Introducing Computer Systems from a Programmers Perspective Randal
![Lecture Coverage Data representations [3] n n It’s all just bits. int’s are not Lecture Coverage Data representations [3] n n It’s all just bits. int’s are not](https://slidetodoc.com/presentation_image_h2/3f2e2263161f7a1751f7272fd6999e89/image-13.jpg)
![Lecture Coverage (cont) Exceptional Control Flow [2] n The system includes an operating system Lecture Coverage (cont) Exceptional Control Flow [2] n The system includes an operating system](https://slidetodoc.com/presentation_image_h2/3f2e2263161f7a1751f7272fd6999e89/image-14.jpg)
- Slides: 29
Introducing Computer Systems from a Programmer’s Perspective Randal E. Bryant, David R. O’Hallaron Computer Science and Electrical Engineering Carnegie Mellon University
Outline Introduction to Computer Systems n Course taught at CMU since Fall, 1998 n Some ideas on labs, motivations, … Computer Systems: A Programmer’s Perspective n n Our textbook Ways to use the book in different courses The Role of Systems Design in CS/Engineering Curricula – 2– ICS
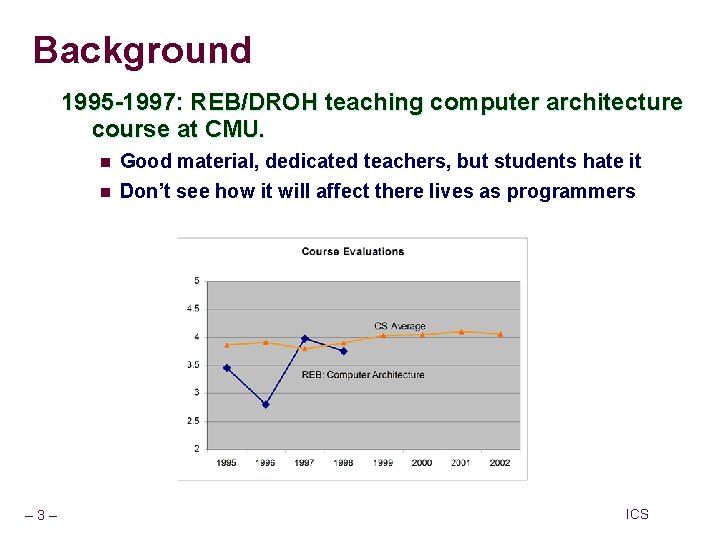
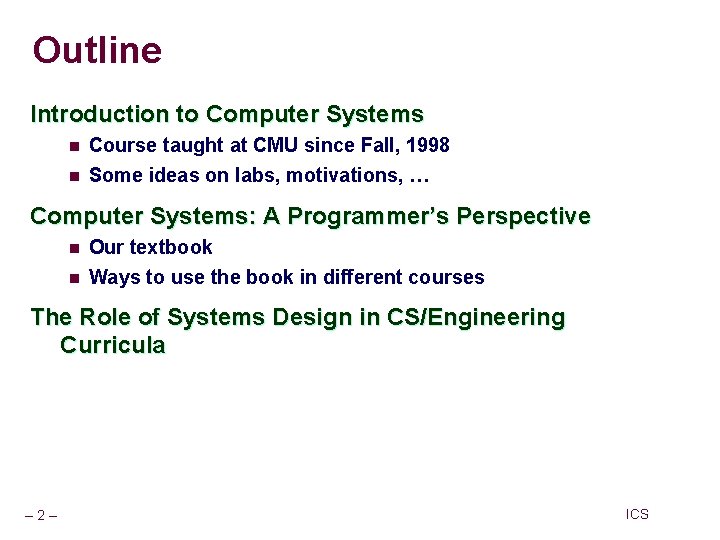
Background 1995 -1997: REB/DROH teaching computer architecture course at CMU. n n – 3– Good material, dedicated teachers, but students hate it Don’t see how it will affect there lives as programmers ICS
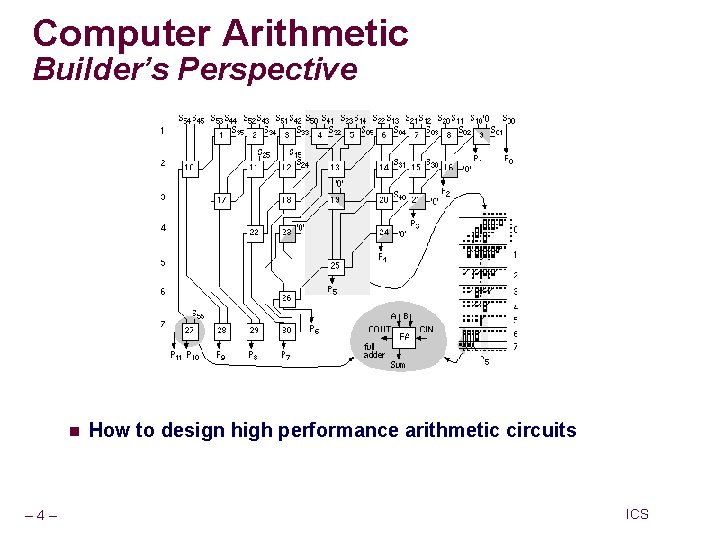
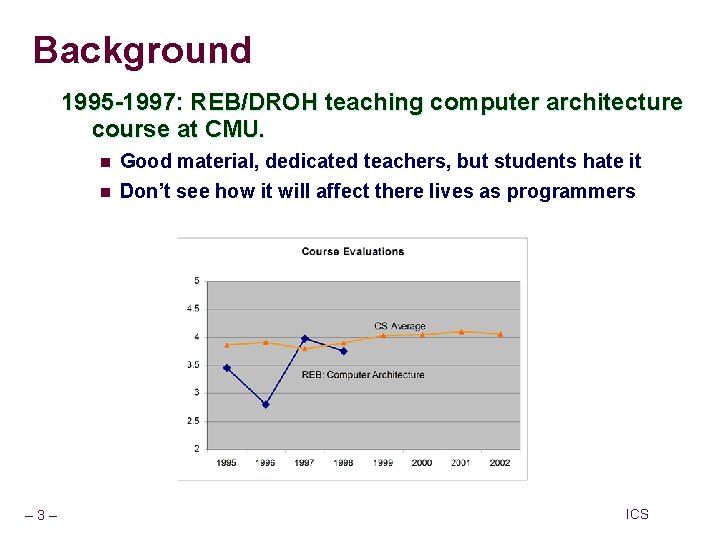
Computer Arithmetic Builder’s Perspective 32 -bit Multiplier n – 4– How to design high performance arithmetic circuits ICS
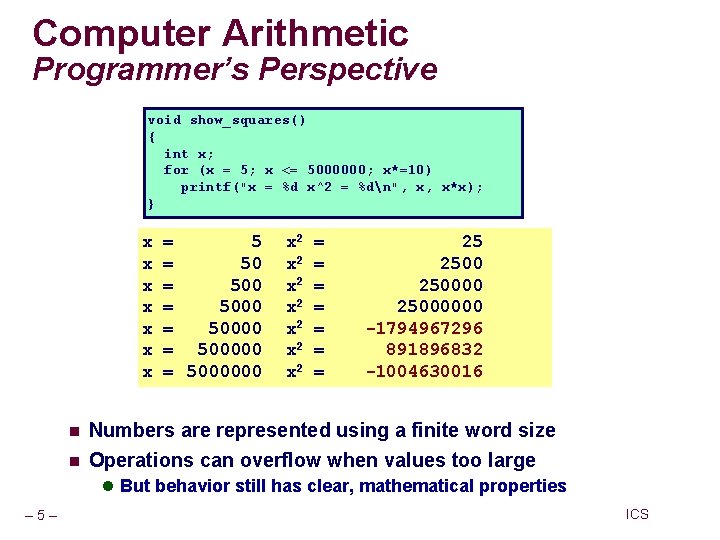
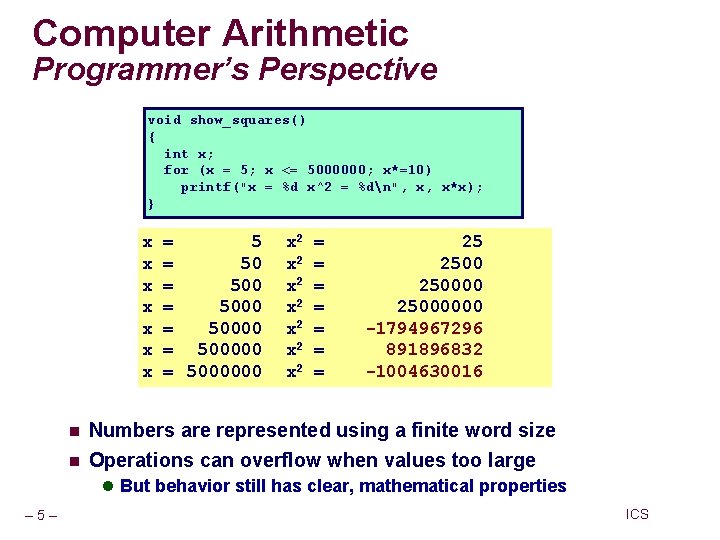
Computer Arithmetic Programmer’s Perspective void show_squares() { int x; for (x = 5; x <= 5000000; x*=10) printf("x = %d x^2 = %dn", x, x*x); } x x x x n n = 5000 = 5000000 x 2 x 2 = = = = 25 25000000 -1794967296 891896832 -1004630016 Numbers are represented using a finite word size Operations can overflow when values too large l But behavior still has clear, mathematical properties – 5– ICS
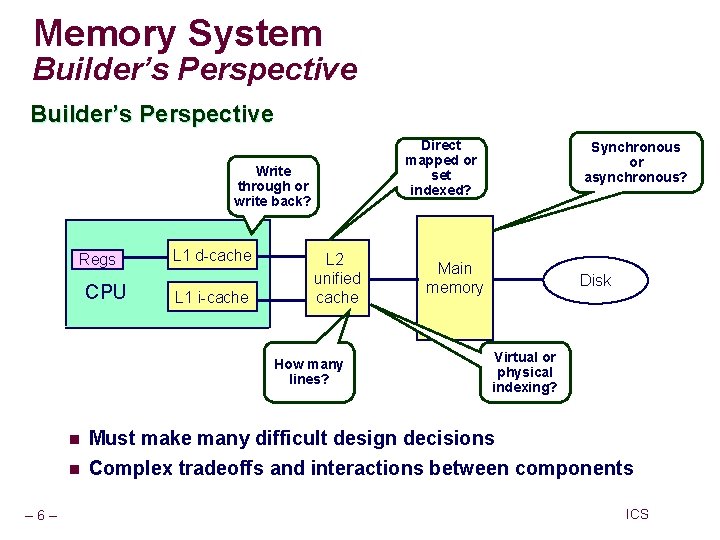
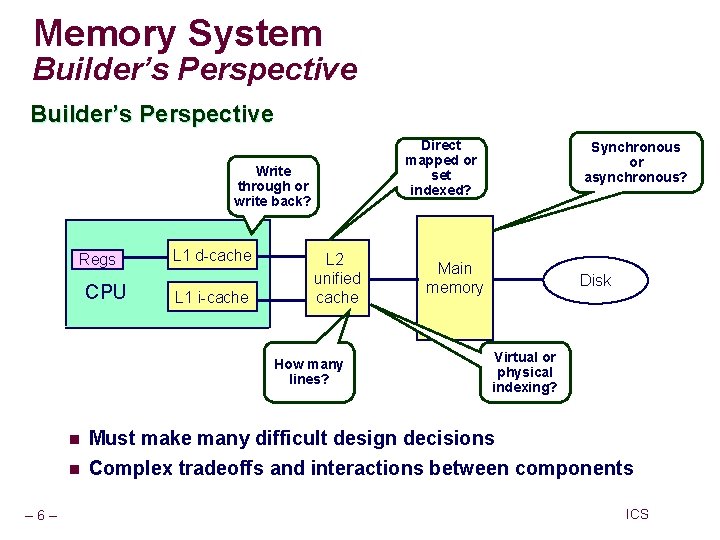
Memory System Builder’s Perspective Direct mapped or set indexed? Write through or write back? Regs CPU L 1 d-cache L 1 i-cache L 2 unified cache How many lines? n n – 6– Synchronous or asynchronous? Main memory Disk Virtual or physical indexing? Must make many difficult design decisions Complex tradeoffs and interactions between components ICS
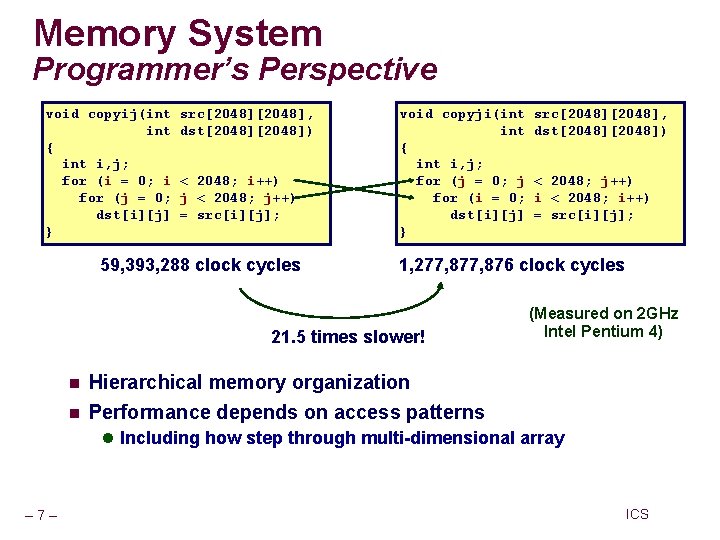
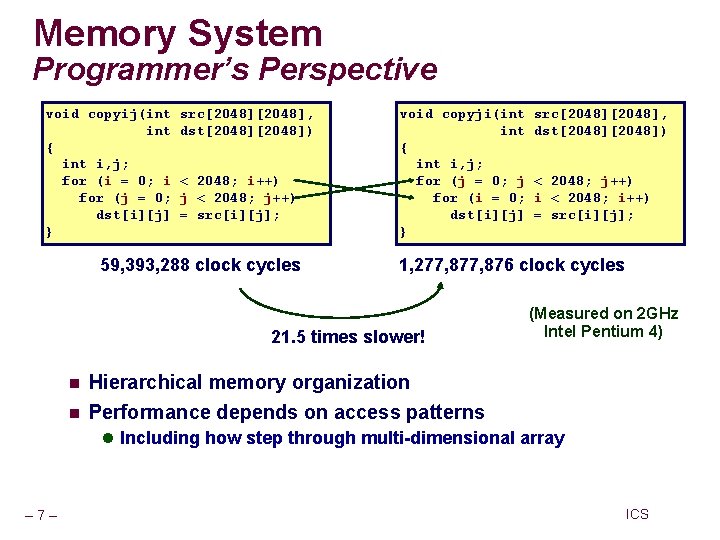
Memory System Programmer’s Perspective void copyij(int { int i, j; for (i = 0; i for (j = 0; dst[i][j] } src[2048], dst[2048]) < 2048; i++) j < 2048; j++) = src[i][j]; 59, 393, 288 clock cycles void copyji(int { int i, j; for (j = 0; j for (i = 0; dst[i][j] } n < 2048; j++) i < 2048; i++) = src[i][j]; 1, 277, 876 clock cycles 21. 5 times slower! n src[2048], dst[2048]) (Measured on 2 GHz Intel Pentium 4) Hierarchical memory organization Performance depends on access patterns l Including how step through multi-dimensional array – 7– ICS
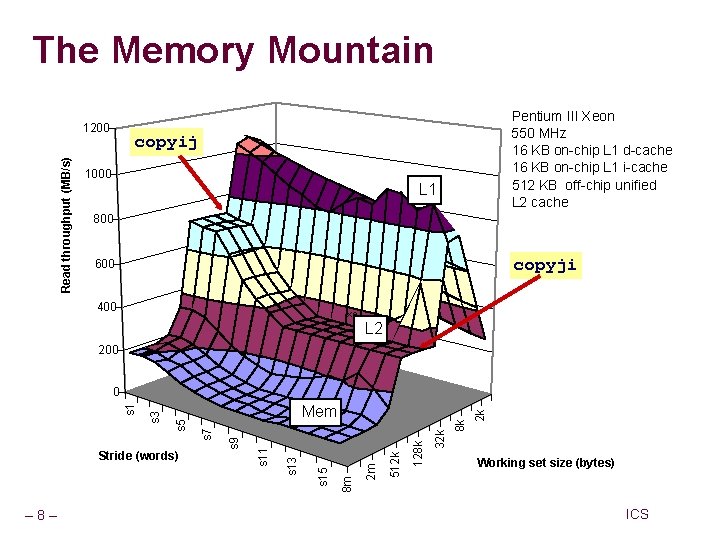
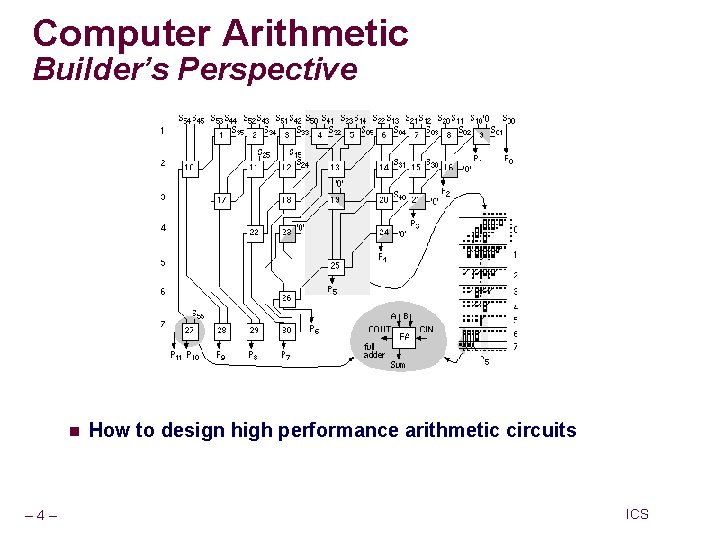
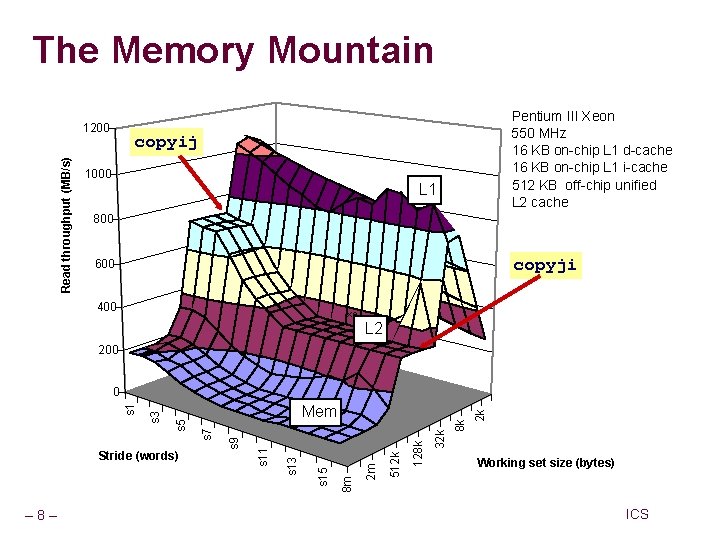
The Memory Mountain Read throughput (MB/s) 1200 Pentium III Xeon 550 MHz 16 KB on-chip L 1 d-cache 16 KB on-chip L 1 i-cache 512 KB off-chip unified L 2 cache copyij 1000 L 1 800 copyji 600 400 xe L 2 200 – 8– 2 k 8 k 32 k 128 k 512 k 2 m 8 m s 15 s 13 s 11 s 9 Stride (words) Mem s 7 s 5 s 3 s 1 0 Working set size (bytes) ICS
Background (Cont. ) 1997: OS instructors complain about lack of preparation n Students don’t know machine-level programming well enough l What does it mean to store the processor state on the run- time stack? n – 9– Our architecture course was not part of prerequisite stream ICS
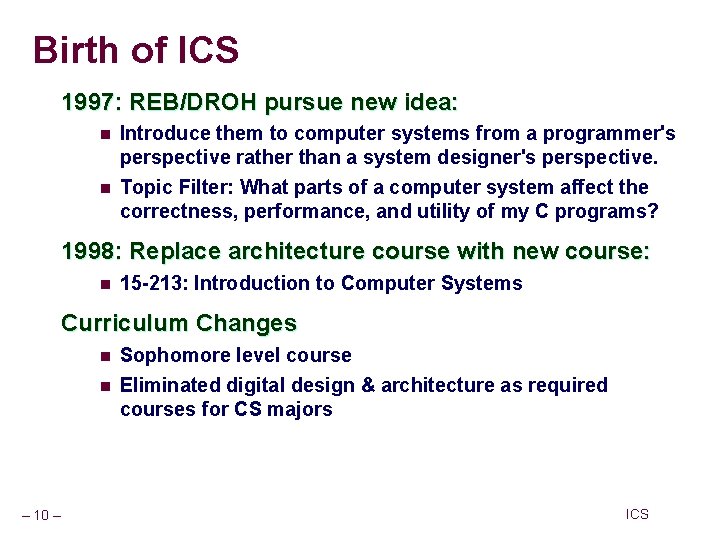
Birth of ICS 1997: REB/DROH pursue new idea: n n Introduce them to computer systems from a programmer's perspective rather than a system designer's perspective. Topic Filter: What parts of a computer system affect the correctness, performance, and utility of my C programs? 1998: Replace architecture course with new course: n 15 -213: Introduction to Computer Systems Curriculum Changes n n – 10 – Sophomore level course Eliminated digital design & architecture as required courses for CS majors ICS
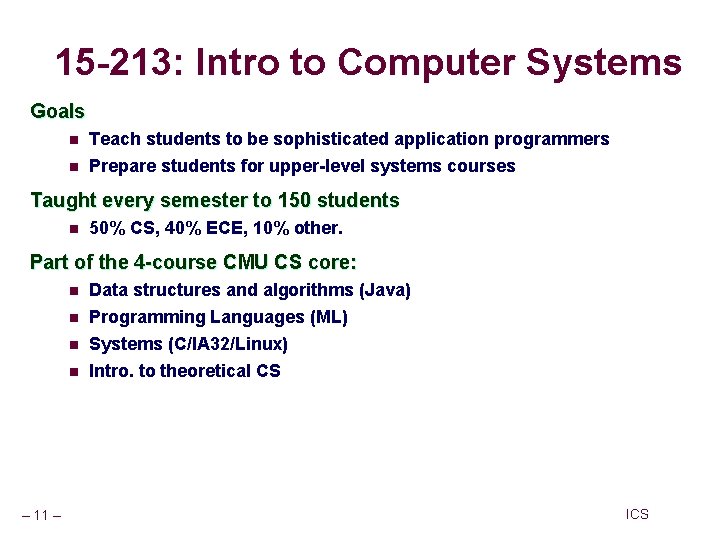
15 -213: Intro to Computer Systems Goals n n Teach students to be sophisticated application programmers Prepare students for upper-level systems courses Taught every semester to 150 students n 50% CS, 40% ECE, 10% other. Part of the 4 -course CMU CS core: n n – 11 – Data structures and algorithms (Java) Programming Languages (ML) Systems (C/IA 32/Linux) Intro. to theoretical CS ICS
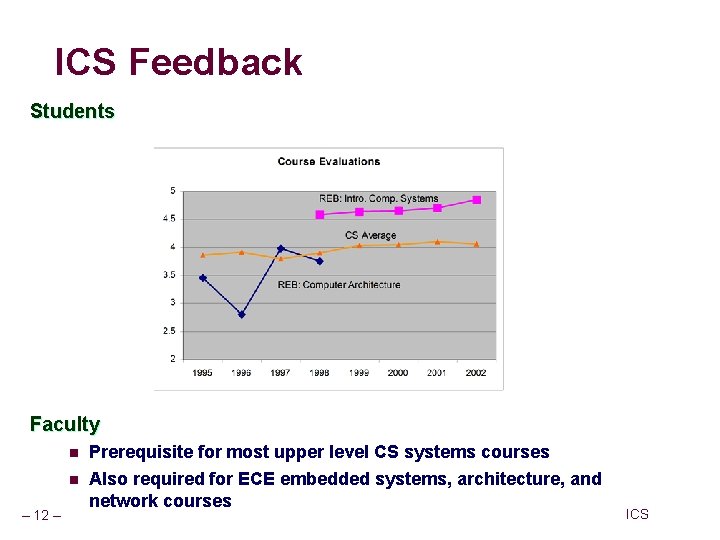
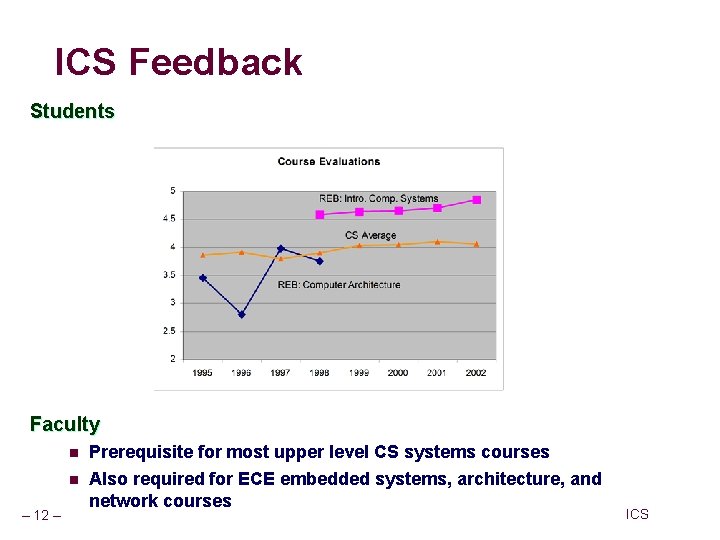
ICS Feedback Students Faculty n n – 12 – Prerequisite for most upper level CS systems courses Also required for ECE embedded systems, architecture, and network courses ICS
![Lecture Coverage Data representations 3 n n Its all just bits ints are not Lecture Coverage Data representations [3] n n It’s all just bits. int’s are not](https://slidetodoc.com/presentation_image_h2/3f2e2263161f7a1751f7272fd6999e89/image-13.jpg)
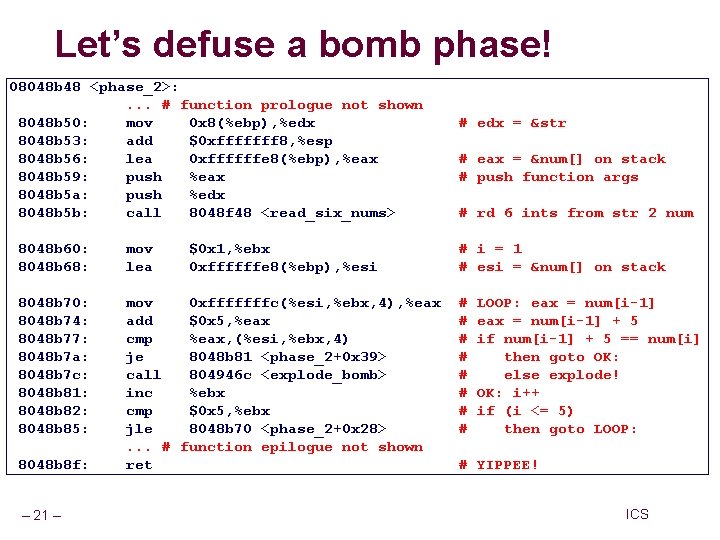
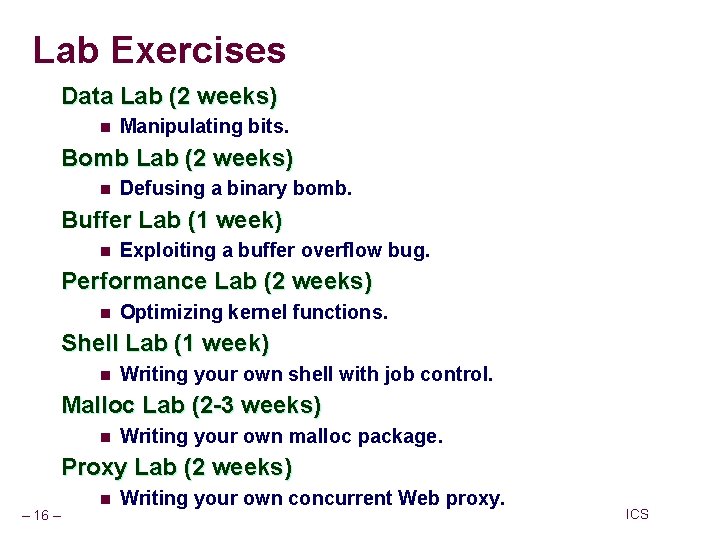
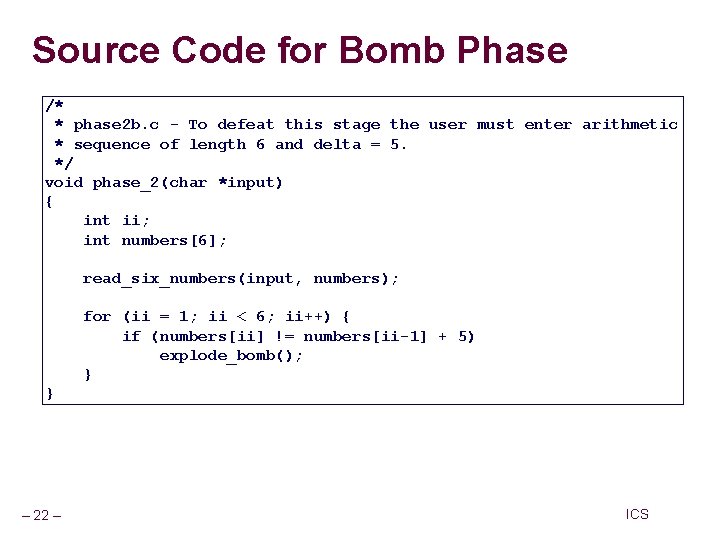
Lecture Coverage Data representations [3] n n It’s all just bits. int’s are not integers and float’s are not reals. IA 32 machine language [5] n Analyzing and understanding compiler-generated machine code. Program optimization [2] n Understanding compilers and modern processors. Memory Hierarchy [3] n Caches matter! Linking [1] n – 13 – With DLL’s, linking is cool again! ICS
![Lecture Coverage cont Exceptional Control Flow 2 n The system includes an operating system Lecture Coverage (cont) Exceptional Control Flow [2] n The system includes an operating system](https://slidetodoc.com/presentation_image_h2/3f2e2263161f7a1751f7272fd6999e89/image-14.jpg)
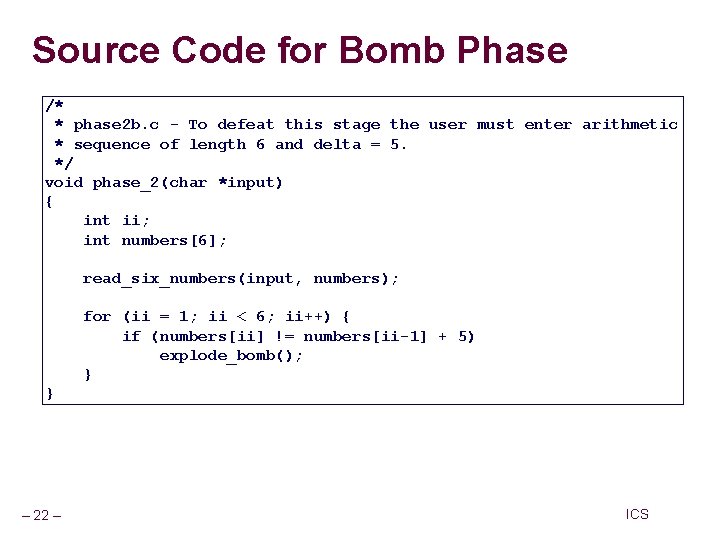
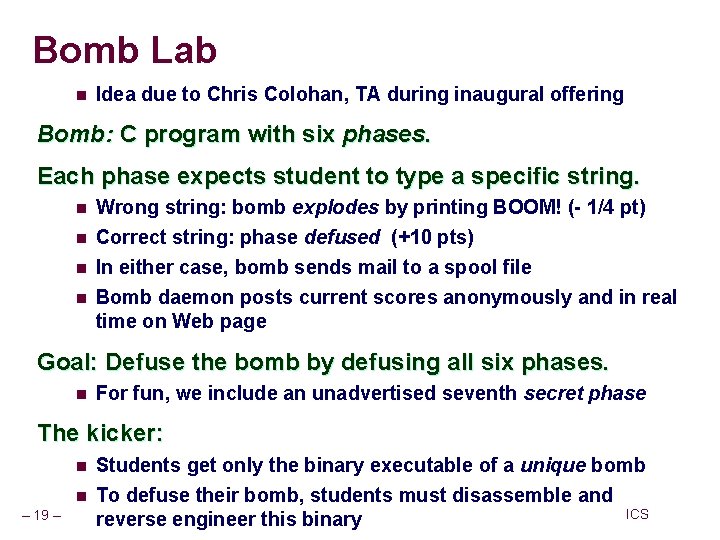
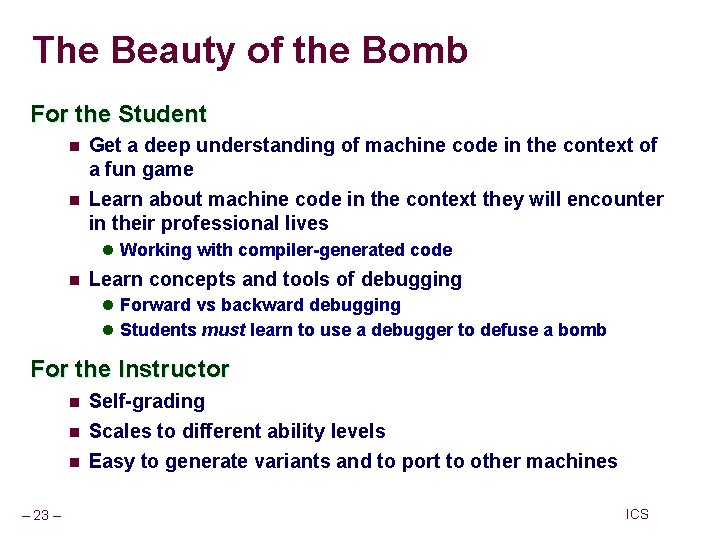
Lecture Coverage (cont) Exceptional Control Flow [2] n The system includes an operating system that you must interact with. Measuring performance [1] n Accounting for time on a computer is tricky! Virtual memory [4] n How it works, how to use it, and how to manage it. I/O and network programming [4] n Programs often need to talk to other programs. Application level concurrency [2] n Processes, I/O multiplexing, and threads. Total: 27 lectures, 14 week semester. – 14 – ICS
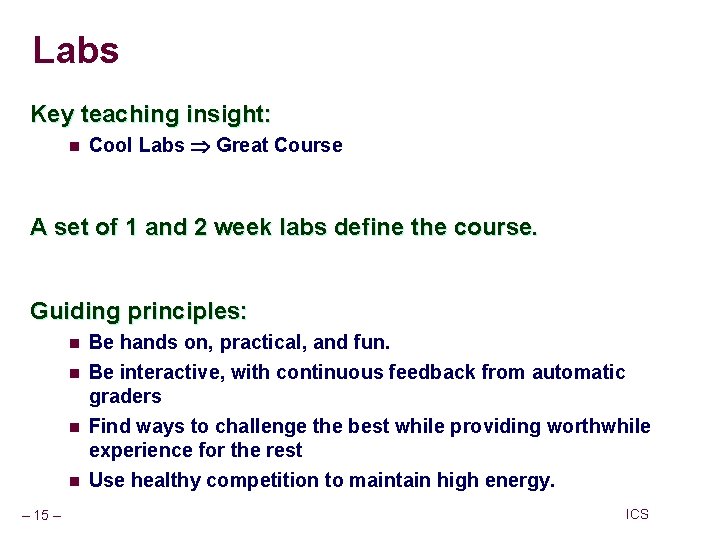
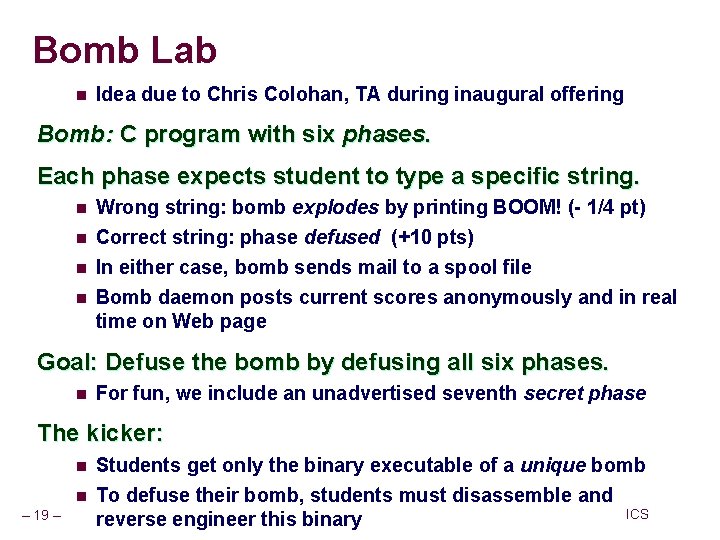
Labs Key teaching insight: n Cool Labs Great Course A set of 1 and 2 week labs define the course. Guiding principles: n n – 15 – Be hands on, practical, and fun. Be interactive, with continuous feedback from automatic graders Find ways to challenge the best while providing worthwhile experience for the rest Use healthy competition to maintain high energy. ICS
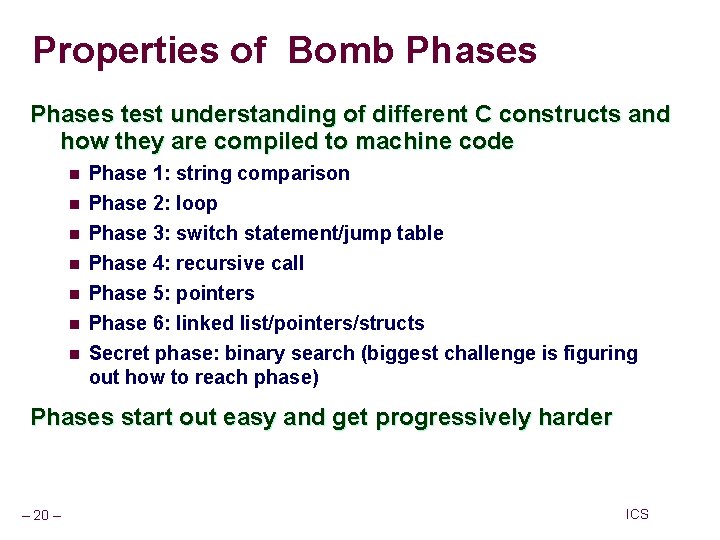
Lab Exercises Data Lab (2 weeks) n Manipulating bits. Bomb Lab (2 weeks) n Defusing a binary bomb. Buffer Lab (1 week) n Exploiting a buffer overflow bug. Performance Lab (2 weeks) n Optimizing kernel functions. Shell Lab (1 week) n Writing your own shell with job control. Malloc Lab (2 -3 weeks) n Writing your own malloc package. Proxy Lab (2 weeks) – 16 – n Writing your own concurrent Web proxy. ICS
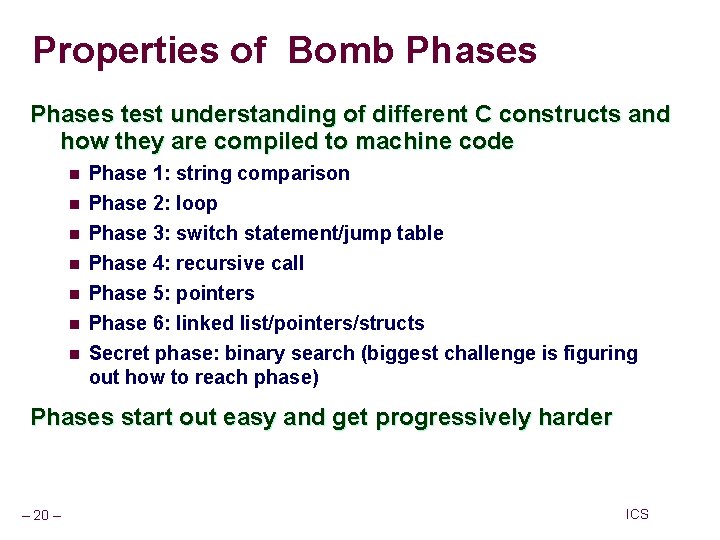
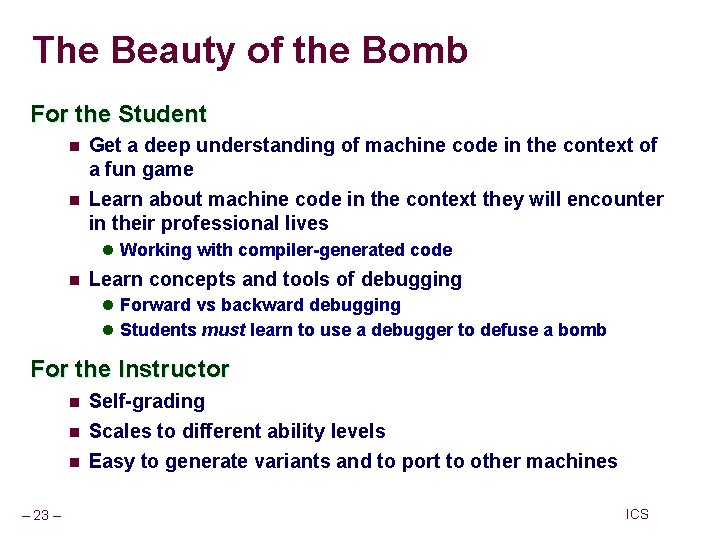
Bomb Lab n Idea due to Chris Colohan, TA during inaugural offering Bomb: C program with six phases. Each phase expects student to type a specific string. n n Wrong string: bomb explodes by printing BOOM! (- 1/4 pt) Correct string: phase defused (+10 pts) In either case, bomb sends mail to a spool file Bomb daemon posts current scores anonymously and in real time on Web page Goal: Defuse the bomb by defusing all six phases. n For fun, we include an unadvertised seventh secret phase The kicker: n n – 19 – Students get only the binary executable of a unique bomb To defuse their bomb, students must disassemble and ICS reverse engineer this binary
Properties of Bomb Phases test understanding of different C constructs and how they are compiled to machine code n n n n Phase 1: string comparison Phase 2: loop Phase 3: switch statement/jump table Phase 4: recursive call Phase 5: pointers Phase 6: linked list/pointers/structs Secret phase: binary search (biggest challenge is figuring out how to reach phase) Phases start out easy and get progressively harder – 20 – ICS
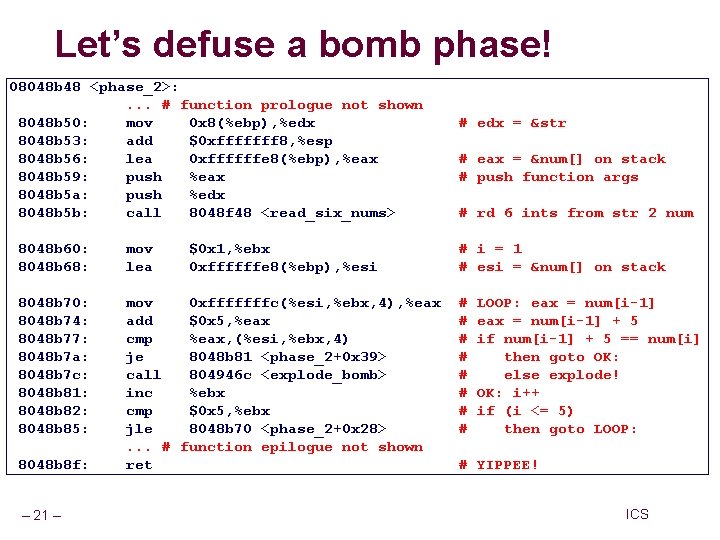
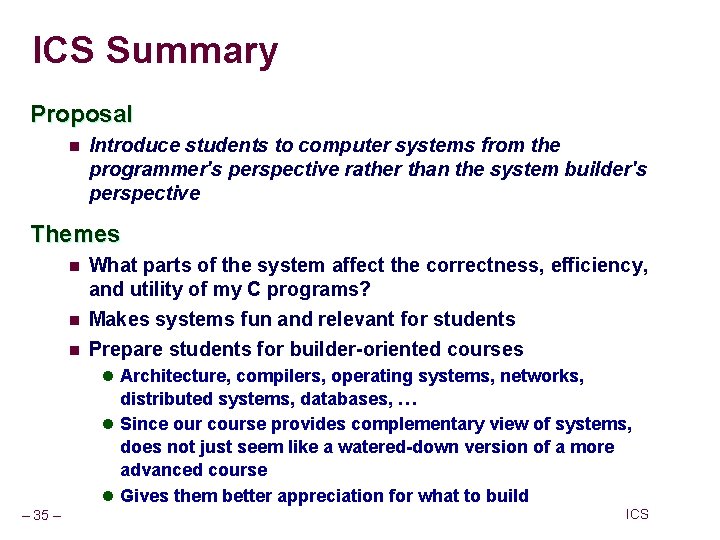
Let’s defuse a bomb phase! 08048 b 48 <phase_2>: . . . # function prologue not shown 8048 b 50: mov 0 x 8(%ebp), %edx 8048 b 53: add $0 xfffffff 8, %esp 8048 b 56: lea 0 xffffffe 8(%ebp), %eax 8048 b 59: push %eax 8048 b 5 a: push %edx 8048 b 5 b: call 8048 f 48 <read_six_nums> 8048 b 60: 8048 b 68: mov lea 8048 b 70: 8048 b 74: 8048 b 77: 8048 b 7 a: 8048 b 7 c: 8048 b 81: 8048 b 82: 8048 b 85: mov 0 xfffffffc(%esi, %ebx, 4), %eax add $0 x 5, %eax cmp %eax, (%esi, %ebx, 4) je 8048 b 81 <phase_2+0 x 39> call 804946 c <explode_bomb> inc %ebx cmp $0 x 5, %ebx jle 8048 b 70 <phase_2+0 x 28>. . . # function epilogue not shown ret 8048 b 8 f: – 21 – $0 x 1, %ebx 0 xffffffe 8(%ebp), %esi # edx = &str # eax = &num[] on stack # push function args # rd 6 ints from str 2 num # i = 1 # esi = &num[] on stack # # # # LOOP: eax = num[i-1] + 5 if num[i-1] + 5 == num[i] then goto OK: else explode! OK: i++ if (i <= 5) then goto LOOP: # YIPPEE! ICS
Source Code for Bomb Phase /* * phase 2 b. c - To defeat this stage the user must enter arithmetic * sequence of length 6 and delta = 5. */ void phase_2(char *input) { int ii; int numbers[6]; read_six_numbers(input, numbers); for (ii = 1; ii < 6; ii++) { if (numbers[ii] != numbers[ii-1] + 5) explode_bomb(); } } – 22 – ICS
The Beauty of the Bomb For the Student n n Get a deep understanding of machine code in the context of a fun game Learn about machine code in the context they will encounter in their professional lives l Working with compiler-generated code n Learn concepts and tools of debugging l Forward vs backward debugging l Students must learn to use a debugger to defuse a bomb For the Instructor n n n – 23 – Self-grading Scales to different ability levels Easy to generate variants and to port to other machines ICS
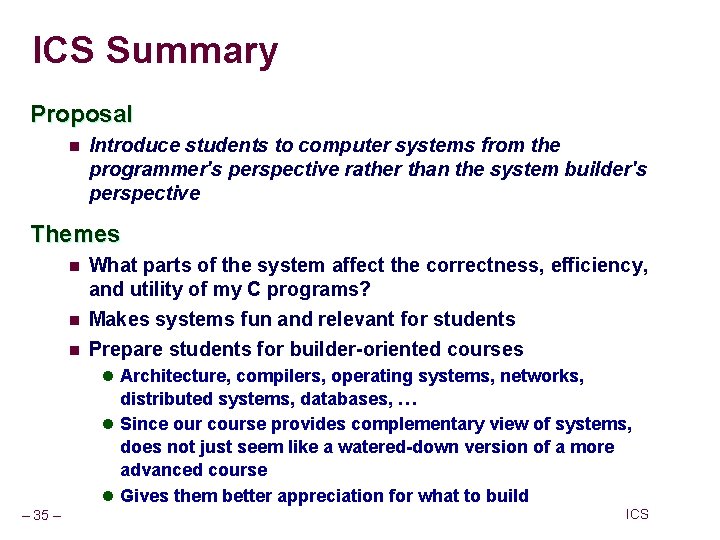
ICS Summary Proposal n Introduce students to computer systems from the programmer's perspective rather than the system builder's perspective Themes n What parts of the system affect the correctness, efficiency, and utility of my C programs? Makes systems fun and relevant for students n Prepare students for builder-oriented courses n l Architecture, compilers, operating systems, networks, distributed systems, databases, … l Since our course provides complementary view of systems, does not just seem like a watered-down version of a more advanced course l Gives them better appreciation for what to build – 35 – ICS
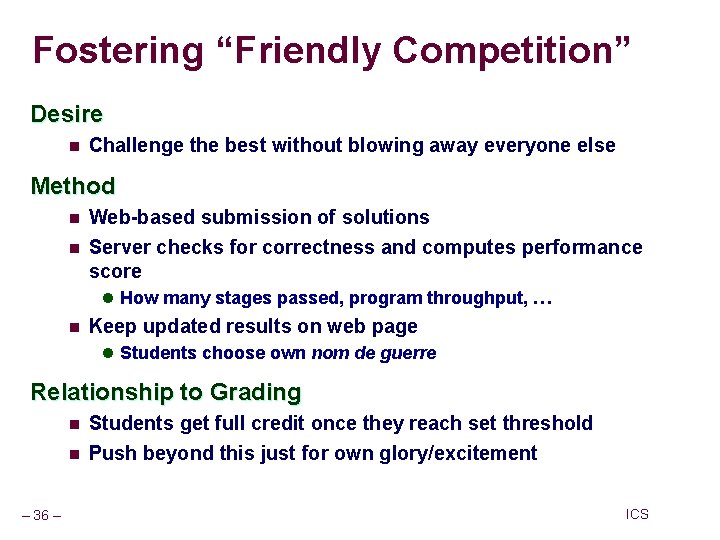
Fostering “Friendly Competition” Desire n Challenge the best without blowing away everyone else Method n n Web-based submission of solutions Server checks for correctness and computes performance score l How many stages passed, program throughput, … n Keep updated results on web page l Students choose own nom de guerre Relationship to Grading n n – 36 – Students get full credit once they reach set threshold Push beyond this just for own glory/excitement ICS
Shameless Plug n http: //csapp. cs. cmu. edu n Published August, 2002 – 37 – ICS
CS: APP Vital stats: n 13 chapters n 154 practice problems (solutions in book), 132 homework problems (solutions in IM) n 410 figures, 249 line drawings 368 C code example, 88 machine code examples n Turn-key course provided with book: n n n – 38 – Electronic versions of all code examples. Powerpoint, EPS, and PDF versions of each line drawing Password-protected Instructors Page, with Instructor’s Manual, Lab Infrastructure, Powerpoint lecture notes, and Exam problems. ICS
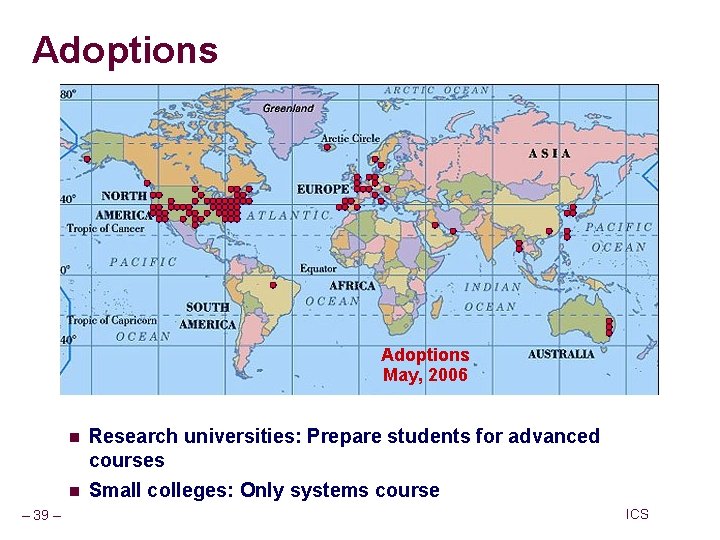
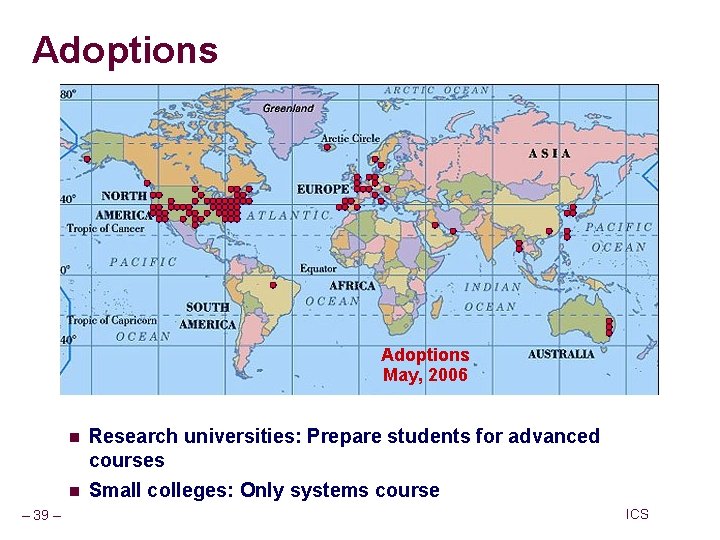
Adoptions May, 2006 – 39 – n Research universities: Prepare students for advanced courses n Small colleges: Only systems course ICS
Translations – 40 – ICS
Coverage Material Used by ICS at CMU n Pulls together material previously covered by multiple textbooks, system programming references, and man pages Greater Depth on Some Topics n n n IA 32 floating point Dynamic linking Thread programming Additional Topic n n – 41 – Computer Architecture Added to cover all topics in “Computer Organization” course ICS
The Evolving CS & Engineering Curriculum Programming Lies at the Heart of Most Modern Systems n Computer systems n Embedded devices: Cell phones, automobile controls, … Electronics: DSPs, programmable controllers n Programmers Have to Understand Their Machines and Their Limitations n n Correctness: computer arithmetic, storage allocation Efficiency: memory & CPU performance Knowing How to Build Systems Is Not the Way to Learn How to Program Them n n – 45 – It’s wasteful to teach every computer scientist how to design a microprocessor Knowledge of how to build does not transfer to knowledge of how to use ICS