Information Warfare Playgrounds to Battlegrounds Last Class Theory
Information Warfare Playgrounds to Battlegrounds
Last Class: Theory of IW WIN-LOSE NATURE OF OPERATIONS l Information resources l Players l Offensive operations l Defensive operations CSCE 727 - Farkas 2
Security Objectives l Confidentiality l Integrity l Availability CSCE 727 - Farkas 3
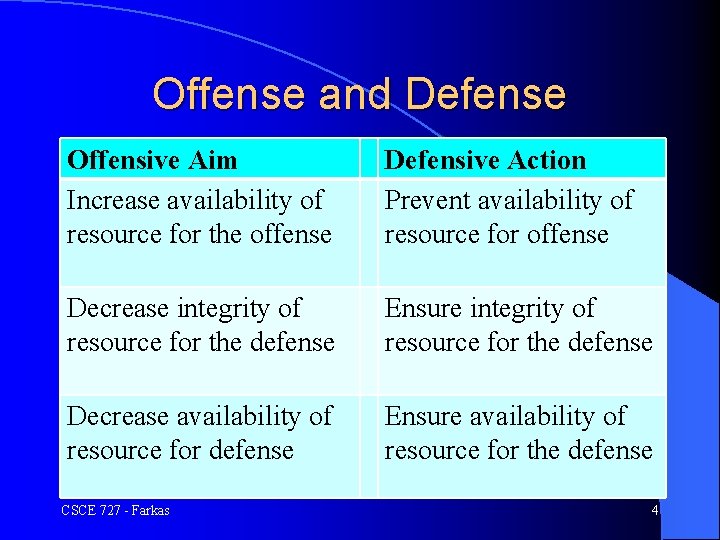
Offense and Defense Offensive Aim Increase availability of resource for the offense Defensive Action Prevent availability of resource for offense Decrease integrity of resource for the defense Ensure integrity of resource for the defense Decrease availability of resource for defense Ensure availability of resource for the defense CSCE 727 - Farkas 4
Offense: Increased availability l l l Collection of secret: – Espionage (illegal) and intelligence (may be legal) Piracy Penetration (hacking) Superimposition fraud (use by the offense on the defense’s legitimate usage) Identity theft Perception management (affect beliefs and behavior) CSCE 727 - Farkas 5
Offense: Decrease Availability for Defense l Physical theft l Sabotage l Censorship CSCE 727 - Farkas 6

Offense: Decreased Integrity l Tampering l Penetration – Cover up – Virus, worm, malicious code l Perception management – Fabrication, forgeries, fraud, identity theft, social engineering CSCE 727 - Farkas 7
Defense – What Not to do Closing The Barn Door After The Horse Is Gone From: http: //blog. johnlund. com/2013/10/closing-barn-door-after-horse-is-gone. html CSCE 727 - Farkas 8
Defense l Emergency preparedness: preparedness capability to recover from and response to attacks l Prevention: keeps attacks from occurring l Deterrence: makes attack unattractive l Indications and warning: recognize attacks before it occurs l Detection: recognize attacks l Response: actions taken after the attack CSCE 727 - Farkas 9

Playgrounds to Battlegrounds
IW Activities l Context of human actions and conflict l Domains: – Play: hackers vs. owners – Crime: perpetrators vs. victims – Individual rights: individuals vs. individuals/organizations/government – National security: national level activities CSCE 727 - Farkas 11
Play l l l Playing pranks Actors: hackers/crackers/phreakers Motivation: challenge, knowledge, thrill Culture: social/educational – “global networks” – publications – forums Law – DHS, Cybersecurity Laws & Regulations, http: //www. dhs. gov/cybersecurity-laws-regulations CSCE 727 - Farkas 12
Crime Intellectual Property Crimes – IT targets: research and development, manufacturing and marketing plan, customer list, etc. – 1996: Economic Espionage Act (U. S. Congress) + amendments l Fraud – Telemarketing scam, identity theft, bank fraud, telecommunication fraud, computer fraud and abuse l Fighting crime l l l P. Roberts, U. S. Congress Hears Of Growing Cyber Espionage Threat To U. S. , 06/29. 2012, http: //threatpost. com/en_us/blogs/us-congress-hearsgrowing-cyber-espionage-threat-us-062912 CSCE 727 - Farkas 13
Crime l Actors: – – – Employees Temporary staff Vendors Suppliers Consultants Trade secrets l Identity theft l Law l CSCE 727 - Farkas 14
Individual Rights Privacy – Secondary use of information l Free speech – Harmful/disturbing speech – Theft and distribution of intellectual property – Censorship l E. Moyer, In Swartz protest, Anon hacks U. S. site, threatens leaks, 01/28/2013, http: //news. cnet. com/83011009_3 -57566016 -83/in-swartz-protest-anon-hacks-u. s-site -threatens-leaks/ l CSCE 727 - Farkas 15
National Security l Foreign Intelligence – Peace time: protecting national interests l Open channels, human spies, electronic surveillance, electronic hacking (? ) – War time: support military operations – U. S. Intelligence Priorities: l l l Intelligence supporting military needs during operation Intelligence about hostile countries Intelligence about specific transnational threats – Central Intelligence Agency (CIA) – Primary targets in USA: high technology and defense- related industry CSCE 727 - Farkas 16
War and Military Conflict l IT support, e. g. , sensors, weapons, surveillance, etc. l Psyops and perception management l Physical weapons (? ) l Cyber space battle (? ) l Unmanned devices (? ) CSCE 727 - Farkas 17
Terrorism l Traditional: – Intelligence collection – Psyops and perception management l New forms: – Exploitation of computer technologies Internet propaganda l Cyber attacks (electronic mail flooding, DOS, etc. ) l l Protection CSCE 727 - Farkas of national infrastructure 18
Awareness l Insider threat l Remote access – authentication l Counterfeit hardware l Abuse of security guidelines CSCE 727 - Farkas 19
Origin of Attacks l Vulnerable computers – Dependence on computers – Education of users – Economy – Monopoly of OS l Non-state CSCE 727 - Farkas actors 20
- Slides: 20