Insecure Connection Bootstrapping in Cellular Networks The Root
Insecure Connection Bootstrapping in Cellular Networks: The Root of All Evil Syed Rafiul Hussain*, Mitziu Echeverria†, Ankush Singla*, Omar Chowdhury†, Elisa Bertino* Purdue University, University of Iowa
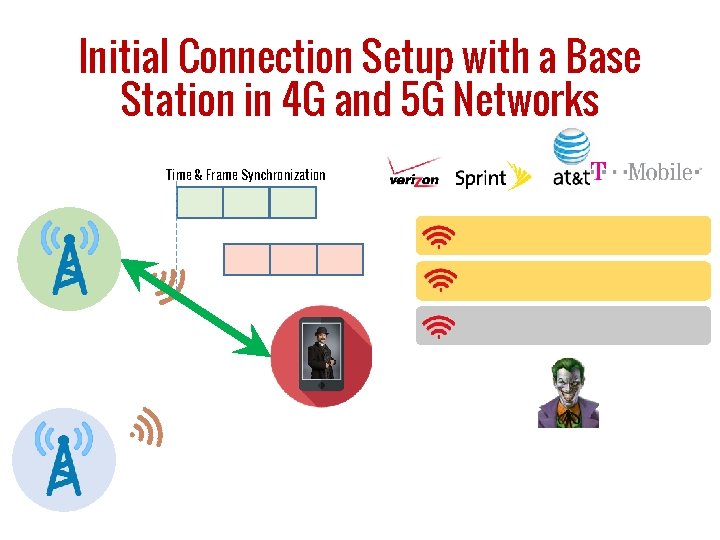
Initial Connection Setup with a Base Station in 4 G and 5 G Networks Time & Frame Synchronization
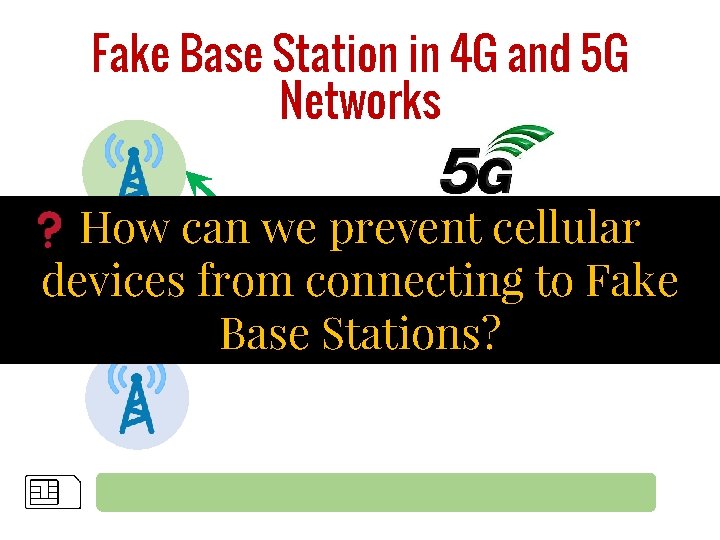
Fake Base Station in 4 G and 5 G Networks How can we prevent cellular devices from connecting to Fake Base Stations? IMSI Response Authentication IMSI Request Reject Registration Reject
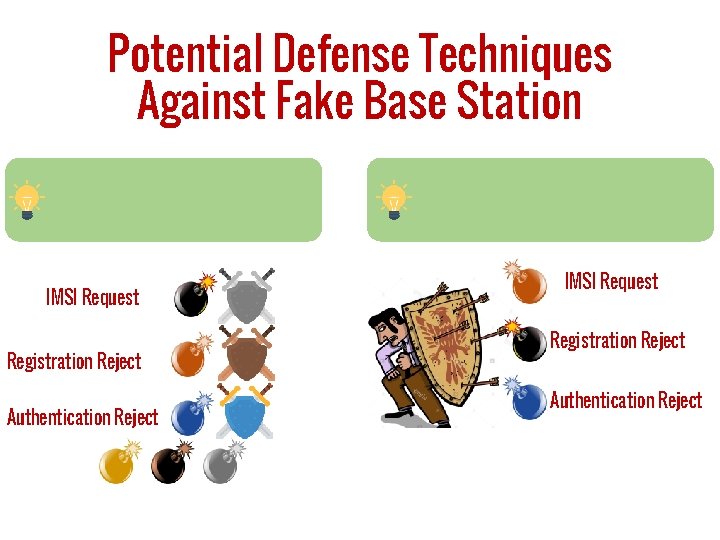
Potential Defense Techniques Against Fake Base Station IMSI Request Registration Reject Authentication Reject
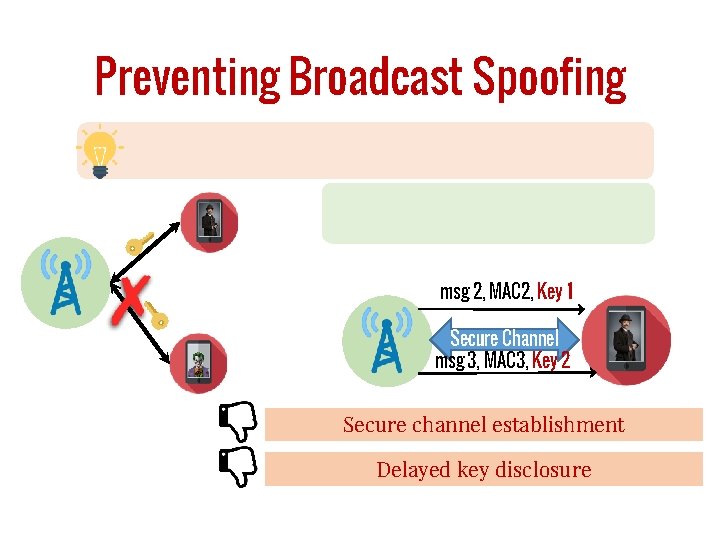
Preventing Broadcast Spoofing msg 2, MAC 2, Key 1 Secure Channel msg 3, MAC 3, Key 2 Secure channel establishment Delayed key disclosure
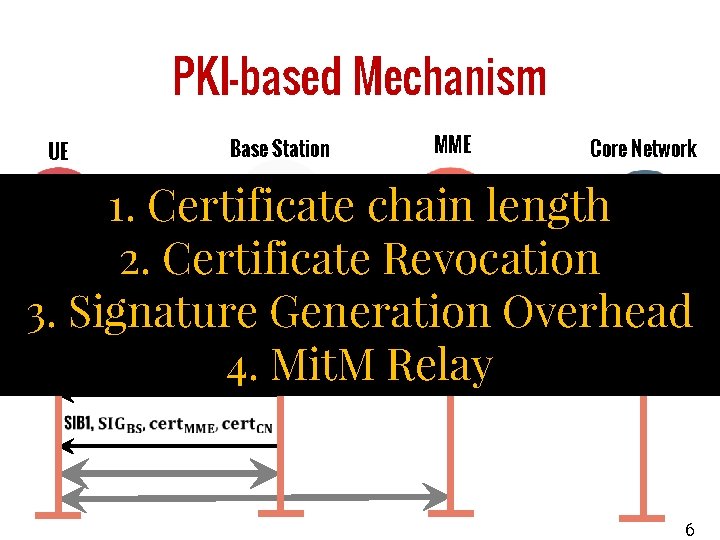
PKI-based Mechanism UE Base Station MME Core Network 1. Certificate chain length 2. Certificate Revocation 3. Signature Generation Overhead 4. Mit. M Relay MME-signed CN-signed Self-signed 6
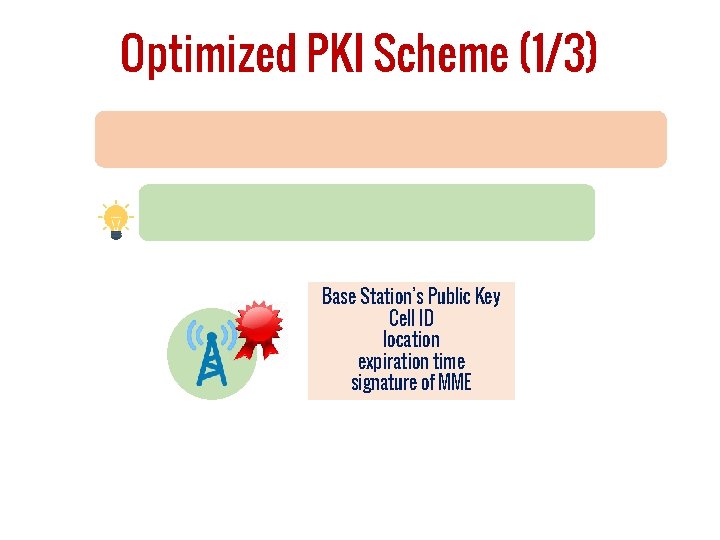
Optimized PKI Scheme (1/3) Base Station’s Public Key Cell ID location expiration time signature of MME
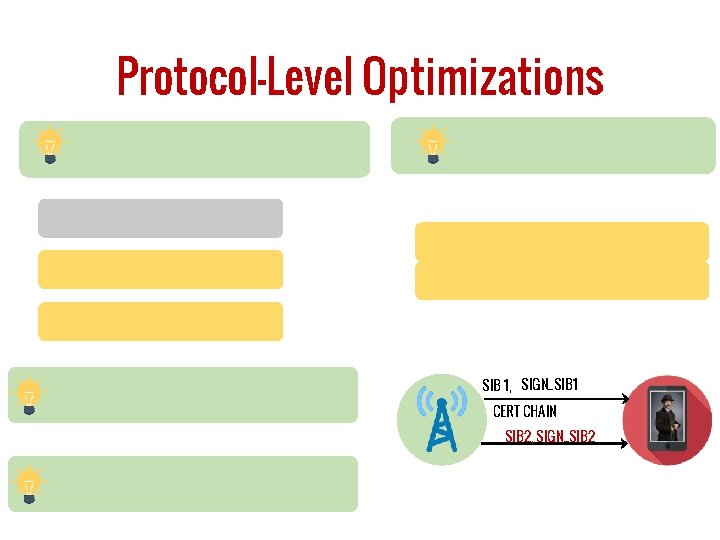
Protocol-Level Optimizations SIB 1, SIGN_SIB 1 CERT CHAIN SIB 2, SIGN_SIB 2
Cryptographic Scheme-level Optimization SIGN_BS, SIGN_MME, SIGN_CN SIB 1, Aggregate
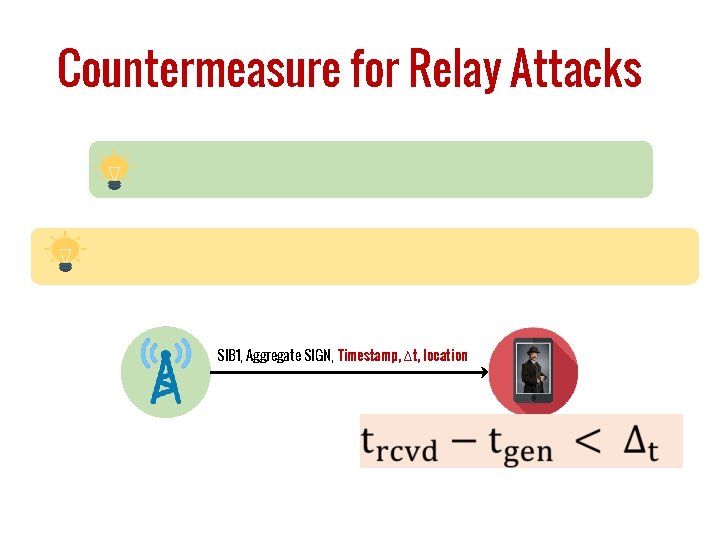
Countermeasure for Relay Attacks SIB 1, Aggregate SIGN, Timestamp, ∆t, location
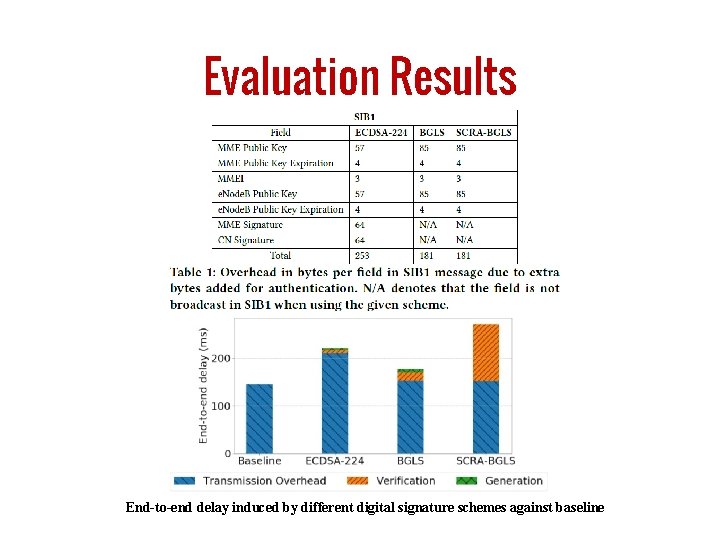
Evaluation Results End-to-end delay induced by different digital signature schemes against baseline
Conclusion

Thank You
Insecure Connection Bootstrapping in Cellular Networks: The Root of All Evil Syed Rafiul Hussain Purdue University hussain 1@purdue. edu
- Slides: 14