Internet Communication Technologies Web Technologies Overview Objectives 1
Internet Communication Technologies Web Technologies
Overview Objectives 1. Introduce basic concepts in data communications and networks 2. Explain what Internet is and how it is organised 3. Show web and network applications can be programmed 4. Give experience in developing simple web & network applications Coverage… Network fundamentals; Client server computing; Internet architecture and organising bodies; TCP/IP protocols; Socket based communications; Application protocols: HTTP, SMTP, POP, IMAP, MIME; Client server computing, etc
Introduction Internet Protocols are used to transfer files or data from one machine to the other. All computers on the Internet communicate with each other using the Transmission Control Protocol / Internet Protocol (TCP/IP). Thus, data is sent from the server to the client (and viceversa) using TCP/IP. Typically, the client is your browser and the server is a program running on a different computer. You use the browser on your computer (called the client machine in Internet lingo) to access the information on another computer (called the server machine). This server machine can be located thousands of miles from your workplace.
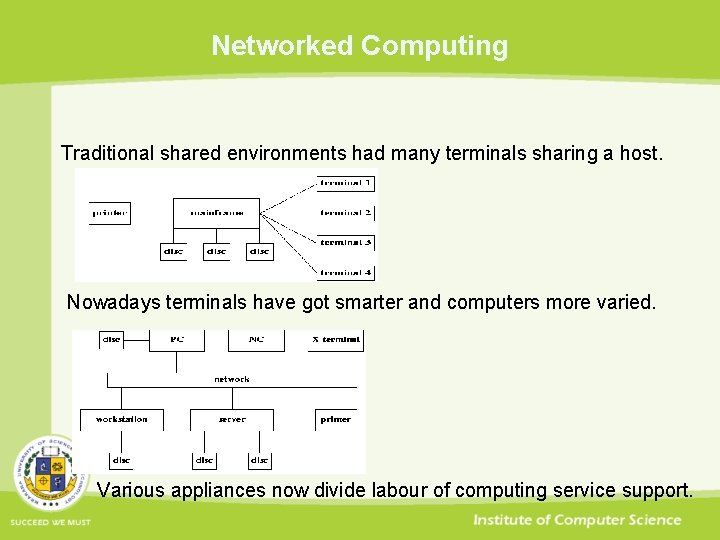
Networked Computing Traditional shared environments had many terminals sharing a host. Nowadays terminals have got smarter and computers more varied. Various appliances now divide labour of computing service support.
Peer to Peer Model In Peer to Peer model of service provision each party sometimes initiates and sometimes responds to other parties provides services to other parties consumes same type of services provided by other parties Peer-to-peer applications are currently of 3 main types collaboration & communication- multi-agents, instant messaging content sharing- Gnutella, Bit Torrent, Morpheus distributed computing pooled computing assets Grids
Peer to Peer Model Peers typically have similar computing power and resources as other peers are invoked by users for one session can handle multiple concurrent service interactions Unlike Client Server model peers both consume and provide services peers are not solely passive nor solely active Peer to Peer Grids share resources such as CPU power - cycles memory - cache storage, fast access memory modules, filespace network access - bandwidth, network connections special resources - spatially immersive display, sensor network
Publish and Subscribe Model In Publish and Subscribe model of service provision publisher publishes stream of data along a channel subscriber receives service by subscribing to this channel publisher is active service provider subscriber is passive service consumer Publishers typically serve multiple subscribers concurrently support multicasting along multiple publishing channels run on powerful shared computer with sophisticated OS
Publish and Subscribe Model Subscribers typically run locally on user's personal computer are largely passive in receiving service are invoked by users for one session Publishers can use encryption to control access by subscribers. Unlike Client Server model publisher is active and not merely responsive like server subscriber is passive unlike clients initiating interaction Radio and TV use this model
Client Server Model In Client Server model of service provision client is service consumer server is service provider client actively requests server to provide service server passively waits to service clients Service provision is purely demand driven. Client software typically: only acts as client intermittently between local processing is invoked by user for one session runs locally on user's personal computer only accesses one remote server at a time doesn't require special hardware or sophisticated OS
Client Server Model Server software typically: is special purpose program providing type of service is invoked when OS boots & executes through many sessions runs on powerful, shared computer with network OS accepts concurrent interaction from arbitrary clients Interaction on Client Server model can either be stateless sessional
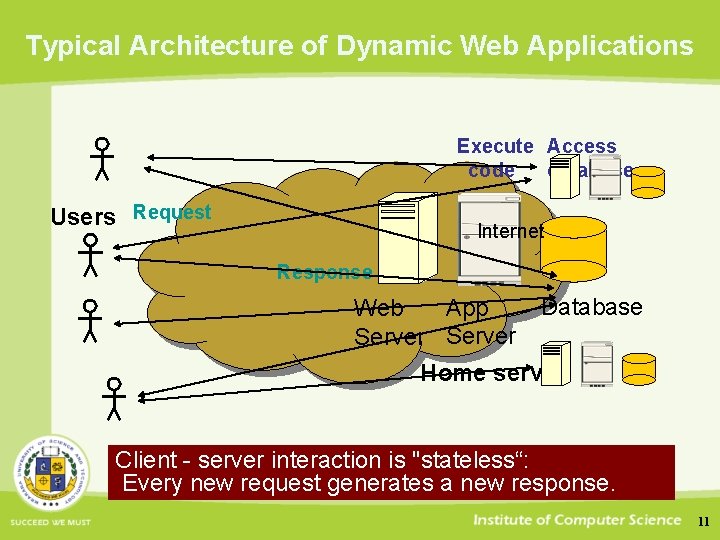
Typical Architecture of Dynamic Web Applications Execute Access code database Users Request Internet Response Database App Web Server Home server Client - server interaction is "stateless“: Every new request generates a new response. 11
Network Protocols Modern networks are designed as series of layers where each layer is built using interface of layer below it offers services to layer above it hides details of all layers below it to layers above it Separating network functionality into layers reduces complexity of network design enables layers to be implemented relatively independently allows swapping of functionally equivalent implementations Set of layers and protocols is called a network architecture. List of protocols, one per layer, is called a protocol stack. Layers can offer connection-oriented or connectionless service.
Network Protocols Connection-oriented service is like telephone where user establishes connection sends and receives messages along route of this connection releases connection Connectionless service is like post where communication is split into a series of messages each message is separately addressed and sent messages may travel to other end by variety of routes
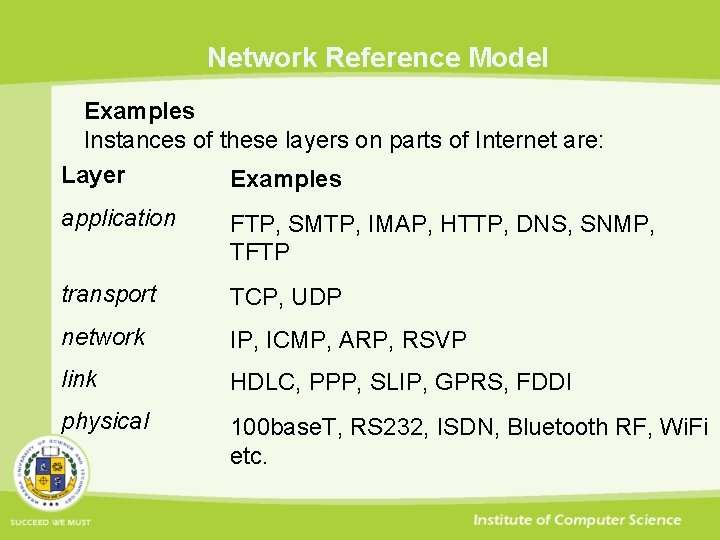
Network Reference Model Examples Instances of these layers on parts of Internet are: Layer Examples application FTP, SMTP, IMAP, HTTP, DNS, SNMP, TFTP transport TCP, UDP network IP, ICMP, ARP, RSVP link HDLC, PPP, SLIP, GPRS, FDDI physical 100 base. T, RS 232, ISDN, Bluetooth RF, Wi. Fi etc.
Electronic Mails- MIME
Nature of Electronic Mail Electronic mail is a messaging system modeled on postal mail that sends, receives and stores messages solely within electronic media. Unlike faxes, the post and telegrams e-mail messages never need to be transcribed onto a physical medium. Unlike the phone, e-mail is an asynchronous messaging service. Unlike paging and SMS, e-mail is not for real-time messaging. Electronic mail systems consist of: user agents: let people read and send messages message transfer: agents move messages from source to destination Mailboxes: store messages sent to recipients
Nature of Electronic Mail Typical user agents are command, GUI or web based programs. Typical message transfer agents are daemons running on servers. Typical mailboxes are files. Typical e-mail systems support 5 basic functions Composition: creation and addressing of messages & answers Display: enabling viewing/rendering of incoming messages Disposition: dealing with message upon receipt Reporting: telling originator what happened to message Transfer: movement of messages from originator to recipient
Electronic Mail Functions Composition: e-mail user agents should enable users to create and address e-mail messages, reply to e-mail messages received Display: e-mail user agents should enable users to browse messages received by main identifying attributes read or render message on demand Disposition: e-mail user agents should enable users to delete received messages save received messages in a folder keep received messages in user's mailbox
Electronic Mail Functions Reporting: e-mail facilities should report on messages sent so users can discover from logs what messages they have sent and when are notified when their messages cannot be delivered can ask for e-mail confirmation that message is received Transfer: e-mail facilities should transfer messages from sender to addressee cope with any delays or problems experienced Transfer may involve use of intermediaries which store and forward e-mail for certain addresses act as gateways to other e-mail or messaging systems
Electronic Mail Features More advanced features of e-mail systems include address book: store of e-mail addresses & short handles for them Aliases: e-mail address pseudonym for recipient of email Attachments: sending enclosures attached to e-mail messages e-mail filtering: programmed processing of e-mail lists: redirecting e-mail sent to list of recipients high priority e-mail: ensuring delivery in short time span multimedia e-mail: handling multimedia - images, voice, applications secret e-mail: encrypting message contents to ensure privacy
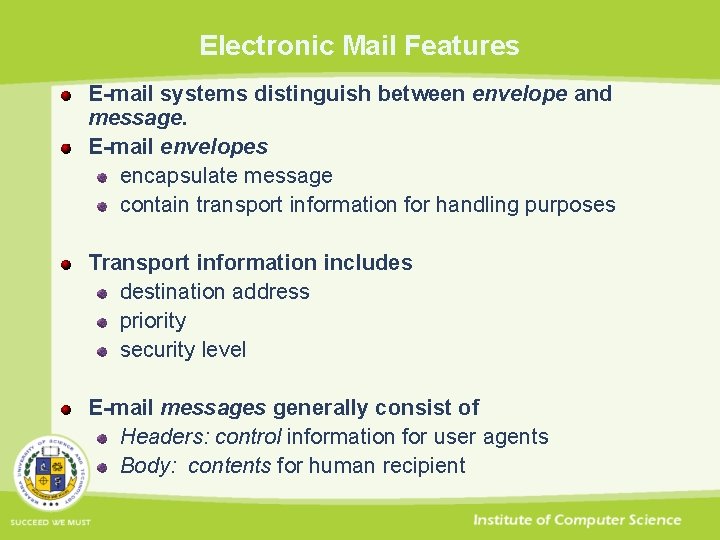
Electronic Mail Features E-mail systems distinguish between envelope and message. E-mail envelopes encapsulate message contain transport information for handling purposes Transport information includes destination address priority security level E-mail messages generally consist of Headers: control information for user agents Body: contents for human recipient
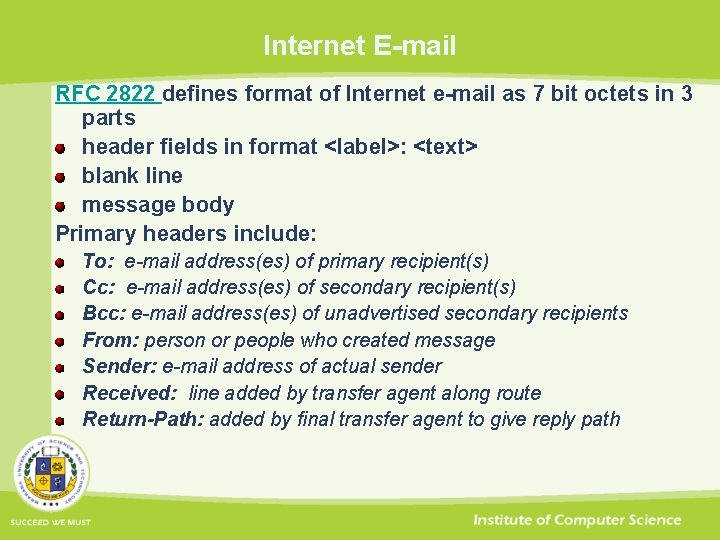
Internet E-mail RFC 2822 defines format of Internet e-mail as 7 bit octets in 3 parts header fields in format <label>: <text> blank line message body Primary headers include: To: e-mail address(es) of primary recipient(s) Cc: e-mail address(es) of secondary recipient(s) Bcc: e-mail address(es) of unadvertised secondary recipients From: person or people who created message Sender: e-mail address of actual sender Received: line added by transfer agent along route Return-Path: added by final transfer agent to give reply path
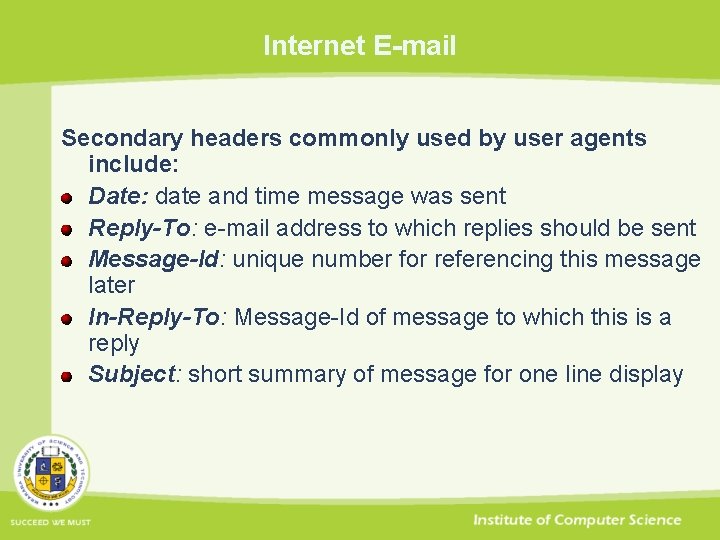
Internet E-mail Secondary headers commonly used by user agents include: Date: date and time message was sent Reply-To: e-mail address to which replies should be sent Message-Id: unique number for referencing this message later In-Reply-To: Message-Id of message to which this is a reply Subject: short summary of message for one line display
Multipurpose Internet Mail Extensions To allow Internet e-mail messages to contain languages with accents, non-Latin letters and glyphs audio, images or video executable scripts multi-part combinations of such elements an extended format MIME was specified in RFC 1521 IANA keeps register of currently recognised media types: http: //www. iana. org/assignments/media-types/
Multipurpose Internet Mail Extensions MIME format continues to use RFC 2822 format introduces five new header types adds structure to message body defines encoding rules for non-text messages MIME defines five headers MIME-Version: identifies MIME version currently 3. 1 Content-Description: free text description of message Content-Id: unique identifier Content-Transfer-Encoding: how body is encoded for sending Content-Type: nature of message
MIME Content Transfer Encoding Types of Content-Transfer-Encoding include 7 bit: un-encoded 7 bit octets (0 to 127 in decimal values) quoted printable: 7 bit octets + special codes for 8 bit octets Base 64: encodes each 3 octets as 4 octets readable in Ascii 8 bit: un-encoded 8 bit octets – unsafe Binary: un-encoded binary - unsafe Unsafe means violates SMTP - relies on extensions for safe transport. Quoted printable encoding is used if only a few octets for 128 to 255 are needed is more efficient in such cases than base 64 encodes high bit set octets as = <hex digit>
MIME Content Transfer Encoding Base 64 encoding is specified in RFC 1521 each 3 bytes of source is divided into 4 chunks of 6 bits each 6 bit chunk can have 64 different values 64 values are represented by letters A. . . Z a. . . z 0. . . 9 + / byte representation of letter is sent to represent 6 bit chunk Base 64 encoding is identical in all ISO 646 encodings e. g US Ascii, EBCDIC etc. always produces about 33% larger encoding than original uses 0, 1 or 2 "="s to pad encoding at end to multiple of 4 bytes
“Man is distinguished, not only by his reason, but by this singular passion from other animals, which is a lust of the mind, that by a perseverance of delight in the continued and indefatigable generation of knowledge, exceeds the short vehemence of any carnal pleasure. ” Represented as a byte sequence of 8 -bitpadded ASCII characters is encoded in MIME's Base 64 scheme as follows: TWFu. IGlz. IGRpc 3 Rpbmd 1 a. XNo. ZWQs. IG 5 vd. CBvbmx 5 IGJ 5 IGhpcy. By. ZWFz b 24 s. IGJ 1 d. CBie. SB 0 a. Glz. IHNpbmd 1 b. GFy. IHBhc 3 Npb 24 g. Zn. Jvb. SBvd. Ghlci Bhbmlt. YWxz. LCB 3 a. Glja. CBpcy. Bh. IGx 1 c 3 Qgb 2 Ygd. Ghl. IG 1 pbm. Qs. IHRo. YXQ g. Ynkg. YSBw. ZXJz. ZXZlcm. Fu. Y 2 Ugb 2 Yg. ZGVsa. Wdod. CBpbi. B 0 a. GUg. Y 29 ud. G lud. WVk. IGFu. ZCBpbm. Rl. Zm. F 0 a. Wdh. Ymxl. IGdlbm. Vy. YXRpb 24 gb 2 Yga 25 vd 2 xl. ZGdl. LCBle. GNl. ZWRz. IHRo. ZSBza. G 9 yd. CB 2 ZWhlb. WVu. Y 2 Ugb 2 Yg. YW 55 IG Nhcm 5 hb. CBwb. GVhc 3 Vy. ZS 4=
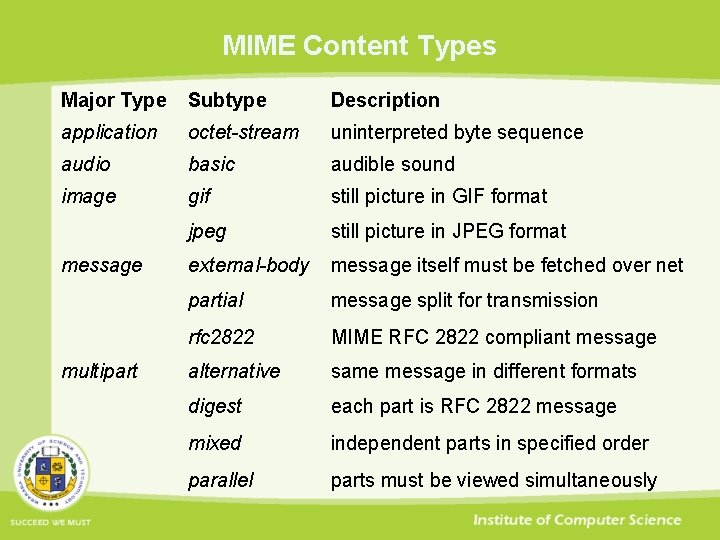
MIME Content Types Major Type Subtype Description application octet-stream uninterpreted byte sequence audio basic audible sound image gif still picture in GIF format jpeg still picture in JPEG format external-body message itself must be fetched over net partial message split for transmission rfc 2822 MIME RFC 2822 compliant message alternative same message in different formats digest each part is RFC 2822 message mixed independent parts in specified order parallel parts must be viewed simultaneously message multipart
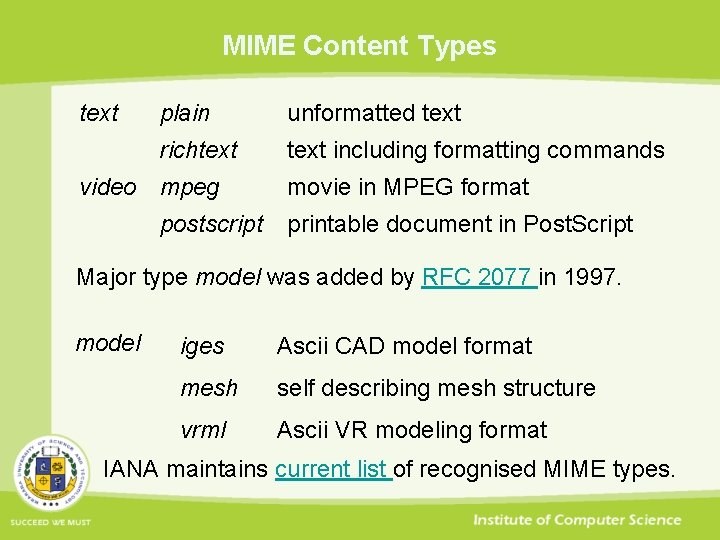
MIME Content Types text plain unformatted text richtext including formatting commands video mpeg postscript movie in MPEG format printable document in Post. Script Major type model was added by RFC 2077 in 1997. model iges Ascii CAD model format mesh self describing mesh structure vrml Ascii VR modeling format IANA maintains current list of recognised MIME types.
E-mail Protocols
Simple Message Transfer Protocol is specified in RFC 2821 SMTP aims to transfer e-mail reliably and efficiently operates independently of network transport service uses intermediate relays to forward mail SMTP is mostly used with TCP transport on port 25 by default. Purposes of SMTP are primarily to mail messages to user's mailbox secondarily to send messages to user's terminal Secondary purpose is rarely used nowadays. Its transactions start with MAIL FROM and end with DATA command.
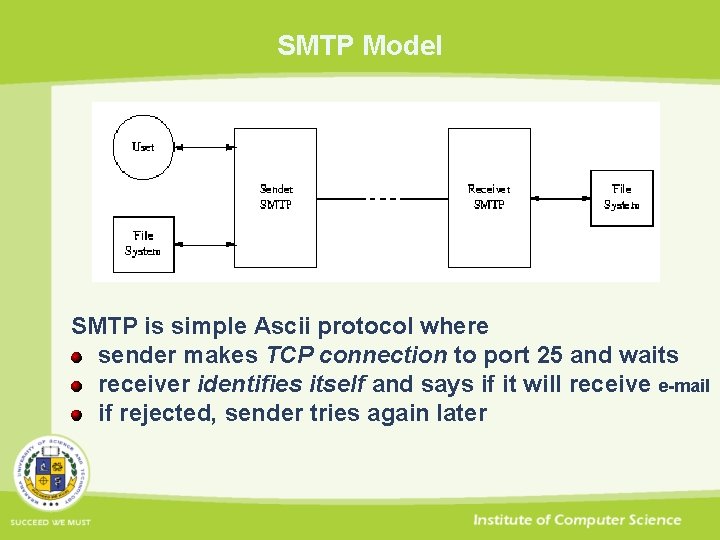
SMTP Model SMTP is simple Ascii protocol where sender makes TCP connection to port 25 and waits receiver identifies itself and says if it will receive e-mail if rejected, sender tries again later
SMTP Model If receiver is willing to receive e-mail then sender announces author and recipient of e-mail if recipient exists at destination, receiver permits sending sender sends e-mail receiver acknowledges e-mail sent any more e-mail is now sent when all e-mail both ways is exchanged, connection is dropped SMTP receivers can refuse e-mail but recommend <forwardpath>. Where recipient of e-mail is not local, SMTP receiver may permit sending announce that will forward e-mail on <forward-path> forward e-mail
SMTP Session In a typical SMTP session, the protocol mainly deals with the following main commands: HELO: names the client (the spelling is deliberate) MAIL FROM: names the sender RCPT TO: names a recipient DATA: asks to send message data Mail Message: sends the message data QUIT: finishes the mail session
SMTP Session Some of the response codes used in an SMTP session. Note: that only the numeric code is standardised - the textual explanation may vary. 220 Server ready: a connection to the server has been made and the server is ready 221 Server closing: the server accepted the QUIT command is ready to close the connection 250 OK: the server accepted the command (one of several similar responses) 354 Send mail: the server accepted the DATA command is waiting for the Mail Message 550 Invalid: the server rejected the command (one of several similar responses)
SMTP Security SMTP service extensions support encrypted communications among SMTP servers authentication Client communicates subsequent SMTP requests using TLS (SSL). Authentication RFC 2554 defines several SMTP service extensions for authentication. Most widely used scheme solicits username and password in base 64:
Mailbox Handling Protocols Internet has two main standards governing mailbox handling POP Post Office Protocol (version 3) IMAP Interactive Mail Access Protocol (version 4) They are available as RFC 1225 and RFC 2060 POP is simple protocol with commands for logging in and out fetching messages deleting messages Its main purpose is to fetch e-mail from remote mailbox store it on user's local machine for later reading
Mailbox Handling Protocols IMAP is more sophisticated protocol that offers selective retrieval of e-mail messages server based message processing shared mailboxes facility for offline client to resynchronise with server IMAP is suitable for mobile e-mail clients simple groupware
Mailbox Handling Protocols - POP 3 protocol defined in RFC 1225 is simple Ascii protocol capable of interactive & programmed use offered by POP 3 server on TCP port 110 All POP 3 commands are terminated by CRLF ('r' followed by 'n') get +OK or -ERR reply with possible explanatory string have multi-line replies terminated by CRLF
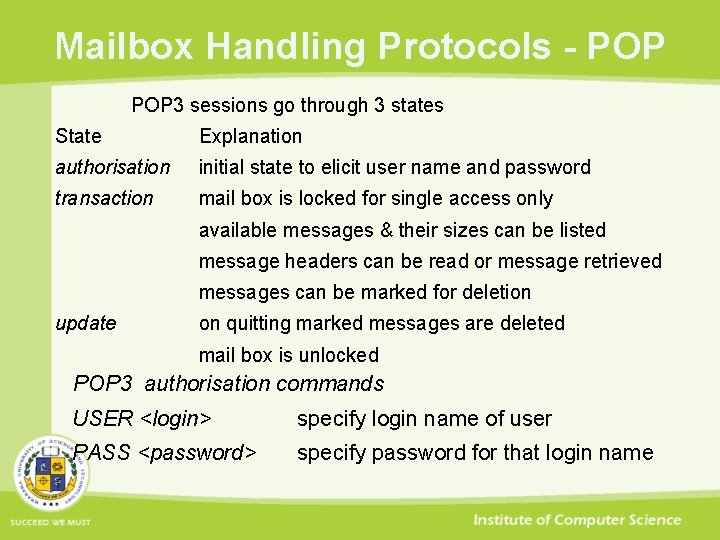
Mailbox Handling Protocols - POP 3 sessions go through 3 states State Explanation authorisation initial state to elicit user name and password transaction mail box is locked for single access only available messages & their sizes can be listed message headers can be read or message retrieved messages can be marked for deletion update on quitting marked messages are deleted mail box is unlocked POP 3 authorisation commands USER <login> specify login name of user PASS <password> specify password for that login name
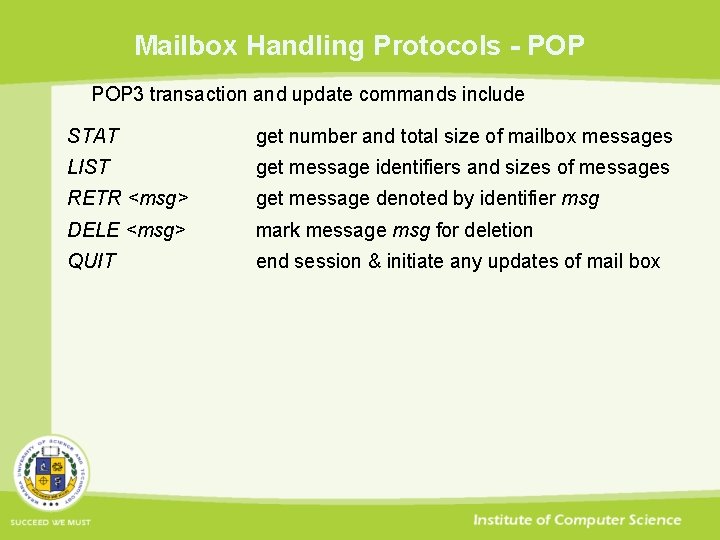
Mailbox Handling Protocols - POP 3 transaction and update commands include STAT get number and total size of mailbox messages LIST get message identifiers and sizes of messages RETR <msg> get message denoted by identifier msg DELE <msg> mark message msg for deletion QUIT end session & initiate any updates of mail box
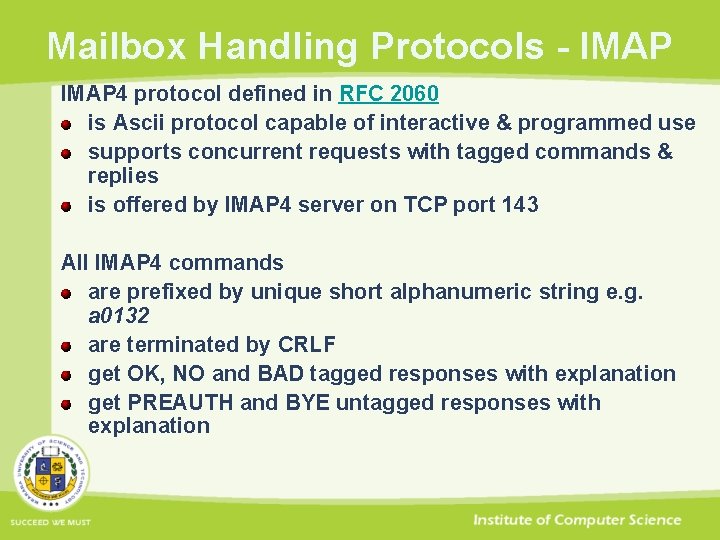
Mailbox Handling Protocols - IMAP 4 protocol defined in RFC 2060 is Ascii protocol capable of interactive & programmed use supports concurrent requests with tagged commands & replies is offered by IMAP 4 server on TCP port 143 All IMAP 4 commands are prefixed by unique short alphanumeric string e. g. a 0132 are terminated by CRLF get OK, NO and BAD tagged responses with explanation get PREAUTH and BYE untagged responses with explanation
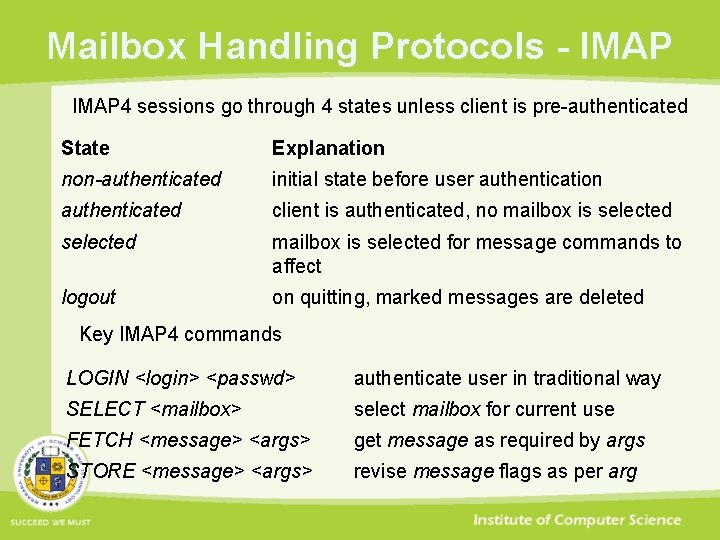
Mailbox Handling Protocols - IMAP 4 sessions go through 4 states unless client is pre-authenticated State Explanation non-authenticated initial state before user authentication authenticated client is authenticated, no mailbox is selected for message commands to affect logout on quitting, marked messages are deleted Key IMAP 4 commands LOGIN <login> <passwd> authenticate user in traditional way SELECT <mailbox> select mailbox for current use FETCH <message> <args> get message as required by args STORE <message> <args> revise message flags as per arg
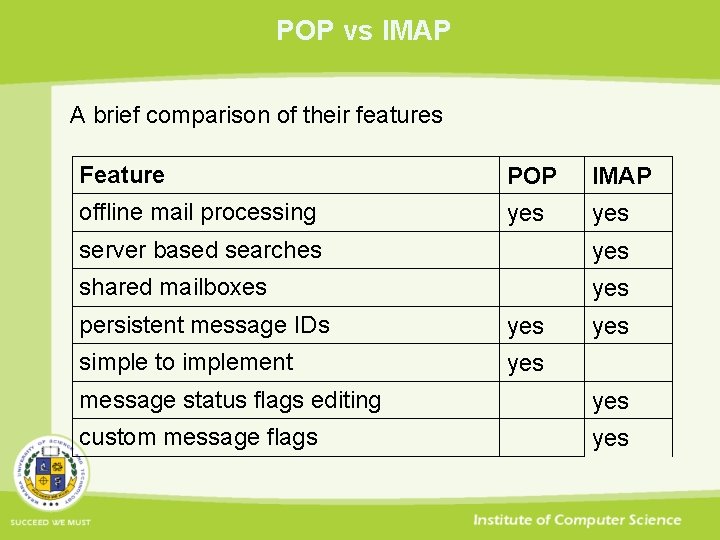
POP vs IMAP A brief comparison of their features Feature POP IMAP offline mail processing yes server based searches yes shared mailboxes yes persistent message IDs yes simple to implement yes message status flags editing yes custom message flags yes
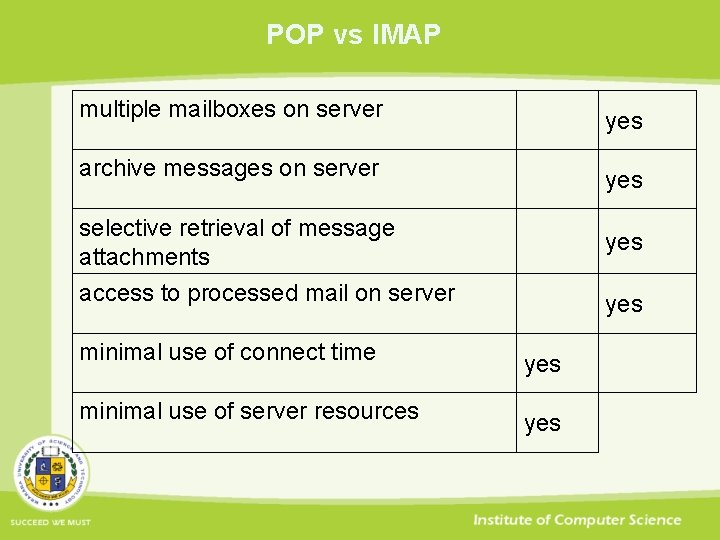
POP vs IMAP multiple mailboxes on server yes archive messages on server yes selective retrieval of message attachments access to processed mail on server yes minimal use of connect time yes minimal use of server resources yes
URLs - What is a URL?
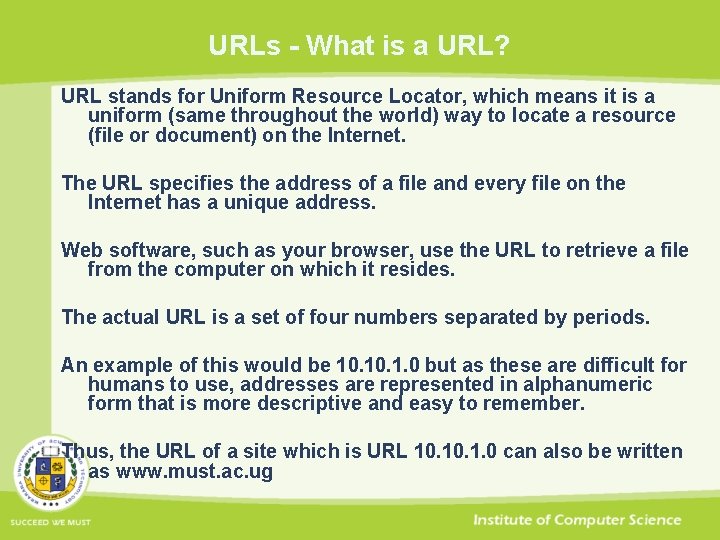
URLs - What is a URL? URL stands for Uniform Resource Locator, which means it is a uniform (same throughout the world) way to locate a resource (file or document) on the Internet. The URL specifies the address of a file and every file on the Internet has a unique address. Web software, such as your browser, use the URL to retrieve a file from the computer on which it resides. The actual URL is a set of four numbers separated by periods. An example of this would be 10. 1. 0 but as these are difficult for humans to use, addresses are represented in alphanumeric form that is more descriptive and easy to remember. Thus, the URL of a site which is URL 10. 1. 0 can also be written as www. must. ac. ug
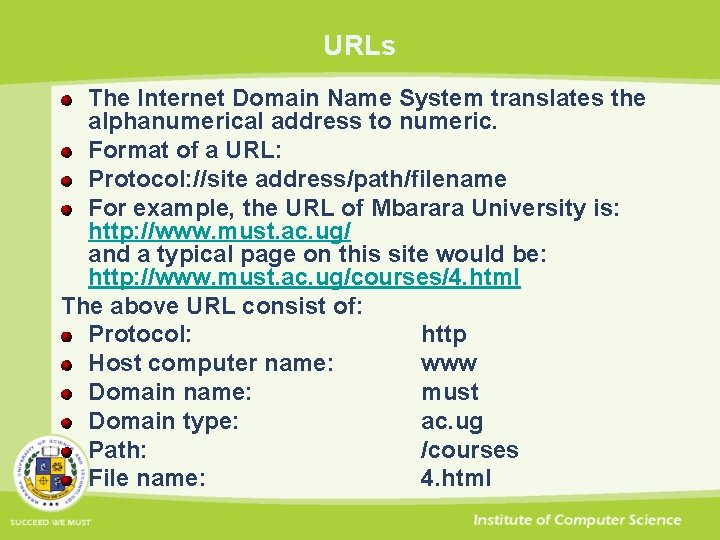
URLs The Internet Domain Name System translates the alphanumerical address to numeric. Format of a URL: Protocol: //site address/path/filename For example, the URL of Mbarara University is: http: //www. must. ac. ug/ and a typical page on this site would be: http: //www. must. ac. ug/courses/4. html The above URL consist of: Protocol: http Host computer name: www Domain name: must Domain type: ac. ug Path: /courses File name: 4. html
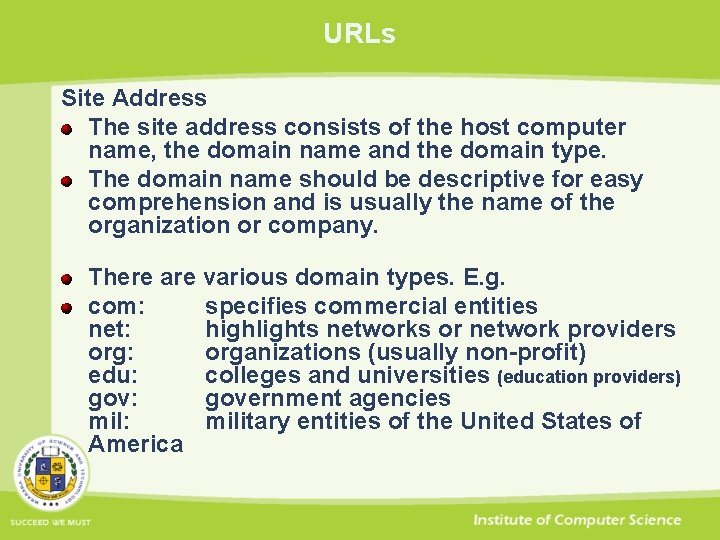
URLs Site Address The site address consists of the host computer name, the domain name and the domain type. The domain name should be descriptive for easy comprehension and is usually the name of the organization or company. There are various domain types. E. g. com: specifies commercial entities net: highlights networks or network providers org: organizations (usually non-profit) edu: colleges and universities (education providers) gov: government agencies mil: military entities of the United States of America
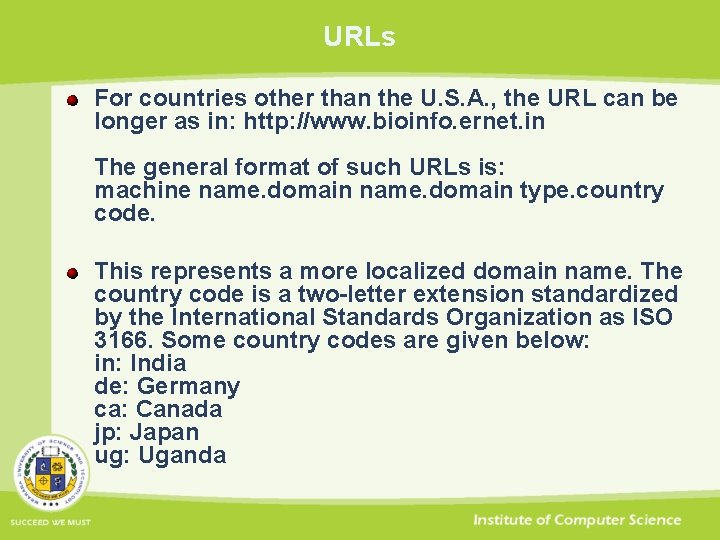
URLs For countries other than the U. S. A. , the URL can be longer as in: http: //www. bioinfo. ernet. in The general format of such URLs is: machine name. domain type. country code. This represents a more localized domain name. The country code is a two-letter extension standardized by the International Standards Organization as ISO 3166. Some country codes are given below: in: India de: Germany ca: Canada jp: Japan ug: Uganda
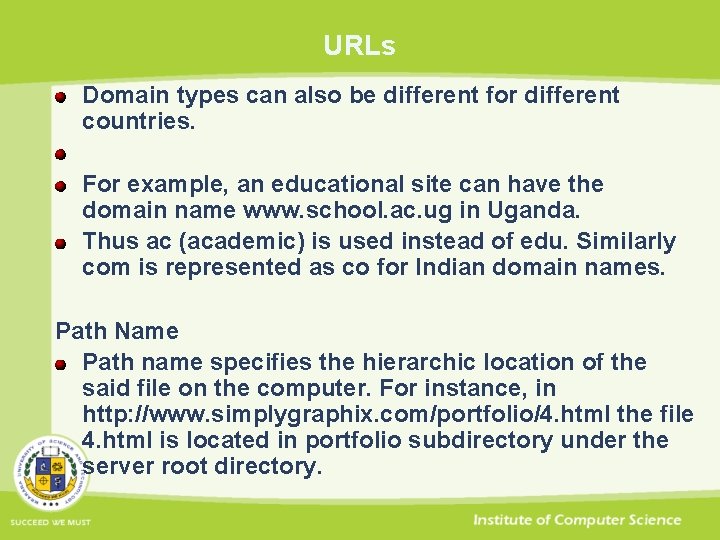
URLs Domain types can also be different for different countries. For example, an educational site can have the domain name www. school. ac. ug in Uganda. Thus ac (academic) is used instead of edu. Similarly com is represented as co for Indian domain names. Path Name Path name specifies the hierarchic location of the said file on the computer. For instance, in http: //www. simplygraphix. com/portfolio/4. html the file 4. html is located in portfolio subdirectory under the server root directory.
URLs Port Browsers communicate with the server using entry points called ports. Associated with each protocol is a default port number, such as HTTP defaults to port 80. The server administrator can configure the server to handle http requests at a different port. In such cases, the port number has to be supplied as a part of the URL. The port number is placed at the end of the URL after a colon. www. some-address. com: 50 HTML Anchors With HTML you can specify anchors within files. These anchors are end points to hyperlinks placed either in the same file or some other files. Anchors are placed to link to specific locations in a file. They can be a part of the URL and are represented with a hash symbol (#) followed by the link name. ww. some-address. com/some-file. html#some-location
URLs URNs are Uniform Resource Names. They are globally unique, location independent identifiers that are part of an extensible, scalable name space with legacy support that allow the identification of a resource even after its lifetime. They are potentially resoluble to URLs, metadata or resources by a network accessible resolution service although this doesn't yet exist. E. g urn: def: //blue_laser A comparable URL would need to specify one specific location for a definition such as: • http: //www. whatis. com/bluelaser. htm
URLs URI’s The Web is an information space. Human beings have a lot of mental machinery for manipulating, imagining, and finding their way in spaces. URIs are the points in that space. Unlike web data formats, where HTML is an important one, but not the only one, and web protocols, where HTTP has a similar status, there is only one Web naming/addressing technology: URIs. Uniform Resource Identifiers (URIs, aka URLs) are short strings that identify resources in the web: documents, images, downloadable files, services, electronic mailboxes, and other resources.
URLs URIs make resources available under a variety of naming schemes and access methods such as HTTP, FTP, and Internet mail addressable in the same simple way. They reduce the tedium of "log in to this server, then issue this magic command. . . " down to a single click. It is an extensible technology: there a number of existing addressing schemes, and more may be incorporated over time.
URN, URL, URI A URN is similar to a person's name, while a URL is like a street address. The URN defines something's identity, while the URL provides a location. Essentially, "what" vs. "where". A URL is a URI that identifies a resource and also provides the means of locating the resource by describing the way to access it A URL is a URI A URI is not necessarily a URL
To make it more clear… URL: ftp: //ftp. is. co. za/rfc 1808. txt URL: http: //www. ietf. org/rfc 2396. txt: URL: ldap: //[2001: db 8: : 7]/c=GB? object. Class? one: URL: mailto: John. Doe@example. com: URL: news: comp. infosystems. www. servers. unix: URL: telnet: //192. 0. 2. 16: 80/: URL URN (not URL): urn: oasis: names: specification: docbook: dtd: xml: 4. 1. 2: URN (not URL): tel: +1 -816 -555 -1212 (? )

HTTP protocol
HTTP protocol Computers on the World Wide Web use the Hyper. Text Transfer Protocol to talk with each other. The HTTP provides a set of instructions for accurate information exchange. The communication between the client (your browser) and the server (a software located on a remote computer) involves requests sent by the client and responses from the server. Each client-server transaction, whether a request or a response, consists of three main parts A response or request line Header information The body
HTTP protocol A client connects to the server at port 80 (unless it has been changed by the system administrator) and sends a request. The request line from the client consists of a request method, the address of the file requested and the HTTP version number. GET /mypage. html HTTP/1. 1 The above request calls for mypage. html file using the GET HTTP method; the version of HTTP used is 1. 1. After the request line comes the header data that consists of configuration information about the client and its document viewing preferences. The header is a series of lines, each of which contains a specific detail about the client and ends with a blank line. A header may look like this: ACCEPT: */* ACCEPT_LANGUAGE: en-us REFERER: http: //www. cit. ac. ug/courses. html USER_AGENT: Mozilla/4. 0 (compatible; MSIE 5. 01; Windows NT 5. 0). . .
HTTP protocol Most of the lines in the header are self-explanatory. The ACCEPT identifies the various kinds of files which the client can display. The REFERER lines contains the document from which the request was generated. In the case above, it is courses. html document from http: //www. cit. ac. ug web site that has sent the request. the The USER_AGENT specifies the browser and gives details on its version number. The body of the request will contain data sent by the client via POST method.
HTTP protocol The server now responds. Again, the response consists of three parts. The response line contains information on the HTTP version number, a status code that indicates the result of the request from the client and a description of the status code in 'English'. HTTP/1. 1 200 OK The HTTP version used is 1. 1 and the status code 200 and 'OK' explain the result of the client's request. The header from the server contains information about the server software and the document sent to the client. Date: Wed, 05 Aug 2007, 13: 25: 54 GMT Server: NCSA/1. 5. 2 Last-modified: Sat, 22 Jan 2007, 05: 15: 43 Content-type: text/html Content-length: 12443
HTTP protocol The header is followed by a blank line that indicates the end of the header information. From the example above, the server sends an html document of size 12443 bytes as shown by the Content-type and Content-length lines. The server line gives details about the server software. The rest is quite evident. One last point on the HTTP protocol- HTTP is a stateless protocol, which means that the connection between the browser and the server is lost once the transaction ends.
HTTP codes After receiving a request from a client (browser), the server software sends a response. The response consists of Response line The header information The body The response line contains the HTTP version number, the status code and a description of the code in 'English'. HTTP/1. 1 200 OK
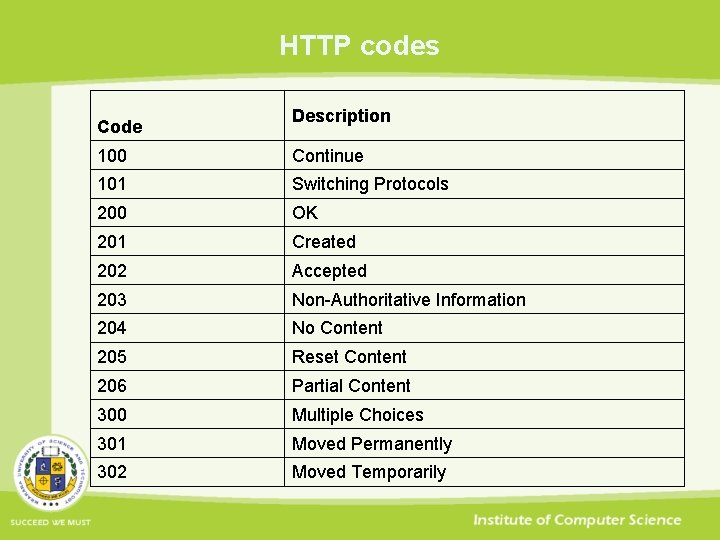
HTTP codes Code Description 100 Continue 101 Switching Protocols 200 OK 201 Created 202 Accepted 203 Non-Authoritative Information 204 No Content 205 Reset Content 206 Partial Content 300 Multiple Choices 301 Moved Permanently 302 Moved Temporarily
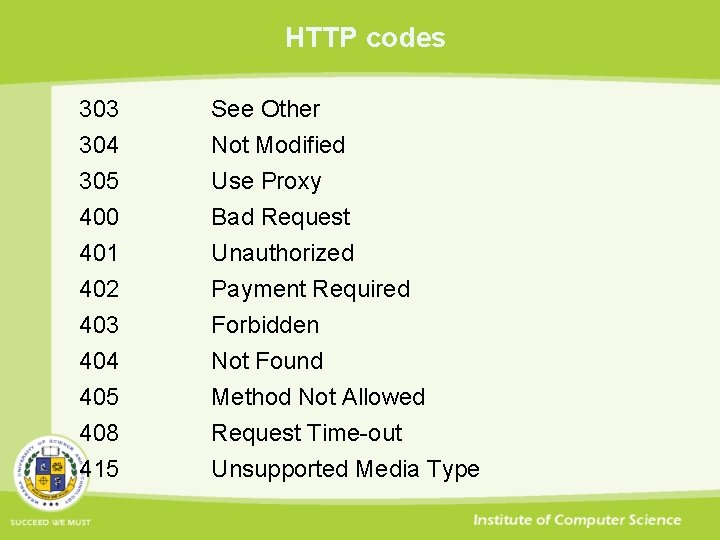
HTTP codes 303 304 305 400 See Other Not Modified Use Proxy Bad Request 401 402 403 404 405 408 415 Unauthorized Payment Required Forbidden Not Found Method Not Allowed Request Time-out Unsupported Media Type
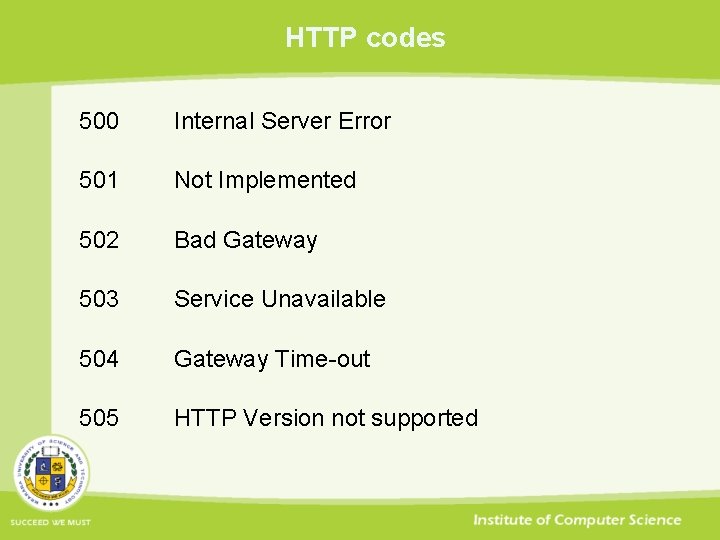
HTTP codes 500 Internal Server Error 501 Not Implemented 502 Bad Gateway 503 Service Unavailable 504 Gateway Time-out 505 HTTP Version not supported
HTTP Client Methods - GET and POST There are three commonly used HTTP methods GET POST HEAD The GET method is used to retrieve HTML documents from the server. It is a part of the request line from the client and tells the server to pass a copy of the document back to the browser or run a CGI program.
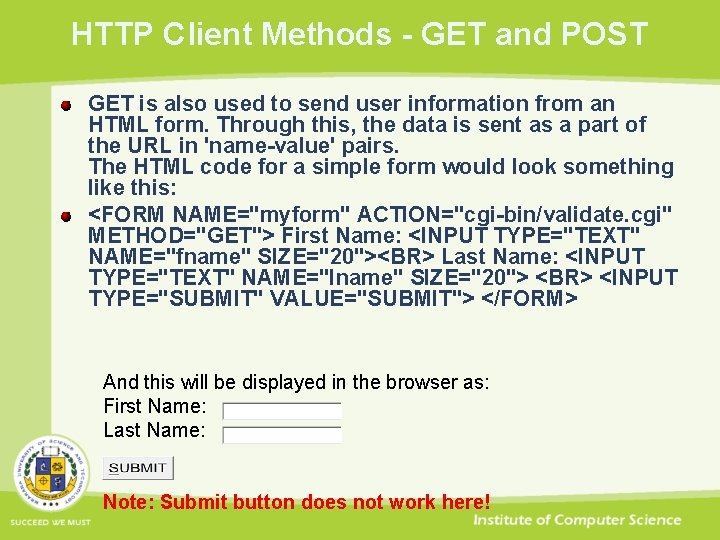
HTTP Client Methods - GET and POST GET is also used to send user information from an HTML form. Through this, the data is sent as a part of the URL in 'name-value' pairs. The HTML code for a simple form would look something like this: <FORM NAME="myform" ACTION="cgi-bin/validate. cgi" METHOD="GET"> First Name: <INPUT TYPE="TEXT" NAME="fname" SIZE="20"><BR> Last Name: <INPUT TYPE="TEXT" NAME="lname" SIZE="20"> <BR> <INPUT TYPE="SUBMIT" VALUE="SUBMIT"> </FORM> And this will be displayed in the browser as: First Name: Last Name: Note: Submit button does not work here!
HTTP Client Methods - GET and POST And this will be displayed in the browser as: First Name: Last Name: Note: Submit button does not work here! Now, let us suppose your name is John Doe. When you submit this form, the data is attached to the URL in namevalue pairs. Each name-value pair is demarcated by a '&' sign and the data is separated from the actual URL with a '? ' sign. Thus after submission the URL in the address/location bar of the browser will be as: www. sitename/cgibin/validate. cgi? fname=John&lname=Doe
HTTP Client Methods - GET and POST Now, let us suppose your name is John Doe. When you submit this form, the data is attached to the URL in name-value pairs. Each name-value pair is demarcated by a '&' sign and the data is separated from the actual URL with a '? ' sign. Thus after submission the URL in the address/location bar of the browser will be as: www. sitename/cgibin/validate. cgi? fname=John&lname=Doe Note how the ? and & sign separate the URL from the data and the name-value pairs, respectively.
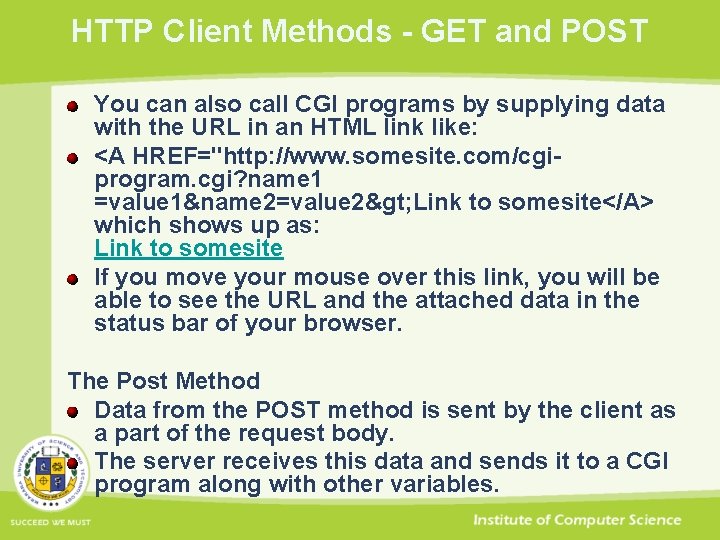
HTTP Client Methods - GET and POST You can also call CGI programs by supplying data with the URL in an HTML link like: <A HREF="http: //www. somesite. com/cgiprogram. cgi? name 1 =value 1&name 2=value 2> Link to somesite</A> which shows up as: Link to somesite If you move your mouse over this link, you will be able to see the URL and the attached data in the status bar of your browser. The Post Method Data from the POST method is sent by the client as a part of the request body. The server receives this data and sends it to a CGI program along with other variables.
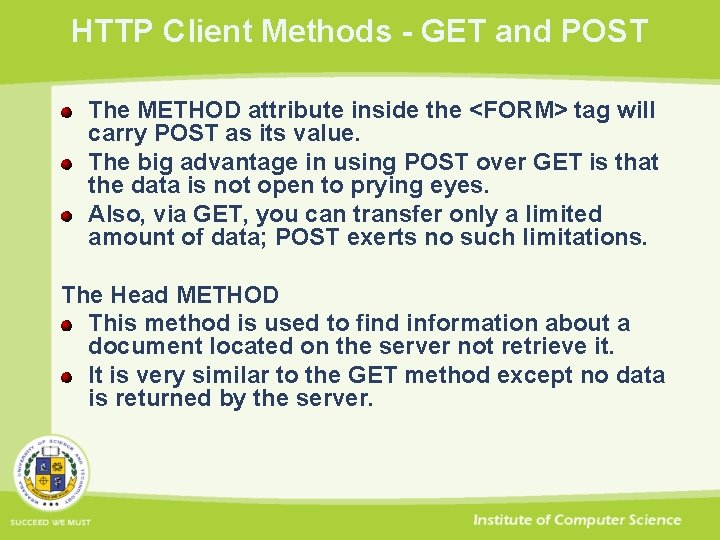
HTTP Client Methods - GET and POST The METHOD attribute inside the <FORM> tag will carry POST as its value. The big advantage in using POST over GET is that the data is not open to prying eyes. Also, via GET, you can transfer only a limited amount of data; POST exerts no such limitations. The Head METHOD This method is used to find information about a document located on the server not retrieve it. It is very similar to the GET method except no data is returned by the server.
The File Transfer Protocol
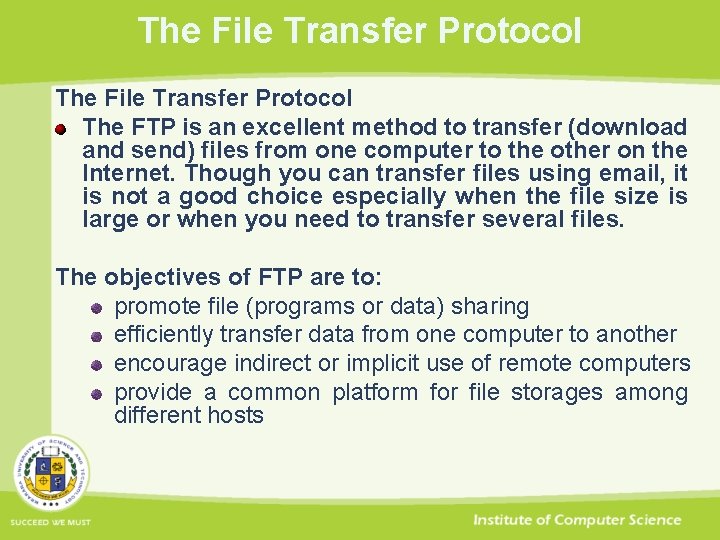
The File Transfer Protocol The FTP is an excellent method to transfer (download and send) files from one computer to the other on the Internet. Though you can transfer files using email, it is not a good choice especially when the file size is large or when you need to transfer several files. The objectives of FTP are to: promote file (programs or data) sharing efficiently transfer data from one computer to another encourage indirect or implicit use of remote computers provide a common platform for file storages among different hosts
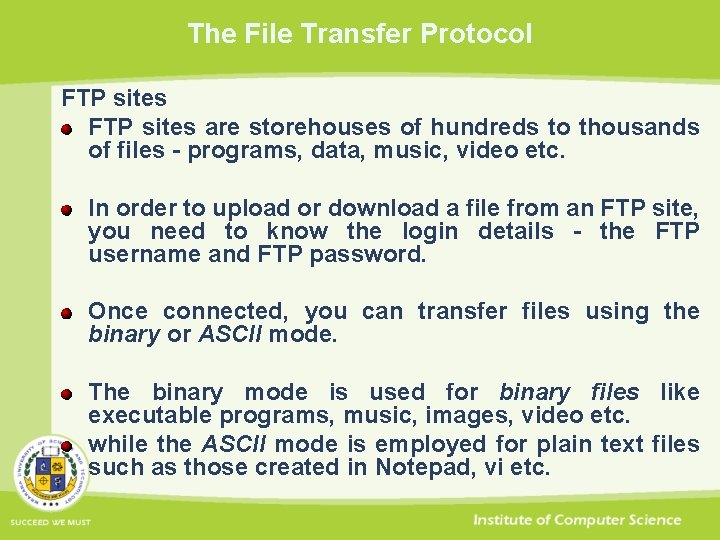
The File Transfer Protocol FTP sites are storehouses of hundreds to thousands of files - programs, data, music, video etc. In order to upload or download a file from an FTP site, you need to know the login details - the FTP username and FTP password. Once connected, you can transfer files using the binary or ASCII mode. The binary mode is used for binary files like executable programs, music, images, video etc. while the ASCII mode is employed for plain text files such as those created in Notepad, vi etc.
The File Transfer Protocol What is anonymous FTP? On connection to an FTP site or FTP server, you would typically be asked the login details - a username and password. However, some severs enable what has come to be known as anonymous FTP. On Anonymous FTP servers you can log in with 'anonymous' as username and your email as password. You would then have access to all the data which has been placed in the anonymous FTP section.
The File Transfer Protocol FTP and web sites The File Transfer Protocol is generally used by web developers to upload web sites to the host - the computer that stores the web site. For example, if you buy a web hosting package, the company would provide you with a username and password with which you'll connect to the FTP server to transfer your files.
The File Transfer Protocol FTP on your desktop FTP is built into the Unix system and can be accessed by typing ftp at the Unix prompt. FTP is also available in Windows. You need to open an MS-DOS window and type ftp at the Dos prompt. The prompt will change to an FTP prompt. You can open an FTP site with the 'open' command. Type 'quit' to come back to the Dos prompt. To get help, type 'help' or '? ' at the FTP prompt. This will list the commands available on your system - check the image below.
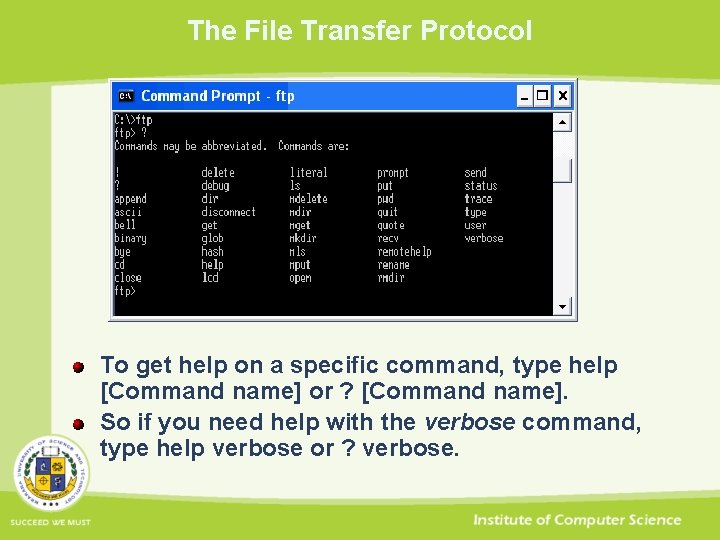
The File Transfer Protocol To get help on a specific command, type help [Command name] or ? [Command name]. So if you need help with the verbose command, type help verbose or ? verbose.
The File Transfer Protocol and the browser Modern browsers allow you to access sites using FTP. For example, if I need to connect to this web site from Internet Explorer on the Windows XP system, I can simply type in ftp: //www. cit. ac. ug in the address bar. A login window then pops up (see below), in which I need to type in the username and password to connect to the host. I can then transfer files using the familiar drag-drop method. So one can actually work in the user-friendly environment of the operating system without knowing all the arcane FTP commands! Now isn't that cool?
The File Transfer Protocol FTP clients If you plan to FTP on a regular basis, I suggest you use an FTP Client - a dedicated program for FTP. There are many FTP clients available (and some of them are freeware). The interface of each program varies, but the information required is almost the same. You should know your username and password of the site (if it is not anonymous FTP) and the server address.
The File Transfer Protocol Using FTP with File Zilla A good web hosting service provides you with an FTP account through which you can maintain and administer your site. Under Windows, FTP connection can be established via the DOS prompt, but an FTP client presents a more user friendly interface. Here, we look at File Zilla, which is a freely available FTP client for the Windows system. You can download it from tim. kosse@filezilla-project. org Once you install this program, it can be accessed from the Programs menu. Some great features are found in commercially available software such as Cute. FTP or WS-FTP.
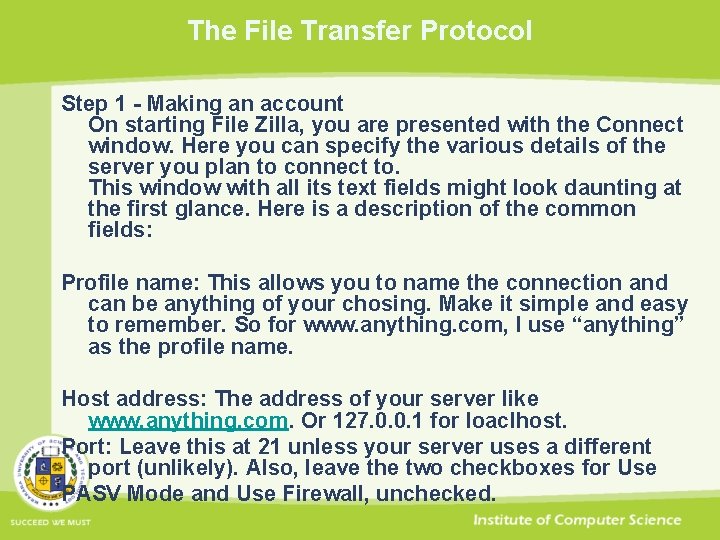
The File Transfer Protocol Step 1 - Making an account On starting File Zilla, you are presented with the Connect window. Here you can specify the various details of the server you plan to connect to. This window with all its text fields might look daunting at the first glance. Here is a description of the common fields: Profile name: This allows you to name the connection and can be anything of your chosing. Make it simple and easy to remember. So for www. anything. com, I use “anything” as the profile name. Host address: The address of your server like www. anything. com. Or 127. 0. 0. 1 for loaclhost. Port: Leave this at 21 unless your server uses a different port (unlikely). Also, leave the two checkboxes for Use PASV Mode and Use Firewall, unchecked.
The File Transfer Protocol Login: Type your login name and click on the Anonymous checkbox to remove the check mark. Password: Type your password if you have any…
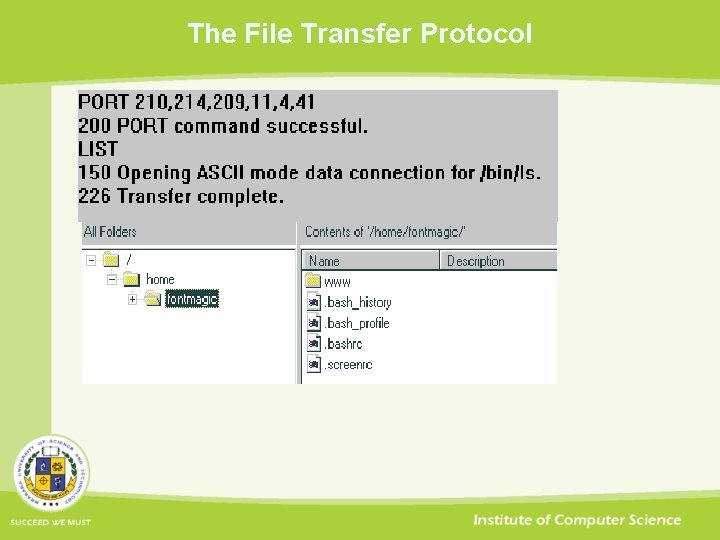
The File Transfer Protocol Step 2: Establishing a connection Start an Internet connection, if you are not connected. In File Zilla client, select the account. The program will try to find the host and establish a connection. As the program sends commands to the host the information is displayed at the bottom. Once this is done successfully, the right window displays the listing of directories and files found at the server while the left displays the directory tree. You should also get a "Transfer complete" message at the bottom.
The File Transfer Protocol
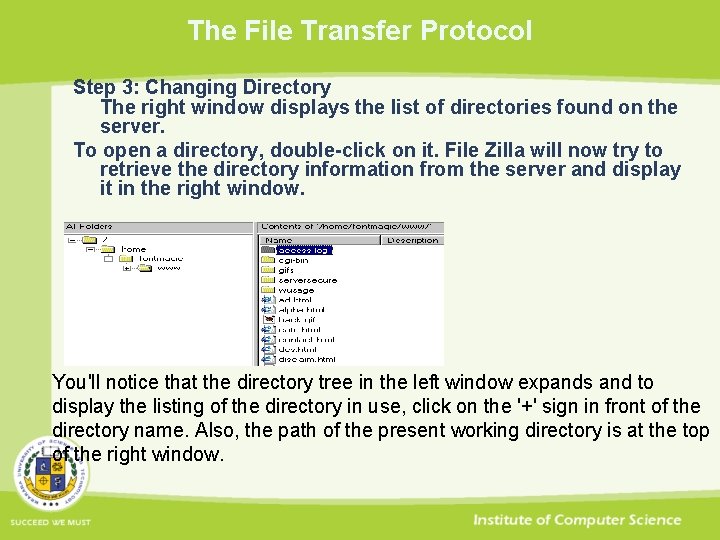
The File Transfer Protocol Step 3: Changing Directory The right window displays the list of directories found on the server. To open a directory, double-click on it. File Zilla will now try to retrieve the directory information from the server and display it in the right window. You'll notice that the directory tree in the left window expands and to display the listing of the directory in use, click on the '+' sign in front of the directory name. Also, the path of the present working directory is at the top of the right window.
The telnet Protocol
The telnet Protocol The Telnet protocol allows you to connect to another machine. Once connected, your computer behaves like a terminal of the distant machine and you can utilize all the resources on the remote system if you have the required permissions.
The telnet Protocol Telnet is a protocol that allows you connect to other computers on the Internet and use the resources present there. These resources can be online databases, chat services, programs etc. Each computer connected on the Internet has a unique address that helps to locate it. This is the IP (Internet Protocol) address. The address consists of a set of four numbers separated by periods. Thus, a typical address can be 10. 0. 1. The addresses can also be written in words www. must. ac. ug, which helps in easy recollection (by humans).
The telnet Protocol To telnet to a computer, you should know its IP address, username and password. Telnet is available on the Windows PC (XP users see the next paragraph). Click on the 'Start' Button and select 'Run'. Type telnet in the Pop-up window. The Telnet window now opens up. Select 'Remote system' from the 'Connect' drop down menu. Type in the remote computers' address. The remote machine will now ask for a username and password. Type these to login. Your local computer now acts as a terminal of the distant machine and you can use its resources including its processor power! Note: Some telnet services require you to connect only to a specific port on the remote computer. In such cases, you should also know the port number and append it to the IP address.
The telnet Protocol The Windows XP telnet window is slightly different. You have to click on the 'Start' button and then on 'Run'. Type telnet in the pop-up window. This should now start the telnet window with the prompt Microsoft Telnet>. To connect to a remote computer type, open sitename. To close the window, type quit at the telnet prompt. Note: The site-name can be the I. P. address of the remote computer, its domain name or the telnet host name.
The telnet Protocol The telnet program is also built into Unix systems. Just type telnet site-name at the prompt. You can use telnet from Macintosh computer employing a telnet client program. Telnet is useful not only to retrieve emails, information and run programs but can also play an important part in web site maintenance.
Use the following link to get access to a telnet server that you can use to telnet. http: //www. kpym. com/2/kpym/index. htm
Domain Name System
Domain Name System Most machines on the Internet use TCP/IP (Transmission Control Protocol/Internet Protocol) to send data to other machines on the Internet. To transmit data from a source to a destination, the Internet Protocol (IP) uses an IP address. An IP address is four bytes long, which consists of a network number and a host number. IP addresses are usually written using four numbers separated by periods; where each number can have one, two or three digits (e. g. 216. 27. 61. 137).
Domain Name System Every machine on the Internet has a unique identifying number, called an IP Address. A typical IP address looks like this: 216. 27. 61. 137 To make it easier for us humans to remember, IP addresses are normally expressed in decimal format as a "dotted decimal number" like the one above. But computers communicate in binary form. Look at the same IP address in binary: 11011000. 00011011. 00111101. 10001001 The four numbers in an IP address are called octets, because they each have eight positions when viewed in binary form. If you add all the positions together, you get 32, which is why IP addresses are considered 32 -bit numbers.
Domain Name System However, IP addresses are hard for human beings to remember don't reveal role, organisation or situation of Internet hosts Domain names provide such useful names for (sets of) Internet hosts. Internet uses DNS system to map domain names to IP addresses. DNS defined by RFC 1034 and RFC 1035 is hierarchical, domain based name space supported by distributed information system of DNS servers
Domain Name System Domain names are registered The Internet DNS consists of a directory, organized hierarchically, of all the domain names and their corresponding computers registered to particular companies and persons using the Internet. When you register a domain name, it will be associated with the computer on the Internet you designate during the period the registration is in effect. From that computer, you can create a website which will be accessible to Internet users around the world.
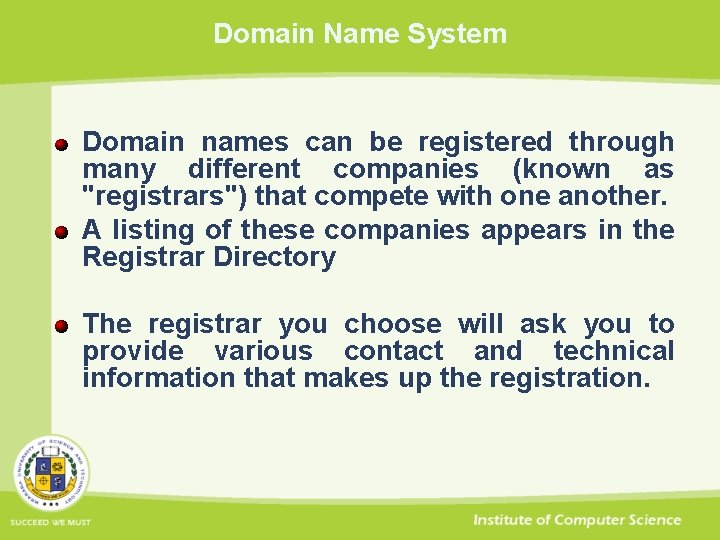
Domain Name System Domain names can be registered through many different companies (known as "registrars") that compete with one another. A listing of these companies appears in the Registrar Directory The registrar you choose will ask you to provide various contact and technical information that makes up the registration.
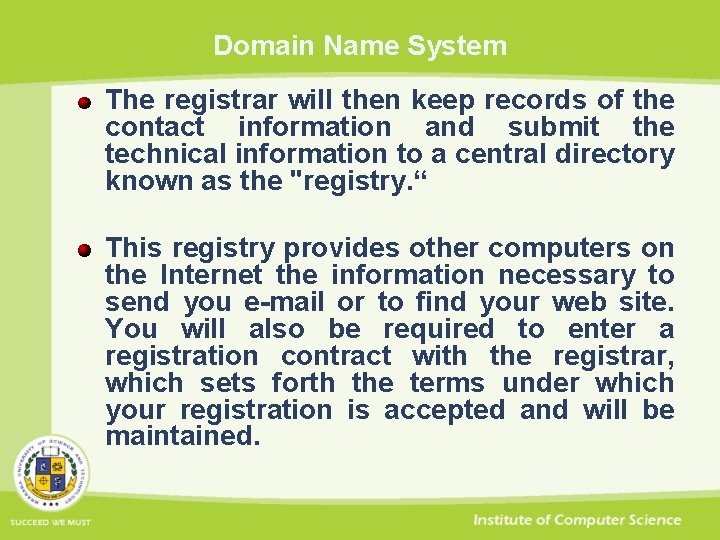
Domain Name System The registrar will then keep records of the contact information and submit the technical information to a central directory known as the "registry. “ This registry provides other computers on the Internet the information necessary to send you e-mail or to find your web site. You will also be required to enter a registration contract with the registrar, which sets forth the terms under which your registration is accepted and will be maintained.
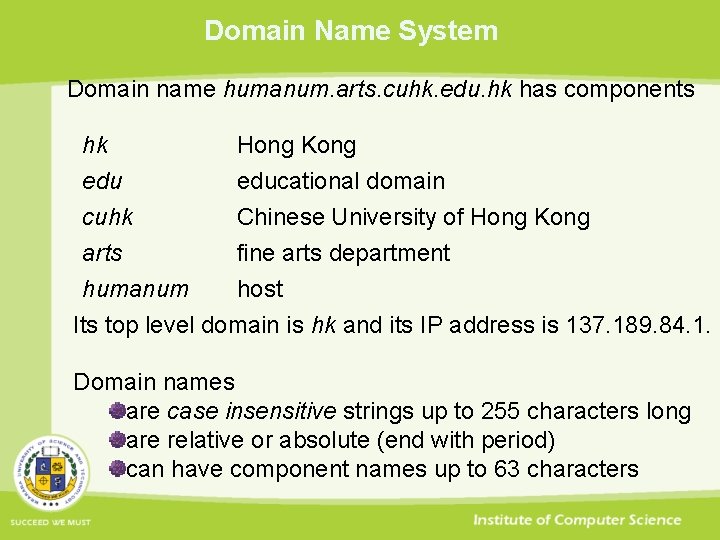
Domain Name System Domain name humanum. arts. cuhk. edu. hk has components hk edu cuhk arts Hong Kong educational domain Chinese University of Hong Kong fine arts department humanum host Its top level domain is hk and its IP address is 137. 189. 84. 1. Domain names are case insensitive strings up to 255 characters long are relative or absolute (end with period) can have component names up to 63 characters
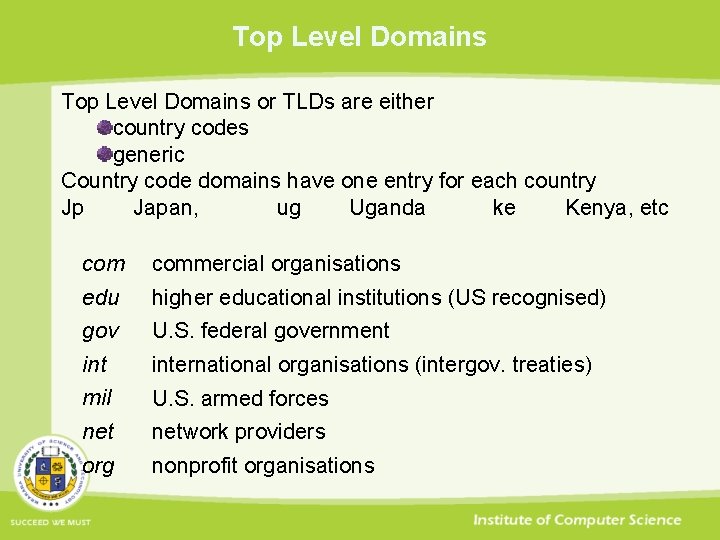
Top Level Domains or TLDs are either country codes generic Country code domains have one entry for each country Jp Japan, ug Uganda ke Kenya, etc commercial organisations edu higher educational institutions (US recognised) gov U. S. federal government international organisations (intergov. treaties) mil U. S. armed forces network providers org nonprofit organisations

Top Level Domains ICANN has introduced 11 other generic top level domains aero aircraft product makers & airline service providers biz firms and businesses cat Catalan linguistic & cultural community cooperative organisations information publishers (no restrictions) jobs human resource managers mobi consumers & providers of mobile products & services museum & cultural heritage organisations name individuals pro credentialed professionals & professional bodies travel industry
Top Level Domains TLDs such as. asia, . mail, . post, . tel, . xxx are being proposed. Inter. NIC records ICANN accredited DNS registrars for TLDs. ICANN operates uniform domain name dispute resolution policy based on impartial arbitration by 1 or 3 person panel judged on written or online submission that responds within 20 days Grounds of complaints about domain names include name is same/confusingly similar to trademark/service mark registering party has no rights or legitimate interests in it name has been registered and used in bad faith
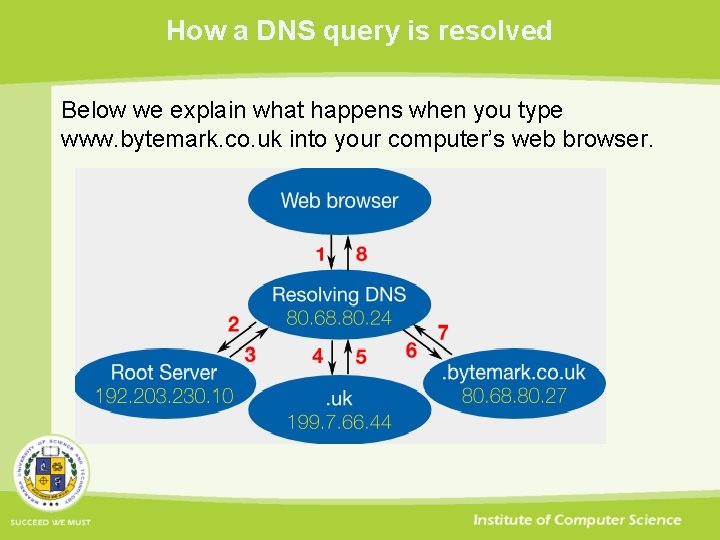
How a DNS query is resolved Below we explain what happens when you type www. bytemark. co. uk into your computer’s web browser.
How a DNS query is resolved Your web browser asks the resolving DNS server what the address of www. bytemark. co. uk is. Your computer already knows where the local resolving DNS server is through its network configuration. For customers on the Bytemark network, the resolving DNS servers are 80. 68. 80. 24 and 80. 68. 80. 25. The Resolving DNS server does not know the address. So it asks a root server the same question. The 13 root servers have globally well-known IP addresses, and are run by a US-based company called ICANN The root server replies that it does not know, but it gives the address of the server which knows about. uk domains. All UK domains are managed by a non-profit organisation called Nominet The resolving DNS server asks the. uk server what the address of www. bytemark. co. uk is.
How a DNS query is resolved The. uk server replies that it does not know, but it gives the address of the server which knows about. bytemark. co. uk domain. This server is (finally!) at an IP address which we manage, on one of our servers. We pay Nominet an annual fee (via a domain registar) to maintain this referral for our domain, and for them to maintain the address as belonging to us. The resolving DNS server asks the. bytemark. co. uk server what the address of www. bytemark. co. uk is. Our server answers the query with the IP address of www. bytemark-hosting. co. uk, and marks the response as “authoratitve”. This is an assertion that the answer is correct and complete. It also adds to its reply that “this data is valid for 24 hours”, so that anyone who is asking can confidently re-use the information for that time without having to issue another query.
How a DNS query is resolved The resolving DNS server finally has its answer, and can reply back to the web browser with the IP address. Crucially it marks its answer as “non-authoratitive”, so that the web browser knows it has the information indirectly.
- Slides: 112