Internet Security Successes Its Hard but its not
Internet Security Successes: It’s Hard, but it’s not Impossible Bill Cheswick Lumeta Corp. 60 slides
Or… There’s a World of Hurt, but I don’t have to Share Your Pain 60 slides
Overview • Introduction/overview • Quick case studies of success • A quick review of what works • What my dad really needs • Predications/advice Vanguard, Feb 2004 3 of 60
Overview 60 slides
Good enough security is good enough • There is no such thing as perfect security • In security vs. convenience, “convenience” may mean not losing a pair of large buildings – Even the policies on the highest security networks are under review Vanguard, Feb 2004 5 of 60
In lots of places, the Internet security appears good enough • Many business have engineered workable solutions: Fedex, Amazon, on-line banking • Insurance companies are starting to offer hacking insurance – Still extremely expensive – (Worried about a hurricane Andrew on the Internet) Vanguard, Feb 2004 6 of 60
Some successes • My dad’s Win XP machine • My home networks • SDSC • Many Lumeta clients • Intellink Vanguard, Feb 2004 7 of 60
You can engineer reliable systems out of unreliable parts • Early calculator at Bell Labs – Checked for invalid codes and retried the computation • Redundancy and layers – Defense in depth – Somewhat simple tools are available Vanguard, Feb 2004 8 of 60
Safe communications on an intranet • Secure servers • Secure communications • Secure clients Vanguard, Feb 2004 9 of 60
Secure servers • The pros run the servers • They can engineer what they want with the tools they want – They choose the operating systems, network configurations, etc. • There are many successful examples – Fedex, Amazon, microsoft. com, whitehouse. gov • There are many unsuccessful examples Vanguard, Feb 2004 10 of 60
Secure communications • We are in much better shape than during the crypto wars of the mid 90 s • In June 2003 NSA announced that AES was good enough for type 1 encryption – When properly implemented, of course • IP/sec, SSL, and even SSH protocol 2 seem to be holding up – (formal methods for analyzing cryptographic protocols sure would be nice. ) Vanguard, Feb 2004 11 of 60
Clients • Thin clients (called “terminals”) are a rarity – I miss my Hazeltine 1200 (sort of) • Most clients are Windows boxes – Way too much functionality • One care engineer a thin client from Unix and Linux systems • They are not thin enough: jailing browsers Vanguard, Feb 2004 12 of 60
Applications • A virus will transport nicely from a secure client to a secure server over an encrypted link • Applications should be as dumb as possible, but no dumber – Email should never execute external programs – Web servers should execute code from trustable sources • Windows update, virus update • Applications ought to be sandboxed Vanguard, Feb 2004 13 of 60
Case Studies 60 slides
Case study: My Dad’s computer • Windows XP, plenty of horsepower, two screens • Applications: – Email (Outlook) – “Bridge: ” a fancy stock market monitoring system – AIM • Cable access, dynamic IP address, no NAT, no firewall, outdated virus software, no spyware checker Vanguard, Feb 2004 15 of 60
This computer was a software toxic waste dump • It was burning a quart of software every 300 miles • The popups seemed darned distracting to me • But he thought it was fine – Got his work done – Didn’t want a system administrator to break his user interface somehow • We’ll get back to this later Vanguard, Feb 2004 16 of 60
Case Study: My home network • Firewall free since the mid-90 s – Internet skinny-dipping • Targeted attacks as well as random probes • Three security levels – Top security backup and support machines and clients – Public servers, hardened, with sandboxed server software – The kid’s Windows hosts, untrusted Vanguard, Feb 2004 17 of 60
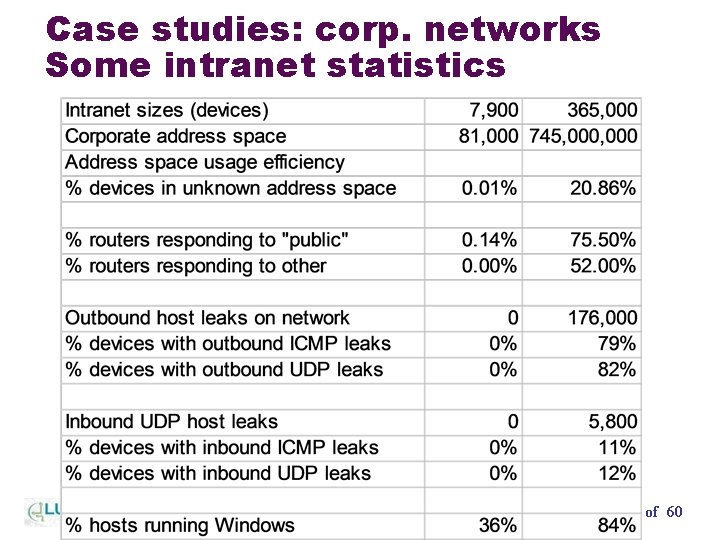
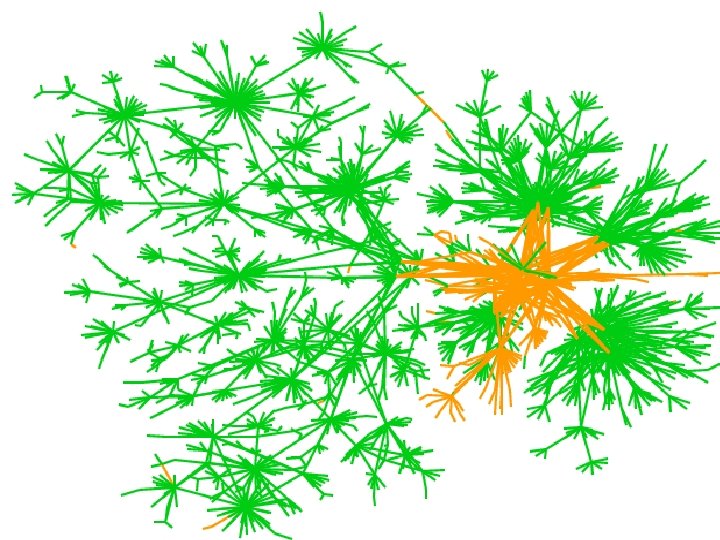
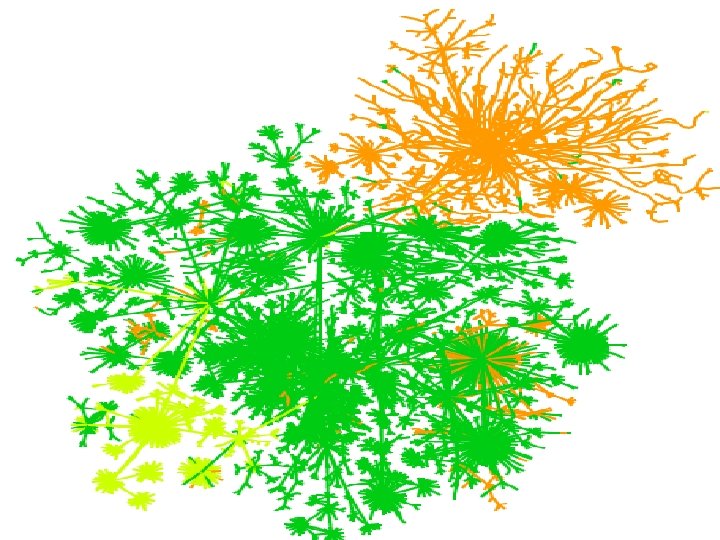
Case studies: corp. networks Some intranet statistics Vanguard, Feb 2004 18 of 60
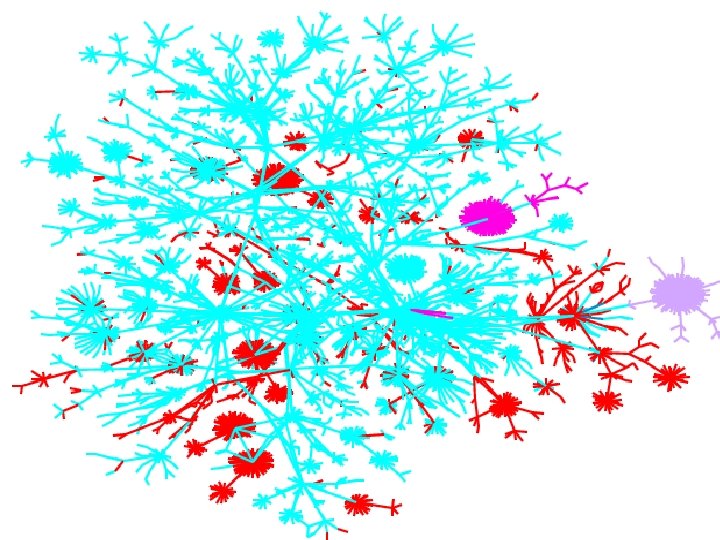
Vanguard, Feb 2004 19 of 60
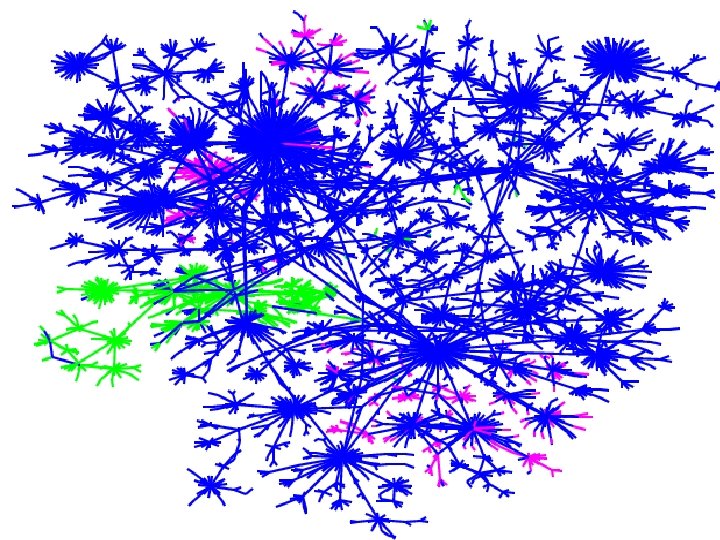
Vanguard, Feb 2004 20 of 60
Vanguard, Feb 2004 21 of 60

Vanguard, Feb 2004 22 of 60
Vanguard, Feb 2004 23 of 60
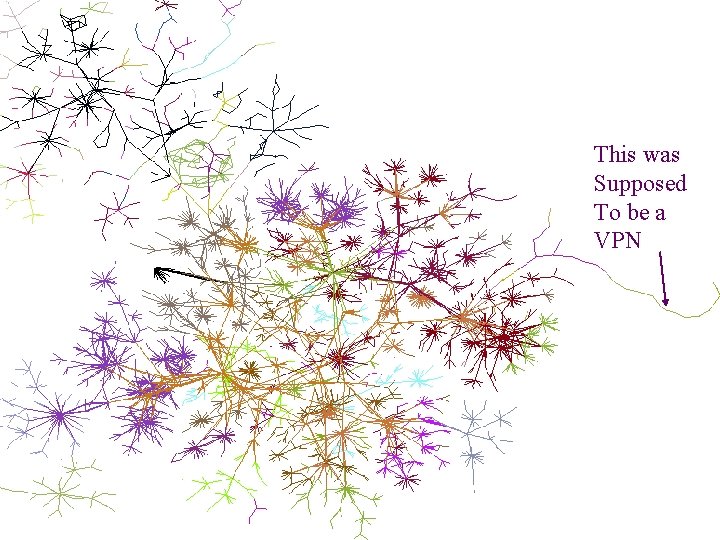
This was Supposed To be a VPN Vanguard, Feb 2004 24 of 60
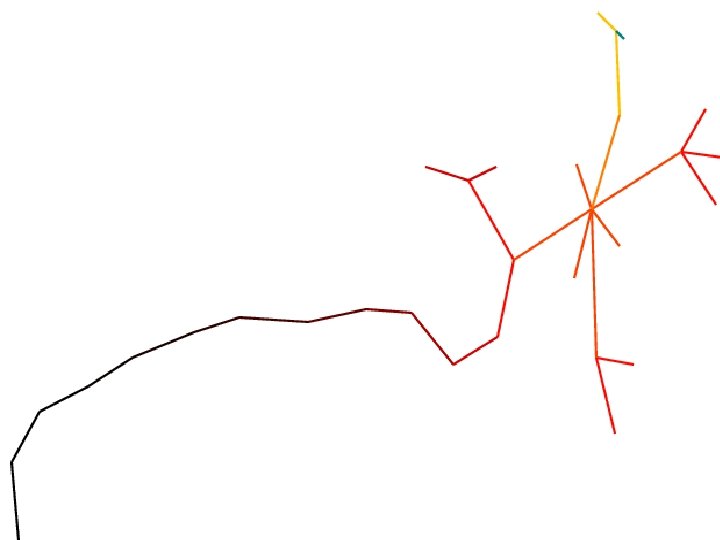
Vanguard, Feb 2004 25 of 60
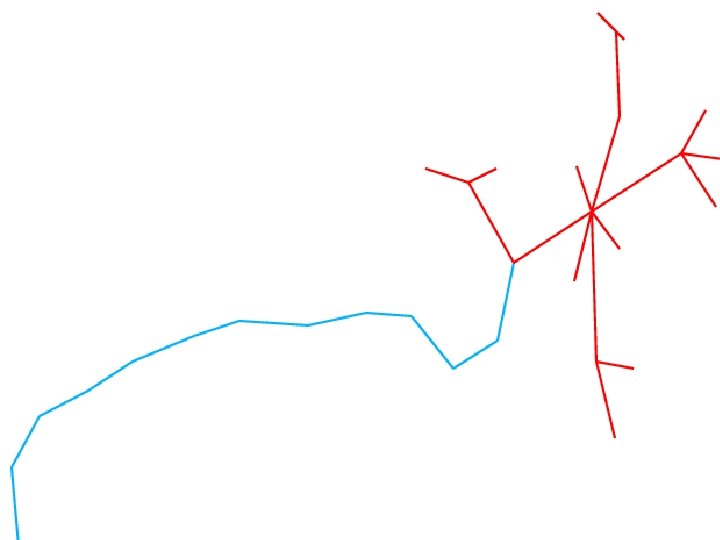
Vanguard, Feb 2004 26 of 60
Case study: SDSC • Educational and research environment • Typically notoriously open environments Vanguard, Feb 2004 27 of 60
SDSC: Research institutions can get it right • 6, 000 users, 300 on site • 5 petabytes of storage, several hundred terabytes of disks • 10 Gb Ethernet, lots of OC-192 connections Vanguard, Feb 2004 28 of 60
Risk analysis • Need to protect integrity and confidentiality of data • Protect resources, including storage, bandwidth, CPU cycles • Protect reputation for security • Threats come from external hackers, clueless users, and careless system administrators Vanguard, Feb 2004 29 of 60
Approach • Trusted networks may contain only reference systems • • Only “reference” systems are trusted Data is stored on file servers File servers are located on trusted networks No plaintext passwords used: ssh and Kerberos employed • Passwords are checked with cracklib before acceptance • Root password is not given out on reference systems. Sudo gives specific permissions Vanguard, Feb 2004 30 of 60
Non-compliant systems • Are installed in the “outback”, a dirty untrusted network • Outback users, and their supervisors, sign agreement that they are responsible for the hosts • Compromised outback hosts may be seized forensic analysis and possible evidence for criminal cases Vanguard, Feb 2004 31 of 60
Reference systems • Available for Linux, Solaris, Irix, Mac. OS, several Windows variants • Installed, patched, and local mods installed to maximize security • Contains software to permit updates from the central reference site upon reboot • Time-synchronized for proper logging, forensics • Centralized logging keeps track of things • Various network wrappers and routing limitations to limit network access Vanguard, Feb 2004 32 of 60
Results • No successful intrusions in four years Vanguard, Feb 2004 33 of 60
Case study: surmises about Intellink • Read about this in Banford’s book, “Body of Secrets” • Uses Internet technology to make numerous highly classified sources available to authorized personnel • The following is mostly personal speculation • It is a terrific thought experiment for an Internet security person. Vanguard, Feb 2004 34 of 60
Case study: surmises about Intellink • Vetted client software – OS; browser; underlying libraries and services link ASN. 1, X. 509, SSL, etc. • Careful monitoring of the network usage • Big mallet to dissuade misuse. – Disconnection, firing, jail time • Hardware encryption devices to enforce enclave access Vanguard, Feb 2004 35 of 60
What works 60 slides
What works • Perimeter defenses work, if you know where your perimeter is and watch it Vanguard, Feb 2004 37 of 60
What works: layered defenses Vanguard, Feb 2004 39 of 60
What works: Enclaves • “Security has a lot to do with numbers” • I think 40 computers is about the limit for me Vanguard, Feb 2004 41 of 60
What works: Virtual machines • IBM’s virus test farm: a sea of Linux hosts running target operating system inside vmware. Disks reinitialized instantly using logging file system. • Terminal for secret networks – Virtual machines for different security levels Vanguard, Feb 2004 42 of 60
What works: Default to safety • Don’t expect users to understand make the right security moves • Make people work to reduce their security: – “screw me” command Vanguard, Feb 2004 43 of 60
What works • Don’t let strangers run programs on your computer • A “stranger” is anyone who isn’t your system administrator and the company he trusts • The mouse is used for cut and paste in my mailer. Period. – Hence, no virus execution is possible Vanguard, Feb 2004 44 of 60
What works: simplicity • ASCII (or Unicode) mail • Twenty-year old email • Telephone SMS version 1. 0 Vanguard, Feb 2004 45 of 60
What works • Small enclaves Vanguard, Feb 2004 46 of 60
What my dad (and most of you) really needs 60 slides
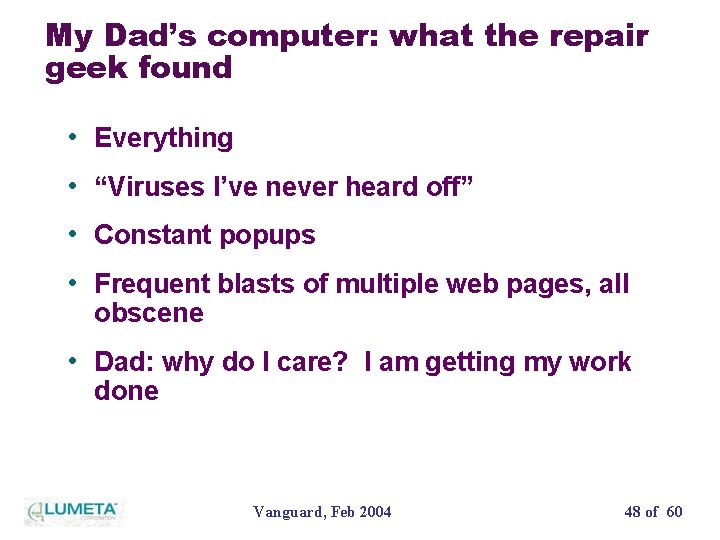
My Dad’s computer: what the repair geek found • Everything • “Viruses I’ve never heard off” • Constant popups • Frequent blasts of multiple web pages, all obscene • Dad: why do I care? I am getting my work done Vanguard, Feb 2004 48 of 60
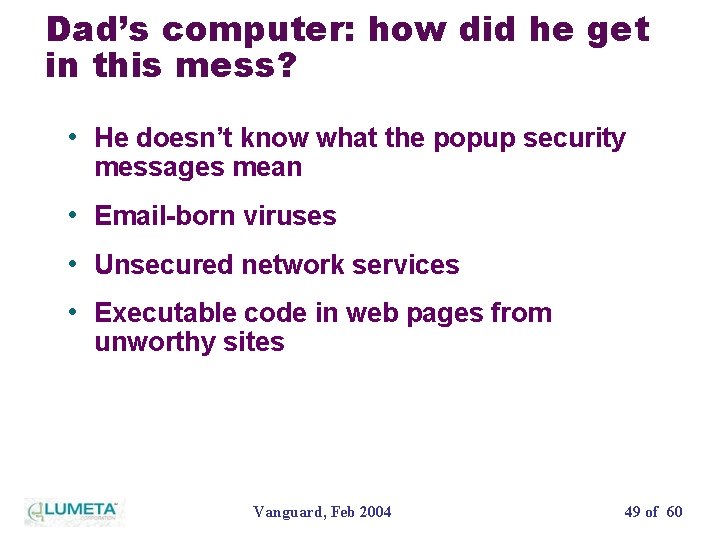
Dad’s computer: how did he get in this mess? • He doesn’t know what the popup security messages mean • Email-born viruses • Unsecured network services • Executable code in web pages from unworthy sites Vanguard, Feb 2004 49 of 60
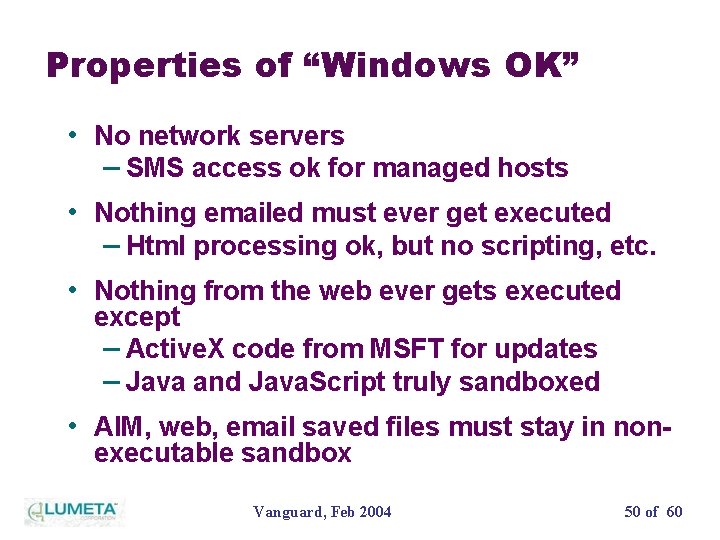
Properties of “Windows OK” • No network servers – SMS access ok for managed hosts • Nothing emailed must ever get executed – Html processing ok, but no scripting, etc. • Nothing from the web ever gets executed except – Active. X code from MSFT for updates – Java and Java. Script truly sandboxed • AIM, web, email saved files must stay in nonexecutable sandbox Vanguard, Feb 2004 50 of 60
Predictions 60 slides
More pain: virus detection appears doomed to me • Ultimately they do try to solve the halting problem • Virus writers are getting very good • Virus detectors have to resort to simulation: fingerprints aren’t good enough • Simulations are taking longer • “Best block is not be there” – Safe fail Vanguard, Feb 2004 52 of 60
Microsoft’s Augean Stables Vanguard, Feb 2004 53 of 60
Microsoft really means it about improving their security • Their security commitment appears to be real • It is a huge job • Opposing forces are unclear to me • It’s been a long time coming, and frustrating Vanguard, Feb 2004 54 of 60
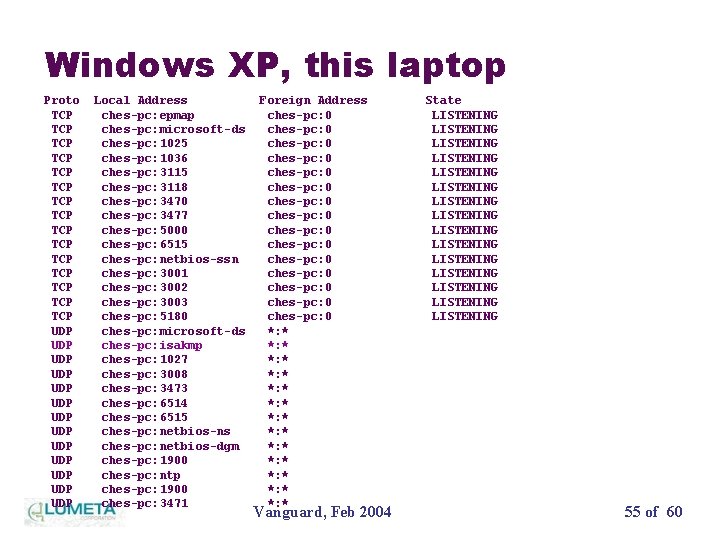
Windows XP, this laptop Proto TCP TCP TCP TCP UDP UDP UDP UDP Local Address ches-pc: epmap ches-pc: microsoft-ds ches-pc: 1025 ches-pc: 1036 ches-pc: 3115 ches-pc: 3118 ches-pc: 3470 ches-pc: 3477 ches-pc: 5000 ches-pc: 6515 ches-pc: netbios-ssn ches-pc: 3001 ches-pc: 3002 ches-pc: 3003 ches-pc: 5180 ches-pc: microsoft-ds ches-pc: isakmp ches-pc: 1027 ches-pc: 3008 ches-pc: 3473 ches-pc: 6514 ches-pc: 6515 ches-pc: netbios-ns ches-pc: netbios-dgm ches-pc: 1900 ches-pc: ntp ches-pc: 1900 ches-pc: 3471 Foreign Address ches-pc: 0 ches-pc: 0 ches-pc: 0 ches-pc: 0 *: * *: * *: * *: * Vanguard, Feb 2004 State LISTENING LISTENING LISTENING LISTENING 55 of 60
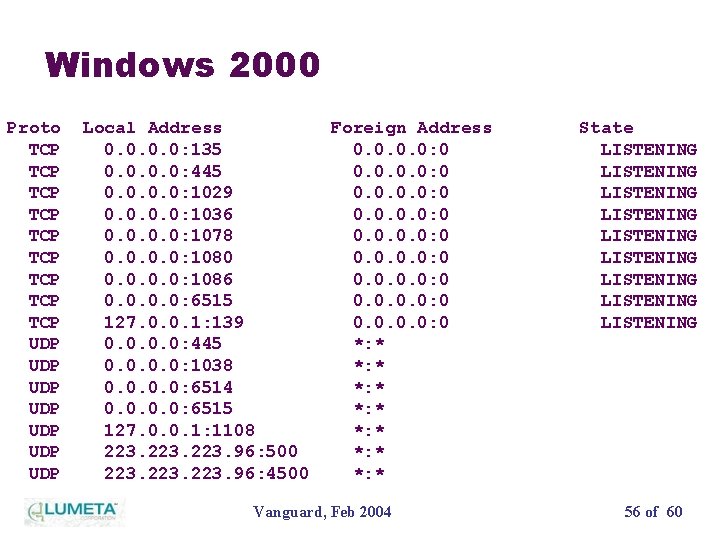
Windows 2000 Proto TCP TCP TCP UDP UDP Local Address 0. 0: 135 0. 0: 445 0. 0: 1029 0. 0: 1036 0. 0: 1078 0. 0: 1080 0. 0: 1086 0. 0: 6515 127. 0. 0. 1: 139 0. 0: 445 0. 0: 1038 0. 0: 6514 0. 0: 6515 127. 0. 0. 1: 1108 223. 96: 500 223. 96: 4500 Foreign Address 0. 0: 0 0. 0: 0 *: * *: * Vanguard, Feb 2004 State LISTENING LISTENING LISTENING 56 of 60
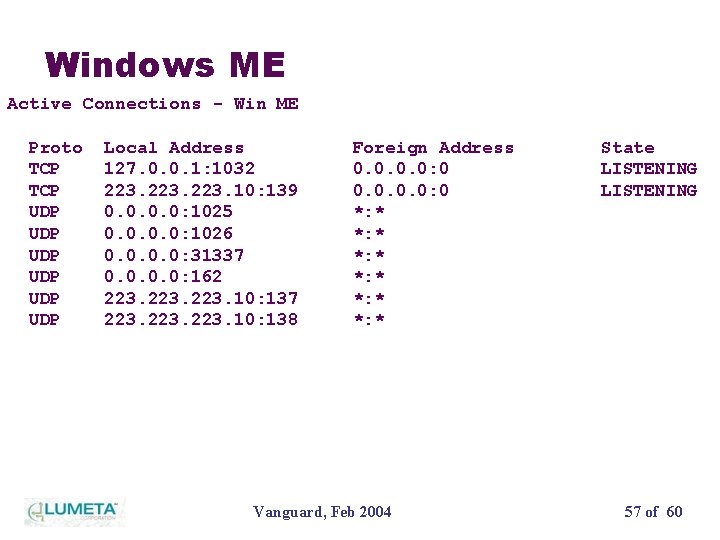
Windows ME Active Connections - Win ME Proto TCP UDP UDP UDP Local Address 127. 0. 0. 1: 1032 223. 10: 139 0. 0: 1025 0. 0: 1026 0. 0: 31337 0. 0: 162 223. 10: 137 223. 10: 138 Foreign Address 0. 0: 0 *: * *: * Vanguard, Feb 2004 State LISTENING 57 of 60
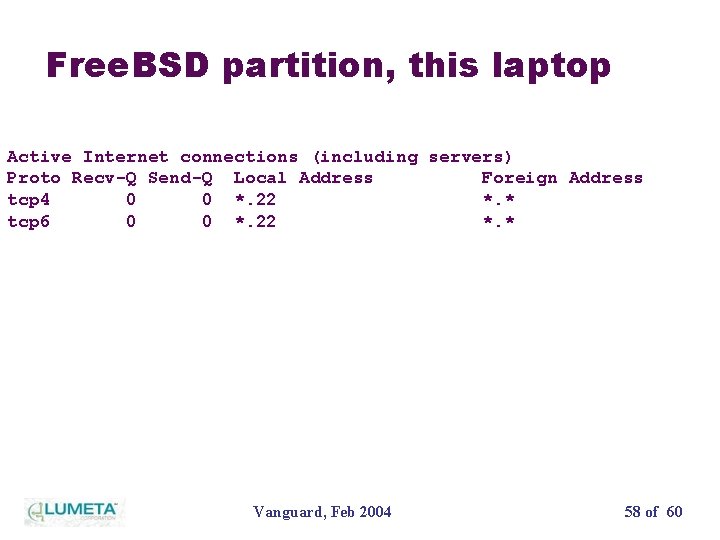
Free. BSD partition, this laptop Active Internet connections (including servers) Proto Recv-Q Send-Q Local Address Foreign Address tcp 4 0 0 *. 22 *. * tcp 6 0 0 *. 22 *. * Vanguard, Feb 2004 58 of 60
Microsoft really means it about improving their security • They need world-class sandboxes, many more layers in their security, and much safer defaults • A Microsoft “terminal” will benefit millions of users Vanguard, Feb 2004 59 of 60
Internet Security Successes: It’s Hard, but it’s not Impossible Bill Cheswick Lumeta Corp. 60 slides
- Slides: 58