DES? Introduction to Cryptography and Security Mechanisms 2005 40
4. Modes of operation Introduction to Cryptography and Security Mechanisms 2005
Modes of operation of a block cipher are operational rules for a generic block cipher that each result in different properties being achieved. In theory any block cipher could be used in any mode of operation, and the decision concerning which mode of operation to use will in practice be influenced by the application and the properties desired. The three modes of operation that we will study are not the only modes of operation proposed for block ciphers, but they are three of the most commonly used. Introduction to Cryptography and Security Mechanisms 2005 42
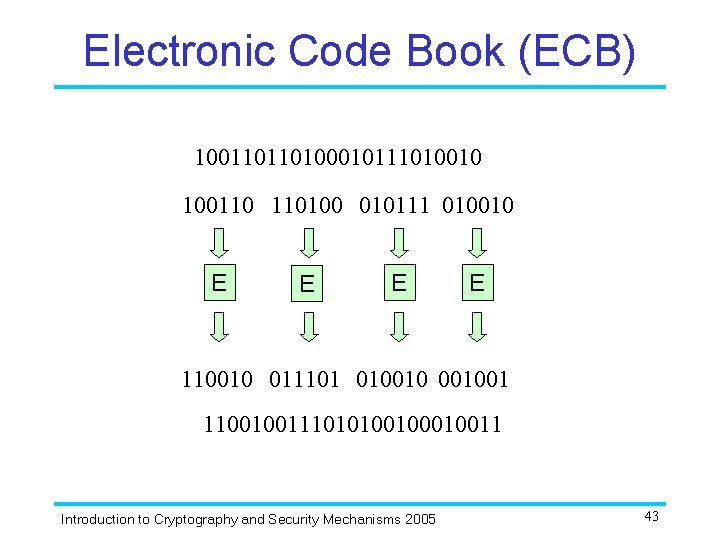
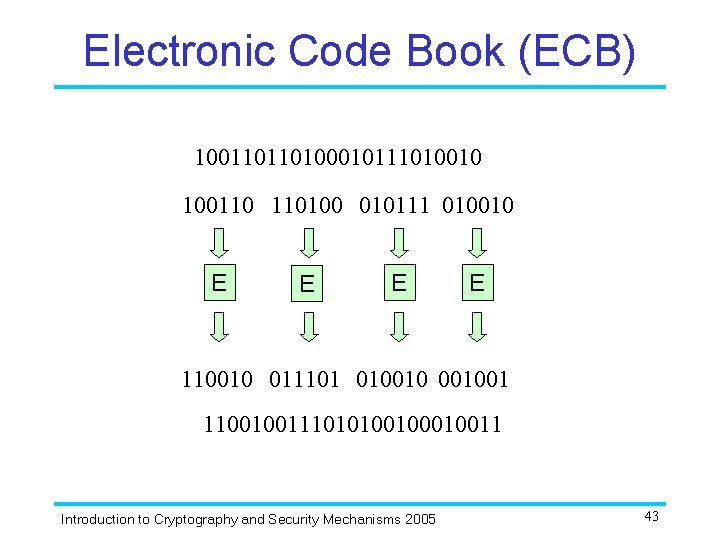
Electronic Code Book (ECB) 100110110100010111010010 100110 110100 010111 010010 E E 110010 011101 01001001 110010011101010010011 Introduction to Cryptography and Security Mechanisms 2005 43
Problem with ECB mode Try to come up with at least three reasons why ECB mode is rarely used and generally regarded as an insecure mode of operation. Make sure you attempt Exercise 6 for this unit in order to further appreciate these problems with ECB mode. Introduction to Cryptography and Security Mechanisms 2005 44
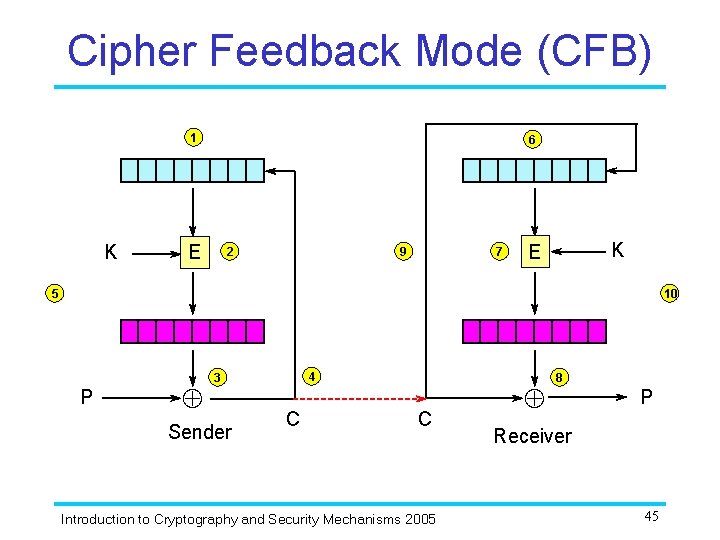
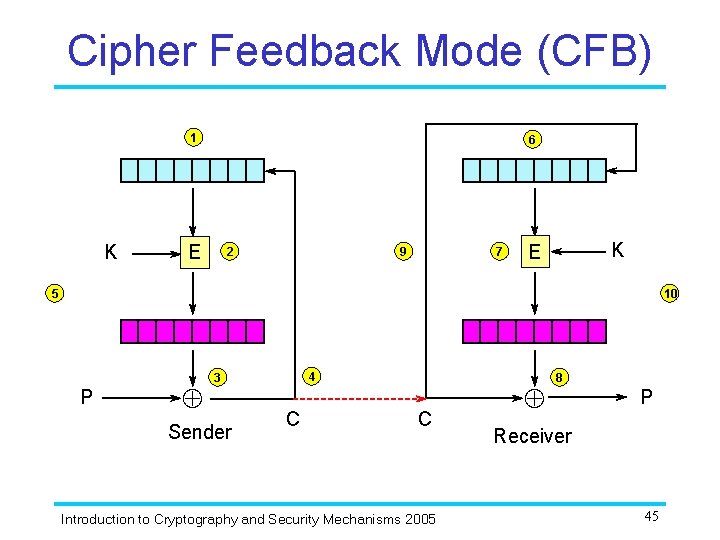
Cipher Feedback Mode (CFB) 1 K 6 E 2 9 7 K E 5 10 P 4 3 Sender C C Introduction to Cryptography and Security Mechanisms 2005 8 P Receiver 45
Cipher Feedback Mode Paradoxically, when using CFB mode you never actually use the encryption algorithm to decrypt anything! CFB mode is actually using a block cipher to make a sort of stream cipher. The encryption algorithm is used as a keystream generator to produce key material. This key material is then added to the plaintext very much in the style of a stream cipher. The receiver also uses the encryption algorithm to generate the same keystream that is needed to decrypt the ciphertext. Introduction to Cryptography and Security Mechanisms 2005 46
CFB in practice Most practical implementations of CFB mode process the plaintext in units of bits that are smaller than the block size. For example, when using an encryption algorithm with a block size of 64 in 8 -bit CFB mode the plaintext is processed 8 bits at a time. This produces only 8 bits of ciphertext. When these 8 bits of ciphertext are fed back, they are not sufficient to replace the current register contents, so the existing entries are shifted along, with the 8 furthest bits dropping out. For what reasons might you want to use 8 -bit CFB mode, rather than full block CFB mode? Introduction to Cryptography and Security Mechanisms 2005 47
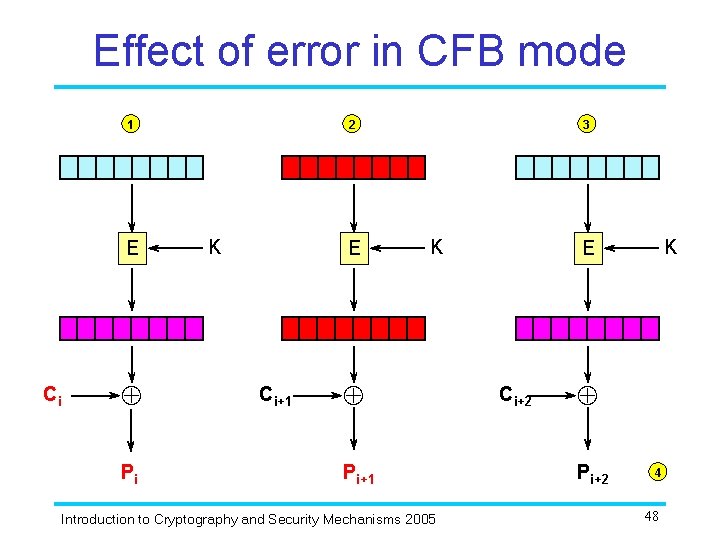
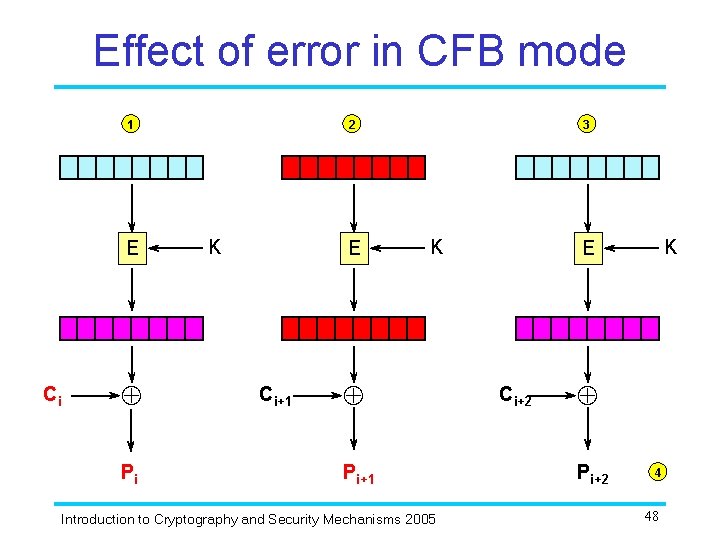
Effect of error in CFB mode 1 E Ci Pi 2 K E Ci+1 3 K Pi+1 Introduction to Cryptography and Security Mechanisms 2005 K E Ci+2 Pi+2 4 48
Properties of CFB mode • • Message dependence Limited error propagation No block synchronisation required Efficiency To what extent do these properties also hold for 8 -bit CFB mode? Introduction to Cryptography and Security Mechanisms 2005 49
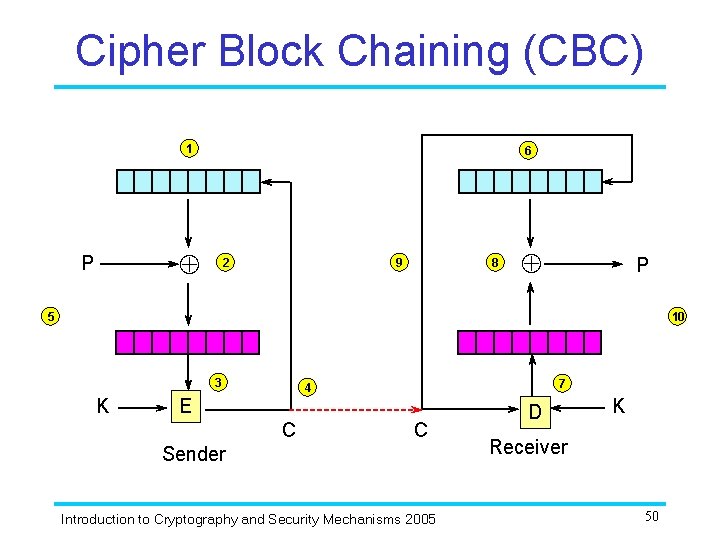
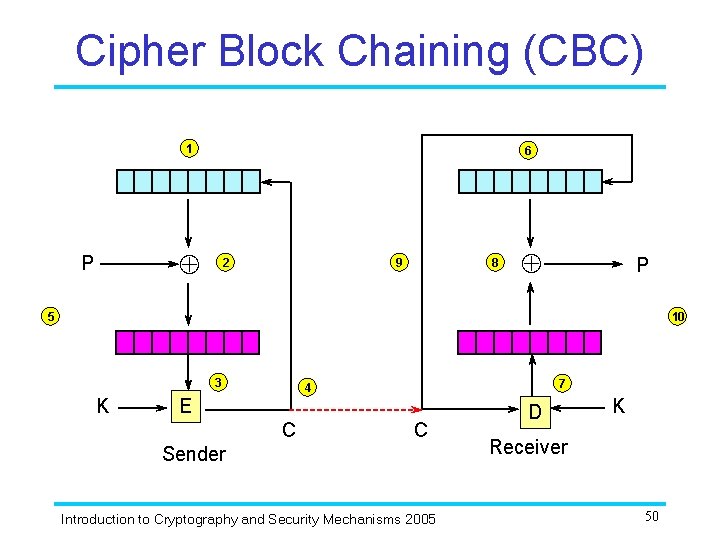
Cipher Block Chaining (CBC) 1 6 P 2 9 8 P 5 10 3 K 7 4 E C C Sender Introduction to Cryptography and Security Mechanisms 2005 D K Receiver 50
CBC mode All CBC mode is doing is adding each plaintext block to the previous ciphertext block, and then encrypting the result with the key: C 1 = EK (P 1 IV) Ci = EK (Pi Ci-1 ) It is worth working through a simple example to get the hang of CBC mode: one such example is provided in Chapter 7 of Piper and Murphy. Introduction to Cryptography and Security Mechanisms 2005 51
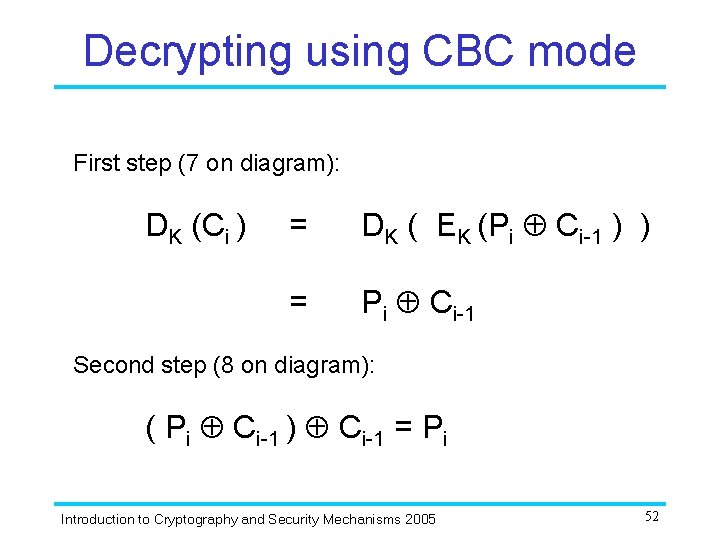
Decrypting using CBC mode First step (7 on diagram): DK (Ci ) = DK ( EK (Pi Ci-1 ) ) = Pi Ci-1 Second step (8 on diagram): ( Pi Ci-1 ) Ci-1 = Pi Introduction to Cryptography and Security Mechanisms 2005 52
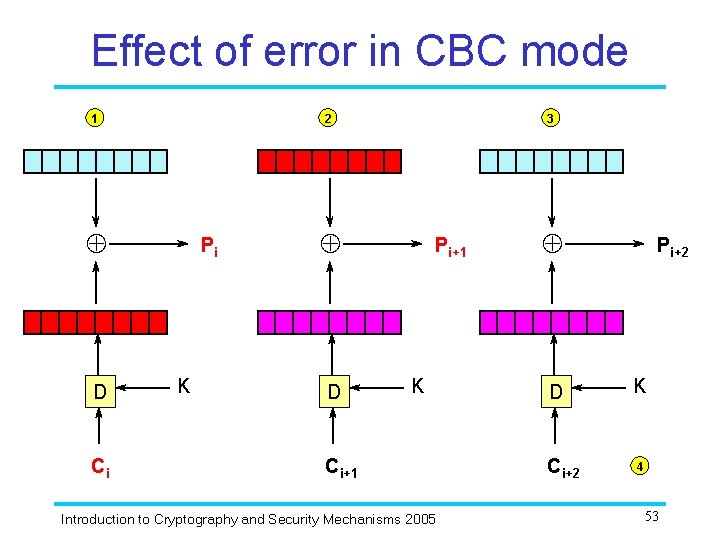
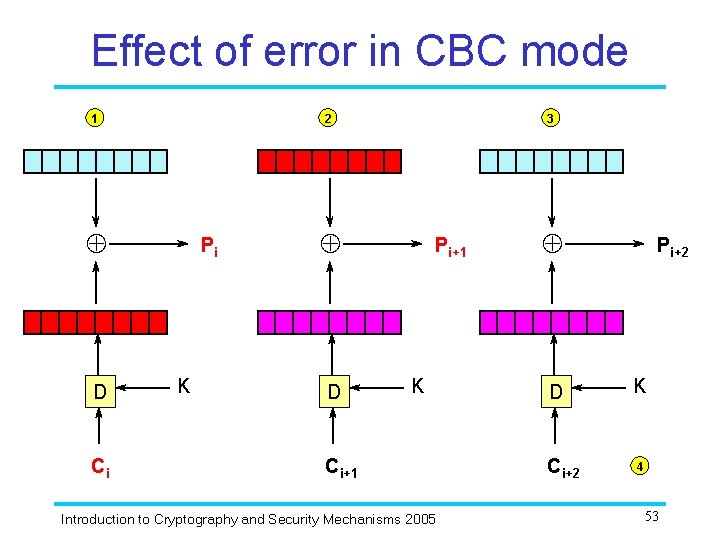
Effect of error in CBC mode 1 2 D Ci Pi K 3 D Pi+1 K Ci+1 Introduction to Cryptography and Security Mechanisms 2005 D Ci+2 Pi+2 K 4 53
Properties of CBC mode Recall the properties of CFB mode. To what extent does CBC mode offer these properties? We will see later that CBC mode can also be used to design a Message Authentication Code Introduction to Cryptography and Security Mechanisms 2005 54
Summary • Stream ciphers and block ciphers are different types of symmetric encryption algorithm. They offer slightly different properties and are therefore suitable for different applications. – Simple stream ciphers are fast and do not propagate errors, making them suitable for poor quality channels and for applications where errors are intolerable. – Block ciphers do propagate errors (to a limited extent), but are quite flexible and can be used in different ways in order to provide different security properties (in some cases to achieve some of the benefits of stream ciphers). • The properties of cryptographic algorithms are not only affected by algorithm design, but also by the ways in which the algorithms are used. Different modes of operation can significantly change the properties of a block cipher. Introduction to Cryptography and Security Mechanisms 2005 55