Introduction to Computer Security Dr Neminath Hubballi IIT
Introduction to Computer Security Dr. Neminath Hubballi IIT Indore © Neminah Hubballi
Next 50 Minutes at a Glance § Administrative stuff § § Instructor and TA Text Book and reading Material Course Content Evaluation Criteria § Fundamentals of security § Define security § Learn why should we care about security § CIA principles of security IIT Indore © Neminah Hubballi
Administrative Stuff § Instructor § Neminath Hubballi and Somnath Dey § Area of expertise in Network Security, System Security § Room No - XXXXXX § Readings § Text Book: § Introduction to Computer Security- Goodrich and Tamassia § Computer Security – William Stallings § Security and Usability Designing Secure Systems that People Can Use – Lorre Faith Cranor and Simson Garfinkel § Additional reading material § You are expected to go through additional material- web has enormous amount of material on security § Two Lectures + One Tutorial per week § Teaching Assistant § Deepak - A Graduate student in school of Computer Science § Tutorials will be handled by him IIT Indore © Neminah Hubballi
Prerequisites § Computer Networks § Operating Systems § C and Java Programming § Working Proficiency with Linux system § Knowing Perl/Shell Scripting will be an advantage IIT Indore © Neminah Hubballi
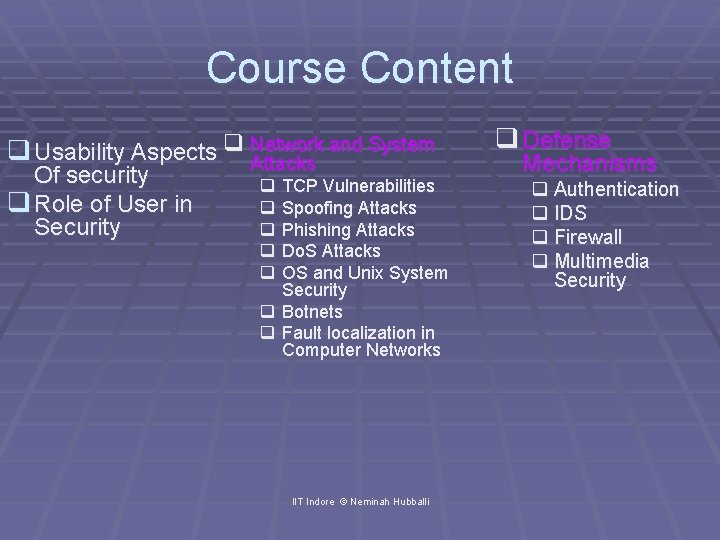
Course Content and System q Usability Aspects q Network Attacks Of security q Role of User in Security q TCP Vulnerabilities q Spoofing Attacks q Phishing Attacks q Do. S Attacks q OS and Unix System Security q Botnets q Fault localization in Computer Networks IIT Indore © Neminah Hubballi q Defense Mechanisms q Authentication q IDS q Firewall q Multimedia Security
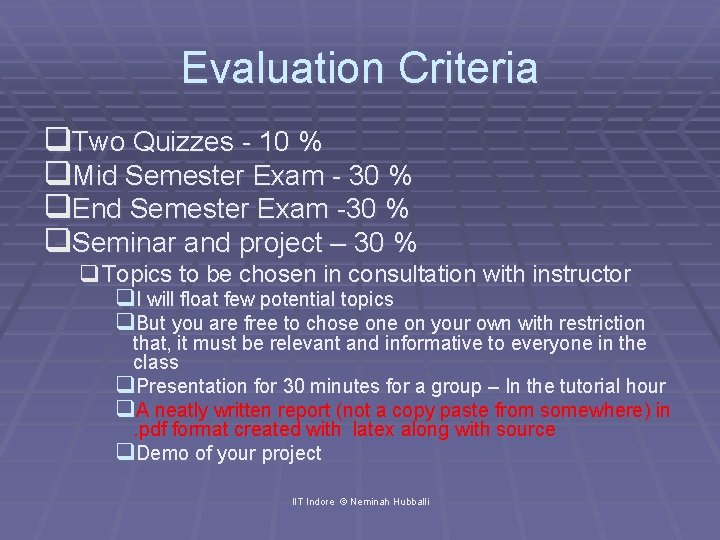
Evaluation Criteria q. Two Quizzes - 10 % q. Mid Semester Exam - 30 % q. End Semester Exam -30 % q. Seminar and project – 30 % q. Topics to be chosen in consultation with instructor q. I will float few potential topics q. But you are free to chose on your own with restriction that, it must be relevant and informative to everyone in the class q. Presentation for 30 minutes for a group – In the tutorial hour q. A neatly written report (not a copy paste from somewhere) in. pdf format created with latex along with source q. Demo of your project IIT Indore © Neminah Hubballi
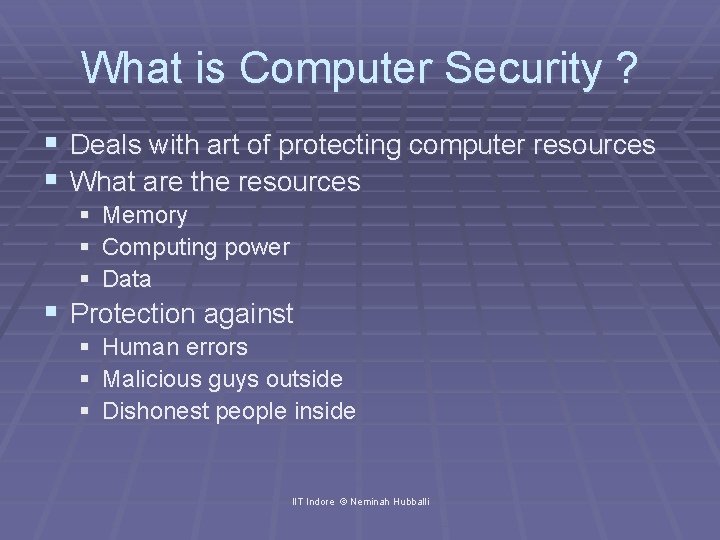
What is Computer Security ? § Deals with art of protecting computer resources § What are the resources § § § Memory Computing power Data § Protection against § § § Human errors Malicious guys outside Dishonest people inside IIT Indore © Neminah Hubballi
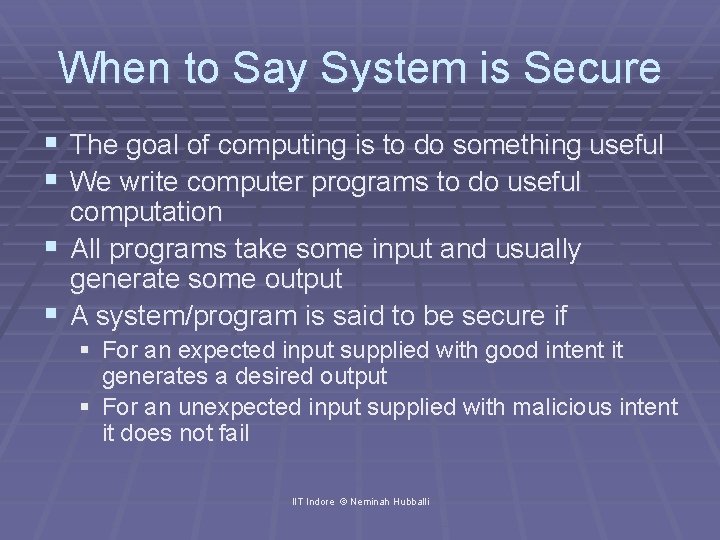
When to Say System is Secure § The goal of computing is to do something useful § We write computer programs to do useful computation § All programs take some input and usually generate some output § A system/program is said to be secure if § For an expected input supplied with good intent it generates a desired output § For an unexpected input supplied with malicious intent it does not fail IIT Indore © Neminah Hubballi
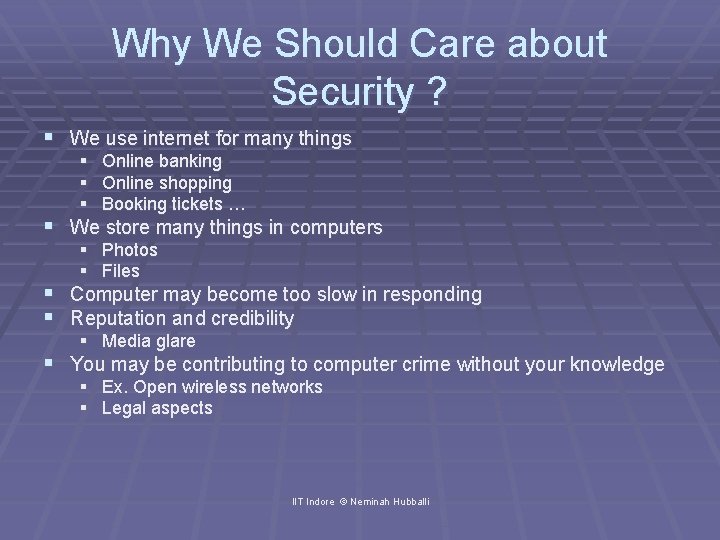
Why We Should Care about Security ? § We use internet for many things § Online banking § Online shopping § Booking tickets … § We store many things in computers § Photos § Files § Computer may become too slow in responding § Reputation and credibility § Media glare § You may be contributing to computer crime without your knowledge § Ex. Open wireless networks § Legal aspects IIT Indore © Neminah Hubballi
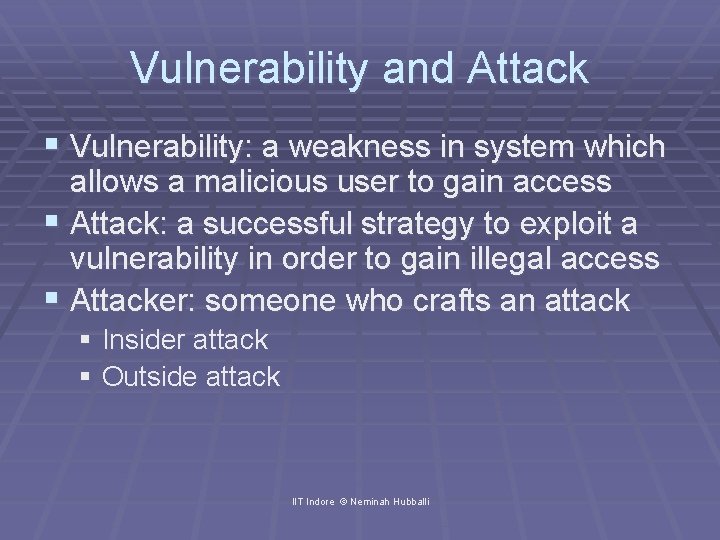
Vulnerability and Attack § Vulnerability: a weakness in system which allows a malicious user to gain access § Attack: a successful strategy to exploit a vulnerability in order to gain illegal access § Attacker: someone who crafts an attack § Insider attack § Outside attack IIT Indore © Neminah Hubballi
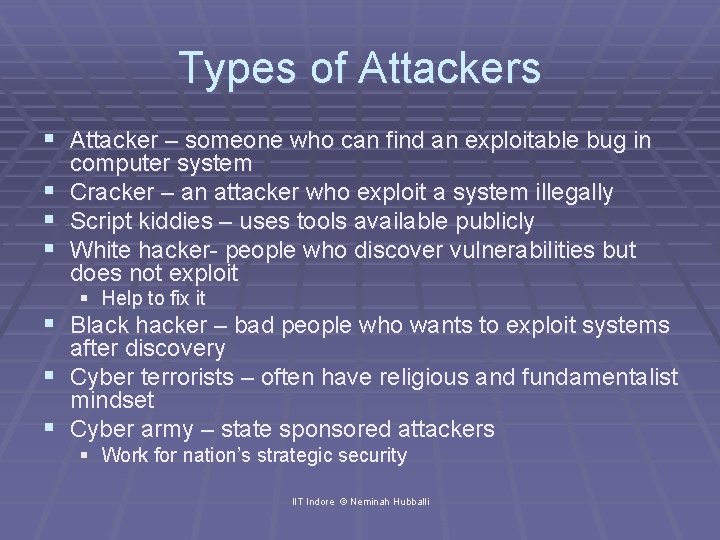
Types of Attackers § Attacker – someone who can find an exploitable bug in § § § computer system Cracker – an attacker who exploit a system illegally Script kiddies – uses tools available publicly White hacker- people who discover vulnerabilities but does not exploit § Help to fix it § Black hacker – bad people who wants to exploit systems after discovery § Cyber terrorists – often have religious and fundamentalist mindset § Cyber army – state sponsored attackers § Work for nation’s strategic security IIT Indore © Neminah Hubballi
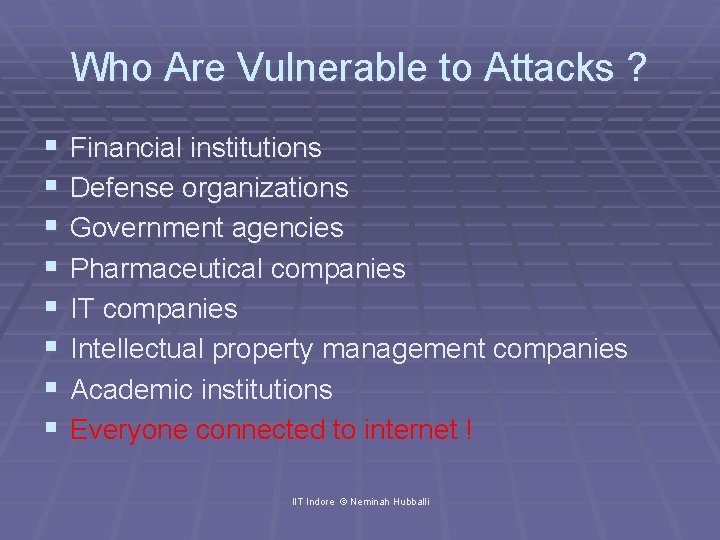
Who Are Vulnerable to Attacks ? § § § § Financial institutions Defense organizations Government agencies Pharmaceutical companies IT companies Intellectual property management companies Academic institutions Everyone connected to internet ! IIT Indore © Neminah Hubballi
CIA Principles of Security § Information security is defined by an acronym CIA § Confidentiality: Avoiding unauthorized disclosure of information § Integrity: An assurance that information is not altered midway of transmission § Availability: An assurance of information access and modification in a reasonable timeframe IIT Indore © Neminah Hubballi
The Value of Your Network § Lost data § Financial loss § Confidential data § Danger of going into wrong hands § Downtime § Calling a customer care which says my server is down § It looks cheap § Staff time § Time invested in repairing and fixing the issue § Reputation § Damage § Financial loss IIT Indore © Neminah Hubballi
Security Mechanism § Economy of mechanism § The easier and simple a security mechanism the better it is to understand § Fail-safe defaults § Default configuration should be conservative § Complete mediation § A security authority should check every action of a user § Open design § Security design should be made public § Separation of privilege § Multiple conditions should be required to get access IIT Indore © Neminah Hubballi
Security Mechanism § Least privileges § Every program must have bare minimum privileges to run § Least common mechanism § Says sharing among users should be minimum § Psychological acceptability § User interfaces should be intuitive § Compromise recording § Sometime it is more desirable to record details of an attack rather than designing a comprehensive security mechanism IIT Indore © Neminah Hubballi
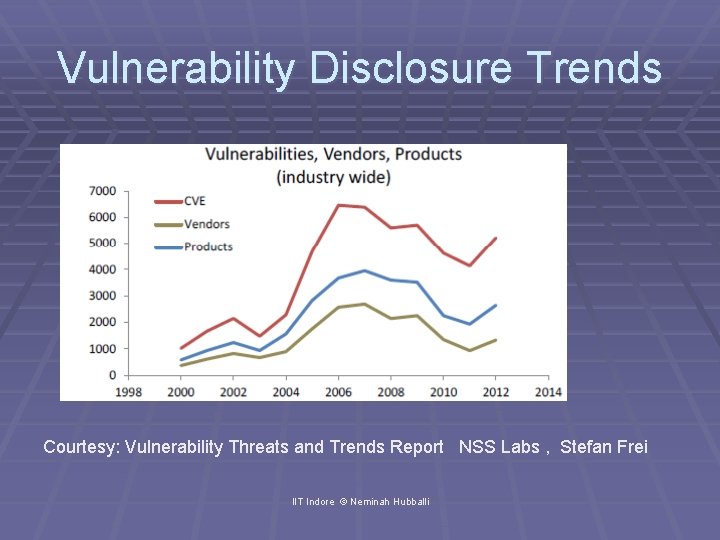
Vulnerability Disclosure Trends Courtesy: Vulnerability Threats and Trends Report NSS Labs , Stefan Frei IIT Indore © Neminah Hubballi
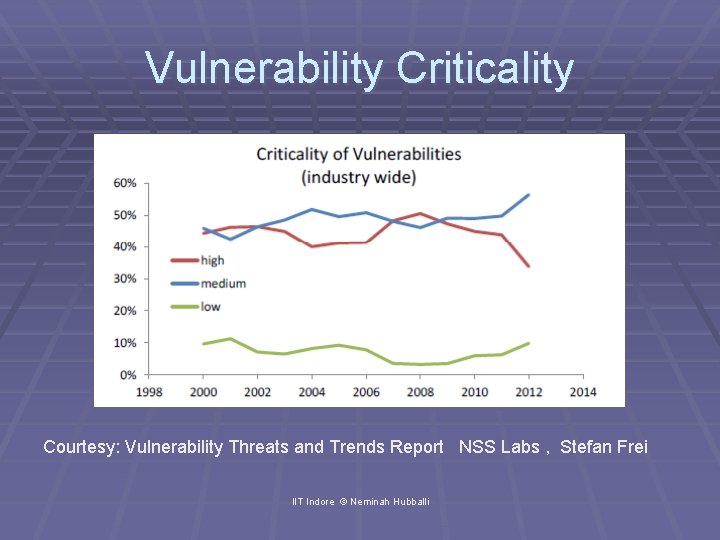
Vulnerability Criticality Courtesy: Vulnerability Threats and Trends Report NSS Labs , Stefan Frei IIT Indore © Neminah Hubballi
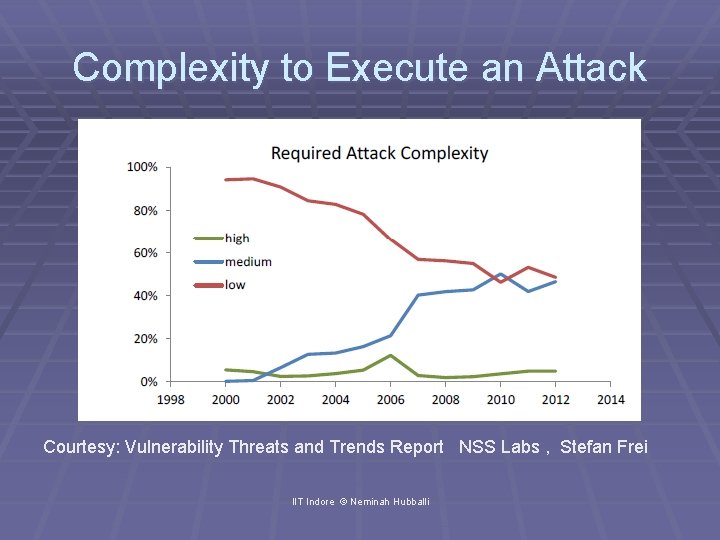
Complexity to Execute an Attack Courtesy: Vulnerability Threats and Trends Report NSS Labs , Stefan Frei IIT Indore © Neminah Hubballi
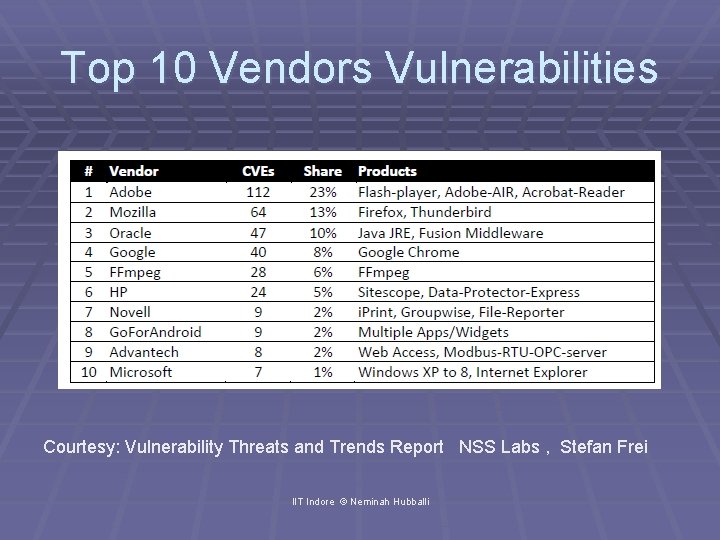
Top 10 Vendors Vulnerabilities Courtesy: Vulnerability Threats and Trends Report NSS Labs , Stefan Frei IIT Indore © Neminah Hubballi
- Slides: 20