Interpolationbased hiding scheme using the modulus function and
Interpolation-based hiding scheme using the modulus function and reencoding strategy u. Source : Signal Processing, vol. 142, pp. 244 -259, January 2018 u. Authors : Tzu-Chuen Lu u. Speaker : Chia-Shuo Shih u. Date : 2018/09/20 1
Outline �Related work �Proposed method �Experimental results �Conclusions 2
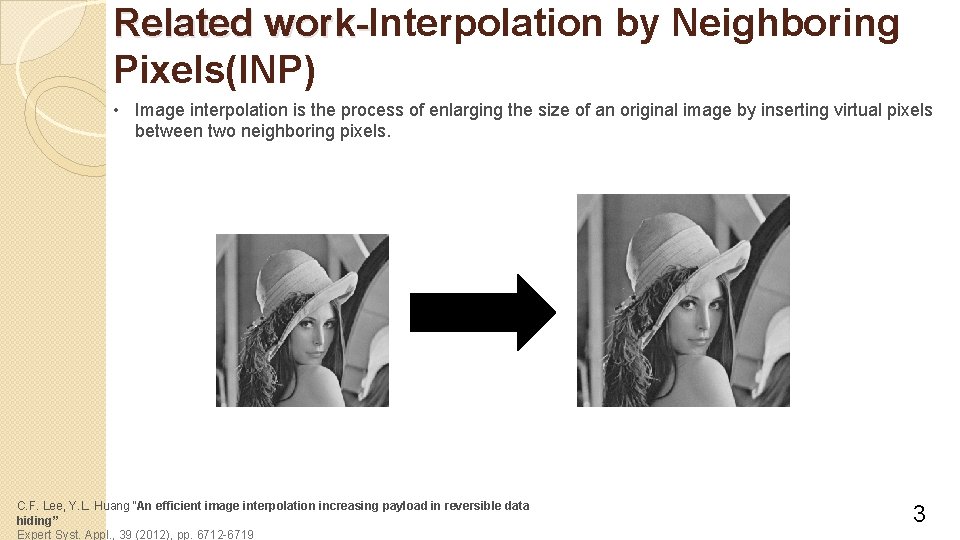
Related work-Interpolation by Neighboring work. Pixels(INP) • Image interpolation is the process of enlarging the size of an original image by inserting virtual pixels between two neighboring pixels. C. F. Lee, Y. L. Huang “An efficient image interpolation increasing payload in reversible data hiding” Expert Syst. Appl. , 39 (2012), pp. 6712 -6719 3
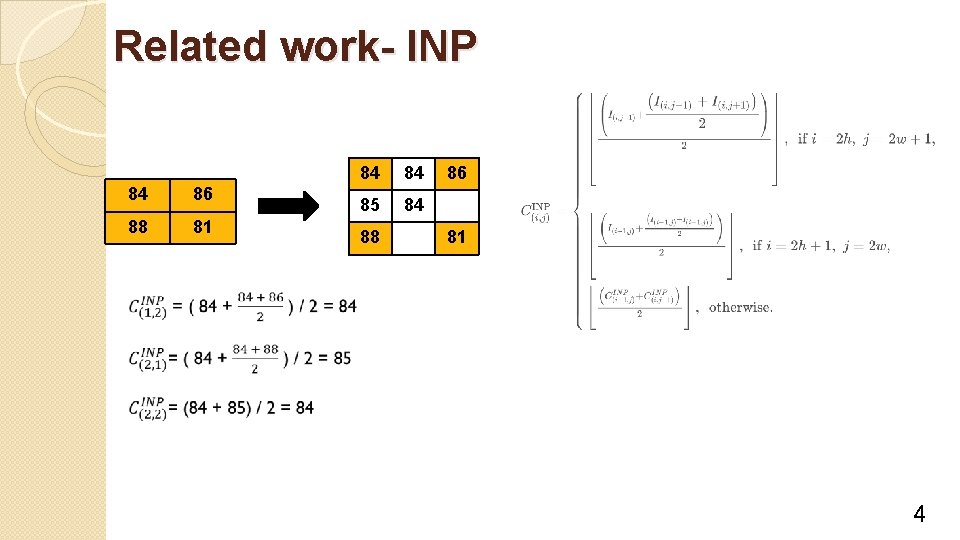
Related work- INP 84 86 88 81 84 84 85 84 88 86 81 4
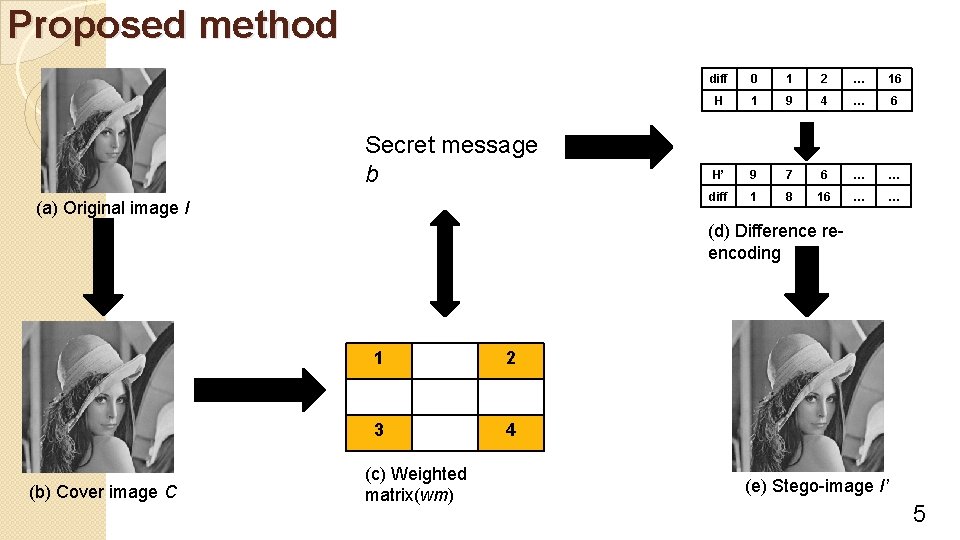
Proposed method Secret message b (a) Original image I diff 0 1 2 … 16 H 1 9 4 … 6 H’ 9 7 6 … … diff 1 8 16 … … (d) Difference reencoding (b) Cover image C 1 2 3 4 (c) Weighted matrix(wm) (e) Stego-image I’ 5
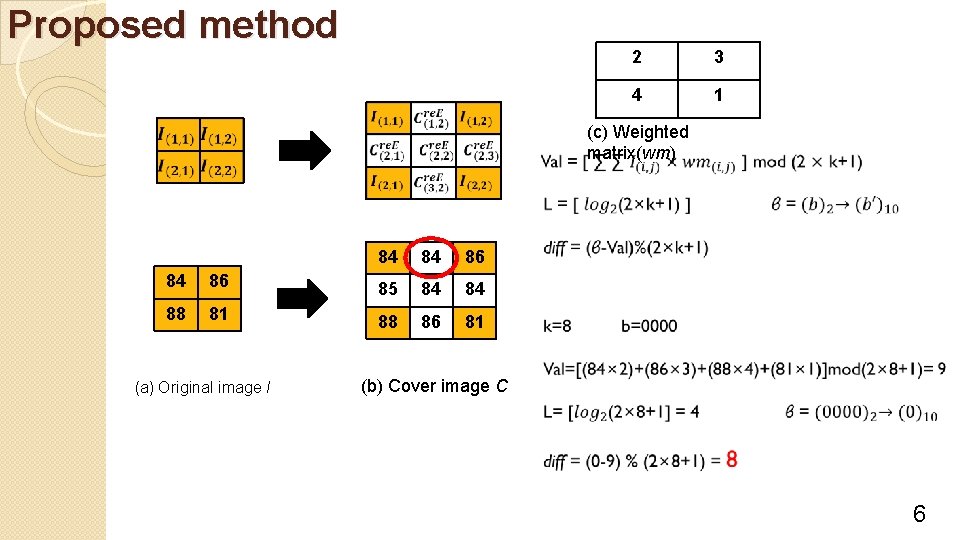
Proposed method 2 3 4 1 (c) Weighted matrix(wm) 84 84 86 85 84 84 88 81 88 86 81 (a) Original image I (b) Cover image C 6
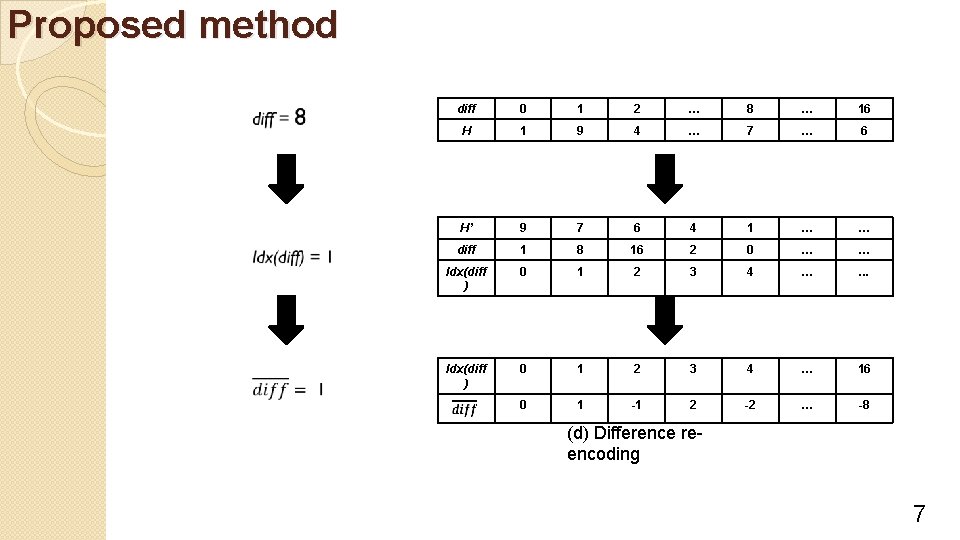
Proposed method diff 0 1 2 … 8 … 16 H 1 9 4 … 7 … 6 H’ 9 7 6 4 1 … … diff 1 8 16 2 0 … … Idx(diff ) 0 1 2 3 4 … . . . Idx(diff ) 0 1 2 3 4 … 16 0 1 -1 2 -2 … -8 (d) Difference reencoding 7
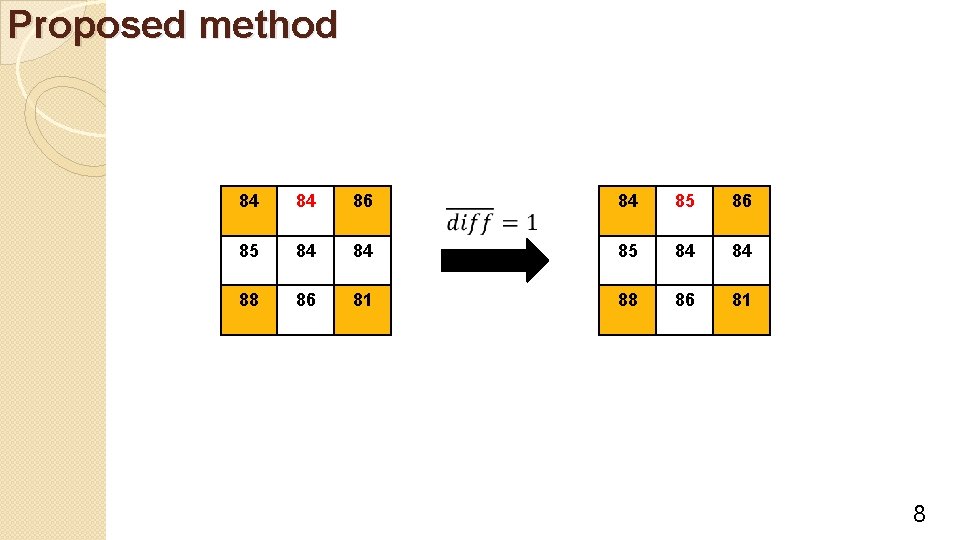
Proposed method 84 84 86 84 85 86 85 84 84 88 86 81 8
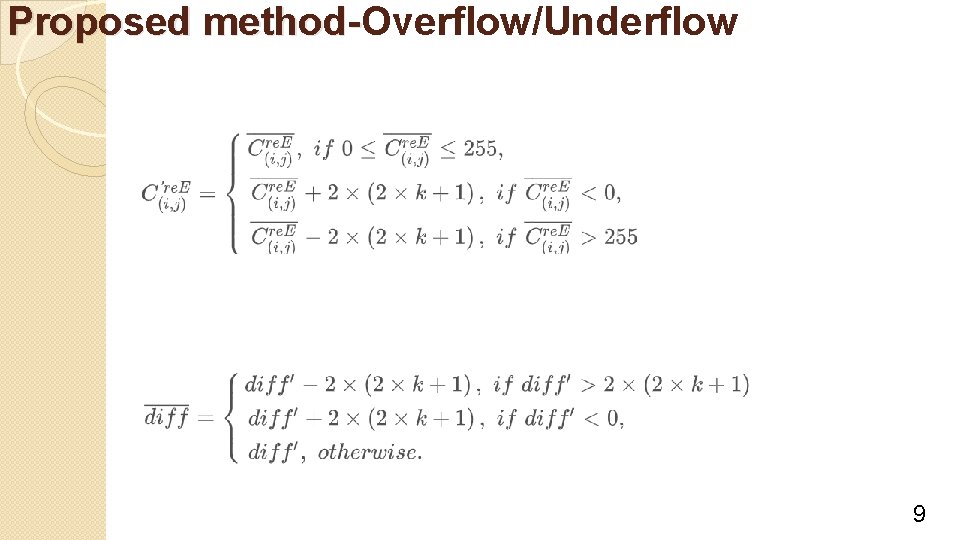
Proposed method-Overflow/Underflow method- 9
![Experimental results Method NMI[5] INP[6] CRS[9] Lu[12] Original re. Encode File Name PSNR bpp Experimental results Method NMI[5] INP[6] CRS[9] Lu[12] Original re. Encode File Name PSNR bpp](http://slidetodoc.com/presentation_image_h2/d9188a36aa15300a412157948e402fea/image-10.jpg)
Experimental results Method NMI[5] INP[6] CRS[9] Lu[12] Original re. Encode File Name PSNR bpp PSNR bpp Airplane 33. 05 1. 05 32. 64 1. 19 31. 54 1. 51 30. 74 2. 83 30. 48 3. 00 36. 03 3. 00 Tiffany 37. 77 0. 93 37. 15 1. 09 36. 00 1. 37 30. 93 2. 83 30. 75 3. 00 35. 02 3. 00 Lake 32. 48 1. 10 31. 76 1. 25 30. 75 1. 60 30. 74 2. 83 30. 48 3. 00 36. 03 3. 00 Lena 34. 89 1. 10 34. 32 1. 25 33. 19 1. 57 30. 74 2. 83 30. 48 3. 00 36. 03 3. 00 1. 10 31. 65 1. 25 31. 36 1. 60 30. 74 2. 83 30. 48 3. 00 35. 99 3. 00 34. 27 1. 10 33. 72 1. 25 33. 39 1. 53 30. 31 2. 83 30. 43 3. 00 34. 85 3. 00 Mandrill 32. 40 Pepper [5]K. H. Jung, K. Y. Yoo ”Data hiding method using image interpolation” Comput. Stand. Interfaces, 31 (2009), pp. 465 -470 [6]C. F. Lee, Y. L. Huang “An efficient image interpolation increasing payload in reversible data hiding” Expert Syst. Appl. , 39 (2012), pp. 6712 -6719 [9]M. W. Tang, J. Hu, W. Song “A high-capacity image steganography using multi-layer embedding” Optik, 125 (2014), pp. 3972 -3976 [12]T. C. Lu ”Adaptive (k, F 1) interpolation-based hiding scheme using center folding strategy” Multimedia Tools Appl. , 76 (2017), pp. 1827 -1855 10
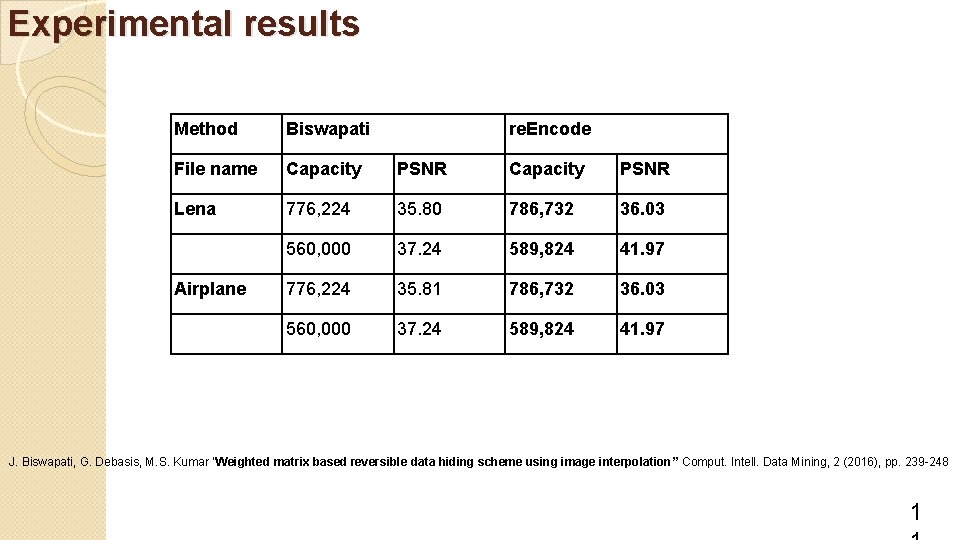
Experimental results Method Biswapati File name Capacity PSNR Lena 776, 224 35. 80 786, 732 36. 03 560, 000 37. 24 589, 824 41. 97 776, 224 35. 81 786, 732 36. 03 560, 000 37. 24 589, 824 41. 97 Airplane re. Encode J. Biswapati, G. Debasis, M. S. Kumar ”Weighted matrix based reversible data hiding scheme using image interpolation” Comput. Intell. Data Mining, 2 (2016), pp. 239 -248 1
Conclusions �This paper Improves Biswapati et al. ’s scheme �The mapping code is half of the re-encoded code. 1
-END- 1
- Slides: 13