Intentional Access Management Making Access Control Usable for
Intentional Access Management: Making Access Control Usable for End-Users Xiang Cao January 24, 2006
Background n Context q n Need q n Shared file-systems as collaborative infrastructure Fine-grained, user-centered, dynamic control of sharing to match trust & ad-hoc collaboration Solution q q End-user management of resource sharing Minimal changes to backend infrastructure 2
Human Factors n “Security is only as good as its weakest link, and people are the weakest link in the chain. ” (B. Schneier, Secrets and Lies, 2000) n Configuration errors -> 90% security failures (Bishop, 1996) 3
Recognition of the Need to Align Security and Usability n n n CRA 2003 “Grand Challenge” PITAC 2005 “priority” Special publications q q n [IEEE Security & Privacy 2004] [Security and Usability, O’Reilly 2005] CHI 2003; WUPSS 2004; CHI 2005; SOUPS 2005 4
Characteristics of End-Users n Security q A secondary task (Whitten and Tygar 1999) q Not an everyday task n Limited technical capacity n Little security knowledge 5
The Gaps n Gap 1: Complexity q q n User interest + expertise (low to non-existent) Task complexity (high) (I will demonstrate!) Gap 2: Intention => Implementation q q Even for simple needs (intentions) e. g. , Lee needs to be able to edit my thesis draft User must be able to: n n Assess state of system: is the intention already fulfilled? Determine how to modify configuration to fulfill intention 6
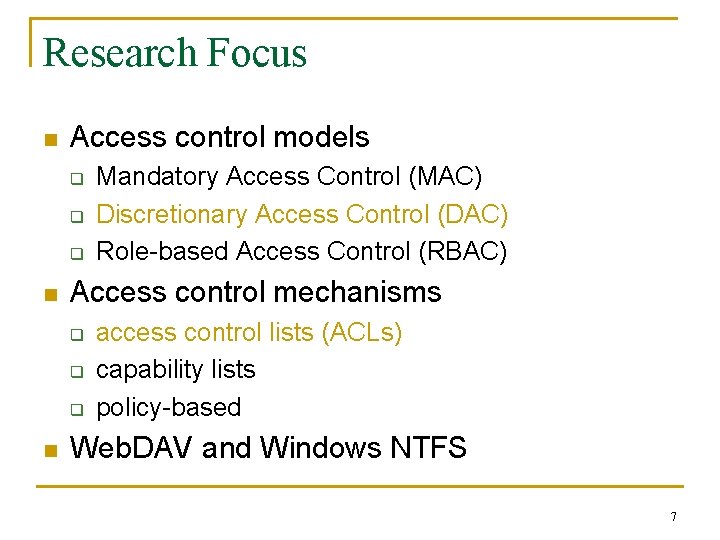
Research Focus n Access control models q q q n Access control mechanisms q q q n Mandatory Access Control (MAC) Discretionary Access Control (DAC) Role-based Access Control (RBAC) access control lists (ACLs) capability lists policy-based Web. DAV and Windows NTFS 7
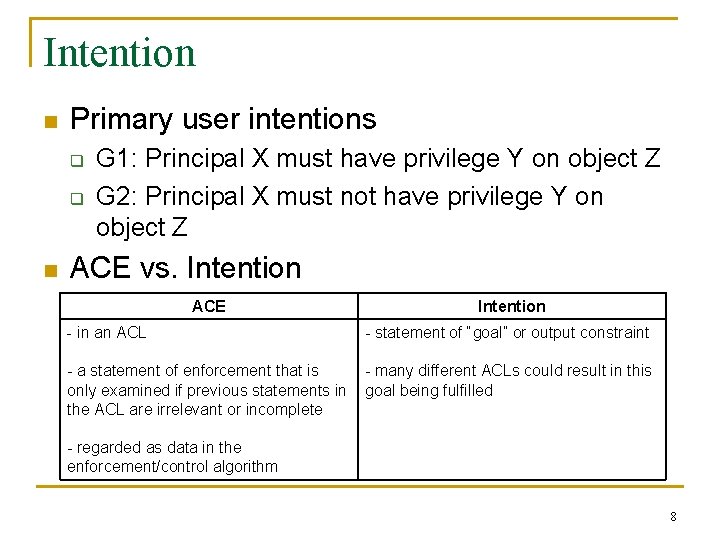
Intention n Primary user intentions q q n G 1: Principal X must have privilege Y on object Z G 2: Principal X must not have privilege Y on object Z ACE vs. Intention ACE Intention - in an ACL - statement of “goal” or output constraint - a statement of enforcement that is only examined if previous statements in the ACL are irrelevant or incomplete - many different ACLs could result in this goal being fulfilled - regarded as data in the enforcement/control algorithm 8
Task Analysis n Norman/THEA models: q q Perceive and interpret information from the environment, and evaluate whether the problem is solved If the problem remains unsolved, formulate a subgoal, according to perceived information, for solving all or part of the problem; if the problem is solved, exit the loop Formulate a plan to achieve the subgoal Execute the actions in the plan 9
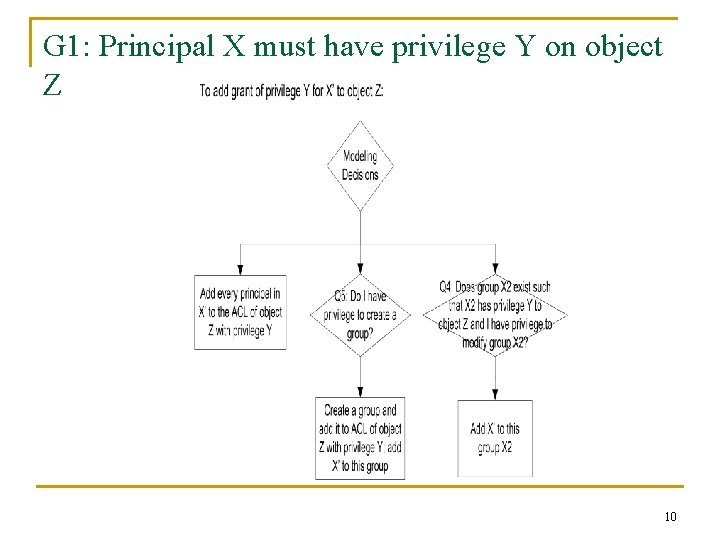
G 1: Principal X must have privilege Y on object Z 10
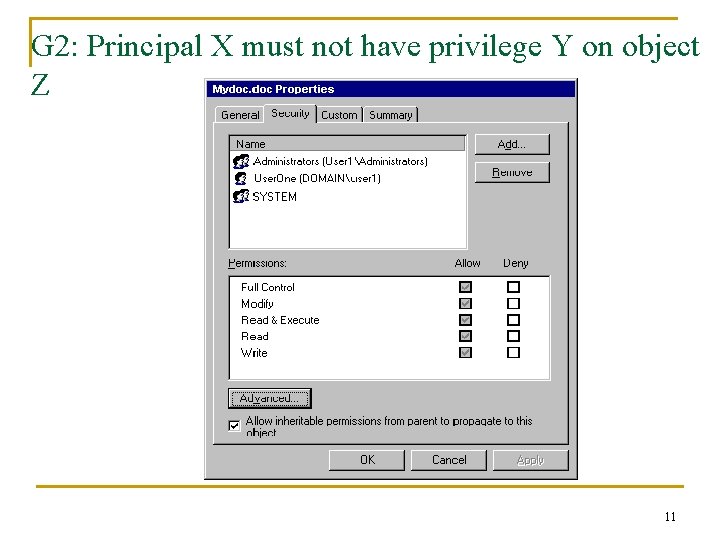
G 2: Principal X must not have privilege Y on object Z 11
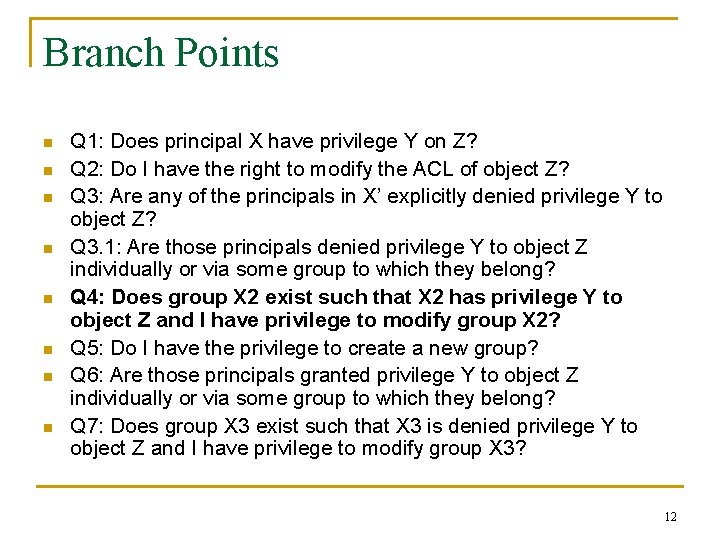
Branch Points n n n n Q 1: Does principal X have privilege Y on Z? Q 2: Do I have the right to modify the ACL of object Z? Q 3: Are any of the principals in X’ explicitly denied privilege Y to object Z? Q 3. 1: Are those principals denied privilege Y to object Z individually or via some group to which they belong? Q 4: Does group X 2 exist such that X 2 has privilege Y to object Z and I have privilege to modify group X 2? Q 5: Do I have the privilege to create a new group? Q 6: Are those principals granted privilege Y to object Z individually or via some group to which they belong? Q 7: Does group X 3 exist such that X 3 is denied privilege Y to object Z and I have privilege to modify group X 3? 12
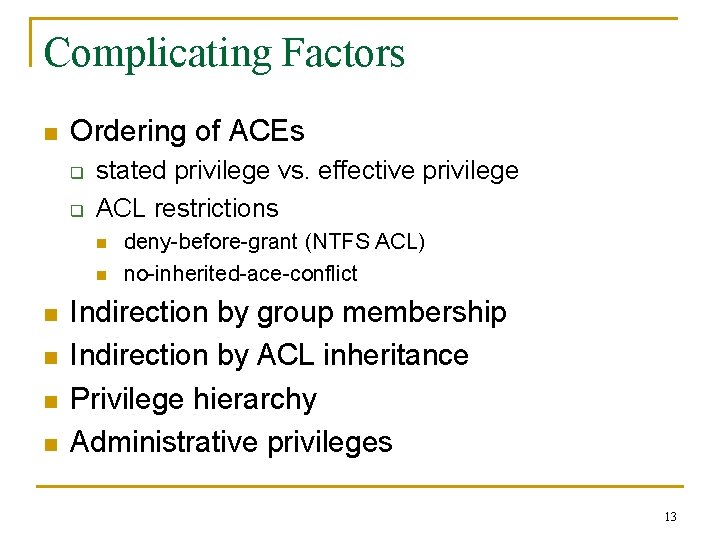
Complicating Factors n Ordering of ACEs q q stated privilege vs. effective privilege ACL restrictions n n n deny-before-grant (NTFS ACL) no-inherited-ace-conflict Indirection by group membership Indirection by ACL inheritance Privilege hierarchy Administrative privileges 13
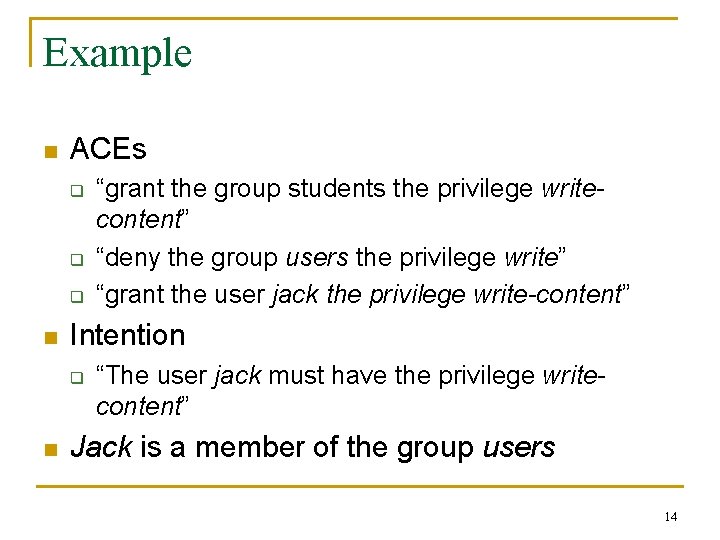
Example n ACEs q q q n Intention q n “grant the group students the privilege writecontent” “deny the group users the privilege write” “grant the user jack the privilege write-content” “The user jack must have the privilege writecontent” Jack is a member of the group users 14
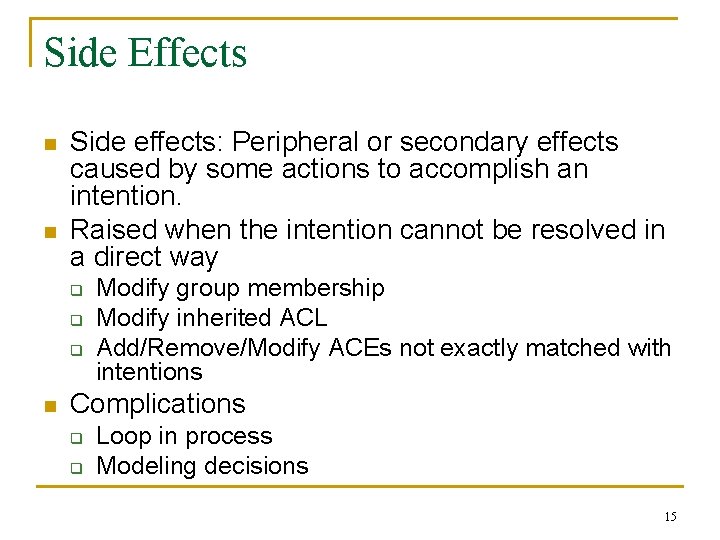
Side Effects n n Side effects: Peripheral or secondary effects caused by some actions to accomplish an intention. Raised when the intention cannot be resolved in a direct way q q q n Modify group membership Modify inherited ACL Add/Remove/Modify ACEs not exactly matched with intentions Complications q q Loop in process Modeling decisions 15
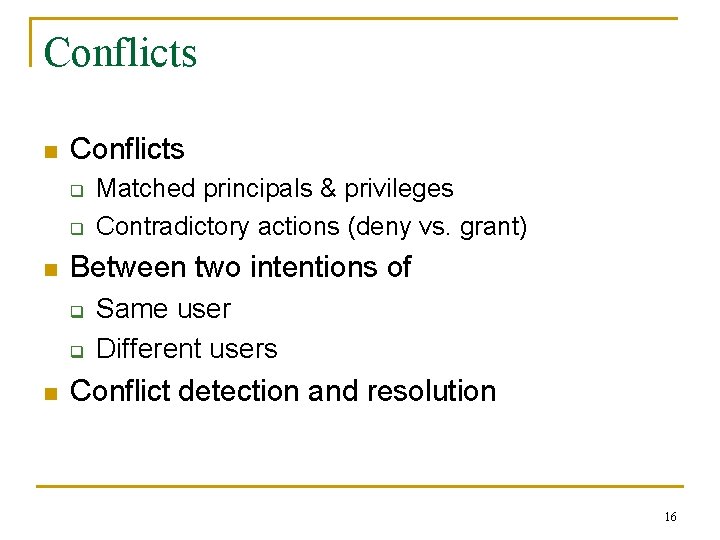
Conflicts n Conflicts q q n Between two intentions of q q n Matched principals & privileges Contradictory actions (deny vs. grant) Same user Different users Conflict detection and resolution 16
Summary of the Analysis n n Gulfs of execution and evaluation * Algorithmic relationship between the goal and ACL configuration changes q n n Incremental changes Direct manipulation A higher level of abstraction based on effects * Norman, Donald A. (1988): The Design of Everyday Things. New York, Doubleday 17
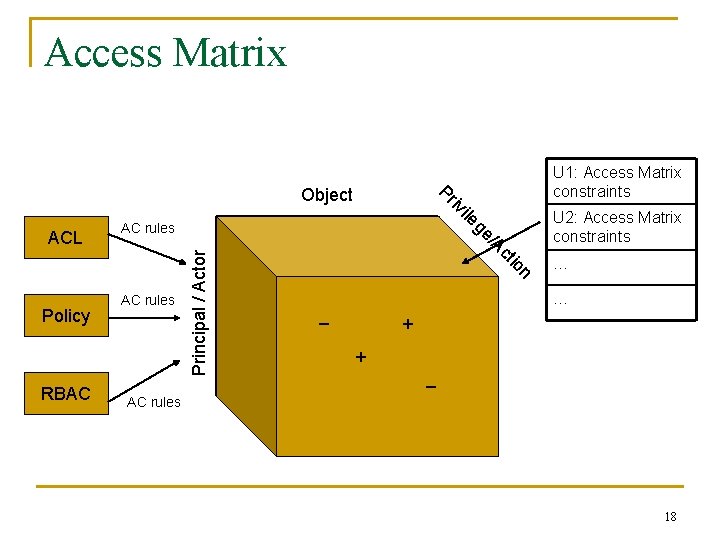
Access Matrix read write n io Principal / Actor ct RBAC /A Policy AC rules read ge ACL AC rules le i iv Pr Object U 1: Access Matrix constraints U 2: Access Matrix constraints … … _ + + _ AC rules 18
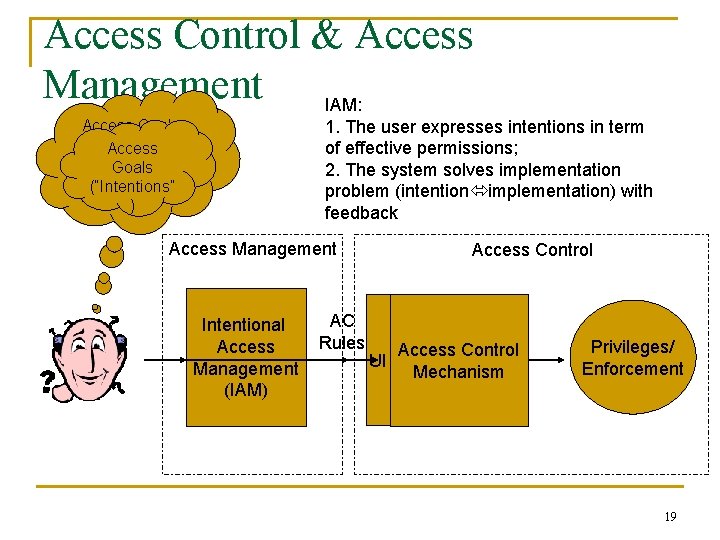
Access Control & Access Management IAM: 1. The user expresses intentions in term of effective permissions; 2. The system solves implementation problem (intention implementation) with feedback Access Goals (“Intentions”) Access || Goals V (“Intentions” AC Rules ) Access Management Intentional Access Management (IAM) AC Rules Access Control UI Access Control Mechanism Privileges/ Enforcement 19
Hypothesis n Intentional Access Management will make the access control system easier to use q q q A level of abstraction matching end-users’ goals No need to learn the access control mechanisms Reduction of the task’s conceptual complexity Accuracy improvement Speed improvement User satisfaction improvement 20
Design Principles n User decisions should be made/requested in an environment where q q n the user has access to essential information needed to make the decision reliably; (Yee’s Principle of Visibility) the system is responsible for predicting and presenting such information when it can. (Yee’s Principle of Clarity) Manipulation in terms of effective permissions Related projects: Zurko (MAP & Adage), Maxion and Reeder (Salmon) 21
Basic IAM – IAM Wizard n n The user initiates interaction with the system by expressing an intention in terms of an output constraint on the access control system; The system translates these intentions into implementation; The system follows Yee’s principles of clarity and visibility in informing the user of the consequences of actions not directly implied by their intentions; and The system informs the user of modeling variations as well as detected ambiguities and conflicts in intentions. 22
Full IAM n n Maintenance of intentions for each user; The ability to retract previous intentions; Maintenance of connections between intentions and implementation actions; and Management of conflicts by initiating user interactions to resolve conflicts. 23
Full IAM (cont’d) 24

Multi-Backend IAM 25
Pros & Cons n Pros q q n A level of abstraction matching end-users’ goals No need to change the deployed backends/enforcement models Ability to resolve conflicts Ability to resolve reflexive needs (“”self-grant”) Cons q Burden on users for tracking and managing intentions over time 26
Implementation: IAM Wizard for Web. DAV n Server: Slide n Client: DAV Explorer q q Existing: ACL Editor New module: IAM Wizard 27
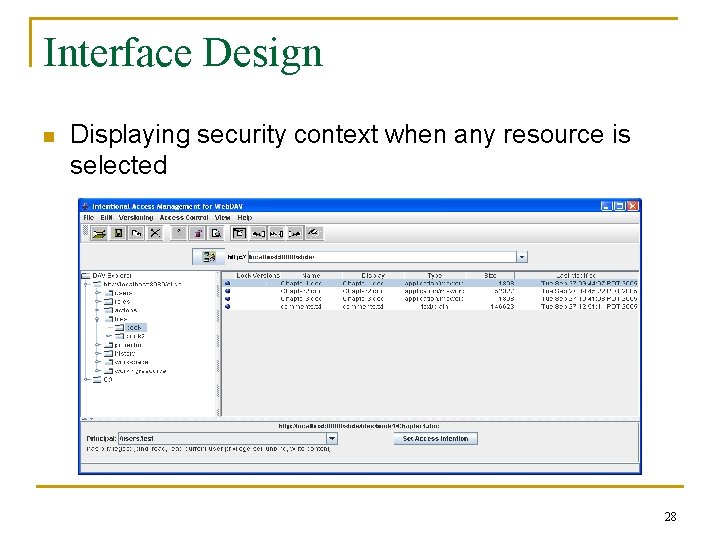
Interface Design n Displaying security context when any resource is selected 28
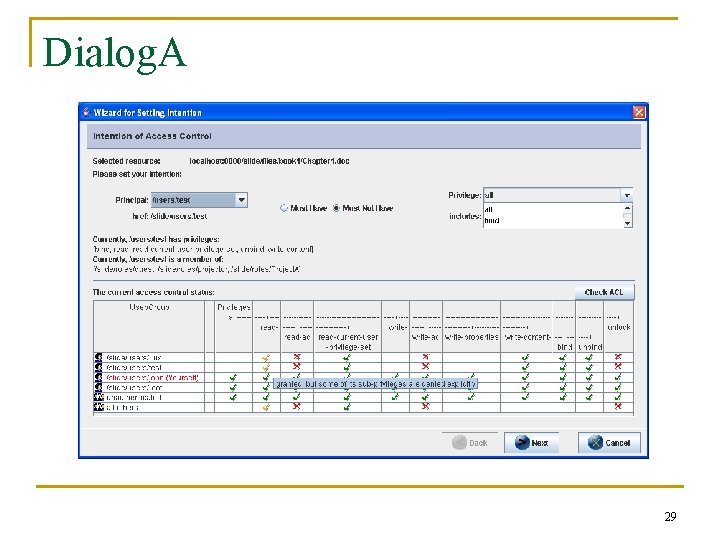
Dialog. A 29
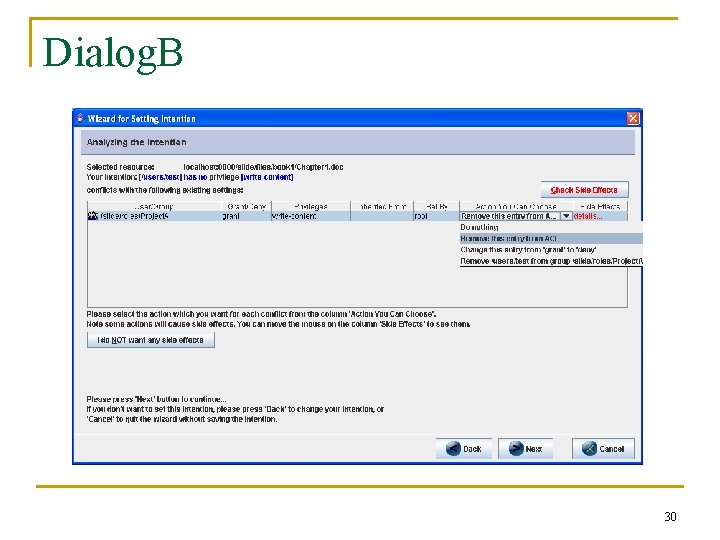
Dialog. B 30
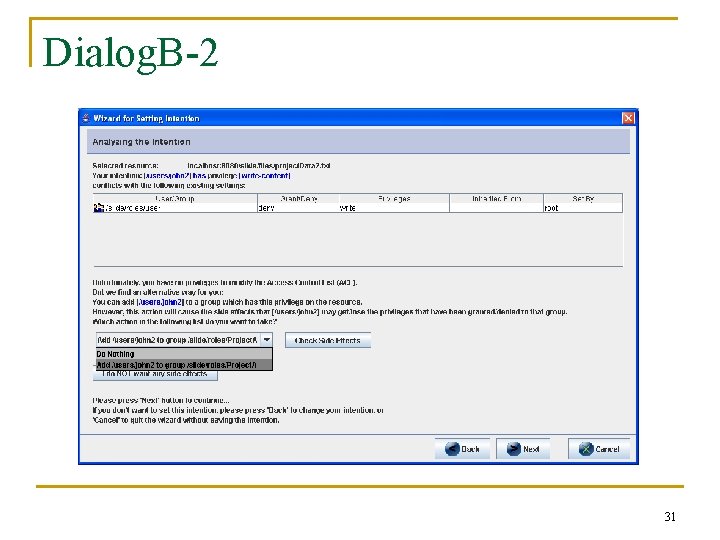
Dialog. B-2 31
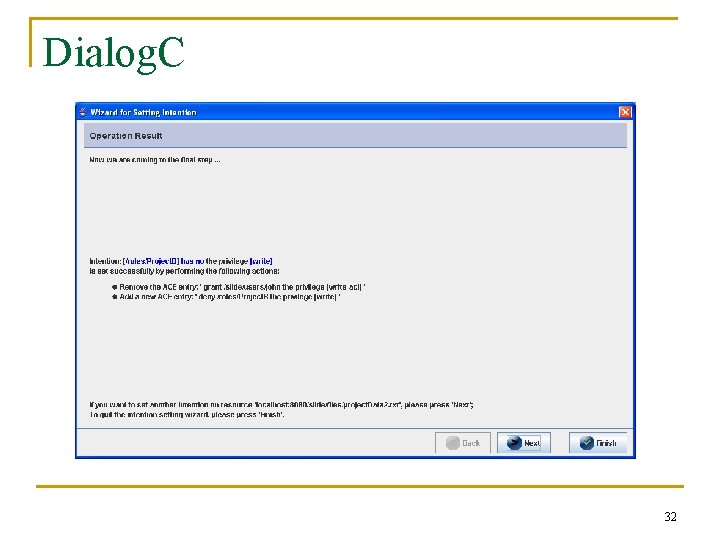
Dialog. C 32
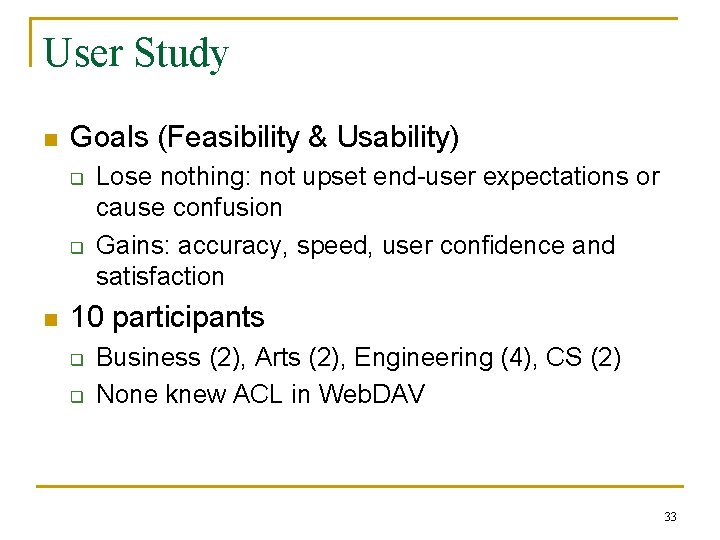
User Study n Goals (Feasibility & Usability) q q n Lose nothing: not upset end-user expectations or cause confusion Gains: accuracy, speed, user confidence and satisfaction 10 participants q q Business (2), Arts (2), Engineering (4), CS (2) None knew ACL in Web. DAV 33
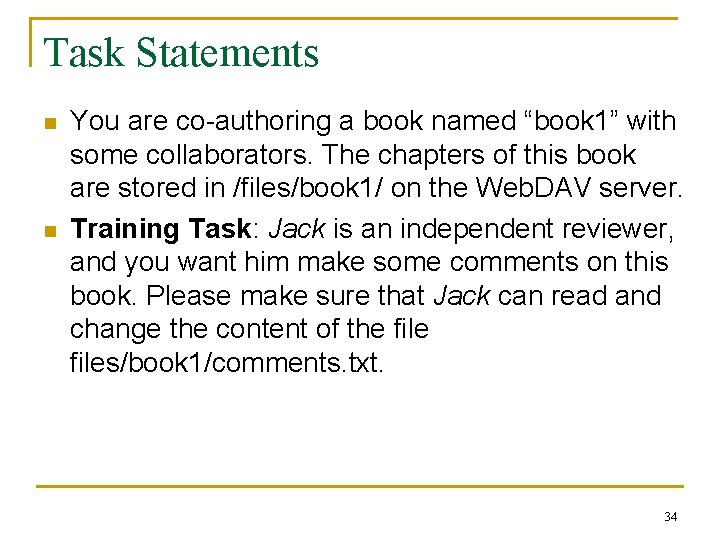
Task Statements n n You are co-authoring a book named “book 1” with some collaborators. The chapters of this book are stored in /files/book 1/ on the Web. DAV server. Training Task: Jack is an independent reviewer, and you want him make some comments on this book. Please make sure that Jack can read and change the content of the files/book 1/comments. txt. 34
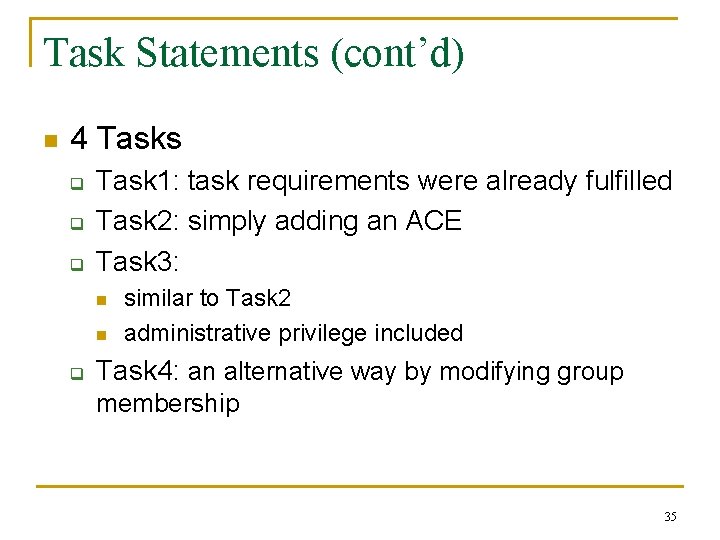
Task Statements (cont’d) n 4 Tasks q q q Task 1: task requirements were already fulfilled Task 2: simply adding an ACE Task 3: n n q similar to Task 2 administrative privilege included Task 4: an alternative way by modifying group membership 35
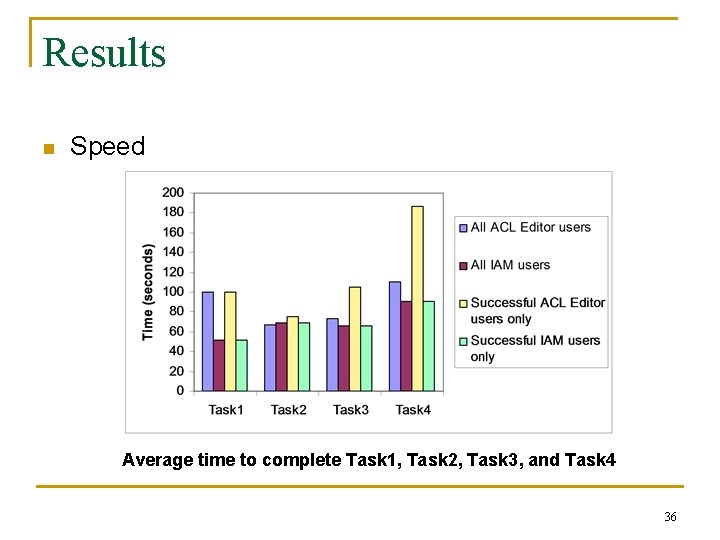
Results n Speed Average time to complete Task 1, Task 2, Task 3, and Task 4 36
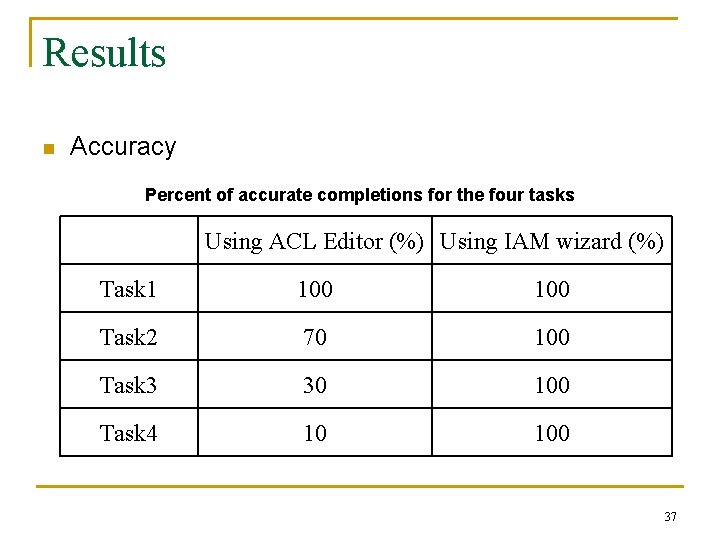
Results n Accuracy Percent of accurate completions for the four tasks Using ACL Editor (%) Using IAM wizard (%) Task 1 100 Task 2 70 100 Task 3 30 100 Task 4 10 100 37
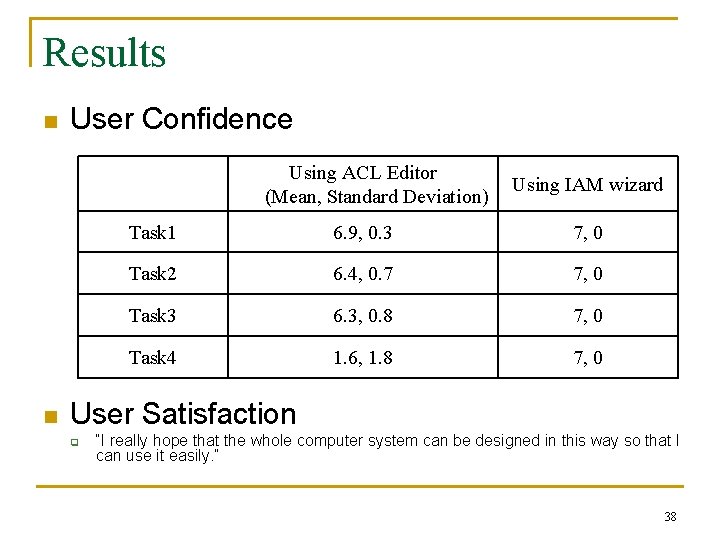
Results n User Confidence Using ACL Editor (Mean, Standard Deviation) n Using IAM wizard Task 1 6. 9, 0. 3 7, 0 Task 2 6. 4, 0. 7 7, 0 Task 3 6. 3, 0. 8 7, 0 Task 4 1. 6, 1. 8 7, 0 User Satisfaction q “I really hope that the whole computer system can be designed in this way so that I can use it easily. ” 38
Achievements n Conceptual change: q q q n Intentional analysis q q n n n directly accommodates users’ task-oriented goals Bridges both the “gulf of evaluation” and “gulf of execution” A high level of abstraction algorithmic relationship between the goal and configuration side effects conflicts modeling decisions IAM models: Wizard, Full, Multi-backend Implementation: IAM Wizard for Web. DAV User study 39
Future Work n Better model of necessary user intentions q n Presentation of privileges in task-oriented terms Full and Multi-backend IAMs q q Resolution of conflicts Presentation and exploration of side effects Interactions with multiple systems Interactions with system administrative actions 40
Q&A Thank You ! 41
42

Philosophy n n n End-user are not security experts They may not understand the complex security mechanisms Therefore, let’s provide usable and powerful security decision support tools to help them control their information more effectively 43
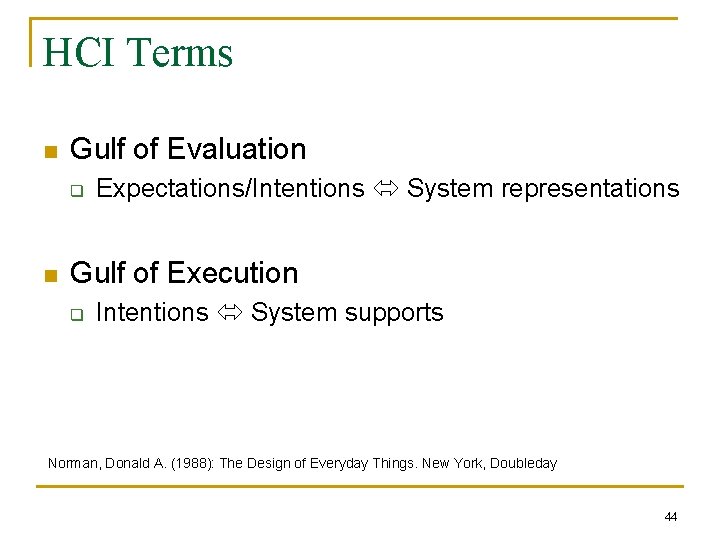
HCI Terms n Gulf of Evaluation q n Expectations/Intentions System representations Gulf of Execution q Intentions System supports Norman, Donald A. (1988): The Design of Everyday Things. New York, Doubleday 44
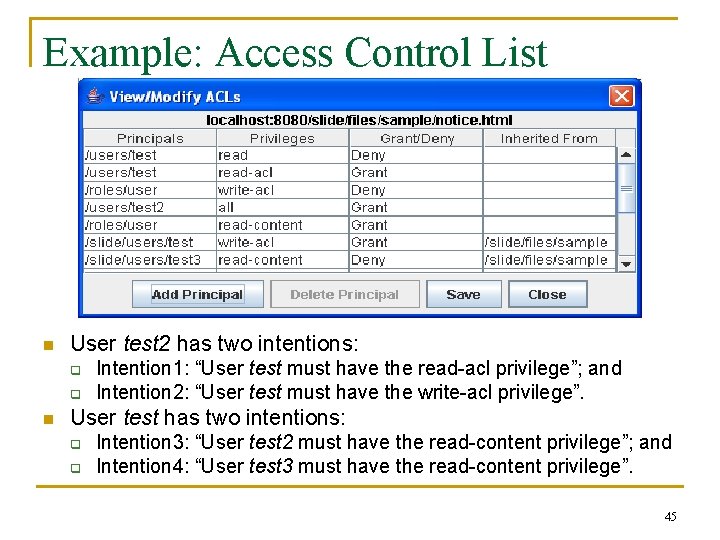
Example: Access Control List n User test 2 has two intentions: q q n Intention 1: “User test must have the read-acl privilege”; and Intention 2: “User test must have the write-acl privilege”. User test has two intentions: q q Intention 3: “User test 2 must have the read-content privilege”; and Intention 4: “User test 3 must have the read-content privilege”. 45
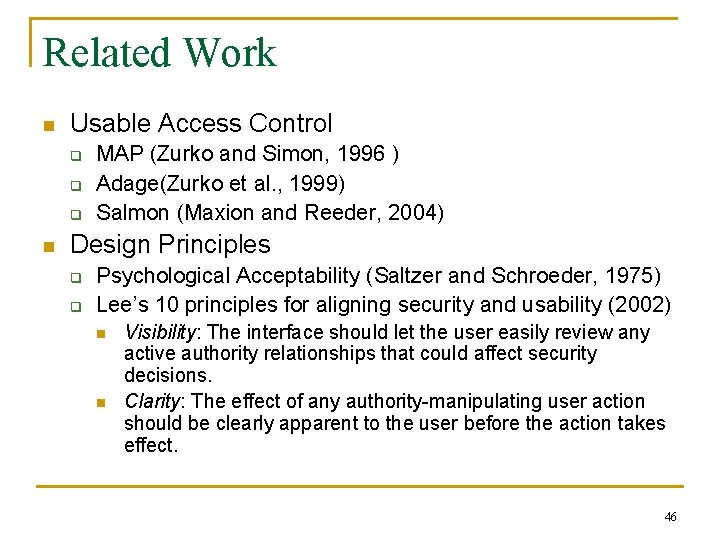
Related Work n Usable Access Control q q q n MAP (Zurko and Simon, 1996 ) Adage(Zurko et al. , 1999) Salmon (Maxion and Reeder, 2004) Design Principles q q Psychological Acceptability (Saltzer and Schroeder, 1975) Lee’s 10 principles for aligning security and usability (2002) n n Visibility: The interface should let the user easily review any active authority relationships that could affect security decisions. Clarity: The effect of any authority-manipulating user action should be clearly apparent to the user before the action takes effect. 46
General HCI principle n The conceptual complexity of a task should not exceed the user’s commitment to that task 47
Task Analysis (cont’d) n n n Assess the current state of the system Decide whether or not the goal is already fulfilled Develop a strategy to decide how to minimally achieve the goal state given the current system state. 48
Modeling Decisions 49
Web. DAV Access Control n n Web. DAV: Web-based Distributed Authoring and Versioning Web. DAV Access Control (Superset of NTFS ACL) q q q n Principal Privilege Resource ACL Evaluation q q ordered ACEs stated privilege vs. effective privilege 50
Windows NTFS Access Control n n n Deny-before-grant Ownership Permissions on files and folders 51

ACL Editor 52
IAM Wizard 53
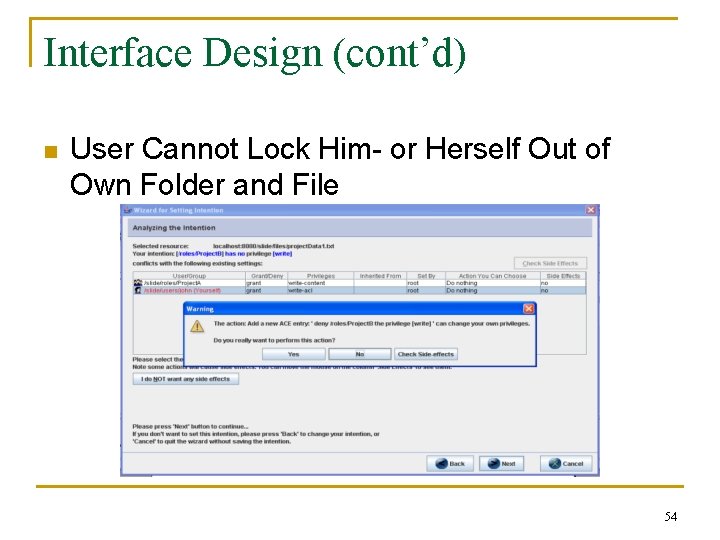
Interface Design (cont’d) n User Cannot Lock Him- or Herself Out of Own Folder and File 54
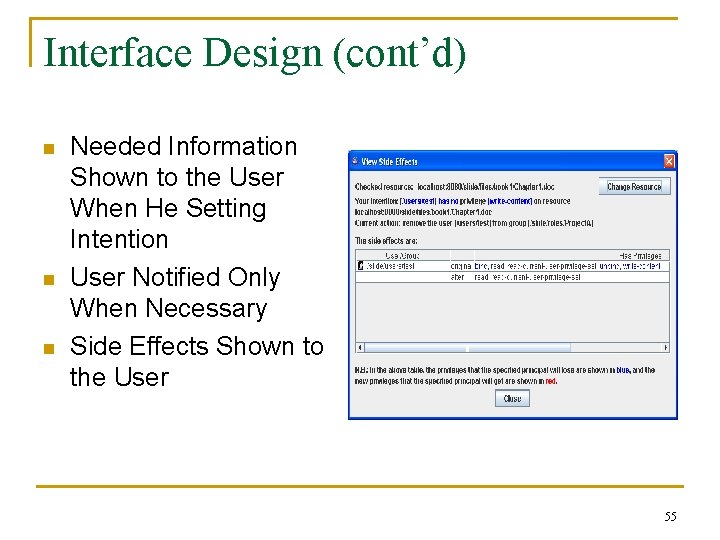
Interface Design (cont’d) n n n Needed Information Shown to the User When He Setting Intention User Notified Only When Necessary Side Effects Shown to the User 55
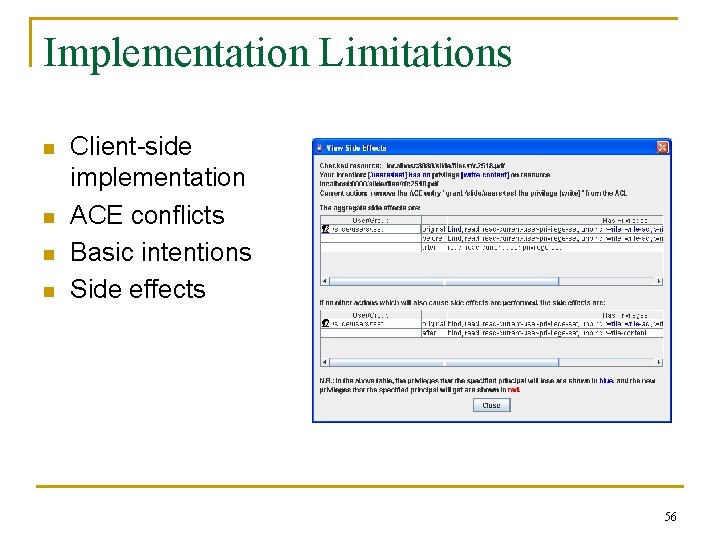
Implementation Limitations n n Client-side implementation ACE conflicts Basic intentions Side effects 56
Definition of Usability * n n n Ease of learning Efficiency of use Memorability Error frequency and severity Subjective satisfaction *Adopted by US Department of Health and Human Services 57
Participants n 10 participants q n Frequency of using computers q n have (8), never (2) Familiarity with ACL and its evaluation q n daily (8), a few times a week (2) Experience of setting file permissions q n Business (2), Arts (2), Engineering (4), CS (2) average (2), know a little (5), don’t know at all (3) None knew ACL in Web. DAV 58
Procedure n Tasks 1, 2, 3: q q n Task 4: q n n 8 - The ACL Editor first, and then the IAM wizard 2 -The IAM wizard first, and then the ACL Editor The ACL Editor first, and then the IAM wizard Learn ACL evaluation before using the ACL Editor Rate confidence on correctness after each task 59
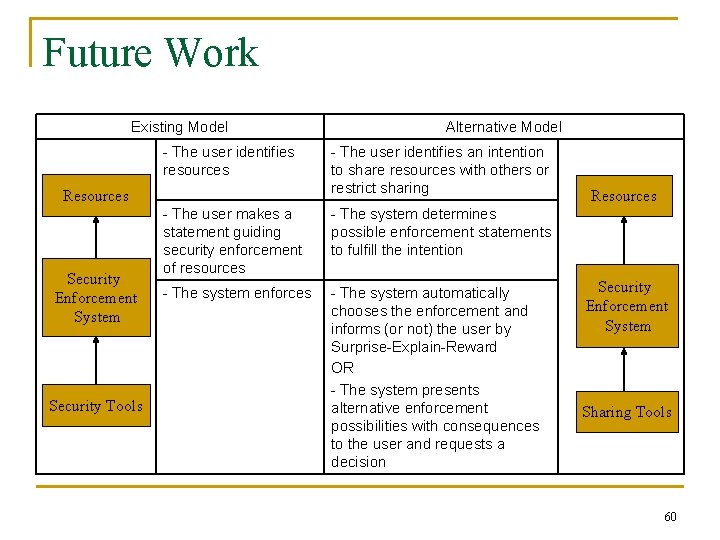
Future Work Existing Model - The user identifies resources Resources Security Enforcement System Security Tools Alternative Model - The user identifies an intention to share resources with others or restrict sharing - The user makes a statement guiding security enforcement of resources - The system determines possible enforcement statements to fulfill the intention - The system enforces - The system automatically chooses the enforcement and informs (or not) the user by Surprise-Explain-Reward OR - The system presents alternative enforcement possibilities with consequences to the user and requests a decision Resources Security Enforcement System Sharing Tools 60
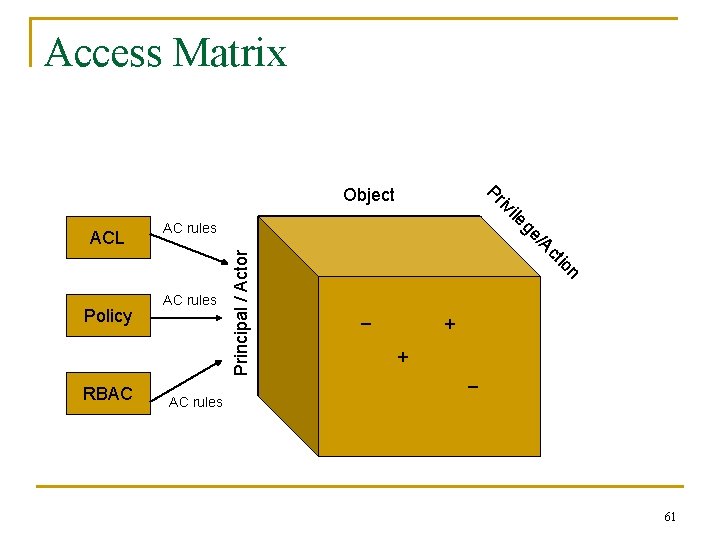
Access Matrix read write n Principal / Actor io ct RBAC AC rules read /A Policy AC rules ge ACL ile iv Pr Object _ + + _ AC rules 61
- Slides: 61