INFS 766 Internet Security Protocols Lecture 11 PKCS
- Slides: 34
INFS 766 Internet Security Protocols Lecture 11 PKCS Prof. Ravi Sandhu
PKCS Public-key cryptography standards (PKCS) v Owned by RSA and motivated to promote RSA v Created in early 1990’s v Numbered from PKCS 1 to PKCS 15 v Some along the way have v Ø Ø Ø v lost interest folded into other PKCS taken over by other standards bodies Continue to evolve © Ravi Sandhu 2001 2
PKCS 1 v RSA Cryptography Standard Ø Version v RSA Encryption Standard Ø Version © Ravi Sandhu 2001 2. 0 onwards (1998) 1. 5 (1993) 3
PKCS 1 v Specifies how to use the RSA algorithm securely for encryption and signature v Why do we need this? Ø Padding for encryption Ø Different schemes for signature © Ravi Sandhu 2001 4
PKCS 1 v Chosen ciphertext attack based on multiplicative property of RSA Ø Attacker wishes to decrypt c Ø Choose r, compute c’ = c. re mod n Ø Get victim to decrypt c’ giving cd. r mod n Ø cd. r. r-1 mod n = cd mod n v Padding property © Ravi Sandhu 2001 destroys multiplicative 5
PKCS 1 v Version 1. 5, 1993 Ø Encryption padding was found defective in 1998 by Bleichenbacher Ø Possible to generate valid ciphertext without knowing corresponding plaintext with reasonable probability of success (chosen ciphertext) © Ravi Sandhu 2001 6
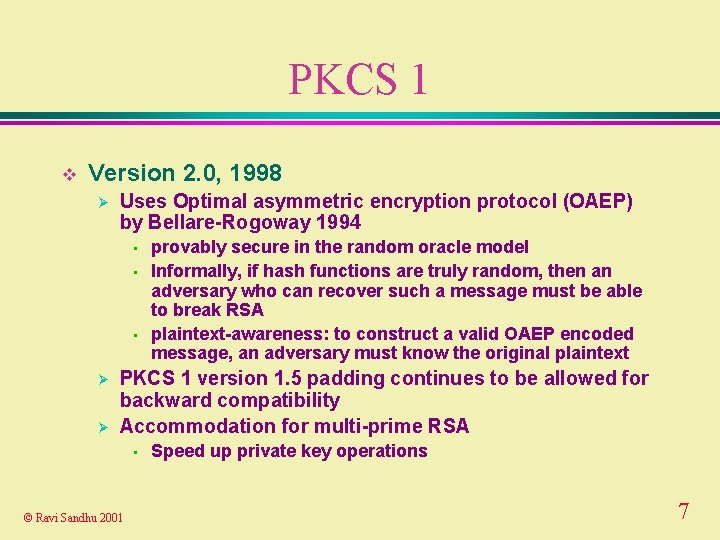
PKCS 1 v Version 2. 0, 1998 Ø Uses Optimal asymmetric encryption protocol (OAEP) by Bellare-Rogoway 1994 • • • Ø Ø provably secure in the random oracle model Informally, if hash functions are truly random, then an adversary who can recover such a message must be able to break RSA plaintext-awareness: to construct a valid OAEP encoded message, an adversary must know the original plaintext PKCS 1 version 1. 5 padding continues to be allowed for backward compatibility Accommodation for multi-prime RSA • © Ravi Sandhu 2001 Speed up private key operations 7
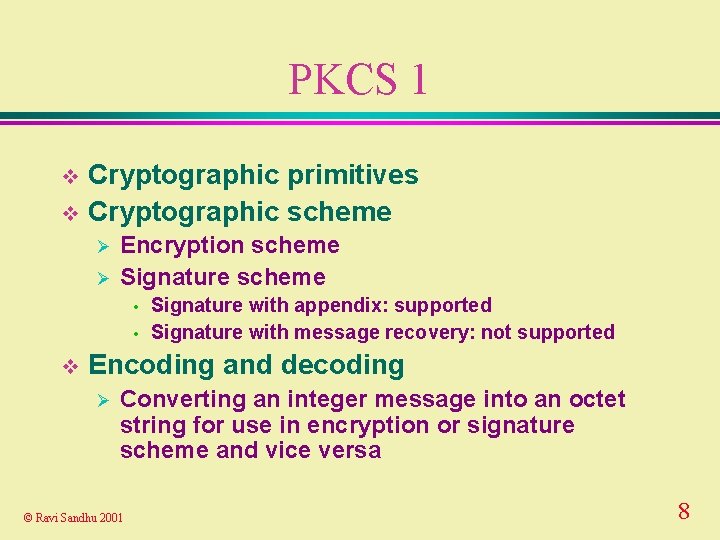
PKCS 1 Cryptographic primitives v Cryptographic scheme v Ø Ø Encryption scheme Signature scheme • • v Signature with appendix: supported Signature with message recovery: not supported Encoding and decoding Ø Converting an integer message into an octet string for use in encryption or signature scheme and vice versa © Ravi Sandhu 2001 8
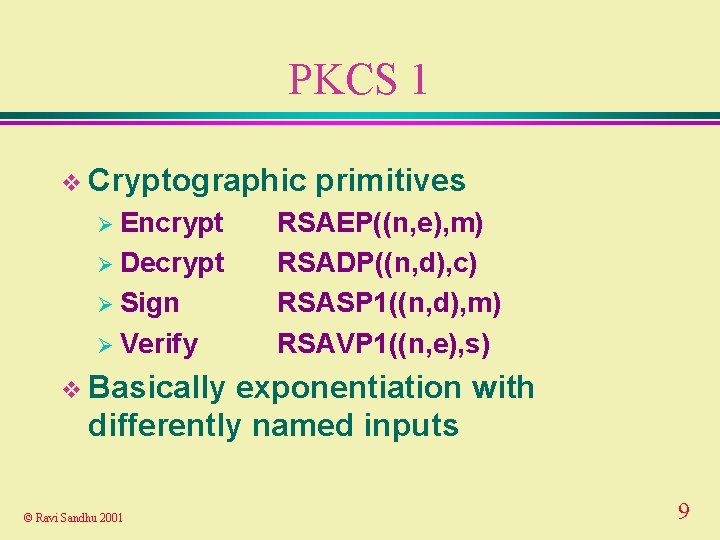
PKCS 1 v Cryptographic Ø Encrypt Ø Decrypt Ø Sign Ø Verify primitives RSAEP((n, e), m) RSADP((n, d), c) RSASP 1((n, d), m) RSAVP 1((n, e), s) v Basically exponentiation with differently named inputs © Ravi Sandhu 2001 9
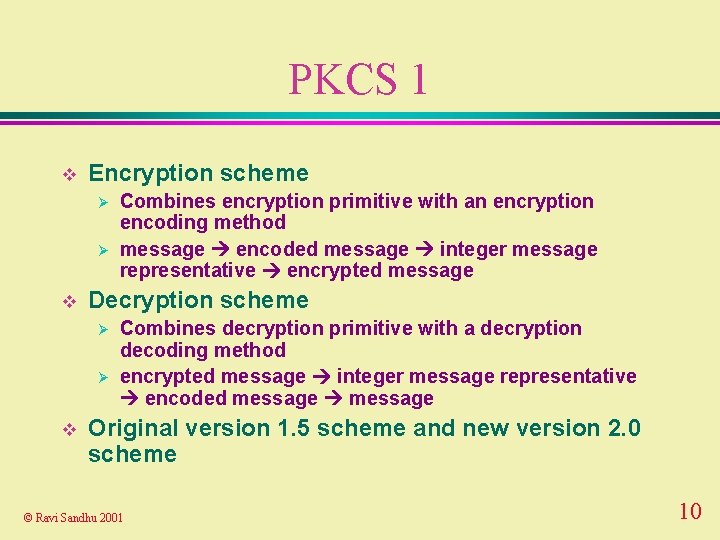
PKCS 1 v Encryption scheme Ø Ø v Decryption scheme Ø Ø v Combines encryption primitive with an encryption encoding method message encoded message integer message representative encrypted message Combines decryption primitive with a decryption decoding method encrypted message integer message representative encoded message Original version 1. 5 scheme and new version 2. 0 scheme © Ravi Sandhu 2001 10
PKCS 1 v Signature scheme Ø Ø v Decryption scheme Ø Ø v Combines signature primitive with a signature encoding method message encoded message integer message representative signature Combines verification primitive with a verification decoding method signature integer message representative encoded message Original version 1. 5 scheme Ø Signature with appendix © Ravi Sandhu 2001 11
PKCS 1 The future v Probabilistic signature scheme (PSS) v Ø Ø Provably secure in random oracle model Natural extension to message recovery © Ravi Sandhu 2001 12
PKCS 5 v Password-Based Standard Cryptography Ø Version 1. 5, 1993 Ø Version 2. 0, 1999 v Oriented towards protection of private keys v Does not specify a standard for password format © Ravi Sandhu 2001 13
PKCS 5 v Password-based Ø Key key derivation function = PBKDF(passwd, salt, iteration count) v salt allows same password to give many keys Ø May actually have same password Ø Separate dictionary attack for every salt v Iteration count controls complexity of dictionary attack © Ravi Sandhu 2001 14
PKCS 5 v Version 1. 5 PBKDF 1 Ø Key size limited to 160 bits Ø Only MD 5 and SHA as underlying hash functions Ø Assumes key will be used for CBC Ø 8 -byte salt Ø No security proof © Ravi Sandhu 2001 15
PKCS 5 v Version 2. 0 adds PBKDF 2 Ø Arbitrary length key Ø Any underlying hash function, most likely with HMAC Ø Salt not fixed at 8 bytes Ø Provable security in random oracle model © Ravi Sandhu 2001 16
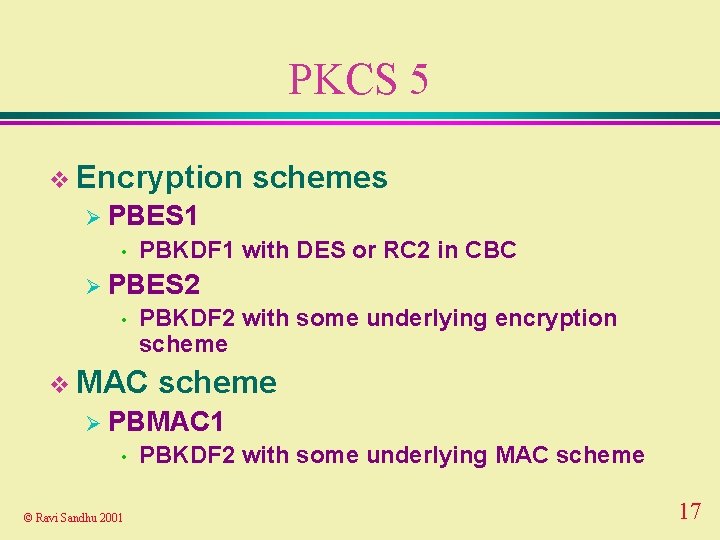
PKCS 5 v Encryption schemes Ø PBES 1 • PBKDF 1 with DES or RC 2 in CBC Ø PBES 2 • PBKDF 2 with some underlying encryption scheme v MAC scheme Ø PBMAC 1 • © Ravi Sandhu 2001 PBKDF 2 with some underlying MAC scheme 17
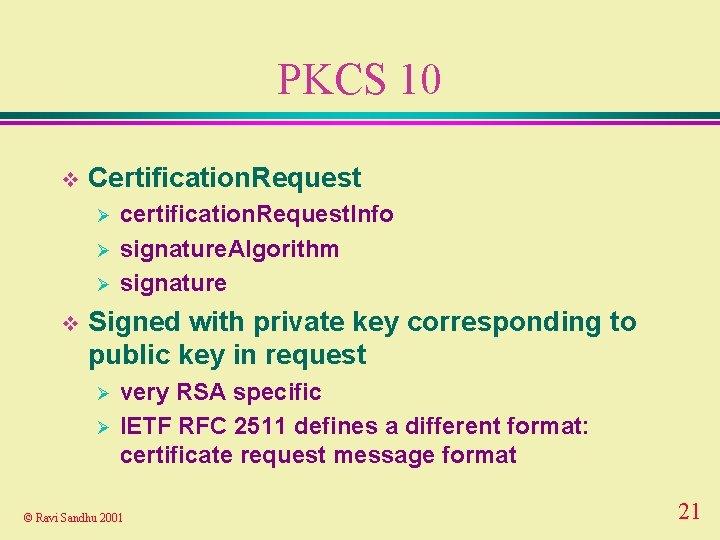
PKCS 10 v Certification Request Syntax Standard v Specifies format of unsigned certificate requested to be signed v Does not specify format of returned signed certificate © Ravi Sandhu 2001 18
PKCS 10 v Version Ø In 1. 0, 1993 widespread use v Version 1. 5, 1998 v Version 1. 7, 2000 Ø Minor changes such as references to PKCS 6 replaced by references to X. 509 v 3 © Ravi Sandhu 2001 19
PKCS 10 v Certification. Request. Info Ø version Ø subject. Name Ø subject. Public. Key. Info Ø attributes © Ravi Sandhu 2001 20
PKCS 10 v Certification. Request Ø Ø Ø v certification. Request. Info signature. Algorithm signature Signed with private key corresponding to public key in request Ø Ø very RSA specific IETF RFC 2511 defines a different format: certificate request message format © Ravi Sandhu 2001 21
PKCS 8 v Private-Key Information Syntax Standard Ø Version © Ravi Sandhu 2001 1. 2, 1993 22
PKCS 8 v Private. Key. Info Ø version Ø private. Key. Algorithm Ø private. Key Ø attributes © Ravi Sandhu 2001 23
PKCS 8 v encrypted. Private. Key. Info Ø encryption. Algorithm Ø encrypted. Data • private. Key. Info BER-encoded and encrypted v Usually © Ravi Sandhu 2001 encrypted using PKCS 5 24
PKCS 12 v Personal Information Exchange Syntax Standard Ø Version 1, 1999 v Builds on PKCS 8 v Further evolution PKCS 15 © Ravi Sandhu 2001 25
PKCS 12 v 6 types of information Ø Ø Ø PKCS 8 shrouded key Private key Certificates • • Ø CRLs • Ø X. 509 Secret • Ø X. 509 v 3 SDSI Whatever Recursive composition of these © Ravi Sandhu 2001 26
PKCS 12 v Each of these can be Ø Plaintext Ø Enveloped • Encrypted using a secret key which is encrypted using a public key Ø Encrypted • • Secret key encrypted Usually password derived – Use PKCS 5 and a password formatting standard which is part of PKCS 12 © Ravi Sandhu 2001 27
PKCS 12 v The entire stuff is then either Ø Signed • And accompanied with signing certificate Ø MAC’ed • PKCS 5 based and accompanied with salt and iteration count v Notice: opposite of usual sequence Ø Encrypt and then authenticate, versus Ø Authenticate and then encrypt © Ravi Sandhu 2001 28
PKCS DISCONTINUED OR DISINTERESTED v PKCS 2 Ø discontinued, v PKCS 3 Ø Diffie-Hellman v PKCS Key Agreement, 1993 4 Ø discontinued, © Ravi Sandhu 2001 incorporated into PKCS 1 29
PKCS TAKEN OVER BY OTHERS v PKCS 6 Ø Extended Certificate Syntax Standard Ø Taken over by X. 509 v 3 v PKCS 7 Ø Cryptographic Message Syntax Standard Ø Taken over by IETF PKIX CMS © Ravi Sandhu 2001 30
PKCS 9 v PKCS 9 Ø Selected Attribute Types Ø For use in PKCS 6, 7, 8, 10 © Ravi Sandhu 2001 31
PKCS 11 v PKCS 11 Ø Cryptographic Token Interface Standard Ø API used by Netscape (pre 6. 0) Ø Microsoft CSP (Cryptographic Service Provider) is a competitor © Ravi Sandhu 2001 32
PKCS IN DEVELOPMENT v PKCS 13 (new, in development) Ø Ø v PKCS 14 (new, in development) Ø v Elliptic Curve Cryptography Standard There are IEEE standards, so not clear why Pseudorandom Number Generation Standard PKCS 15 (new, in development) Ø Ø Cryptographic Token Information Format Standard Crypto API neutral © Ravi Sandhu 2001 33
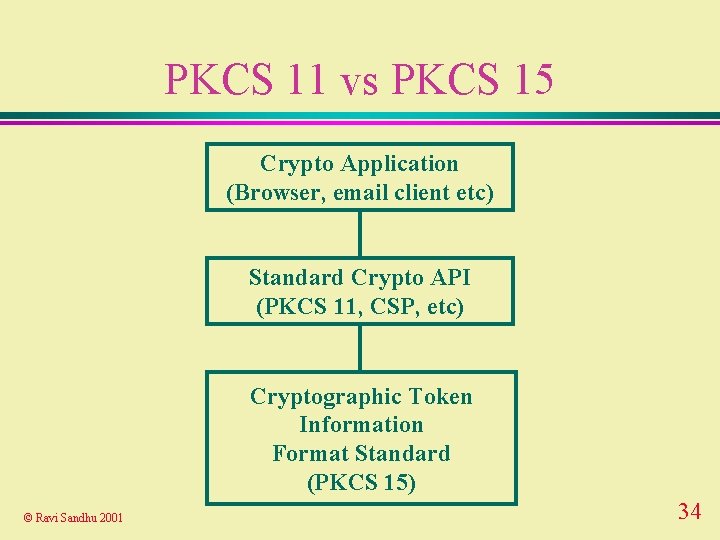
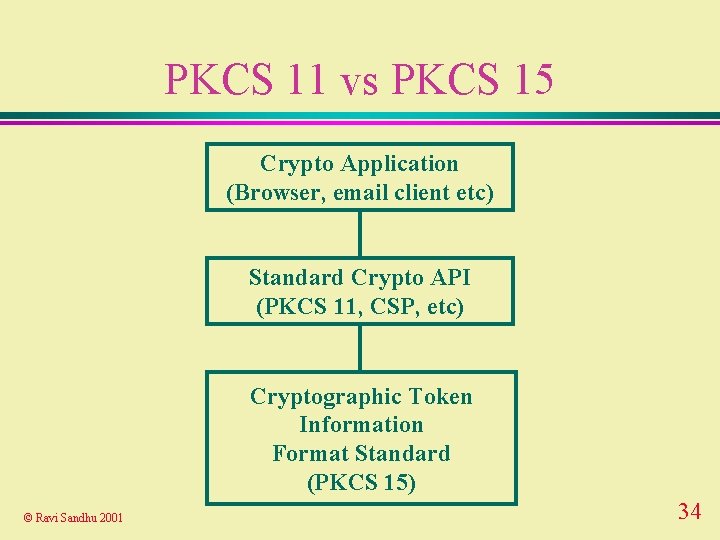
PKCS 11 vs PKCS 15 Crypto Application (Browser, email client etc) Standard Crypto API (PKCS 11, CSP, etc) Cryptographic Token Information Format Standard (PKCS 15) © Ravi Sandhu 2001 34