Integrity of multimedia data Techniques for digital watermarking

- Slides: 21
Integrity of multimedia data ●Techniques for digital watermarking ●An example in the Wavelet domain ●Experimental results: evaluation
Watermarking ●Basic idea To insert a invisibile structure (watermark) inside a «host» signal in order to mark it ●Result ü Author identification ü Which alteration? Which quality? ü Evalutaion of the similarity between the original and teh altered data

Applications Applicazioni Copyright Protection E-commerce Video-on-demand Authentication E-commerce forensic Multimedia distributuion Hidden annotation medical imaging cartograpgy indexing & retrievial Secret communication Military and intelligence Alternatives to cryprography
Example ●Method ü Request analysis ü Choice of watermarking techniques ü Improvements on the state-of-theart
Method ● «musts» ü Do not compromise the image quality ü Capable to reveal unauthorized modification üJPEG 2000 compression is «legal» ü unauthorized modifications are difficult ü To localize altered area
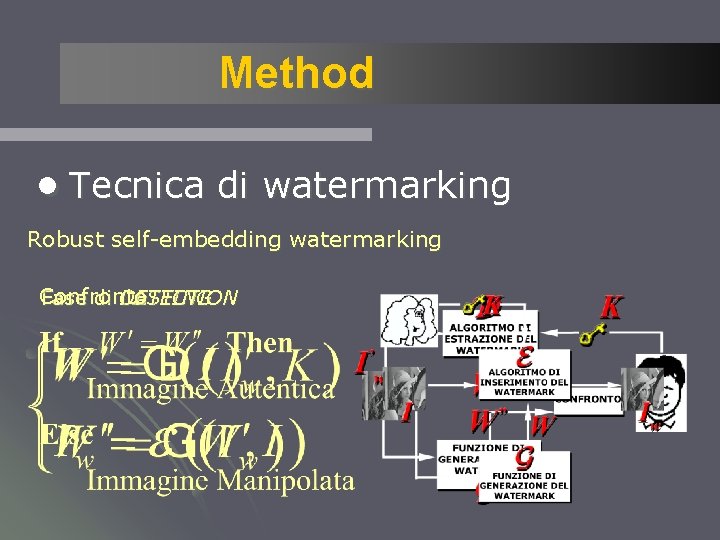
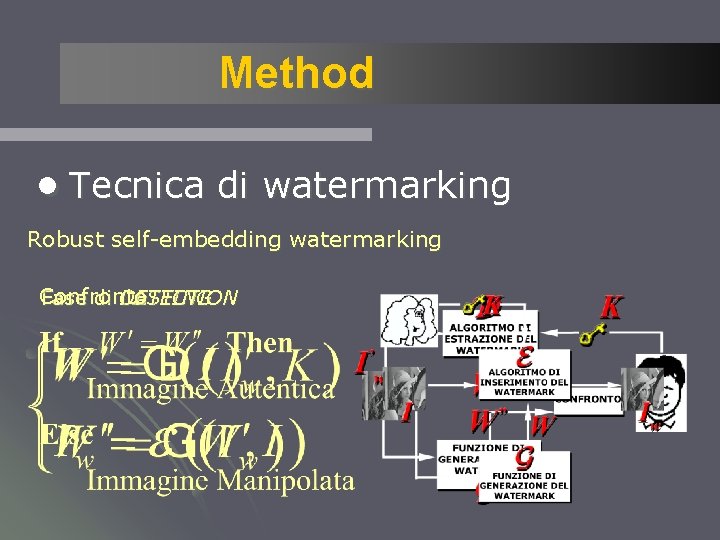
Method ●Tecnica di watermarking Robust self-embedding watermarking Confronto DETECTION Fase di CASTING
Method ●Improvements üWatermark is less visible ü Correct thealterations ü Resistant to JPEG 2000 compression
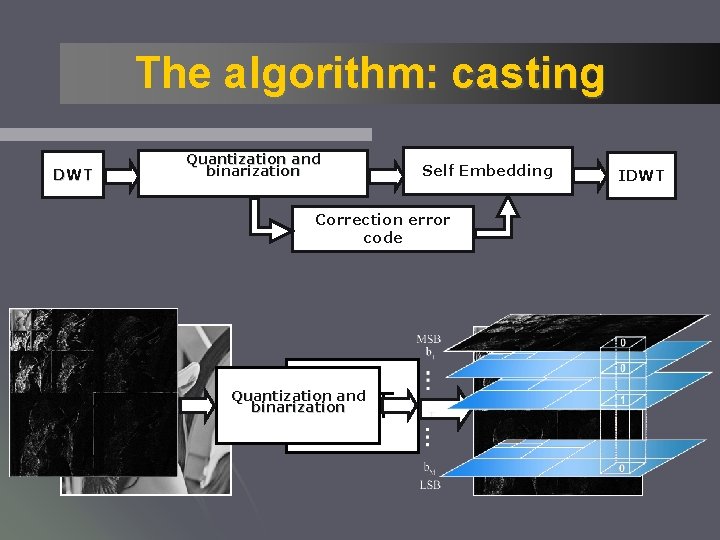
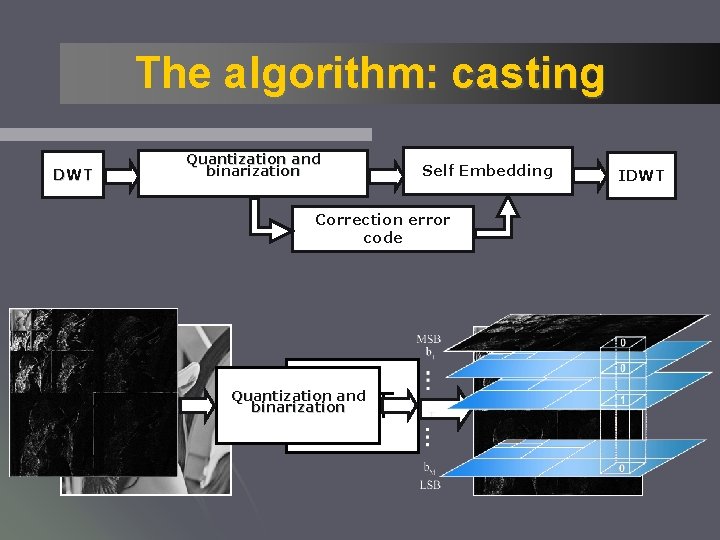
The algorithm: casting DWT Quantization and binarization Self Embedding Correction error code DWT Quantization and binarization IDWT
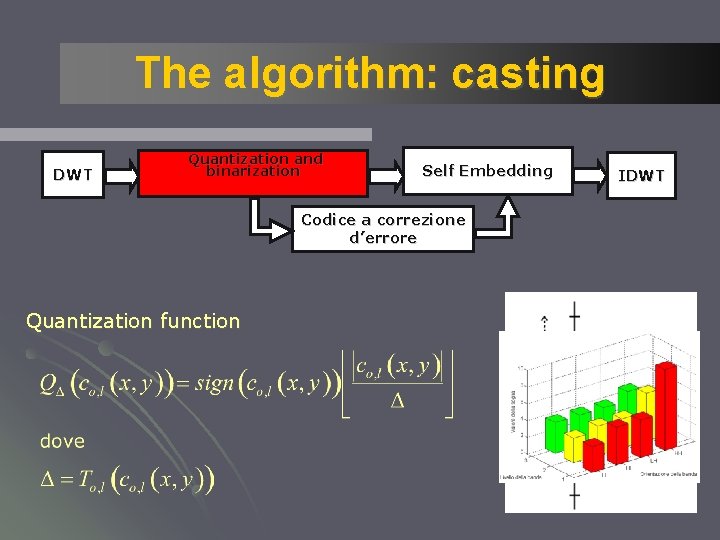
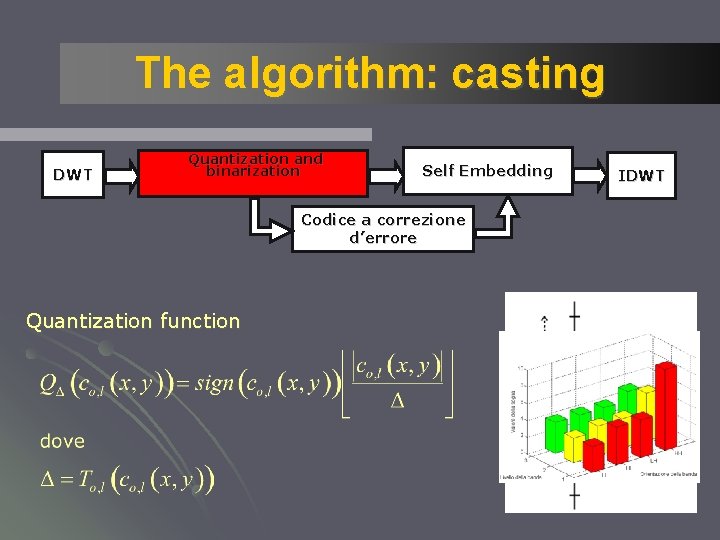
The algorithm: casting DWT Quantization and binarization Self Embedding Codice a correzione d’errore Quantization function IDWT
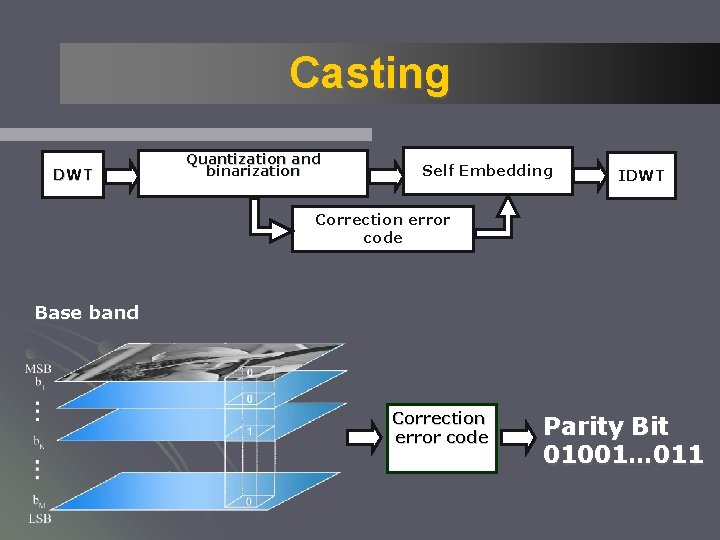
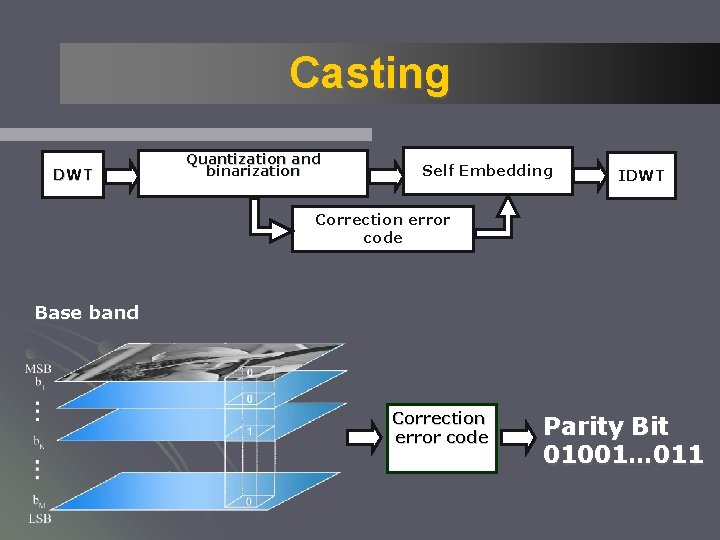
Casting DWT Quantization and binarization Self Embedding IDWT Correction error code Base band Correction error code Parity Bit 01001… 011
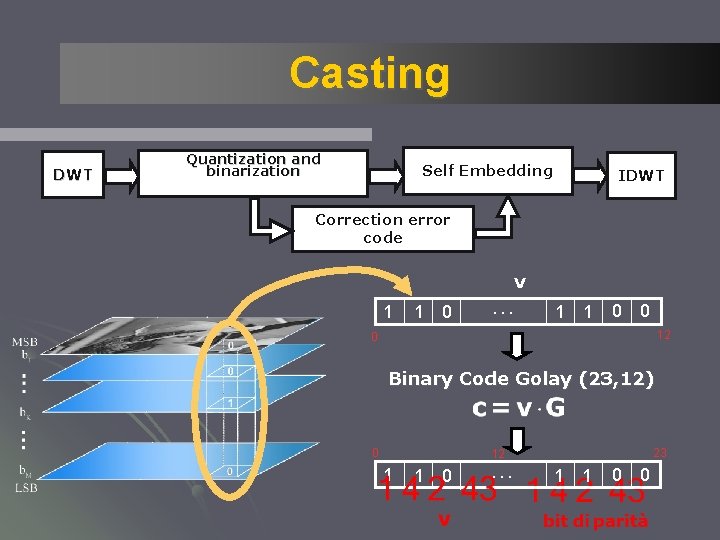
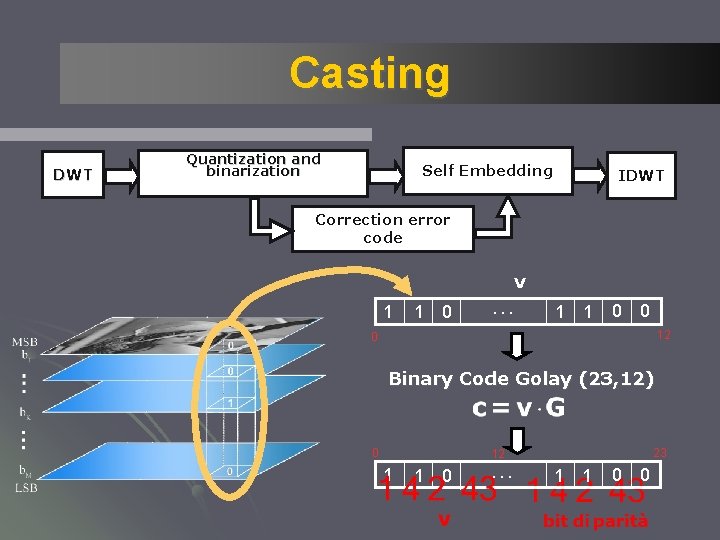
Casting DWT Quantization and binarization Self Embedding IDWT Correction error code v 1 1 0 … 1 1 0 0 12 0 Binary Code Golay (23, 12) 0 23 12 1 1 0 … 1 1 0 0
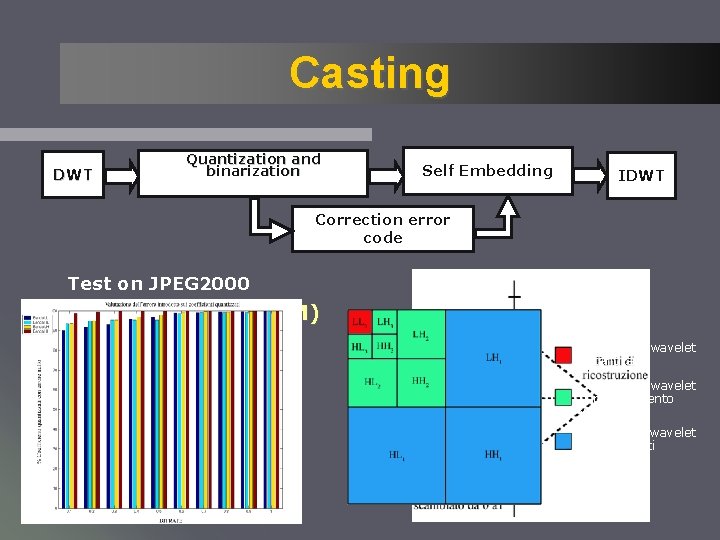
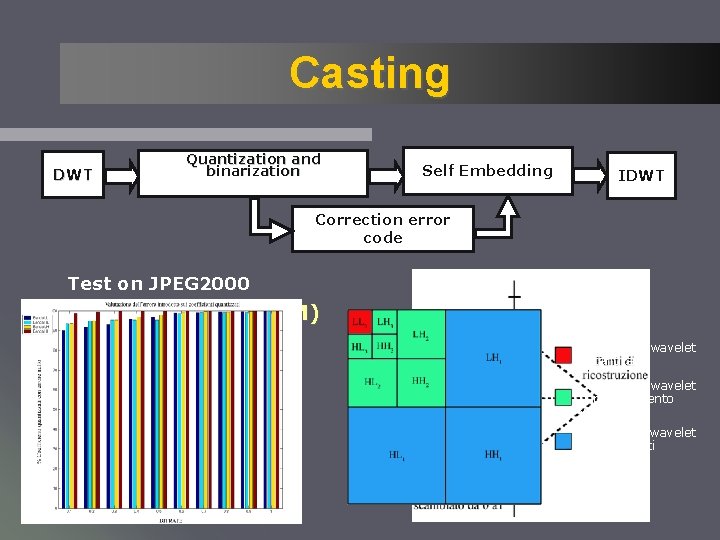
Casting DWT Quantization and binarization Self Embedding IDWT Correction error code Test on JPEG 2000 Low Bit Modulation (LBM) Coefficienti wavelet autenticati Coefficienti wavelet per inserimento watermark Coefficienti wavelet non utilizzati
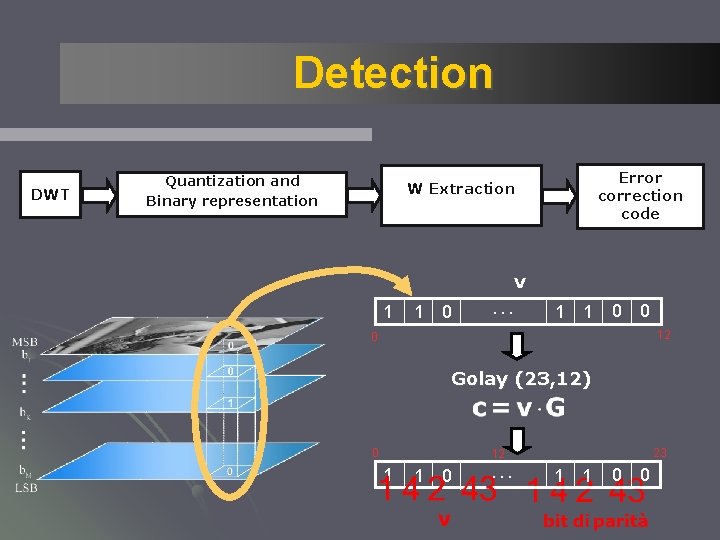
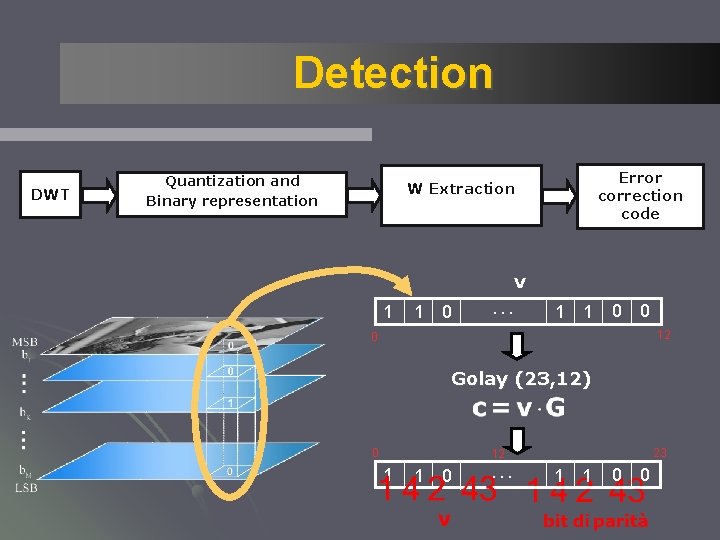
Detection DWT Quantization and Binary representation Error correction code W Extraction v 1 1 0 … 1 1 0 0 12 0 Golay (23, 12) 0 23 12 1 1 0 … 1 1 0 0
Experimental results ●Which images? ●Which Metric? ●Evaluation of watermarking percetion ●Evaluation of robustness ●How to reveal and correct alterations?
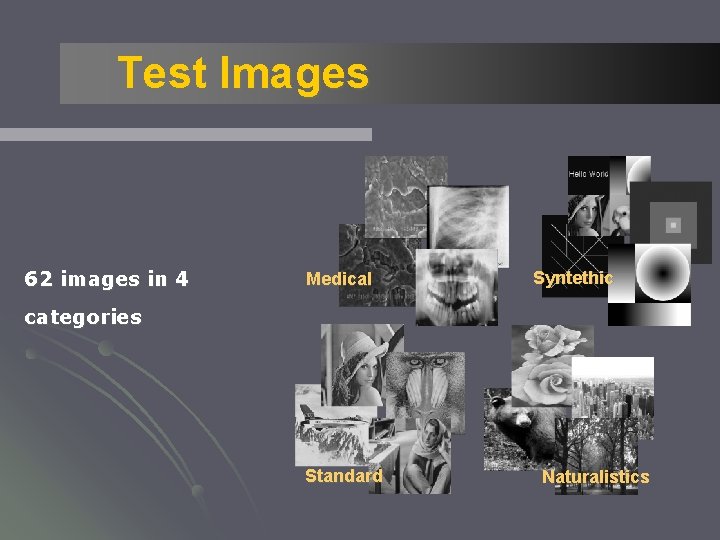
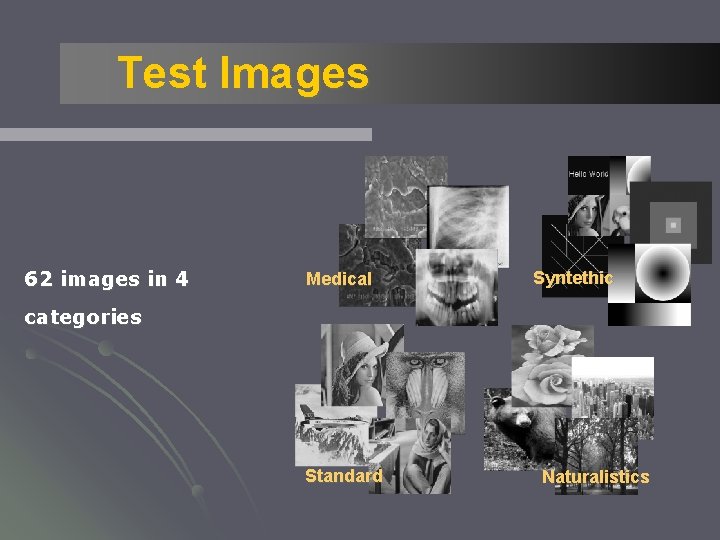
Test Images 62 images in 4 Medical Syntethic categories Standard Naturalistics
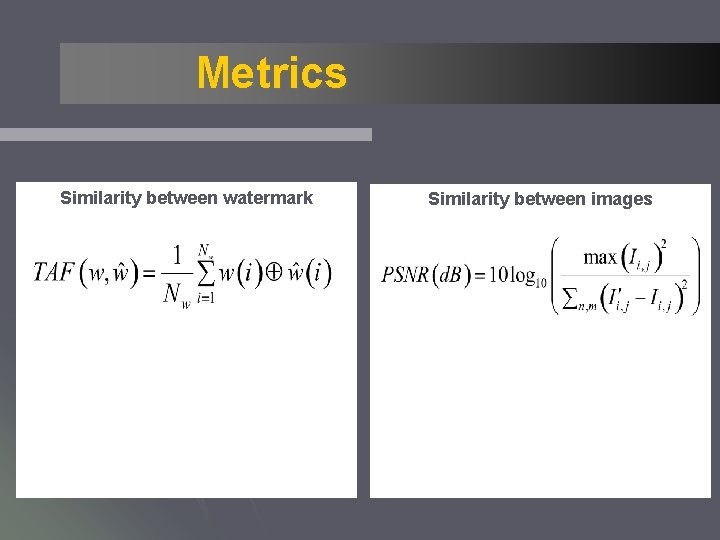
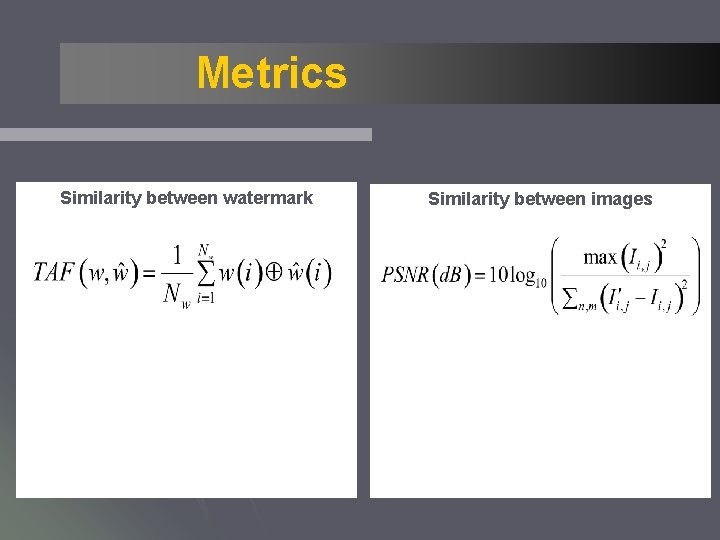
Metrics Similarity between watermark Similarity between images
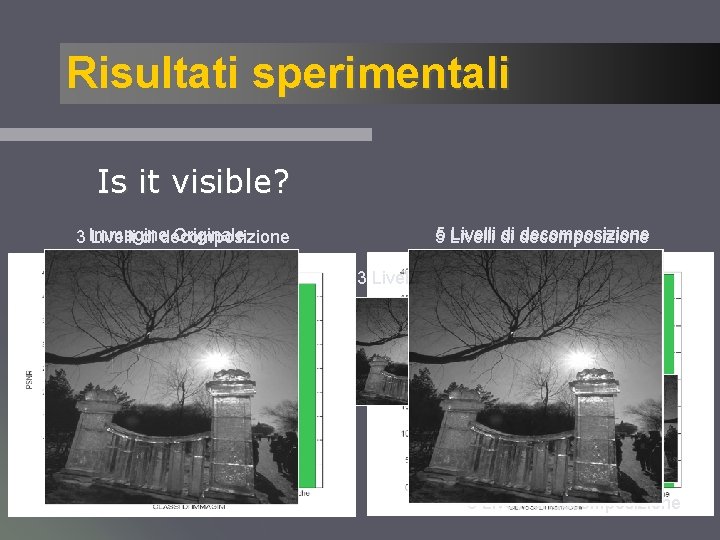
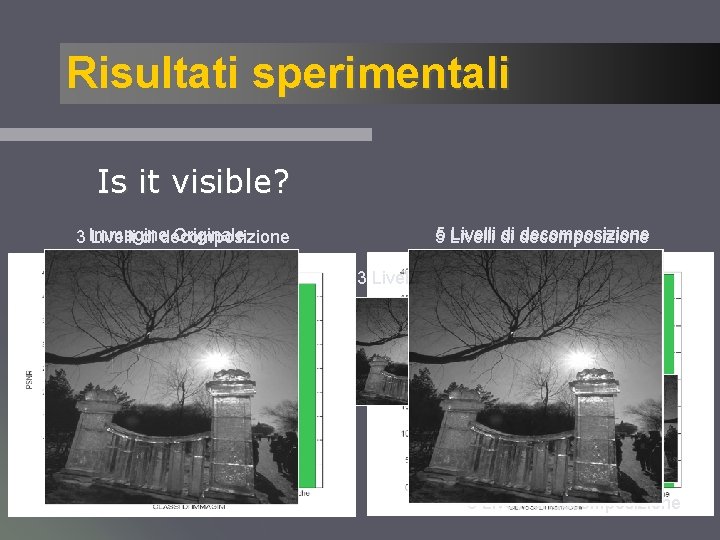
Risultati sperimentali Is it visible? Originale 3 Immagine Livelli di decomposizione 5 Livelli di decomposizione 3 Livelli di decomposizione 5 Livelli di decomposizione
Experimental results What about robustness? ? ? • Simple attacks ü ü Gaussian noise Median filter Gaussian filter lossy compression JPEG 2000 • removal attacks ü Removal of watermark ü removal of an area of the image üLoss of synchronization
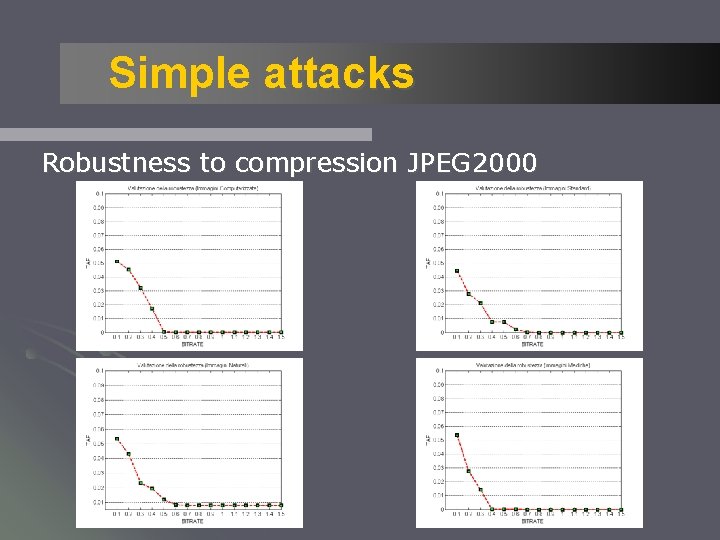
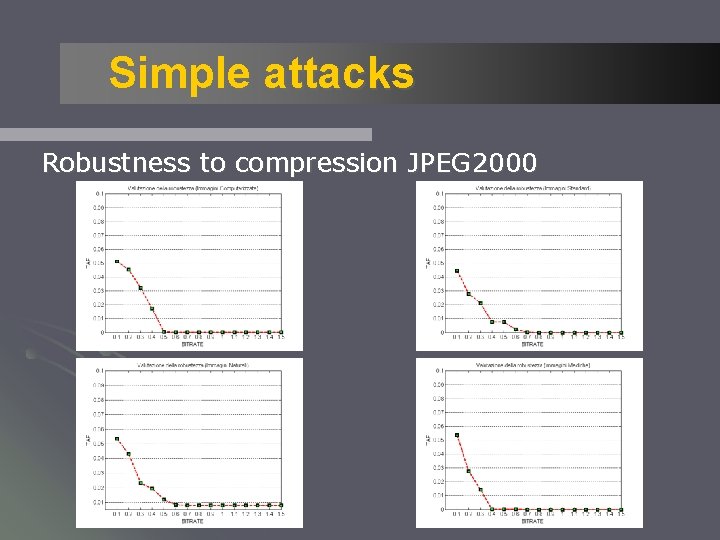
Simple attacks Robustness to compression JPEG 2000
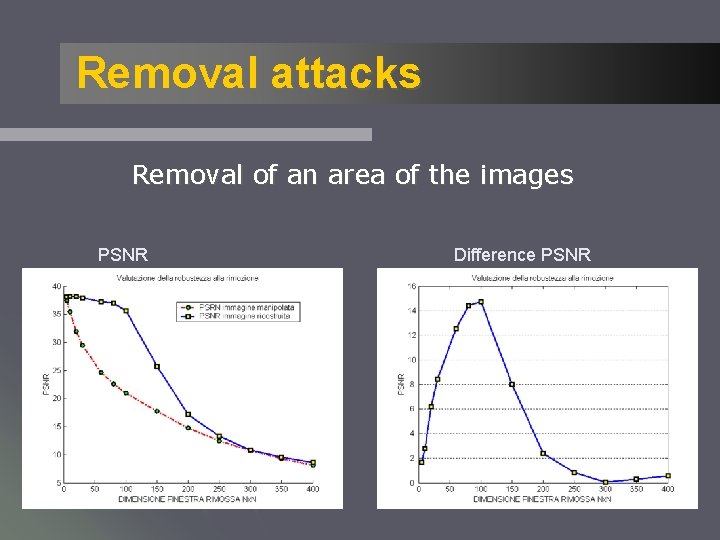
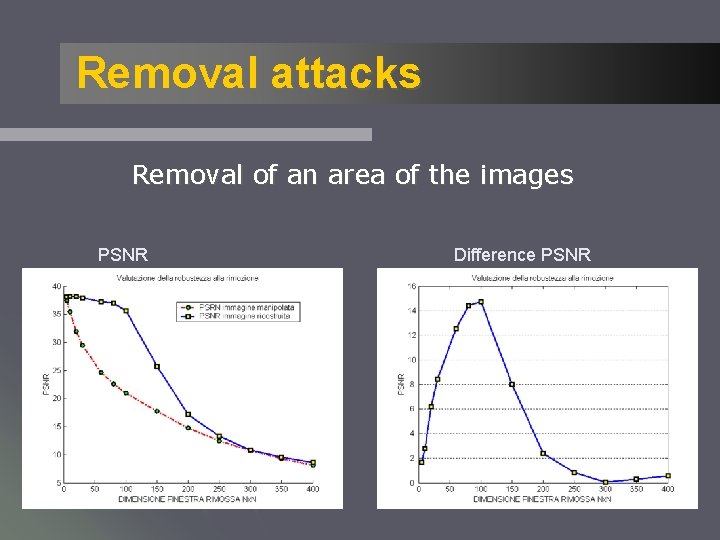
Removal attacks Removal of an area of the images PSNR Difference PSNR
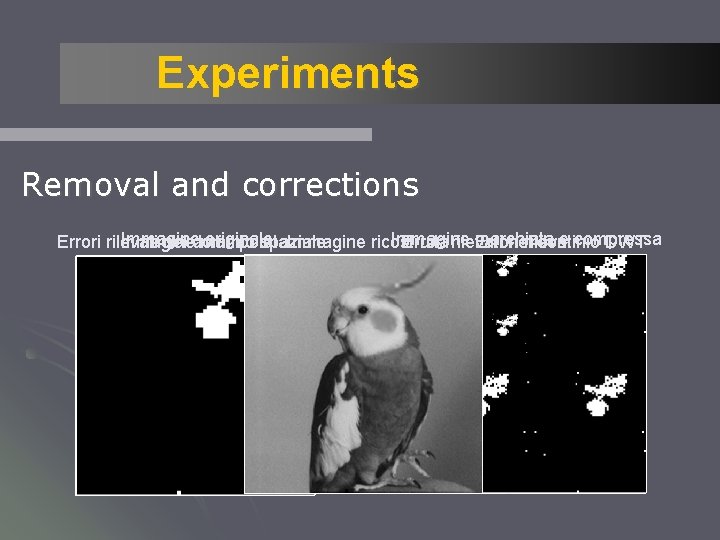
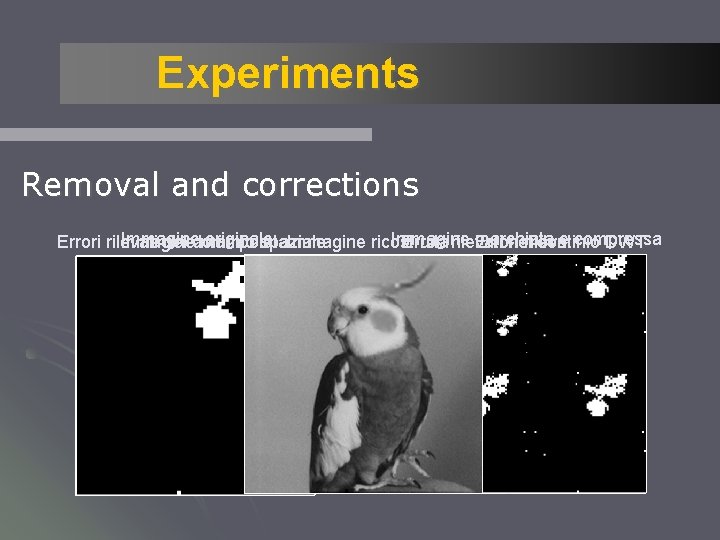
Experiments Removal and corrections Immagine originale Immagine marchiata e compressa Errori rilevati Immagine nel dominio manipolata spaziale Immagine ricostruita Errori rilevati Errori nelrilevati dominio DWT