Ing Ondej eveek GOPAS a s MCM Directory

- Slides: 13
Ing. Ondřej Ševeček | GOPAS a. s. | MCM: Directory Services | MVP: Enterprise Security | CEH | ondrej@sevecek. com | www. sevecek. com | ACTIVE DIRECTORY FEDERATION SERVICES
AD FS XML over HTTP/S based authentication and "trust" Replacement for AD trusts Free download
AD FS vs. local user stores Local user stores AD LDS (LDAP), SQL, XML, … you must manage the accounts you know their passwords you must reset and unlock and disable AD FS leaves account management on the account partner side you never see their password
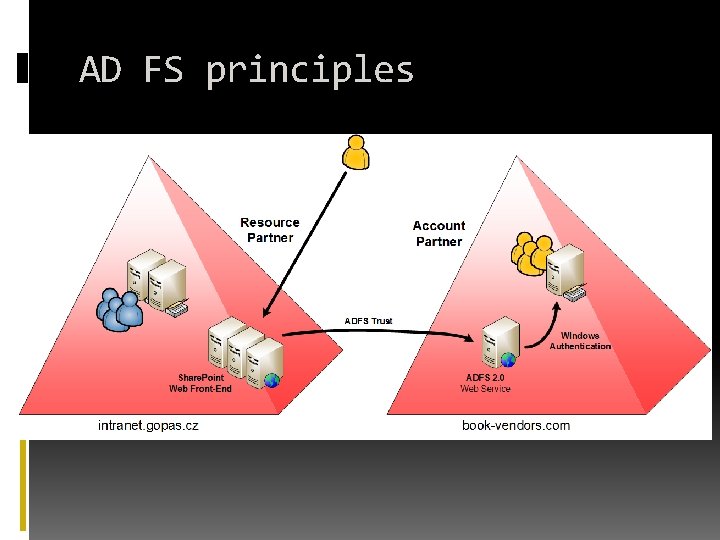
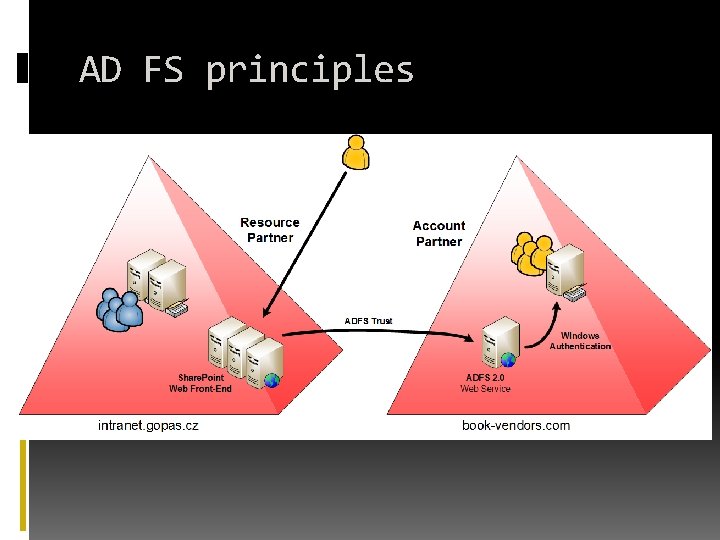
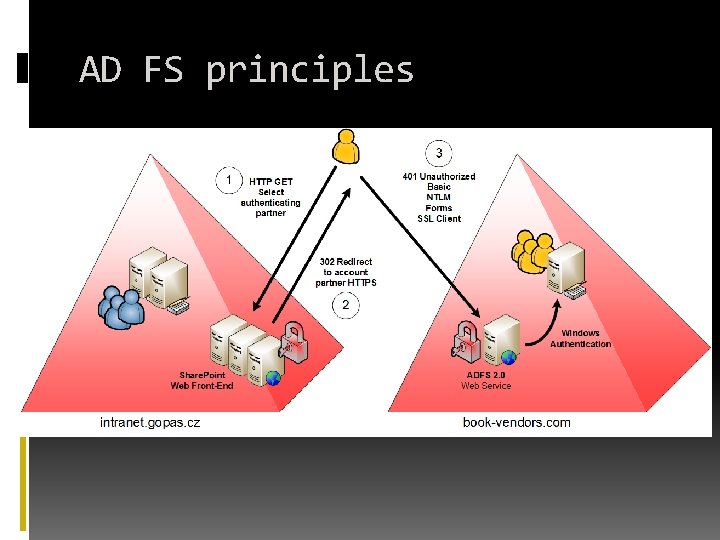
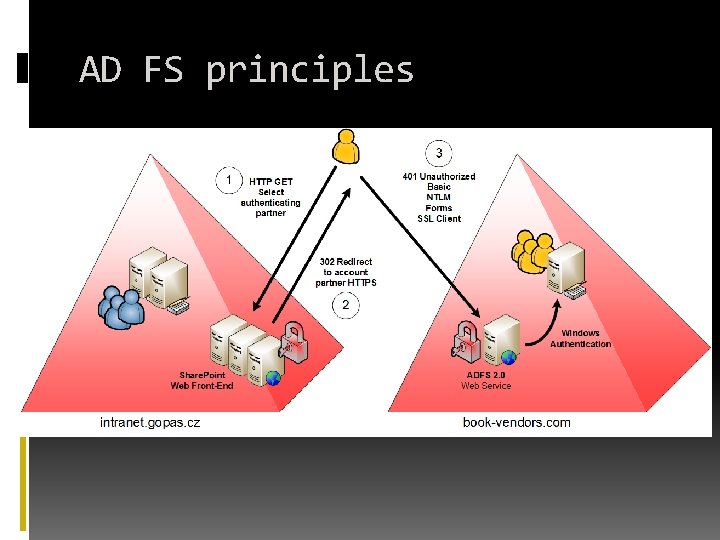
AD FS principles
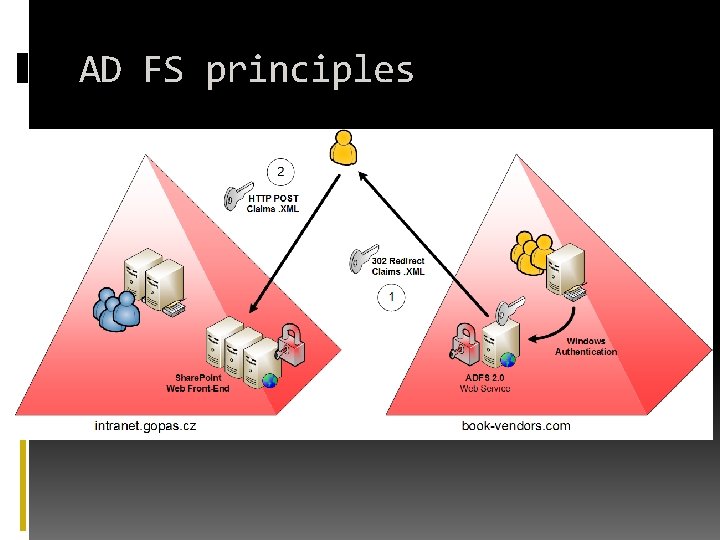
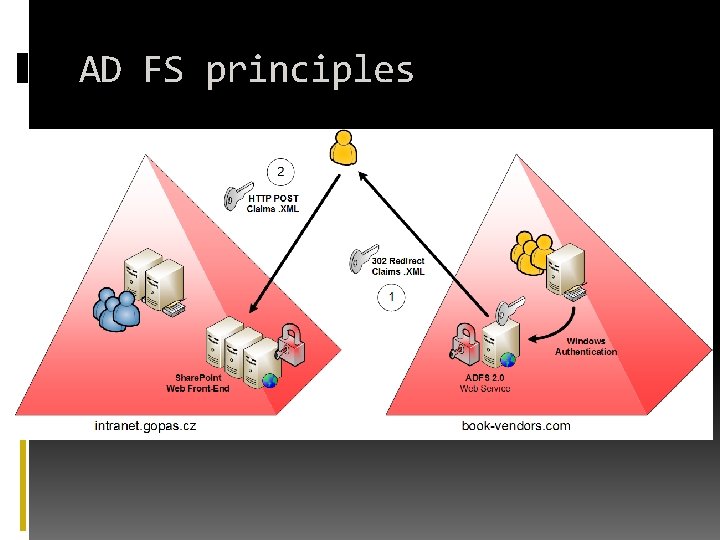
AD FS principles
AD FS principles
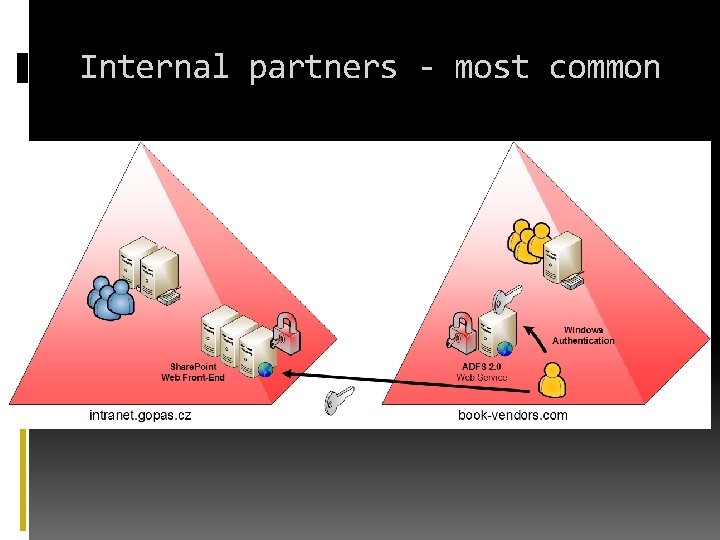
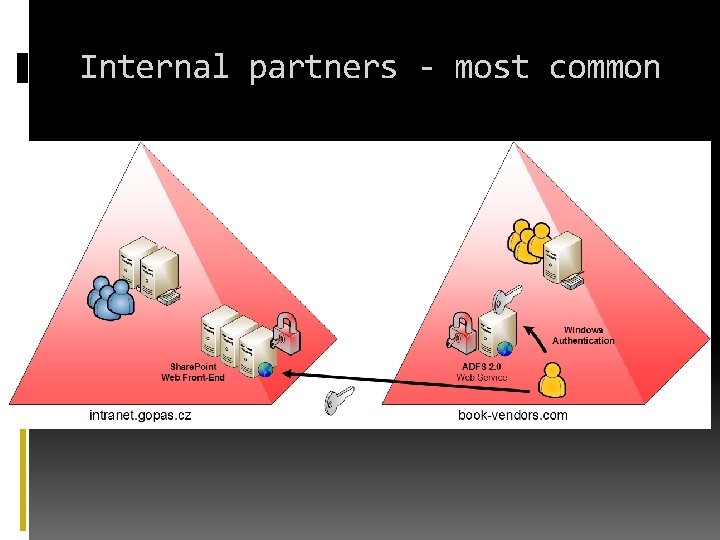
Internal partners - most common
Share. Point WS Federation passive URL This is the resulting redirection after client is authenticated and claims are processed and signed https: //intranet. gopas. cz/_trust/
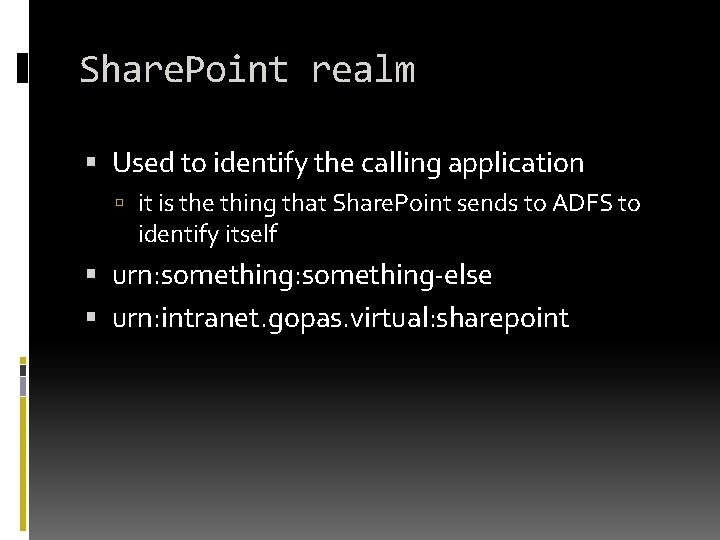
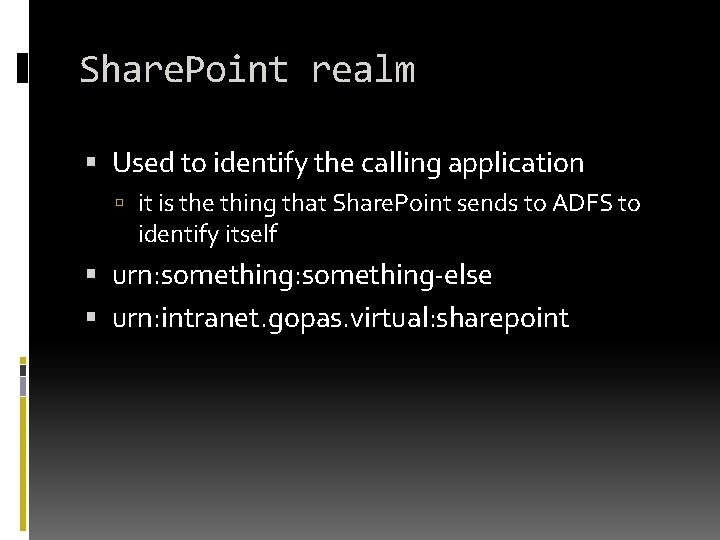
Share. Point realm Used to identify the calling application it is the thing that Share. Point sends to ADFS to identify itself urn: something-else urn: intranet. gopas. virtual: sharepoint
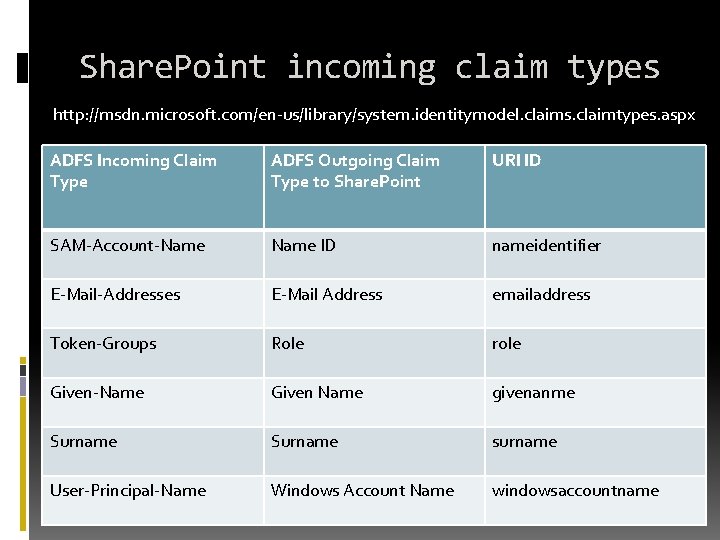
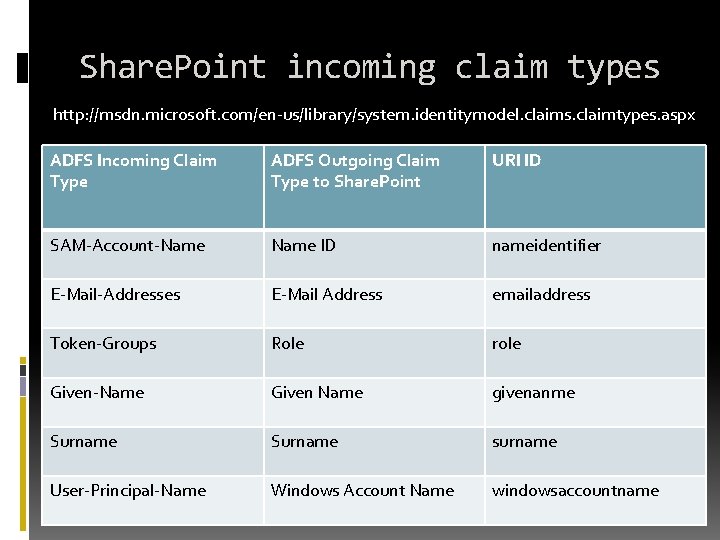
Share. Point incoming claim types http: //msdn. microsoft. com/en-us/library/system. identitymodel. claims. claimtypes. aspx ADFS Incoming Claim Type ADFS Outgoing Claim Type to Share. Point URI ID SAM-Account-Name ID nameidentifier E-Mail-Addresses E-Mail Address emailaddress Token-Groups Role role Given-Name Given Name givenanme Surname surname User-Principal-Name Windows Account Name windowsaccountname
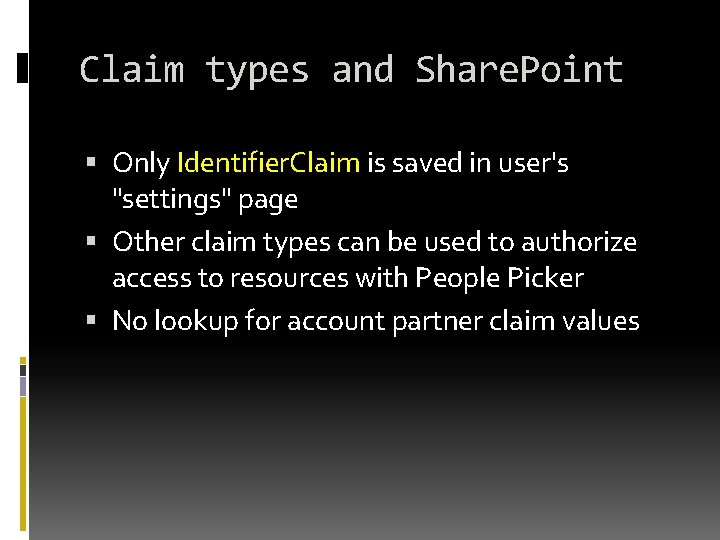
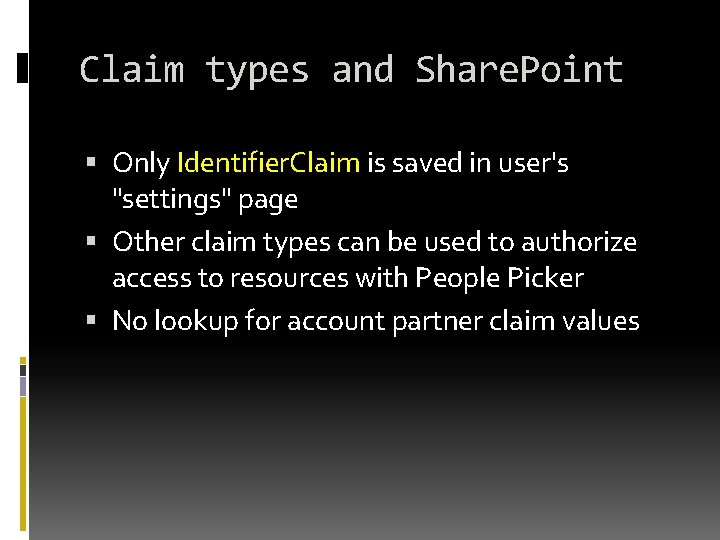
Claim types and Share. Point Only Identifier. Claim is saved in user's "settings" page Other claim types can be used to authorize access to resources with People Picker No lookup for account partner claim values
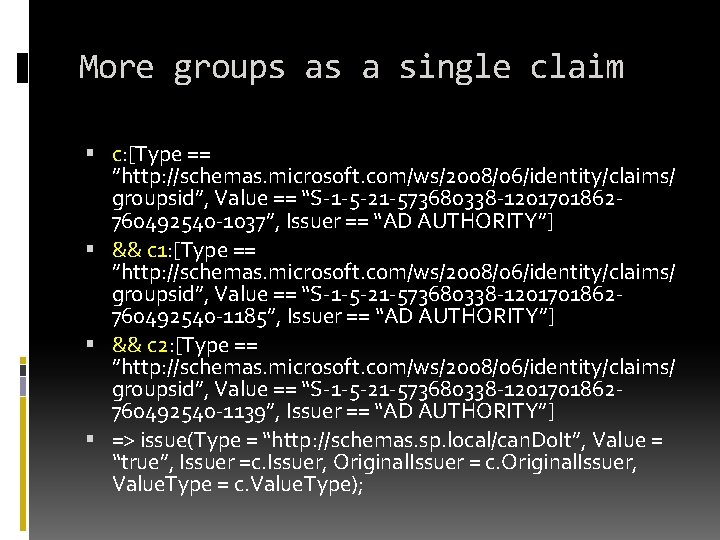
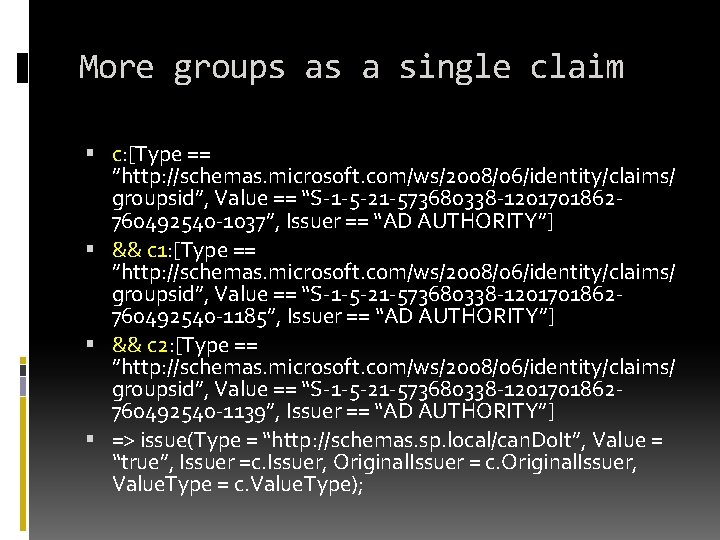
More groups as a single claim c: [Type == ”http: //schemas. microsoft. com/ws/2008/06/identity/claims/ groupsid”, Value == “S-1 -5 -21 -573680338 -1201701862760492540 -1037”, Issuer == “AD AUTHORITY”] && c 1: [Type == ”http: //schemas. microsoft. com/ws/2008/06/identity/claims/ groupsid”, Value == “S-1 -5 -21 -573680338 -1201701862760492540 -1185”, Issuer == “AD AUTHORITY”] && c 2: [Type == ”http: //schemas. microsoft. com/ws/2008/06/identity/claims/ groupsid”, Value == “S-1 -5 -21 -573680338 -1201701862760492540 -1139”, Issuer == “AD AUTHORITY”] => issue(Type = “http: //schemas. sp. local/can. Do. It”, Value = “true”, Issuer =c. Issuer, Original. Issuer = c. Original. Issuer, Value. Type = c. Value. Type);

Ing. Ondřej Ševeček | GOPAS a. s. | MCM: Directory Services | MVP: Enterprise Security | CEH | ondrej@sevecek. com | www. sevecek. com | Active Directory Federation Services THANK YOU!