InternetMarks Visual Marks for Cyber World Hitachi Ltd
Internet/Marks - Visual Marks for Cyber World - Hitachi, Ltd. 1999. 4. 15, 16 All rights reserved. Copyright (c) 1
Basic Concept of Cyber-World Marks • Marks (e. g. , traffic signals) are extremely useful in real world. • Convey information briefly and clearly • Familiar to non-professionals • Marks (e. g. , blue-ribbon marks) are useful BUT insecure in cyber world. • Easy to forge and tamper • Easy to copy-paste on unauthorized data • Useful and Secure marks are desired for cyber world. All rights reserved. Copyright (c) 2
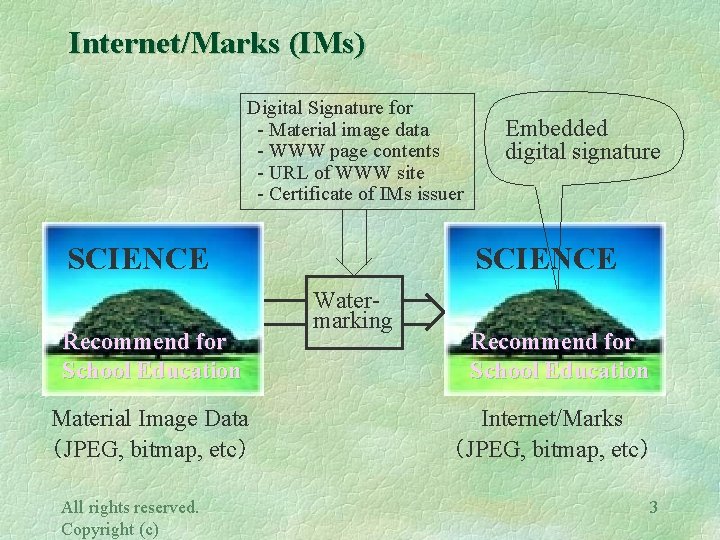
Internet/Marks (IMs) Digital Signature for - Material image data - WWW page contents - URL of WWW site - Certificate of IMs issuer SCIENCE Recommend for School Education Material Image Data (JPEG, bitmap, etc) All rights reserved. Copyright (c) Embedded digital signature SCIENCE Watermarking Recommend for School Education Internet/Marks (JPEG, bitmap, etc) 3

Structure of Internet/Marks Secret key Data on which IMs is pasted Paste All rights reserved. Copyright (c) Hash IMs Digital signature detects - Forge and tamper of IMs - IMs copied on unauthorized data - Forge and tamper of data Embed by Digital Watermarking 4
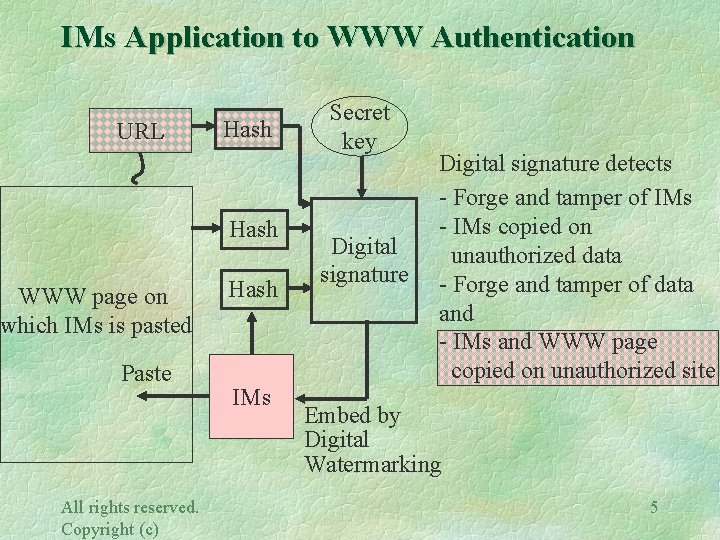
IMs Application to WWW Authentication URL Hash WWW page on which IMs is pasted Paste All rights reserved. Copyright (c) Hash IMs Secret key Digital signature detects - Forge and tamper of IMs - IMs copied on unauthorized data - Forge and tamper of data and - IMs and WWW page copied on unauthorized site Embed by Digital Watermarking 5
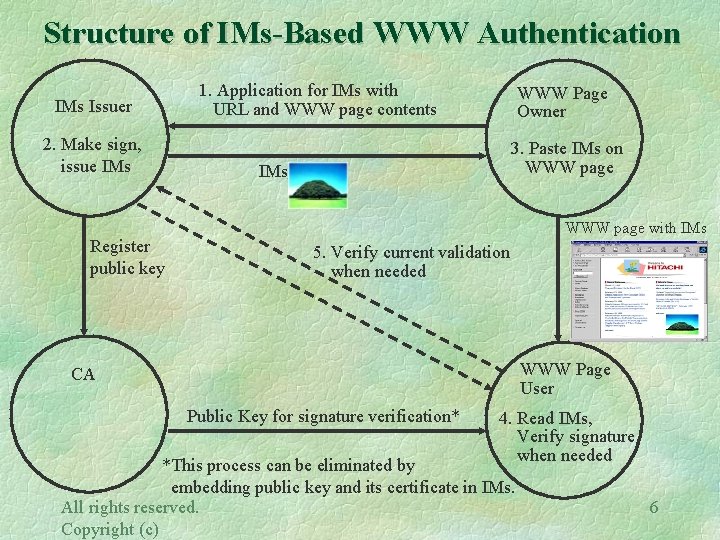
Structure of IMs-Based WWW Authentication IMs Issuer 2. Make sign, issue IMs Register public key 1. Application for IMs with URL and WWW page contents WWW Page Owner 3. Paste IMs on WWW page IMs WWW page with IMs 5. Verify current validation when needed WWW Page User CA Public Key for signature verification* 4. Read IMs, Verify signature when needed *This process can be eliminated by embedding public key and its certificate in IMs. All rights reserved. Copyright (c) 6
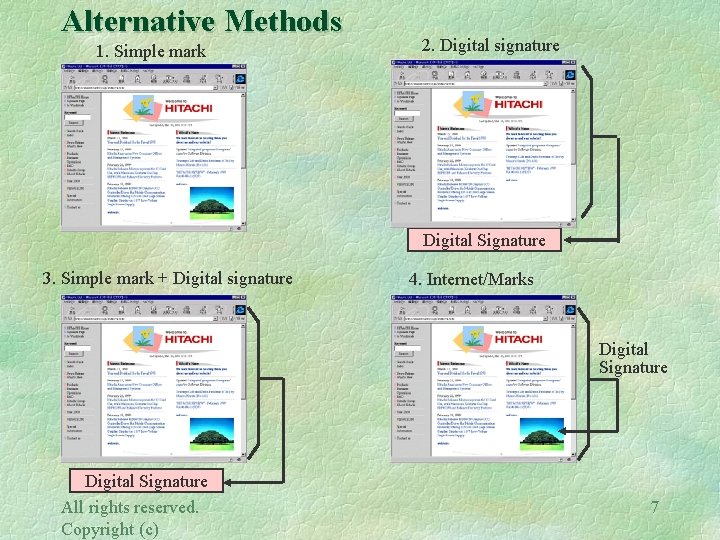
Alternative Methods 1. Simple mark 2. Digital signature Digital Signature 3. Simple mark + Digital signature 4. Internet/Marks Digital Signature All rights reserved. Copyright (c) 7
Comparison with Alternative Methods - Performance Summary - All rights reserved. Copyright (c) 8
Comparison with Alternative Methods - Operations - All rights reserved. Copyright (c) 9
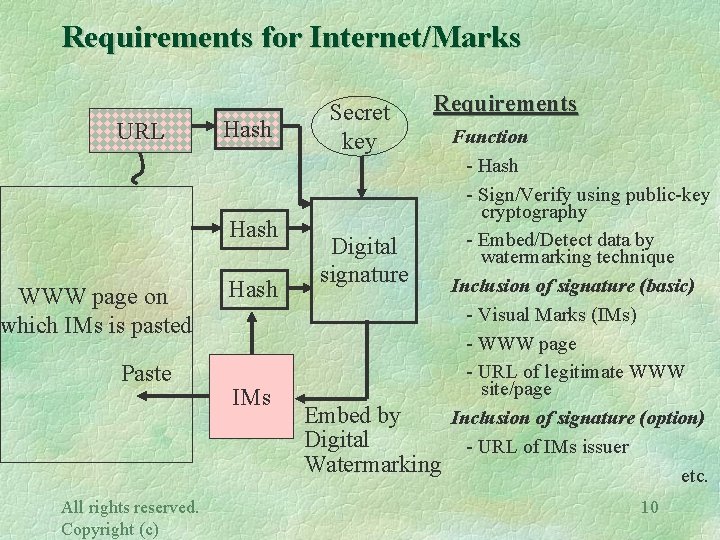
Requirements for Internet/Marks URL Hash WWW page on which IMs is pasted Paste All rights reserved. Copyright (c) Hash IMs Secret key Requirements Digital signature Embed by Digital Watermarking Function - Hash - Sign/Verify using public-key cryptography - Embed/Detect data by watermarking technique Inclusion of signature (basic) - Visual Marks (IMs) - WWW page - URL of legitimate WWW site/page Inclusion of signature (option) - URL of IMs issuer etc. 10
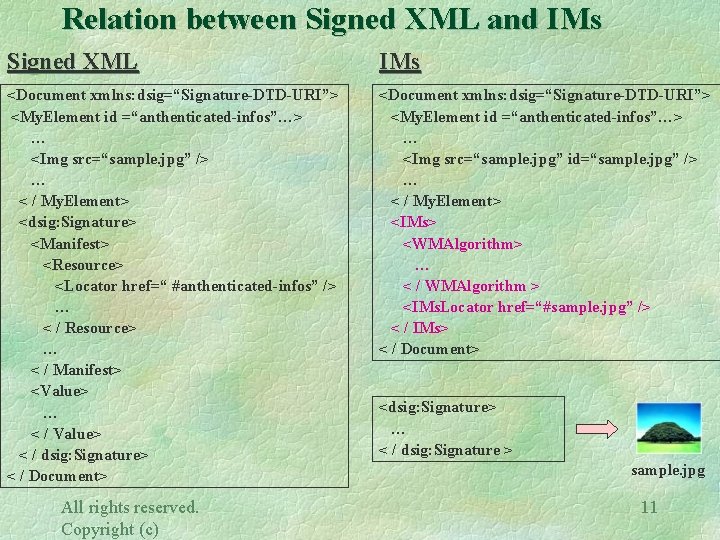
Relation between Signed XML and IMs Signed XML IMs <Document xmlns: dsig=“Signature-DTD-URI”> <My. Element id =“anthenticated-infos”…> … <Img src=“sample. jpg” /> … < / My. Element> <dsig: Signature> <Manifest> <Resource> <Locator href=“ #anthenticated-infos” /> … < / Resource> … < / Manifest> <Value> … < / Value> < / dsig: Signature> < / Document> <Document xmlns: dsig=“Signature-DTD-URI”> <My. Element id =“anthenticated-infos”…> … <Img src=“sample. jpg” id=“sample. jpg” /> … < / My. Element> <IMs> <WMAlgorithm> … < / WMAlgorithm > <IMs. Locator href=“#sample. jpg” /> < / IMs> < / Document> All rights reserved. Copyright (c) <dsig: Signature> … < / dsig: Signature > sample. jpg 11
- Slides: 11