Internet and Intranets Chapter 11 By Stephen Harris
Internet and Intranets Chapter 11 By Stephen Harris
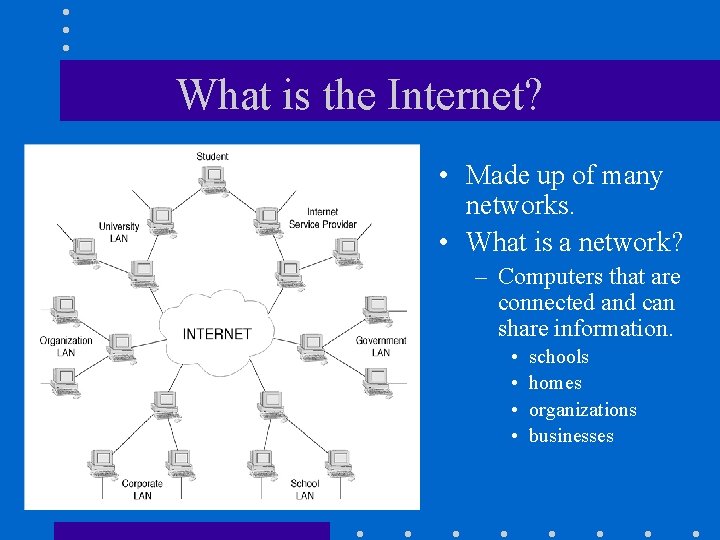
What is the Internet? • Made up of many networks. • What is a network? – Computers that are connected and can share information. • • schools homes organizations businesses
Types of networks: • Wide Area Network (WAN) – Connects computers over a large geographic area, such as a city, county or country. – Usually found on a much smaller area, such as a college campus. • Local Area Network (LAN) – Connects individual computers to one another. – Could be a network within a lab or a single building.
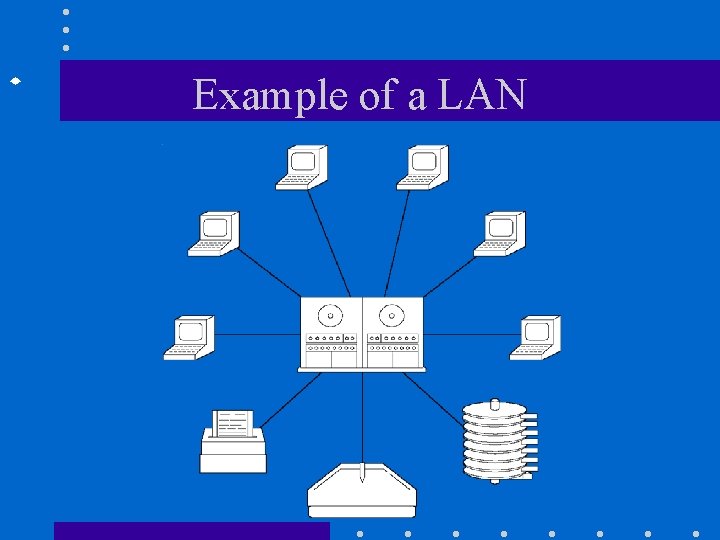
Example of a LAN
How do I connect to the Internet? • You will need a modem. – Modem and phone. – Cable modem. • You will need an Internet Service Provider (ISP)
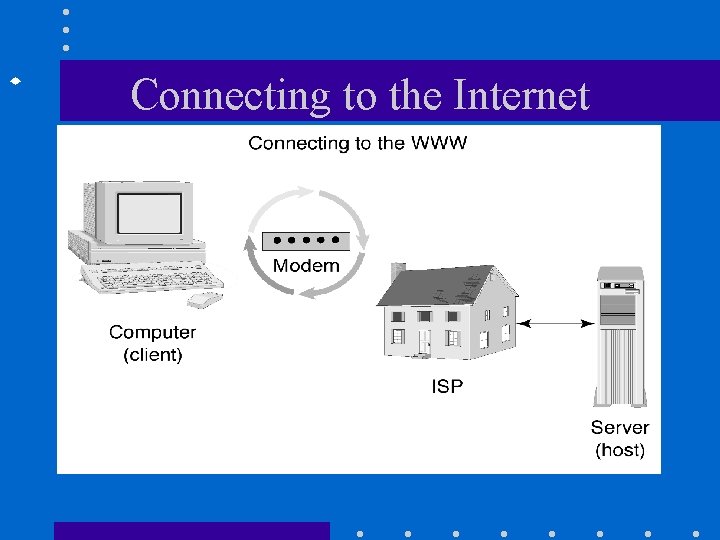
Connecting to the Internet
What can I do on the Internet? • • Electronic mail. • Search for information. – Yahoo is a good Bulletin boards subject catalog. Chatrooms – Altavista is a search Audio engine. communications. • Video communications.
How do I use email? • Unique ID – each user on the internet has a unique address. – example: ga_harris@yahoo. com • “ga_harris” is the name. • “yahoo” is the computer network. • “com” is the type of organization.
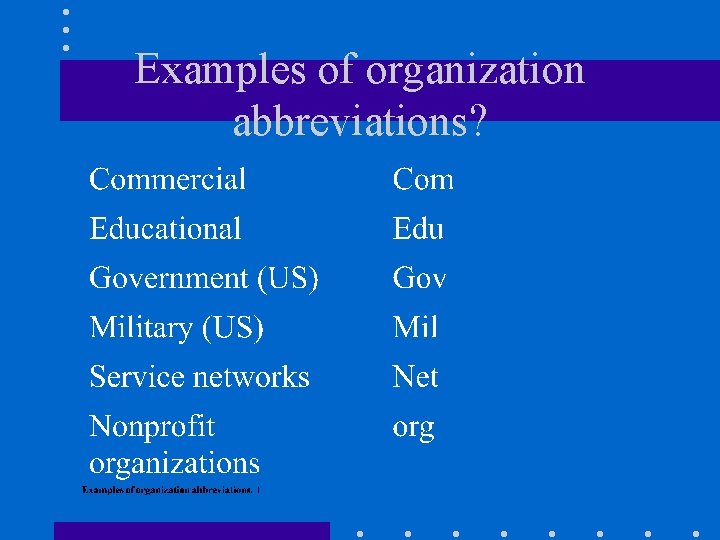
Examples of organization abbreviations?
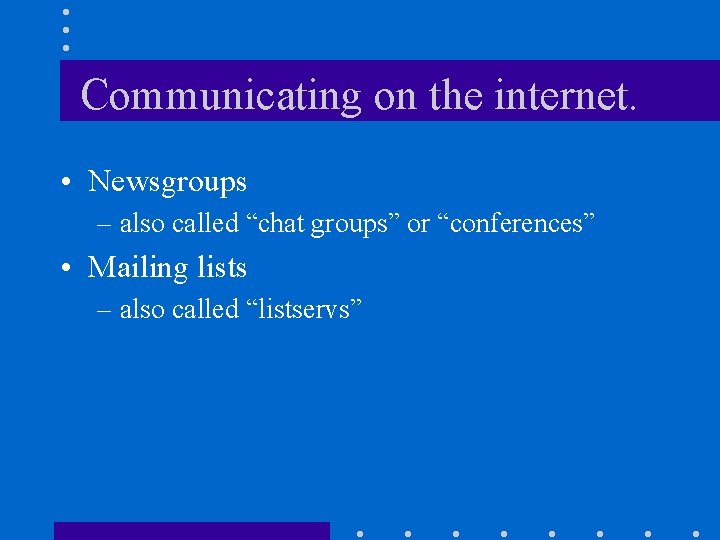
Communicating on the internet. • Newsgroups – also called “chat groups” or “conferences” • Mailing lists – also called “listservs”
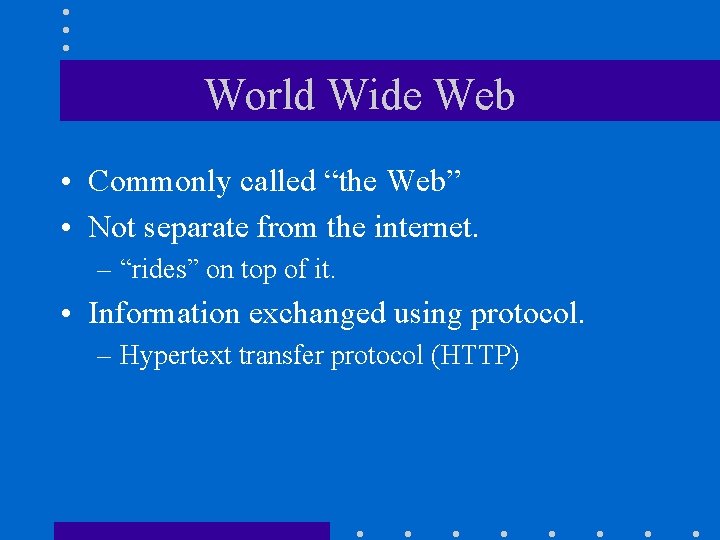
World Wide Web • Commonly called “the Web” • Not separate from the internet. – “rides” on top of it. • Information exchanged using protocol. – Hypertext transfer protocol (HTTP)
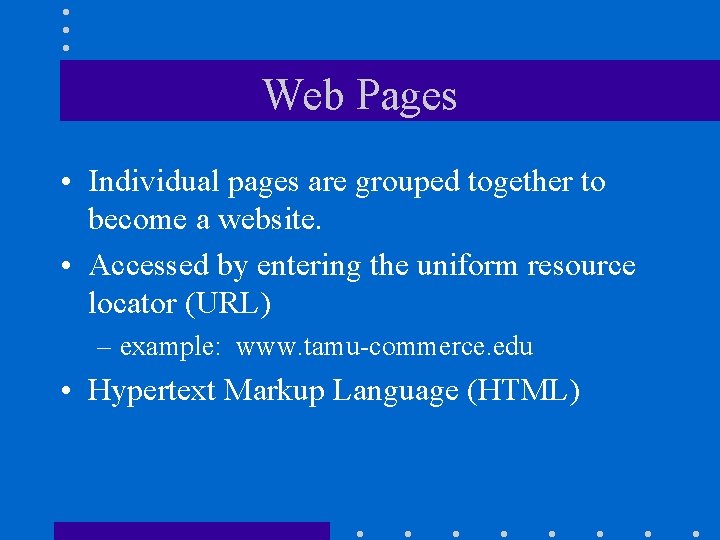
Web Pages • Individual pages are grouped together to become a website. • Accessed by entering the uniform resource locator (URL) – example: www. tamu-commerce. edu • Hypertext Markup Language (HTML)
Hypertext Markup Language HTML • Set of formatting commands. • Requires programs to read. – Examples: • Internet Explorer • Netscape • Software available to create pages. – Example: Microsoft Frontpage
What is an Intranet? • Internal network for companies or schools. • Allows remote access via dialing in to network. • Unwanted users controlled via “firewall. ”
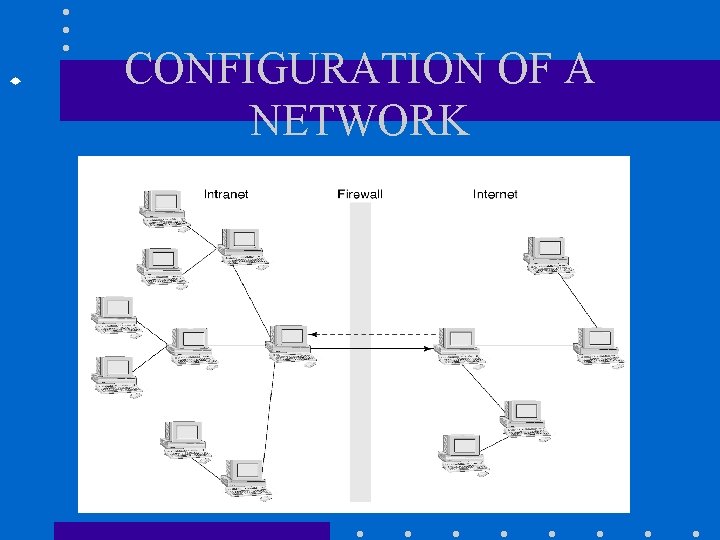
CONFIGURATION OF A NETWORK
ASSURE • • • MODEL Analyze Learners State Objectives Select Methods, Media, and Materials Utilize Media and Materials Require Learner Participation Evaluate and Revise
- Slides: 16