Internet Vulnerabilities Criminal Activity Cyber Terrorism and Cyber
Internet Vulnerabilities & Criminal Activity Cyber Terrorism and Cyber Warfare November 14, 2011
Terrorism - FBI “The unlawful use of force and violence against persons or property to intimidate or coerce a government, the civilian population, or any segment thereof, in furtherance of political or social objectives. ”
Terrorism - DOD “The unlawful use of, or threatened use, of force or violence against individuals or property, to coerce and intimidate governments or societies, often to achieve political, religious or ideological objectives”
Terrorism - DOS “Premeditated, politically motivated violence perpetrated against noncombatant targets by sub national groups or clandestine agents”
FBI - Terrorism Descriptions § Domestic or Foreign § “Depending on the origin, base, and objectives of the terrorist organization. ” § Terrorist Activities § Incident § “A violent act or an act dangerous to human life, in violation of the criminal laws of the United States, or of any state, to intimidate or coerce a government, the civilian population, or any segment thereof, in furtherance of political or social objectives. ” § Prevention § “A documented instance in which a violent act by a known or suspected terrorist group or individual with the means and a proven propensity for violence is successfully interdicted through investigative activity. ”
More on Terrorism § § § § Political in nature Smaller weaker group vs. larger group No legitimate means of protest Violence against civilians Symbolic targets Designed to provoke response Aimed at larger audience
What Makes a Terrorist? § A disaffected individual § An enabling group § A legitimizing ideology
Terrorist Goals § Leadership § Followers § Short-term goals § Long-term goals § Political change § Revenge § Renown § Reaction
Terrorism Matrix § People (or groups) § Locations (of perpetrators, facilitators, victims) § Methods/modes of action § Tools § Targets § Affiliations § Motivations
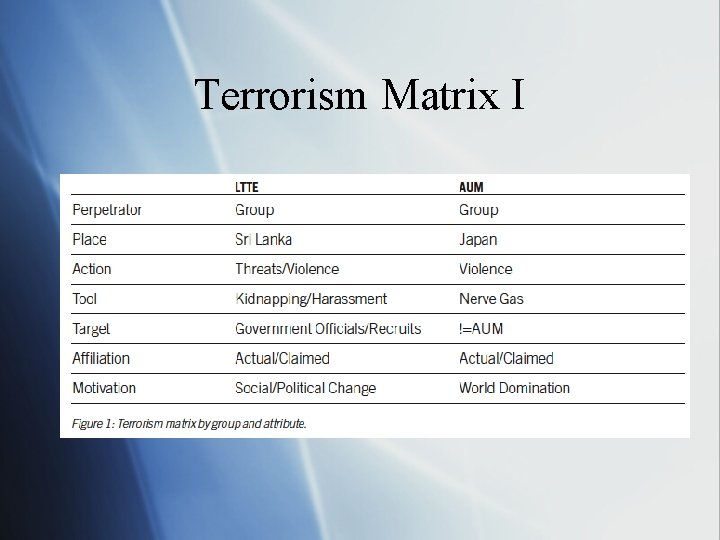
Terrorism Matrix I
Cyber Terrorism "The premeditated, politically motivated attack against information, computer systems, computer programs, and data which result in violence against noncombatant targets by sub-national groups or clandestine agents” FBI
Is Cyber Terrorism Really Terrorism?
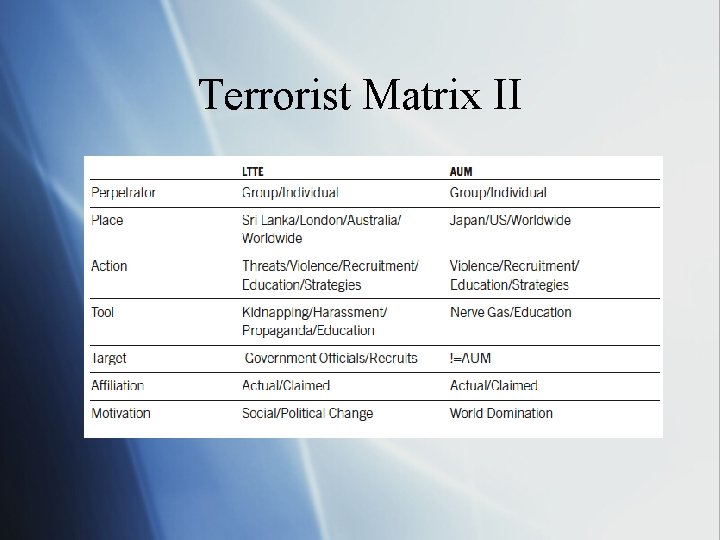
Terrorist Matrix II
Worst Cyber Terrorism Attack to Date September 11, 2001
Cyber Terrorism - Dynamics § Three types of attacks § Physical § Conventional Weapons § Syntactic § Malware § Semantic § More subtle approach § Errors & unpredictable results § Attack user’s confidence in the system
Cyber Terrorism - Steps § Reconnaissance § Gain detailed information about target § Social engineering, dumpster diving § Scanning § Determine targets computer software & network organization § Gaining access § Take over the target § Stolen passwords, network vulnerabilities
Cyber Terrorism - Steps cont. § Maintaining access § Allow further access § Rootkits and backdoors § Covering tracks § Maintain control § Gather further intelligence
Cyber Terrorism - Potential Effects § Targets § § § § Water supplies Electrical power supplies Emergency services Telecommunications systems Transportation systems Banking & financial systems Government
Countering Cyber Terrorism § Raise security levels in the private sectors § Communication & coordination systems in the private sector § Communication & coordination systems in government § Establish emergency response plans § Promote research & development § Add & revise legislation § Promote international cooperation
How Terrorist Use the Internet § Propaganda § Recruitment § Information storage § Communications § Funding
Terrorist Web Sites
Google Maps
Cyberwarfare “The use of computers and the Internet in conducting warfare in cyberspace”
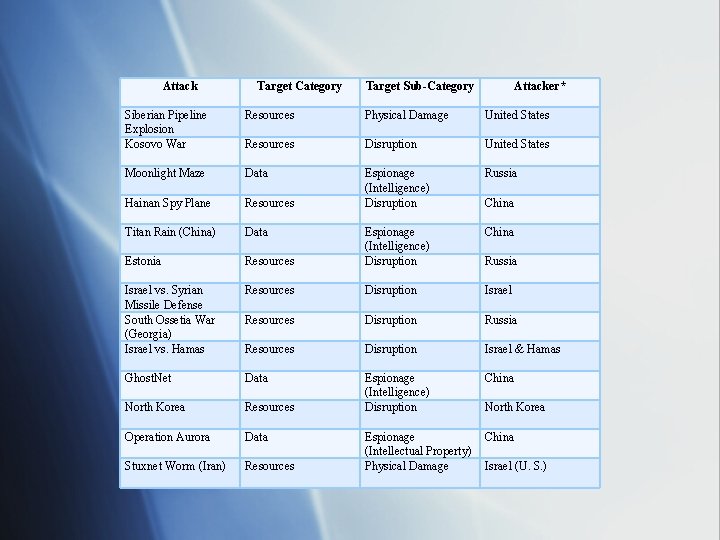
Attack Target Category Target Sub-Category Attacker* Siberian Pipeline Explosion Kosovo War Resources Physical Damage United States Resources Disruption United States Moonlight Maze Data Russia Hainan Spy Plane Resources Espionage (Intelligence) Disruption Titan Rain (China) Data China Estonia Resources Espionage (Intelligence) Disruption Israel vs. Syrian Missile Defense South Ossetia War (Georgia) Israel vs. Hamas Resources Disruption Israel Resources Disruption Russia Resources Disruption Israel & Hamas Ghost. Net Data China North Korea Resources Espionage (Intelligence) Disruption Operation Aurora Data China Stuxnet Worm (Iran) Resources Espionage (Intellectual Property) Physical Damage China Russia North Korea Israel (U. S. )
Cyberwarfare Questions § § § § Will we know who did it? Can retaliators hold assets at risk? Can they do so repeatedly? Can cyberattacks disarm cyberattackers? Will third parties stay out of the way? Might retaliation send the wrong message? Can states set thresholds for response? Can escalation be avoided?
Most likely use of cyber terrorism, and cyber warfare In tandem with a physical attack.
- Slides: 26